
Phishing Analysis
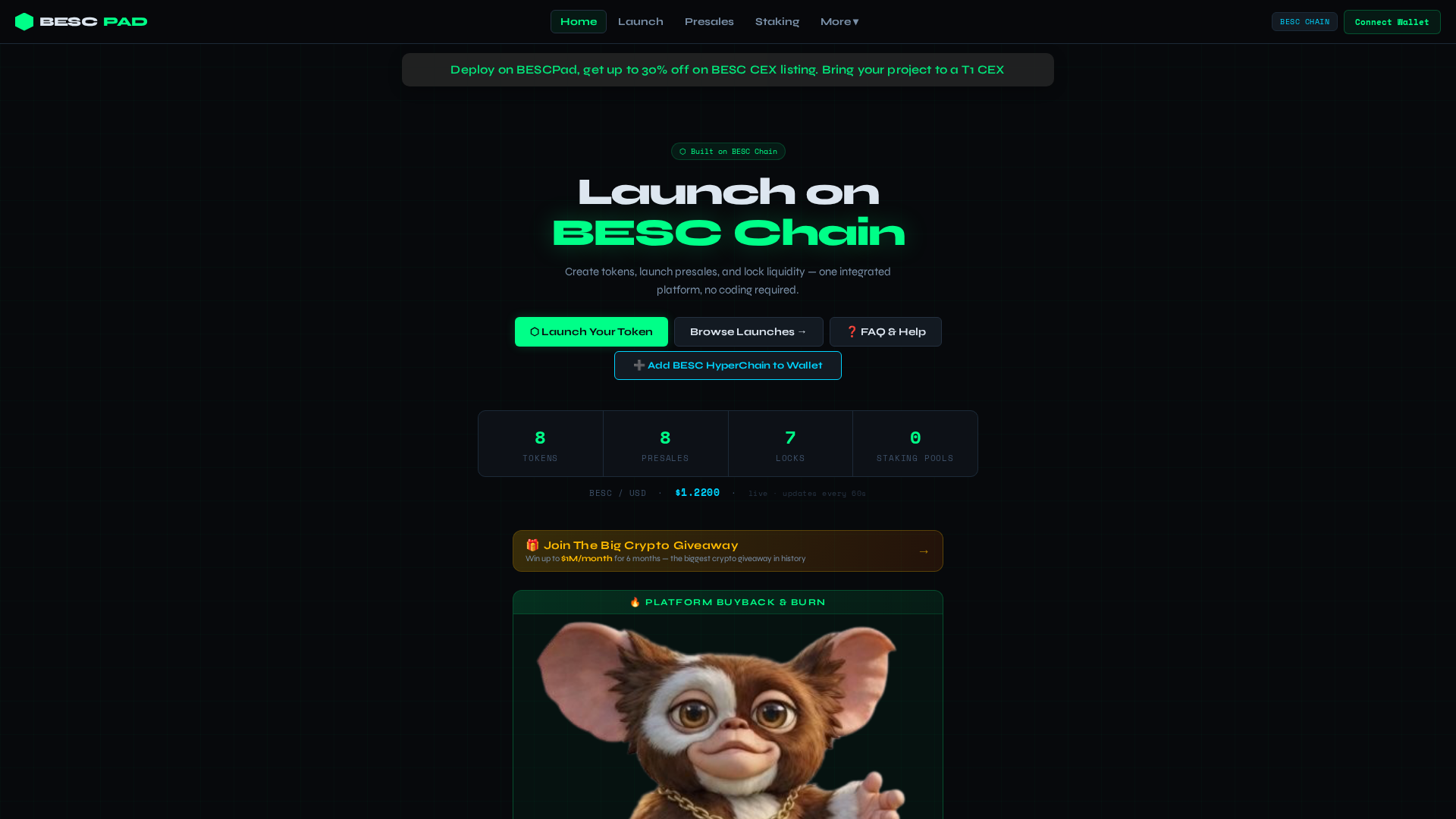
Detailed analysis of captured phishing page
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T156549370E254EE32A2A7C099A5A4CB6F3180D706C74B075497B8876EB9CBDF1DF211D8 |
|
CONTENT
ssdeep
|
6144:SPrH4VKWy3K855gVOpDQUVzaJdYnPjytG1UJClbwT:QUV43lDQUVzaJdYnPjytG1UJClbwT |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cc66996633ce3398 |
|
VISUAL
aHash
|
1018183800181818 |
|
VISUAL
dHash
|
69b2b2207020b2b2 |
|
VISUAL
wHash
|
bd18183c3c3e3c3e |
|
VISUAL
colorHash
|
38600008200 |
|
VISUAL
cropResistant
|
69b2b2207020b2b2 |
Code Analysis
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- base64_strings
🎯 Kit Endpoints
- ${_safeLogoUrl}
📡 API Calls Detected
- stats
- contenthash(bytes32)
- addr(bytes32)
- addr(bytes32,uint)
- https://explorer.beschyperchain.com/api?module=token&action=getTokenHolders&contractaddress=
- services.php
- contract
- proxy
- promo.php
- POST
- navlinks.php
- text(bytes32,string)
- ${CHAIN.explorer}/token/
- account
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 39 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 39 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Scan History for bescpad.xyz
Found 2 other scans for this domain
