
Phishing Analysis
Detailed analysis of captured phishing page
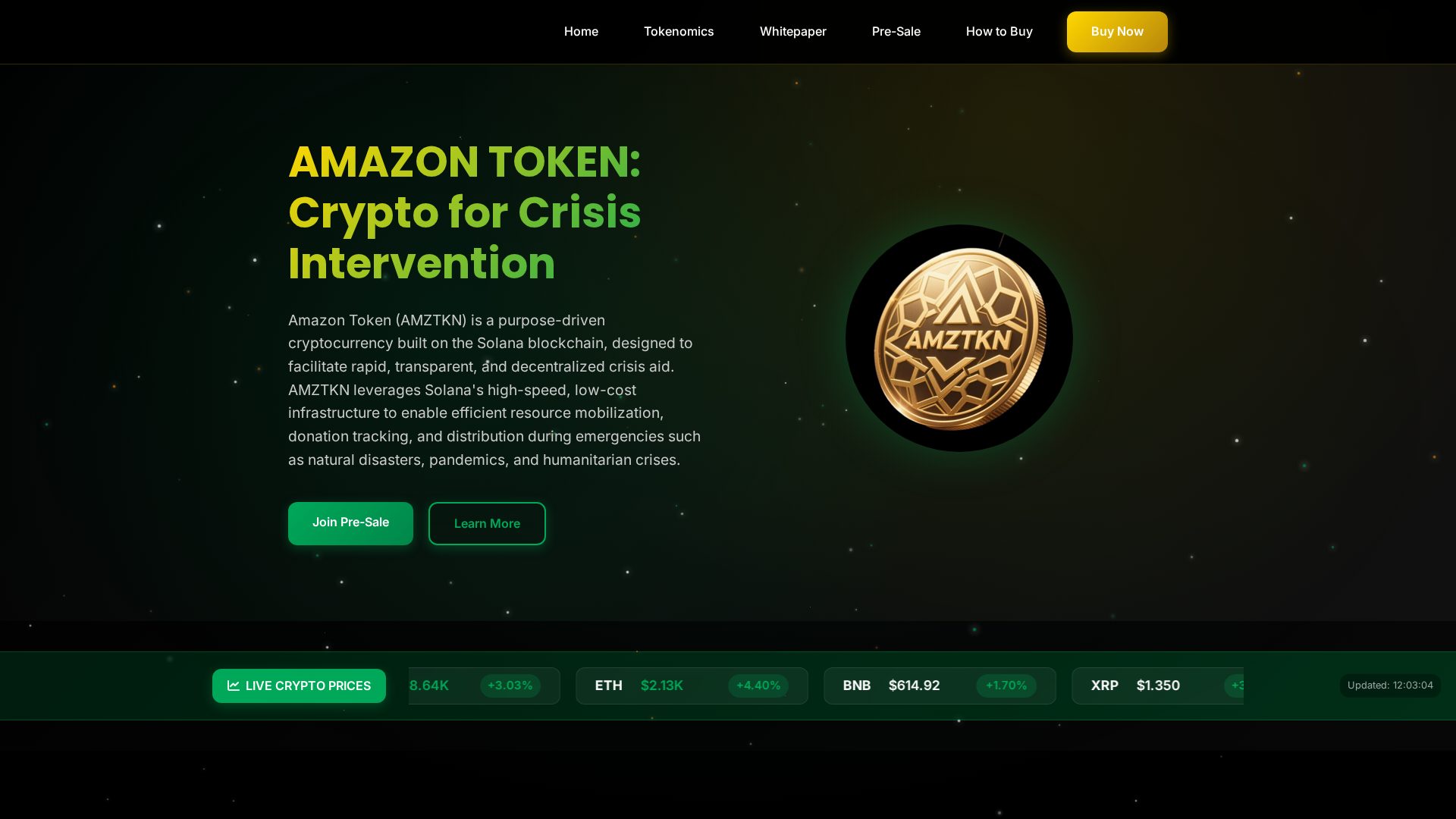
Visual Capture
Detection Info
https://amazontoken.co/
Detected Brand
Amazon
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
5e56157c-5eb…
Analyzed
2026-04-01 10:03
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1223330709506863260DBE39976E1974E0BB21241FB53062D15FFBDA183CDAFEC87E942 |
|
CONTENT
ssdeep
|
1536:TkgUb61Htydyw68uLzQxj8NqF7jhY6q1wB118bq+cXcAWeZ5kD9jJfq3H3tZzylF:cS7vL |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
82963c6d3e9236e5 |
|
VISUAL
aHash
|
06727c3c7c207e00 |
|
VISUAL
dHash
|
3cc6c9e9c0d49890 |
|
VISUAL
wHash
|
067e7e7e74607e00 |
|
VISUAL
colorHash
|
38200009600 |
|
VISUAL
cropResistant
|
70c0c1a3497236c8,3cc6c9e9c0d49890 |
Code Analysis
Risk Score
65/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Banking
🎣 Personal Info
📡 API Calls Detected
- https://api.coingecko.com/api/v3/simple/price?ids=solana,bitcoin,ethereum,binancecoin,ripple,cardano,dogecoin,polkadot,avalanche-2,polygon-pos&vs_currencies=usd&include_24hr_change=true
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Amazon users
Attack Method
credential harvesting forms
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Banking, Personal Info
🏢 Brand Impersonation Analysis
Impersonated Brand
Amazon
Official Website
https://www.amazon.com
Fake Service
Banking/payment service
⚔️ Attack Methodology
Primary Method: Banking Credential Theft
Victim enters banking credentials including account numbers and security questions. Attacker gains full access to victim's banking services.
Secondary Method: Client-Side Form Interception
JavaScript intercepts form submissions before they reach the fake backend. This allows real-time credential harvesting and validation without server round-trips.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
amazontoken.co
Registered
2025-11-24 12:55:27+00:00
Registrar
GoDaddy.com, LLC
Status
Active (127 days old)
Hosting Information
Provider
GoDaddy
ASN
🤖 AI-Extracted Threat Intelligence

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.