
Phishing Analysis
Detailed analysis of captured phishing page
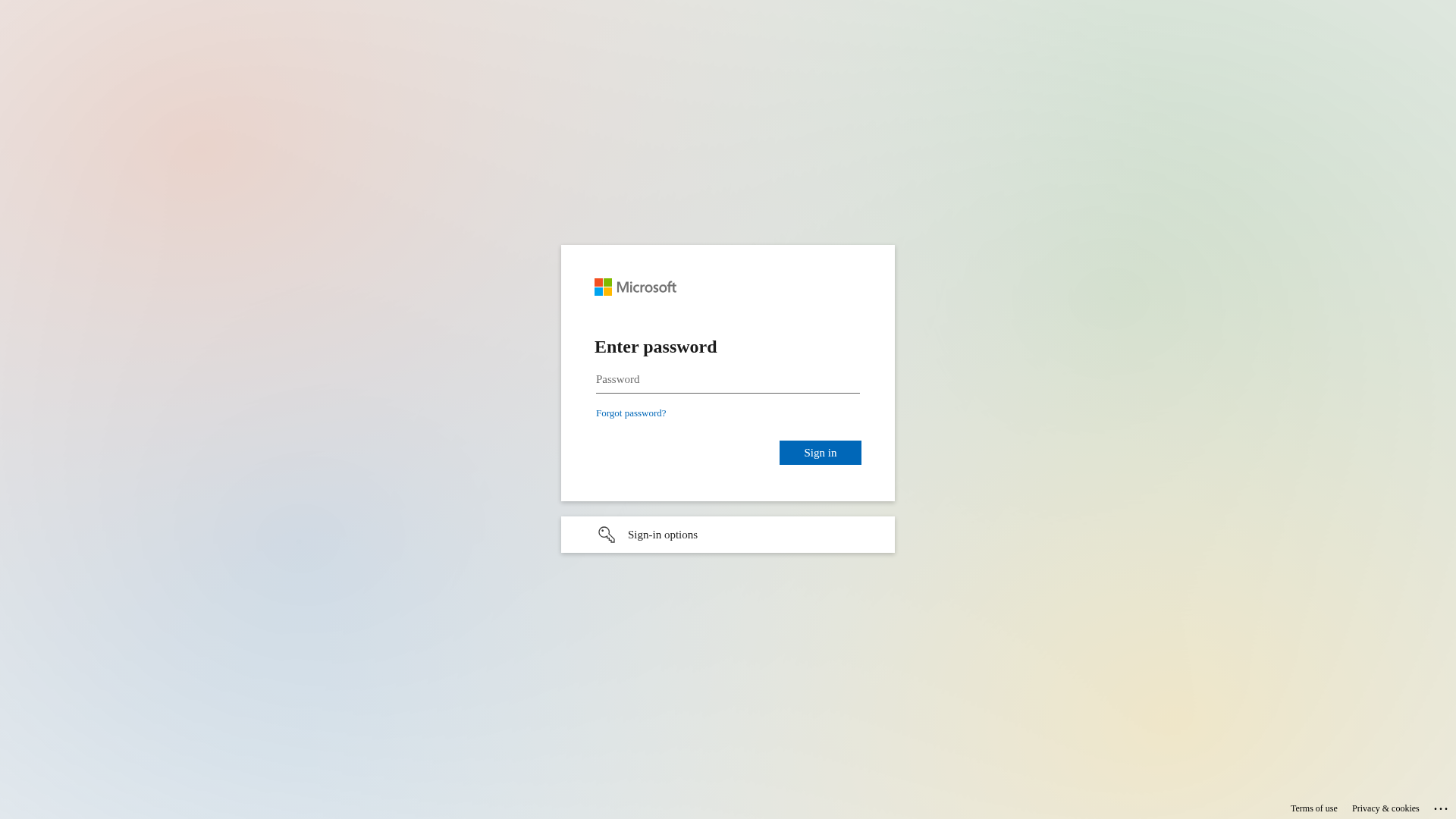
Visual Capture
Detection Info
https://signin.broker/lcaP_QQD3aYxE38XRA
Detected Brand
Nexi
Country
International
Confidence
100%
HTTP Status
200
Report ID
73c1fecf-ade…
Analyzed
2026-02-24 14:40
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T150D1007160509D3B4283C7D4B3B96B5F3394C346EA97565A67F8C38C0EE3E66CC1A226 |
|
CONTENT
ssdeep
|
96:nIpkCGTHRPyJkrwkM6ds39TbJG9KjsWsjOkq0U2gs0sjOkjOVJQ6Q6ynQjNsjOkY:9Yk8J9TbJG9apSOVJQyyQjn |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9c497326cc99d9e4 |
|
VISUAL
aHash
|
18001818191f0f9f |
|
VISUAL
dHash
|
7161713331727d38 |
|
VISUAL
wHash
|
191818181f1f1fff |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
7161713331727d38 |
Code Analysis
Risk Score
70/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Credential Harvesting
• Target: Nexi users
• Method: Phishing website
• Exfil: Compromised email addresses and password
• Indicators: External email domain, login form
• Risk: HIGH
🎯 Kit Endpoints
- https://passwordreset.microsoftonline.com/?ru=https://login.microsoftonline.com/common/oauth2/authorize?client_id=00000001-0000-cff1-ce00-615666661420&response_mode=form_post&response_type=code+id_token&scope=openid&msafed=1&msaredir=1&client-request-id=d98292e6-fa3f-ce32-5660-21bc5137cc6d&protectedtoken=true&domain_hint=nets.eu&nonce=928359376394.ec82d3ed-b372-7cd6-3e42-fcfc13352e79&state=c3ltZW9ua29uc3Quc3BhbGFzQGV4dGVybmFsLm5leGlncm91cC5jb20#
- https://login.microsoftonline.com/common/login#
- https://login.microsoftonline.com/common/oauth2/authorize?client_id=00000001-0000-cff1-ce00-640818305952&response_mode=form_post&response_type=code+id_token&scope=openid&msafed=1&msaredir=1&client-request-id=d98292e6-fa3f-ce32-6691-21bc5137cc6d&protectedtoken=true&domain_hint=nets.eu&nonce=505545635837.ec82d3ed-b372-7cd6-3e42-fcfc13352e79&state=c3ltZW9ua29uc3Quc3BhbGFzQGV4dGVybmFsLm5leGlncm91cC5jb20#
- https://login.microsoftonline.com/common/oauth2/authorize?client_id=00000001-0000-cff1-ce00-739902897354&response_mode=form_post&response_type=code+id_token&scope=openid&msafed=1&msaredir=1&client-request-id=d98292e6-fa3f-ce32-4571-21bc5137cc6d&protectedtoken=true&domain_hint=nets.eu&nonce=389797825437.ec82d3ed-b372-7cd6-3e42-fcfc13352e79&state=c3ltZW9ua29uc3Quc3BhbGFzQGV4dGVybmFsLm5leGlncm91cC5jb20#
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Credential Harvesting
The page is requesting a password with email address is external to the expected domain.
🔬 Comprehensive Threat Analysis
Threat Type
Two-Factor Authentication Stealer
Target
Nexi users (International)
Attack Method
Brand impersonation
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Personal Info
🏢 Brand Impersonation Analysis
Impersonated Brand
Nexi
Fake Service
Login
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker is attempting to steal user credentials by presenting a fake login form that mimics the appearance of the legitimate Nexi login portal.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
signin.broker
Registered
Unknown
Registrar
Unknown
Status
Unknown
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
DP World
https://signin.broker/yEXpO8mh47e1zQ
Apr 01, 2026
Copart
https://sso-security.com/hmoR7AjmD5_J9_rblw
Mar 31, 2026
Malta International Airport
https://sso-security.com/Z6nTr6YHvIOQYEcQ
Mar 31, 2026
Microsoft
https://l0gln-m1croqsoqftcom-1drvverfil3es.fwh.is/?i=1
Mar 31, 2026
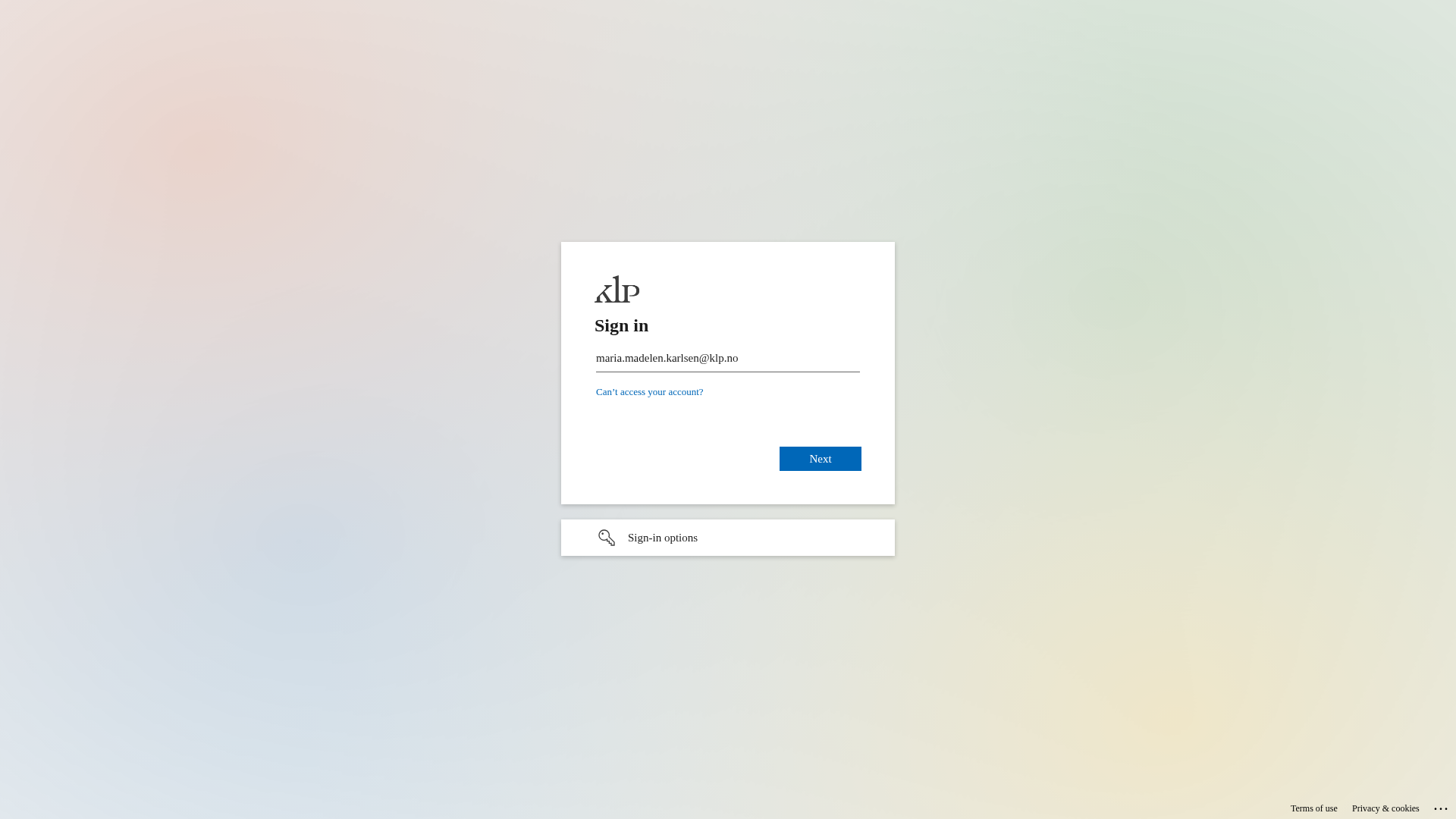
KLP
https://authentication.ms/Q0geWwh1if8
Mar 30, 2026
Scan History for signin.broker
Found 10 other scans for this domain
-
https://signin.broker/yEXpO8mh47e1zQ
https://signin.broker/5zVgHVxEiqRCA7A
https://signin.broker/6rdkQnvl4pM
https://signin.broker/JZkM5hhKcgDXzbIe
https://signin.broker/qZkR7_8L9uyvgQ
https://signin.broker/IgP0txnmBRyrcuFo
https://signin.broker/BqHpjz7odUsi
https://signin.broker/JxcO4CqSIq8qMA
https://signin.broker/ibvC2nuFhKniBQeO
https://signin.broker/205ozFHBMcc?/DZI/threads/898...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.