
Phishing Analysis
Detailed analysis of captured phishing page
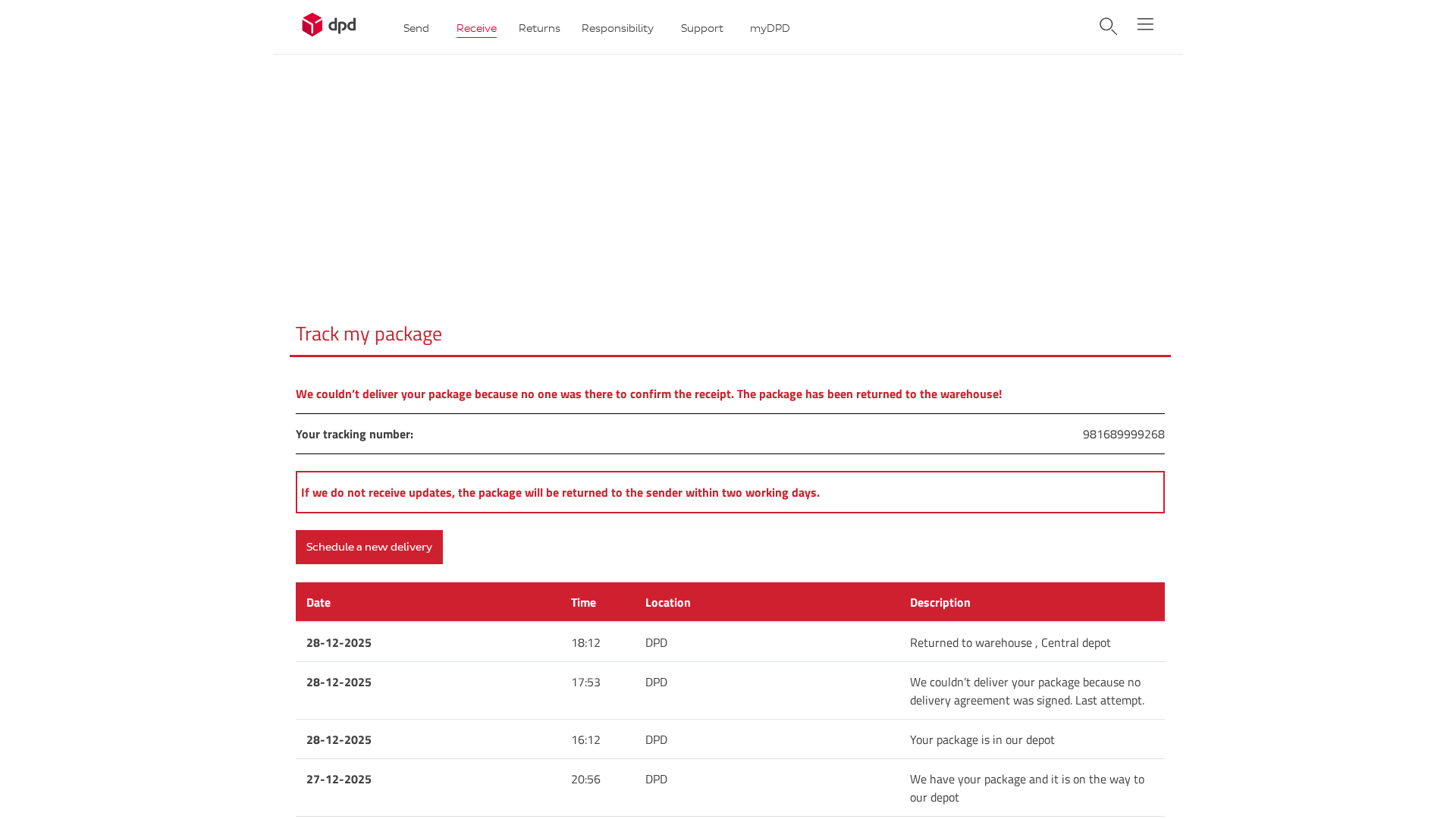
Visual Capture
Detection Info
https://138-68-183-9.cprapid.com/de/update.php
Detected Brand
DPD
Country
International
Confidence
100%
HTTP Status
200
Report ID
7545a659-969…
Analyzed
2025-12-31 06:47
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1A2B2027094B5B63F009F7391A7386709A3D39783CB520BE567F8936D4B8AE84DC23169 |
|
CONTENT
ssdeep
|
192:bixLoxwz77qKHv/ySchJrVUmZGko5XTCReWyRMOsUFf9kIT/JO:mx8xw7pvKpJrVUIGkc+TxFUH/JO |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
bcc3c33c83693cc3 |
|
VISUAL
aHash
|
ffffffc3df8181ff |
|
VISUAL
dHash
|
39000027292b1342 |
|
VISUAL
wHash
|
8fffff8181818189 |
|
VISUAL
colorHash
|
07000000007 |
|
VISUAL
cropResistant
|
39000027292b1342,0000db6464649b24 |
Code Analysis
Risk Score
90/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 Banking
🔬 Threat Analysis Report
• Threat: Package delivery scam using DPD branding.
• Target: Customers expecting DPD deliveries.
• Method: Claims undeliverable package and urges scheduling new delivery via a malicious link.
• Exfil: Potentially redirects to a form requesting personal information or payment details.
• Indicators: IP address URL, brand impersonation, generic 'undeliverable package' scam.
• Risk: HIGH - May lead to personal data theft and financial loss.
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
🎯 Kit Endpoints
- ./app/wp-content/themes/DPD_Login/css/styles.min5b21.css?ver=6.0.2
📡 API Calls Detected
- POST
- https://whos.amung.us/stats/
- GET
📤 Form Action Targets
- date.php
- #
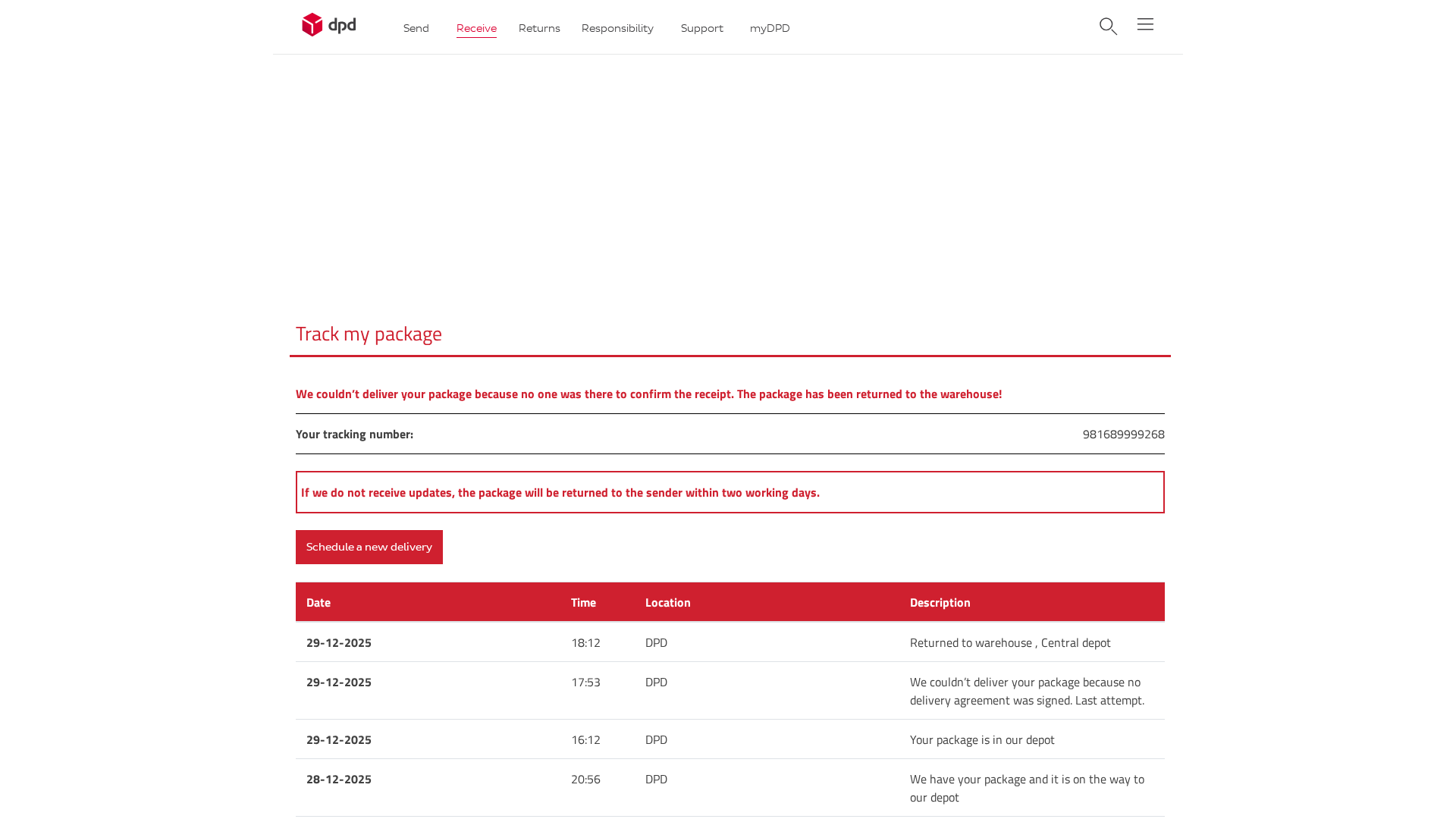
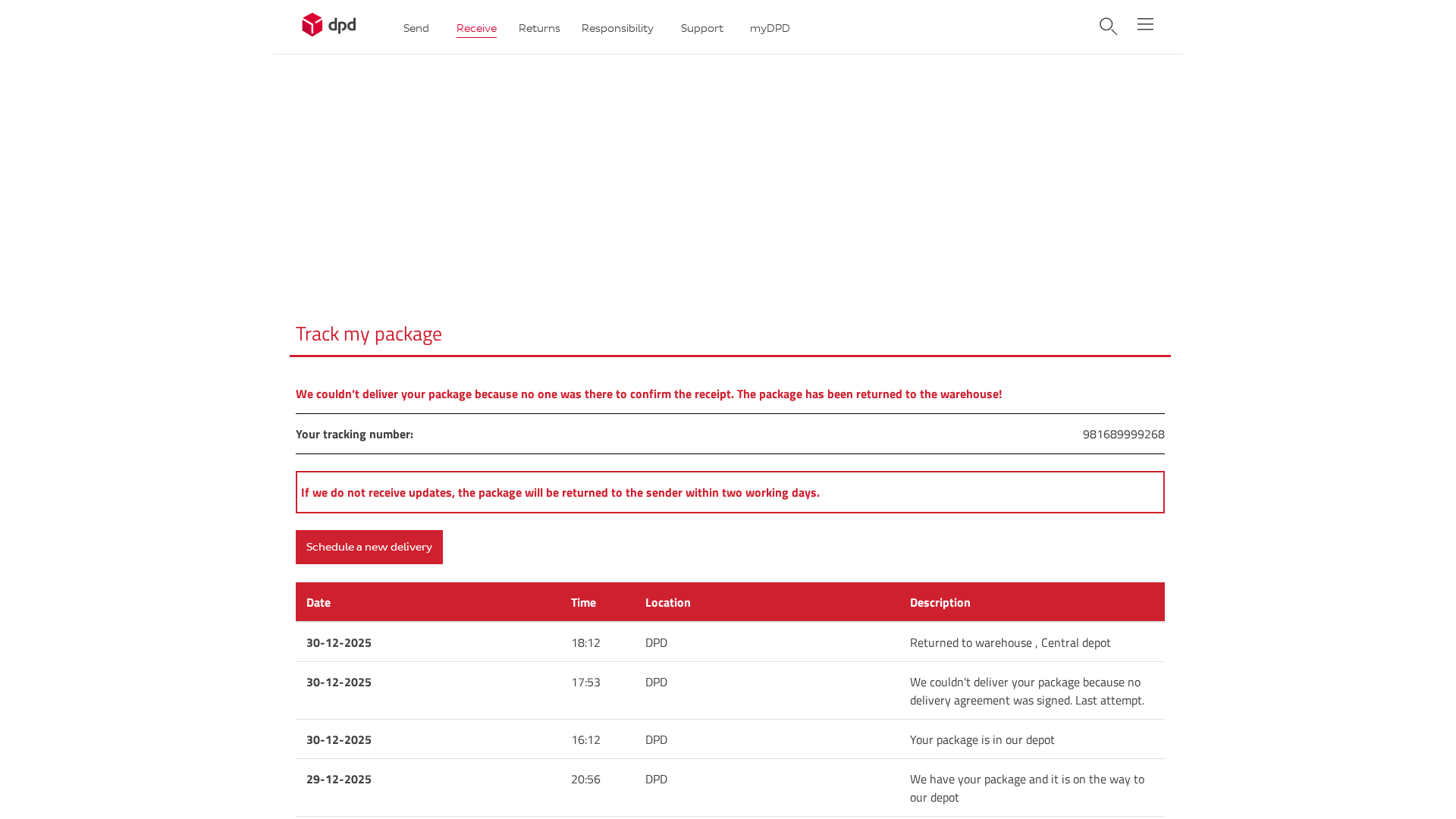
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
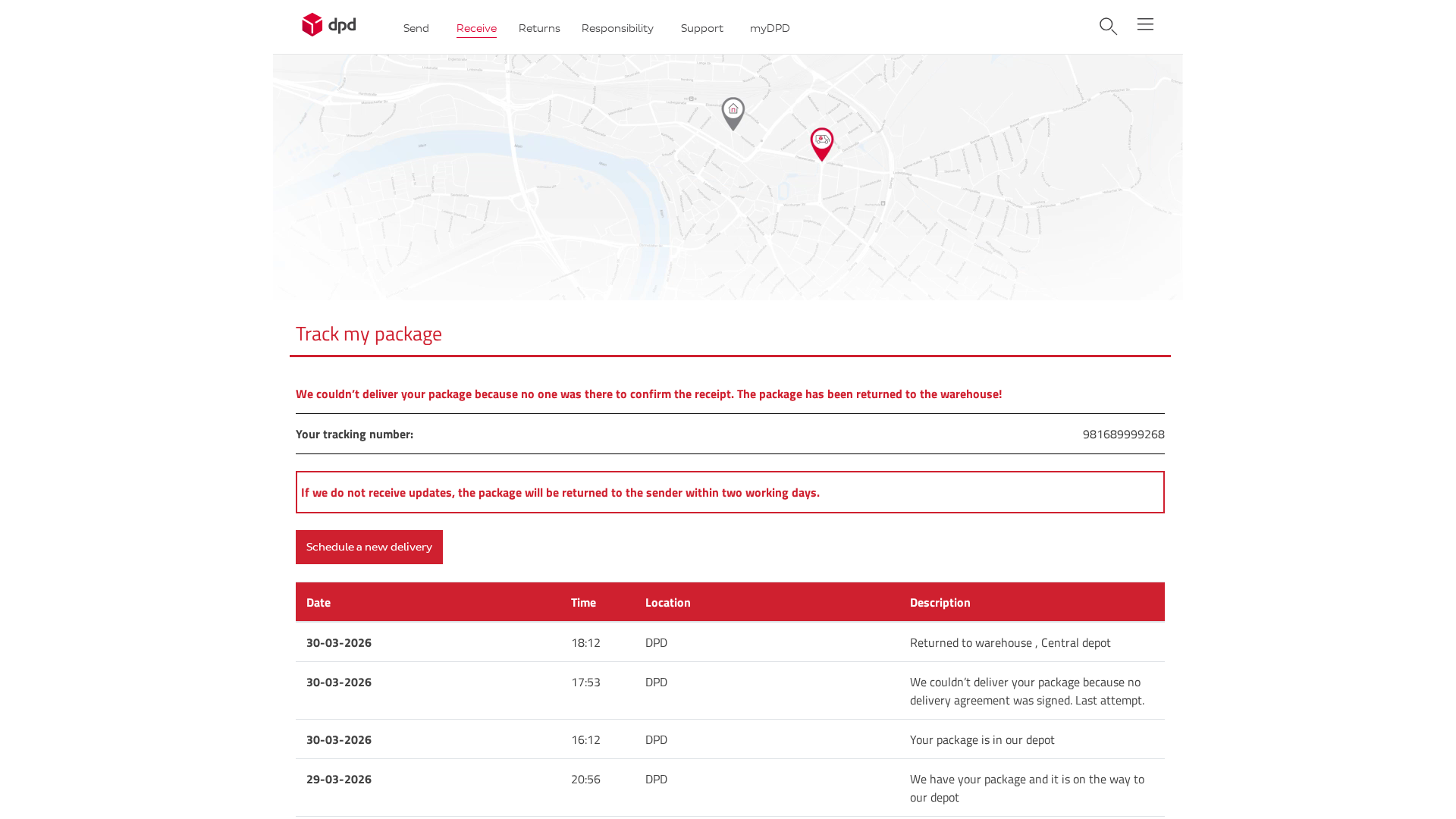
DPD
https://161-35-72-148.cprapid.com/dpd/update.php?vqc2lgxt4kr...
Mar 31, 2026
DPD
https://212-227-48-175.cprapid.com/de/update.php
Jan 07, 2026
No screenshot
DPD
https://138-68-183-9.cprapid.com/de/update.php
Dec 31, 2025
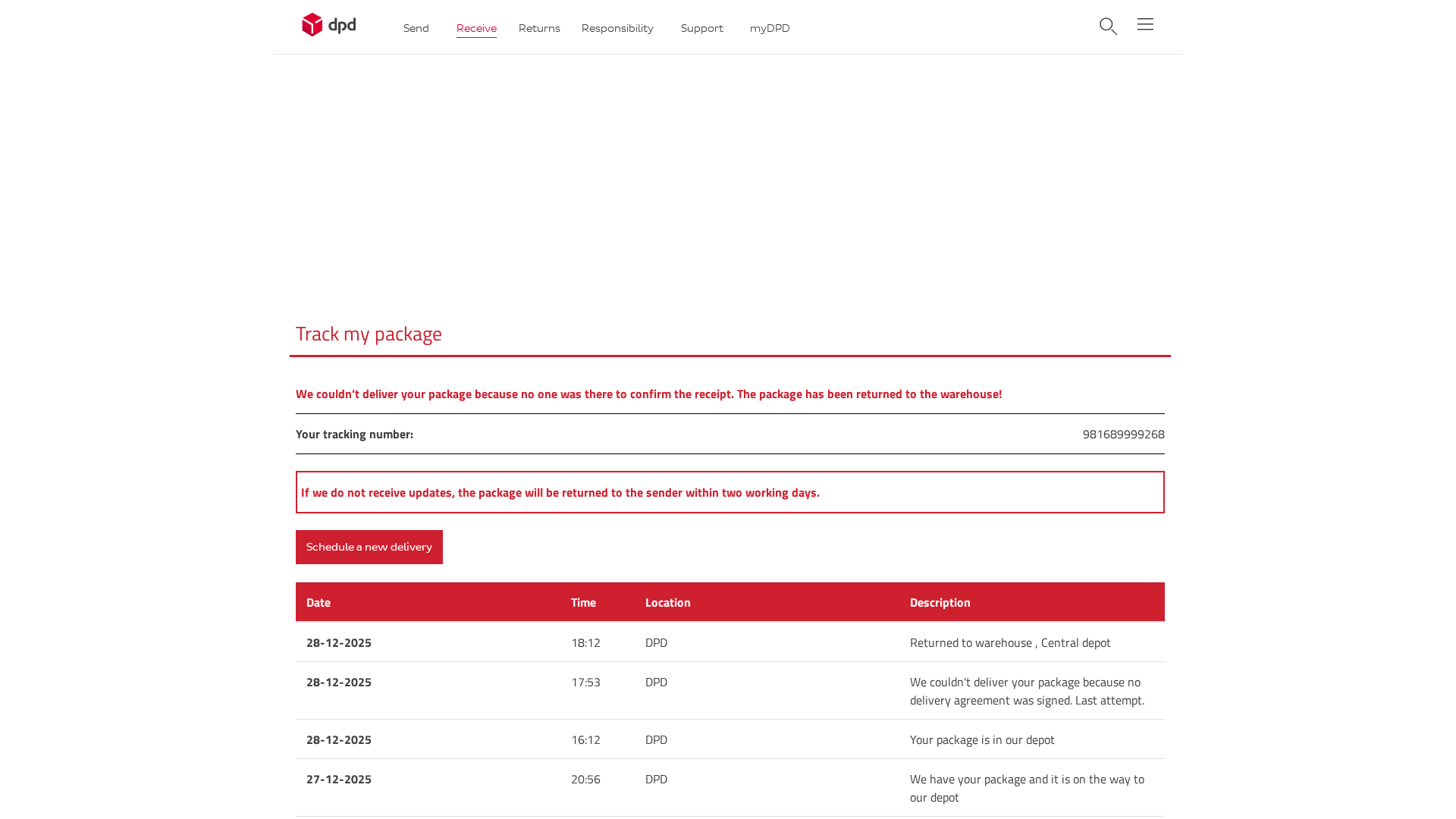
DPD
https://217-160-164-192.cprapid.com/de/update.php?g1hdiel1pc...
Dec 30, 2025
DPD
https://69-164-193-72.cprapid.com/de/update.php
Dec 30, 2025
Scan History for 138-68-183-9.cprapid.com
Found 6 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.