
Phishing Analysis
Detailed analysis of captured phishing page
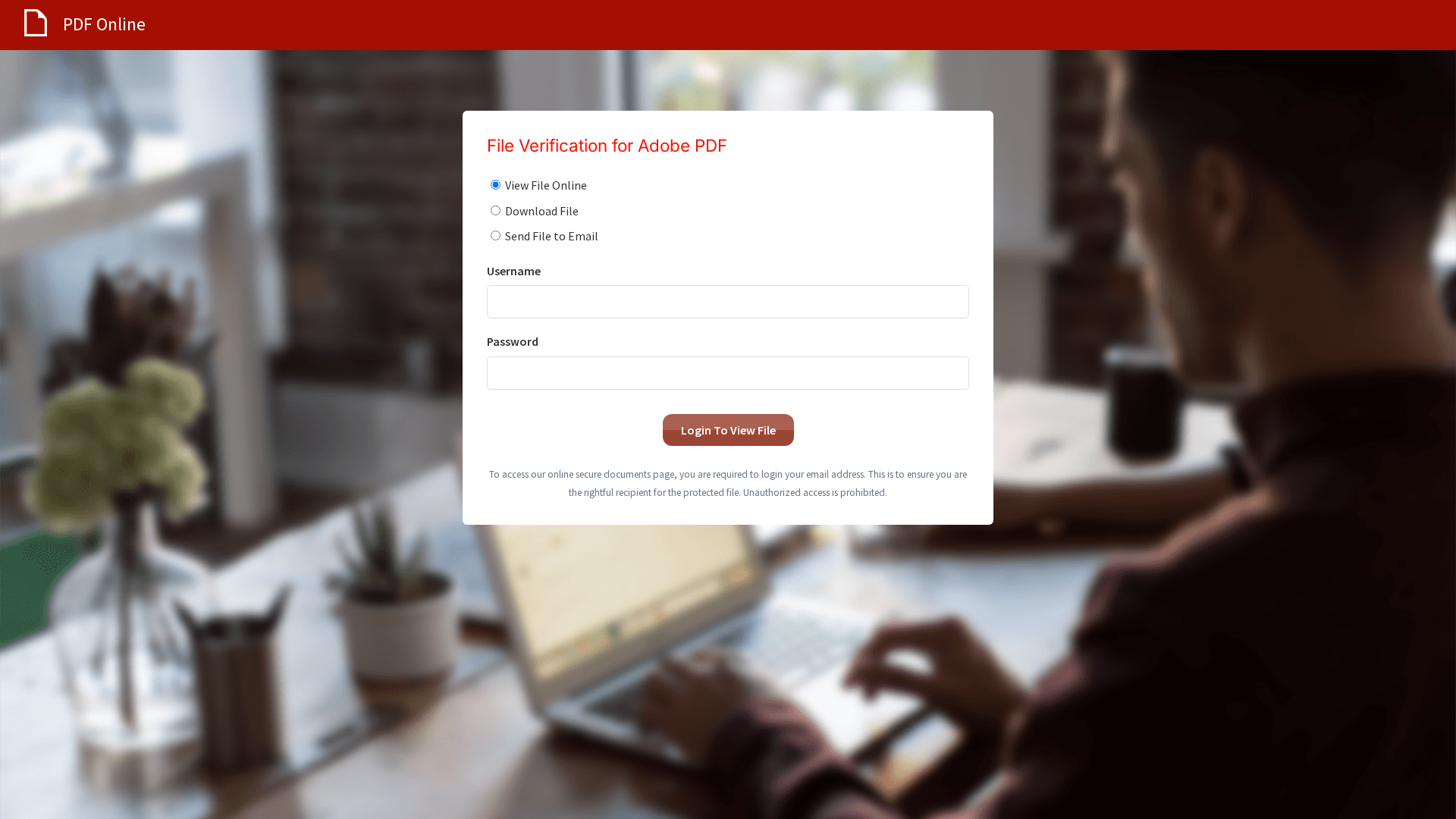
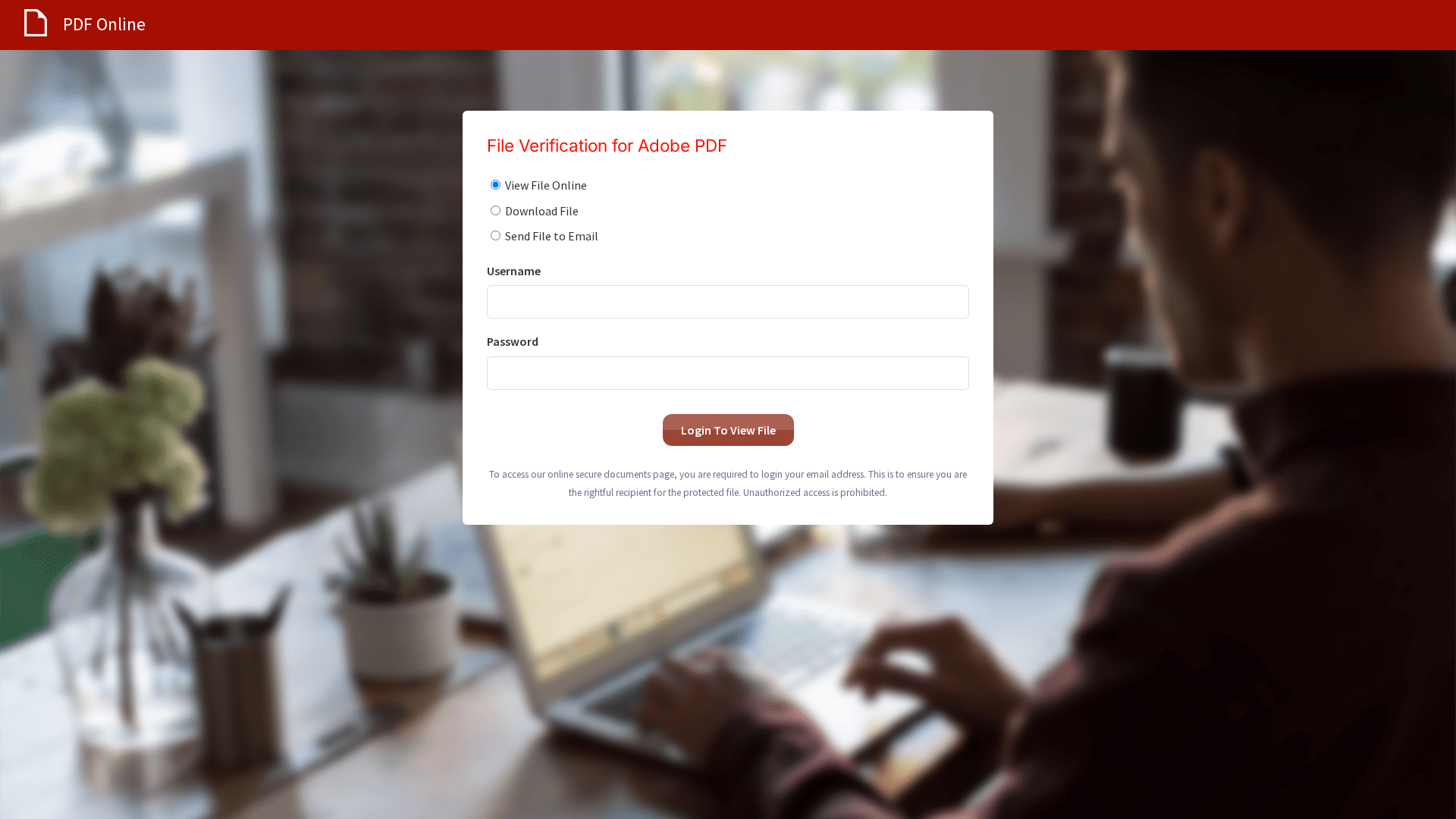
Visual Capture
Detection Info
http://site.applerts.net/s/63bzgfsvbwsfcdx7y9/85201f/8681e9a8-b42e-44fc-8482-459b41358d3c
Detected Brand
Adobe PDF
Country
International
Confidence
100%
HTTP Status
200
Report ID
844680ee-218…
Analyzed
2025-12-28 12:17
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1BA61433590459C7B6252D39873D6FF0461CAC2A6CB0E6C00A2F4D3CCEBE7D20DEA65A5 |
|
CONTENT
ssdeep
|
48:nICYcV+cgNstRemx3YfkljfvHg68SBF0YTgl76214zeVb8JoaTokg:nClckkJfvHg68S0YTgQU4SNqomokg |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
de9c732427382537 |
|
VISUAL
aHash
|
98bcbc3c3c7cf8a0 |
|
VISUAL
dHash
|
3038316868a02949 |
|
VISUAL
wHash
|
18bcbc3c3c7cf8a0 |
Code Analysis
Risk Score
65/100
Threat Level
CRITICAL
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Credential harvesting phishing targeting Adobe PDF users.
• Target: Users needing to view/download PDFs online
• Method: Fake login form designed to steal usernames and passwords.
• Exfil: Likely to a remote server controlled by the attacker (not visible in screenshot).
• Indicators: Domain 'site.applerts.net' does not match 'adobe.com', a login page appears, requesting username and password.
• Risk: HIGH - Immediate risk of credential theft if login information is entered.
🔐 Credential Harvesting Forms
📤 Form Action Targets
- /site/submit
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Adobe PDF
https://federalnewsmagazine.com/s/63BZGFSVBWSFCDX7Y9/85201f/...
Mar 15, 2026
Adobe PDF
http://currentnewsalerts.com/s/63BZGFSVBWSFCDX7Y9/85201f/868...
Mar 09, 2026
Adobe PDF
http://current-news-alerts.com/s/63BZGFSVBWSFCDX7Y9/85201f/8...
Mar 06, 2026
Adobe PDF
https://site.applerts.net/s/63BZGFSVBWSFCDX7Y9/85201f/8681e9...
Mar 01, 2026
Adobe PDF
http://mail.amazingholidaycoupons.com/s/63BZGFSVBWSFCDX7Y9/8...
Feb 18, 2026
Scan History for site.applerts.net
Found 1 other scan for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.