
Phishing Analysis
Detailed analysis of captured phishing page
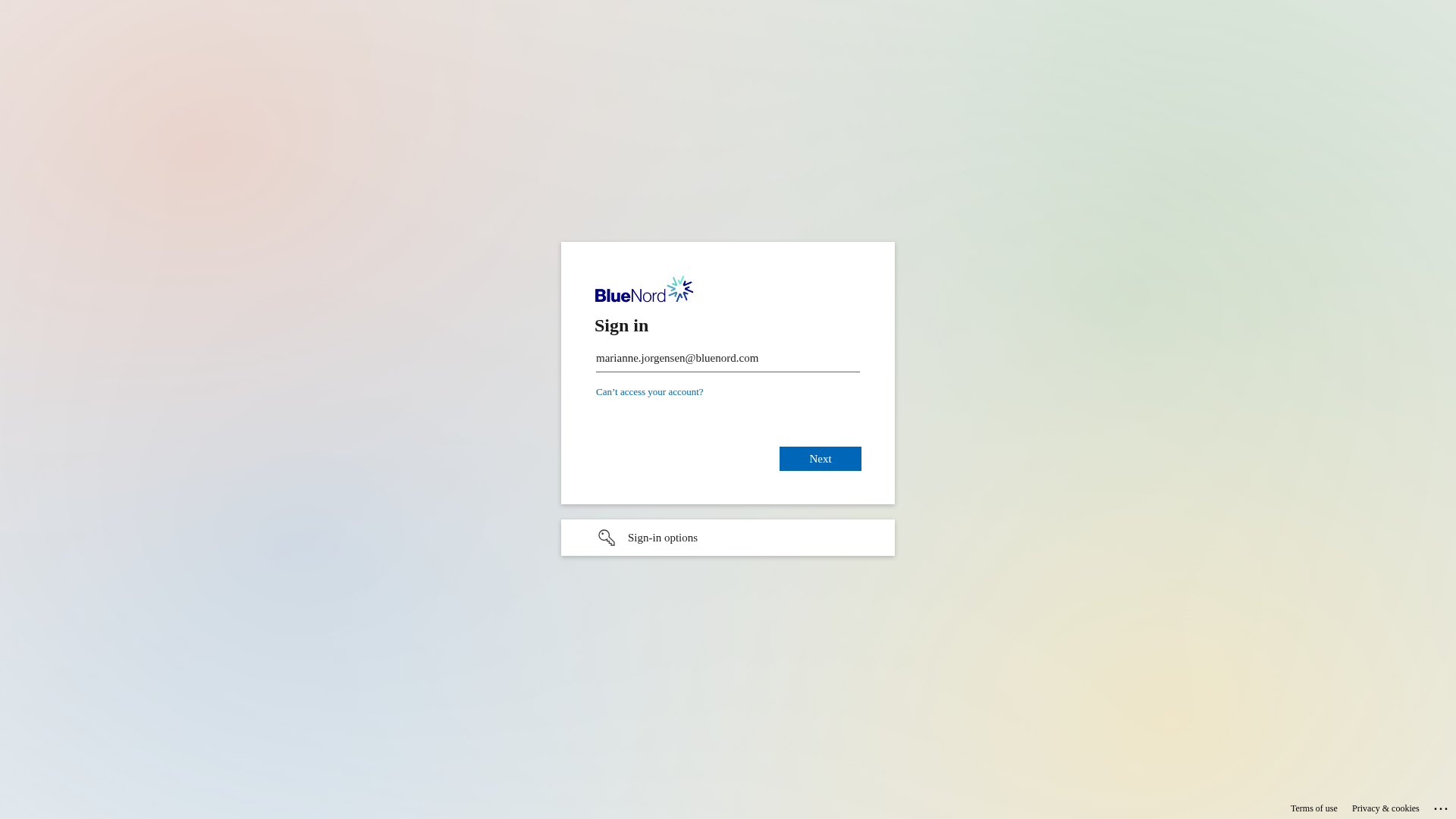
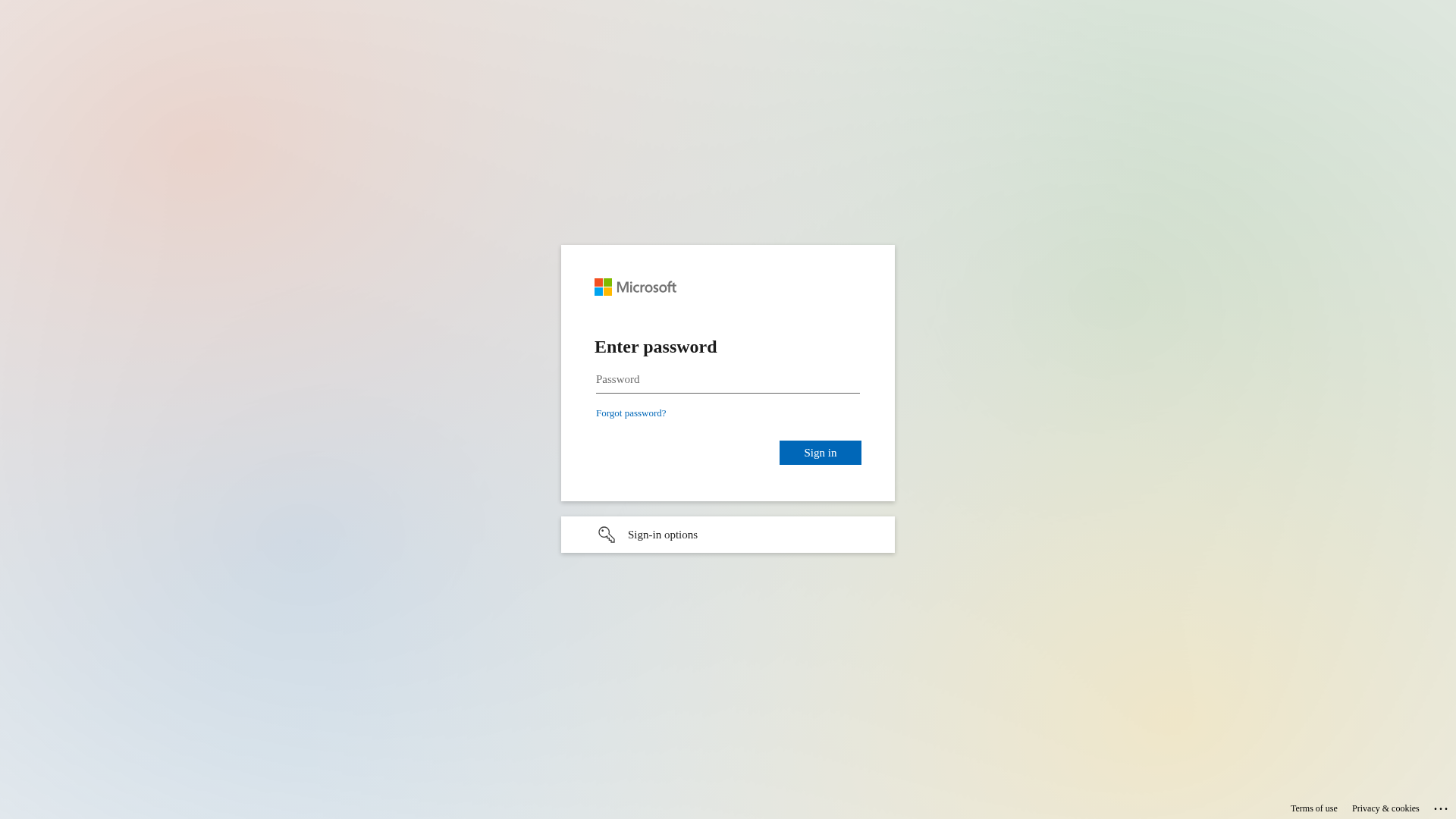
Visual Capture
Detection Info
https://security.email-microsoft.com/DiYC_SMAvt1aV3ltaQ
Detected Brand
Microsoft
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
592a6a0a-c17…
Analyzed
2026-03-30 20:14
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1C3D101705050AD3B4293D7D8B3B56B8F3394C346EA87565A63F8C74C1EE3E66CC1A222 |
|
CONTENT
ssdeep
|
96:DIpkCGTHRPykDkrwkMyQJs39TbJG9KjsWsjOI60U2gs0sjOIzOVJQ6Q6ynQjNsjg:ZPk80B9TbJG9aJ6OVJQyyQjH |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9c497326cc99d9e4 |
|
VISUAL
aHash
|
18001818191f0f9f |
|
VISUAL
dHash
|
7161713331727d38 |
|
VISUAL
wHash
|
191818181f1f1fff |
|
VISUAL
colorHash
|
07000000180 |
|
VISUAL
cropResistant
|
7161713331727d38 |
Code Analysis
Risk Score
70/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Personal Info
🎯 Kit Endpoints
- https://login.microsoftonline.com/common/oauth2/authorize?client_id=00000001-0000-cff1-ce00-468375055177&response_mode=form_post&response_type=code+id_token&scope=openid&msafed=1&msaredir=1&client-request-id=d98292e6-fa3f-ce32-7897-21bc5137cc6d&protectedtoken=true&domain_hint=bluenord.com&nonce=394876372407.ec82d3ed-b372-7cd6-3e42-fcfc13352e79&state=bWFyaWFubmUuam9yZ2Vuc2VuQGJsdWVub3JkLmNvbQ#
- https://login.microsoftonline.com/common/login#
- https://passwordreset.microsoftonline.com/?ru=https://login.microsoftonline.com/common/oauth2/authorize?client_id=00000001-0000-cff1-ce00-871410085982&response_mode=form_post&response_type=code+id_token&scope=openid&msafed=1&msaredir=1&client-request-id=d98292e6-fa3f-ce32-5147-21bc5137cc6d&protectedtoken=true&domain_hint=bluenord.com&nonce=333762339690.ec82d3ed-b372-7cd6-3e42-fcfc13352e79&state=bWFyaWFubmUuam9yZ2Vuc2VuQGJsdWVub3JkLmNvbQ#
- https://login.microsoftonline.com/common/oauth2/authorize?client_id=00000001-0000-cff1-ce00-698395420493&response_mode=form_post&response_type=code+id_token&scope=openid&msafed=1&msaredir=1&client-request-id=d98292e6-fa3f-ce32-1446-21bc5137cc6d&protectedtoken=true&domain_hint=bluenord.com&nonce=966250119726.ec82d3ed-b372-7cd6-3e42-fcfc13352e79&state=bWFyaWFubmUuam9yZ2Vuc2VuQGJsdWVub3JkLmNvbQ#
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Personal Info
🔬 Comprehensive Threat Analysis
Threat Type
Two-Factor Authentication Stealer
Target
Microsoft users
Attack Method
Phishing webpage
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Personal Info
🏢 Brand Impersonation Analysis
Impersonated Brand
Microsoft
Official Website
https://www.microsoft.com
Fake Service
Account verification service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: Two-Factor Authentication Bypass
Victim is prompted for 2FA code after entering credentials. The code is intercepted and used by attacker to access victim's account in real-time.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
security.email-microsoft.com
Registered
2019-03-08 11:38:07+00:00
Registrar
Gandi SAS
Status
Active (older domain)
Hosting Information
Provider
Gandi SAS
ASN
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
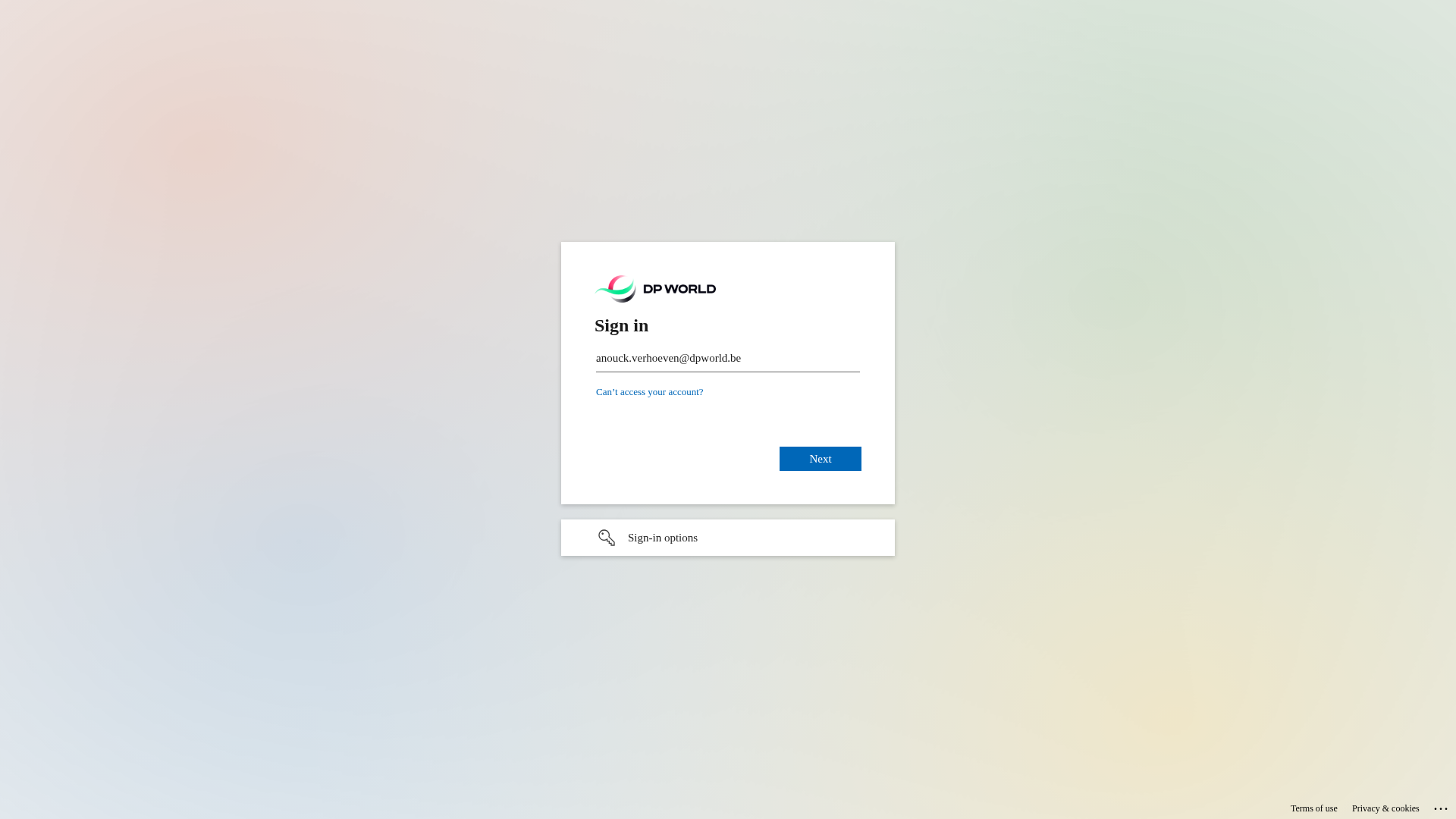
DP World
https://signin.broker/yEXpO8mh47e1zQ
Apr 01, 2026
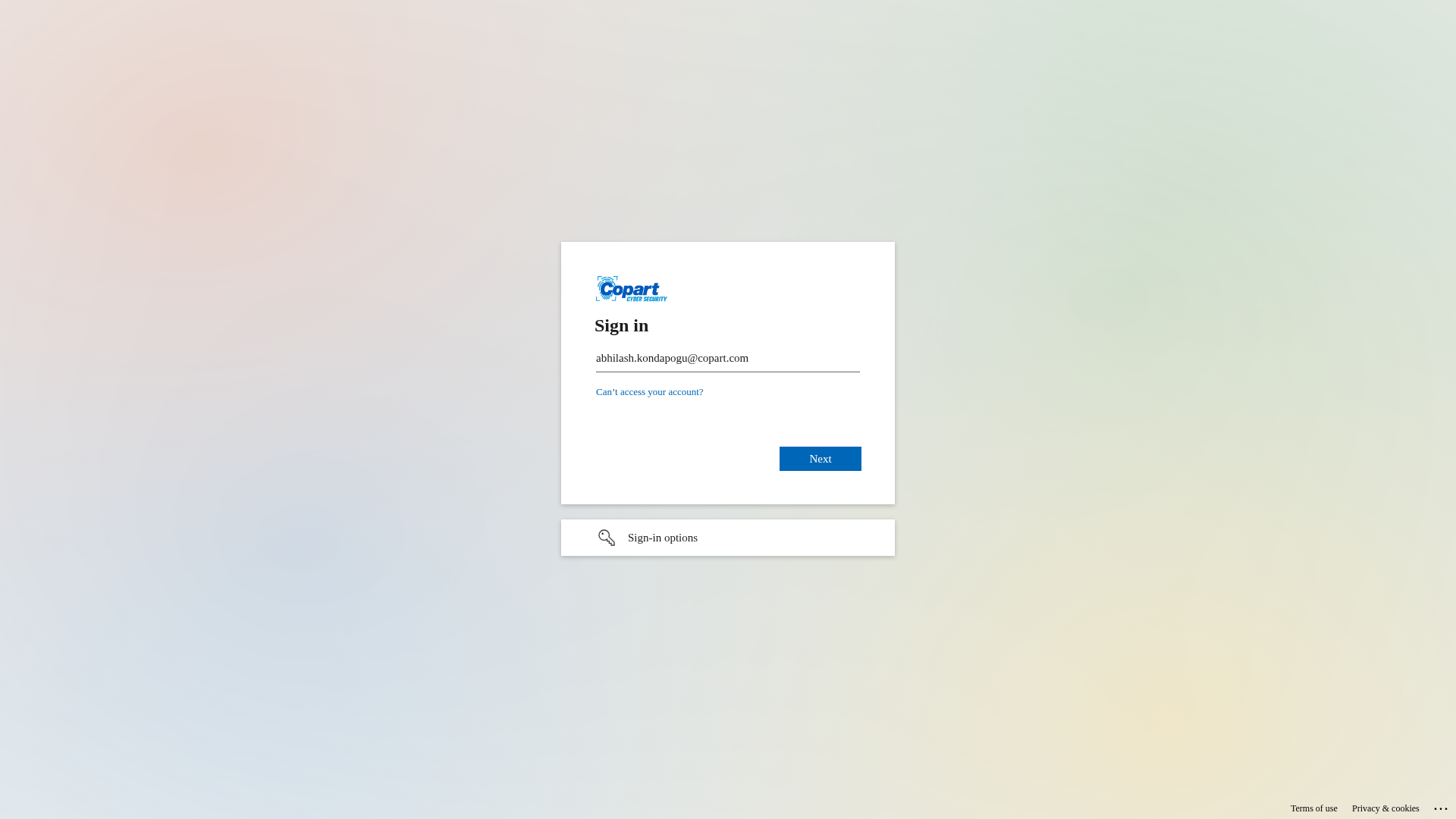
Copart
https://sso-security.com/hmoR7AjmD5_J9_rblw
Mar 31, 2026
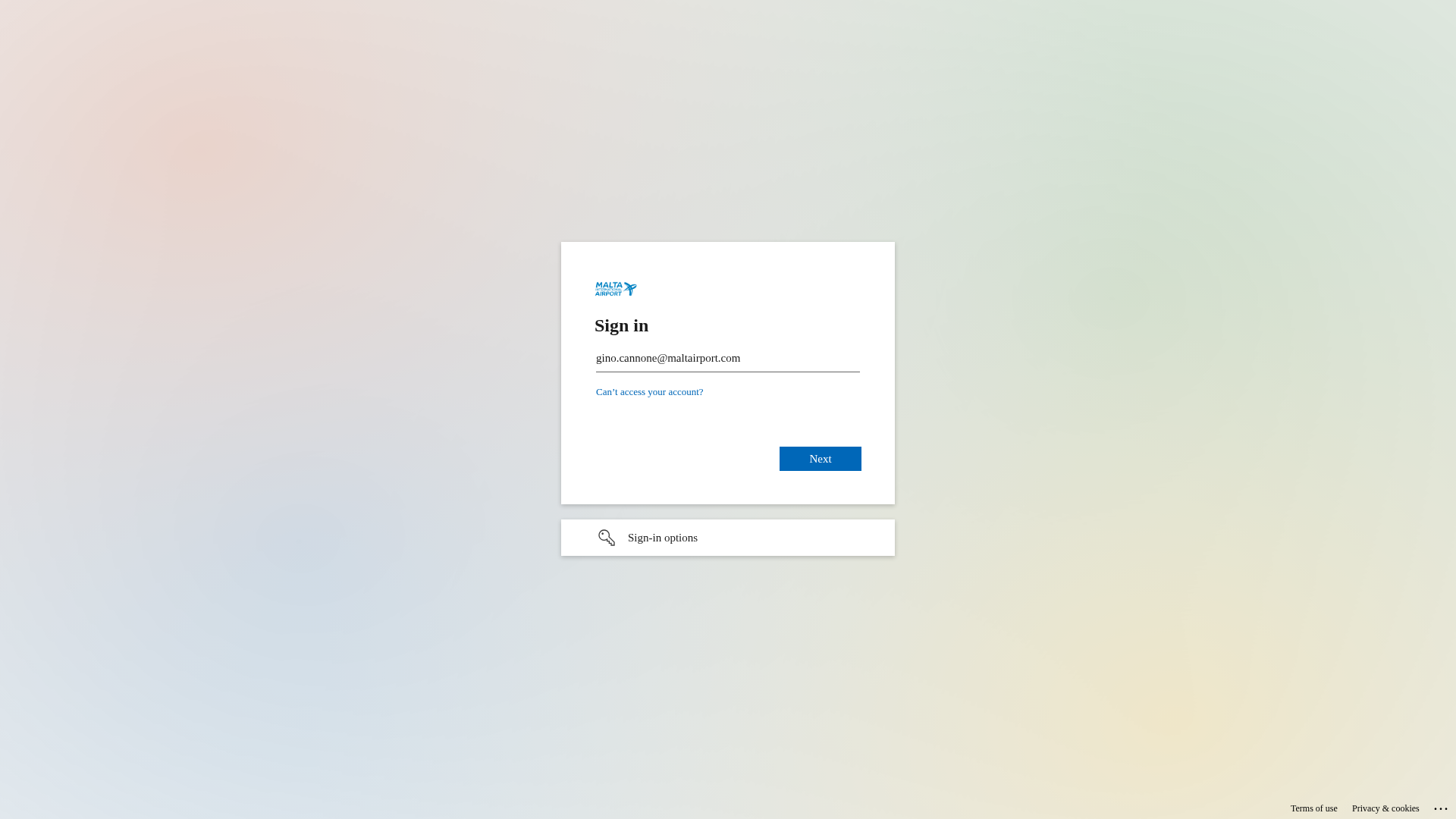
Malta International Airport
https://sso-security.com/Z6nTr6YHvIOQYEcQ
Mar 31, 2026
Microsoft
https://l0gln-m1croqsoqftcom-1drvverfil3es.fwh.is/?i=1
Mar 31, 2026
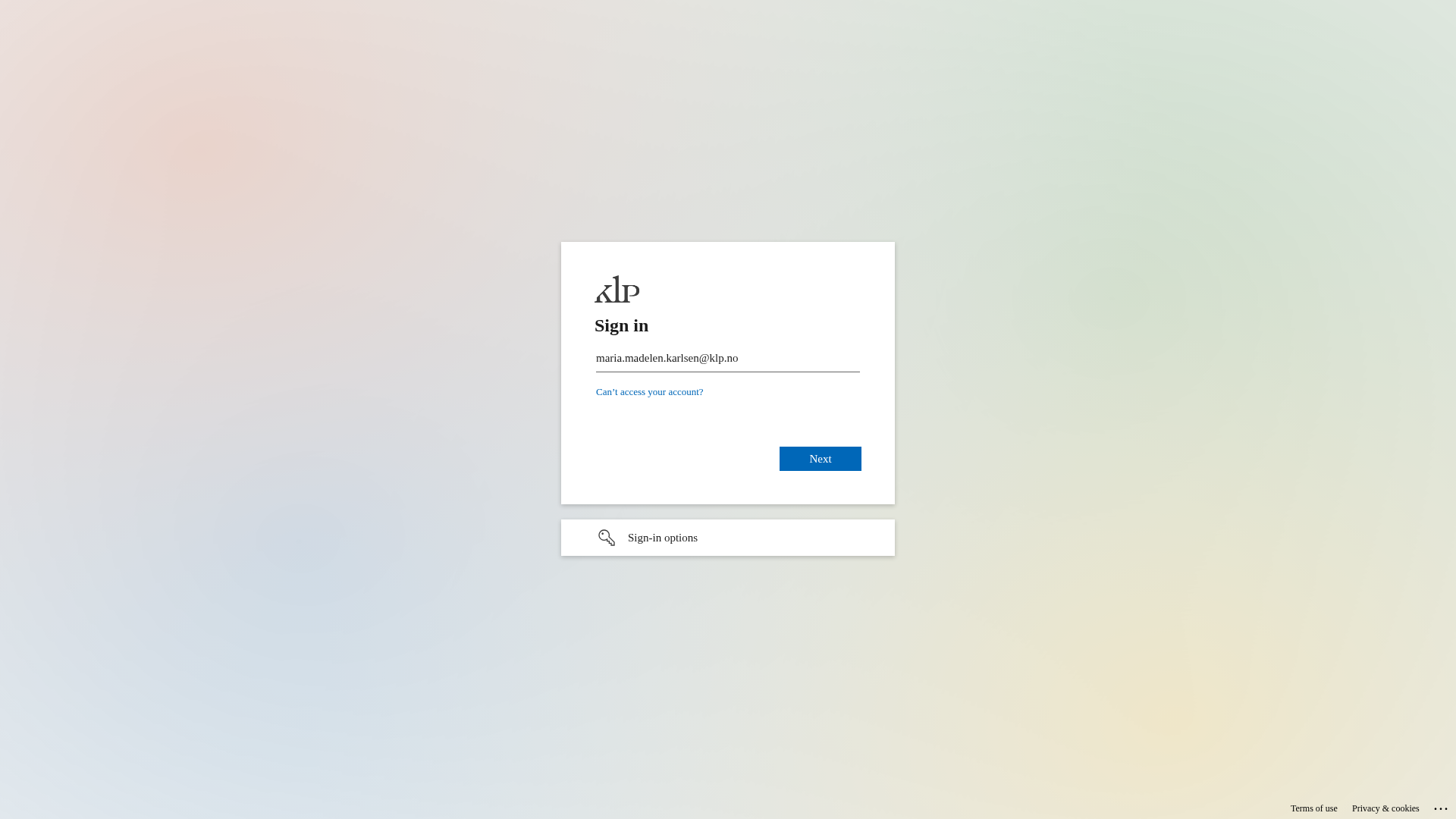
KLP
https://authentication.ms/Q0geWwh1if8
Mar 30, 2026

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.