
Phishing Analysis
Detailed analysis of captured phishing page
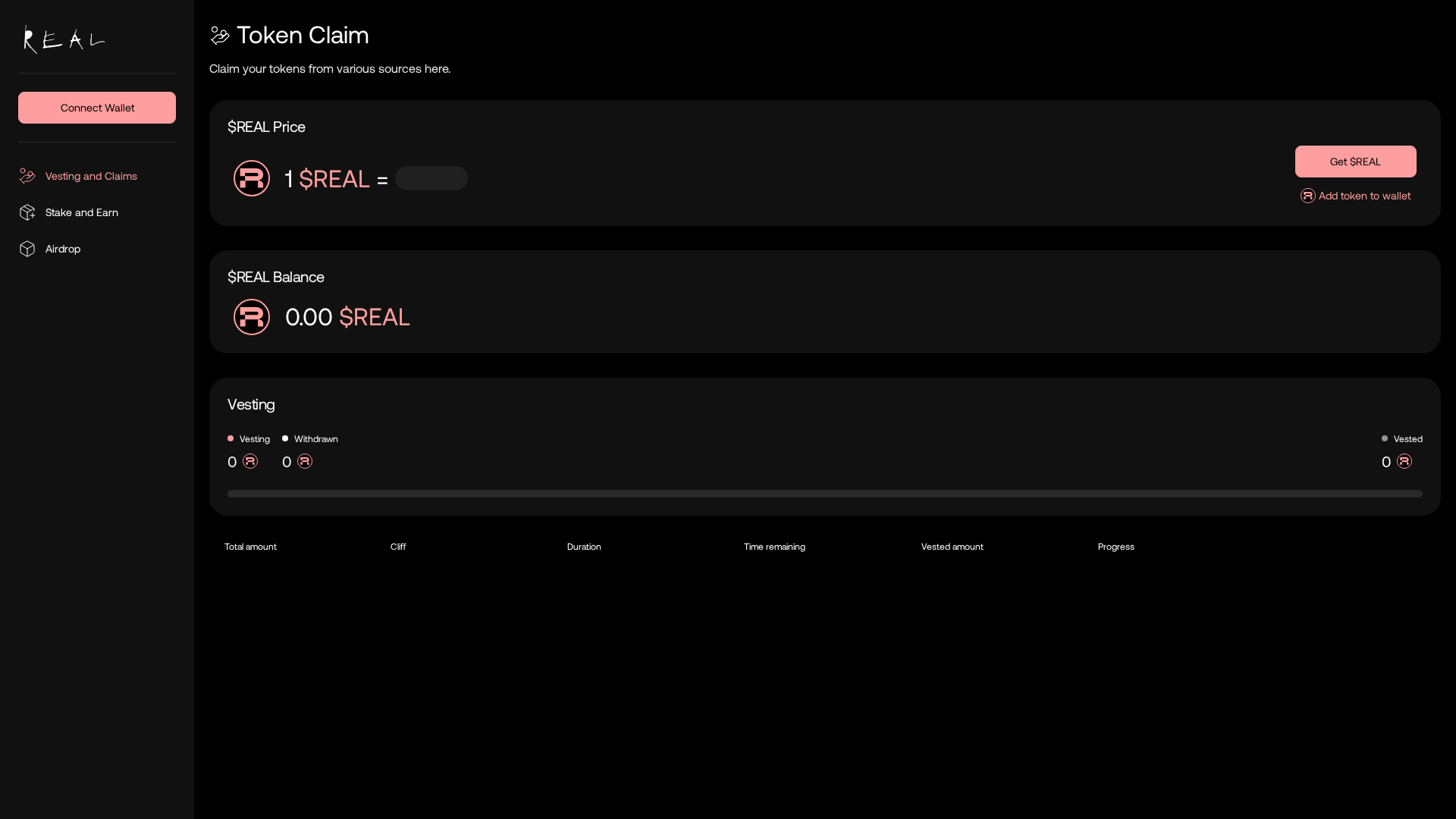
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1C6934BE83258B22B597383AB50EE31037279521B580D4D20A258ED9EF6F8C5FB067FD5 |
|
CONTENT
ssdeep
|
768:dDyuVaSbqe7wayKS4UfINc2iRaZls02bybMdN/zgsk0Y16JPYLOT6CHoZuGOjjg6:J1eAbU1RSs02ObI/i3UwLVCcuGOjjRn3 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
ffe97f7c50545000 |
|
VISUAL
aHash
|
c0ffffffff808080 |
|
VISUAL
dHash
|
0003918091100000 |
|
VISUAL
wHash
|
c0ffd0feff808080 |
|
VISUAL
colorHash
|
38e00000000 |
|
VISUAL
cropResistant
|
0003918091100000 |
Code Analysis
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://verify.walletconnect.org/7569c63c696a4e8aeb3217c1b1332bd7
📡 API Calls Detected
- http://ip-api.com/json
- https://relay.farcaster.xyz/v1/channel/status
- https://relay.farcaster.xyz/v1/channel
- 0x3b3b57de
- /api/eth-price
- https://logs.dynamicauth.com/api/v1/
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 427 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 427 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
