
Phishing Analysis
Detailed analysis of captured phishing page
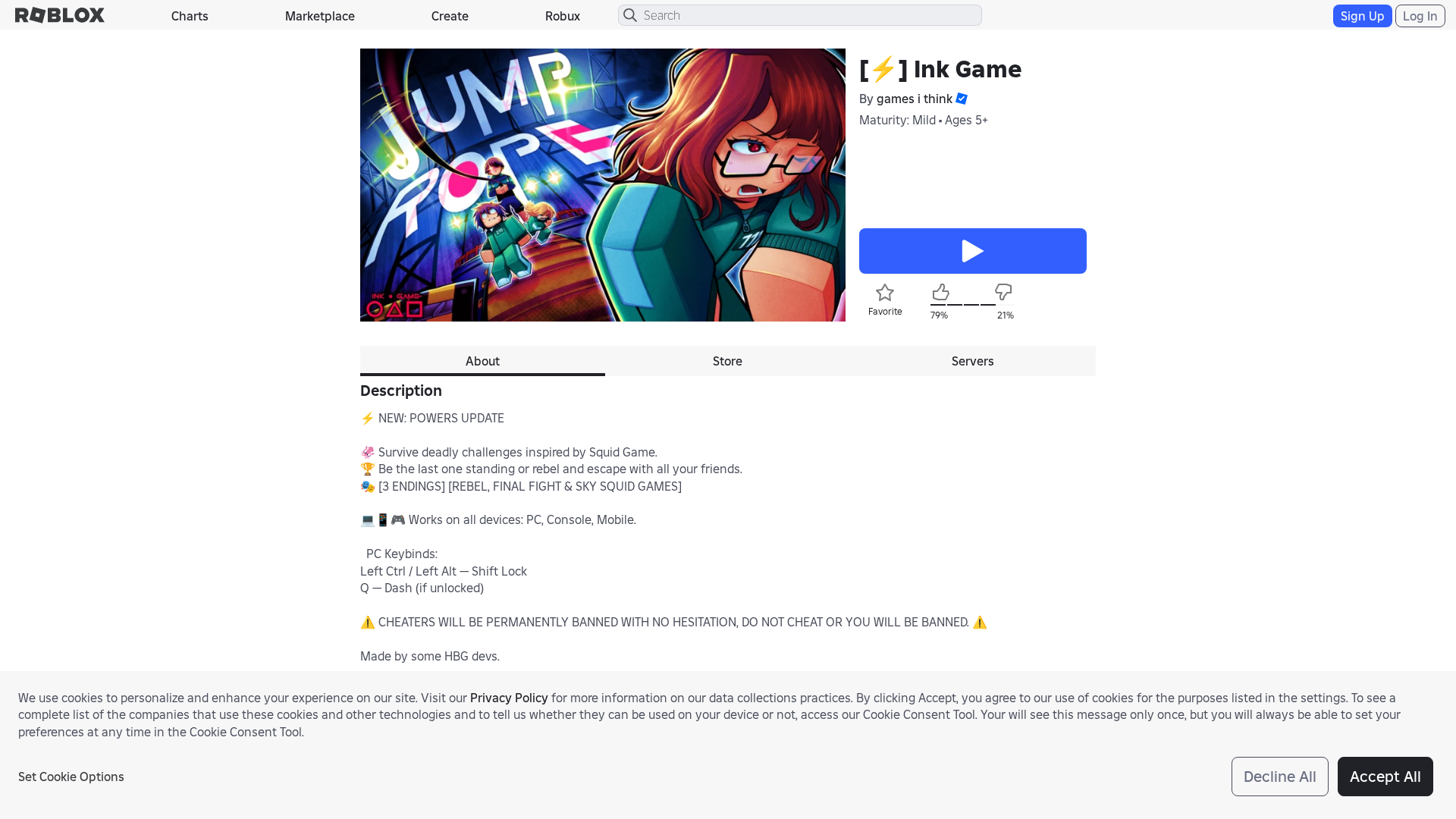
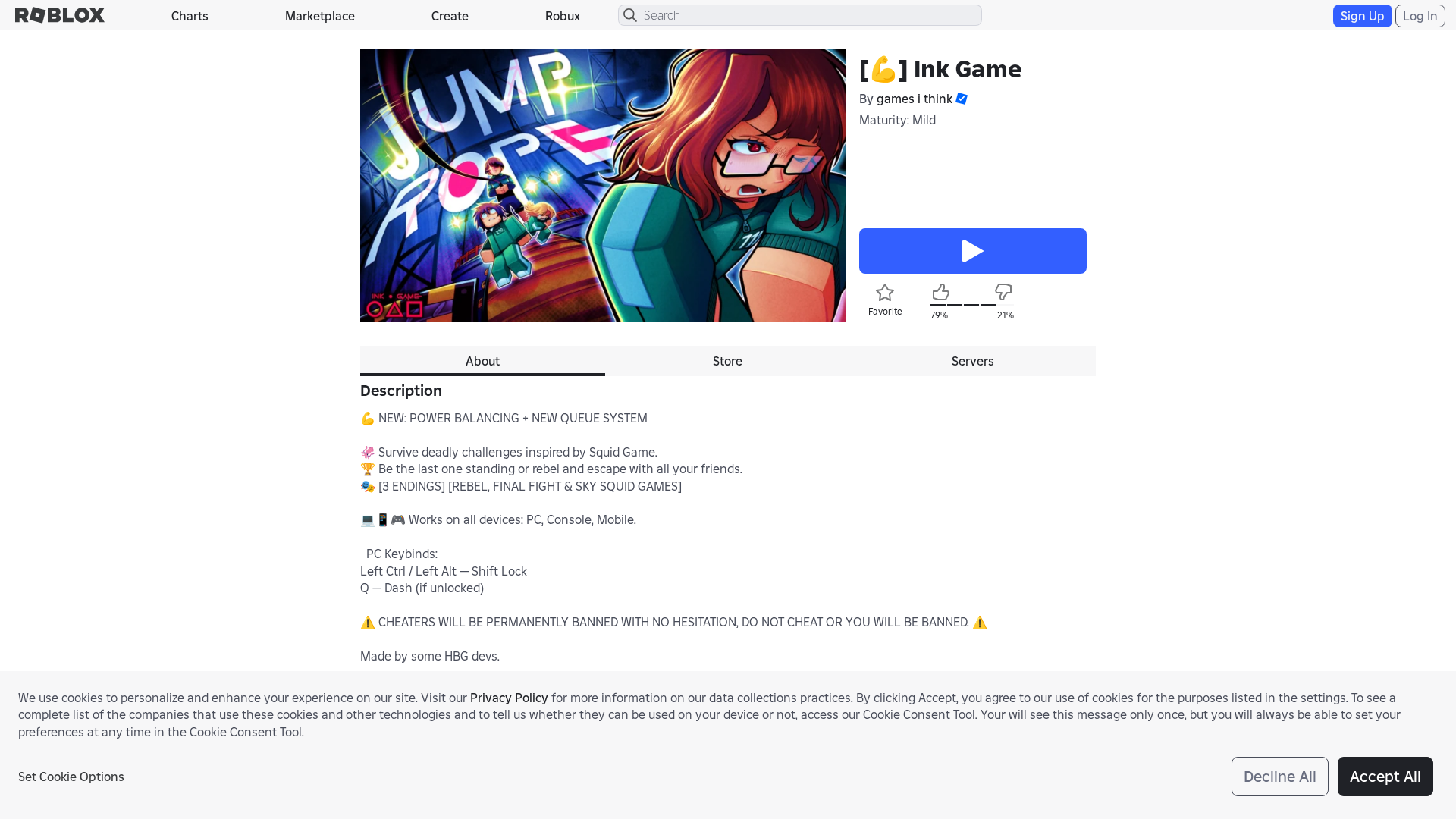
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1FF43B772A1111837617B92D9F515B716A1D3E70ECA839BE2E2F8A3760FD9C21FC1341A |
|
CONTENT
ssdeep
|
768:iGXB1/ybQ9bu5RbyFzWqrvrvE730KbvBRTsfE7O10F8AgF9NpBxJ8m8:iGXB1/yc9K5RGjMrBXTWyC0M9NTxJ8m8 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b03056cecd897d69 |
|
VISUAL
aHash
|
c7c7c3cffffffffe |
|
VISUAL
dHash
|
ae0f8e1e303c35c0 |
|
VISUAL
wHash
|
42c7c3c7cfdf0114 |
|
VISUAL
colorHash
|
072000000c1 |
|
VISUAL
cropResistant
|
ae0f8e1e303c35c0,64ec320692d2d2fa |
Code Analysis
🔬 Threat Analysis Report
• Threat: Impersonation Phishing
• Target: Roblox users
• Method: Domain spoofing and potentially malicious javascript.
• Exfil: Unknown, form actions suggest search may lead to data exfil.
• Indicators: Domain mismatch, use of obfuscation in the javascript.
• Risk: High
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- /catalog
- https://roblox.com.ly/info/blog?locale=en_us
- https://roblox.com.ly/catalog?CatalogContext=1&Keyword=
- /login?returnUrl=7296304782725682
📡 API Calls Detected
- get
- https://ro.blox.com/Ebh5?pid=experiencestart_mobileweb&is_retargeting=false&af_dp=
- https://en.help.roblox.com/hc/articles/7997207259156
- https://apis.
- GET
- POST
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 180 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker likely uses a look-alike domain to trick users into entering their Roblox credentials, which are then harvested.
Secondary Method: Malicious Javascript
Obfuscated Javascript suggests further malicious activities are attempted, which can range from additional data exfiltration (potentially through form actions), to browser takeover and crypto-mining.
🌐 Infrastructure Indicators of Compromise
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for roblox.com.ly
Found 10 other scans for this domain
-
https://roblox.com.ly/users/4640507355/profile
https://roblox.com.ly/users/2194372325/profile
https://roblox.com.ly/games/101898538399240/Jump-I...
https://roblox.com.ly/users/5291108144/profile
https://roblox.com.ly/games/85966125008822/Untitle...
https://roblox.com.ly/games/71062734985098/Untitle...
https://roblox.com.ly/users/990529183/profile
https://roblox.com.ly/users/306177933/profile
https://roblox.com.ly/communities/9381660007/
https://roblox.com.ly/communities/684258283/
