
Phishing Analysis
Detailed analysis of captured phishing page
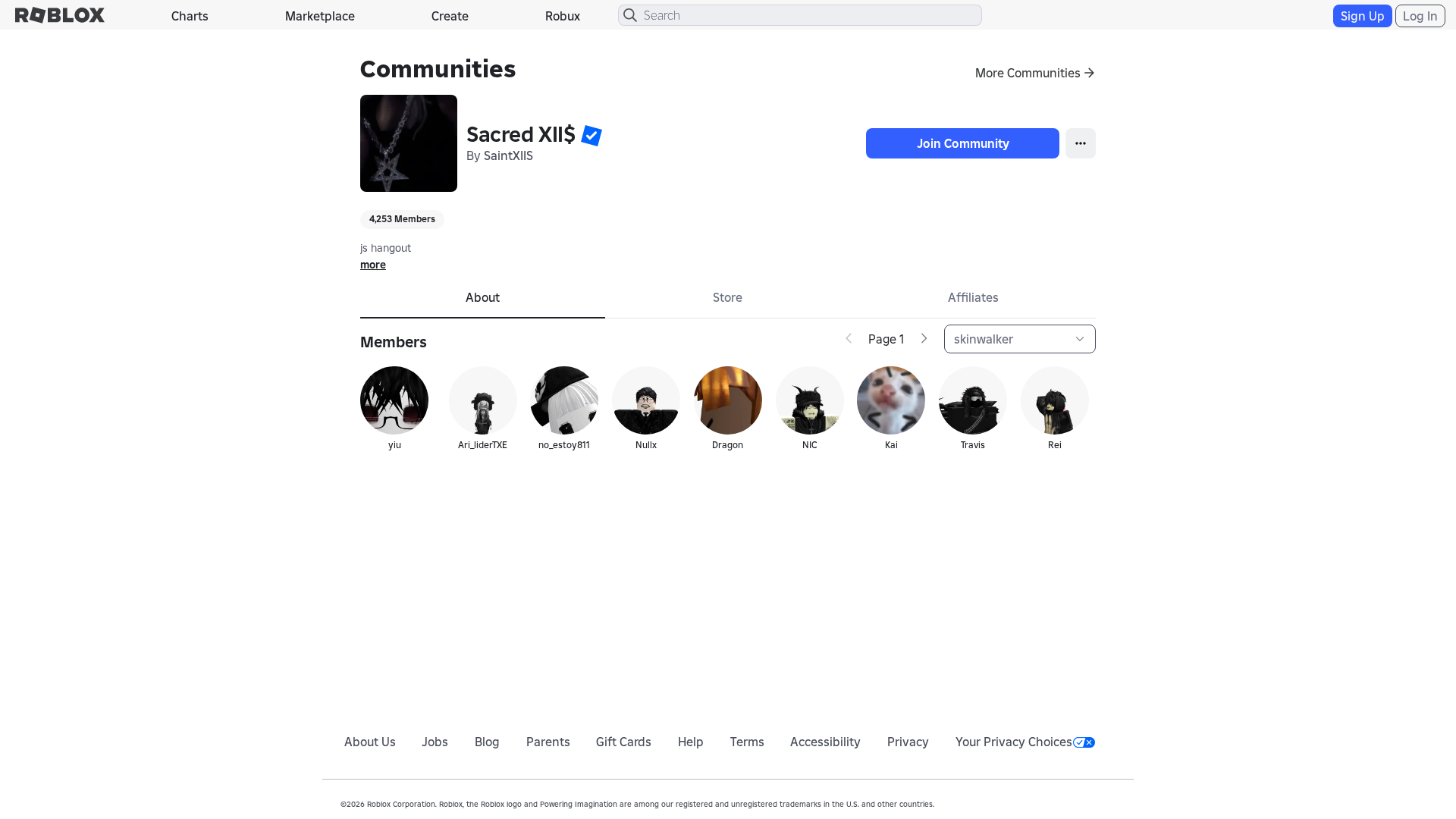
Visual Capture
Detection Info
https://www.roblox.com.ml/communities/7337089828/SacredXIIS
Detected Brand
Roblox
Country
International
Confidence
100%
HTTP Status
200
Report ID
873b81b8-f98…
Analyzed
2026-01-24 00:07
Final URL (after redirects)
https://www.roblox.com.ml/communities/7337089828/SacredXIIS#!/about
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T16263E7B29354683690AF59C6F478BF0563E3DF4AC64346D6B5F8A32A0DD8CA1F807417 |
|
CONTENT
ssdeep
|
768:NdHXBG33VQZelzuOUuOgpmMF9LT3X+iEy:NdHXBG3KZQzuOUuOgpl9LbX+iEy |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
bc3c9c4363c3c3c3 |
|
VISUAL
aHash
|
1a93ff83c3ffffff |
|
VISUAL
dHash
|
b23620260e000206 |
|
VISUAL
wHash
|
0083c383c3ffff81 |
|
VISUAL
colorHash
|
072000081c0 |
|
VISUAL
cropResistant
|
b23620260e000206,51d16169454dc545 |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Roblox account credential harvesting phishing
• Target: Roblox users
• Method: Fake Roblox website with a login form stealing user credentials
• Exfil: Data sent to an unknown location (likely a malicious server) via JavaScript form submission
• Indicators: Suspicious TLD (.ml), URL domain contains the brand name, JavaScript form submission, and obfuscated JavaScript
• Risk: CRITICAL - Real-time credential theft
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- js_packer
- base64_strings
🎯 Kit Endpoints
- /catalog
- {{ $ctrl.getCatalogPageUrl() }}
- https://www.roblox.com.ml/info/blog?locale=en_us
- https://www.roblox.com.ml/catalog?CatalogContext=1&Keyword=
- /login?returnUrl=9281673406662287
📡 API Calls Detected
- https://en.help.roblox.com/hc/articles/7997207259156
- https://ro.blox.com/Ebh5?
- get
- POST
- https://apis.
📤 Form Action Targets
- /search
Similar Websites
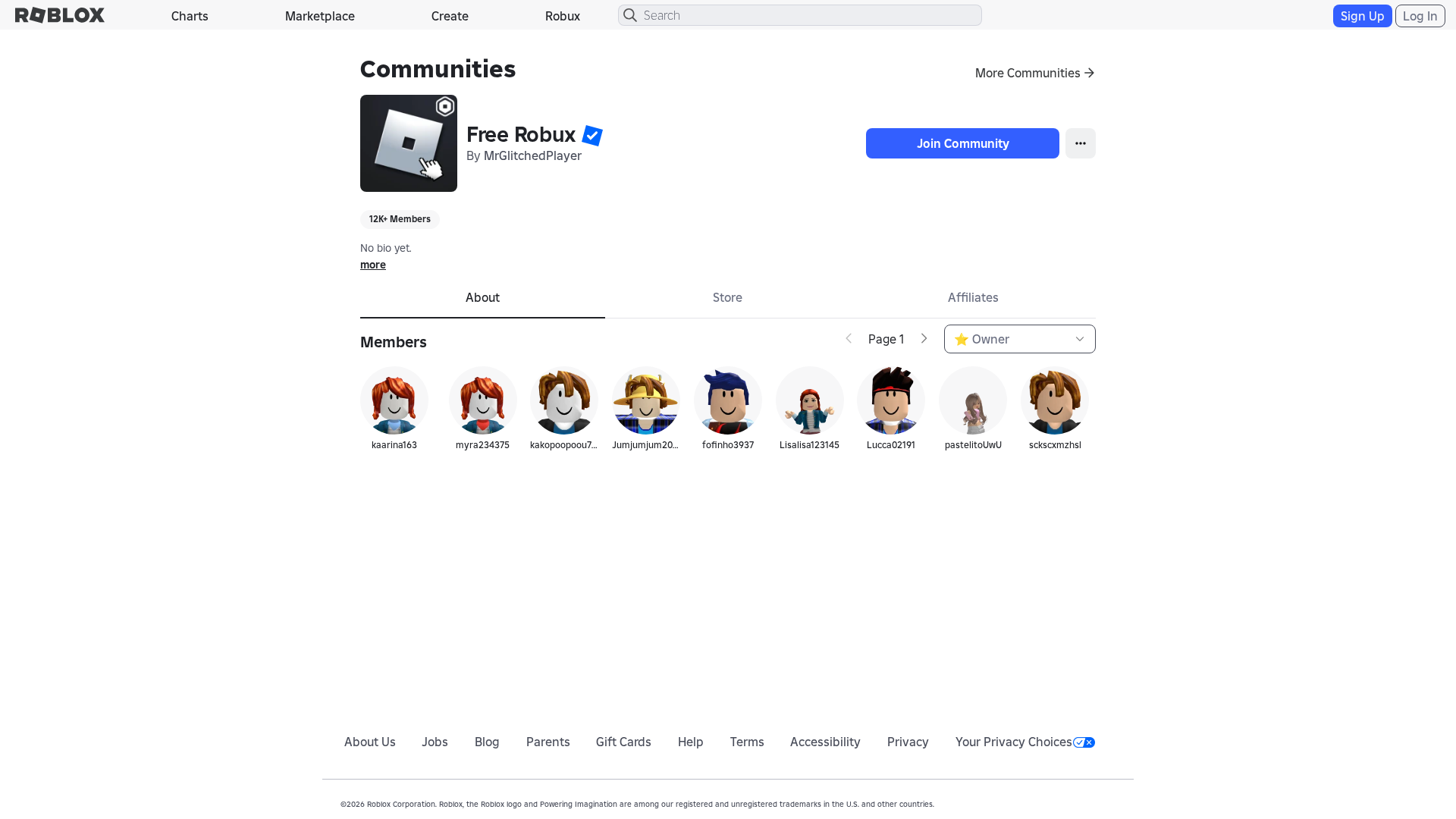
Pages with identical visual appearance (based on perceptual hash)
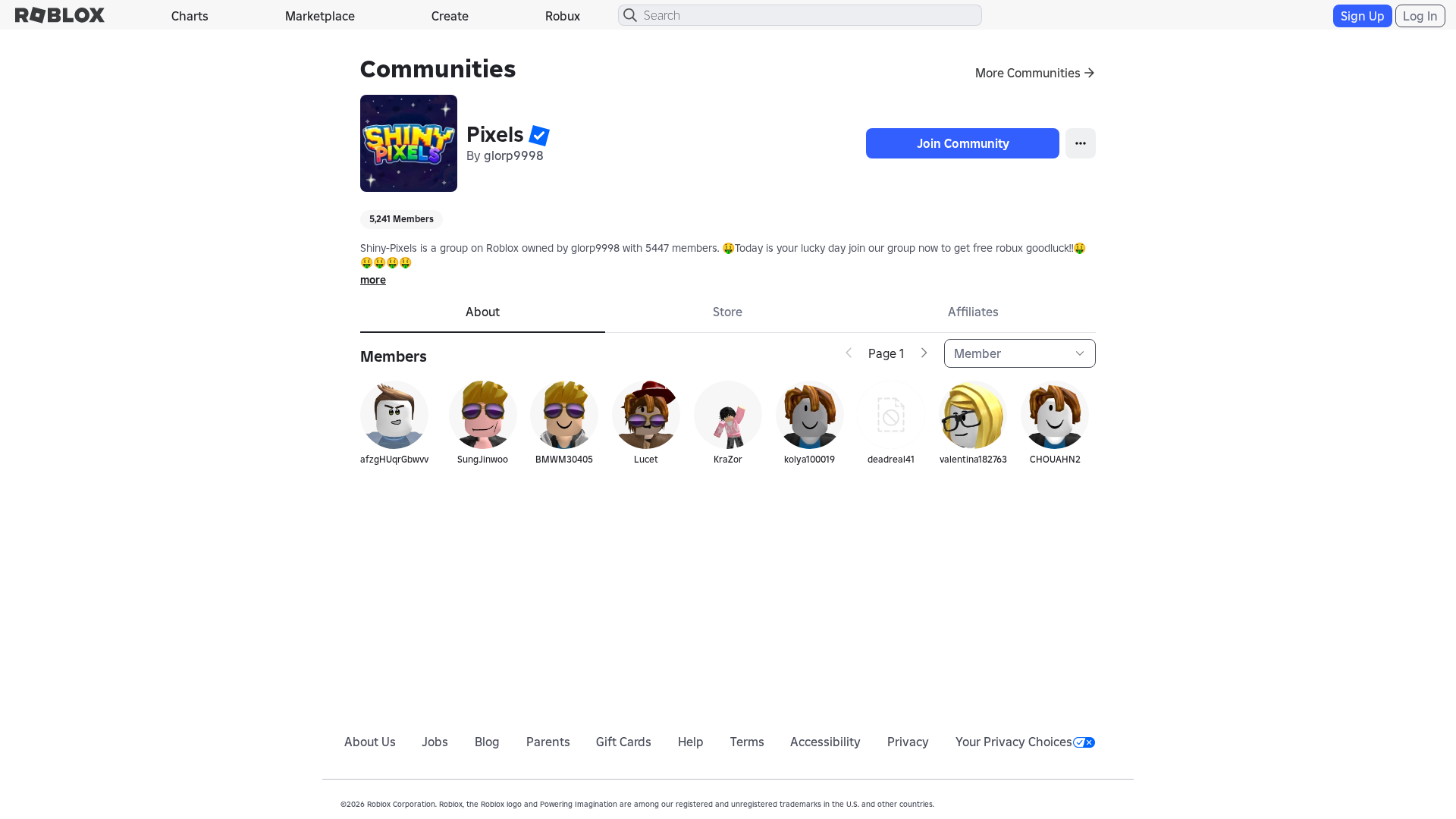
Roblox
https://www.roblox.re/communities/3297083824/Pixels
Mar 28, 2026
Unknown
http://www.roblox.re/communities/5012226136/Free-Robux/
Mar 20, 2026
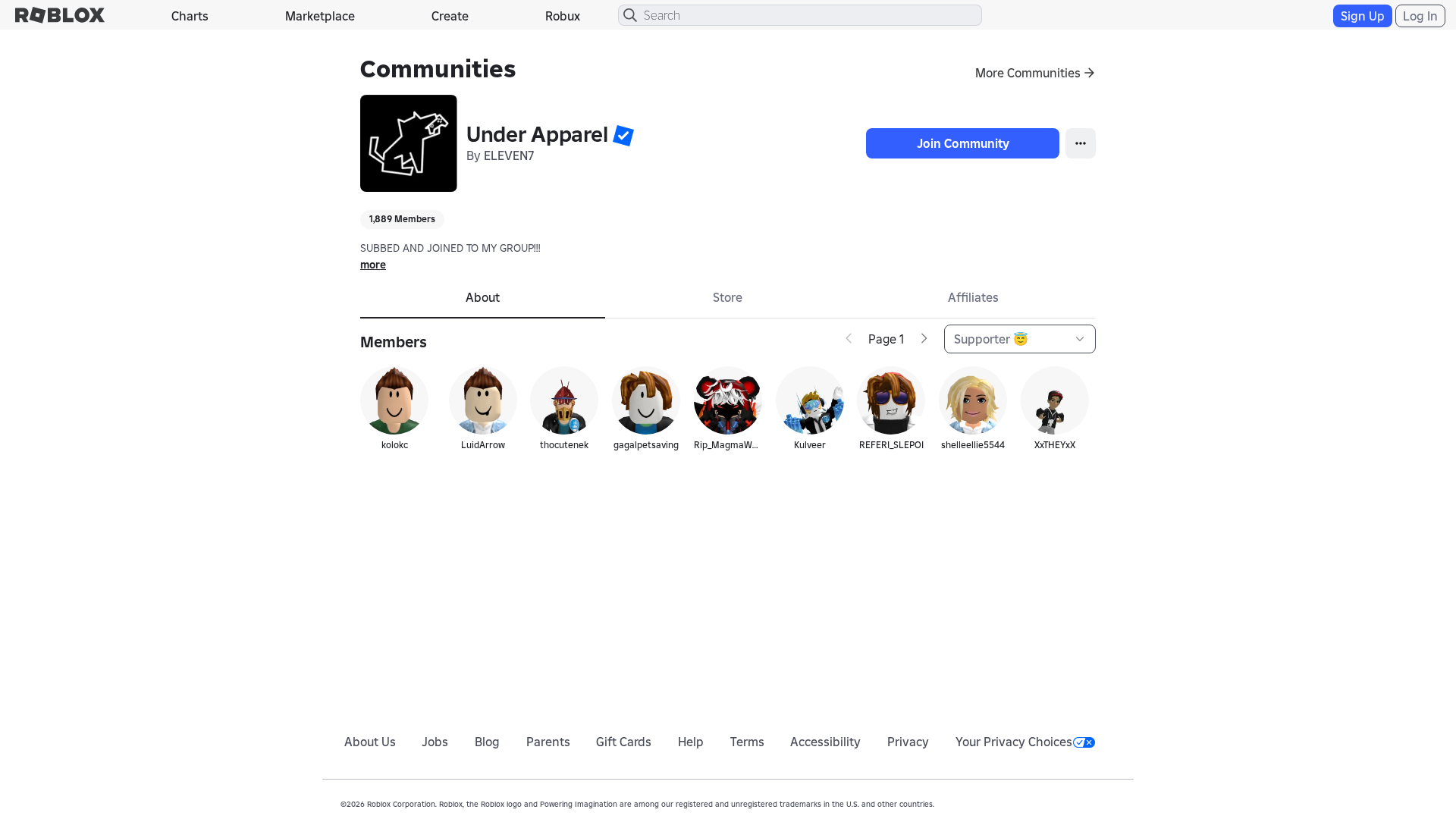
Unknown
https://www.robiox.com.ps/communities/1516628578/Private-Ser...
Mar 20, 2026
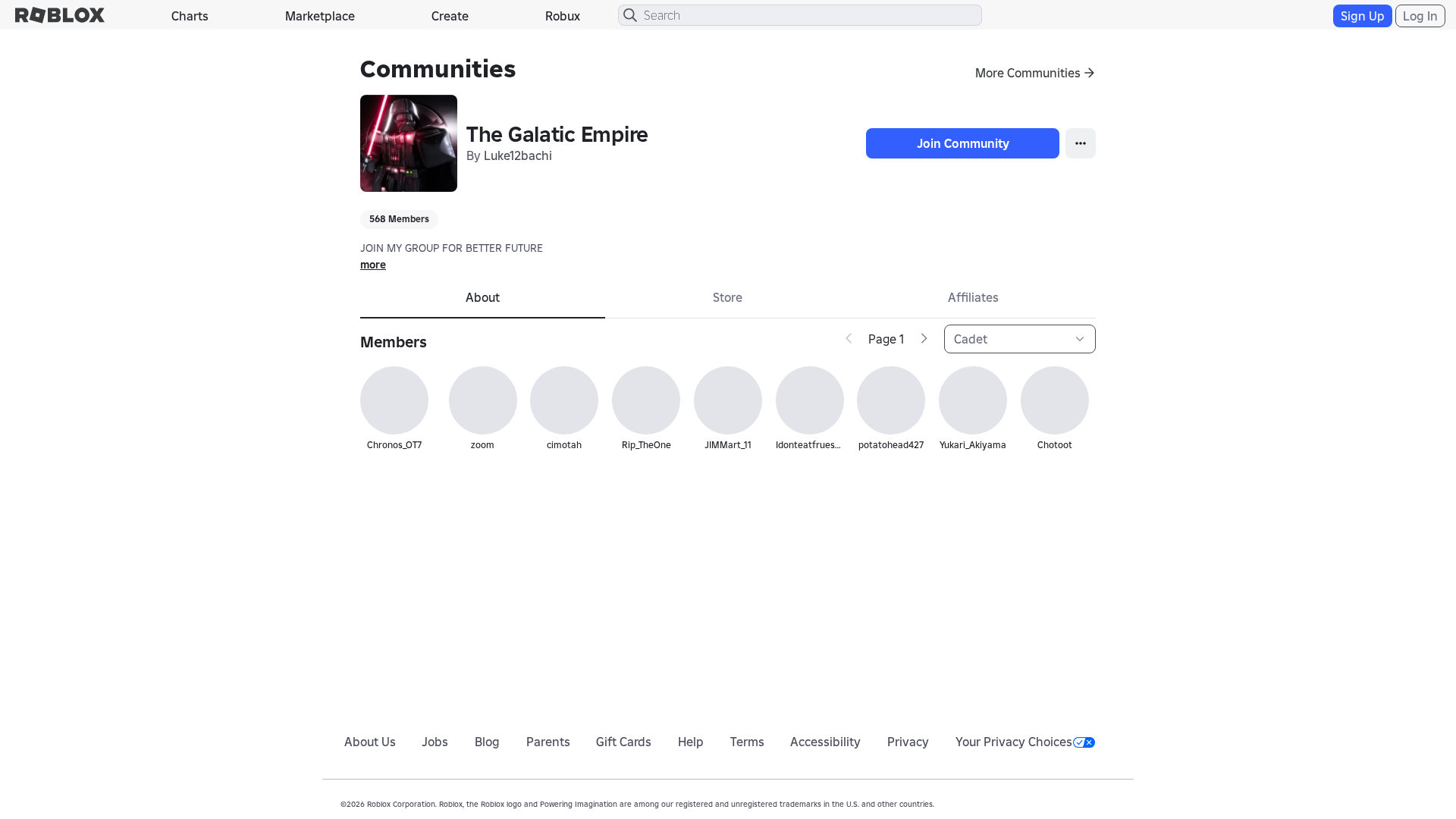
Roblox
https://www.roblox.com.ml/communities/3874207629/The-Galatic...
Jan 24, 2026
No screenshot
Unknown
http://www.roblox.com.ml/communities/1024247292/iShowJvn/
Jan 22, 2026
Scan History for www.roblox.com.ml
Found 10 other scans for this domain
-
https://www.roblox.com.ml/games/123573053194279/EV...
https://www.roblox.com.ml/users/4359662752/profile
https://www.roblox.com.ml/games/102438880728881/Te...
https://www.roblox.com.ml/games/920587237/Adopt-Me...
https://www.roblox.com.ml/games/83789872591767/Swo...
https://www.roblox.com.ml/communities/7111087128/R...
http://www.roblox.com.ml/communities/8359925132/FA...
https://www.roblox.com.ml/users/8640321039/profile
https://www.roblox.com.ml/users/5222656123/profile
https://www.roblox.com.ml/users/23215749/profile

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.