Phishing Analysis
Detailed analysis of captured phishing page
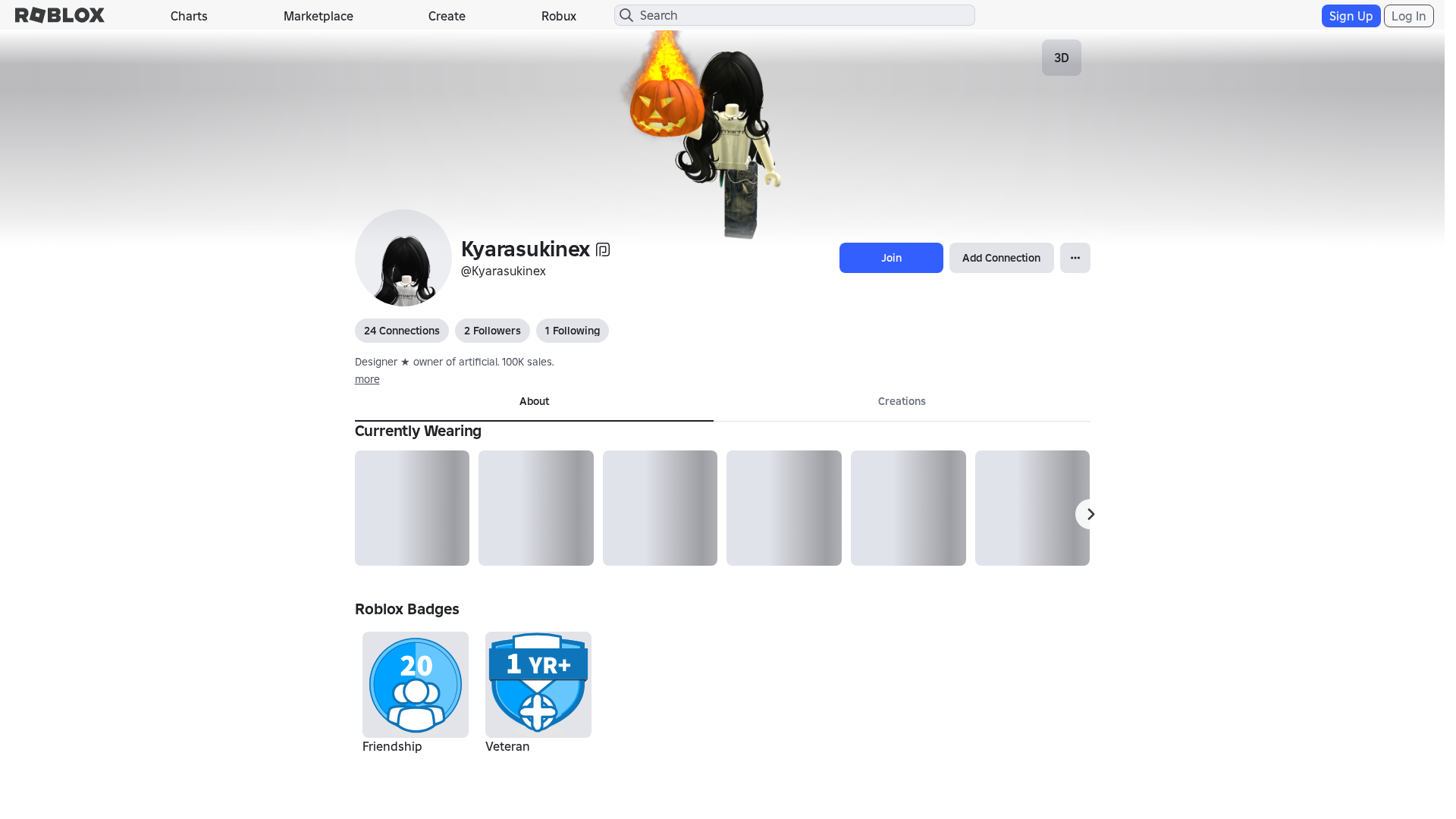
Visual Capture
No screenshot available
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T12483857292542437617B79CAF064771AA2D3D74FCA8246E1A2F8939A0FD6CE1FC1740E |
|
CONTENT
ssdeep
|
1536:rEZXWn9rt51+Be4dr5PNYuOVeVFZv7Hg7Hz7HO7HS7HI7Hb7Hn7Hm7Hk7He7HO7z:oZXWn51GBFOuOy7A7T7u7y7o777H7G7m |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b0471363c798ecbc |
|
VISUAL
aHash
|
0000d3ffc3c3dfff |
|
VISUAL
dHash
|
e8c8b63016063032 |
|
VISUAL
wHash
|
0000c3dfc3c3cfdf |
|
VISUAL
colorHash
|
070010080c0 |
|
VISUAL
cropResistant
|
e8c8b63016063032,37376751192747a7 |
Code Analysis
🔬 Threat Analysis Report
• Threat: No threat detected.
• Target: Roblox users.
• Method: Legitimate Roblox website content.
• Exfil: No exfiltration detected.
• Indicators: No suspicious indicators.
• Risk: LOW - Legitimate content.
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- js_packer
- base64_strings
🎯 Kit Endpoints
- https://www.roblox.com/catalog/14618207727/null
- https://www.roblox.com/catalog/17606243214/null
- https://www.roblox.com/catalog/1365767/null
- /catalog/2510233257
- https://www.roblox.com/catalog/92757812011061/null
- /catalog/1402432199
- https://www.roblox.com/catalog/99519402284266/null
- /catalog/131592085
- /catalog/10159600649
- https://www.roblox.com/catalog/973771666/null
- https://www.roblox.com.ml/catalog?CatalogContext=1&Keyword=
- https://www.roblox.com/catalog/12644968167/null
- https://www.roblox.com/catalog/80173850283177/null
- https://www.roblox.com/catalog/94680592831224/null
- https://www.roblox.com/catalog/111007665254899/null
- https://www.roblox.com/catalog/93337771456291/null
- https://www.roblox.com/catalog/17568567276/null
- https://www.roblox.com.ml/info/blog?locale=en_us
- /catalog/973766674
- /catalog
- https://www.roblox.com/catalog/138156157075393/null
- /catalog/973771666
- /catalog/139607718
- https://www.roblox.com/catalog/124343282827669/null
- https://www.roblox.com/catalog/131592085/null
- https://www.roblox.com/catalog/115905570886697/null
- https://www.roblox.com/catalog/10159600649/null
- /catalog/1365767
- https://www.roblox.com/catalog/973766674/null
- https://www.roblox.com/catalog/2510233257/null
- /login?returnUrl=1039120924209493
- https://www.roblox.com/catalog/1402432199/null
- https://www.roblox.com/catalog/139607718/null
- https://www.roblox.com/catalog/119897350346054/null
📡 API Calls Detected
- https://ro.blox.com/Ebh5?
- get
- babylonjs
- POST
- https://apis.
- https://help.roblox.com/hc/articles/30428367965460
- GET
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 934 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The phishing kit deploys a credential harvester that intercepts user inputs in real-time via form fields labeled 'Sign Up', 'Log In', 'Join', and 'Add Connection'. The harvested credentials are likely exfiltrated to a remote server for immediate use in account takeover attacks.
Secondary Method: OTP and Financial Data Theft
The kit includes an OTP stealer and card stealer module, designed to capture one-time passwords and payment card details. This enables attackers to bypass multi-factor authentication and conduct unauthorized transactions.
🌐 Infrastructure Indicators of Compromise
Domain Information
🦠 Malicious Files
Obfuscated JavaScript files containing credential harvesting, OTP stealing, and card skimming functionality.
📊 Attack Flow Diagram
┌──────────────────────────────────────────────────────────┐
│ 1. VICTIM RECEIVES PHISHING LURE │
│ - Email/SMS with fake Roblox login link │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 2. VICTIM VISITS FAKE ROBLOX SITE │
│ - Clones official Roblox login page │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 3. CREDENTIAL INPUT │
│ - Victim enters username/password │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 4. CREDENTIAL HARVESTING │
│ - Form captures input data │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 5. DATA EXFILTRATION │
│ - HTTP POST submits credentials to attacker server │
└──────────────────────────────────────────────────────────┘
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Light
- : Heavy
- : None
- : None
- : Light
- : None
- : None
- : None
- : None
- : Light
- : Light
- : None
- : Light
- : None
- : Heavy
- : None
- : None
- : Heavy
- : Heavy
- : Light
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
┌──────────────────────────────────────────────────────────┐
│ 1. VICTIM RECEIVES PHISHING LURE │
│ - Email/SMS with fake Roblox login link │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 2. VICTIM VISITS FAKE ROBLOX SITE │
│ - Clones official Roblox login page │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 3. CREDENTIAL INPUT │
│ - Victim enters username/password │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 4. CREDENTIAL HARVESTING │
│ - Form captures input data │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 5. DATA EXFILTRATION │
│ - HTTP POST submits credentials to attacker server │
└──────────────────────────────────────────────────────────┘
🎯 Malicious Files Identified
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for to.lk
Found 10 other scans for this domain