
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
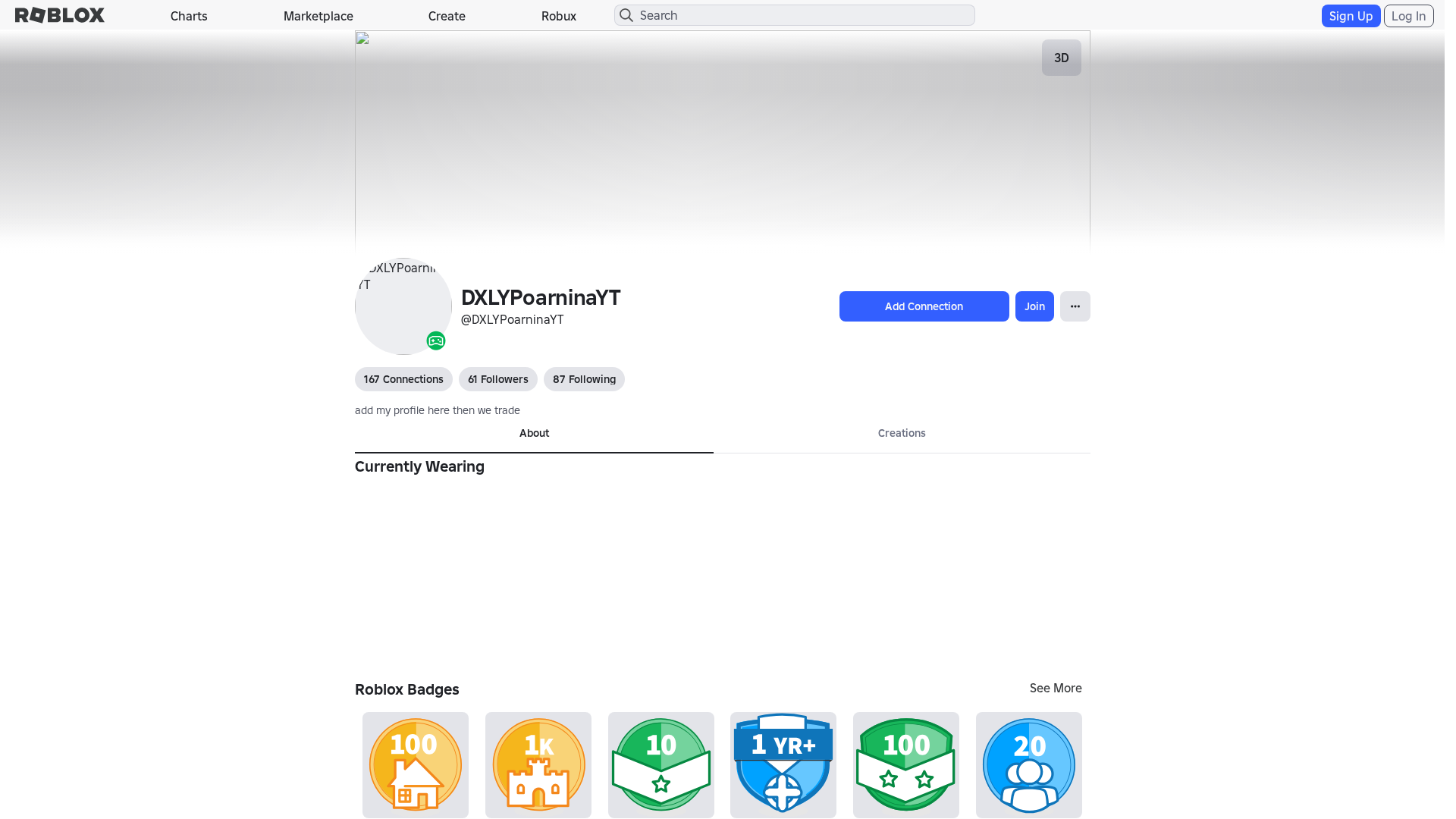
Detection Info
http://www.robloxt.co/users/2021794753/profile/
Detected Brand
Roblox
Country
International
Confidence
100%
HTTP Status
200
Report ID
75832fa6-888…
Analyzed
2026-02-11 23:49
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T11693B9B29251243320BFB1D5F1297709A2D3D74EC68287D1E2FCA36B1ED6CA1F817856 |
|
CONTENT
ssdeep
|
1536:uAEXWnSracJuOKRorHBPmzzXXMd6MiucCOK:vEXWdcJuOf5mzzXXMd6M1cCOK |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
ec19669334cde592 |
|
VISUAL
aHash
|
0000fbdbffffffc3 |
|
VISUAL
dHash
|
f0e8963638002606 |
|
VISUAL
wHash
|
000042c3dfffdfc3 |
|
VISUAL
colorHash
|
072000082c0 |
|
VISUAL
cropResistant
|
f0e8963638002606 |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Impersonation
• Target: Roblox users
• Method: Typosquatting
• Exfil: Potentially credentials or account information
• Indicators: Typosquatted domain, similar visual layout
• Risk: HIGH
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://trades.
- https://js.rbxcdn.com/c55290a7a9b53c3a9097db6781f8b4e6.js
- https://en.help.roblox.com/hc/
- https://search.
- https://voice.
- /catalog
- https://feross.org
- /login?returnUrl=
- https://api.
- https://itemconfiguration.
- https://inventory.
- https://tarobi-dev-test.com
- https://js.rbxcdn.com/5c8a2ba3737908f693394045e81ebd71c77cde6f87550ea51f7833e8c98200ae.js
- https://engagementpayouts.
- https://feross.org/opensource
- https://roblox.com
- https://followings.
- /login?returlUrl=2021794753
- https://chat.
- https://sourcemaps.rbxcdn.com/internationalCore-db1cf6cdaa102b16.js.map
- https://тест
- https://presence.
- https://catalog.
- https://accountsettings.
- https://js.rbxcdn.com/a3fe79f1bfdd96b7f0ad20eab2de7a05.js
- https://a
- https://app.lightstep.com
- https://sourcemaps.rbxcdn.com/translationResources-69e5843ef57e17f4.js.map
- https://a/c%20d?a=1&c=3
- https://js.rbxcdn.com/df687479f6a19a6541dc4c819b900ac9b19bef72681f89040066b80bf8f82c15.js
- https://js.rbxcdn.com/964fdc5ae2518a2c9c9d73f67eee026b844e68c2d3791ac6c8e28c0f979a3854.js
- https://mui.com/production-error/?code=
- https://tarobi-dev-sandbox.com
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://www.roblox.com/info/blog?locale=en_us
📡 API Calls Detected
- https://help.roblox.com/hc/articles/30428367965460
- get
- https://ro.blox.com/Ebh5?
- POST
- GET
- https://apis.
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Domain Typosquatting
The domain name is very similar to a popular brand (Roblox), increasing the chance of confusion.
Recent Domain
The domain is recently registered, a common practice used by attackers.
Obfuscation
Code obfuscation attempts to hide malicious behavior.
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Roblox users (International)
Attack Method
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
HTTP POST to backend
Risk Assessment
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 163 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Roblox
Official Website
https://www.roblox.com/
Fake Service
Roblox User Profile
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker likely aims to steal user credentials by mimicking the Roblox interface to capture login information if a fake login page is presented.
Secondary Method: Potential Malware Distribution.
The presence of obfuscated javascript code can be a indicator of a attempt to inject malicious code to the user's computer.
🌐 Infrastructure Indicators of Compromise
🦠 Malicious Files
Main File
0c2a7c793ed0761b93b214956992ffb44014abcb404fd8bd2f9a7eb32ea0a600.js
File Size
🔬 JavaScript Deep Analysis
Operator Language
English (1%)
Total Code Size
3.8 MB
🔗 API Endpoints Detected
Other
108
🔐 Obfuscation Detected
- : None
- : Light
- : Heavy
- : None
- : None
- : Light
- : None
- : None
- : None
- : Light
- : Light
- : None
- : Light
- : None
- : Heavy
- : None
- : Heavy
- : Light
- : Heavy
- : None
🤖 AI-Extracted Threat Intelligence
🎯 Malicious Files Identified
Main Drainer
0c2a7c793ed0761b93b214956992ffb44014abcb404fd8bd2f9a7eb32ea0a600.jsFile Size
3855KB
Scan History for www.robloxt.co
Found 10 other scans for this domain
-
http://www.robloxt.co/users/241551989/profile/
http://www.robloxt.co/users/1927163377/profile/
http://www.robloxt.co/users/241551989/profile/
https://www.robloxt.co/users/2021794753/profile/
http://www.robloxt.co/communities/410369504/
https://www.robloxt.co/login?returlUrl=1662831989
https://www.robloxt.co/charts
https://www.robloxt.co/users/1662831989/profile
http://www.robloxt.com.es/users/1832287491/profile...
http://www.robloxt.com.es/users/1219671190/profile...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.