
Phishing Analysis
Detailed analysis of captured phishing page
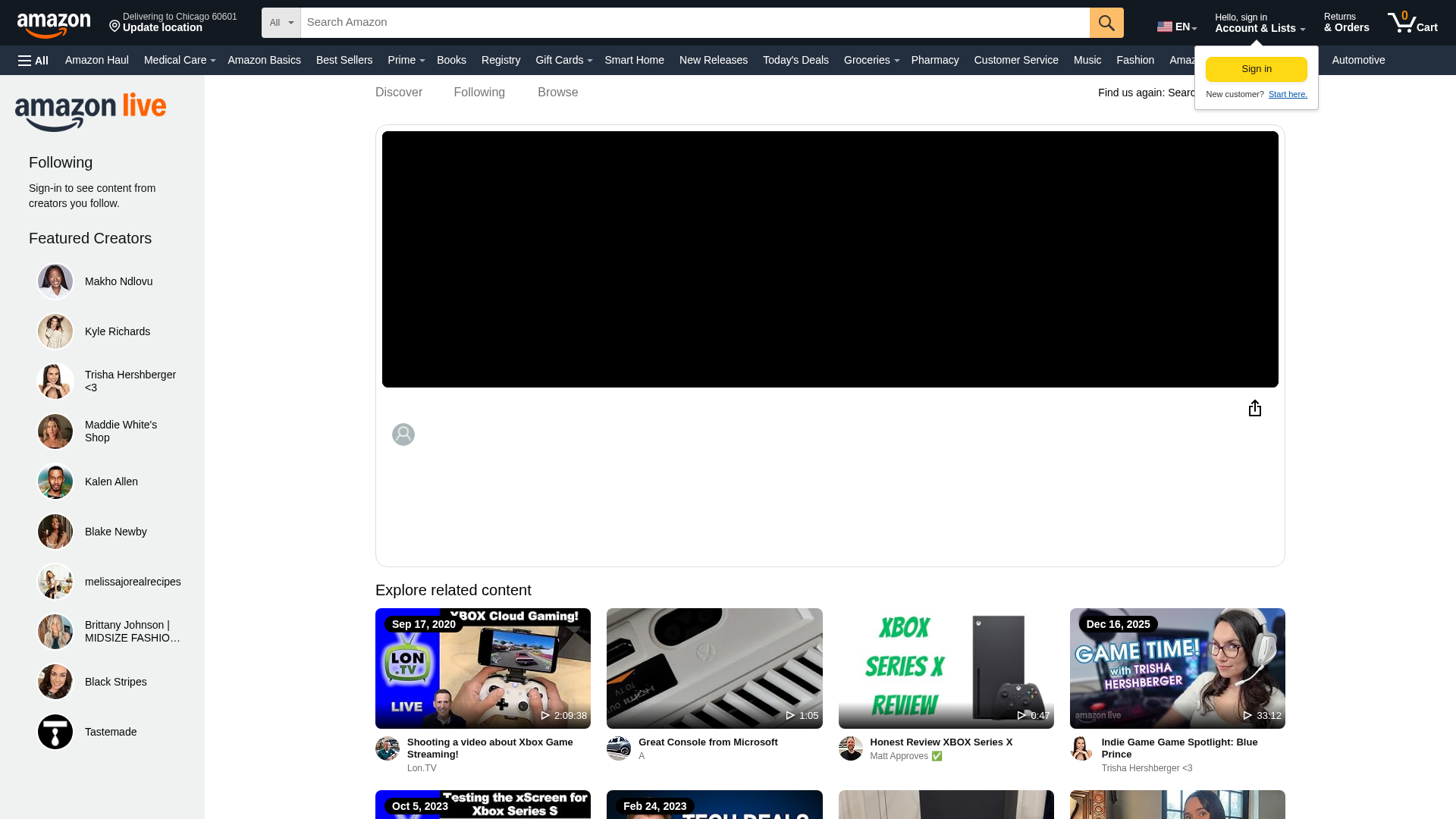
Visual Capture
Detection Info
https://link1-b24.pages.dev/live/video/0593e61138764ce79cf5afb2b4e59eec?ref_=dp_vse_rvc_7%2F
Detected Brand
Amazon
Country
USA
Confidence
100%
HTTP Status
200
Report ID
741765aa-cea…
Analyzed
2026-02-17 07:12
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T17A349331D5A41033052B2ACDF4B8B79DD7D3E38FDA4688C295E943A80BE1DA8B7365D4 |
|
CONTENT
ssdeep
|
1536:NN4tMzRTCP3tSMV1dB3QLmZZCdw1lToSiblsG1BslU4skPas/aos4cYsoAlsW8Fa:XcWRHu3QiDlUbgRg |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e8681797877a4743 |
|
VISUAL
aHash
|
38c1c1c1ffffcdff |
|
VISUAL
dHash
|
f8938393c099998b |
|
VISUAL
wHash
|
00c1c1c1ffffc1c9 |
|
VISUAL
colorHash
|
17207000000 |
|
VISUAL
cropResistant
|
8282c2d2d2828282,93938393c099998b,d0d9e8d8c80a922a,0000000000000000,36dea4a9ac6fe7a7,9fbab42870e1c38f,795d930c48191539,3333537353133333 |
Code Analysis
Risk Score
100/100
Threat Level
MEDIO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Amazon users
• Method: Impersonation via free hosting
• Exfil: Unknown
• Indicators: Free hosting and brand logo
• Risk: Medium
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://m.media-amazon.com/images/G/01/poppin/AmazonLive/2023_Apr_Jun/amazonlivelogo_whitebg_LeftJustified.png
- https://openjsf.org/
- https://unagi
- https://${(0,fe.d)(n,t)}/custom/vsevideodataaggregatorcontracts/amazon-api-vse`,o=ge.A.get(),s=yield
- https://d231gvmk20yd16.cloudfront.net/${e}.json`,a=yield(0,o.uj)(t),{response:n}=a;if(n&&200===n.status){const{data:{url:e}={}}=n;e&&u(e)}}catch(t){c.A.error(`Failed
- https://m.media-amazon.com/images/S/sash/iu3jwAvFfCbpMfl.js?name=app-desktop
- https://www.aboutamazon.com/?utm_source=gateway&utm_medium=footer&token=about
- https://m.media-amazon.com/images/G/01/follow/follow_button_sprite.png
- https://api.eu-west-1.prod.proxy.live.amazon.in/
- https://player.live-video.net/1.19.0/amazon-ivs-wasmworker.min.wasm
- https://m.media-amazon.com/images/I/81BXdoJ-FBL.js?AUIClients/FWCIMAssets
- https://unagi-cn.amazon.com
- /?ref_=footer_logo
- https://logistics.amazon.com/marketing?utm_source=amzn&utm_medium=footer&utm_campaign=home
- https://dl.amazon.com/redirect?url=${encodeURIComponent(e)}&customFallbackUrl=${encodeURIComponent(t)}&campaignId=${a}&failureMode=MobileWebMostly`)({url:s.toString(),customFallbackUrl:p.toString(),campaignId:
- http://tiny/c1mr5h0u
- https://in-pre-prod.amazon.com
- https://${(0,fe.d)(r,t)}/custom/asvmetadataaggregationservicecontracts/amazon-api-asv`,c=yield
- https://www.amazon.com
- https://email.aboutamazon.com/l/637851/2020-10-29/pd87g?utm_source=gateway&utm_medium=amazonfooters&utm_campaign=newslettersubscribers&utm_content=amazonnewssignup
- https://m.media-amazon.com/images/S/sash/pDxWAF1pBB0dzGB.woff2
- https://m.media-amazon.com/images/I/51FVzmwFLsL.js?AUIClients/FollowButtonWidgetAssets
- https://pr-keyos-twitch.licensekeyserver.com/core/rightsmanager.asmx
- https://lodash.com/
- /ref=nav_logo
- https://m.media-amazon.com/images/S/sash/KxsQ4i4lXiocHNA.js?name=353
- https://twitter.com/intent/tweet?text={text}&url={url}
- https://images-na.ssl-images-amazon.com/images/S/amazon-avatars-global/default._SX50_QL100_SCLZZZZZZZ_.png
- https://m.media-amazon.com/images/I/${o}.${l?
- https://m.media-amazon.com/images/G/01/shopbylook/shoppable-images/next_tab_control._CB416468320_.svg
- http://www.apache.org/licenses/LICENSE-2.0
- https://m.media-amazon.com/images/G/01/poppin/social_share_logo/icon_twitter.png
- https://m.media-amazon.com/images/I/21pj1OVABnL.js?AUIClients/ShareWidgetTriggerAssets
- https://tiny.amazon.com/hnqhhg9
- https://m.media-amazon.com/images/I/31hknpW-QwL.js?AUIClients/BotDetectionJSSignalCollectionAsset
- https://sustainability.aboutamazon.com/?utm_source=gateway&utm_medium=footer&ref_=susty_footer
- https://www.pinterest.com/pin/create/button/
📡 API Calls Detected
- GET
- POST
- https://9eya4arjbh.execute-api.us-east-1.amazonaws.com/prod/reportvideo
- https://
📤 Form Action Targets
- /s/ref=nb_sb_noss
- get
📊 Risk Score Breakdown
Total Risk Score
85/100
Contributing Factors
Free Hosting
The use of free hosting is a major red flag for phishing.
Brand Impersonation
The site is trying to look like Amazon.
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Amazon users (USA)
Attack Method
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
HTTP POST to backend
Risk Assessment
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 7453 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Amazon
Official Website
amazon.com
Fake Service
Amazon Live
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker likely wants to steal your Amazon login credentials. They use a website that looks like the Amazon login page to trick you into entering your username and password, which the attacker then collects.
🌐 Infrastructure Indicators of Compromise
🦠 Malicious Files
Main File
21fYSeFelaL.js
File Size
🔬 JavaScript Deep Analysis
Operator Language
English (1%)
Sophistication Level
Basic
Total Code Size
4.0 MB
🔗 API Endpoints Detected
Other
122
Telegram API
1
🔐 Obfuscation Detected
- : None
- : Heavy
- : Light
- : None
- : Light
- : Light
- : Moderate
- : None
- : Moderate
- : Light
- : Moderate
- : Moderate
- : Light
- : Light
- : Moderate
- : Heavy
- : Moderate
🤖 AI-Extracted Threat Intelligence
🎯 Malicious Files Identified
Main Drainer
21fYSeFelaL.jsFile Size
4071KB
Scan History for link1-b24.pages.dev
Found 6 other scans for this domain
-
http://link1-b24.pages.dev/playstation-pulse-3d-wi...
https://link1-b24.pages.dev/gp/css/homepage.html?r...
https://link1-b24.pages.dev/playstation-pulse-3d-w...
https://link1-b24.pages.dev/live/video/0593e611387...
http://link1-b24.pages.dev/playstation-pulse-3d-wi...
https://link1-b24.pages.dev/live/video/0593e611387...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.