Phishing Analysis
Detailed analysis of captured phishing page
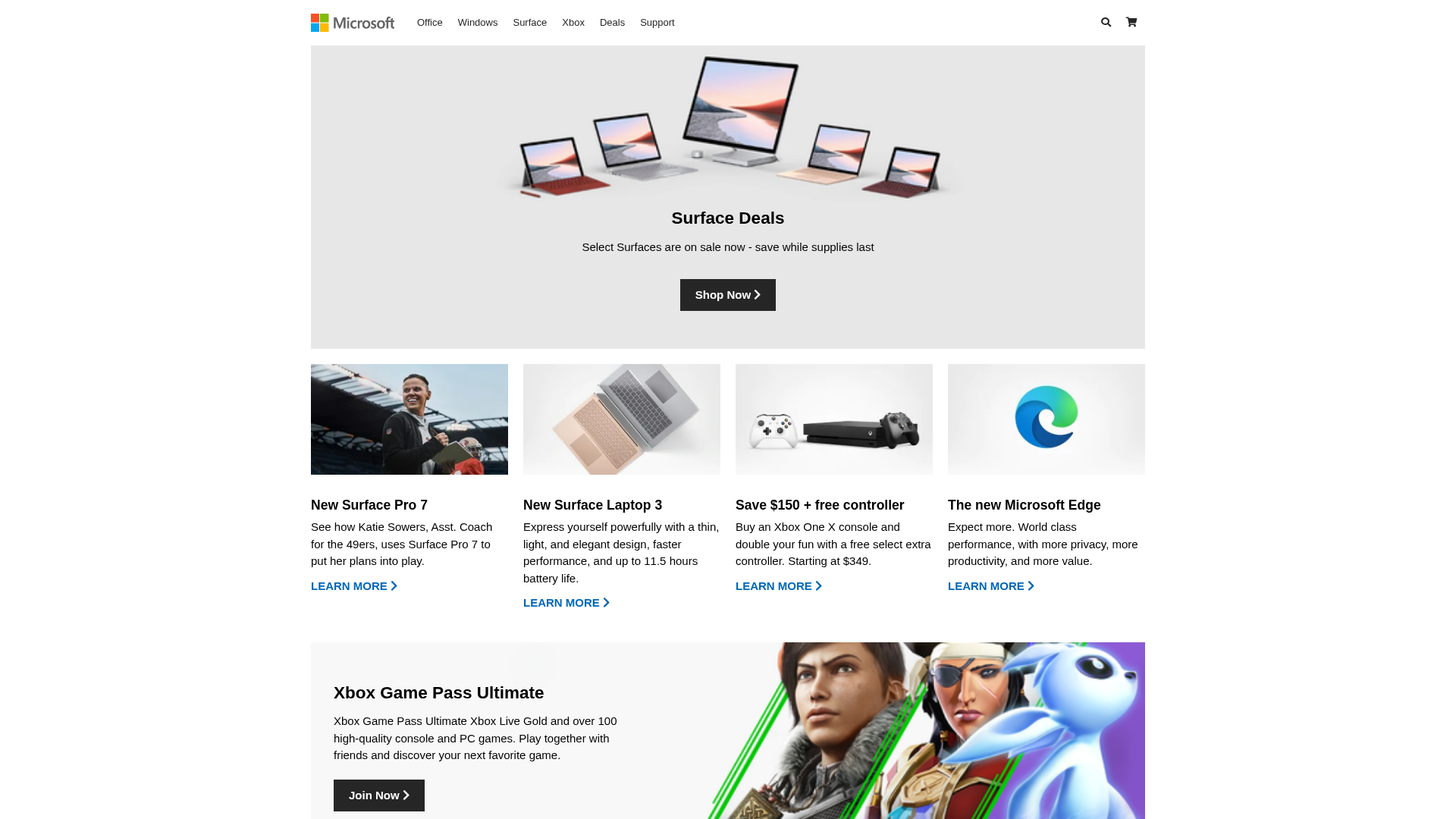
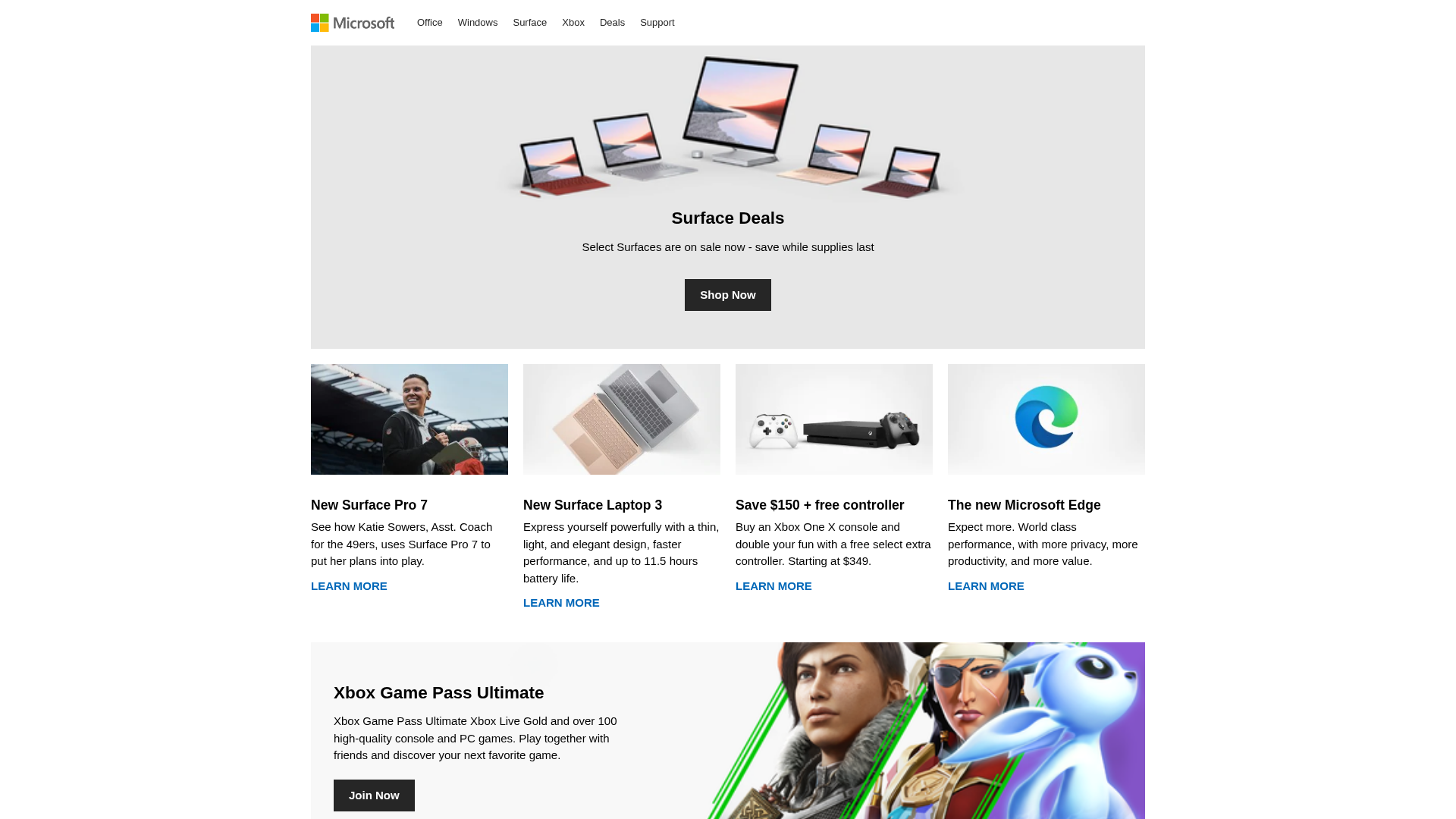
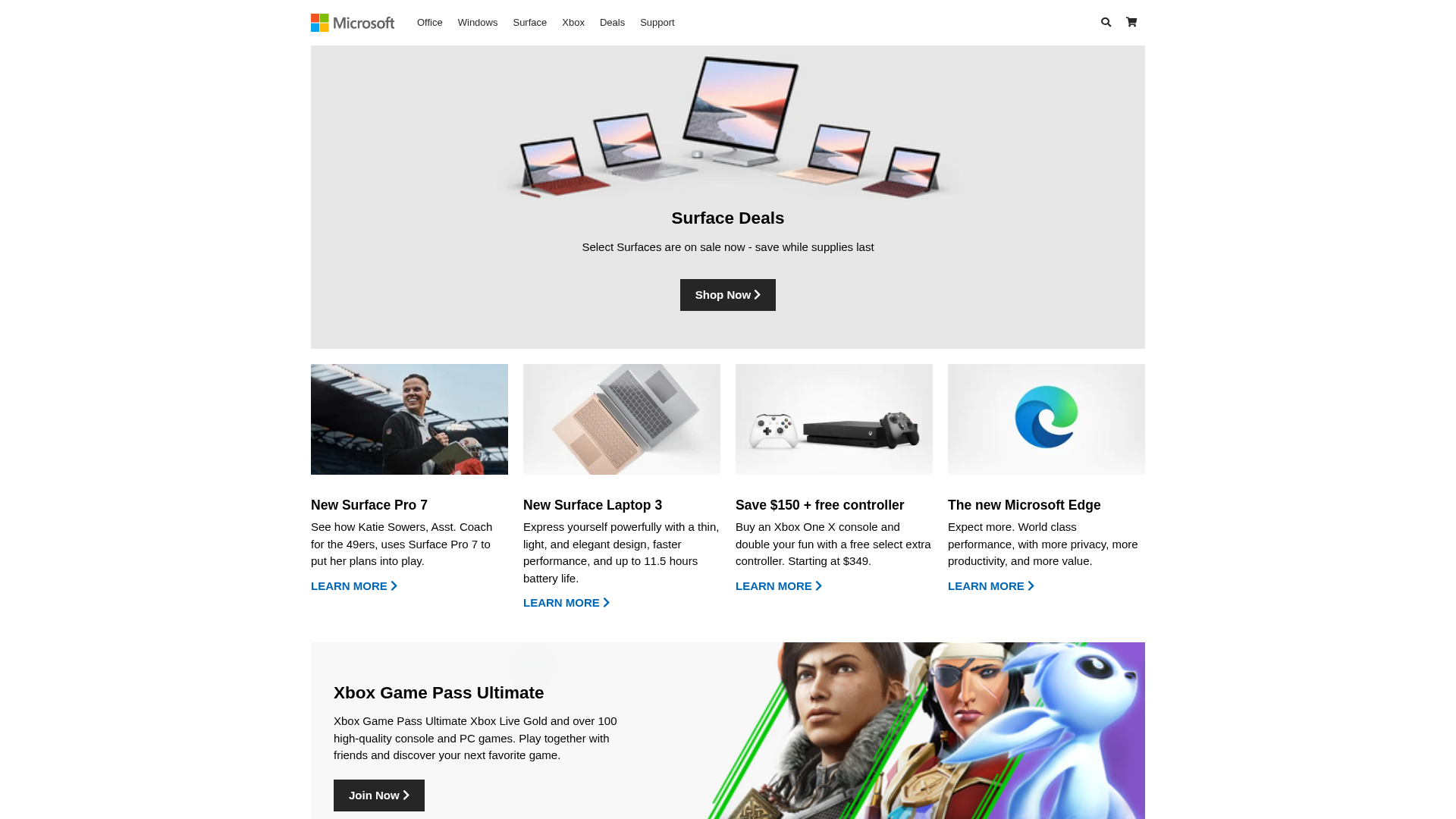
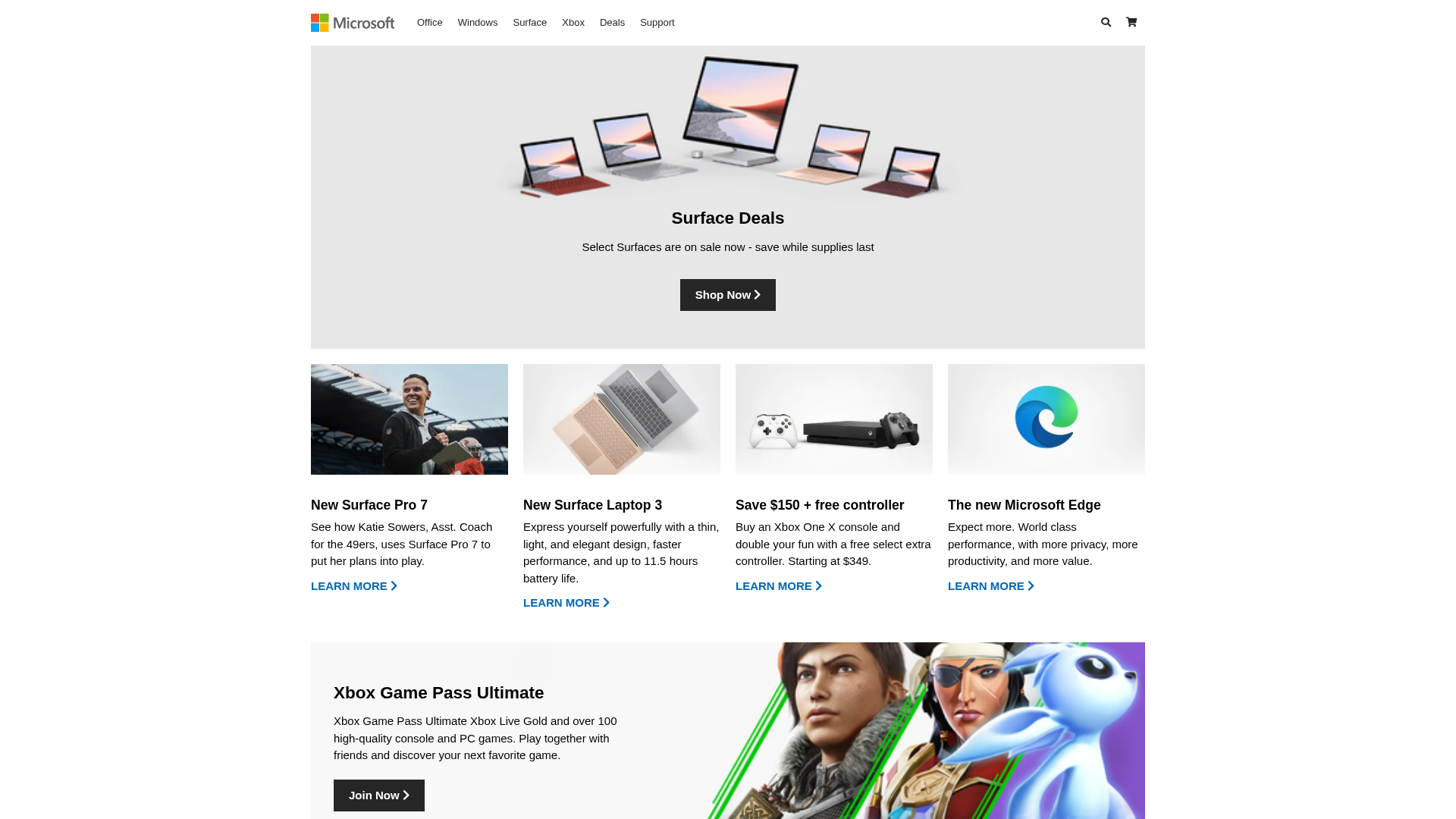
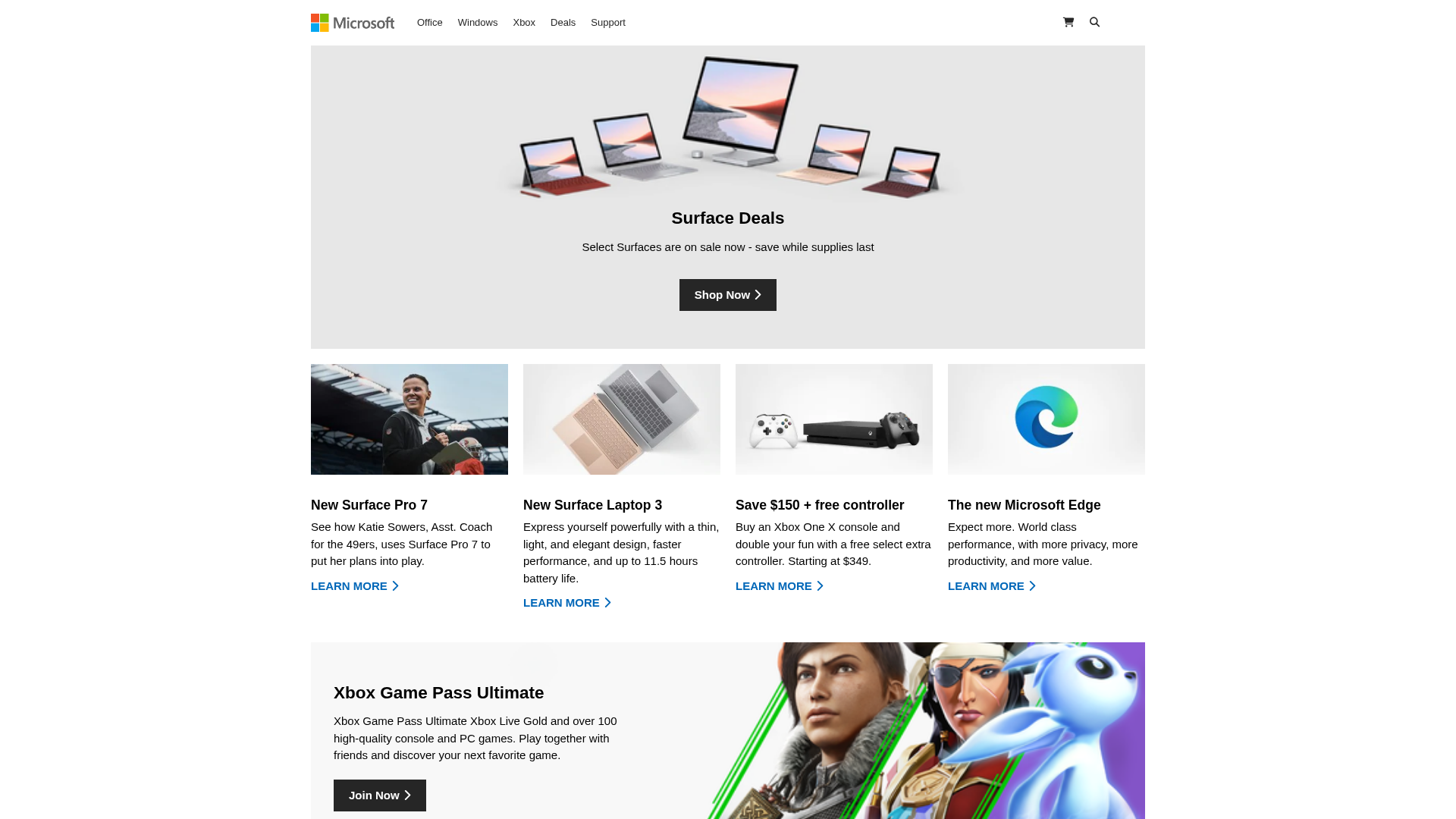
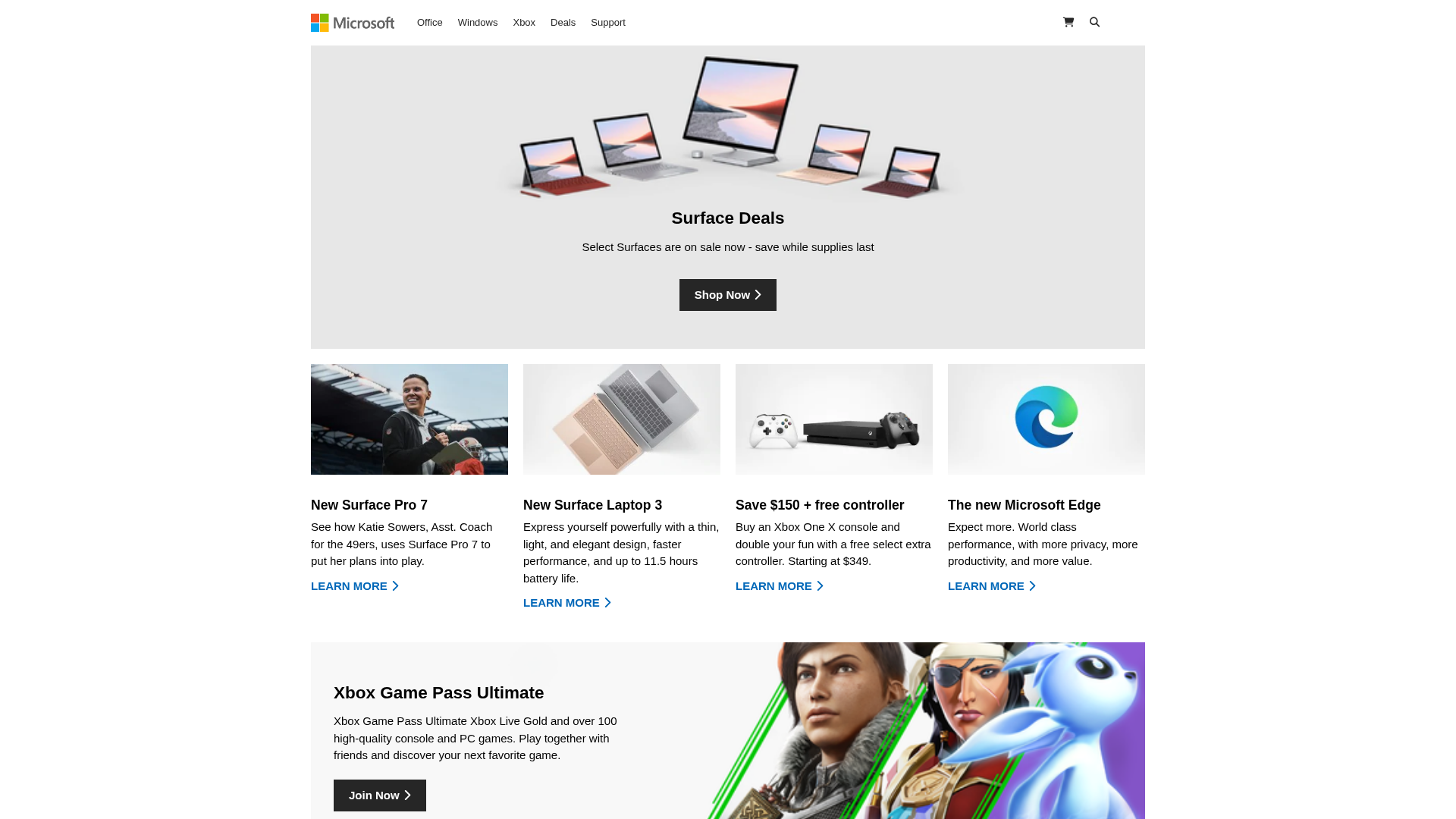
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1F1D1BF623084713B47D3739EBD14B79DE39B41A78B2A0F0165B5590FAEA3B4ACC011AF |
|
CONTENT
ssdeep
|
96:nZpEFuPyTl3ZTOwCQPfF9jinPk+M8kq4PJn9vKraLz2E1X:ZvApTy+fvqk+MxJFvz5Z |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
ec93649b3cc3c32c |
|
VISUAL
aHash
|
e7c3e38383fff3d1 |
|
VISUAL
dHash
|
2f0f0f2b370a2727 |
|
VISUAL
wHash
|
c7c3c38383e3d1d1 |
|
VISUAL
colorHash
|
07401200000 |
|
VISUAL
cropResistant
|
2f0f0f2b370a2727,cced7c7e38de3f1e,2734050c9c2d2a5c |
Code Analysis
🔬 Threat Analysis Report
• Threat: Impersonation
• Target: Microsoft users
• Method: Mimicking the official website
• Exfil: Unknown, likely credential harvesting or malware distribution.
• Indicators: Microsoft logo, free hosting, design mimicry.
• Risk: High
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Brand Impersonation
The attacker is trying to impersonate Microsoft by copying the website design and using the Microsoft logo to lure users into providing credentials or downloading malware.
Secondary Method: Credential Harvesting / Malware distribution
The goal is to steal login details or infect the victim's device with malware, likely through links to a phishing page or by malicious downloads.
🌐 Infrastructure Indicators of Compromise
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)