
Phishing Analysis
Detailed analysis of captured phishing page
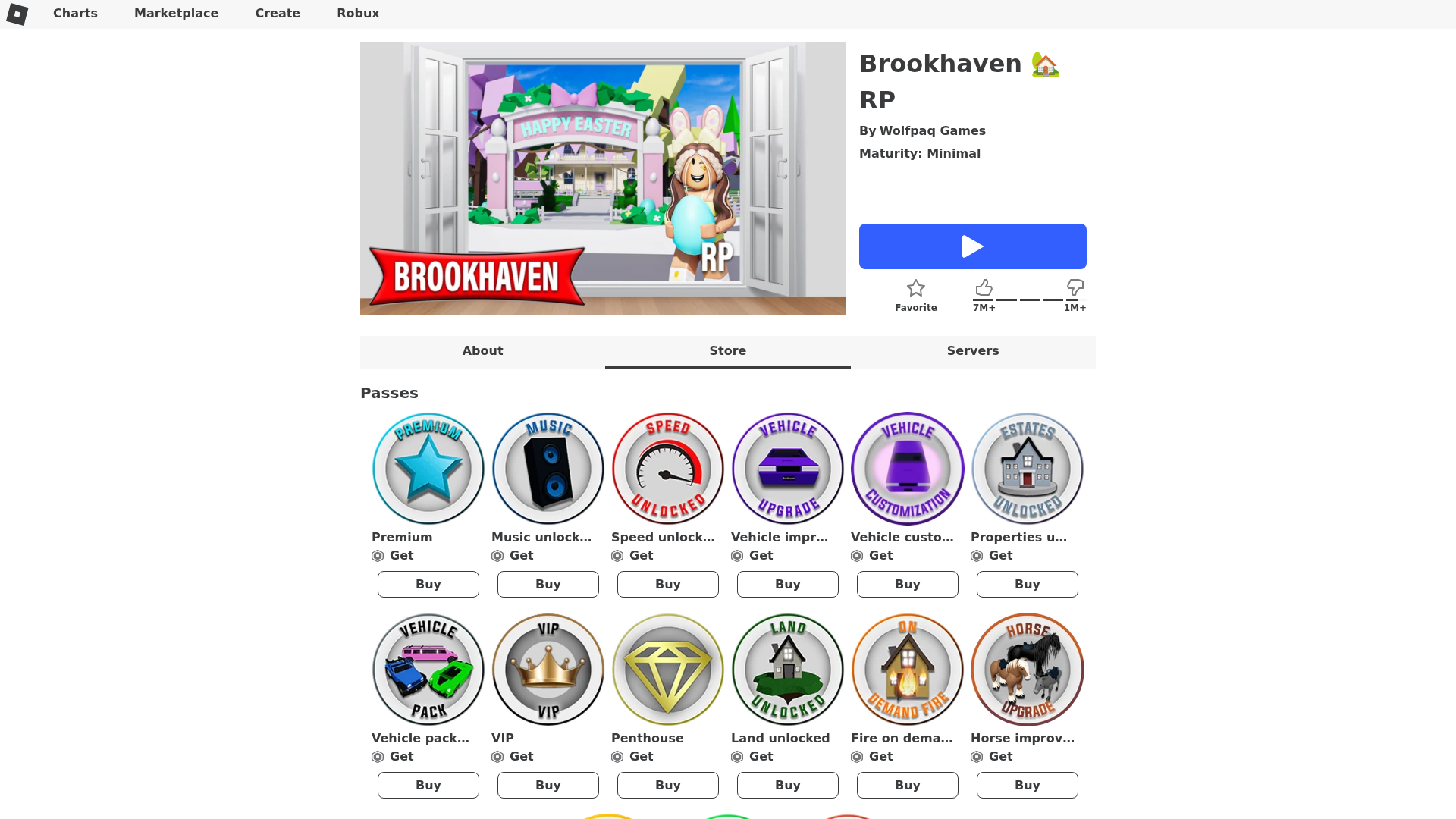
Visual Capture
Detection Info
http://brookhavenrp.site/
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
837618ba-166…
Analyzed
2026-04-01 10:16
Final URL (after redirects)
https://brookhavenrp.site/store
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1CA6284A131140AAB1237C5CCFD60AF497082F24BC617679965FE12921FCBD6BFE79422 |
|
CONTENT
ssdeep
|
384:c+BvFw9DeGSty8m6LDzCmn2jHaVdn1h6p:LL8DeGSty8m6PzCmn2jHaV9H6p |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b03393c7c6cccc6c |
|
VISUAL
aHash
|
c7c7c3cfc3c3c3f7 |
|
VISUAL
dHash
|
9e1e9e0e96169606 |
|
VISUAL
wHash
|
03c7c3c7c3c3c3c3 |
|
VISUAL
colorHash
|
07200000080 |
|
VISUAL
cropResistant
|
9e1e9e0e96169606,0834b4b2b0b43408 |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Personal Info
🔒 Obfuscation Detected
- atob
- fromCharCode
- unicode_escape
- base64_strings
📡 API Calls Detected
- https://www.google.com/ccm/geo
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Personal Info
Code Obfuscation
JavaScript code obfuscated using 148 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Two-Factor Authentication Stealer
Target
Roblox users
Attack Method
obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Personal Info
- 148 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Credential harvesting service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 148 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
brookhavenrp.site
Registered
2025-04-29 17:36:09+00:00
Registrar
HOSTINGER operations, UAB
Status
Active (336 days old)
Hosting Information
Provider
Hostinger
ASN
🤖 AI-Extracted Threat Intelligence

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.