
Phishing Analysis
Detailed analysis of captured phishing page
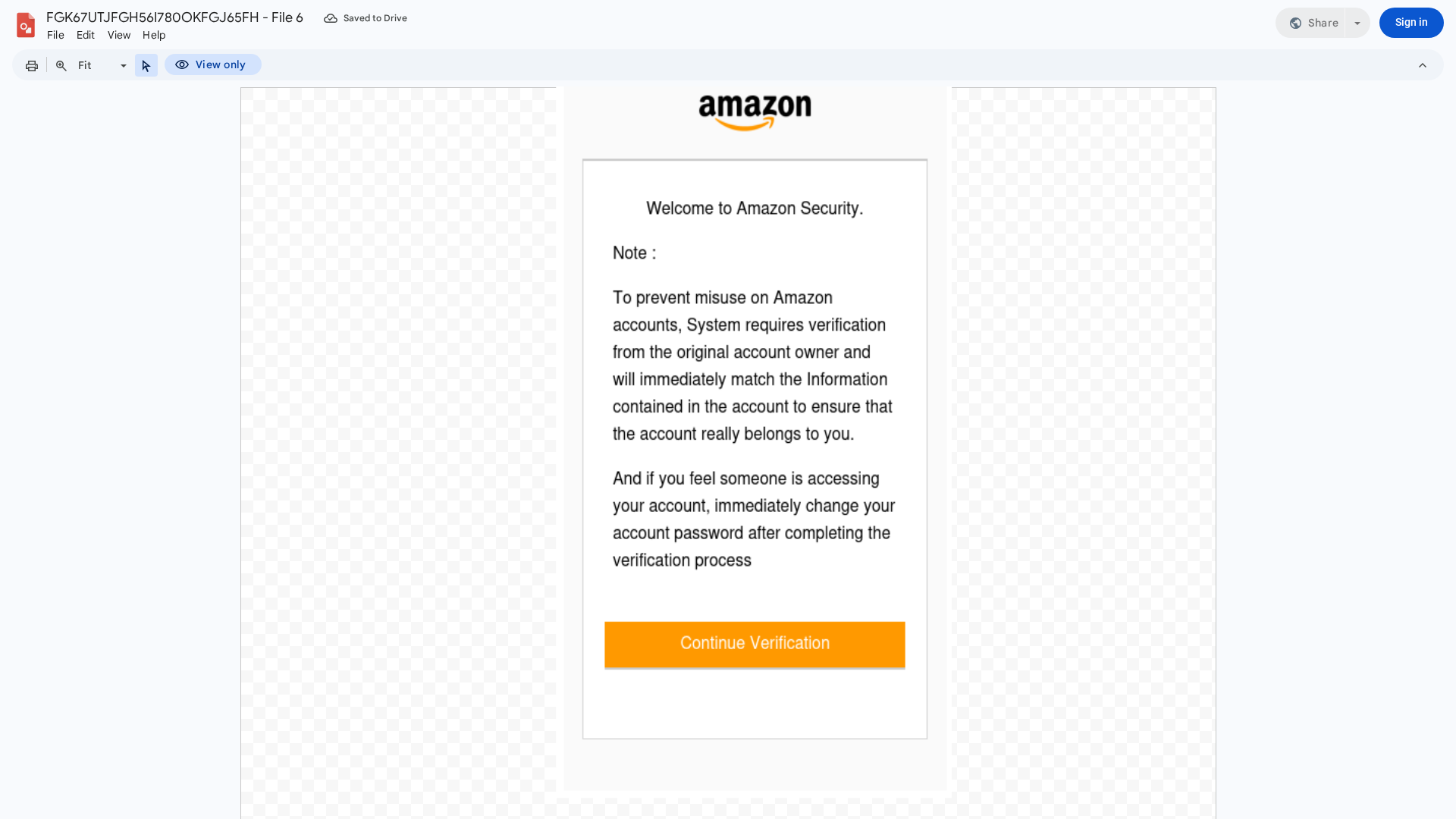
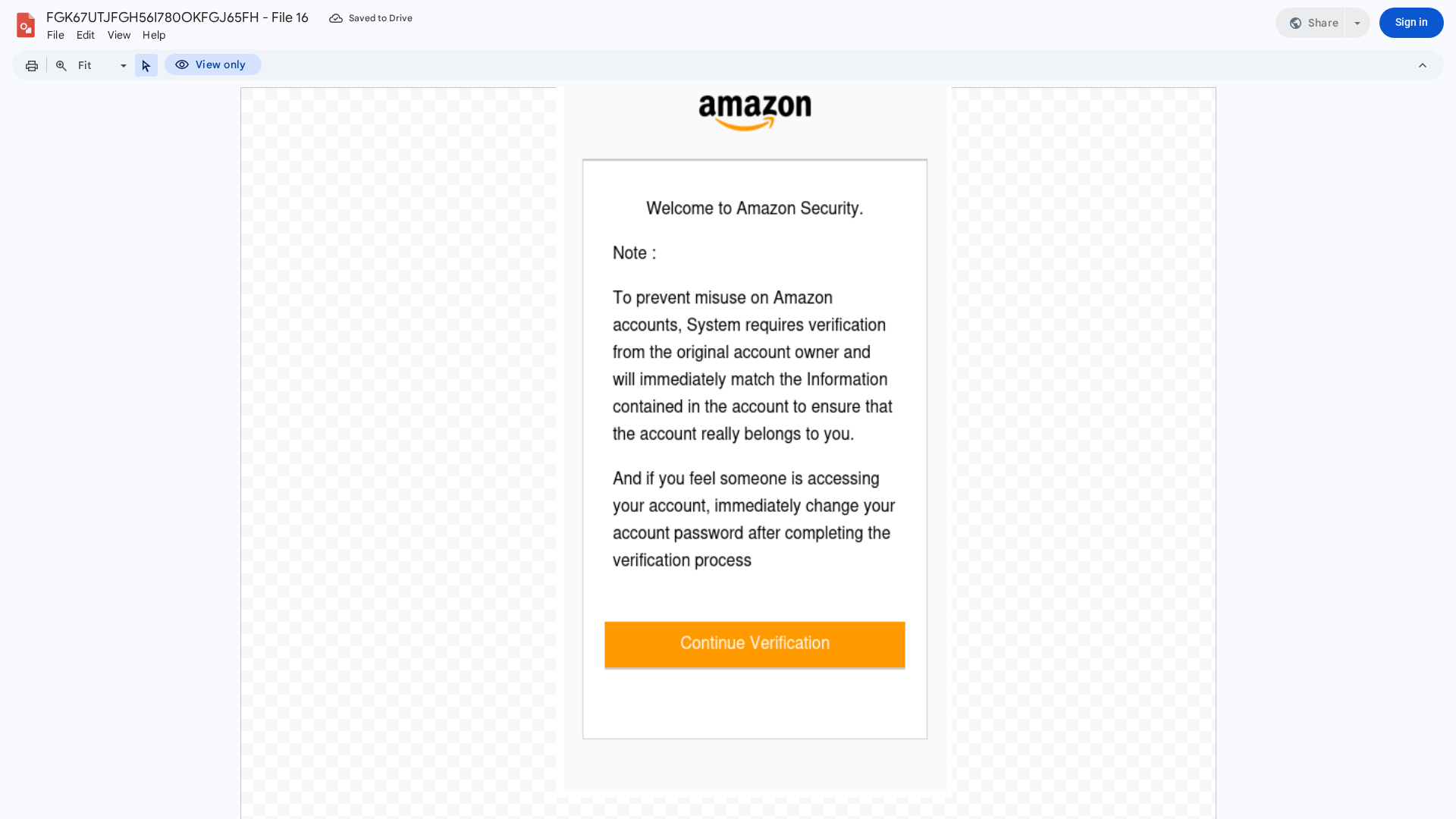
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1D3131133C0132132525B52E9F8A0775A2293C31EDE4708491B7CDB913BFBDAA7987A5D |
|
CONTENT
ssdeep
|
768:gURm/CCiwL5t/DVDJ6a+co6v+c6o4IE/Irb5dEoGEqOzVWsPk6TRC1mX6nwCTT:vRmaCDL5t/1J6fco6Gc6o4L/Irb5dEoI |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e6151d071575995d |
|
VISUAL
aHash
|
26e7efe7e7e7e7ff |
|
VISUAL
dHash
|
ec4d4c4c4c4c4c70 |
|
VISUAL
wHash
|
0066e6e66666667e |
|
VISUAL
colorHash
|
07000030000 |
|
VISUAL
cropResistant
|
ec4d4c4c4c4c4c70 |
Code Analysis
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- document.write
- hex_escape
- unicode_escape
- base64_strings
📡 API Calls Detected
- ol
- kbd
- a
- /videos/u/0/debug/fetchmediafromfilestorage?mediaId=
- p
- footer
- li
- td
- POST
- h2
- GoogleDocs
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 925 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 925 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for docs.google.com
Found 10 other scans for this domain
-
https://docs.google.com/drawings/d/1sj4whBVnBiYbBM...
https://docs.google.com/drawings/d/1yLlUaHnTsx9QSl...
https://docs.google.com/drawings/d/1HkX3Q8Vmr0bSej...
https://docs.google.com/drawings/d/1RCgegAUJGIZOBP...
https://docs.google.com/drawings/d/18Q2Qo6ik56ER5d...
https://docs.google.com/drawings/d/1LyvbqGTLtDzf81...
https://docs.google.com/drawings/d/1QKtwKh3JuUaEHs...
https://docs.google.com/drawings/d/1fL_fne4OgKiCLk...
https://docs.google.com/drawings/d/16f_LOTLDkqMT1D...
https://docs.google.com/drawings/d/11hOe-NpeBFsnAL...
