
Phishing Analysis
Detailed analysis of captured phishing page
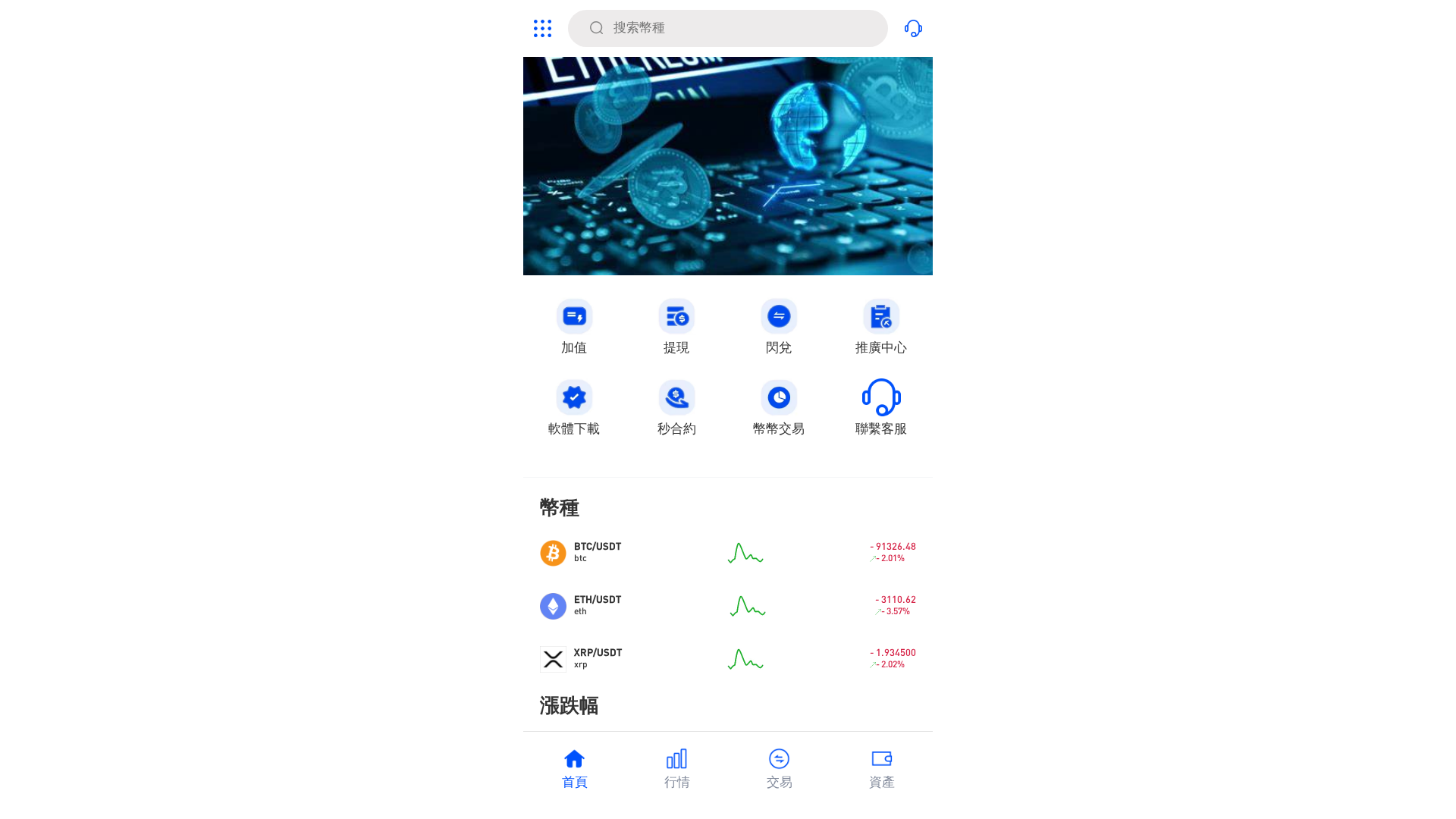
Visual Capture
Detection Info
http://gxh5.geminis-pro.com
Detected Brand
Geminis Pro
Country
International
Confidence
100%
HTTP Status
200
Report ID
85e0d663-ac6…
Analyzed
2026-01-20 10:51
Final URL (after redirects)
https://gxh5.geminis-pro.com/#/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1E2C2DF31F20271071673F9C8F8613F0FB2A6B70B820295586A6945E47DCBCF6B7929B5 |
|
CONTENT
ssdeep
|
384:KF1tF3F2F2FwFhFsF+FfTEFwuS9EXbtMcgQgzT1g9U:K71iiwTk6fTEFwuS9EXbtMcgQgzT1gO |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b333338ccccccccc |
|
VISUAL
aHash
|
e7c3c3ffffffffff |
|
VISUAL
dHash
|
4d4d4d041c14141c |
|
VISUAL
wHash
|
c0c0c0e4c3c3c3c3 |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
4d4d4d041c14141c,e38f8dceefefaf2e |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Banking
🎣 Personal Info
WebSocket C2
🔬 Threat Analysis Report
• Threat: Cryptocurrency platform phishing
• Target: Users of Gemini Pro or other cryptocurrency platforms
• Method: Imitates a cryptocurrency trading app interface to collect user data or credentials
• Exfil: Data potentially exfiltrated via WebSocket URLs, JavaScript form submission and possibly custom API
• Indicators: Recently created domain, obfuscated JavaScript, WebSocket communication, JavaScript form submission.
• Risk: HIGH - Potential for theft of cryptocurrency or personal information
🔒 Obfuscation Detected
- fromCharCode
- unescape
- base64_strings
📡 API Calls Detected
- POST
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Unknown
https://cdn.gosafemode.com/screenshots/e937158b39e7.png
Apr 08, 2026
Unknown
https://gfhfsw.weebly.com/
Mar 18, 2026
24/7 Telecom
https://grateful-aspects-830309.framer.app/
Feb 11, 2026
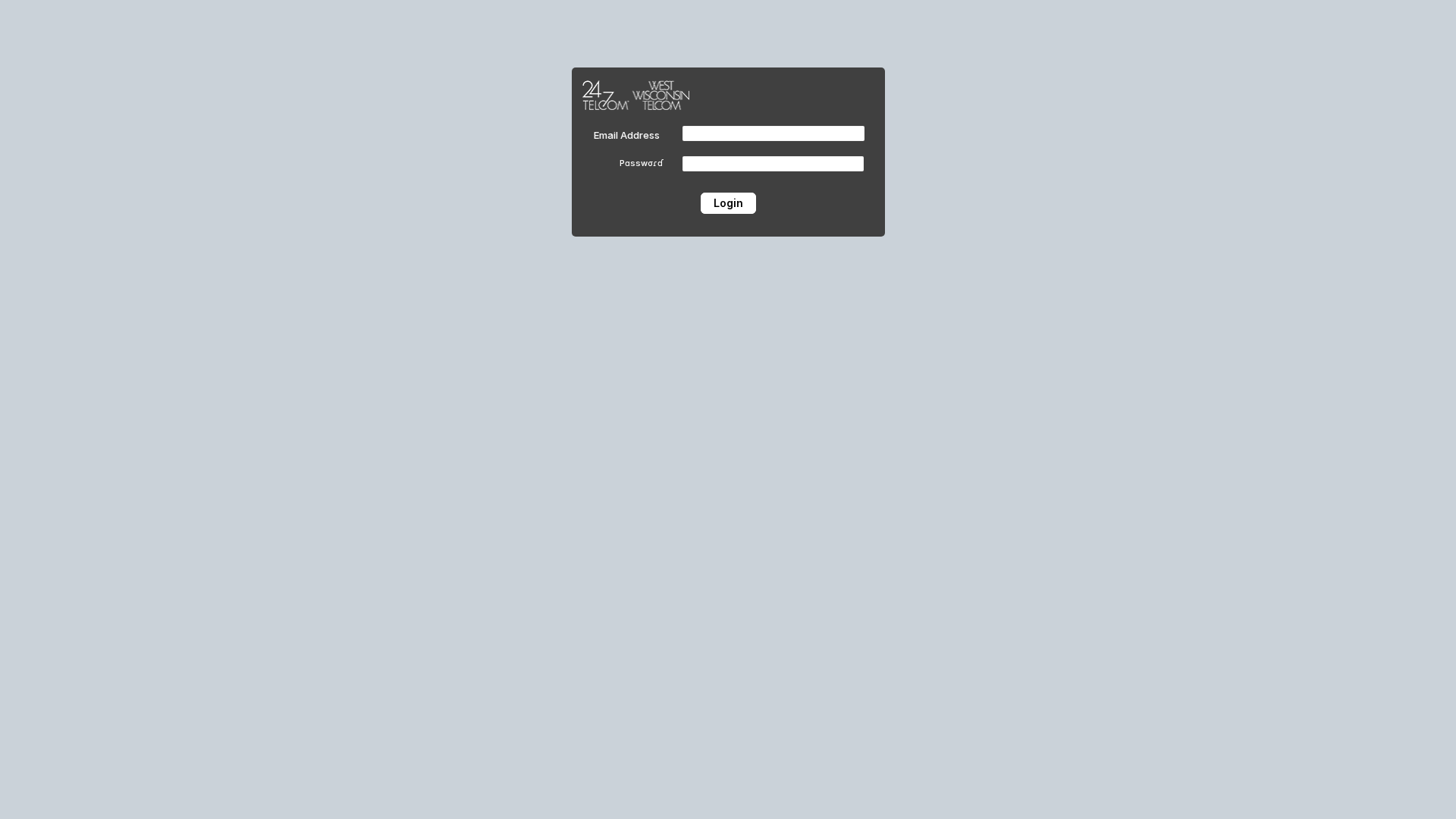
24/7 Telecom / West Wisconsin Telecom
https://grateful-aspects-830309.framer.app/
Feb 11, 2026
No screenshot
PancakeSwap
https://pancakeswap.finance-beta-service-alpha-online.pro/
Jan 01, 2026

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.