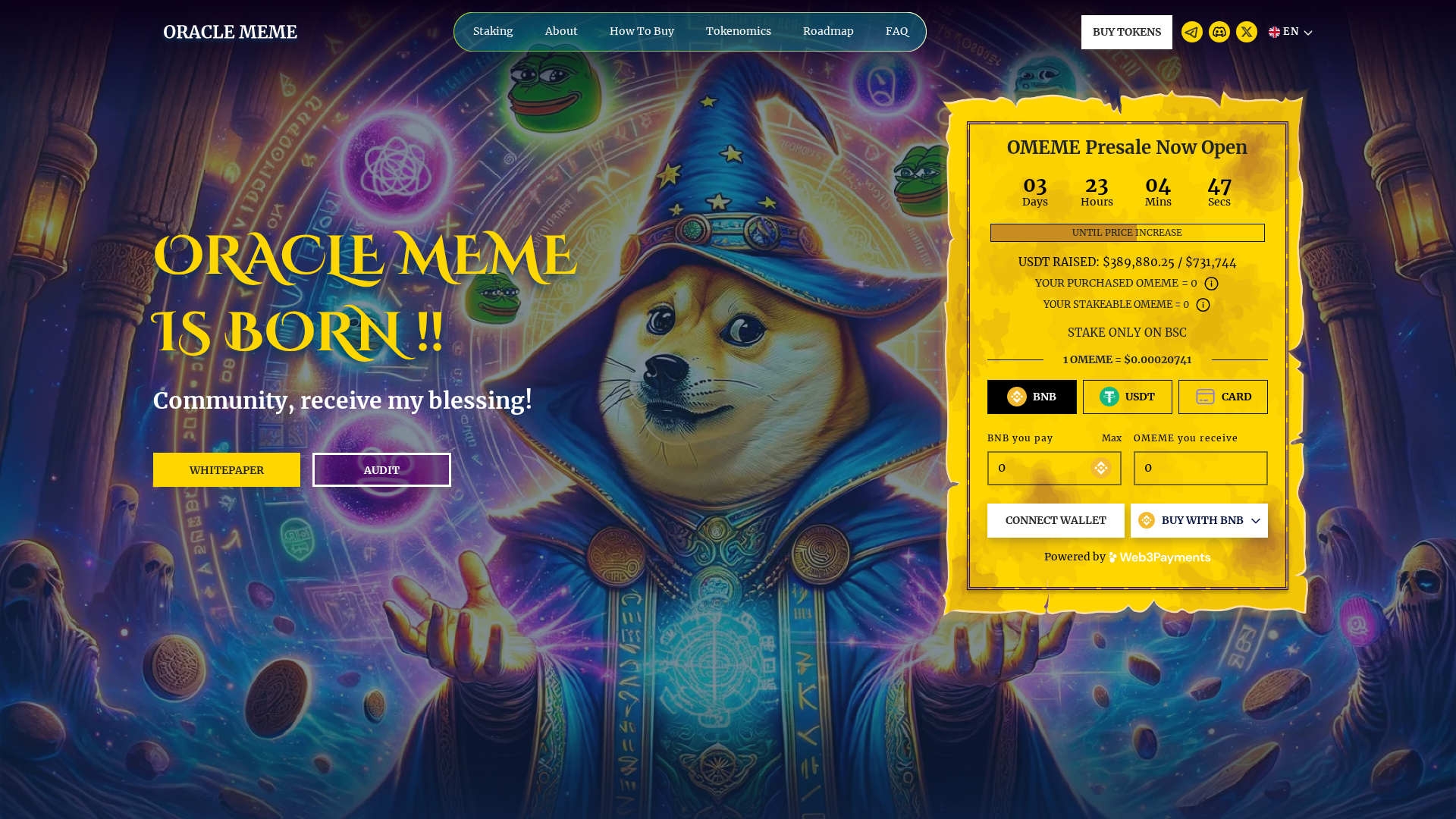
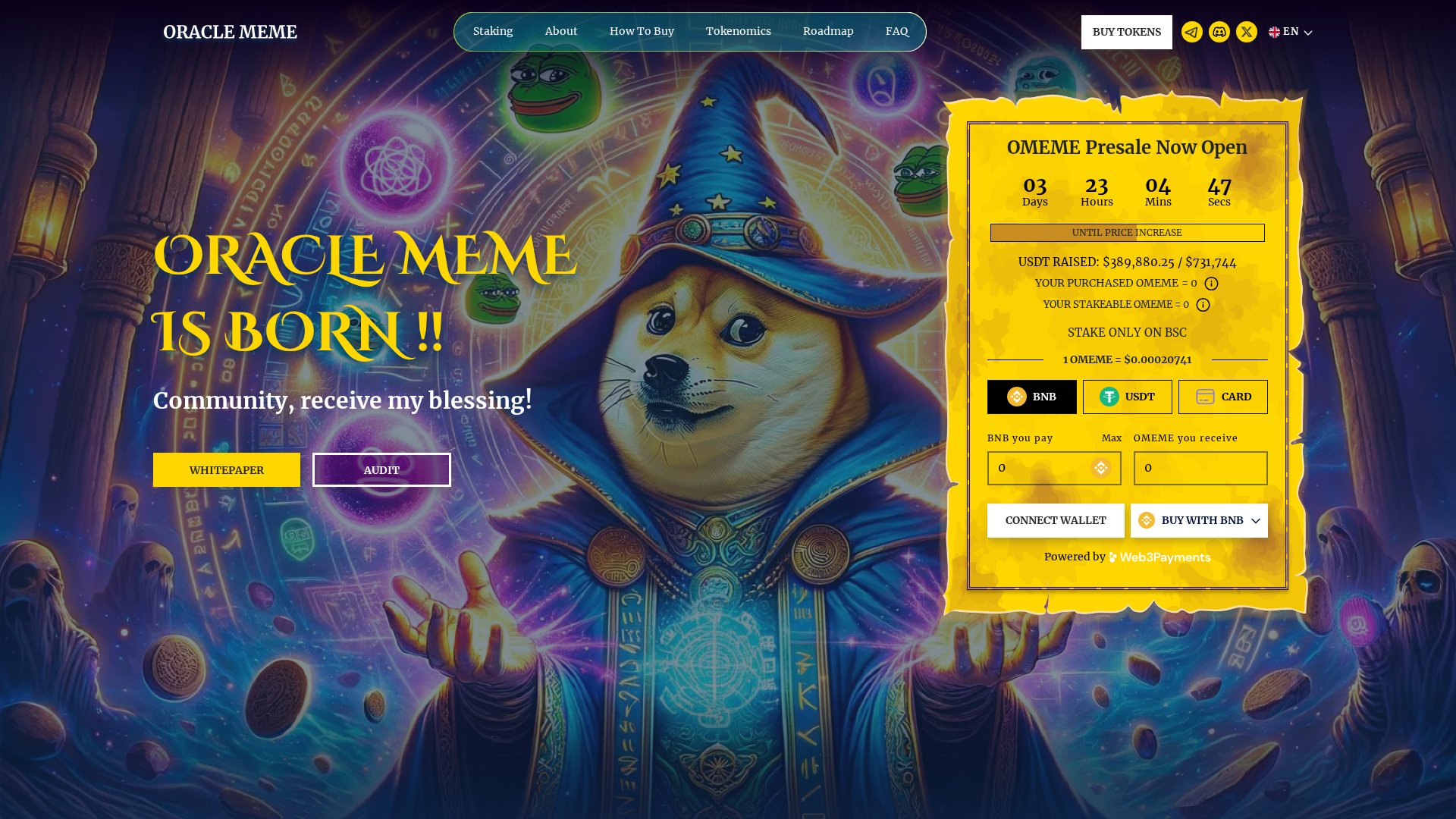
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T15B93EFB0216018AE07C7FC9874A73F465172C5EAE21A2984A7BC5AB58ED1FD4CCD63D3 |
|
CONTENT
ssdeep
|
1536:4b0UXdTRv1l/bdlzgPN4IN5aiduRx1E/qdczfPY4vN2ardTRSylREAElw+l2rlZi:4XdTRv1l/bdlzgPN4IN5aiduRx1E/qdP |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
95974a366949366d |
|
VISUAL
aHash
|
022e766e66261200 |
|
VISUAL
dHash
|
f4ccecde9eccd496 |
|
VISUAL
wHash
|
027e7e6e66673e00 |
|
VISUAL
colorHash
|
01001208040 |
|
VISUAL
cropResistant
|
a8b49ec636a6b0d1,f4ccecde9eccd496 |
Code Analysis
🔒 Obfuscation Detected
- eval
- base64_strings
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: OTP Stealer, Banking
- 4 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Two-Factor Authentication Bypass
Victim is prompted for 2FA code after entering credentials. The code is intercepted and used by attacker to access victim's account in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 4 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for oraclememe-com.pages.dev
Found 1 other scan for this domain