
Phishing Analysis
Detailed analysis of captured phishing page
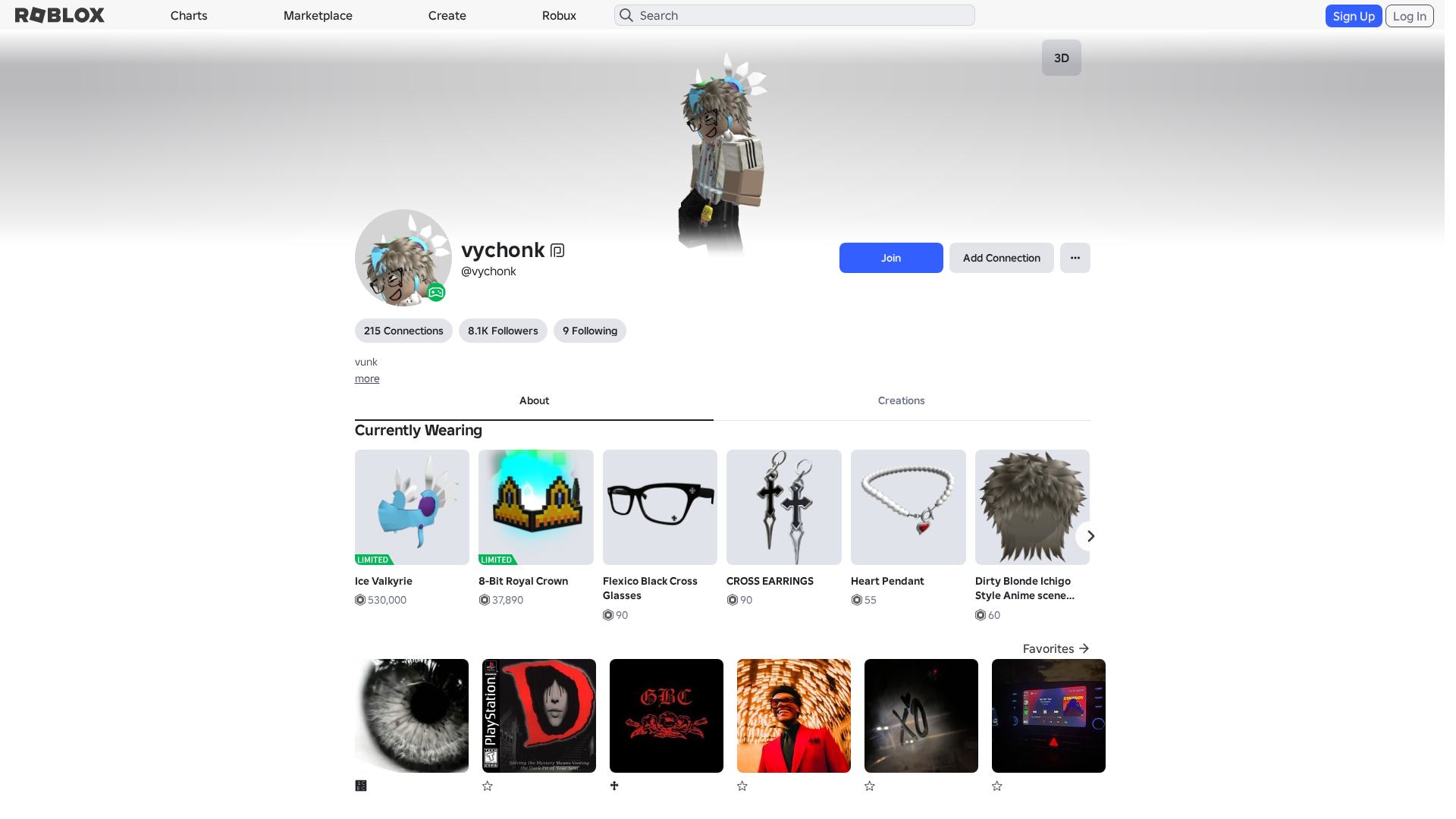
Visual Capture
Detection Info
https://roblx.me/s/hFtjv5
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
66cfb9f1-b01…
Analyzed
2026-04-03 10:34
Final URL (after redirects)
https://www.robiox.com.py/users/303645146467/profile
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T17E832E7292542837617B79DAF064672AA2D7C70FCA8346E1A2FCD39A0FD6CD1E85340D |
|
CONTENT
ssdeep
|
1536:4SPXWnQrUH+egwsgcugAHgUwgxSgZBg0hgzhgGygBOgyogB4gl6gSAgwOgoagx+b:/PXWhH+A3XlHiZdS7DWyIV+SDXCZuvRM |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e996614999bc8e69 |
|
VISUAL
aHash
|
0024d7ffcbfbc3c3 |
|
VISUAL
dHash
|
e8c8263092129292 |
|
VISUAL
wHash
|
0000dfffc3cbc3c3 |
|
VISUAL
colorHash
|
07200010040 |
|
VISUAL
cropResistant
|
e8c8263092129292,4900717060500041,7616969496969491,2963c5c3c7603809,4c6a29292275033c |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/6532800250/Polar-Bear
- https://api.injuries.lu/catalog/12528202193/unnamed
- /login?returnUrl=
- https://api.injuries.lu/catalog/17706397060/lipstick-marks
- https://api.injuries.lu/catalog/10964458219/Fleur-de-lis-Pendant
- https://api.injuries.lu/catalog/17164857317/Flexico-Black-Cross-Glasses
- https://api.injuries.lu/catalog/11094996060/Heart-Pendant
- https://api.injuries.lu/catalog/126354114956642/adidas-Community-Animation-Pack
- https://api.injuries.lu/catalog/1029025/The-Classic-ROBLOX-Fedora
- https://api.injuries.lu/catalog/104468204349555/Dirty-Blonde-Ichigo-Style-Anime-scene-boy-hair-Y2k
- https://api.injuries.lu/catalog/121911959295081/Kid-tantrum
- https://api.injuries.lu/catalog/1365767/Valkyrie-Helm
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F303645146467%2Fprofile
- https://api.injuries.lu/catalog/140600227095432/NFL-Jump
- https://api.injuries.lu/catalog/106537993816942/adidas-Community-Animation-Pack
- https://api.injuries.lu/catalog/24123795/Al-Capwn
- https://api.injuries.lu/catalog/104072580597361/FORSAKEN-John-Doe-Pose
- https://api.injuries.lu/catalog/82462065668801/Thai-style-DJ-Dancing-kneel-up-down
- https://api.injuries.lu/catalog/15716540044/CROSS-EARRINGS
- https://api.injuries.lu/catalog/106810508343012/adidas-Community-Animation-Pack
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F303645146467%2Fprofile
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/128159108/Black-Iron-Bucket-of-Ultimate-Pwnage
- https://api.injuries.lu/catalog/215718515/Fiery-Horns-of-the-Netherworld
- https://api.injuries.lu/catalog/123695349157584/adidas-Community-Animation-Pack
- https://api.injuries.lu/catalog/93993406355955/adidas-Community-Animation-Pack
- https://api.injuries.lu/catalog/123080658312456/Fuggler-x-SpongeBob-SquarePants-Plushie-Keychain
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/14618207727/Default-Mood
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/10159600649/8-Bit-Royal-Crown
- https://api.injuries.lu/catalog/87337809867327/Awkward-Epic-Face-Dynamic-Head
- https://api.injuries.lu/catalog/124765145869332/adidas-Community-Animation-Pack
- https://api.injuries.lu/catalog/4390891467/Ice-Valkyrie
- https://api.injuries.lu/catalog/110511723808460/SpiderMan-Hanging-Pose-Original
- https://api.injuries.lu/catalog/88660205895997/white-blue-argentina-y2k-emo-boy-shirt-jersey
- https://api.injuries.lu/catalog/1285307/Sparkle-Time-Fedora
📡 API Calls Detected
- https://ro.blox.com/Ebh5?
- GET
- https://apis.
- https://kyxn.dev/api/shorten
- https://kyxn.dev/api/shorten/TKvzwH
- /api/pageview
- get
- https://kyxn.dev${e.endpoint}
- /api/shorten
- POST
- https://help.roblox.com/hc/articles/30428367965460
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 212 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Roblox users
Attack Method
credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
HTTP POST to backend
Risk Assessment
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 212 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 212 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
roblx.me
Registered
Unknown
Registrar
None
Status
Age unknown
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for roblx.me
Found 9 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.