
Phishing Analysis
Detailed analysis of captured phishing page
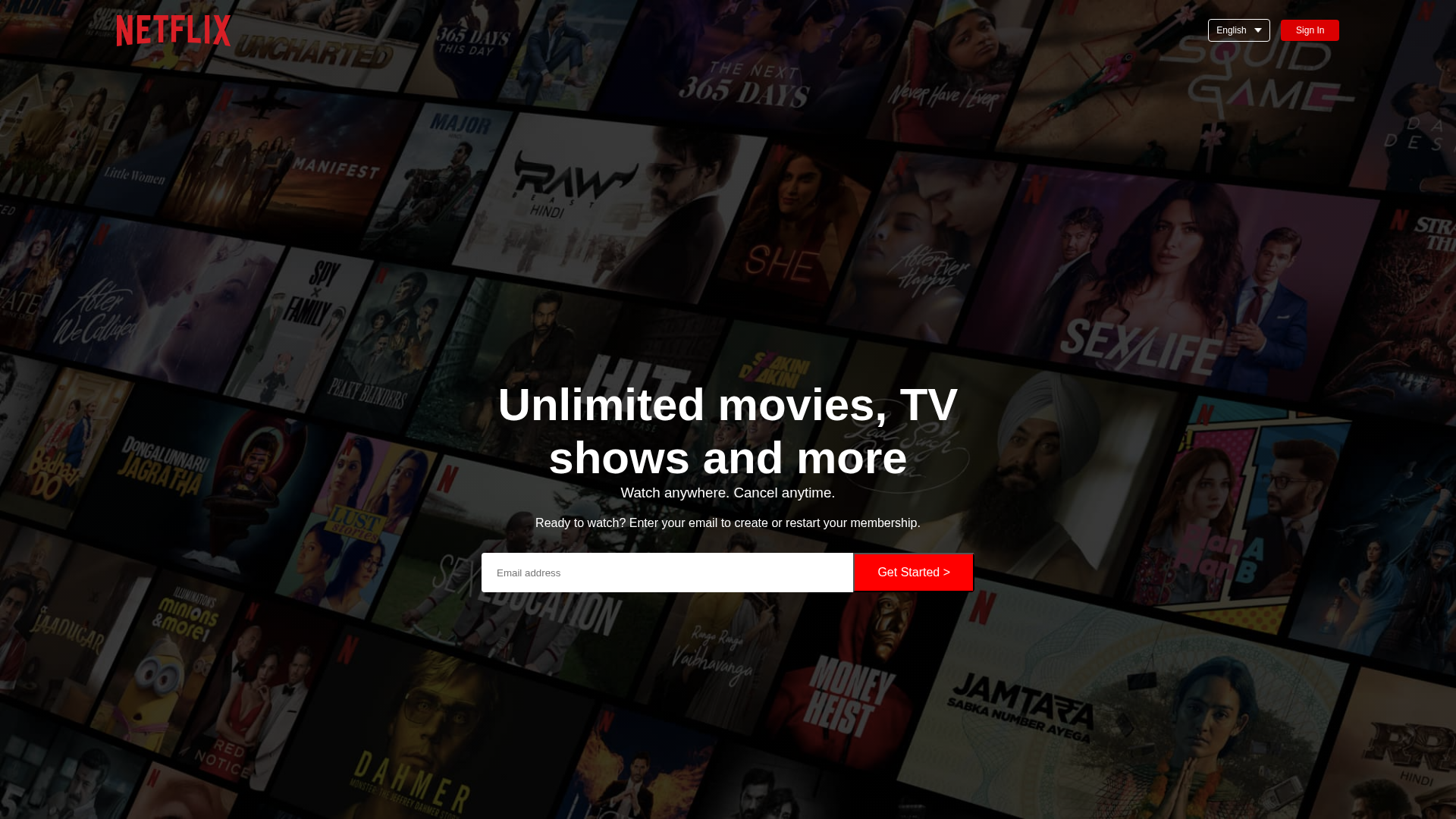
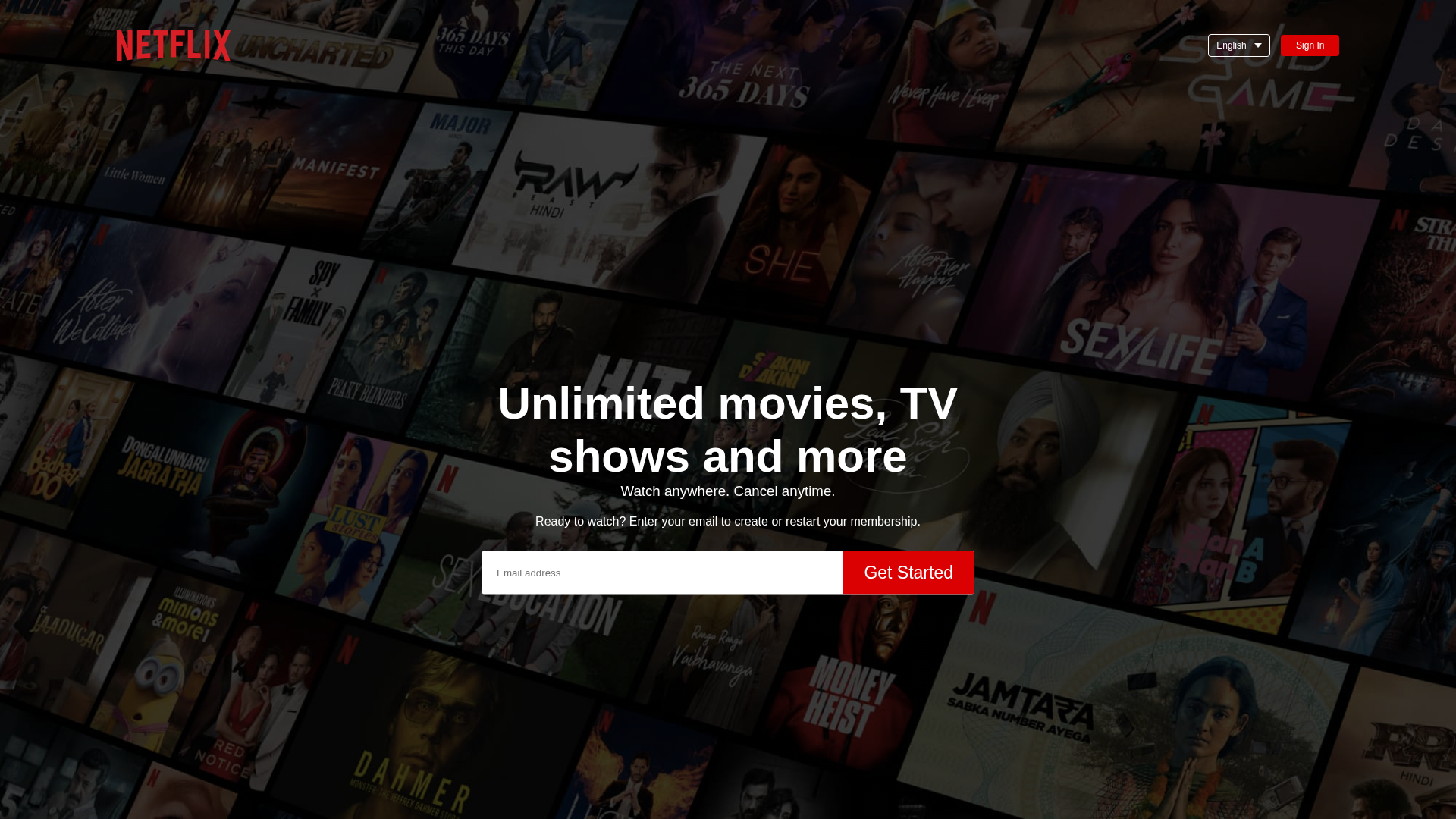
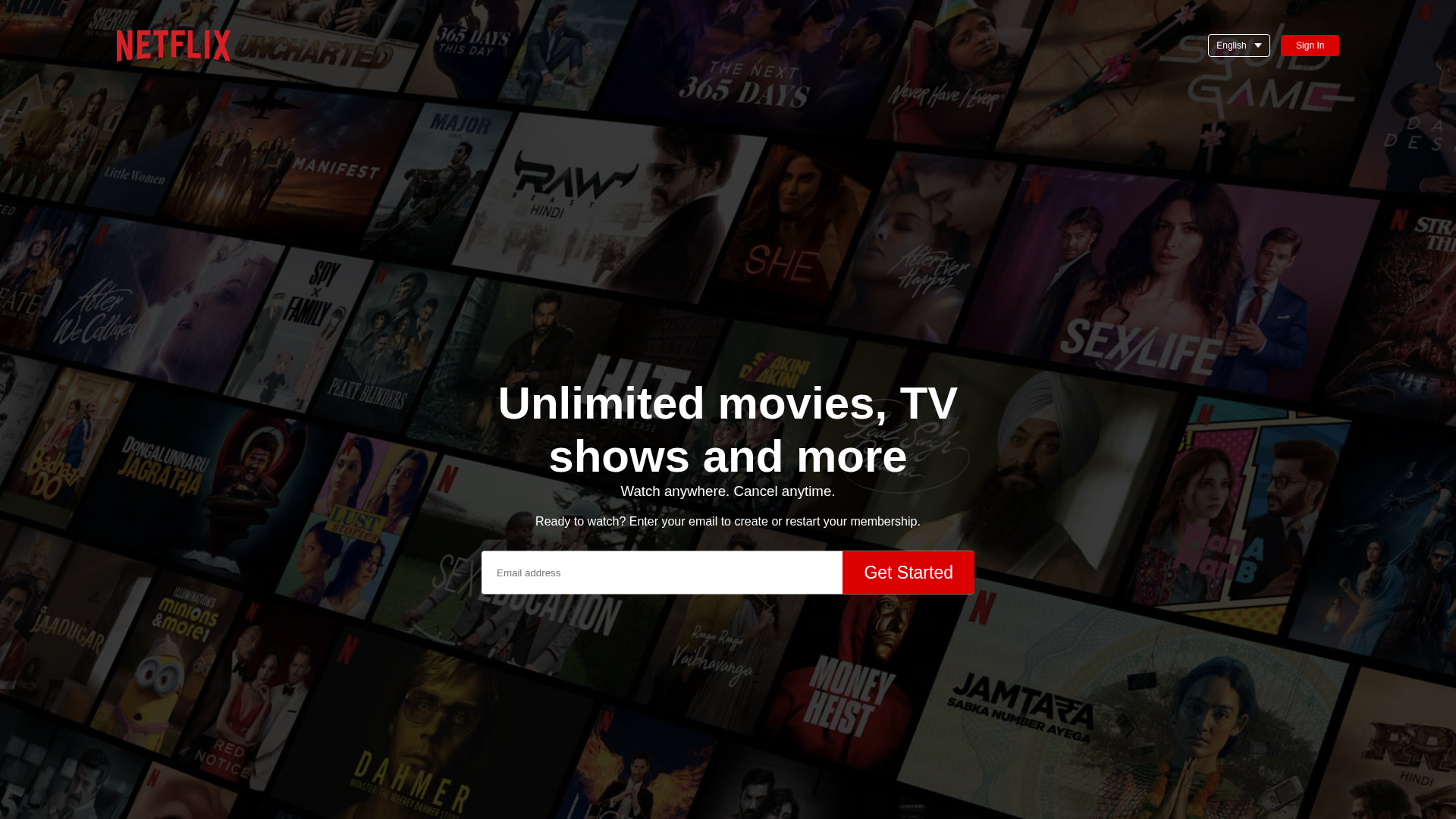
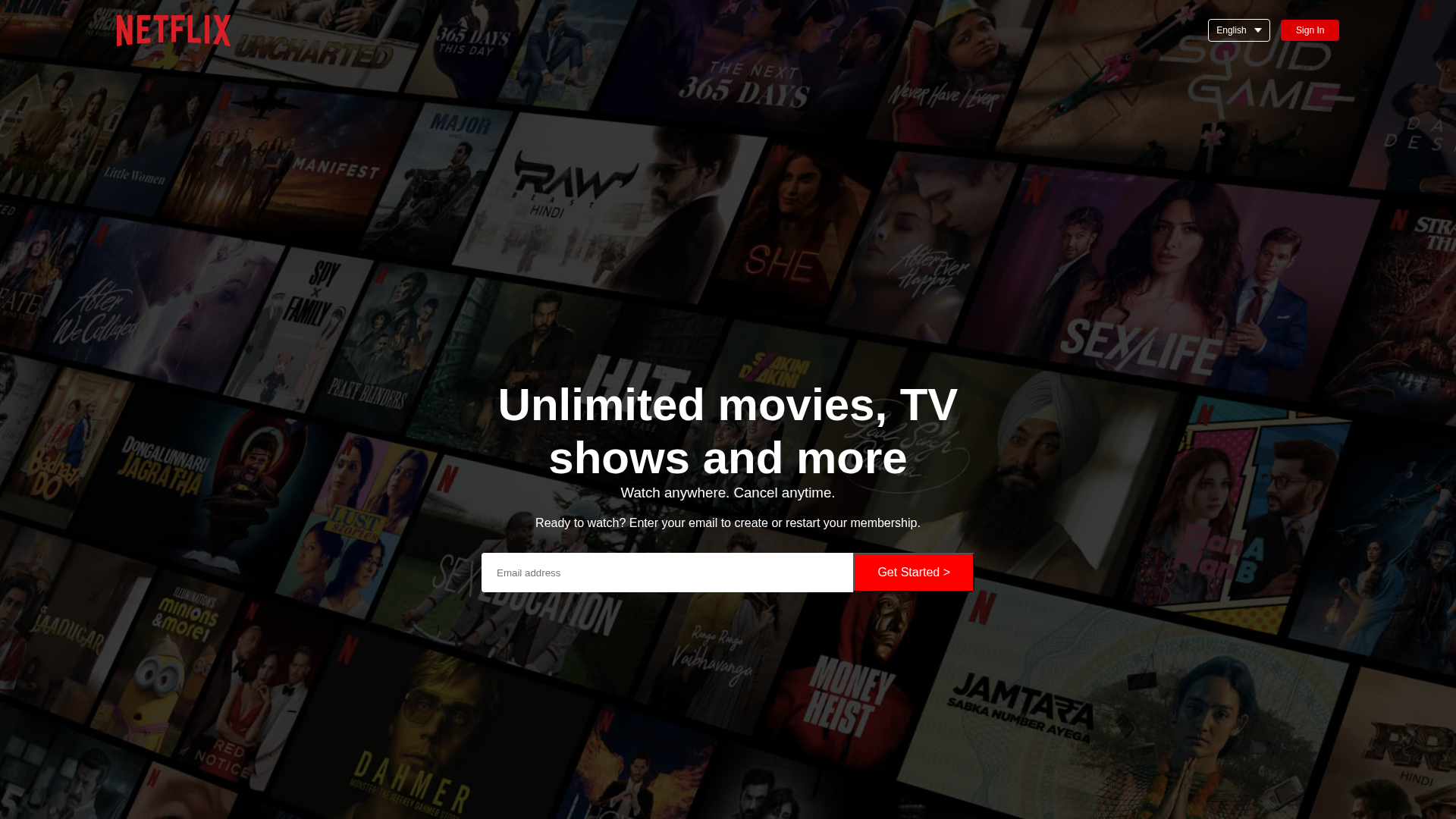
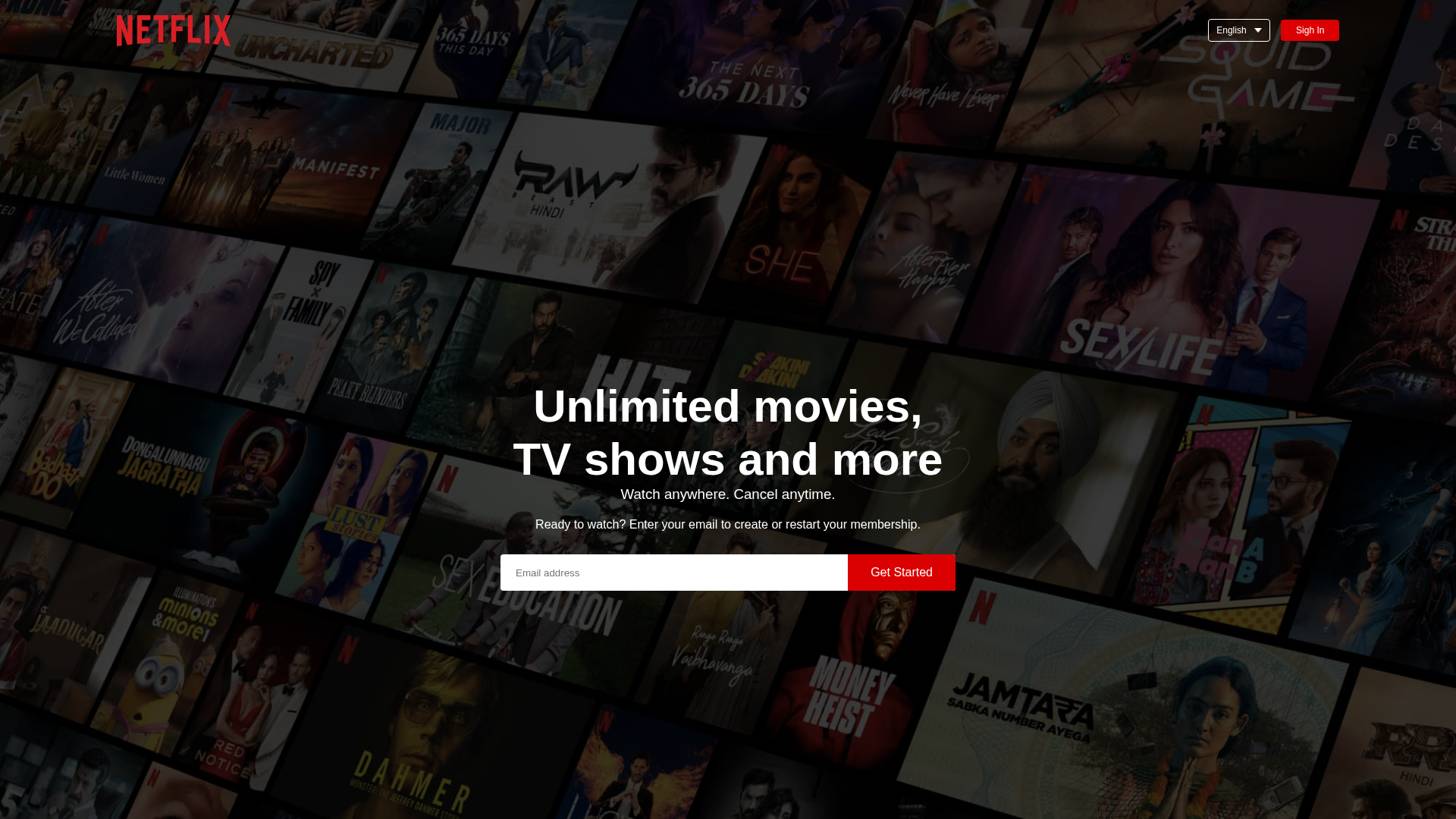
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1E66142745044597B45C357B07B32AB2EB78682C0DA63270820E9C75FEFEAE09CD1E6A5 |
|
CONTENT
ssdeep
|
48:n8qUHSuTIJ5F0p63mRCKc6259mnShAhoxGx9WhKHimF10fejon/a:nnsbW3PKHC9mnwAhua9WhmiQXoi |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cc6732cd7131cc33 |
|
VISUAL
aHash
|
423060d83c3c0705 |
|
VISUAL
dHash
|
8664aeb272602c0d |
|
VISUAL
wHash
|
c63070fe3e3c8707 |
|
VISUAL
colorHash
|
39e00008000 |
|
VISUAL
cropResistant
|
ca0082c242c28282,8664aeb272602c0d |
Code Analysis
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
🏢 Brand Impersonation Analysis
Fraudulent Claims
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters credentials into 2 fake forms. Form data is captured via JavaScript or backend submission and transmitted to attacker's server for account compromise.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
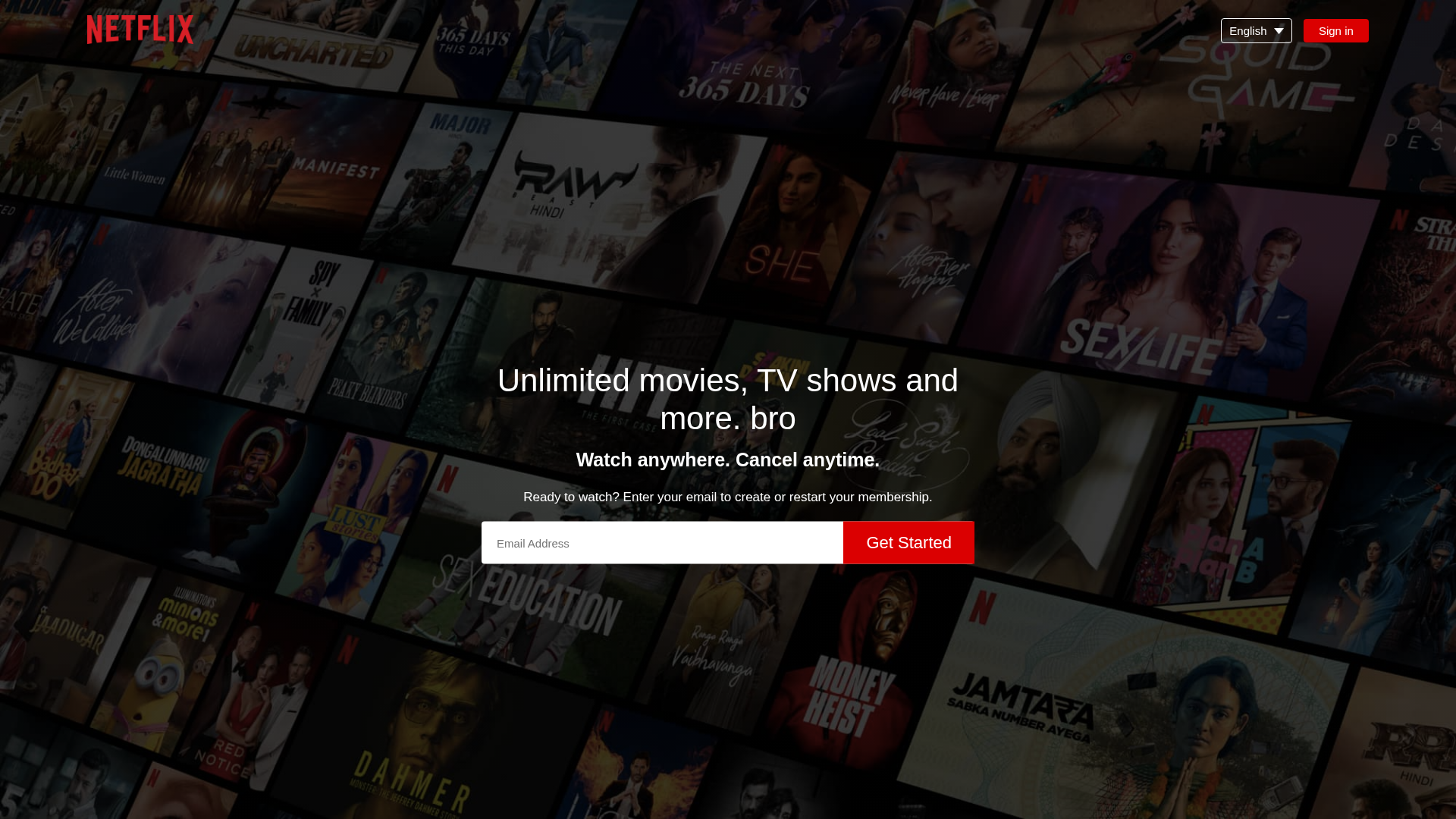
Scan History for mazinlatheef06-del.github.io
Found 4 other scans for this domain
