
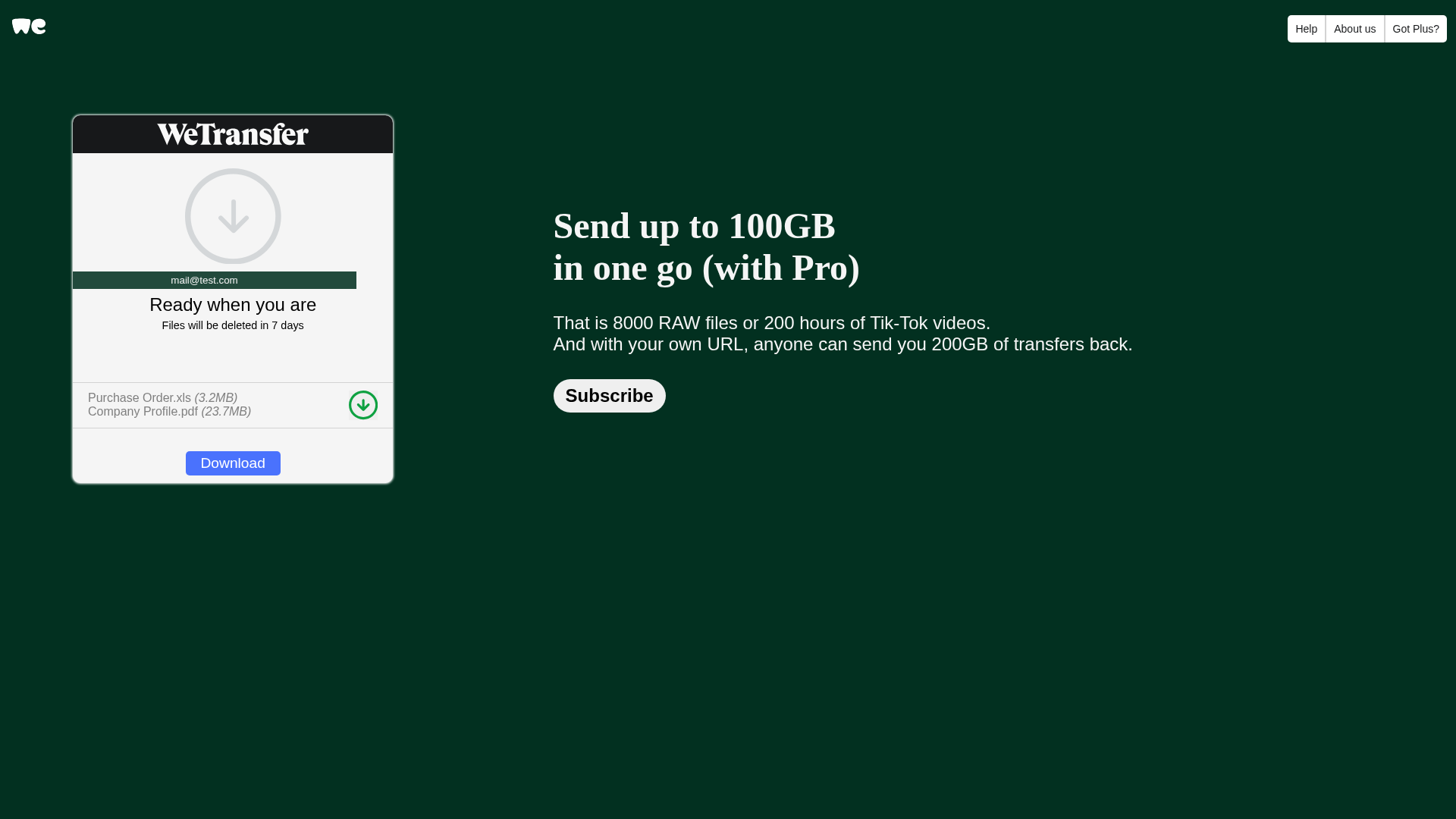
Phishing Analysis
Detailed analysis of captured phishing page
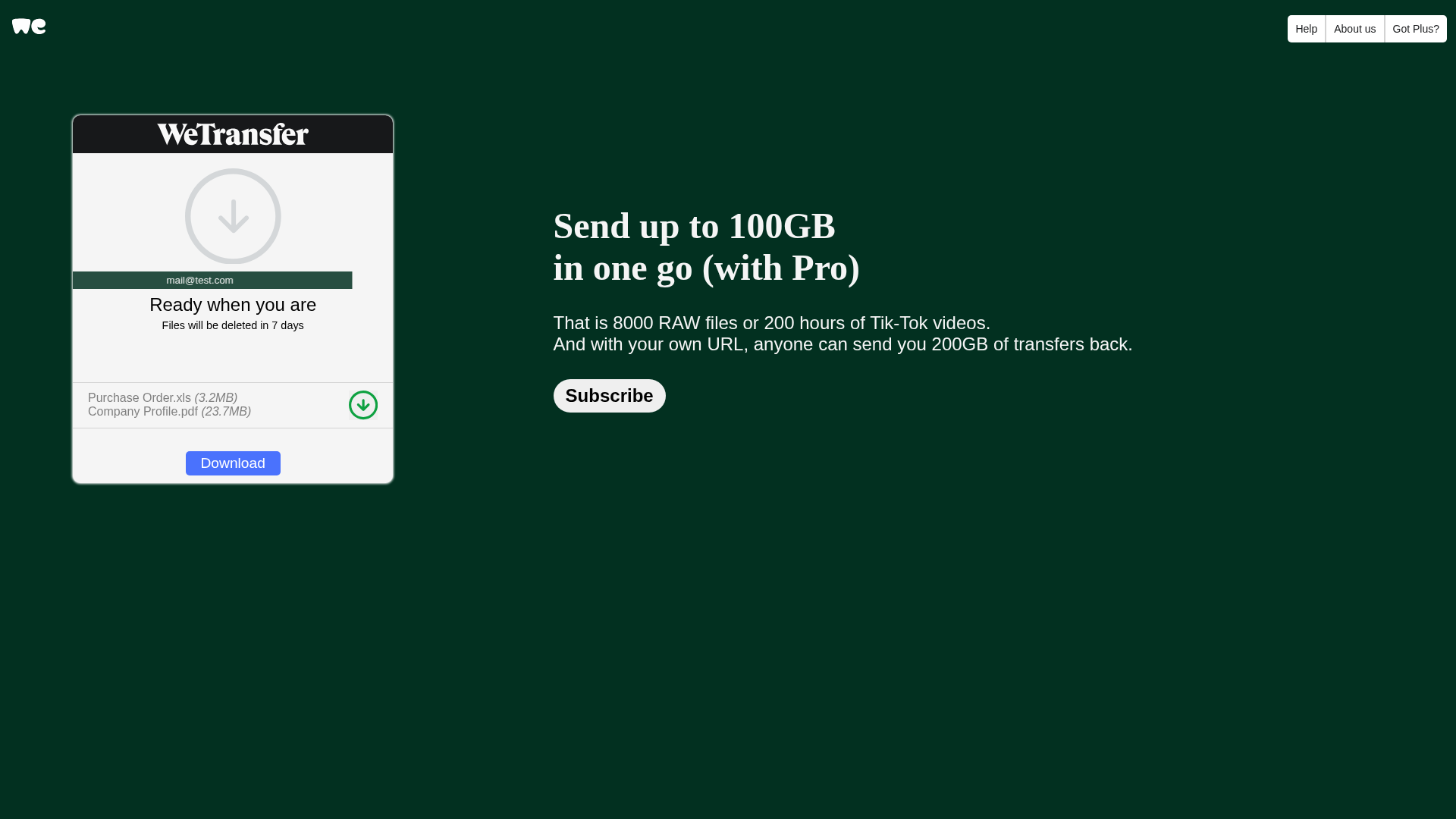
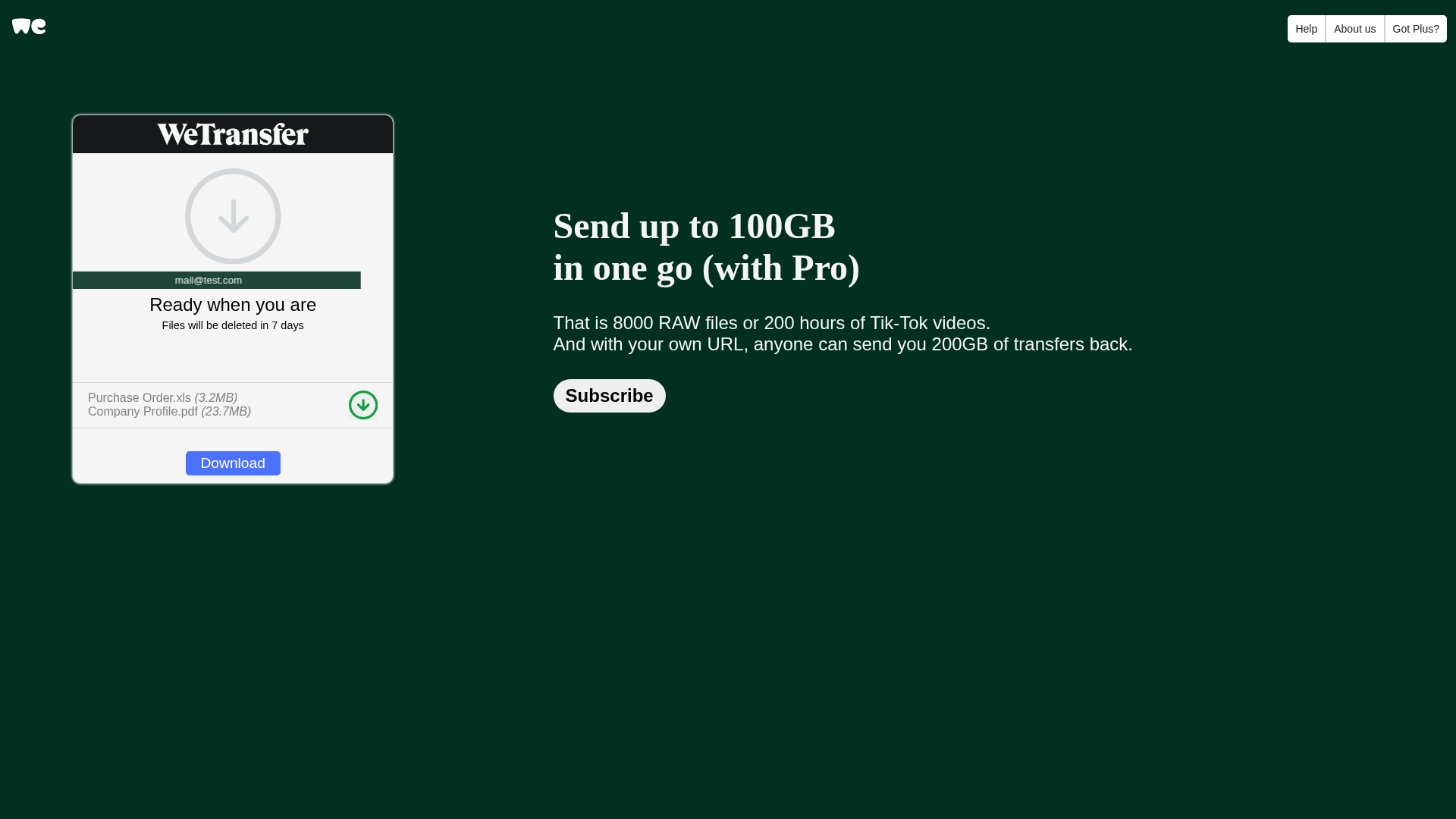
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T179724C5A9E2C5C1D830926A7E3DE09CC613DD397DB5901C494FAE8C888D7A64DCCAC9D |
|
CONTENT
ssdeep
|
192:SLwJ7tvTKuuvhAZ44vW398QNJdJdrUWi5cPQ1+LKNon/KNwJORY1xVVCsQufEUo9:Sc/TKusK49SQnp7i5cNLKeARYvWc0 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e0e00f0fea8f0fe8 |
|
VISUAL
aHash
|
01c0f8f0e0000000 |
|
VISUAL
dHash
|
6b90929096788000 |
|
VISUAL
wHash
|
f1f0f8fef0400000 |
|
VISUAL
colorHash
|
00000000e00 |
|
VISUAL
cropResistant
|
4d14672716680c8e,6b90929096788000 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Impersonation Phishing
• Target: WeTransfer users
• Method: Malicious link or attachment
• Exfil: Unknown (likely stealing data or credentials)
• Indicators: Domain mismatch, impersonation.
• Risk: HIGH
🔒 Obfuscation Detected
- atob
🎯 Kit Endpoints
- #logo-path
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Personal Info
- 2 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Impersonation with Download/Subscribe buttons
The attacker creates a fake WeTransfer page with 'Download' and 'Subscribe' buttons. When the user clicks on the Download button it likely will try to download a malicious file or lead to another phishing page.
Secondary Method: Credential Harvesting
The site may be designed to steal login credentials, by tricking the user to enter their data.
🌐 Infrastructure Indicators of Compromise
Domain Information
🔬 JavaScript Deep Analysis
🔐 Obfuscation Detected
- : Light
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for lvgseguranca.com.br
Found 10 other scans for this domain
-
https://lvgseguranca.com.br/
https://lvgseguranca.com.br/wp-content/we/83773922...
https://lvgseguranca.com.br/wp-content/we/83773922...
http://www.lvgseguranca.com.br/wp-icons/we/276373....
https://lvgseguranca.com.br/wp-includes/5678fsghaj...
https://lvgseguranca.com.br/wp-content/we/83773922...
https://lvgseguranca.com.br/wp-includes/z836763/19...
https://lvgseguranca.com.br/wp-includes/z836763/19...
http://lvgseguranca.com.br/wp-content/we/83773922....
https://lvgseguranca.com.br/wp-content/we/83773922...
