
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
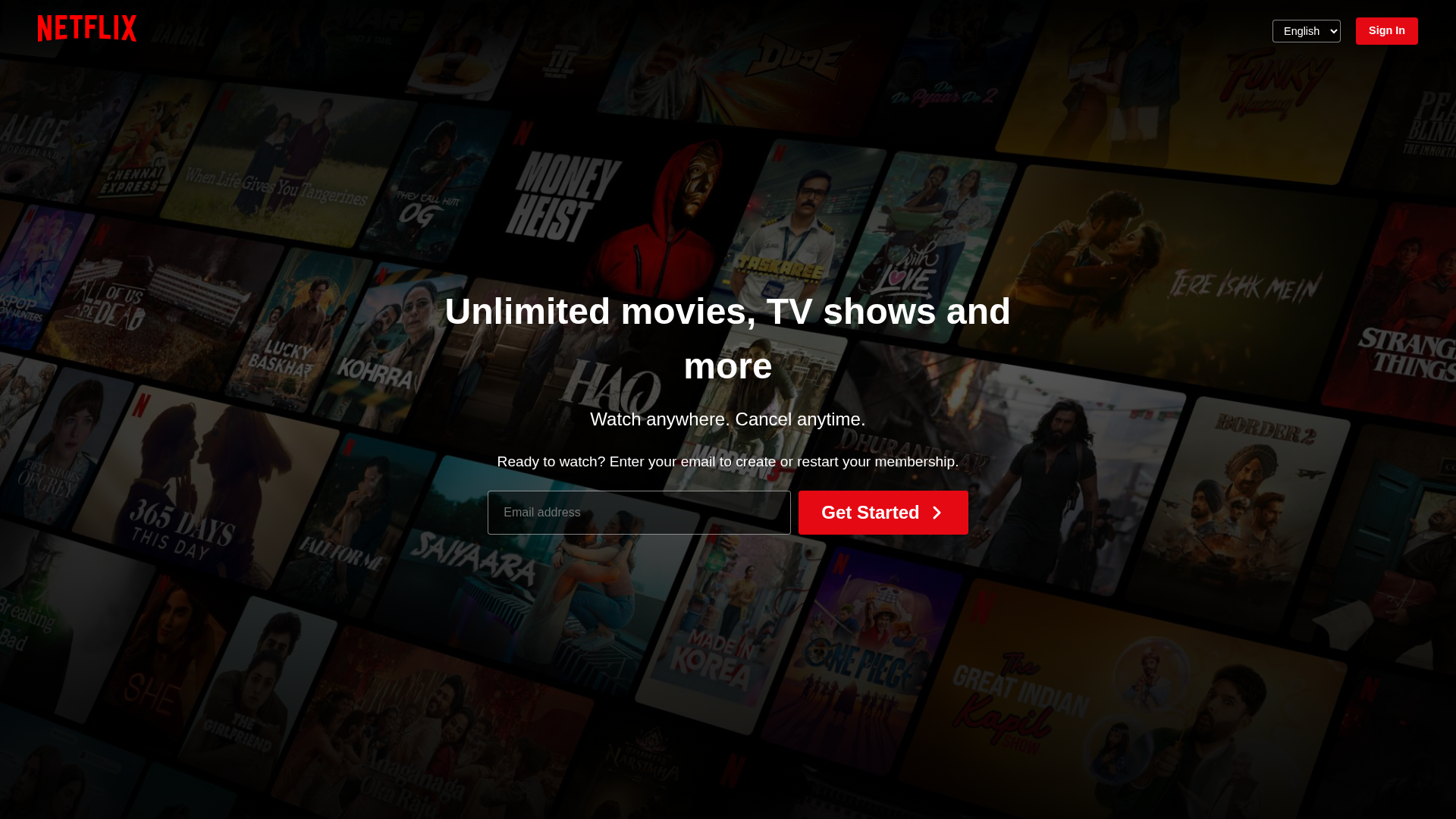
Detection Info
https://nishantparihar1102.github.io/Netflix-clone/
Detected Brand
Netflix
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
89297c18-592…
Analyzed
2026-04-06 11:22
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T14F3295BB1045A63B11A381E1F7796F2FB1928185CB561604A1F9C379AFD8E09EC637C4 |
|
CONTENT
ssdeep
|
192:/qj8p12ihsaErvC4NJ5gOaKf1nh9mgRnwIemTgj7O0f3tj26FPSi2xjWnxhsU:/q02/PrvC+J5Z5NVRnUfjfr2xSUU |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
99b3262caccacbb1 |
|
VISUAL
aHash
|
0042fcfedfb80000 |
|
VISUAL
dHash
|
578cd870b23294ce |
|
VISUAL
wHash
|
0146fefeff981a00 |
|
VISUAL
colorHash
|
30c00000001 |
|
VISUAL
cropResistant
|
578cd870b23294ce |
Code Analysis
Risk Score
50/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
📊 Risk Score Breakdown
Total Risk Score
70/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester
Credential Harvesting
Credential harvesting detected with 2 form(s) capturing sensitive data
🔬 Comprehensive Threat Analysis
Threat Type
Credential Harvesting Kit
Target
Netflix users
Attack Method
credential harvesting forms
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
MEDIUM - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
🏢 Brand Impersonation Analysis
Impersonated Brand
Netflix
Official Website
https://www.netflix.com
Fake Service
Credential harvesting service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: Client-Side Form Interception
JavaScript intercepts form submissions before they reach the fake backend. This allows real-time credential harvesting and validation without server round-trips.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
nishantparihar1102.github.io
Registered
Unknown
Registrar
Unknown
Status
Hosting platform (subdomain)
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.