
Phishing Analysis
Detailed analysis of captured phishing page
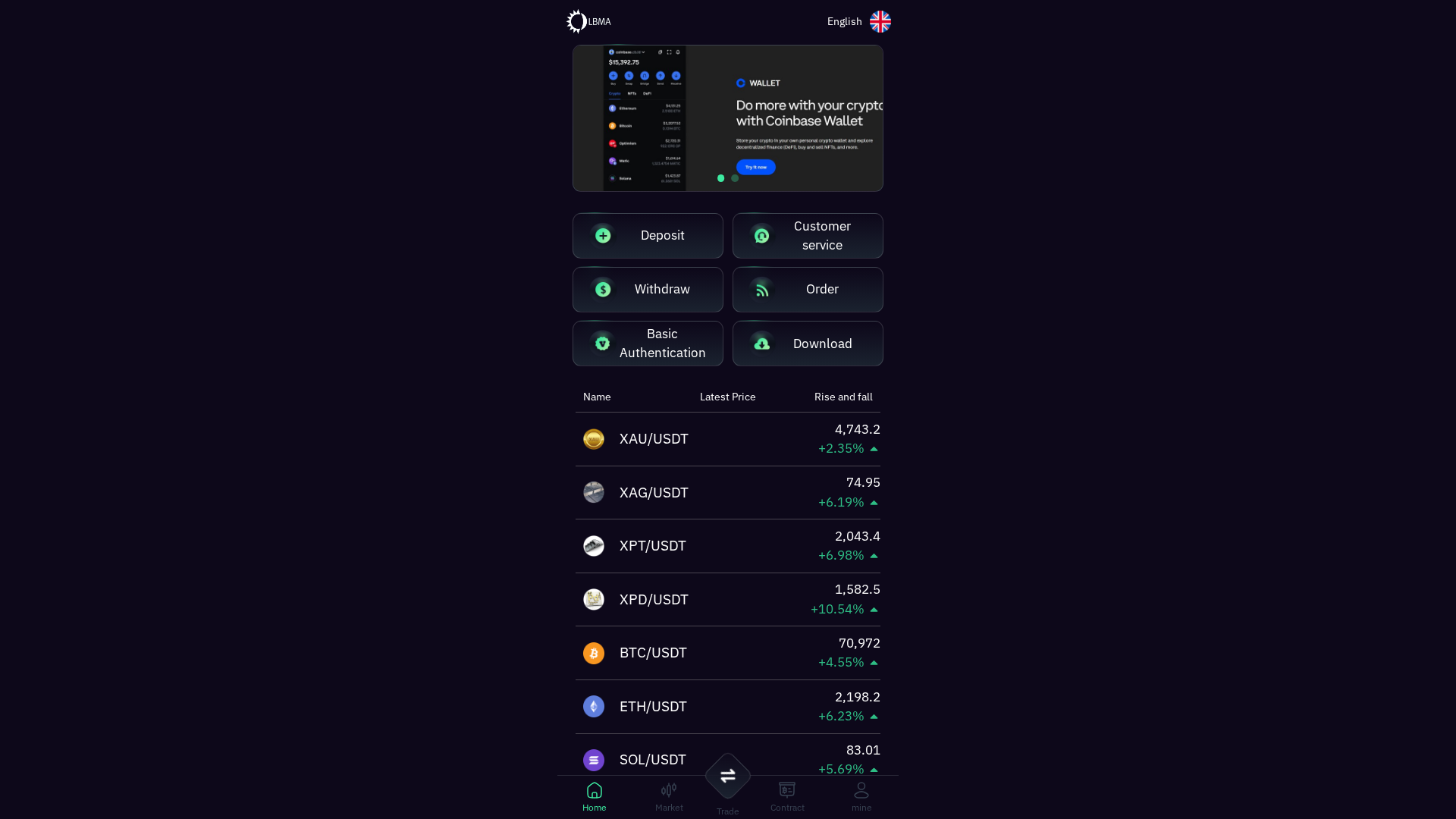
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T177A2ED22705249BB407BC2D5A870BF8DA9E2F70EC556C505F3FC16481FCAEBAF961864 |
|
CONTENT
ssdeep
|
384:lPBdx9agSKQygNf8lxR9TbwL6VlxL9tb1R6VlxP9dbJu6Vlx/9tbnB6VlxG9gbrr:ZBdx9agSKQygNf8lxRRbwL6VlxLnb1Rf |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cc99996666666666 |
|
VISUAL
aHash
|
1818181818181818 |
|
VISUAL
dHash
|
3232323220202030 |
|
VISUAL
wHash
|
3c3c1c1c18183838 |
|
VISUAL
colorHash
|
3800b000200 |
|
VISUAL
cropResistant
|
3232323220202030 |
Code Analysis
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
🎯 Kit Endpoints
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAEAAAABACAYAAACqaXHeAAADm0lEQVR4Xt2bP2/TQBiH+xH4CB2aUIkFiS8QBuKIAcFOpa4wMSCxuoEOiKkMFKYAEwy0HYtYWBBlKp1gywBDtwoJiTH0DVx0eXxn3zlnx76f9CjR3Xv3/ol98TnOykoNGiYX7231OxMfHg7We5ynNUpvrl5gQotCH40Ug66CYdIZ0e/SxSBrYsw4atd5EGeGwGpleK2zybhqEQNZNoyvMm31u2M6bwrpYH2V8QYVHTaUatYGg6NGw/gXEidvC8yjlDhp22A+XuJkbWSYdPeZl5OavNr7IpfmzK9QnKTtML9ccXAsME+jYjr0idOpwEGxwXznROMYyd080ThWmPdUNIoZ41pAo9iZS162kTQo4uDJg8nH108z7Xm4jPn6fm9qxzaBtq79JuYKwM48djauTkyinY5JZ6c/M3a6rbxXNnqbiaJ+E3KnulQBQupw95F1fjlSRKptfPIlYysFoh7fupKxs+FdAAkitOhDMIk2yk5OF4p2NqbJ+/xoUYXoQ/Hq/u1pv7yyT/j26cNsvHwwOxu9WYy0teH16QtHey9ngYcSfSiKCqAOf73tbXo305ZHev3SZa8CCCH1eW+UmV9RpgAqPrZZSTrHSy0A51bIQlZkd7i7PetTeuN5BAjeBRBCyPbp275mTau7TbTLw7sAtgDLiHMLSrKoifSjgba6fZ5NHt4FCKnnd25Y5y9q8+nPw6sAVcjmo6jNpz+PpRdAZPIh79WewGRnG+OLcwGqlMmPWgPUq8glJtoU0bgC2HzRRv/KE+n7Atrm0cgCCIfPtqd93BozHnl/9G70b4x2beBE0j1wLoC6MqtC9KX7s10JmsZ+1/YHLkz3AulgrccOG1VIbWJImQKoMbS14b0dFkLqz+9fmfkFXmyxX5Cxqk8ka4De5kKpAgghZPtkbaca7WxxnJ3+yNjZKF0AHVl45O6NuoNDqT7hheHKjyiZNju01ftEprtGNjKP09CgLHJOy+GoVmZfTIko0da138Rc8iEL0BaY/8qw392nUaww95loGCvMe6bzK6MxjWODOWfEAbHBfDNKkzXn2+Rtg7laxYFRkHg+QZqZoOUwv0KV+cW4qTA3Z8XwrWB8GMJHnLBNyILOfEqJE7eBtL+WMo+FRAdNJs17EmwRtWG/sPA5X6S0F/4/gaFgrJWKzpfMMeOrRU24VmBMS1E66GwysKphDI1QHUcEfTZWIY+Kylf2OvT/B5hjJkfkz9F1JvwXjqO1aofmH/sAAAAASUVORK5CYII=
📡 API Calls Detected
- https://admin.bibirouge.com/BiB.mobileconfig
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 16 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 16 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
