Phishing Analysis
Detailed analysis of captured phishing page
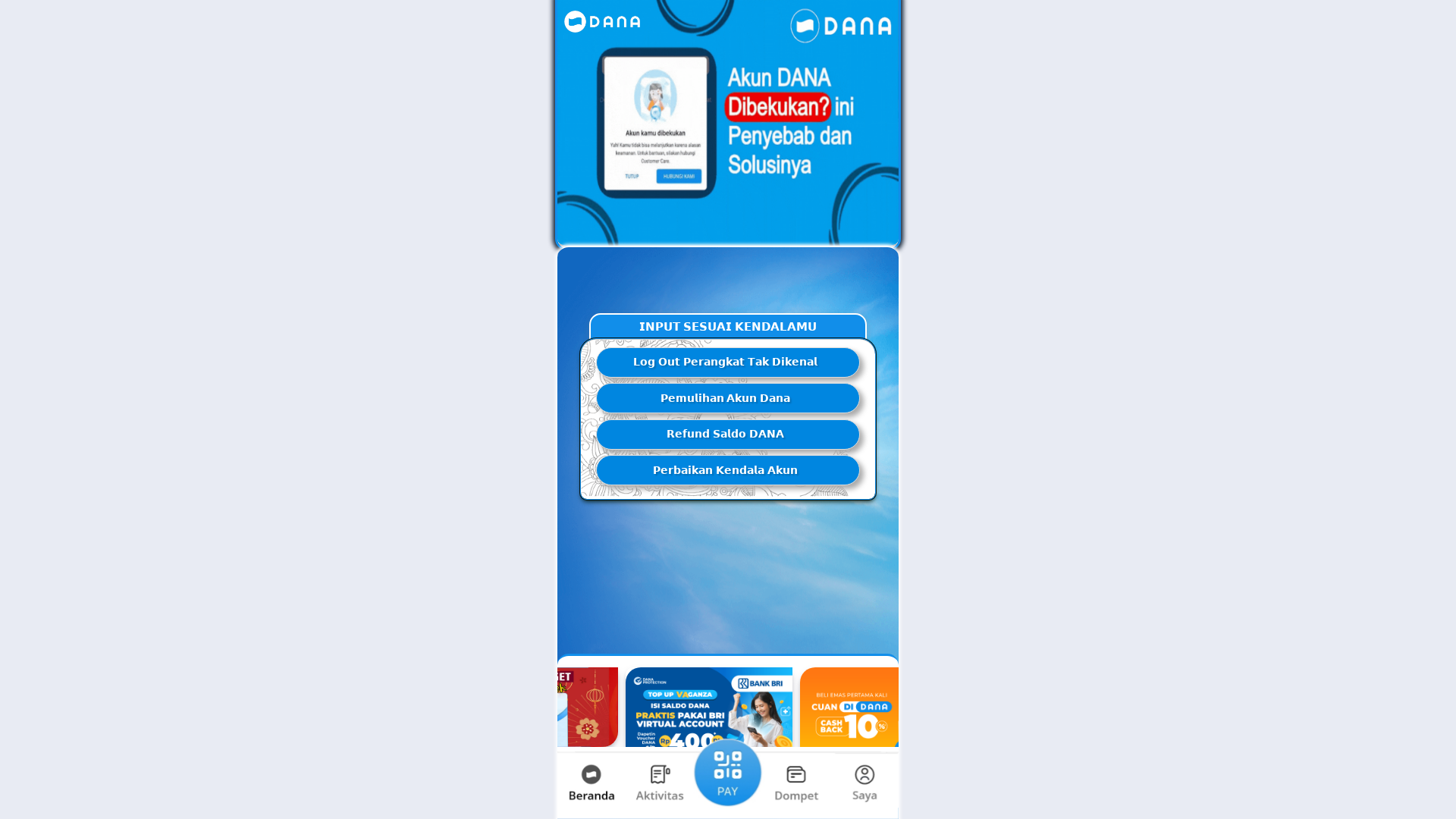
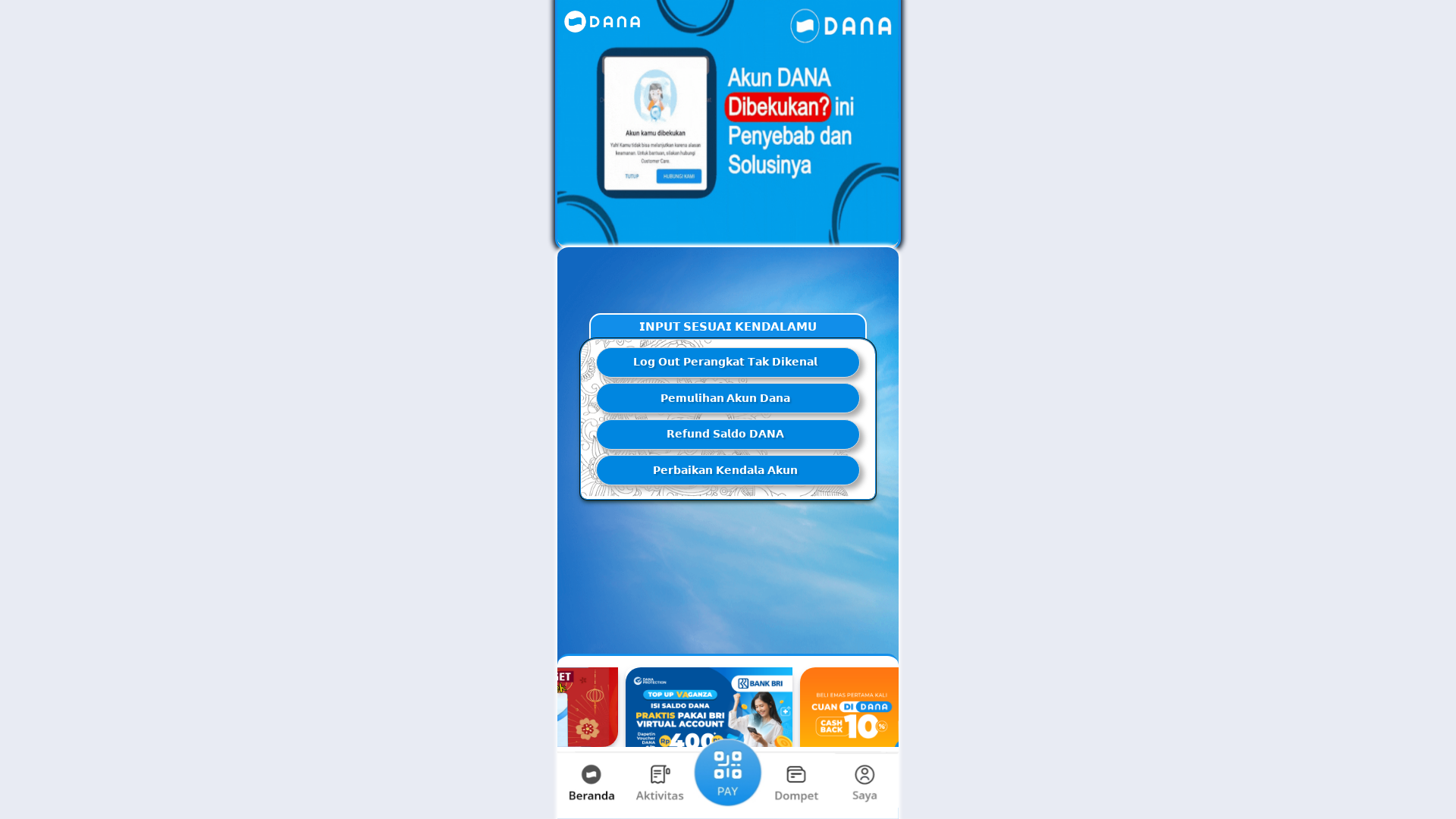
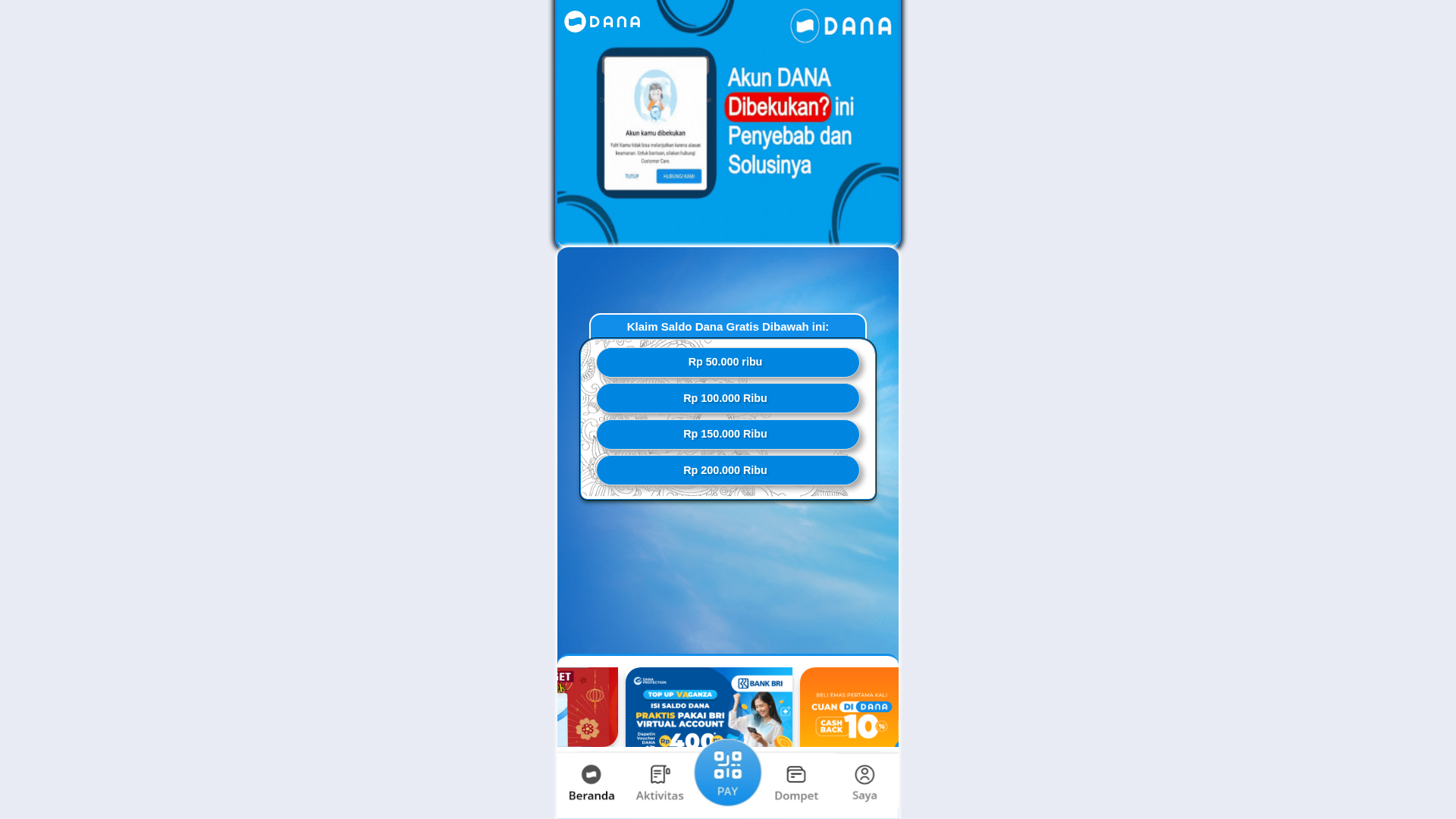
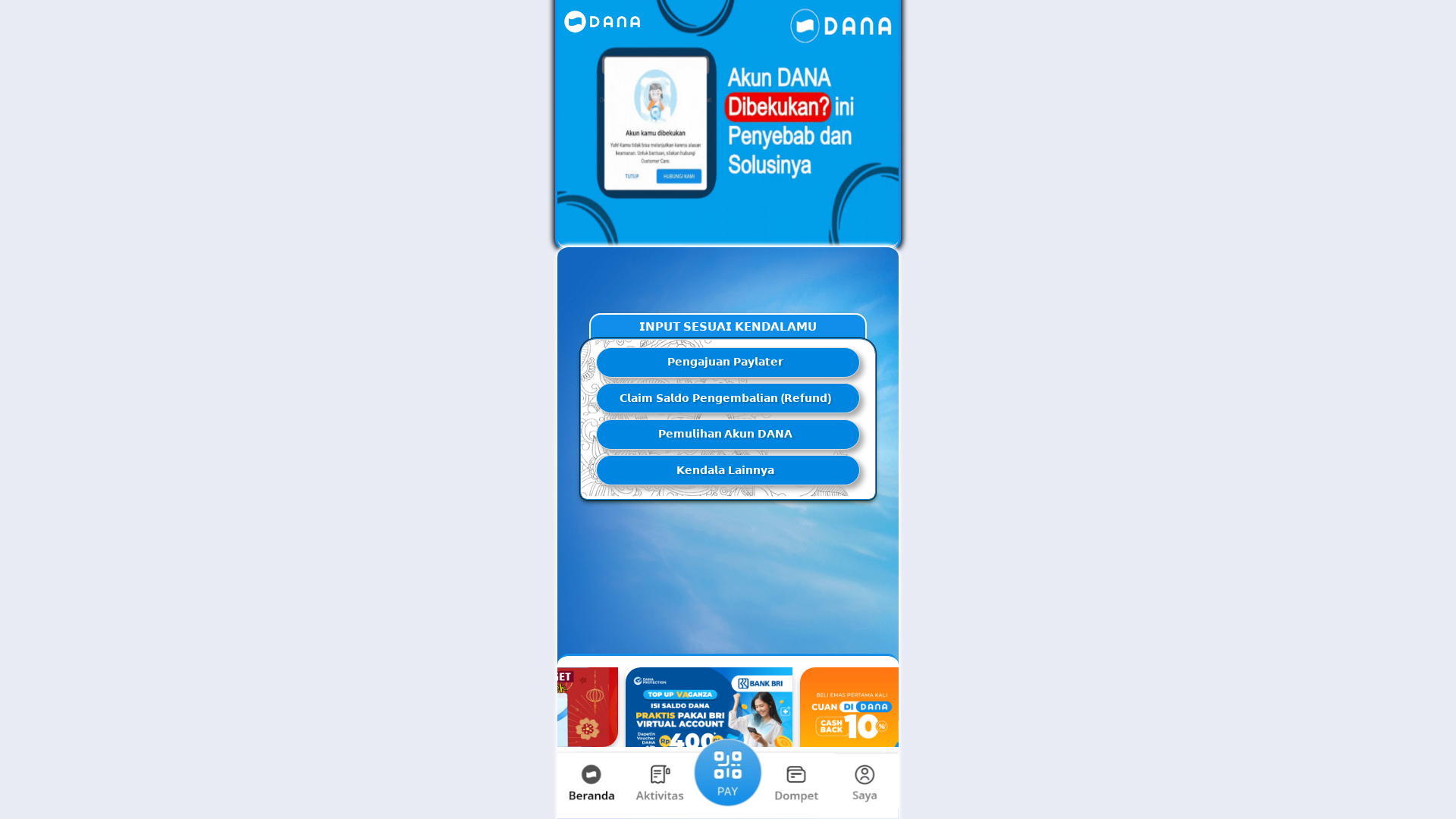
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1386297F16148141F2326D5C5EAA6BFCD6266C50ACB0E057BF6B4249FB68ECF8C4B2350 |
|
CONTENT
ssdeep
|
384:QIKSiSpp1MGgR7It8bg2TKXkDPTWlUNk9Gs90s90s90zdti:QIKjwpuGg5zbg2T4kDPTypAs6s6s6zds |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b366cc328e339933 |
|
VISUAL
aHash
|
e7e7e7e7e7e7e7e7 |
|
VISUAL
dHash
|
4d4d4d4d4d4d4d4c |
|
VISUAL
wHash
|
0707070707072727 |
|
VISUAL
colorHash
|
060020001c0 |
|
VISUAL
cropResistant
|
4d4d4d4d4d4d4d4c,aa8e8e8e969aa6a6,96d237b2d201a2d0,1ecccac8c97dfcf8,ffffffffffffffff |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: DANA users
• Method: Impersonation and account recovery scams
• Exfil: Unknown, but likely credential theft and financial information.
• Indicators: Domain mismatch, use of obfuscation and multiple forms
• Risk: High
🔒 Obfuscation Detected
- fromCharCode
- unescape
📡 API Calls Detected
- POST
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
- 4 obfuscation techniques
🏢 Brand Impersonation Analysis
Fraudulent Claims
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The site is designed to trick users into entering their DANA account credentials. The attacker will then steal the credentials for malicious purposes. The site is a clone of a DANA service, such as customer service or account support, and is used to capture credentials.
Secondary Method: Social Engineering
The site uses tactics like fear and urgency to trick users, offering fake services.
🌐 Infrastructure Indicators of Compromise
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for qwip.qzz.io
Found 2 other scans for this domain