
Phishing Analysis
Detailed analysis of captured phishing page
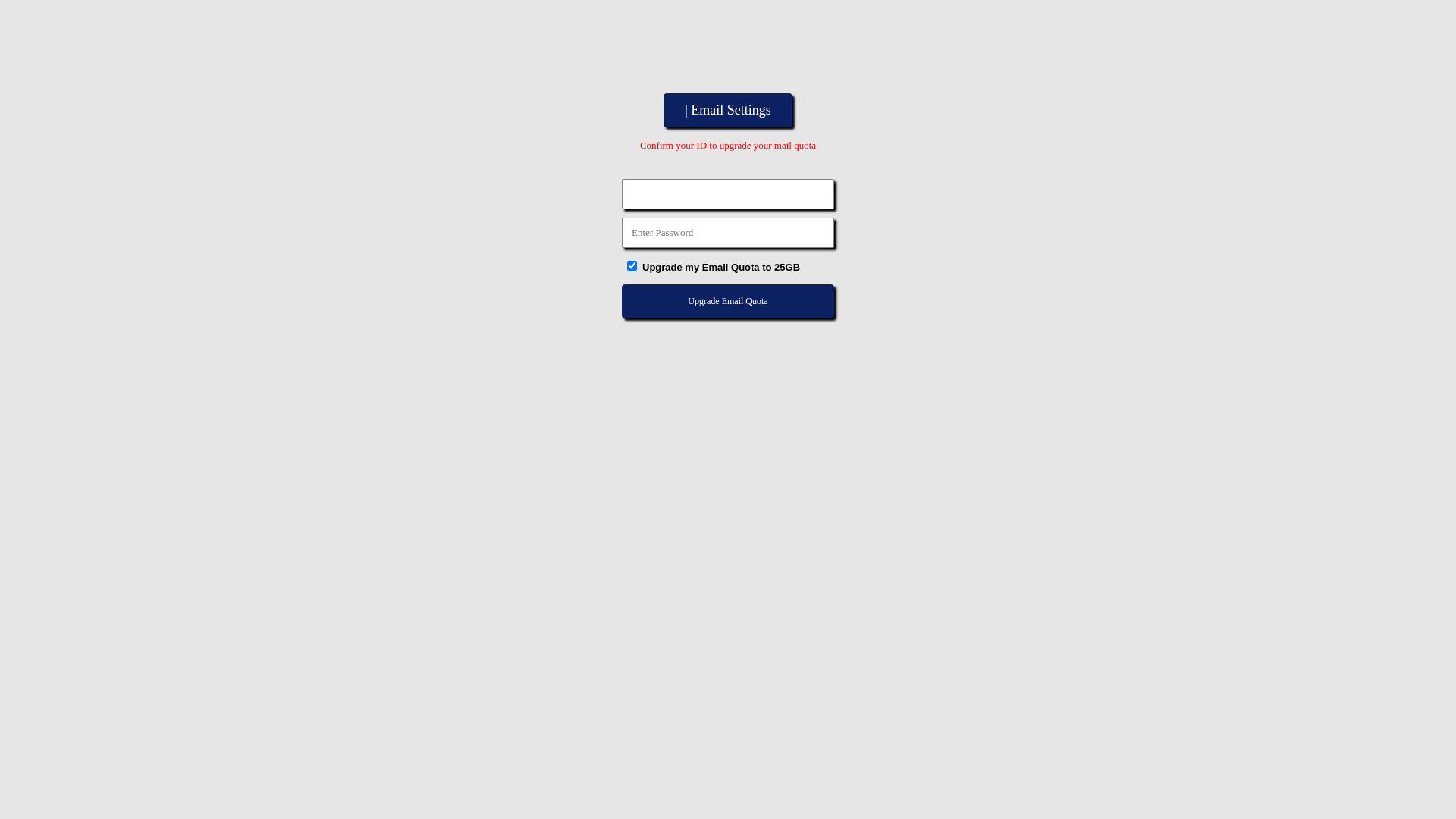
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T14C51C0B07A94022DB4D18445A210BFCB62F28321527111245CE7FD6FDADB5F4D9EA2FE |
|
CONTENT
ssdeep
|
48:EQJR9lRp4lRslRgMAckgmZatoGnuLlR2rJ9xZAcUuC4ACblFJ9xZAc5ylC9wE4RE:d9H2HsHzhoAuLHkJ9xnRC413J9xnkQ9j |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e6668c9999333399 |
|
VISUAL
aHash
|
e7e7e7e7ffffffff |
|
VISUAL
dHash
|
0c0c4d4c30080000 |
|
VISUAL
wHash
|
c3c3c3c30f0f0f0f |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
0c0c4d4c30080000 |
Code Analysis
🔐 Credential Harvesting Forms
📤 Form Action Targets
- none.php
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for www.buyukeczane.org
Found 2 other scans for this domain
