
Phishing Analysis
Detailed analysis of captured phishing page
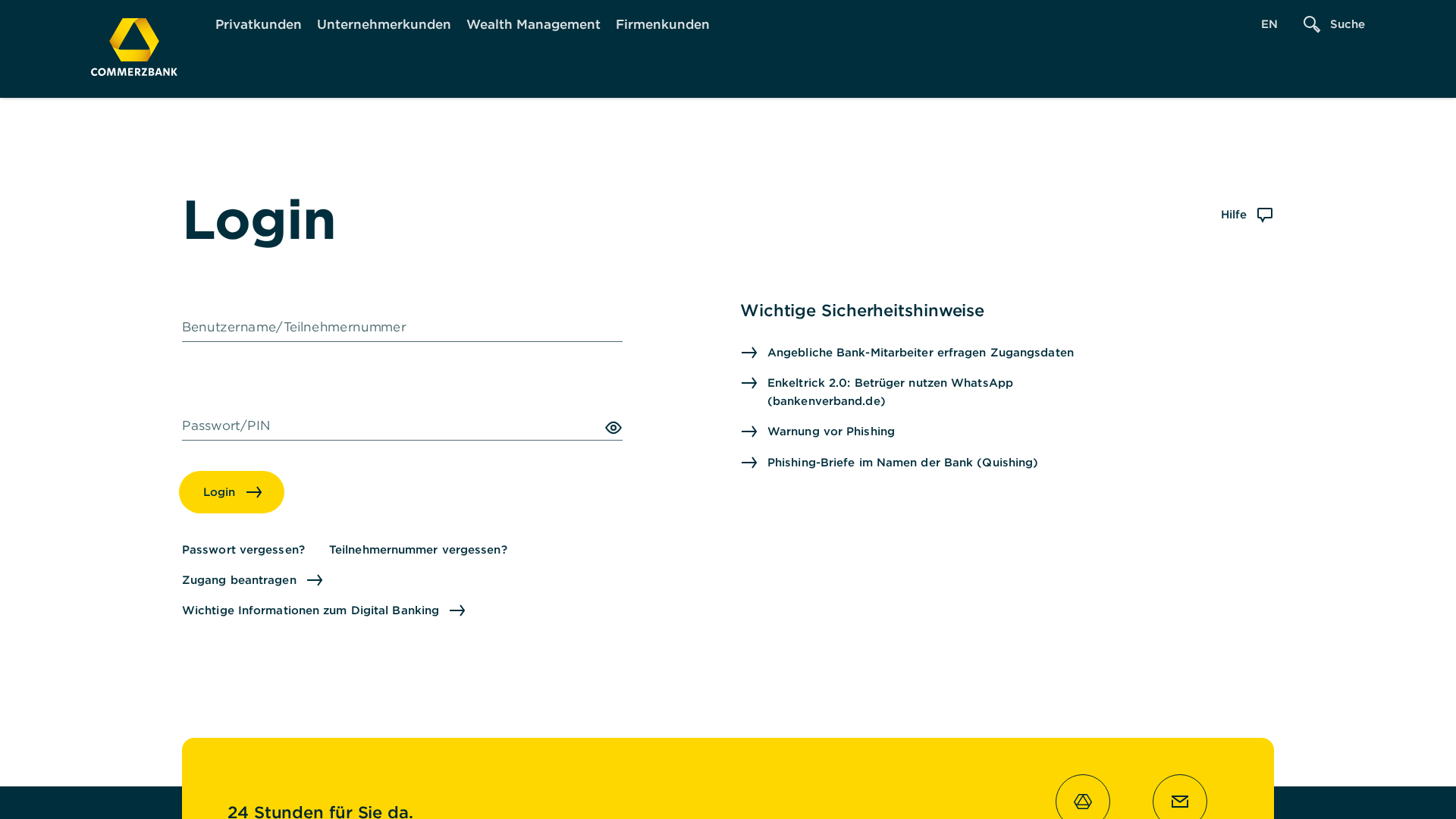
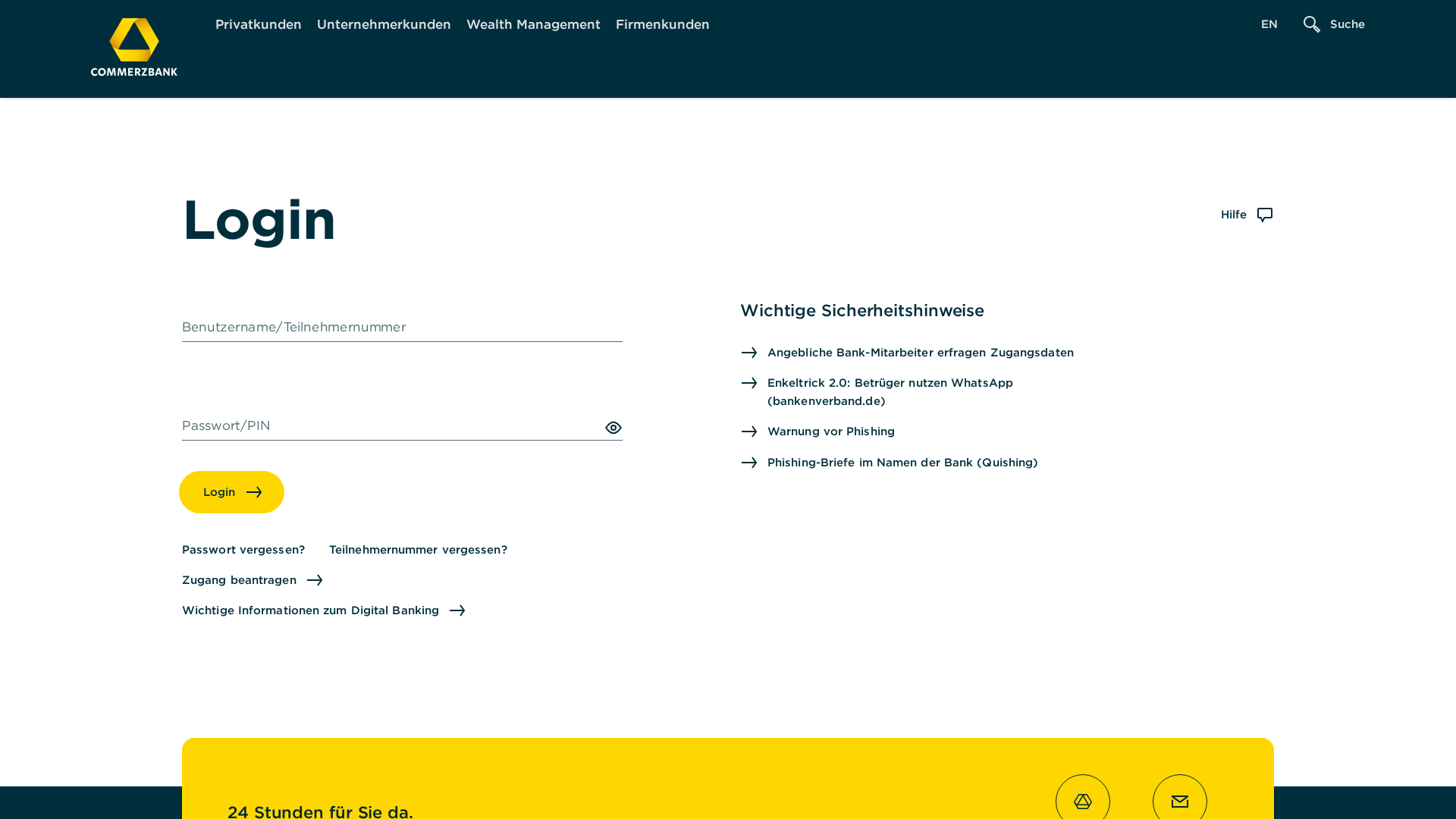
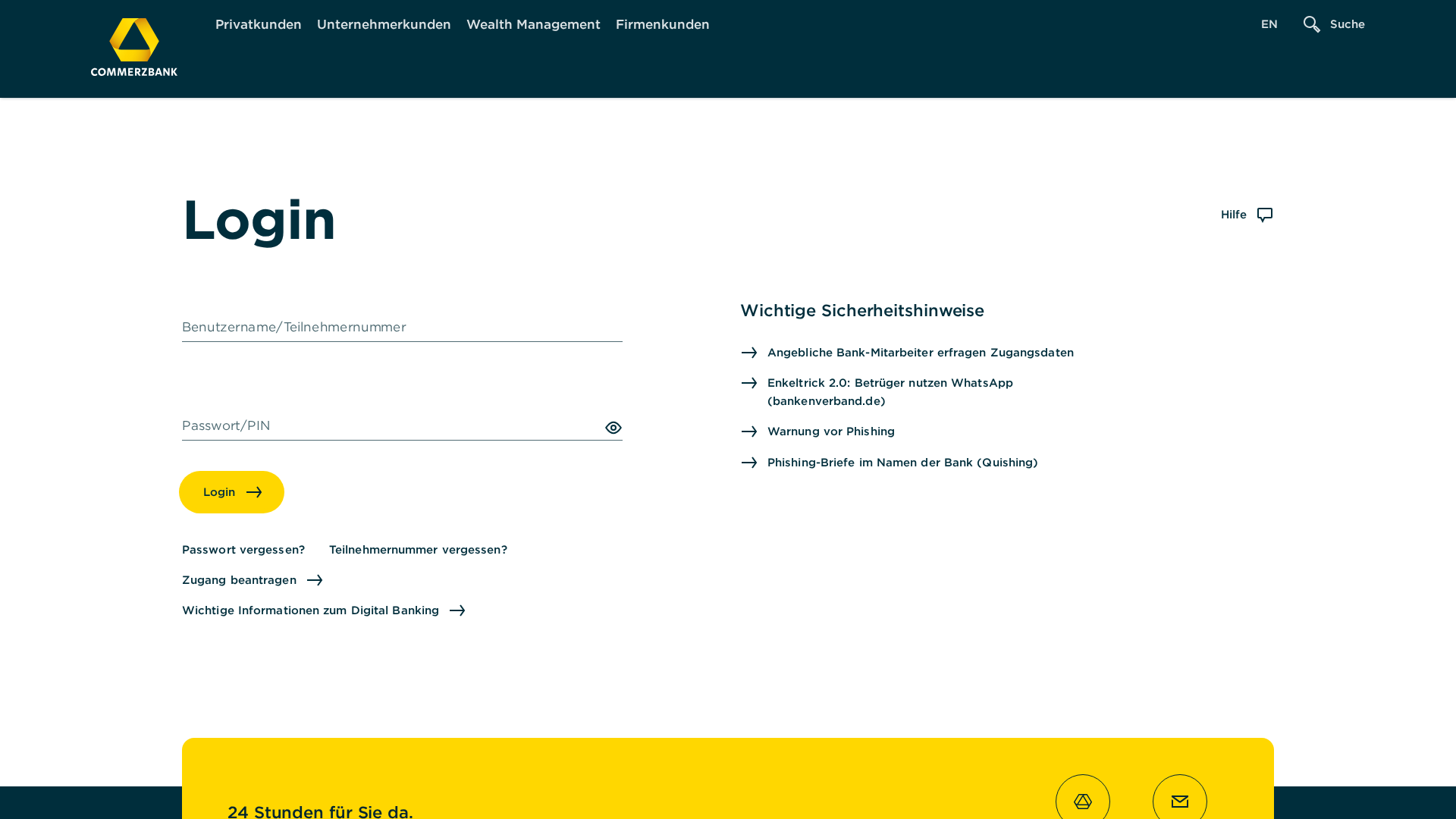
Visual Capture
Detection Info
http://vrmirror.pages.dev/service/online-banking
Detected Brand
Commerzbank
Country
International
Confidence
95%
HTTP Status
200
Report ID
5d7d1524-d9b…
Analyzed
2026-02-22 12:24
Final URL (after redirects)
https://vrmirror.pages.dev/service/online-banking
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1D1735BA054C87A7342F31BC4B9A3AF396396831ECE4AC405DDE942C41FF7CF9A896915 |
|
CONTENT
ssdeep
|
384:A9rxNR9MvCh4o3k69pvmEVfSyqZpTZAfqAvkq73Y3ua3F0dF0TFYqt:AXNR9MvyfUAvmEVfSyQfq7DOESxt |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
8f6f507a406e152f |
|
VISUAL
aHash
|
00ffffffffffff00 |
|
VISUAL
dHash
|
237864a6467020e0 |
|
VISUAL
wHash
|
00bfb583839fff00 |
|
VISUAL
colorHash
|
06000010180 |
|
VISUAL
cropResistant
|
61612646666002e0,18e7a738202020c0 |
Code Analysis
Risk Score
50/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Commerzbank customers
• Method: Impersonation via login form on a free hosting site.
• Exfil: Credentials (username/PIN)
• Indicators: Free hosting, brand logo, login form.
• Risk: High
🎯 Kit Endpoints
- /lp/login
- https://kunden.commerzbank.de/lp/login?language=en_GB
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Free hosting with brand logo
The use of a free hosting provider (pages.dev) combined with a legitimate brand logo is a strong indicator of phishing.
Login form detected
The page contains a login form, which increases the likelihood of credential harvesting.
Brand impersonation
The page attempts to impersonate the Commerzbank website.
🔬 Comprehensive Threat Analysis
Threat Type
Credential Harvesting Kit
Target
Commerzbank users (International)
Attack Method
Brand impersonation + credential harvesting forms
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
MEDIUM - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
🏢 Brand Impersonation Analysis
Impersonated Brand
Commerzbank
Official Website
https://www.commerzbank.de/
Fake Service
Online Banking Login
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker is attempting to steal the user's login credentials (username and password) by presenting a fake login form that looks like the real Commerzbank login page.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
vrmirror.pages.dev
Registered
None
Registrar
None
Status
None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Commerzbank
https://vrmirror.pages.dev/konten-zahlungsverkehr/wissen/sic...
Apr 07, 2026
Commerzbank
https://vrmirror.pages.dev/service/online-banking
Mar 20, 2026
Commerzbank
http://vrmirror.pages.dev/konten-zahlungsverkehr/wissen/sich...
Mar 02, 2026
Commerzbank
https://vrmirror.pages.dev/hinweise/impressum
Jan 24, 2026
Commerzbank
https://vrmirror.pages.dev/service/wie-kann-ich-phototan-akt...
Jan 19, 2026
Scan History for vrmirror.pages.dev
Found 10 other scans for this domain
-
https://vrmirror.pages.dev/konten-zahlungsverkehr/...
https://vrmirror.pages.dev/service/online-banking
http://vrmirror.pages.dev/konten-zahlungsverkehr/w...
https://vrmirror.pages.dev/hinweise/impressum
https://vrmirror.pages.dev/service/wie-kann-ich-ph...
https://vrmirror.pages.dev/service/wie-kann-ich-ph...
https://vrmirror.pages.dev/service/online-banking-...
https://vrmirror.pages.dev/service/online-banking-...
https://vrmirror.pages.dev/prozess/WebObjects/Proz...
https://vrmirror.pages.dev/service/online-banking-...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.