Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1F2D1652FA2983326878345DA767F12DFCE6A00DC47B2DFD9D8B4981CA2E941C46760D6 |
|
CONTENT
ssdeep
|
192:qP8waviqt6T2OuGvYR0wOFT/z0MjyyPSxj9mnCb:08waviqt6T27upCyaxECb |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
bec9c13c30c13e3e |
|
VISUAL
aHash
|
ffdfbfff8383ffff |
|
VISUAL
dHash
|
fb3767c72e2ed3fc |
|
VISUAL
wHash
|
1b0313f383830f7f |
|
VISUAL
colorHash
|
07201000600 |
|
VISUAL
cropResistant
|
fb3767c72e2ed3fc,929dcc8f98adac54,292c54dce04c4c4d,edac9c8c9accd839,24a7ceae8c8c5a55 |
Code Analysis
🔒 Obfuscation Detected
- fromCharCode
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Personal Info
- 2 obfuscation techniques
🏢 Brand Impersonation Analysis
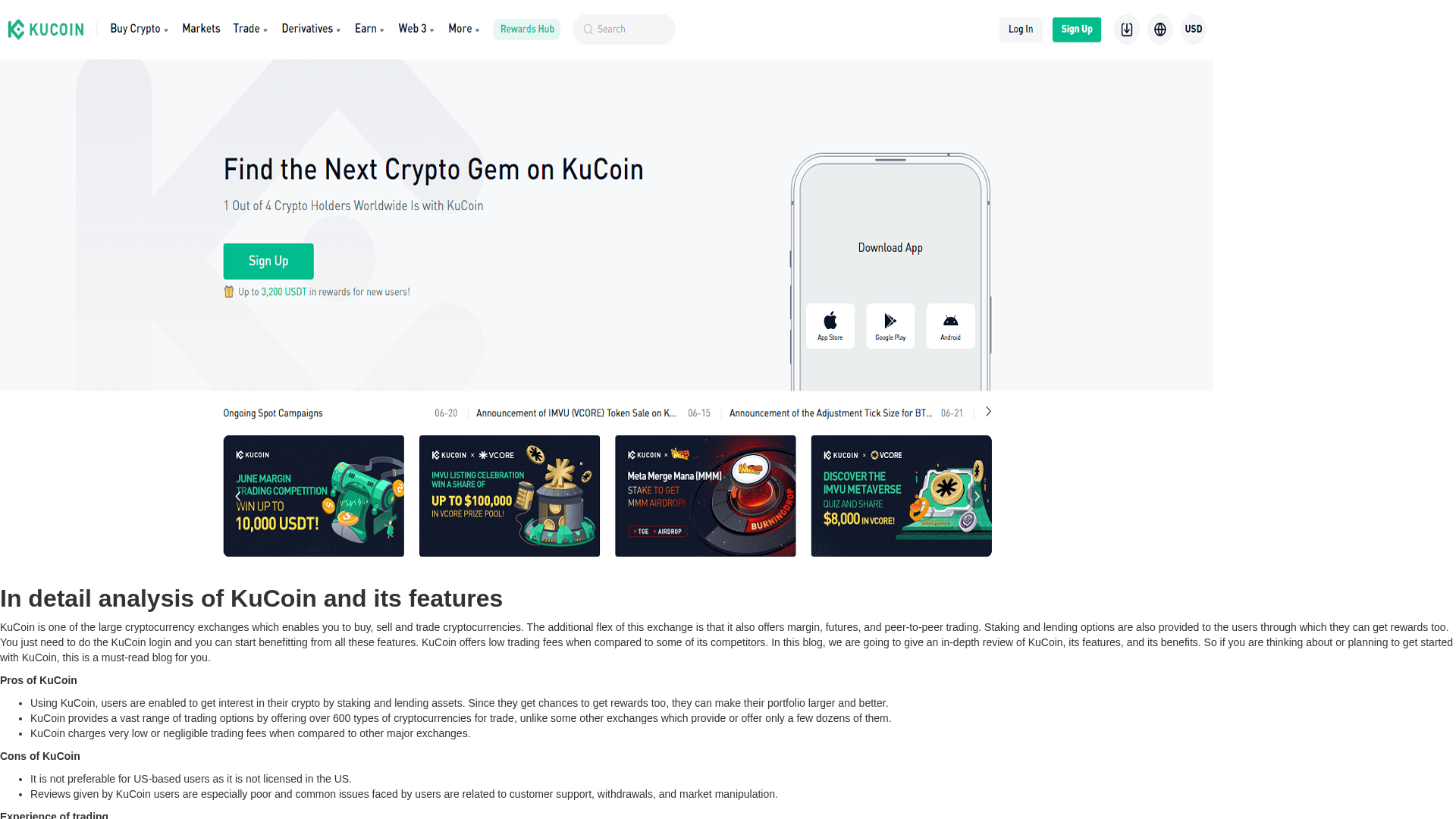
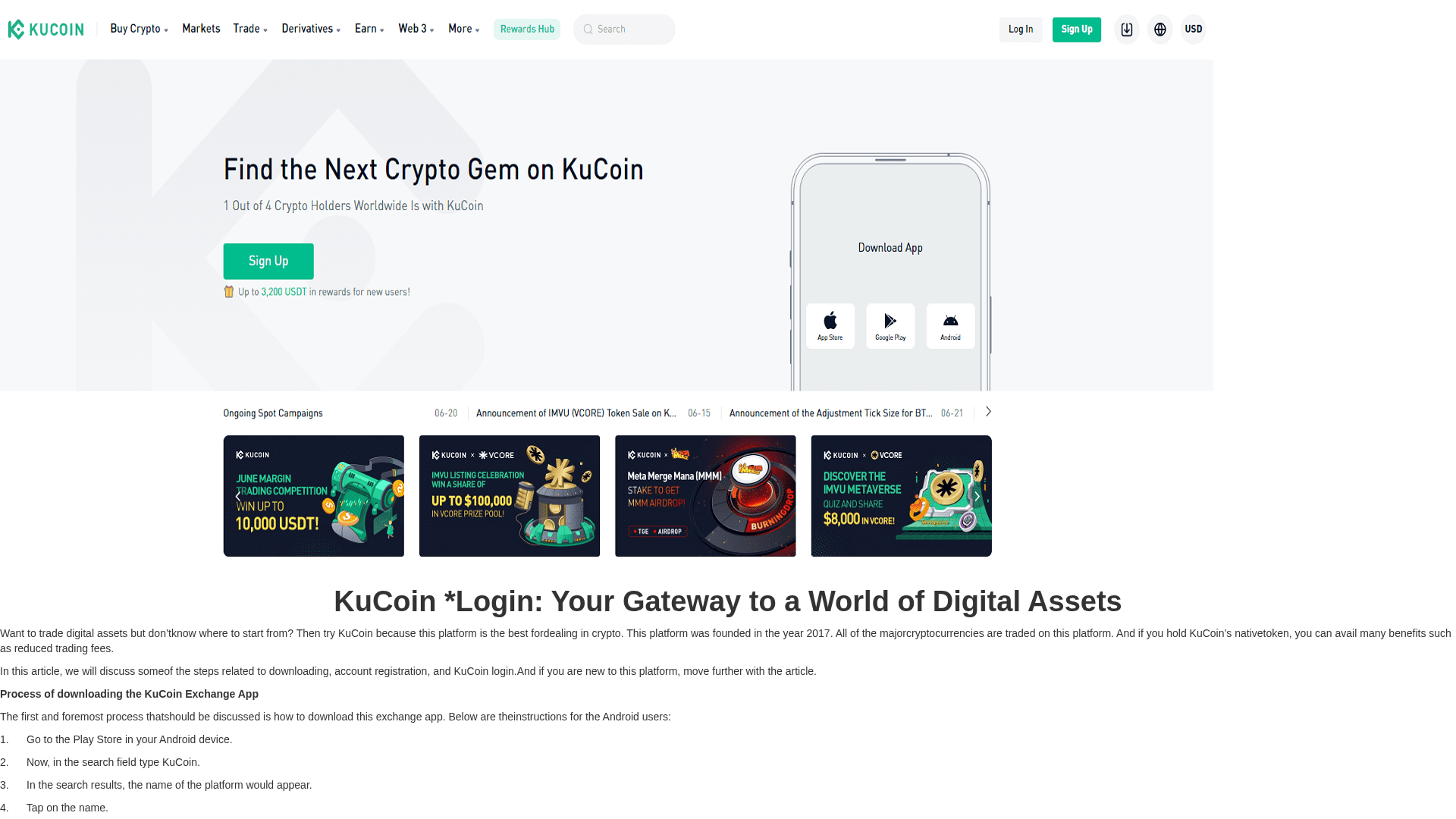
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 2 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for kaocoinlouigns.webflow.io
Found 1 other scan for this domain