
Phishing Analysis
Detailed analysis of captured phishing page
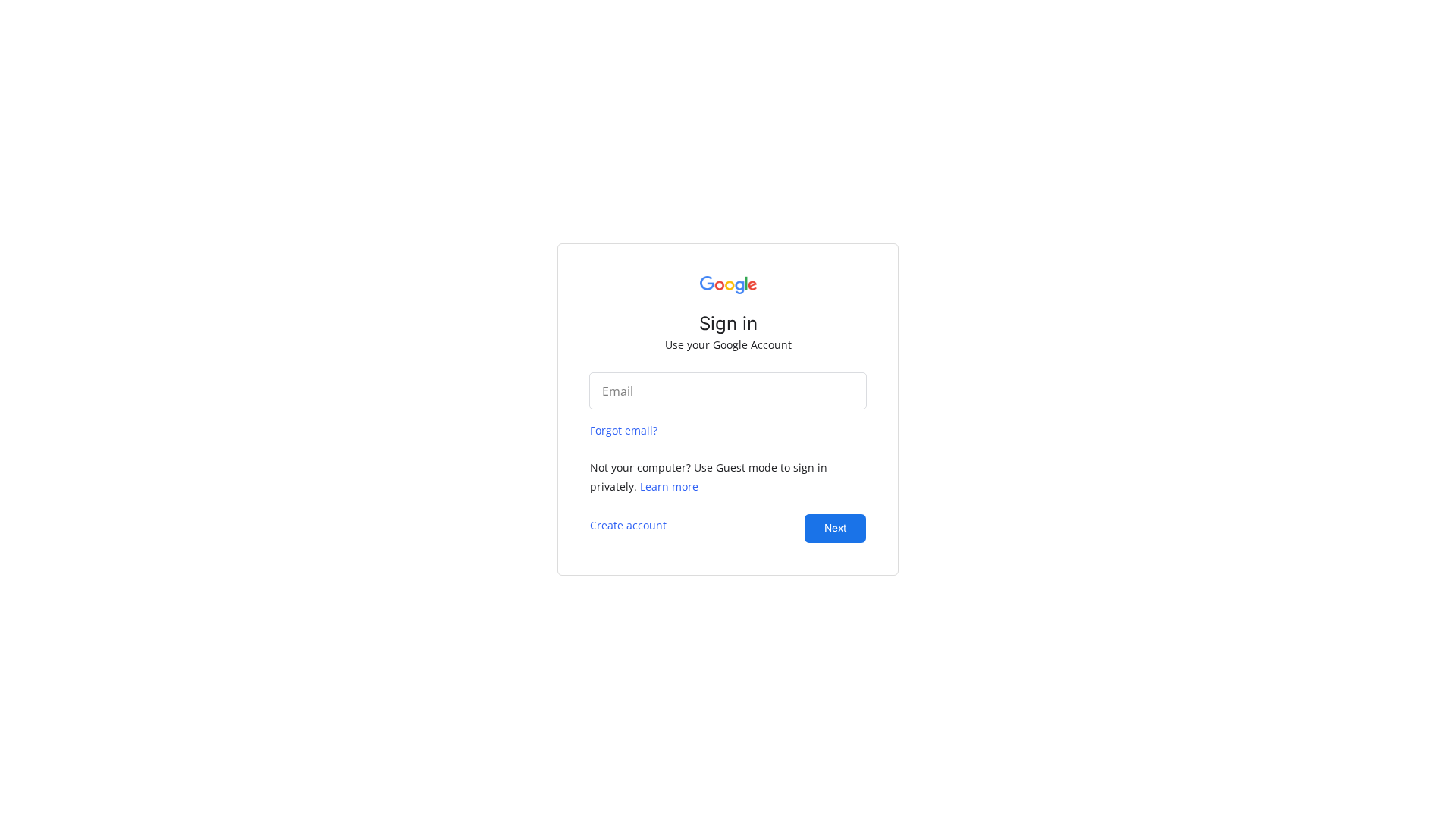
Visual Capture
No screenshot available
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T15D81E03290819D770193D3E072BAAF1636C1C2A5CB075A0453F8E3CD6BE7D82DE75699 |
|
CONTENT
ssdeep
|
48:nICYcV+ct368TwDM4+Era6W4oRn2Z9vQZbF7nrSTZE8bnmwY4wtzzeYyXlofvlXB:nP68aM47aTfyvOlST7mhHSYy2fvtSkr |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e6999964339b6631 |
|
VISUAL
aHash
|
ffffe7e7e3e3ffff |
|
VISUAL
dHash
|
000008080c040000 |
|
VISUAL
wHash
|
3f3f272724243c3c |
|
VISUAL
colorHash
|
07001000180 |
|
VISUAL
cropResistant
|
000008080c040000 |
Code Analysis
🔐 Credential Harvesting Forms
📤 Form Action Targets
- /site/submit
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
🏢 Brand Impersonation Analysis
Fraudulent Claims
⚔️ Attack Methodology
Primary Method: Credential Harvesting via Fake Document Portal
The phishing page mimics a document-sharing portal, tricking victims into entering credentials to 'access' a non-existent file (e.g., '2513501.doc'). The single form captures input in real-time and submits it to an attacker-controlled server via HTTP POST, likely without client-side validation.
Secondary Method: Subdomain Spoofing
The URL abuses the 'webshar.es' domain by creating a subdomain ('mail.my.webshar.es') to impersonate a legitimate service. This technique exploits trust in the parent domain to evade email filters and increase click-through rates from victims.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : None
- : None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for mail.my.webshar.es
Found 2 other scans for this domain
