Phishing Analysis
Detailed analysis of captured phishing page
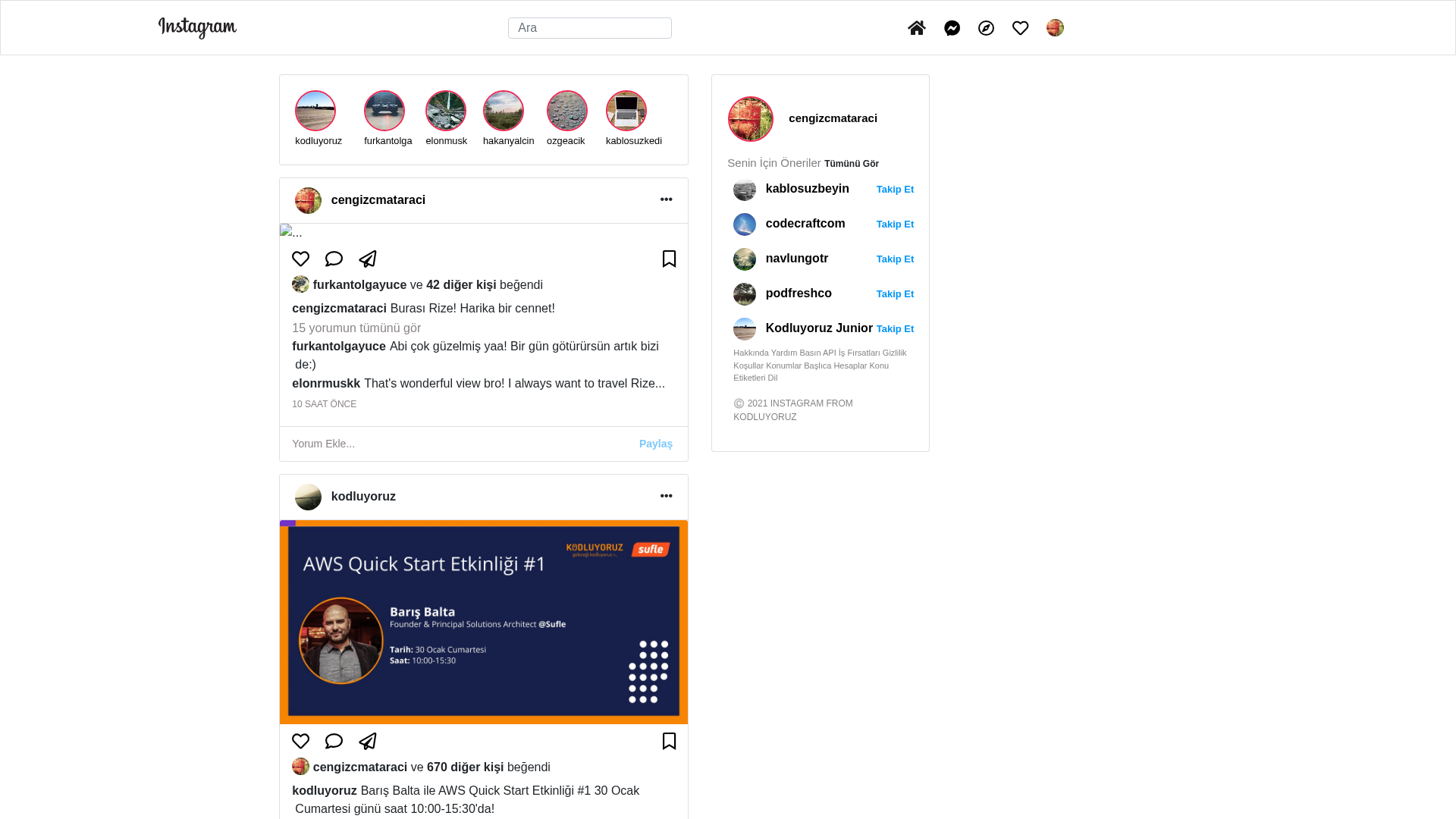
Visual Capture
No screenshot available
Detection Info
http://instagram-clone-five.vercel.app/
Detected Brand
Instagram
Country
International
Confidence
95%
HTTP Status
200
Report ID
8654e2b0-8a7…
Analyzed
2026-03-12 15:23
Final URL (after redirects)
https://instagram-clone-five.vercel.app/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T12E8273A2C240553B4193C1C5F924EFBAA2E0038EE75309D6B3FD81B7F34DD255A22A9D |
|
CONTENT
ssdeep
|
384:GCN+2o55ATFN+lPOOb6nV5ATIN+ZobJtl5ATIN+8HPYbAXCu:GOo+kBb6nZtbJ3dgbAyu |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b8c63839c738c6c7 |
|
VISUAL
aHash
|
ffcff7ffff8f8f9f |
|
VISUAL
dHash
|
1a2c2c2c381a1a38 |
|
VISUAL
wHash
|
02878787878f8f8f |
|
VISUAL
colorHash
|
070000081c0 |
|
VISUAL
cropResistant
|
1a2c2c2c381a1a38,279390a829a3ab4b |
Code Analysis
Threat Level
BAJO
🔬 Threat Analysis Report
• Threat: Impersonation
• Target: Instagram users
• Method: Using a Vercel subdomain to mirror the Instagram interface.
• Exfil: Potentially credentials or other data, if a form was present.
• Indicators: Free hosting, brand logo, UI mimicry.
• Risk: Low
🎯 Kit Endpoints
- https://about.instagram.com/blog/
📊 Risk Score Breakdown
Total Risk Score
30/100
Contributing Factors
Free Hosting + Brand Logo
Vercel.app used to host Instagram content.
Impersonation
Visual mimicry of Instagram's UI.
🔬 Comprehensive Threat Analysis
Threat Type
Instagram Credential Harvester
Target
Instagram users (International)
Attack Method
Brand impersonation + credential harvesting forms
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
LOW - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
🏢 Brand Impersonation Analysis
Impersonated Brand
Instagram
Official Website
https://www.instagram.com/
⚔️ Attack Methodology
Primary Method: Brand Impersonation
The attacker is attempting to mimic the appearance of Instagram to deceive users.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
instagram-clone-five.vercel.app
Registered
None
Registrar
None
Status
None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for instagram-clone-five.vercel.app
Found 3 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.