
Phishing Analysis
Detailed analysis of captured phishing page
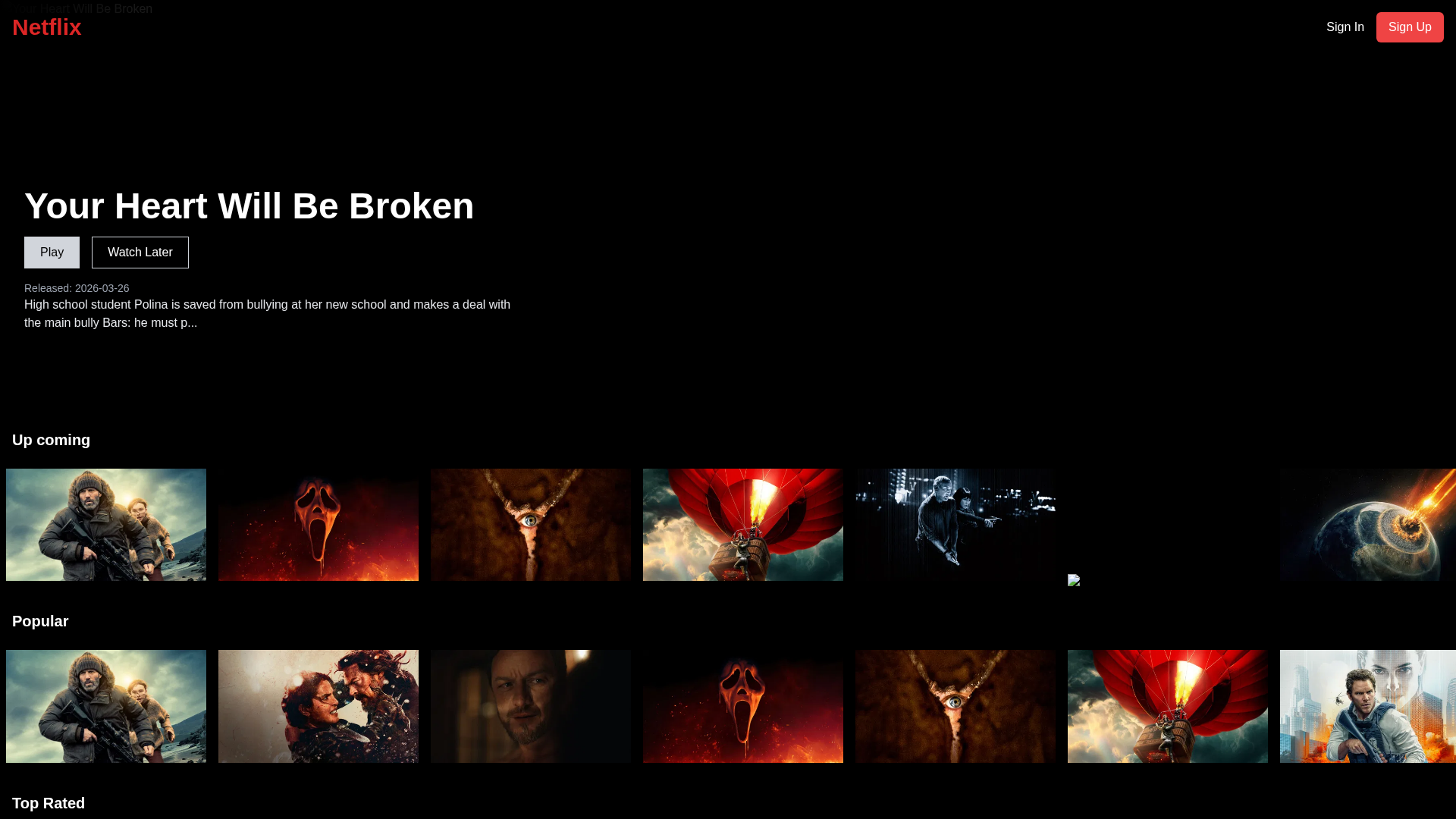
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T114040BA863135663950B03F4EB31A27F729FD2CEE0671B68D718C8733A9C4D85921ADD |
|
CONTENT
ssdeep
|
768:ujJYjqYjt0cFbjf1mXVZgfrZWjL4exuX+Fbyxg3fYtFjyCtOI8Ezku/SKXQB4ykZ:mu+2pPYe4rliCc9J5H4Jm60HO2 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
fa47a0ca16a05efa |
|
VISUAL
aHash
|
0000c00099d9e7cf |
|
VISUAL
dHash
|
0180010031318f17 |
|
VISUAL
wHash
|
0140e000fdf9efef |
|
VISUAL
colorHash
|
30400018000 |
|
VISUAL
cropResistant
|
e74e5e4d4d0dcc4e,0180010031318f17 |
Code Analysis
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- unicode_escape
- base64_strings
☁️ Cloud Backend
- Firebase: netflix-nextjs-37f55.firebaseapp.com
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking
- 57 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 57 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Scan History for netflix-clone-psi-seven.vercel.app
Found 2 other scans for this domain
