
Phishing Analysis
Detailed analysis of captured phishing page
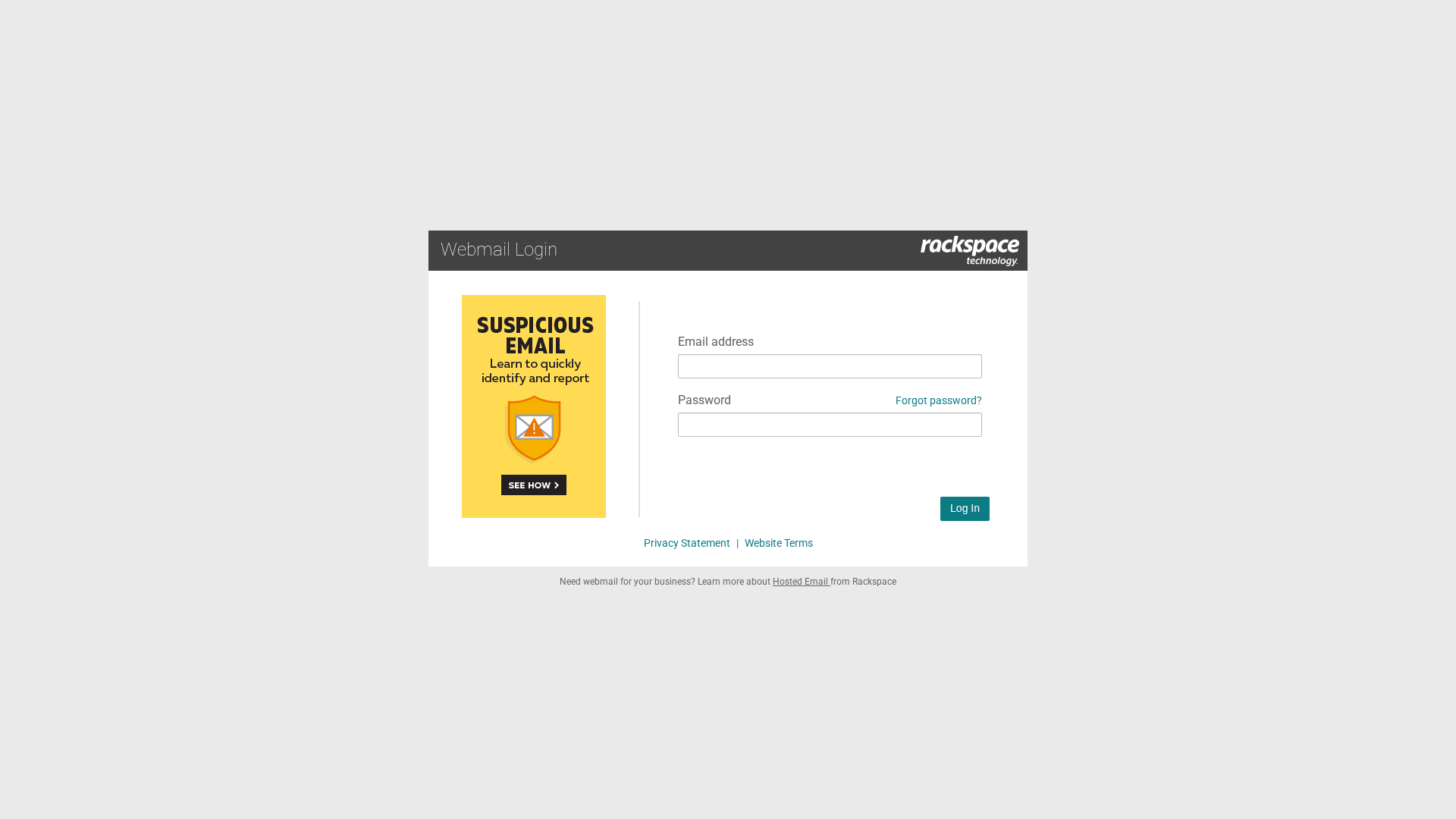
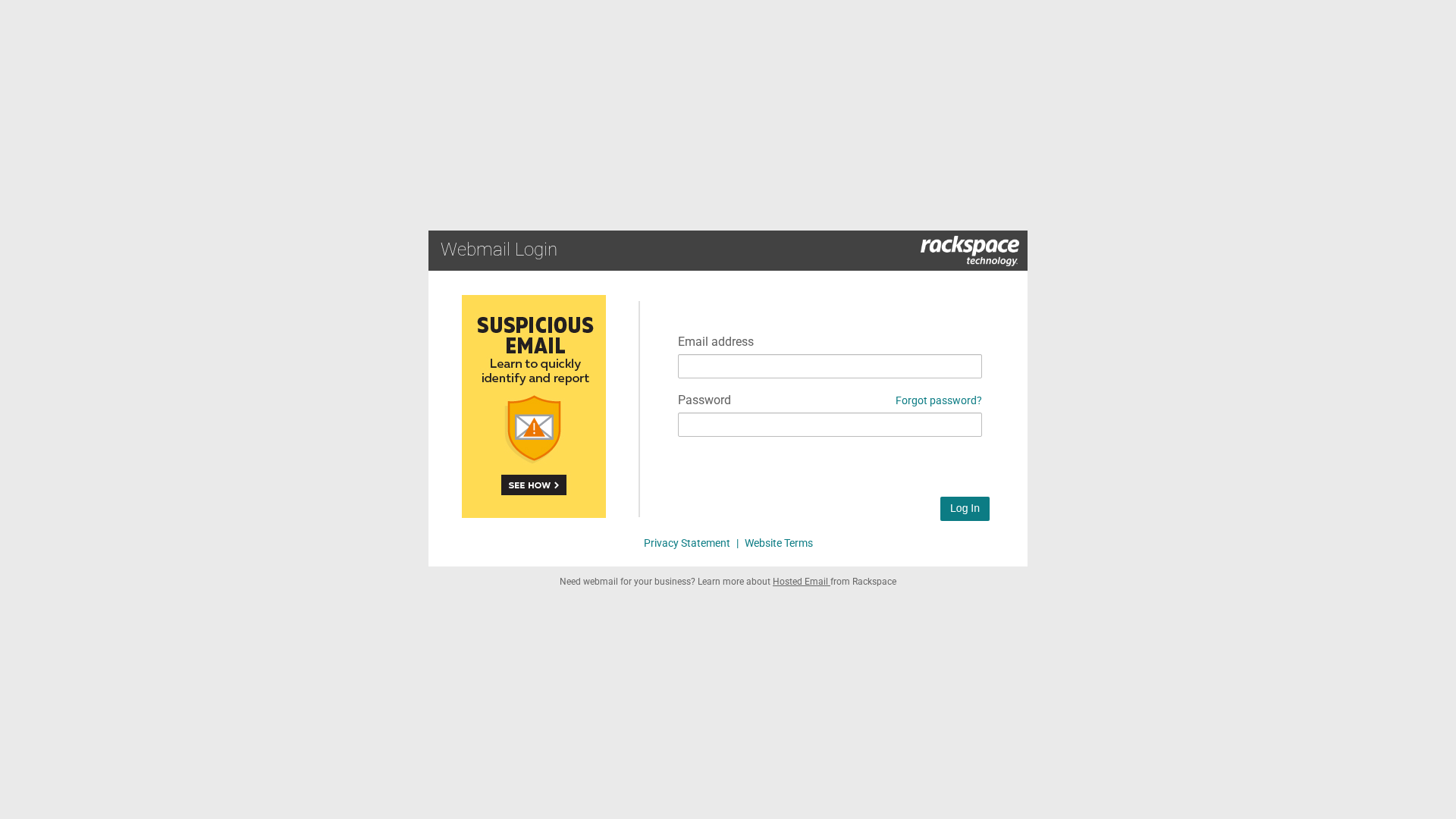
Visual Capture
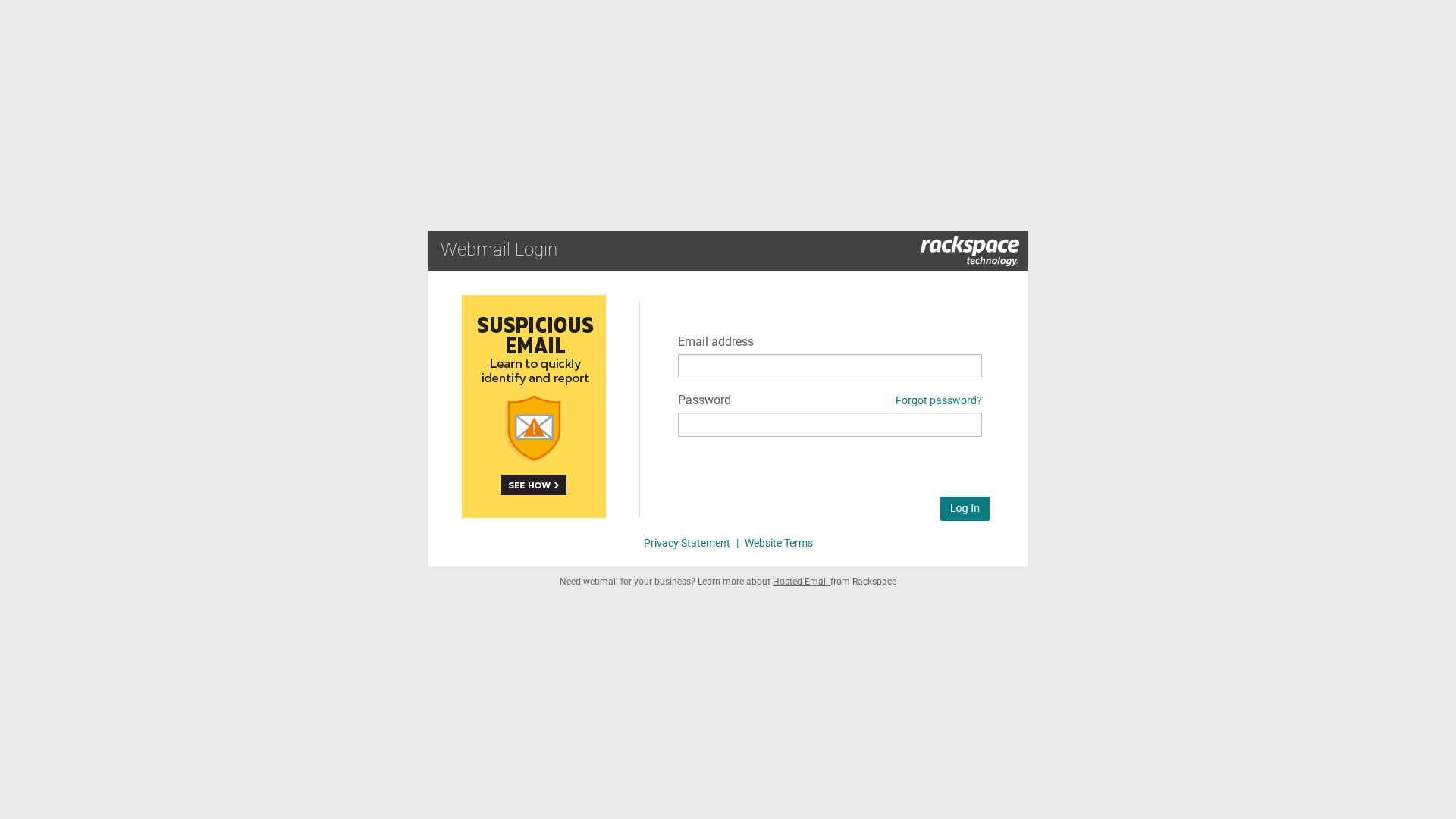
Detection Info
https://eu.orbitor.dev/ipfs/bafkreihujo3bmunbephpn7m6jfuctzqs4s4o55rhftb3gg3gojv2csr6ue/
Detected Brand
Rackspace
Country
International
Confidence
100%
HTTP Status
200
Report ID
784da821-f7f…
Analyzed
2026-02-27 06:19
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1FF5112704068EC239642DAD0BBF9EF1E6249C365CB035B4992F4938D1EC6D82CD5A6FD |
|
CONTENT
ssdeep
|
48:7/wULTHn5fBtWWxIS9u9oFWgid33f+fgTbQbgefUVbqn9BL:nn9xNFWge/+Yesw9J |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b130c6cf99336475 |
|
VISUAL
aHash
|
ffe3c3cfdfffffff |
|
VISUAL
dHash
|
20069e9990780c00 |
|
VISUAL
wHash
|
f0f0c0cc1c3c3030 |
|
VISUAL
colorHash
|
07000030000 |
|
VISUAL
cropResistant
|
20069e9990780c00,004b0b0b0b81c301 |
Code Analysis
Risk Score
68/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Rackspace users
• Method: Credential Harvesting
• Exfil: Unknown (atob obfuscation suggests data is being sent)
• Indicators: Mismatched domain, login form.
• Risk: High
🔒 Obfuscation Detected
- atob
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Domain Mismatch
The domain eu.orbitor.dev is not the official Rackspace domain.
Presence of a login form
A login form is present on a suspicious domain.
Obfuscation
atob obfuscation detected - increased risk of malicious activity
JavaScript Form Submission
JavaScript is being used to submit the form, which is common in phishing attacks
🔬 Comprehensive Threat Analysis
Threat Type
Two-Factor Authentication Stealer
Target
Rackspace users (International)
Attack Method
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer
- 1 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Rackspace
Official Website
rackspace.com
Fake Service
Webmail Login
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The site attempts to steal Rackspace login credentials by presenting a fake login form on a malicious domain. The obfuscation is likely used to hide the data exfiltration method.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
eu.orbitor.dev
Registered
Unknown
Registrar
Unknown
Status
Unknown
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Unknown
http://ipfs.io/ipfs/bafybeibscpr6fccaljtamoq5ivu4ahrv4wgm5jx...
Mar 13, 2026
Rackspace
https://bafkreifvsvj7pzsn5wsb6gt3onj7ez2rvxgdvrhybg47gxzwg6a...
Feb 28, 2026
Rackspace
https://bafkreifvsvj7pzsn5wsb6gt3onj7ez2rvxgdvrhybg47gxzwg6a...
Feb 28, 2026
Rackspace
https://bafkreihujo3bmunbephpn7m6jfuctzqs4s4o55rhftb3gg3gojv...
Feb 27, 2026
Rackspace
https://apac.orbitor.dev/ipfs/bafkreihujo3bmunbephpn7m6jfuct...
Feb 27, 2026
Scan History for eu.orbitor.dev
Found 7 other scans for this domain
-
https://eu.orbitor.dev/ipfs/bafkreihxkhc3zqivf7yc4...
https://eu.orbitor.dev/ipfs/bafkreietmq2owe4mmr4ol...
https://eu.orbitor.dev/ipfs/bafkreihxkhc3zqivf7yc4...
https://eu.orbitor.dev/ipfs/bafybeib3akl4qjotpnzpk...
https://eu.orbitor.dev/ipfs/bafkreiawyallprtg2yz32...
https://eu.orbitor.dev/ipfs/bafkreiczdadxptbewxsum...
https://eu.orbitor.dev/ipfs/bafkreiczdadxptbewxsum...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.