
Phishing Analysis
Detailed analysis of captured phishing page
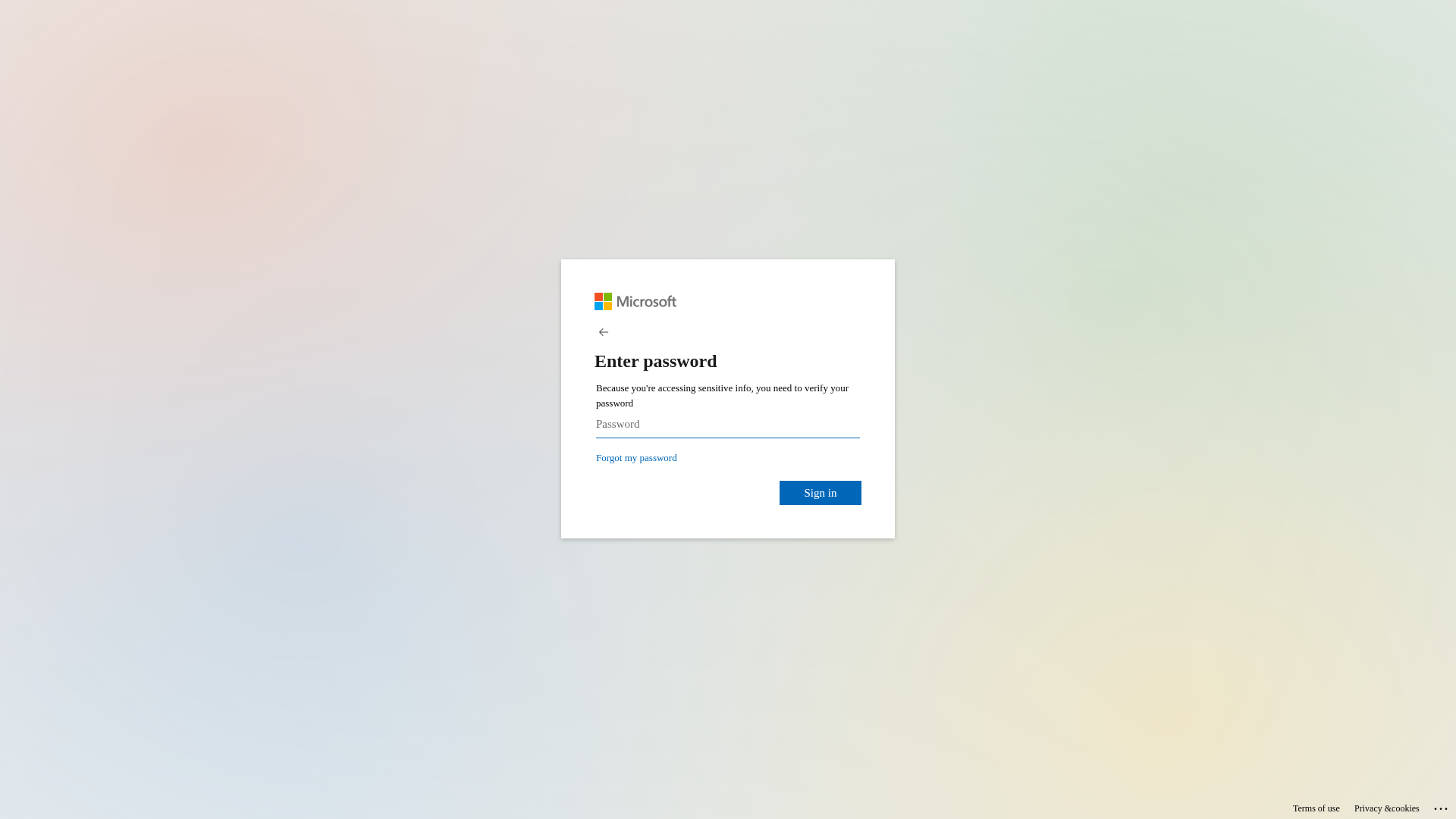
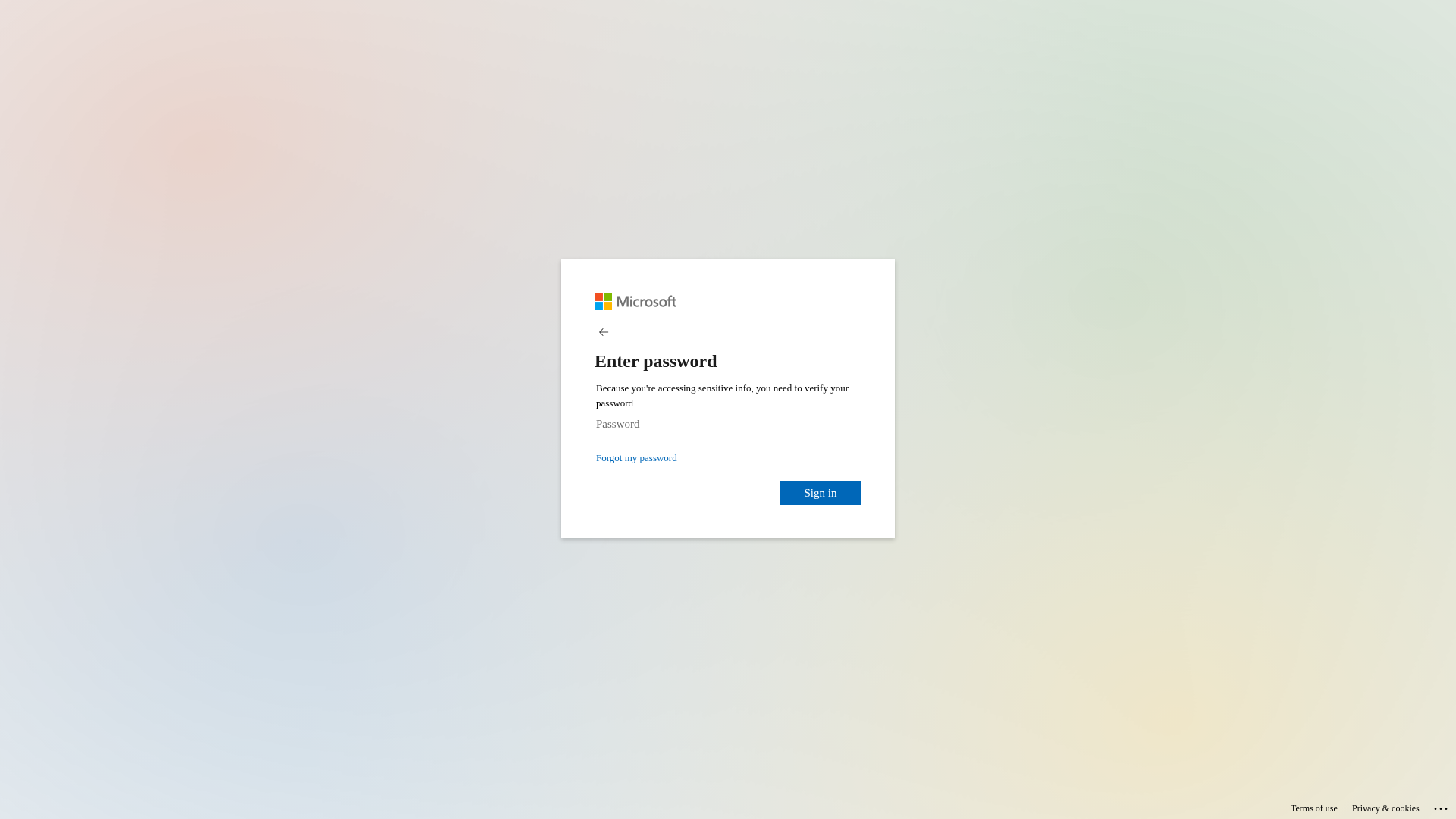
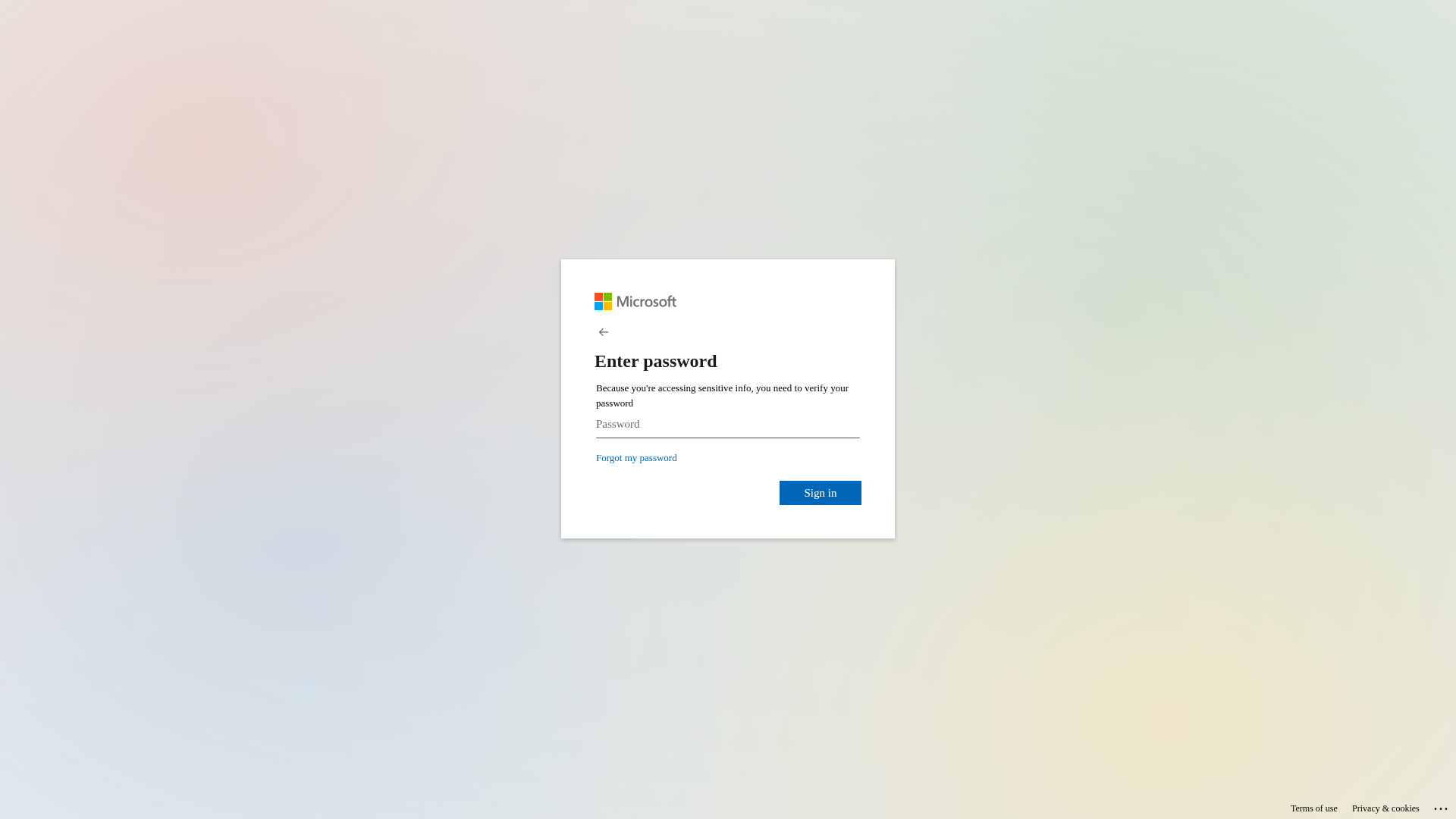
Visual Capture
Detection Info
https://bafkreiamrnq7ksq62eeqix4zhkowtijcmi6wo6yw4awvuiffm3gyd5nzdi.ipfs.dweb.link/
Detected Brand
Microsoft
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
5ed6d9e2-927…
Analyzed
2026-02-27 06:23
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T146C13031A000DD2B03C2D7E8A6BAB70B7355C349D6435A565BF8C38D5EE3EA5CC26261 |
|
CONTENT
ssdeep
|
96:n9eFWPJYKP06hiXlAm3JRy6wgsrs2dRd8ujsiMf/PzeQMvuQ6w60nQJvi:8Q0XymZy6HicnzeDuQ6B0QJvi |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9c4b7326d899cce4 |
|
VISUAL
aHash
|
180018181d1f0f9f |
|
VISUAL
dHash
|
7161713331357938 |
|
VISUAL
wHash
|
191818181f1f1fff |
|
VISUAL
colorHash
|
07000000180 |
|
VISUAL
cropResistant
|
7161713331357938 |
Code Analysis
Risk Score
79/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Personal Info
🔒 Obfuscation Detected
- atob
- fromCharCode
- base64_strings
🎯 Kit Endpoints
- https://passwordreset.microsoftonline.com/?ru=https%3a%2f%2flogin.microsoftonline.com%2fcommon%2freprocess%3fctx%3drQIIAYWSu4vTAADGm_au1zvQO0VEEeQGBxXS5tU8Kg49m0uba5LWJO0lgyVt0jyaV9u0aTIdTo43OdwkIg4nLk4iiDffdIuLoyCIgxxOiou9v8Dlgw9-fMv321jDi2QRKkL3c3ARrtzBUKysEX0KpDQcBTEKhkANQ3AQLaM4ikCwXobQydWNrQP6258nN7_Sr3efvnn1-fzvMXDbiqJwWimV4jguBsOhPTCKg8AruZqv2775HgDOAOA7ABxlVw0flMXj7BRHCRzFSJzCcQzBYAinigrCJbzE2mqXjlSmjSgJBPEevWhKZswz7YhH5ITzOJj3VFeoWY66ZHlGhjlmyTs0xj1a8qluNbuspUijiPd4m5eqsSApy53O6Et2U6jOIgu5iGBip8av7PowmHi9MJhGR7nn2YlpRA1nFOm2WWtFCian7LSh2qbLNxGQjOtE0yL0RJtbLT1g91TIjljHpgYttGeIC7_pDQfueMF1zJDSGMVE6WqDEXFWwtvKUBLS_VQQSXjIk464GzHJqDkLU6xOmi5EJCEqzOmpk87mCYmEYrutN4ZUn9ujPTcZDagIdvpwYKhpDZwlrTFIWb3I1H1kZIug2yCEMcu0SEXq-QuC1z153JrLUoDAEYjUFTFs99vYXOt03J2eXN-btYxJzbGZVNUbEJ4ws2RB7ldHeNmtph6PonKP6gwm83A6ZQPJEbvxu1x-eaYX-Ke5y0Fo-La-HU6Coe0aZyvAj5XrhfxW4UZmO3P3GpSrFAobW5mL9nsFeLm6tEU-qDz4ufmRfvvi3q2TT4eZ09VSXVW7jiA1-qQSsIsBYcCxxPnCTuQmlkSNISTAm_N-jdEI7CFcgQ_zwGE-f5q_0qj1eFoSpSpfqz6uIT3oPA88W8t8WP-PfyeXMv8A0&mkt=en-US&hosted=0&device_platform=Windows+10
📡 API Calls Detected
- GET
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Personal Info
Credential Harvesting
Credential harvesting detected with 3 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 6 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Two-Factor Authentication Stealer
Target
Microsoft users
Attack Method
credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Personal Info
- 6 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Microsoft
Official Website
https://www.microsoft.com
Fake Service
Credential harvesting service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 6 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
bafkreiamrnq7ksq62eeqix4zhkowtijcmi6wo6yw4awvuiffm3gyd5nzdi.ipfs.dweb.link
Registered
2017-02-24 01:05:26.675000+00:00
Registrar
CSC Corporate Domains, Inc.
Status
Active (older domain)
Hosting Information
Provider
CSC Corporate Domains, Inc.
ASN
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Microsoft
https://ipfs.io/ipfs/bafkreicyxx5lcva7kw2zgenize2mh3in3llzmd...
Apr 07, 2026
Microsoft
https://ipfs.io/ipfs/bafkreiamrnq7ksq62eeqix4zhkowtijcmi6wo6...
Feb 27, 2026
Microsoft
https://ipfs.io/ipfs/bafkreiamrnq7ksq62eeqix4zhkowtijcmi6wo6...
Feb 27, 2026
Microsoft
https://ipfs.io/ipfs/bafkreihepzgltwylwmrklub4zkjk4saxdwpkrb...
Feb 10, 2026
Microsoft
https://ipfs.io/ipfs/bafkreiclpeo3f2fqma2osalepnknn4wusqh735...
Feb 03, 2026

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.