Phishing Analysis
Detailed analysis of captured phishing page
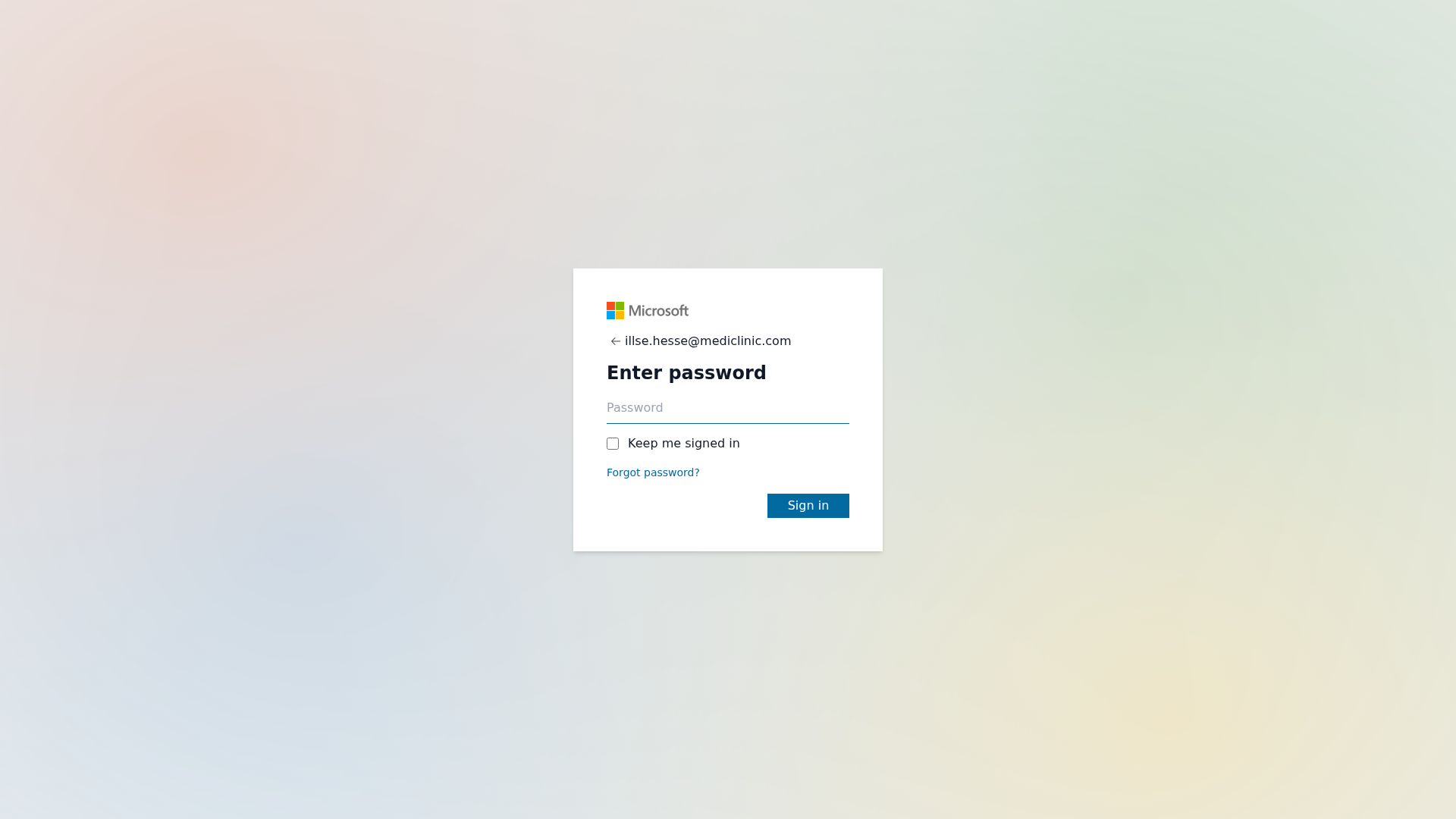
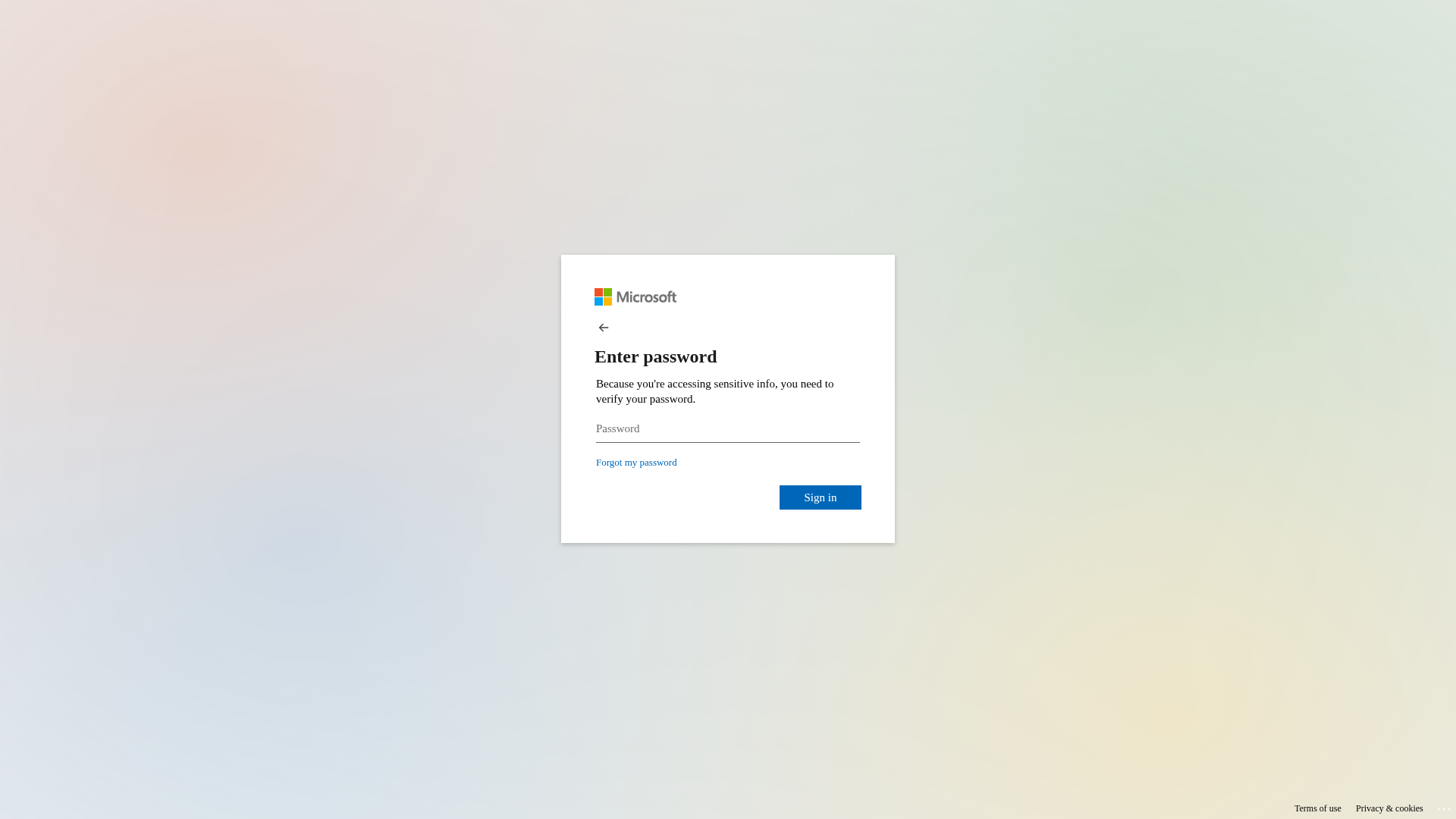
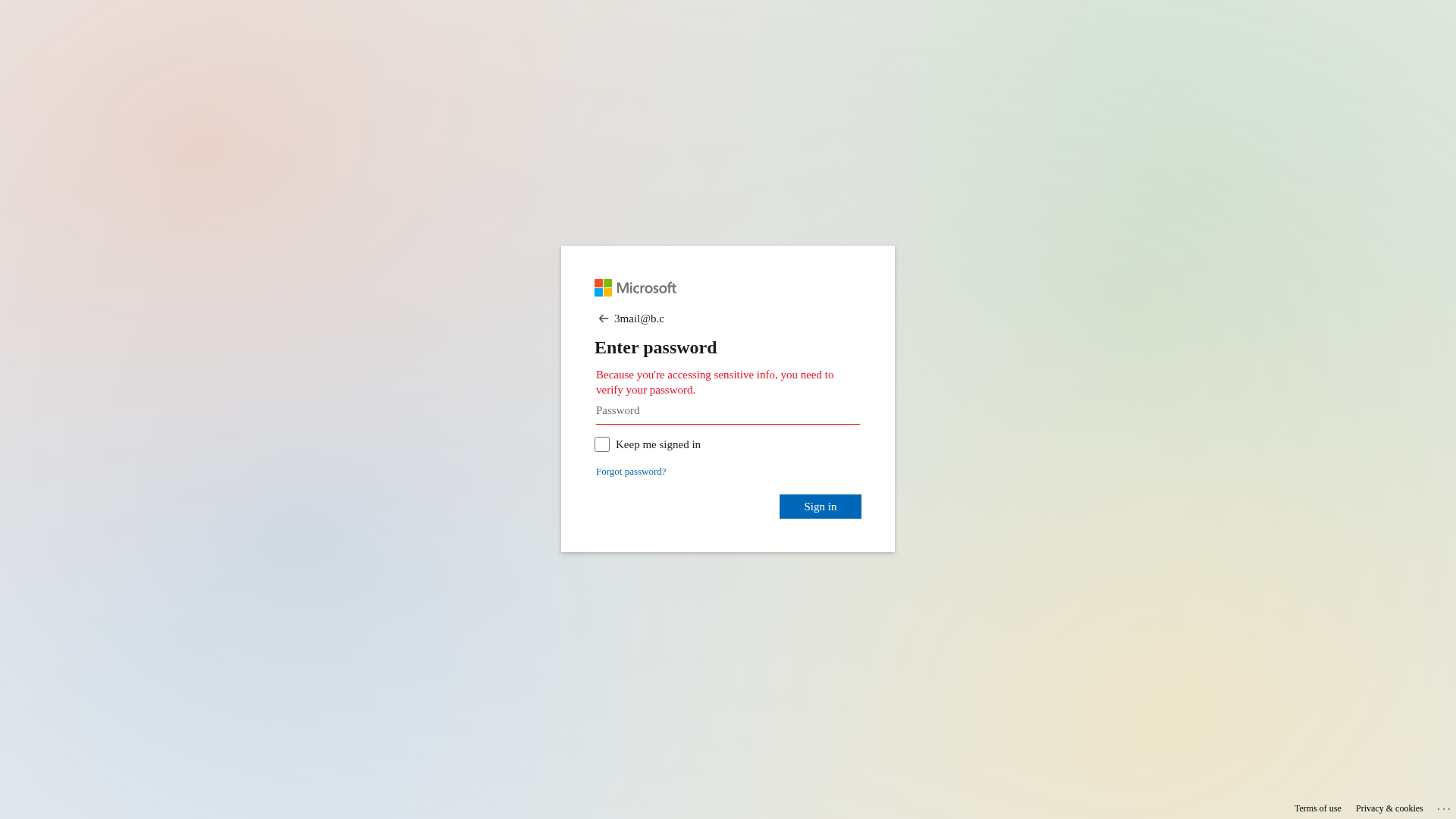
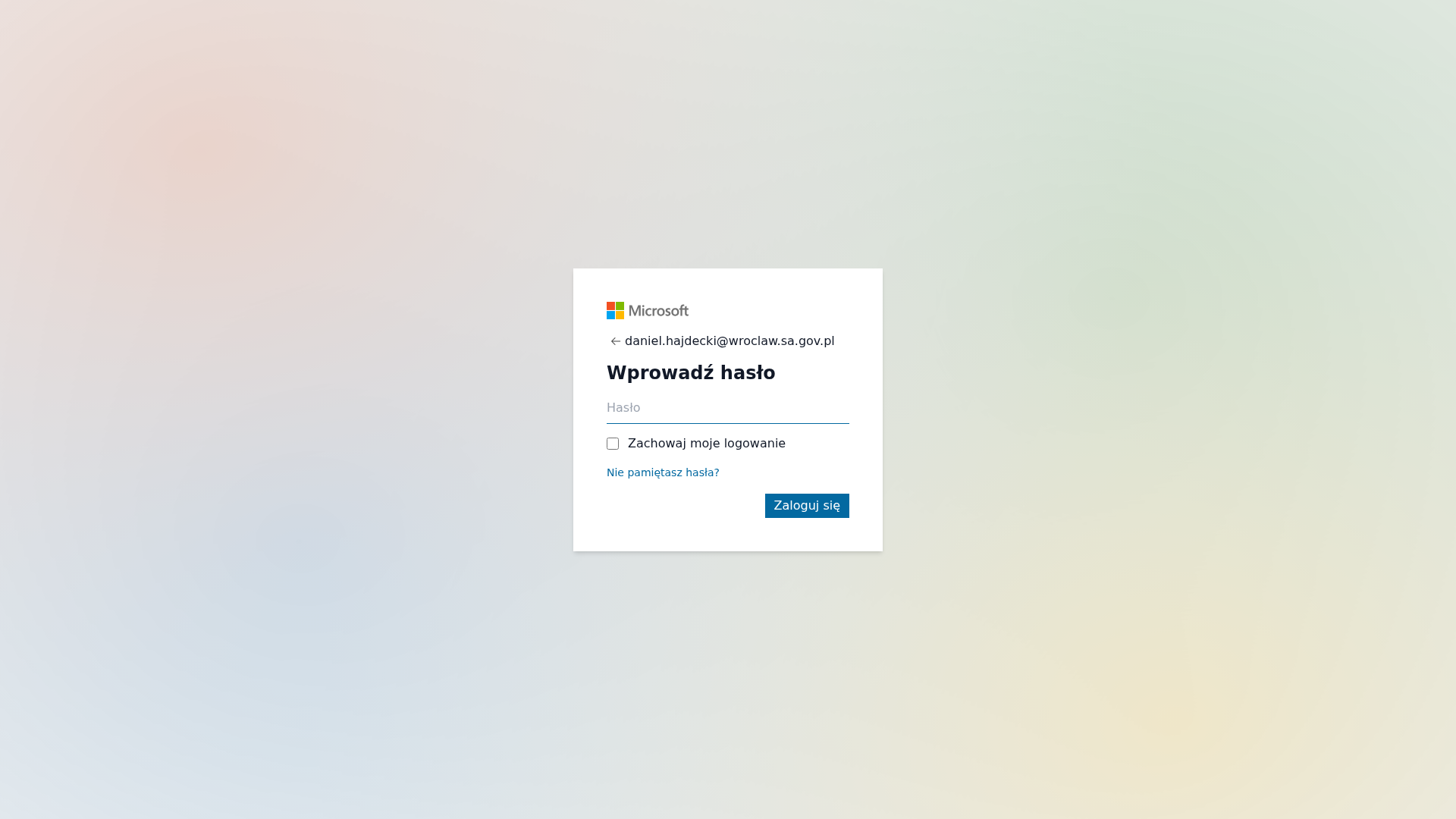
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1D641243060548C27918391F17AB07F0B299AC309DA775D85B7E993BB6AD5DA4CC002A5 |
|
CONTENT
ssdeep
|
48:YoHZA04uL5to4iatHRHBYzUS9ocmy1aFDgCESBw:NAAGZ9L2E/r |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9c4b6326d999cccc |
|
VISUAL
aHash
|
180018181d1f0f9f |
|
VISUAL
dHash
|
7161713331347939 |
|
VISUAL
wHash
|
191818181f1f1fff |
|
VISUAL
colorHash
|
07001000180 |
|
VISUAL
cropResistant
|
7161713331347939 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Microsoft users
• Method: Impersonation and credential harvesting
• Exfil: /link-action/a20XqKnKx0Piq0L6cU5ZaaZ693BBa8yV9ziF
• Indicators: Unrelated domain, password request.
• Risk: High
🔐 Credential Harvesting Forms
📤 Form Action Targets
- /link-action/a20XqKnKx0Piq0L6cU5ZaaZ693BBa8yV9ziF
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker aims to steal the user's Microsoft account credentials by creating a fake login page that closely resembles the official Microsoft login. The user enters their password, and the attacker captures it.
Secondary Method: Spear Phishing (Potential)
The presence of a specific target email address suggests this could be spear phishing, targeting specific individuals within the Wroclaw government. The attacker may have had prior knowledge or targeted the user.
🌐 Infrastructure Indicators of Compromise
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)