Phishing Analysis
Detailed analysis of captured phishing page
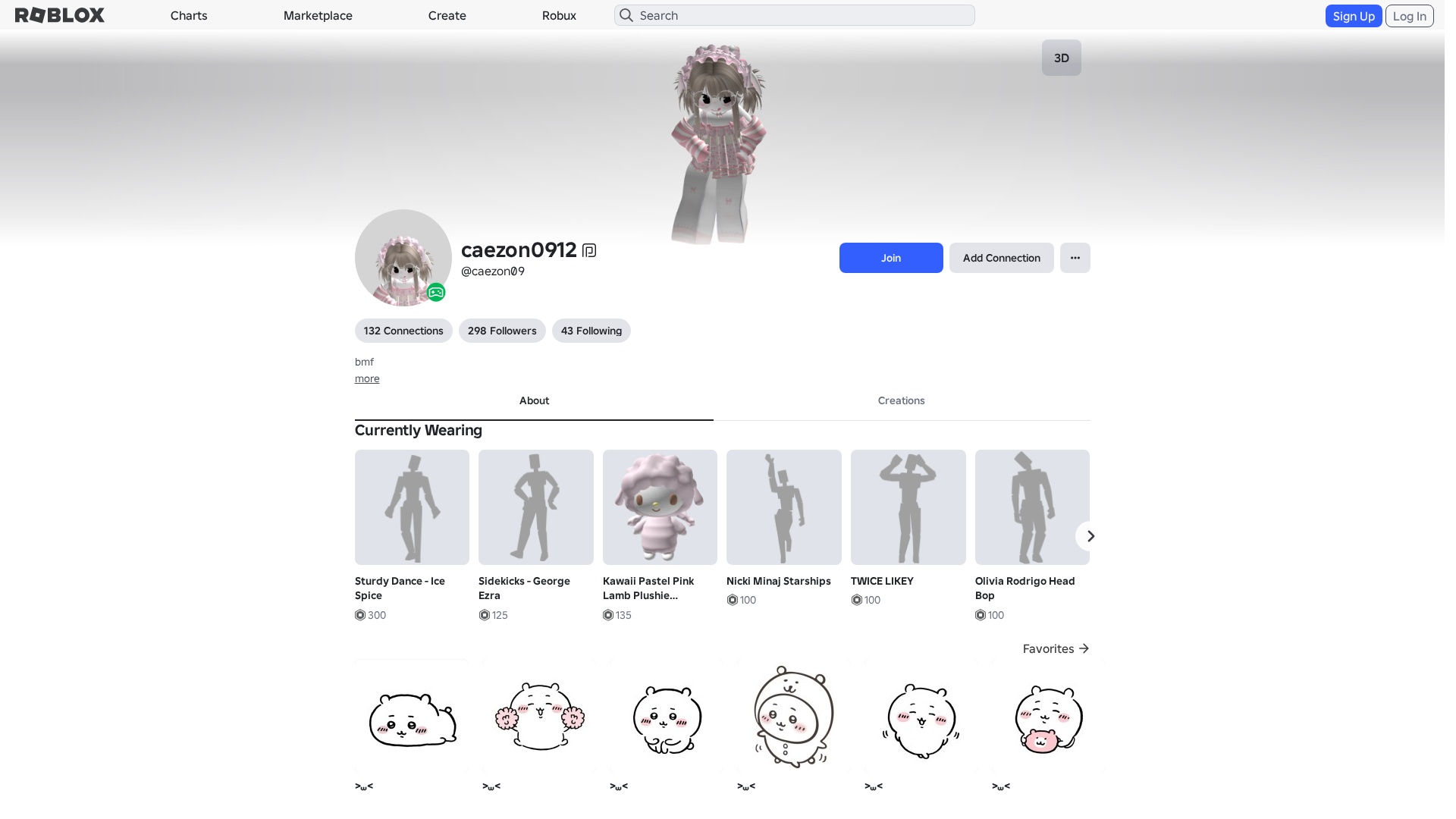
Visual Capture
Detection Info
http://www.roblox.com.ml/users/9001773404/profile
Detected Brand
Roblox
Country
International
Confidence
100%
HTTP Status
200
Report ID
8a319744-e24…
Analyzed
2026-02-05 23:43
Final URL (after redirects)
https://www.roblox.com.ml/users/9001773404/profile
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T14873867292502437617B79DAF164771AA2D3C70FCA8256E1A2F8939A0FD6CE1FC1740E |
|
CONTENT
ssdeep
|
1536:aYfXWn9r2vF+vOruaE+YuOYeZgZ57Hb7HD7H/7Hy7Hv7H37HE7H37Hn7HF7H37Hp:hfXWAvF1SRruOm777j7f7S7P7X7k7X7P |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b4164363999cbcec |
|
VISUAL
aHash
|
0000d3ffc3c3ffff |
|
VISUAL
dHash
|
c8c83630161e0006 |
|
VISUAL
wHash
|
0000d3cfc3c3ffe3 |
|
VISUAL
colorHash
|
072000180c0 |
|
VISUAL
cropResistant
|
c8c83630161e0006 |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Roblox users
• Method: Malicious website designed to steal credentials
• Exfil: Potentially user credentials, personal information.
• Indicators: Suspicious TLD, Obfuscated JS, Form Actions.
• Risk: High
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://www.roblox.com/catalog/2510233257/null
- /catalog
- https://www.roblox.com/catalog/10647852134/null
- /login?returnUrl=898530923948889
- https://www.roblox.com/catalog/607785314/null
- https://www.roblox.com/catalog/12995014400/null
- https://www.roblox.com/catalog/10638267973/null
- https://www.roblox.com/catalog/12995018829/null
- https://www.roblox.com/catalog/2510230574/null
- https://www.roblox.com/catalog/12995017412/null
- https://www.roblox.com/catalog/2510238627/null
- https://www.roblox.com/catalog/2510235063/null
- https://accountsettings.roblox.com
- https://api.roblox.com/users
- https://www.roblox.com/catalog/12995020128/null
- https://www.roblox.com/catalog/607702162/null
- https://www.roblox.com.ml/catalog?CatalogContext=1&Keyword=
- https://www.roblox.com.ml/info/blog?locale=en_us
- https://www.roblox.com/catalog/2510242378/null
- https://www.roblox.com/catalog/301811432/null
- https://www.roblox.com/catalog/2510240941/null
- https://www.roblox.com/catalog/2510236649/null
- https://www.roblox.com/catalog/12995015868/null
📡 API Calls Detected
- https://apis.
- GET
- https://help.roblox.com/hc/articles/30428367965460
- POST
- get
- https://ro.blox.com/Ebh5?
- babylonjs
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Suspicious TLD
The use of .ml is a strong indicator of phishing.
Obfuscated Javascript
Obfuscation hides malicious code.
Form submission
Form submission is suspicious
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Roblox users (International)
Attack Method
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
HTTP POST to backend
Risk Assessment
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 300 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Roblox
Official Website
roblox.com
Fake Service
Roblox
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The site likely attempts to harvest Roblox login credentials through a fake login form or social engineering tactics. It mimics the Roblox website to trick users.
🌐 Infrastructure Indicators of Compromise
🦠 Malicious Files
Main File
https://js.rbxcdn.com/a3fe79f1bfdd96b7f0ad20eab2de7a05.js
File Size
Functions: sendData(), submitForm()
📊 Attack Flow Diagram
User fills <input name='username'> → submitForm() → fetch('https://api.roblox.com/users') → credentials sent to attacker
🔬 JavaScript Deep Analysis
Operator Language
English (1%)
Total Code Size
3.6 MB
🔗 API Endpoints Detected
Other
95
🔐 Obfuscation Detected
- : None
- : Light
- : Heavy
- : None
- : None
- : Light
- : None
- : None
- : None
- : None
- : Light
- : Light
- : None
- : Light
- : None
- : Heavy
- : None
- : Heavy
- : Heavy
- : Light
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
User fills <input name='username'> → submitForm() → fetch('https://api.roblox.com/users') → credentials sent to attacker
🎯 Malicious Files Identified
Main Drainer
https://js.rbxcdn.com/a3fe79f1bfdd96b7f0ad20eab2de7a05.jsFile Size
45KB
Malicious Functions
sendData()submitForm()
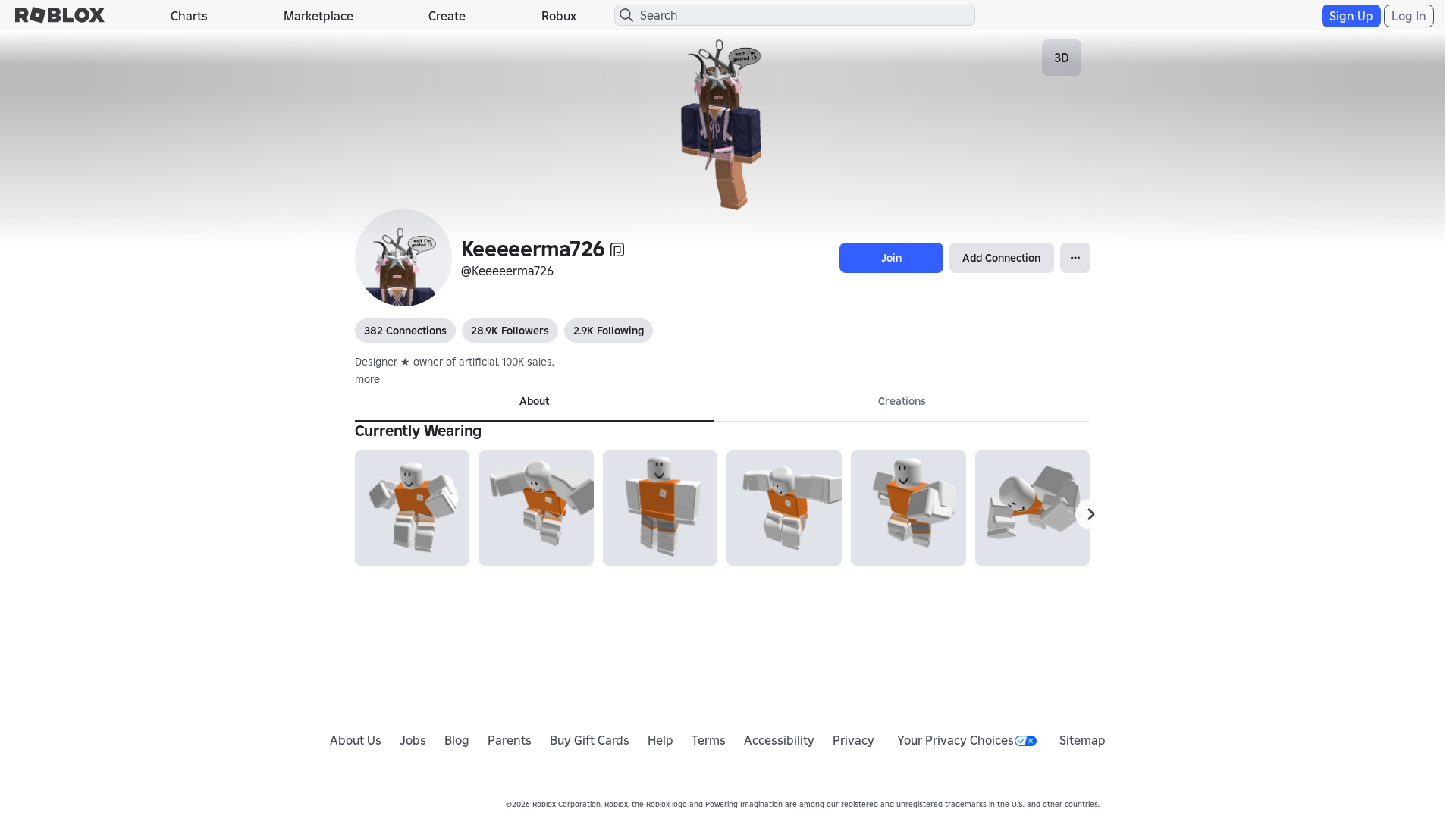
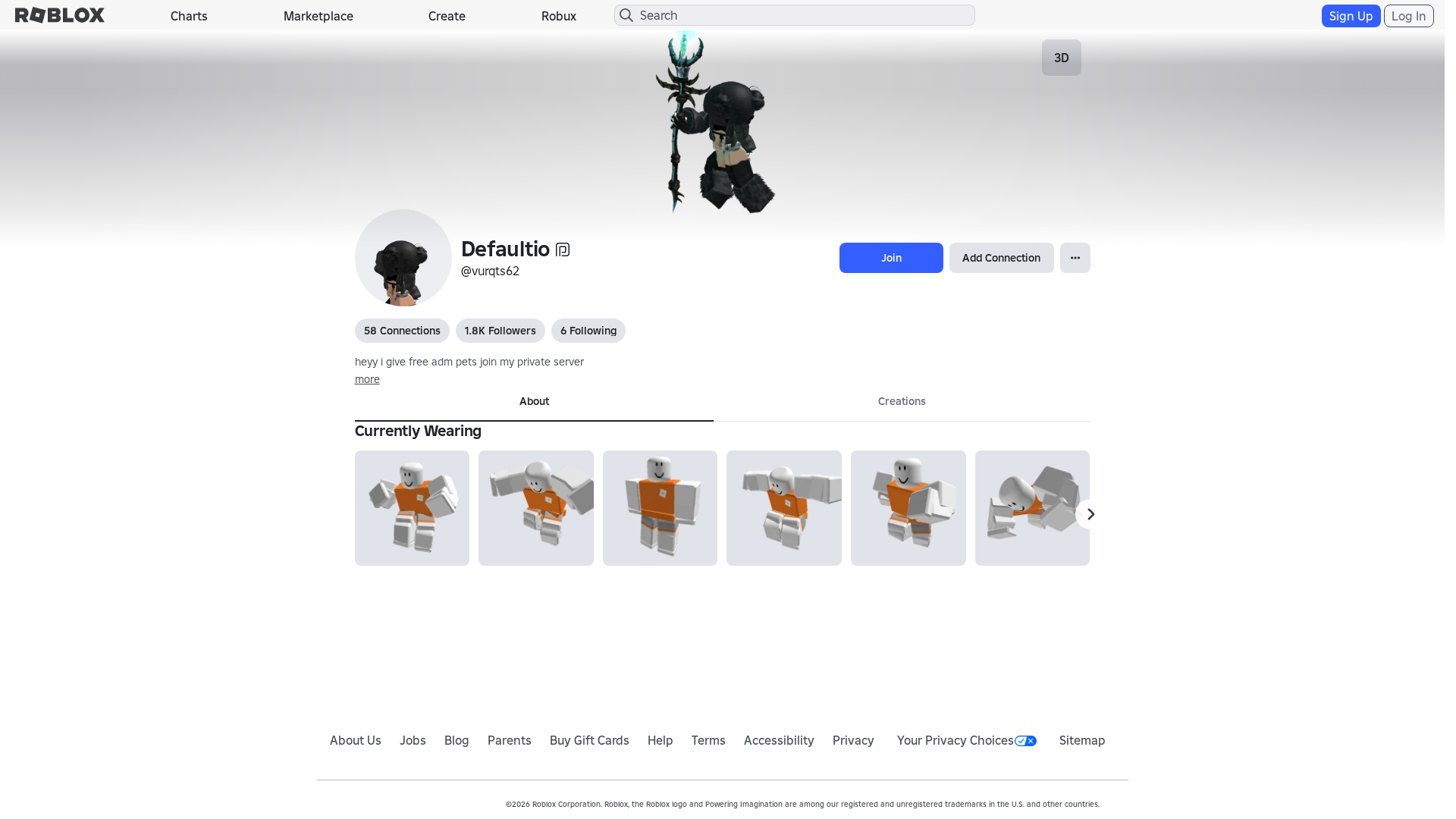
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for www.roblox.com.ml
Found 10 other scans for this domain
-
https://www.roblox.com.ml/games/123573053194279/EV...
https://www.roblox.com.ml/users/4359662752/profile
https://www.roblox.com.ml/games/102438880728881/Te...
https://www.roblox.com.ml/games/920587237/Adopt-Me...
https://www.roblox.com.ml/games/83789872591767/Swo...
https://www.roblox.com.ml/communities/7111087128/R...
http://www.roblox.com.ml/communities/8359925132/FA...
https://www.roblox.com.ml/users/8640321039/profile
https://www.roblox.com.ml/users/5222656123/profile
https://www.roblox.com.ml/users/23215749/profile

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.