
Phishing Analysis
Detailed analysis of captured phishing page
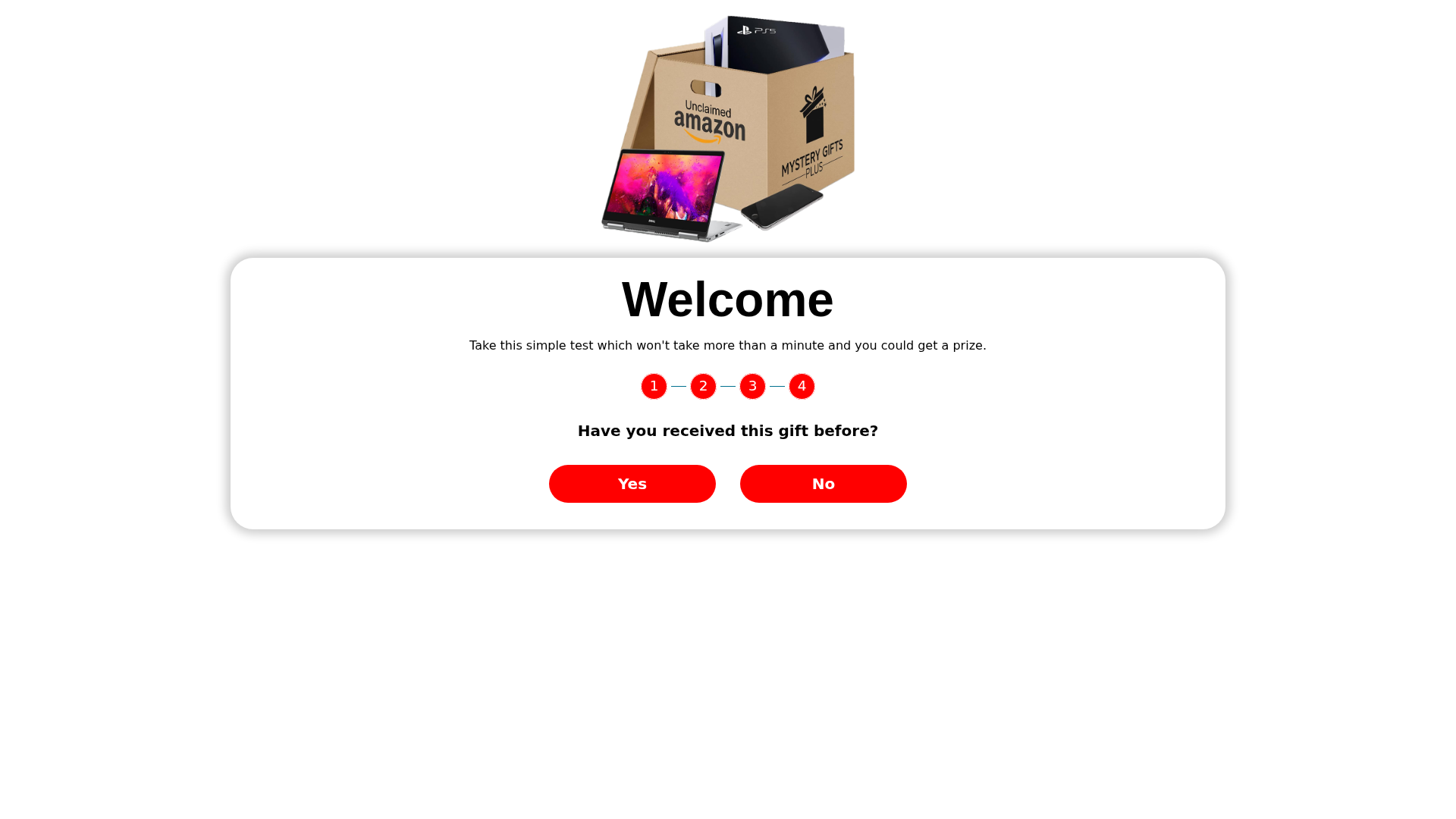
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T176618A715449D8BF82C3C2E086783B5E36C1CA86EE2B1A9886F4D30D1FEBD90ED07155 |
|
CONTENT
ssdeep
|
48:llMLEY0OW2IbSAwwy6qj4OQHj4OQgj4OQtj4OQ8pt8BjH5c7BjHY3BjHM/9MBjH3:LTaw9ycAzuozscqK0 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e666c666cccc9833 |
|
VISUAL
aHash
|
e7e7e7e7e7e7ffff |
|
VISUAL
dHash
|
2d4d0f0d4d0d0008 |
|
VISUAL
wHash
|
27278080a581ffff |
|
VISUAL
colorHash
|
07400018000 |
|
VISUAL
cropResistant
|
2d4d0f0d4d0d0008 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Amazon customers
• Method: Gift/Prize scam
• Exfil: Potentially personal information (answers to questions)
• Indicators: Unrelated domain, gift claims, survey, obfuscation.
• Risk: High
🔒 Obfuscation Detected
- unescape
📡 API Calls Detected
- POST
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- 2 obfuscation techniques
🏢 Brand Impersonation Analysis
Fraudulent Claims
⚔️ Attack Methodology
Primary Method: Brand Impersonation
The attacker creates a website that mimics the appearance of a legitimate brand, in this case Amazon, to deceive users into providing sensitive information. The use of a prize claim is a common tactic.
Secondary Method: Social Engineering
The website employs social engineering techniques such as offering incentives (gifts) and creating a sense of urgency to trick users.
🌐 Infrastructure Indicators of Compromise
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for im.nbpublic.com
Found 10 other scans for this domain
-
https://im.nbpublic.com/loading_page/paypal/paypal...
http://im.nbpublic.com/loading_page/snack_box/snac...
https://||im.nbpublic.com/loading_page_cpl/amazon/...
https://||im.nbpublic.com/loading_page/amazon/amaz...
http://im.nbpublic.com/loading_page/amazon/AmazonG...
https://im.nbpublic.com/loading_page/paypal/paypal...
https://im.nbpublic.com/loading_page/amazon/Amazon...
https://im.nbpublic.com/loading_page/snack_box/sna...
http://im.nbpublic.com/loading_page/snack_box/snac...
http://im.nbpublic.com/loading_page/snack_box/snac...
