
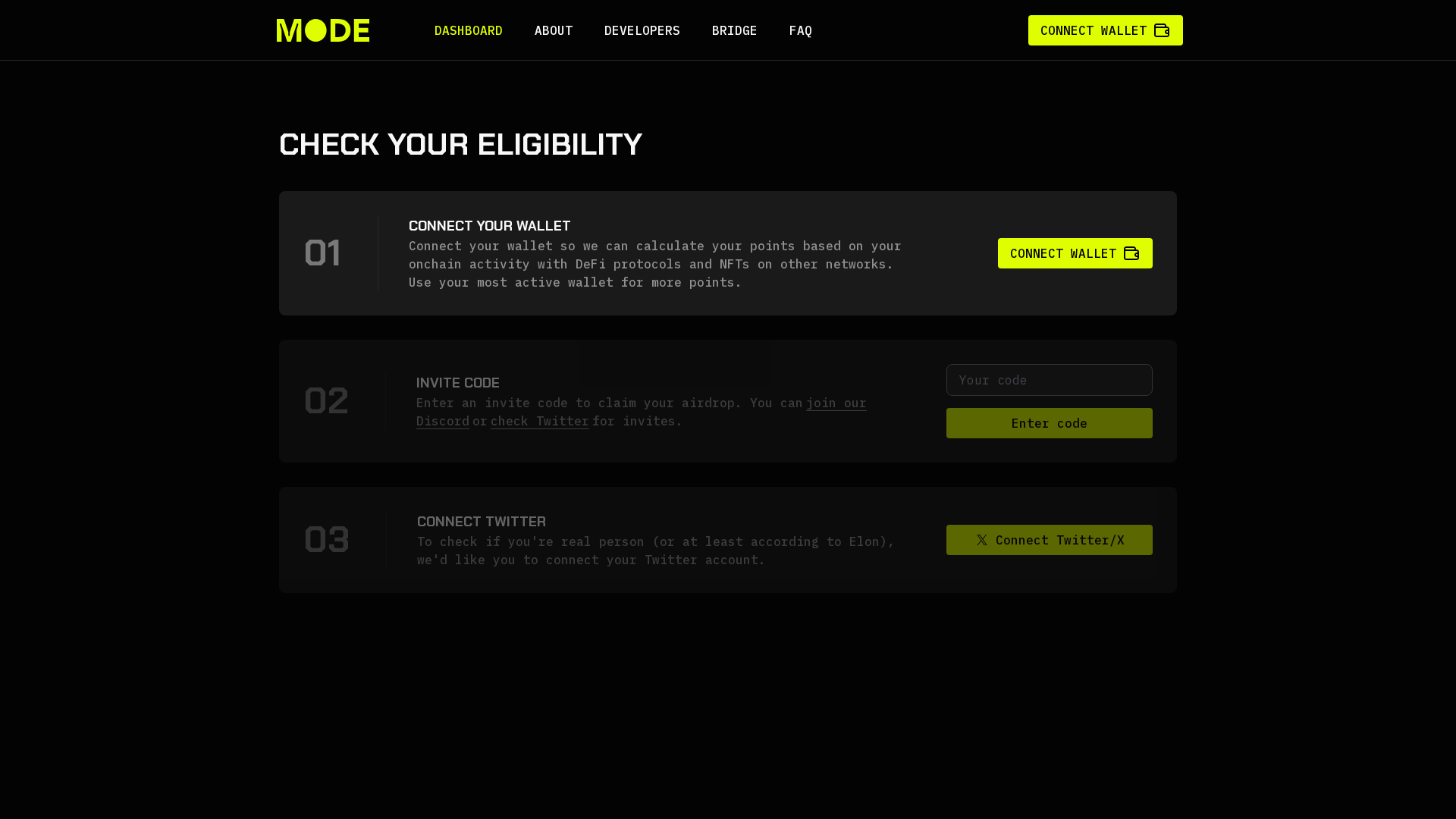
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1B472D7787EA431B9310747B8B1959B9EF15B121ECB13ACE4F2C892D453CE8B6CD851E8 |
|
CONTENT
ssdeep
|
192:ATnOiRwdp7Rwb51kgaDXaip5gUNo8ewwYFqf6rMIo8ewwYF+SP9MYb:SnOAwuSO8eV58eyvb |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
96d66d3434b49696 |
|
VISUAL
aHash
|
66707e3e36360000 |
|
VISUAL
dHash
|
d4c9e4ccccec1204 |
|
VISUAL
wHash
|
76707e7e7e7e0000 |
|
VISUAL
colorHash
|
38000007000 |
|
VISUAL
cropResistant
|
d4c9e4ccccec1204 |
Code Analysis
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- unicode_escape
- js_packer
- base64_strings
🎯 Kit Endpoints
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAIAAAACACAYAAADDPmHLAAAACXBIWXMAAAsTAAALEwEAmpwYAAAAAXNSR0IArs4c6QAAAARnQU1BAACxjwv8YQUAAEgiSURBVHgB7b15rCXXeSf2naq629t73zeJiyhLIinJtmx5oWJgxhPb48CTEew4iCUgQIIggWUPEiR/BLb+ySSTAJaBAIPxeGAJA8y+2GOPZzyjkWlZsjYuTZESSbHZbPber99+392r6szv+75zqk7Vva/ZFCmKlvo0qu9999Zyzvm237eccw19h9uNgT0bT+gxMvSIJTpjiM6SpRX8fZbutbJZuoQ52cIcXcJfz+Dv83mDzh/rmEv0HWyGvgPtRtc+FhP9VxjEz98j9Btshi5FRI9bS585tGgepze5vWkM8Iq1Kwu79Kt4+wlw8Qrda29+AzNQTp/MGvT4m6UZ3jAD3CP8W99AtC389+k0pt9+o4zwhhhgddf+qrH0m/cI/11qTiMcXjKfpm+zfVsMIMAupd/D28foXvvuNzBCFtNHvh1tENHrbCz1SUpP0z3iv32aJRbIp29u20/Q62yvSwPc7trfgrp/3Q+51966BoL+JryFT76O8++ure3Y38sNfYzutbd9iwAQDy6Yj9/NuXfFALe69jxOfJjutb9M7fzhRfPoa530mhiAJf8e8f9StkfWdu3vvdZJd2QA2PzfuKf2//K23NLHbu/a37rTOXuaAEb7QJefonvtL33Lc/q1o8tmJi1nMgD7+ezq3QvwfM+0rSyhR2fFCWaagDijP71H/O+ptuICd1NtigFWd+zHOLBA99r3WntsVqCoYgIkxAvpv8cA37Ntq5fSuXP7zJb/oKIBYPd/9R7xv6fbylxSjeQWGuAe8Pu+aRUtUGgALtu6R/zvi1bRAoUGgN//yj31/33TthAm3sdvRANwDd894n9ftZXbTHNyDBDbe+He77dmuWiXPAaI6CfpXvv+aoZ+Xl5cedcr9D3cwO0Cduqve533/dIyeANJNKFHvldHbevv8Z/FWK3Vv62juKGA8KZ6XfBx5V7fC1MWN+ixhFfs0He5fbsTal/rQyOZMBqOLY3GOQ0nhvpjojSTVClO1afGMIRxbKgZE7UaRG0cTT4SBMeikmH8PT0jmTfY/+96s/RIwv+9kd7bvT6YNTszvjPm9U2efY0v+fsRCL7Tz2hz19J2z4LohkapoQxUKwiPB/Ozo0gPZoIkVoI3YiV+G8d8m2gJx1xLP6togsCmWFMd2t2OwdTuU364x8Vm+pRvl3yYi7MJBn/G2ru/KFSbXq1WehH2bEoHU7W3Th2Hf1P9NrPEawZTTbKcNncyurWV0+1tS7tDSDskfsKEzw2eE5GNmOhGoK+JA+LHSnxGxPweykAYgd83+2AEvHaaRMvMDB2ixY4yyVRnzXR398Qdrt/W0DTB92KI2nMq96DXzwhg+jPJ3Ub/KsQOOD78Ls0s1C3RYKyfxZhwnrh2UwoVg5OrNnfWgOsfVSYjYJz+MKebGxO6tpaB8EQ7AyOqfpKiPzmJpLPEM+EjUNYw8Zm4kOaIj1jS36IB5L3VvopZwD2AkSjB340R0TqYoQPTsAxtsH+eQ2owGU03lj2IU/Q1ZHYz47z6fKPvExxj9CGzekkD/W06Bp2aP3r9Zolpb1a79rW0avWOdvq79a2ULlzN6eJNSxu7EU2szmCjaWgRE3V0n6FTB4hOrqhKlfHP6F04kVOS4873vR2NM7qyOqGXr40h9Ya6fZb4iMYTVvOQ9twRnqUeYm5iZQAmOhOfNYBIu/tb3nsmiJQJ+JGRWguZdD4EJ7BpaKhpOIjxHZhX7BB0c4quxedm+ktry7EyPrkORr61S7Q2AAPkeg33iZ+7CIY7CMY7PK8ayVCNGWr0ei0muHsGmNHZ3X5OX35mSM+8mIMJIhqkEWWYWQP9GTUjStoAVlCXbXR2AccxMMDDJ4jeAWZoRFUmME5CzCz9GUxaDsN1bXVEz18e0/U1S1tdI+p+BOKzqs8zHO4ikBsEZ8K7Vz6aSuyo4dQ+Az33XhjBmQVnKYpny99MCNJzMTzBCAu43z6M8egitMJCoOnqY6h9Vtf4DFavrBN94wbRbWjQEX/OHXB98UzJ89bCsYA+n17CXLJQNcs5pBkm9U5MkOz1xZTk1767dHVMf/ynA3r5Fdjbfgypt5RHkLmG1UluSYKJGuBoaGkwB9Q1/t4cEl1GHuqHT0OCWtOS7pnAhj3P9aWPmzx3oUcvXknpNhiOpX6Ie04g9Wx+BOC5jkeYrchYR3j0JTdq43HPjJSIOU9s7lB+cMSuD3k4EXnZHQyTRvhjxGNz4+qCYocxtuNLavL8zLO5oaBfRLX3OEYjS1972dALYIAePypRyjDBI2eSTK6vI/Zq8LqL526DUW52iR6EQJ1eCfDZLDyxR5vJALPAl+80vz77Yp/+8E8GdP2GoV4/0skXfYlLmph0UCLGidAFwsV88GTmeIWACkP0MYAPgwkOzDm1mLtHmprWcX9cXx3Q0y8O6JXrQPc7UPdDuHYpgz+APH4+n5q7i3nSMHPs2jGBY6dGWbItS32uz2NNwI/OciWUCTRO7HGIpYKxfN+YGHi02OiJVTXtmaEHopxYhlaYp6IvlTmlAEpZxjBEn33G0KUdXM/M0nRglLTPthyS9IO7x2aCmYHxAQtAd6wCdt9+1RTSTPla6Tu9BgNMTb67gR/AN18a0j//Nz1avWlogM6nE5Y8i45aZVd+If3bskZgBDVxE88djZUhLkILpDj3J86ACTr6HC91BQdbVfkvvdqlrz43oBur4PpdIxI3wnNZ5Wc4KReUrzPE1xonNTkgrs1VM+QO1dvMYYBcz8usTrjjieJ95JhRrvW0zMt58Go5ZSaMlBmYCUZOI5zAcWwpMGm2imO5vz3Y+D95kuilDVwPbWgcFolCLyUAvbnviHvlr/AYYYQRTEeG57/7cIkzTI0JZmmCaQ1gaxcFxLh8fUT/5j90afUW0D5UHttbaU5EcsMEUGnkAfCBcCMZRtOZ41y8H6PXsBp0FUDny1eJfvKM2rEQX/DBkv3157fpyW8y8S11ISLsYYzFp1fGy0S6nZhmykERqM0mgEdnrOpRnlzW/ZEtiZp74jv7njsGjJzkhaA096YiQO+5k8TcMRJrBX5lrTBhZsA4T+1TbRJOr5fmzz5h6YVbhsZNJVbi8EfkiB+bgAlz14dcn1thgkiJ/8xNxCtwrzMrNUx1BzOQzKJ9HU3y50Po7X/7uR26fCWn8diom5coYXlScow8Q++YKSwIlMNIGkig/D1Ru5anqm55kgDiaYDPIdz0BLj3R0+pu+XNwBgi9cTXN+n8N4Ygfg7iG7F/YwDNlJ/DegYzYnPWN3jFcwzfmG09HsIuqLh5PJMNN2GZPp9yqkb3AsKQmZ4Hf27m3+eOuUlVtTBArn/nbnz8d+qOM/sDk+Ke86WnLT17CRimqcROklLqOcbAh2eu3JaE5znkV+sONXd4jpvfJ66qm7rSmc0EYRxnigEqLp6tTswXn9qlly7kAljYp05cVMwAMVmOsGWqDlPo9QxHDsNrwCg5onJ5w+jE4EgyNxDHBIwFLsAcnACKPrvsOB4z+NWnIfnwMG6upgBYRtRripvwhDLx2TRYzKrV0J5OiOhDED9T5E9zkUpL5kBUSPHAtvo3psYMXiPxf7kjgGAaokIC+W8+JzalhvCMkjmG4/en95cewirA3l88DfzEhGirxBtnoryv33TPGTnJTx3xs4mOM88CTWD0HhbMBCVAX4dAffiMwzghExBNud9JneBhwMKj4o3tlD7/pSF1d0v2kRAuo2xxtpgY1rlPqg9zZgK20zgiaARW/TYtVZmfQB7YDtT6l64AOIFzO9AaT57foS98qU+rt1OofGgczHLSiWhxMaYmnOEUBN4GaNrtqYmRfjJnABgaPM8wJmhxPyLphyD43Kn9TKVWCO4Ak3HuVsAbxRthHFIJzJwKFvo7LuEQ8QKIuDinsQD2LtIJSUBsF2Zy3FdNN8D7+w/rPf7kc4idoO/5kpP8ICLZitW9ZP4deY2ZuoOJj/tkY32fT9xcRurOZk47vIi/z8L0nFopiV4AwVkaYJbqL9wivP/y+R6tbeQKtrxNzNwN2e7Hpf2SzyD1E5ZQxwS559i8tKXh49hergFQPgX1tdjr0+N/NqIbNzIh/qFTCZ187zy1j87RGHoxwwy3YCvm0fN0O6NvfG1ELz2XUgYIbiEu0dAqLSNTmK8QvPlsoFerMgNO0n3wx5iqSTBUjjl3BGE+n1+ARgLRb4KCN523wZLbcpHCY7isC+22BmL3MD7WhqNtQ89/C2NeUmkvIpMuwNRxR+rmShggcwQf65EN3DF0Ji1WTcLn8Zg20OEnryoIZVMyywvw76e9gIDwfGwiyve1Z0ZQ/fy3Im5W8SzZYgo40obIRNLMiRMLEURGTMKE1bWz/xydS1UdWy/9VAZXBGOw/XoVnf+LCd2Cn9+Yz+mBD82ROd2hK2DvCLPU4IwdootNMECPGe5gQmf+SkIHH87pa3/Up+4LA4rhDzXAjca5Erk1pQ201WeHrlJkSgYI5yKnUm2mY445wGxBE2ZzOW1A0yUQ1Rakv9lWgjYaGqyB4FMPFy8fBDNANV+5DhD9oqFb38B3DvBRNC39c4leP8mUCYT4qUo7MwHfOAduSnGMPAM01cNKnDbkcVzZ0Igig9DIVM1ZgQeYAQobSFRNzLgJe+GVIa2v2wKJpszFIyudijAzmQuxNpkBYOvZLmc4ORUgZMWe20xfc0bvTq0xfSSqFqk7mDsmuL2b4P45vfuvtekWxHyCnibzEXVgzxvIyjAD8ES3XESMpc5gxh76a3P0FExGujkmy8GopJR2m5daoGLfbenuCT1cVtAjb7H95DyHTIm/ASPbRXQrWWZJjyXamYAAC5hJ9mQyXDxxSD5xTJBBFZ+wbPehDdZAryNO9HzEMVa7z5LPWoAfzcSfeOK7w4DgBMnPoVVGwBHDgbq3Zk7zFjYv79nFfV6C23x82WmZuug7Wid1vRBGxMaQ8mdfGIv083cs+Uz8yUg5k12+LNJZSvCU+TkEXtid4+BMrudPWFvgjyhzYdqsVL8+pMrXDzMdcIQJffCnIrrEzAT9FeVDGr16kQ4jzPrYo/fRQQTgJ8AEWzj3ypjVHQgAxLv/dESnf6pD37qwK6jfNDUXUNFoAfbw0uCJ77OAXgtYqs4Fj2eECb/dyyg6whK4STef+nPKrj5DP/7QMfrFX/xZuu/UCeAVuKtg9EuYp+fhuawajdzNQRKPH4e5gAawjviR0wLMdD79zAIxdC4zH5kDf4aTUjzvkOoh8i67cIvHzGkYe7QIoeB+skQ1NJ7AAaaXwWyPnlRzFGK8UMtNg8BASm6tT+ji5UyRPbtgYytMweqfpZknVCQdED2D1DaSnI6fashTOELHSSEGbB4QMnIXLTBxDITrG04VszuZYYBH70/pxpwVzdJ9/gl6+ff/f9p9+av0RZzw3PveR5/61P9H739U96vgiXoJ6vizkIYtPGv+TEIxEk+Nec5FaKzAawCv+kPzVqB/R3hhgKhUlz4CmDtVPHFBnvSlb9GlP/wkDW88Afp16fJ/iOgr//Yf0j/5x/+Izp49Iyr/DIThQ7jmSfDjF4ABkKWmwx9CIudFgEMPQB0xhAGcMHBfWPrHngkceG7gaGMeb4Met7+e0xAgmNqIdq5E6DebYZKDw/Apjgkou4FnX4W22DdXI3ygBaJZwM9PzEXE+3s9nUQm2gQMkPHBdh29zAHSsn5Gox346asZXYW2uHWlRyv7c6hH2EcOwBjlkjzLBQQxM0n0bOI4O9N0LNu4BB/02j0ay8Ofpm/9/U9Q98XPAUds45k9+uY3nqa/9eufQJ/60l/O07932dD/dIboA7hqDQmiZiOnZUxKkpipGL9H8KG7GwVJFpa+xJTumtcCmQONzCA5ElGX/vXfoeHNF/BFXzsOx6+7s0W/8zt/j8LGNv1HoYI/ygkbEOQ6cMJx3rQlJmd7Subzz80d8cdO+q2bIw6Wjq5kdOGzKW0h+Ta8kdNkA7ToYm4HDiC6Oc2dgPUhUK9uUMWr88C4GH9dKmwwR68AjAn4Y3uUKvEl+CAIPxepTwcZjeEmjm5PaOfShJ77YxDiW31aWOJAEQdk+OaZMEyGXmVgmhRBpVEf0UQcqWeqAT7PdmlzMqZl26fb/+7/ocn2FR2RzV341NLq6m169tlnKxPdxMz9wrmIDjx7i/Z3Ujp2zCj69W5bMDBbB4PkUr2zGMAFdcR7cThg+NJnabR5kRjd6rxZMs6HvHLlKg0GA6q3s5DAv7LoIoLvUJsfAlDfB25i+1M9MufrN3gcN1P6s787oJ2bE3yX6Xd9krnznhYzi3XXZA6zXN/SUHHhEQWvBQOU7E4FDmBJvYLEiwRcWJWPVYVHVg+Od+YgWraLAwwwgbcw2QQjbE7oiT/aBZiZQApxrlGjz15Bxp4BjgkzwG5G/W5OPWiP/nZOg01I0XggE/4+epG2bl1ywKXkV2aAHKO7cuXy1CSztnnoREpLizkOVbHW6Xm+bhYzeJcv9qVgUa3Ygqqagxlh8/qfY5IHMieWtO4gwxcDJEbW1m5j0ic0q30AAnEANx5xvGAxGJYL5Pj7M+HHLoDkAz3z6N/zf9LHvccc85R/6peShLqNu0Eh4e5a1rRbMD8b/dLkifYP8EBSt/3+pC6Iu72t0RPhKDH2qr0E/OFv9rtZcrM+ujVWmG2QajPLMa3dGFATPY8RDTQcGnZxAQ5tsStJcA27zLHoXIrPdhBnGB6d0CJMx9FonTrtNhB/E4NIcX4uRGQN0uv1MBFpBbMwyOTPmsg/x4hPJ7HT2W4yfMhUhpdTRQeKL+xUcMNlLTlbaALi535yeFLHu5iPSUE5Lj5JIZH9/gCBsp70eVYT4Uem9AIHxRbUj7eBuvWh46FLKPmgjgwFwHMTLk/rAIJg69YR3CgxvDlxCaRiaC5mwbmTW3AZjwSJqQIC2NAEBPaBj9ubTv0bF9rNrHObNNAiQR4mpsB3JpAireZ+HqClm9cGNDdvlSE4NoARZmDtdKxmY4SEdg/PWL8xoduA85vXhjIJBwGeFjotWlhckMmUWL6geSuM0IekvfO+++R5Itk4Ulw4ROhtewdxgNhWw6SBVvOSbINJ8Fm9hqsEioPJofq8yB8N0UIa0EpcyJeTYyN690MPSZ9z16+Cvu7vNhNkYFWKHTD13onPj4yc+vcBM2aAHoJbnfuatPjDLYoaKvHSd04iNaOitM0HlUJC873Wdqji/hb0pr2SQWira6nk+cWlA4crA+Ta2YnaccYAHPWzPk+J3rYPNyhrAg/sTKjVzDQpw/64JIWMJHK4sYmZ8HvcY7ST0RD++8oDQLWHDZ17xzlqQwPE0M0xRmZjW3T6vnfeR48+/IhMEAd7ePInMHI73T5dubxDcWte8IoNKFcZdK7h1wUAs/1HcUAymqkGUUQ11ibQBhiAZ335wI/S+vXPyslwQHGA4EBgS0vL9L/+b/+7xD58CpdqTNCDpuzBJuebiRAtd/fPnM8vOf7MeVaOgeHM0DZu1jmKGAhiIWMAwNHLYABwa4zwOLvNUUsrnCSL6LSCL0The3MkMnQDwxaFEhEOeh2OtsTZqQQj/Dd7AhN4BswAnvjC0yBmg0ui5uAnI/A/GgPLI2htIp1164EgRshh28lwQoPtMe2ujeDTDqh3s0+7F8a0NTC0vLyP3vve94n0N5oN6nQ6kKwGHThwgH73d39X08AZu6eq+vv9MYJVfbr06ph1hZonZwI0VadmgPmtcwBM+hCI9058jFjt6AA+h38en4Zs+4RNYEu9WZQCEszWiTN/nY6d/oCMR6U8QX8P0t/+2/8vHT16TMxBymA3t4Xks+ZKQeGXb6S0C1zF4WCPSXJn71lSR2mp/q3TALxGYcgu4gqbgIgW3t2Q+sYYJiFawOscx06UAYzPKxhyCQ8d/k6vpgECeif16J//cmfXS50tI3oAfimj9T4TMReC8kT7f60VTsFq5MJiFNubPXQokcJMMhoQEpSaqulIAQTT7oTG62Mabwxo7cs7tPDAKSRKDP3Kxz4mhP/c5z4nmuCBBx6kX//1v0UnTpwUohuMlPs2xsR2If0vXNigm7fHdOZBdTWd2LkxqcpdWIEJOYhnjmIad7WcrMs1i22d6GVM5gqLxLUCQhSEkjllhLiQ0E/9/N+hzc2naOvGU/QDDxyl//7jP0uHD84jTpJKeprPi4LiQBaOHsze156FORx0CoDnU7vs73ONhNQSuPi/VP9YxSZjCAJHWXOopvZZfIY4SdwB8RfwOUcB2+5oOk2QlKFungKuUmItFsXTsYAiFBy6B3z0BzqJCqJ0AiUHwMBvrIiee2o9yoaItDB7ETv1QP4JfJJBbwSNIPE4J1FaxJGDaCkzANJk490xXofwY4dwJ9do84UWfeXBA/TT7+rQL//yf0u/9Eu/jMmMaRHQnu3rCDPFap+1AzMmS//q+i7yFZsKVI0yrGD0yJVU5zoT4wVoHRB+ApvaF/dUi1Y5SjcHUzCGBht3NMTslYe31YIVOE4PqVtfT+gHHvkgnfovPkjvOMbnxZiviRA/Q0RHK4xNQXzWCp87Dxf2VkzHTzZoe5WcIJTJJXH7yIXFMyqCUSqQGtOQuoElaMUVdVliRPhYA8QcDXRmIPYM4MChxwF8xHHpBfgweWKocImLJsGIia2EQaXgQ4JAygAS3HEzxMRnoNeYNzJgjgymIFSKeGRzMS9GIuZCcgLQAOhROoJbg7hyDlOR2zFFHUjvtW36V4+36cfPNanDAMcosUW6nD2OY+3xBP3YAvB77sUNevzJLu4fCyC0zp5GguodHuBLWN1yYAtonAs32+yWIbTaCwos2HU6asu/i8ylG0YCkLp2u4nnDmkZIdh1aMqEw3RSo5CJ16ILTtRusM9+9aalv/dHc3T0XUuQUq2T9NLPr6IBUldcQiUA9FnLiQ+UcT+41vEg3wAIZFEZgEPhScsdDAwbagI8XTPF6dSypVYwRTLIVixAUYHCUibKs0BCVoirHXe2P88KAxkjLLlzC67QWpcGO31MRB9qNadTR47rfZw0cESQTUHG7h2YIE+ZsDiQzWh0uNAkpu6lbfr0H87Tx36mIwsvuC98TuYIZCLFJ71+Spdv7NI//fw2bWxkwOc6Ora5BSLOqEDkpseqORe3c4RnRQBRcWIkijbq6hy0xg7z1ICj14YMulr7G/QybPn8UkqLAGatpkY8mZA8ZmZQxggMTm9tWfonXz5M7UMLkE4Nu7B05i7Em2VlmNmb3yJl7kDp0oJLHfN3ELL83Rg7klLsTooWYMJzNrKlZoAZwJsw8jR1OL0odXNMkJBXAZYqcQDPEORVkDcHTHix/bmg8PZBTMjxBnW3YcOvgfCIP7I0g/cxsFQBoruLXGuVcQREMVYgHAYHgGN7sYVBNER0v/TMQIj/C4+1aa5ttODDaEgrx3Vd2NRvXRvRP/tyj155ZSL4pAndrYxLxQKPtBADYBRc3s00ZTZBFDKHxmHVyeoigl8+wXFoH39uilSwjxtEHhhywQZUsMla9NyrDaB2jNNw0YqhXQDcpsklTtAHwLi02qCnVw8jvN2hTivSOklyBOqXWT7JkCZEFNjtMHspKr2p0p3Ae1n6r414LZtILHV3VP03OCU9p+no3BWp5oEGC+laCLx1GqBAhQETcCw9RAwlilRtwHbkxA91yB5LaGNtgphAhk4iecvlL2J8tCzLE6RAxDYvGQHSaKXkJpdaseZcE1ISOy419GdPDunC9ZT+6oda9ODJJrUAhAYQlZdXc/raxYyeugibvsHxCGXipAU3UypVrFbX8oTntpCmUa+BQNOIVjddTWPDuLSsZjEJOf6VfaaI/1MQNCqCkowFuP7B+YqvbDTo1k5K+xYyJF1Scat2ewmCL8u0mS1Qe18syanEEVi0SEOrhmyQ5y8YICpVf8F0EyVqHisDSvEq1P4xJJeOw61cvYrr8fn8nGIAcSUnNJX5LNxhU44pCUXdE5nHxpzkLzRhApltK3KP7/7pReotNWgTodwIA2yMEC+AMc0A6kwaS3w8AjFz65lHn27EACmysq42W6p6oTpbnYb4/ew1ZM5JvnrD0t//gyH8bMQVkDAf5AkkTb9POagy4oikUVwBURqBAblOkVf7xCPvDysT9OBi7mMbvM1uLFct5aJtIqjwGGB1+TQCLtA2Q2+DvQS6SfT1fdw/CwFhBmrJotKEVtGXyxuu7oEjBO2IOvsjAY2xK/wsgjuJVgxLTYXTApL1M662LyCWmIee80RsWbfAjIChw60letdBpJmvqgng8SKDrpglK1V9FFFI6rIkrKLuPcexMMxFru7Pz4C6cqzGPvA3lmm92ZK6di5FakCNy8MGyNVvANHvDoVpWvMd5w97O2zLLkRaUCIFDUaDGU2o/zhR422cafKTwItB7K7L2ZpIcQQznZRGgZkQWxhgFrub0K3ncgFEzACRW1xpvUuYNcQLkQzaxI0NkcsYWcX5Fa5RMIXqLGoXSXMFY58PkaxdpCuNW1p93OEVw4u+TJ3VPI/JFOsQ/bBz51FIXd9YK3l4AapE9Rxq9/LGj+YS89GWZvukuJVKgCtMwPkJvJ59h+IYWYHF502oMCms6BpxVcv75yRmhs3nN4vzfmGlddkrKx184INt6i93qM81WWyTuPomdhihi8gfiJj1EomSzR9cLKJoBfFd4ahoFRfDFjQqZWUN8fktHsRrDHylbcYYRPx+xN05PI1+NRfbuAahYszueA3xeWCC/mRINy+u030/cArawqgZoHLUGoQ0wnhsT1OeIMxOAiltIm3bXjBai2dLEJg7KeG+9Hc5b2ElAdOABzC3L6L2kj5jLGu69L4+Pm+CiJwNTArPp6/zi12xJxPMB3F8JJJP58CQhZ2Hl6xVz6T39Wsa+VnsOq7iu7Ng4MkmVddcEq9otjLmQv0H3ydUI75/3bcUK/eKS6OBjX2HYzr47nnYPV1QLwsWLYOvXCaz12L1qzPQgD9sOm03mSr9vvomF8LnZcgSTNZsJ+LuSezfRM6HN6JSueCBq4kMRn7gDOzqkY6o2QySPN5FlHClSTuLTeq9cIk2r9yCTVyjM3C5xBVTDtKAVW6lbpGTRfG8bhpheQEr8hctxAK4ts8XYXp17dUua5Ht1Uw03vEfjGn5JBigowsxEqfeeyDU6qtaqlUQ3/Ofi0T6xJS4gFxaJ8ky1QKZO997MMwAnGqRFVUgrB27+oWGmhGuQ5TILweLcM8bY12xnG8H5px0TwPv+kl3bKllkhAAFlgArwf3x8JhQrREw4zveG+bbm7DrstyayVSC3eYA3Ns961IKQdtWLo7K3OY99it3tHJF8k3ylDGbdZgYs3BJtAcDBplKTdmz7GM1k0w4cBQC+dWgIKb9P5TEb3/dEzvgGs1xCT+zu8DEK53aHT0II2v3qIrz1+nMw+d0wDWpIwDeEQcuQpQtuHRYgQGwjiWFJ37KFzoAnIfdm5bIf6xH2vQ8iHMD1ywnz2BmEFHVS6Sn/QtMFBnUZlgc62UwMIFKyqjtU6SiR9x2TxyJGwOfPAmIiqWt7F0S4n4DRJGloW3eGba0iJVNh1SRIrzOLu6r60g0Qsy32tlTlP6YfMMkRS14p4H3PsDKw2ESA31uuoRzEM9NpZbNFzT5Dmrfa7pmwPYSRy6N0x8q9m7Oaj/zOVRc+fSRLGyHZd/CZe72jjmJAEwYvt1WZc1upjEiM2NaP70In3wAaL/+bGclgE629AYc3MtMRkffuAs/Xf/xzZ9/lIq97p9fQMRvwGkLEHYWKOVErVMI8musR7kYlOOAzSWlPjsQtmGjj/NggSQ0whryI0svSeR8zhS+JFOSh/YlxTg6kEQ/idw/hOQ1H8fqX3f3nTjc+ancO8yVyE15BiElsjxKuYsKc83Li2ZsqVF0ir/c5VyCfwskuRdfBm4BojAiHi/OtKl6tt9BzhJ9y+otIAXotADCNtcO6aVZaP+NCTl/oeadHvHiD1m6WViNsB6cx1Nn7G6ZuLzJEsJN/QOT7ysmXPLWmUhSZC2LOqhDEt4ItLPX5RIVVl5ASr/w8gU/g8/Ak8AOX+OtnE+gA+WpjYo8n/9L/fRcfbhsxFC0F1au3pbq2xcKlvS15kLYontj8T2M/HbmLBW27lYof13YVpOi/di4xJb+PwFpLJvDjT8G0wcD+WHkFD66EnkFU4qEg8jfr5cywNiSYxxaB1ajBfZFgs+XPLNrwsw0FBN9HECLTDZKivRUlf6xSao7VYBcVSTcxve2Wpgbo/4PWC8Vgv7THs1nHQSPn7iVqm0Fho0HDuE7tQ3a4Zm223IYFwKiiN1XOKKg6tlpLbdPZXXEHCM3Few+KW8rOgF/LmYt4evPFEJ3LaFlZj+5ge44MOVlYEqzAQj+FLjSSqxhjMnF+j//PWHofJHEmjauLmOa60SzWp4mFx5Olc0yAYWHPefVwTPizmYMcR9zsvoGbtn2+s57HpKY5g5Ay2z+SpiEZeHdBt51uGoWpzCDfCDHoZ7Nr+vRnw5lBGlpG7o6iolv1LWWxal4J4RcP+lH8TnG7oegItn07RkEB5iy9Uy8Hyze9h0XtQSTMTKgtmTzFFF9Gva4OTRBgCeomkOY+ZkympWJqaYAePsSySE5YGZlhWis+SnLmMYmbAWzrmErjaJA0JRkUSP5H5+vWETvv9Dx6wMQqRG0sCZEH6MfAPnCFIX7nvPew7RoYMtIfjW6qYGrEg3g2O124pzDZDEGjpldc7JoPmO7vXD4pB5BnAHE2TzNp7THVNvdUyDi2PZqGJ1Y4Ls4wBBnyE0UTY1sT98UKU2G5XFnUx86zQSmwBOqXNRDTNCNnTV1qPplVSsRRunSDKB4r66WgEfLZS4jcMOksjLdH0BT++RpbxMTNF0qwSCyDiaONfw1LEmAjBGYPskjxyhHXgj54+6KkrZg4crcXnEnUiIMoZ0pJGmbbUwxLjQsC0AB1cKyb2SWMqrjEMnciavvAFrP3pGYwW+NCzn2oKcrXgs6WZ2BWV5FZ5x7MR+un2zS1u3N4RR2KzEAkRzmsO9hiPXV7eLCUs+71vEtpYlR6JsAQhkBtgBoftIXKXbMC9tXsCY0c5OBibI6PABeDwJz0lL8hjGQe1juGeL0XeqNxWiTxzxc3UH0j6X1EHzMf5hbyBxoHikxJBV7w1lSp6kNjBQ/4IS3+Oq3MUp/HZ7rBGgqGgu5qWSlk4fdEId4jwqP5uqCAp4gfYj0nfqREKvQmw4chW79KqeZ4rEgu7Dg0O0xEQkjJd3DwZshKxWr7gnSlaRo3aSD1B7SM5F1FhNiUolfYwv9i3oUi+tC1QmmEiRSSTizIzAjNWDTW4iQMXP49KxyXgM4iQK5mQZl8U4BPpq2rTp3KlE3avUB4Cs8wYcBti5gQQXaxpcNzxuJHjSRczjFkLgxw4OqNnQ7WjaHTBBrEwgKliWauW6hiJVZsj8wlk2Y4hdcP6h0dRQLqtaEwUUcJ6AcWHieD+p6+zDxv5MRzjfb34Wssa0iOjq8f3RTMn3j0gK78AWgaNKe+Bci26tprQ7Mbr9iLCdnpXlekWDq38xCXFb3UNJCcOesd1MIJ1Np4IYsDEqz/LcoWGtFZSycVv6p7LVS57LZEnpWFYOIRezMtENoRwDZLz4BBrq1q0+9UAoAyll5tnt7gIQzcHPtoX/nVq3b0BQQlWs08uIKl4RTyhsdPfGlhbFYJxjuKG86IRt/9rGmG6vZ0gtazaQJbuNPDPjGRaYPm+fM3LlMs4NFOYXswgGQDaTAR0zoohi7EO2phAw3tvItLR/spgG6J8DcMaJrq87KVYROeDJInFmf45sZUx7IwBXD1CohNp7bqeOtWjf/j711/Rkk5Mrc3KVrGxbMSGJY4AErhnbZsYCXADKk8UXihSw5MJecgAnz/SQzCDllRy4D5rIChlEQi7cyOk9p8uoCuOAiYClEZjBSPqVt6t5+eVd2uyNEORpCbDahR82v3BIA0KZxiFy52J5lemRsS+Vdl5sERvJwMTD9a4sucqhQdLdOdnOxECCd4EL1taQP+AkmGQ/4aFM2sBN8Jh2YyTJECQfuxXVrr4g90CUy8Rw7wmvcWkZWS5mfREHOhjLREcam3D94pxAvKTZP+M3lHAElHIylwSSwBIm7/6zpgxG1bnAujhA+JkJ3vj3C3MJvfN0k1a31AREroZNJsdt98IM0GCw2ImpfXiehhd3pEycgzDkAA+7j1yskUkNAIguRyoH+xFS1i2SHklMQR9hgLwz+trLGf3cB0upVHSeSZBpNFaNwJL49efWee0kcvZNnDdBZG6DkrNuLLkzM4oziwF6lT9zHvD5ZLeHPg8kwDWBbk3HWxDARQDKMT6f0OY2F79yjfcQkz+kERBlCwzw+UuLtHMTOYtUMZMwtltRxQLAJXM58hfZgANMplws6sGwT2NT5DAE9wU4gFf7zjkGcKkRhhm8sHY0dgmmCQeEgE/2N6boHtKYh53YGYP3J/ll1Q+cnadnL/RobVPdhtS5Jyx9PSCO+RVE/gB6BmCCxXfuo+0LtyApEylf4hBVFutEcKo2HWfCABmIJpPAYI6LNLhknBeRRpEs6fbol+9z+UZCX/mWpQ++U4tSrCsyZW0ylopgSxcvjemFVzcpa2PQDCwhDoPtW6UryGVkiS6jKmymC/KMXDUOTzoEVjDBwMXdJ9s7kuZmlzHDfXYR9D+HcS51cpw3oglmfWtzImCxB6mfh3YY2WX6l88s0ng98wEPKUvLi2qoXLRFBpc1HTRleb3xS5KMixMg9ytMw9iBgTRzNlcv7zNaAhaXK5mZ+DsjZQDWjKA9PXhKl8fVBTpkAn4tIoEBFJhiiDZ8isMIDV+6lhe7ZcjCg1g3i2LAt4DYelfi6pCPUwdo59oqpYuQmJZykWwRxxogVw3AXJQzE3A8s6lVs2zvObmkUule0YPd22P6zJ81qZNk9M4jznzkej7vXbS9M6FXrg/o6tC4YBImbzhGWlfvx6o/jnJn4lwwxxVMMAPwbh5+GyEeW9uv3kXXB7zCkpkUZqUJkLsGk9QdgQk6vH4hA/5JxRR1t4cIQKVcvkv/6dpJ2gRuMiCiRD8lFG5cbWUu45e1BfCYJArIXMfJHnGrSNUUZxul+MbouV0I2RGE550J8HV/PA7eiYQ3oJjwTujihMFtXkzuaPt9m9ogIpT+0CM4cQSnfn2k0pPpBDHYGEe8M3cEjwETAl99DCIsv+8gjbZ3aXyzJ9KdLcbiDQhRmQEEBwDHjxG0gXrl1CnjhhaQk3FhQlcOIJ0YY2LXblj6v/+gQT94jujRUxNaQSh2CNa/fjunr75k6PkrCFTJlnW8/gCTDM00zmKxzXxPlgYt8tC8hKxTcCVmzMSywZjRSY1dLQQrjh4yjbL7CDjFIKrCNa9PXUxh49GP+zI6eySVEPIQtv/i2hKd3zyG8WnIOW7pegq/cZB1XkEqC2vBODnwSgoQO451k0CujLIa/xUviZmDJR/368DdbB7SUHBR9Usq/VxOxkw85gARGOHAPir3C6zRtPjAdSvxfxTBPFO90NcEnDyC3EBrSLsDko0gs8xl7CZqBnivnBVw56APVb+vQfvff4xW/+ISDa8OqYHOcw077yLKA2P1l4+GsH+7QMIbAE1IG0N/jcEAUaOhCNfZQC+xo/VUJP8LL7A5QCqYVxulHAzKpAiEPQ4JCLGbt8tl0nOaB4D0RoDRnTldjCJBFF7YAqlLERPgvQ6GLgDEz5XSh6Yfu6U+MiwREhWj1aGE15Jl9Tou38rp0vXM7S3QABO0EZ+fowWYiwhU4no99vuNOO2mQNiCb2RxZyaLYWMkAKIUYx5L4kPjA7x8jEPGifoDS+eQ9zjFKWj1GHzSSH8LQXHYmNU/xw/QzdP7NN1uaG8m8CA4IZoGiJ7orgZETpgHwDt9LAbYSiXeL3G5SCWHJWhjy9JB5Mf3Aw+kvCUM4veHf/wcbTx9jQY31mX5TcRrnJEAzwGYsmGfst11DHYdXH2SsrkVEAQoupEC2DRKU+R6ypI0gk1NGhOaYHIHLFQ8kQwqeQZA1MZECzzjubZoHq4R4MWaCd43YTv7I1cwKn65ZuMko5YoymbiSzjVhb95mRkXXESdBrwKmJTLPS3LPtyQ6l4tWjGisZpQVw3kSlJe07hihMDWR3CyUuJ4QgUEczKIEFzqDRCLaKnZ4nzwRKuNoh5sPZJN+x5uU/sY5y0c+vc7f+VK9MyFq5n4KbyEZXD4A8ejUqBpWrC9wJMJTICpvVYYgtQe/sD9DTr/wkT3RkVnjV85RLyOACFTTDRvkboMc5CNAPygMlceOUbNq/PUQ5p2srUBovVxzRiE6Ll+LABo9cHdYykTnzQbutl0EpWJC1v650Kw9UyAXQL3ryH1ibFEA/N2DlQbIwAFJuGNirlYhINBCE2vHI5o+6YGZTj9ypk43mRp0oxc7MHtU5Dp5gpcNp7DT8+5SAV/sCcjrhtCwOnGEAwQS8VPhIBCjmhSNj+PQM2CeEKCXcZ5Mc++xstK8ku9Iv5o4SwyRhYgcKhJNN3iBQmqoy1avq9NnVPNsqTMSb4obAeQc+eJpU71ZzsWcRsr5s4EdDN7aAGpB/CiVjCJqf4dfn7uRIvuOz2kZ57XyuA4jtR/n1ipXe9K4ITBEZhgWX1/Tsm2jy9QNJ9AgpdpvLFNk+4OGARSZfska+sGXKI1xGTDLkKac9klUXcakTpC4yKEPkkkRe+ZLMSQDIQUlWKiMENtTipJSJbdtkzcy/1Hcon9Tya6r4Fh+8/lZDBX40g3m8wyqUulhNUqGOAwcugb0B6txSYmGAwHVyGShTDch1iIKUgdQafGwjwktAPNo+uxrNs10sp/GtLV+EIk6yeZkeZOLSMTiXR2I4EGQNKtlUjYu7kAoIf7RBIWLoNVvlzMRyj9fgWSPOKK5l0EoYArHr4vLkv5aI/XigZwHBJWiRTqP1IT4Ct5eHeuH3t/h755oQsAFolLwzt3sSfP9pW3cOV9BCZQtbKV+rwCGgYxFmKVTeCf05yrsOA6Ph4IumBHNAaKTpbYt26AUAA8HBZ1e6UWO3s4YSIXMhYNLBKhoFGzyRFSuw0JE/NaghH048mzhl69wYtIM92cigMsDMRGuqmVZB5suV6Pd/Hat5LRFmY4wr2iVipawMqWa6lIcQwmi1g7IPwbd/icWO2HrH1QNqVAg+kk5sVy88Xjc9RaboAxwQCcmWzFklzTTKujTxSA8aCgpdg1lInPxa3AYLxHw088YqWQp7g+EP0KU1CAATxDVLRA8HflAhxnj7foRx4Z0uNfgZodaTawwVWHEhXUbFt3pEuv2JJH4Hiuz2MVlwPs2LTl/P85qe8nV7CR8dZr0AJxAo0ABsiTxFUX+ao+7aXUHMimE0S2qJ7IyzV8Tue12rp5A1f+LsL+717IFVwxo7CLBR065lVC8BQkdAqTFUOlZ3PqEgrTsXEFkSO4e7Fsg0qiffTHJ/DKy8AAWlmKI1fAKBhDomSZm2Rfi2eEezkPkCzNi6ng8vK4bSTTGiUlodQkWU36lGCoKGwttoEB8TmhxGssj8Mr+pFH50o9acr7RSHwc+/9bSsYoAL+9jj4xJ/6kUV65coGXbyCPDnEhSuHGg0NYIxdQoWXfIxcpIWjghKCZaDFy724XpA5f8w/eZFphS2umHQn1JhnkDkR08EVvZSYIsNW+PFudw7j2cKagklkHaDTBE0wwSjTgQ1Hbv9Cpit8JwOtJMtWxq42j/EDzmcXboQBDDCxQx5MFGutAmuAiYql1vvFUvYexWU8VhfL6HOkH8YWdt3XA6Ypr/JVF1Ri+4xprOYqIgeqo1AqnfTnvrYxdTUDbludCZJSHZiqj/7NOXhppqQVUbEFHtWEOjyS4lMbcMmsVyq5iVe5fPRnlukf/NMNurnG6+2MbJPKy6x42d6YEW7uFoG4tYTi+0t2D4PljRylaBTqHz5XlGluUwskUlmUwFpCas5kBvXB4TbyZZ9dRbJgBef8uh1NGUhybKA/5L0ONCuWTbTwgquWOFXNOeAc5swglpG1eNUtzBqXjKEvG5uZq+41bul1VEyIcXWRPjJmndoXehfEcz9M5zaxnjATwgSyQPAKa+lv27l7ceRqJk1RZkZBxLKQ/GBPpQyS34aw/Ox/2aJDh5OZwjr1WejyU1gTqAxb8APdQSNwO7jSoF/86yv0mX+xSZubuYROi9VELmAvhY+pRu44A8hH7twhmVRWfQyksqbY7Cjn2Dj8aACviLMHNnOWPlGV6OfFUAAGHEGoZIbiPTo7Aii9cpWjKR3lDQ7JjlW3Wt1kR4nJqWw2G/AOUo7LwP+/sZaK1Is0Ra403WiffGEMWa+FMpV8l/kzrow+cnFnyZDuAkg22867SCSjaSax7vTJm2vHWjORe41ng6ogv9XeyBWP4B7xcEI/9zfm6P0fmCvKyT1eC4WXakIcAsJKHMCHhAV85OXN/H76stOH85f53NNwV/7H/+YgfeZf3qar1zLZutQpQ1e4YTXbl1mX9rXkl7iIGm2yGtcieQ6b8g4knJqd61hZACp+JheiJFrYUSRIrFdYOjJrbcm4Nhy5/lTcxVcHtDifiNr2XcgnLvpDTmVLvB39med9Bi1dvT6m7pYmbTjvIKpdi99UtbPGyQNNXWQUndhGilAS567GCdxHMM8kg7vbbYqkG9ZEnDGF+TGNuFhfUeRCXOBKNomWuAUXknJ8I6V9cxn9wi8t0nsfmS9/4yiiaUYwNUxA1VbVAP5kG3BLUGrkf1RBXp2HcGB/Qh//6EH6j5/foq8+2ZPfEsjdVtqS/rSa85fsn6tlUunQIhLdoC+WrNahwy36yM+8i9ZXb4NofSn5zoC6BVa5DgmxTGH9C2gcAlnBArbMg95YnVD7VI/mECDKR7HsNCrb3fBiBmE+hzNggJswA/tWcrpwmSeaF51OdBGr9XVY3tzo2IxzVfWZTPTc/bhULgi7jegnM/Sp4zGd+7l30Bc+36XLiI5OdkiWcE1gChMBk5FIP0nlk9F9FDLdDl8kf+w24oJb+677DSR/P50621biU0n4cMNr70WEuKCUFEfzGzuqw4oyKOemZIGvmeblggndA9gVIPjPrf79IjKGf/wfWRukuvjRlT9J1CvXpeC8cpZDuMzWYuehY5uNDJy8n37irz5EB46swFYO6Iv/6Wl65dIQASYuR4tlE4bMRjoprq9+4m3xW2zOOTRuIyX3A4BRnAg+2b8UUwv36m40aTIwsrRMiwAZxFp4C7mEXFcRCtzdHIFAcEtHI0lg+S1hilRiwHwsrhFp/SHn8Vnqeb1EG1ZnadHQuTNt+uCPPUTJ/AHZ0OL8V27Sl77YBS250kM1k2IA/aUzeYIQQdcP+Anej/799M+v0Pvev4isoy7MKQ5X2JKEn7nD74FcMEeoKW6CAYpCDHf4n0DxAYfMMUG+FwMEBweEXnqpS0+e36BvvtCjfi9zdkxj+Z7obN/n5nK6/4Fl+tCHT9PxM4cKSeZOpshsfOWLz9FLL+7QLgAaJ3ayPFIw51SvdRmjckcut5TE2zlXwRwJYEuk7rAJ96sDtNxiCc2c+sespQCkI8RadxFNS7tj2dwiR3otyyeO+J4BPK85hnO7SESylC2TsrMmoklzcH1XVmK6774lEP89SPkuUzjA7taQvv7UOj37dBfp5Eg8Iet/JSr3JiWnDkLOp5ELePSHF+nRH1wR9zaeQWTPAP5v/8un3ix4vGqiKhZQBnAd81uiWAoYIJ9N6GIrc6cBstq5slQKQOXmrQGtI3S6szWSSl4GU/OwxwcOdOjAoXkkaZo0bZn0E67pe+EbF+npJ2/J7wPy5siTLCr22LHuB3zyoIZL59fF6VmijEoWewQSYuZUH6JupqlbdFtn1wwjdAZnPeTph8hV8K4lEq9IVcsYNzkyVbmz9+rzswvLks+lcRxCnucfkzzQovc9coTufy8kvzU/9YORfsQcFl5fG9DmGjDHdiobafIcLSwkdPAQkmoHW7TEAaPEFJLsFlMVhI/3kny/AbY7v24O5PVWd1oDaB6+NAN+wisqPzALfkcNzzT+xw5soEWKTZe81nSa1DOfncEAXmSuXrlBf/GFi7S6mtFgyNpA1wpmjgkKzGFLDOhvGBkXFxdToGsPIyceOSdgci2f4qqQfDSRNLWsOygkX5ex6+3coEzuIqSZ/D4Cb4fLexSzH74EM3P02AJ94EPn6PR9D7pglQ7IhuOq4S4KQZvxnkepqkN17gnqf6QjiWtM4c9xIYpiF/QZRzJz5m0JLDz4KzYuMC5r5rRVsbTEReL4b8nmGiqWQkcBtvBEimYQv94V9fKgAs8cp/0HlumJr7xIL7JJ2NXfBxZTkZniRycoCL9aawvwKidm5H48Qit0ZYWwG6vlEi0+xlqiphXLqas+Kt1Ff/PI+E2oOBSeS0nc3HwEld+kBx86TA//0HuAJw6Qd0srBK9Ocxmlo2niROERlRVAntAmsO3heW6BVQX9Fw+pk1s0gOtgUZlb1wJeigP177eKL37QiMrviyXh/jr3HVGpYYr3Id1sMDNUYwx3zs3rq/TVL78svn2/b6TM2/8IhSy6DJ/jBiJq2ig5IvKvfvcydVVzX6/IMQtZd6BuX1ExavRc/UFK3YGEF5O0YZOXQfiTp/fDRt9Px3mhvpmRizdUpNZDNF4QiWrSb0qwViD80J7PMgc1LVGx/Y4RTHA/EXRmgJAAnigeCxSbRoVMkAXmIbD/vo6vYICaSSmYYAYjhK8UMkXACT4WxAWhl165Rt949jpdvrJLvHv8eGKdWbAFPrCF25Y7raboyli/65EHE75COVe3tTj0HFnTKJOrv0bK2wG3O7x1XYNOnlyh977/ATpx+jRCz20VdFuVPO+TV36LkGg64EYlSi+YINQGUVUbeOJHpgoGTcAkdbNSjwqaWzvWevtEdjYW8EwQgkLvHfjv0oBB6ra/lMhp6Z/FBFPnhcwSfMcSv7a2Sc8/9ypdurRBGxv66yac9s0y49YfWLcy198oI1fbXu5y5jJJ1tuxYil7LtIuv+XHv1WEwNXcHMDZwXk6eeYw3f/QOTp09Lh6Ga8h0ZWoXE3tV0xD7fxCYqMS0BWYoEb8UPIL4Bc8Iwr641uhAVw8o0qAuikI1Hoo9QUAtDUmqDNUQOAK0T3zUfVcJfJsjVE/bzgc0Y1rq3Tp4i26fo3D00P57SH5hZPMOvOgCRt1HT1o0YF67aCTmOuk8m/4gOgs7cvLHaj5Q3TqzAk6cuIYVH+noup9/L5uw++KAaj6d11S61E+/1P2IVOEv3pe4AJ3T7//8VQ/+GU1wAAhYcpgS+GWlmbAMUJoFvLQ3ocaJLiPpdkqPfyuLvG53eN+RGU8oKYd2H5vb2/TzWu3afUmmGFrV7axGwzG4mbp8jI1DR4fsG1nV4t/cayDmMDSyjyIPk8HjxygQziW9x8A2k6q0k01KQ6CLd52FxMdqPWC4O59VGeMuhaoEd9QNbgTEr5gFqo+txINDBkwZIBQC3jCU/De2/Fw/XyeU2V3y7xGqApRnd2xM5itwnhU3p+C51qqaqGZZqPGTPJIy+ndPo6BbOs+4gifLCvX9YlJEkmBRwtOfLvThprv4P28W6RRReq0h0QX8XgTBFzMnW1whRj1+9aui2omIaoRP/x7ivjuvb9n6JEIA3g6T5kCS1VsQNPErm9rOpPwRFMaIBD+4lqawQAhjgi1T26nGWYvrEABs1HwXFN7b2tEJqI72/YZElqPyRcoPqoSc9Y9Q0YIn103JaHLVzERNUbx14Z99hPvn7fnL4ea+uy498JIkRLHc7onhgwuD4hCpeT664UIEU0xRB5KriOwBOlscA8XVxA0nVeZR8yBqWoB330bDM9OD7Uy4RWp3ItANSIbQ1PqP46qzDEViAnuJfetEWYWEUPmIs8AVGqaaMZ9w3tOTQJpTeAlPPwsBcSoXOAmuZAKO4PwgeRTXJXM4keVaVr6QzPjgzZCUMfNUkWUl4xgqMQZJghMGfeZNzOl6i9fi8HTtGbwk2RrY68wQ53whqZU/FQwhgLVHDAMmdLuF5qApp9dqG33WQg0o1mMSDWmqr0vVH/J8Zc4GLY1JSG2OjEBvYoHeQktJnyWOqbg2iAG4N84fpm2/TYwKZ74jjj+V8BDrWMDbVEHkERUwQr1MYVtL8mZZb8rKj6QxDgEZIEfHp5f1wR+8iuCWiN+ARhr1xdI39BMM0VOQILHhO+3EqjXV3HiI+GgKwzhJ95LmSm/85tM2oARvLawNUm3cUkEL23kJJZs1d3zzOQJnfn3pDVzxTnODAlWMAETumebgPAhY4f9CtU9zSDGLOKHhKxH6UKAVqD2GpMUapyoovLrHdmLsJXwMQWErp03NS6qajk4Q69yQcglqreaBghNgGeK4u62fEiFEUx5HxtRxSjboGf+XK+iRLO4zyWXEJgYz4i25nL68vWCGQNtUjwjmIA7tXDSw0mtv4YMEBK8AGMRVQI4IfPU39efXWHKQG0bS9MYodZPCvpZqPQaUxTPM3Sek0HnafqLipR4JgjtiJfyyqU2eDA5++6viabNS8EoVJPSQL17BohsKeki7UGiSZgmL/FEmHksNFLQx1k8UJfACgMQzbb/pkTiTHS/IHNKCwRovUJ4EzzX0hRSr2OEKUKaaYYoLg/vQzSlCdwzzydwhR+Pk5lfBiJf1QRyQ1tlFEu1zlM16FHcNvzMBIRyn3uC8hF7QtuqKRJiRyXwk/MjPZe8efDPs1XmsjNnougOzVL/IWgLJb0C/Ez17zqD1FV/qMYt1eaqJtlTn9f6OoXT7ob4JGmQ8/Ld6q59hZwnULkRBVIZSH8oyaHfbWhaxRYTH3R0FjqflTPwQSY7I8hUxCKIZkYK68Cy6E/Q35kTVJO4utqe0gDu+xADyN8x3RE8+s/rnkfRoVDYwq9q51ZMiLnjbepfXjq8YM75beL+AP//av3i4iazOOouH+bPrZgUZw7CmgAvAc4CCGEls2VLu27C7KwhKvbQNwEDEFWKTeoaIOhG+cbszQQV1T2DgHVNUDcP3CqBnGJSqMJgU5JrZjAG7cEA4cTXxjOT+Noe5/+EAZAT+/24xgC1+ShSmXWNUOn83TR3gbhtVBLYuPuGUuEf43MRviilwASm6hJ6z6ECBIlmgsE9ulVRqVPgj+6sCaj2XZh39+5g5RkBkQuCmdeevplU3VPU97iPpc9UbnW7azdxj5W7udjOetheOjVglromCT8rXDcKzEZAxLBecS81P+tzCu9lqn2tDKP2XWTKz6YYIfDvzSxJ959TlaHq+CJ8JZr995R01/saMNBd84BT//y2gH+Y29/Gxb9xV9ebGf1zn03Z9/Kh6rMH9xDJ9yrLSW1BnHCy3Dk2punIY8AAUV3tB0xQsf13UAMBraqawNBMkzCFEYKx+mvrYM0z0ZQXVZ/UOkVN5aWqlenuFQD8/09S/ZrNTbuSJvTK3WqB12rFGOxstWbrb0xNVdvqPQpimjsAPVu6gnUt4u9bf/YsIGb2kNQ6MadMApXCUHkNrye6a7B21xL9+tpWltKjx/aZS/yHZ1Tat89ssRagN6nVJ3CqzZDCWZNafO79amdPfR3crDq5ymtcrZWvHL6kOnZ19XH5WVFVGymiD6txp8qvTdUk+P7WNUZo8/ear9f67E1on/HEn3rGm60F7qbV7X74ubwGUluYFVv7vPZ9xe+v3YeCv2eaMtdmSTAFhPbnhKr9Tjbe36/iTX2HKLxng+3PJvSRPRmA281t+wlw+m/RW9jsrA8CTFF/tbVz68xQvK9dW38/1UyNCUINRFTBB8VrKNl2tpqfcu/oO6be79iQU/n4sSXz6fCzmX2AR/Cn6OBj9Ba3WbhA/qwRMNQW9WtmBXpCpqjcew8zVPmbZjPFLGmfel+/Eb31RA+eXyD/sM0KAvPOKB9PEnr6rTQF3Aqa+De2/JxmTGyF+IYqHokJGCFMh1aQ8wxiV/4201/OInr4t5nVQfNdJLw+fiuF6p/1XTTrQ7YRoavwVrbQrhoTfOCZwavjIAJXeR8ASQq/r50fvtbX1YfnU3hPCr4Pzg8LNaSFhP8uE58bUuifDO1+2O7Yt9Wu/RTdIUL4VraZ6tu9zsIQs0zAzGDVLEwwi2jmDhrCTp8bvHxXG7r2ySOL5jf3+v41+7i6Yz+Ns36F3gYtoPmehCvO3QPs2Rq+uOtwdp0B6sxk6a1H9a/VEO49vGQ+dqdT7qrLAIWMBx6ht1kLC1VmehK+BcS2gfaogPPgOxNeV4frwbVv54ZuPgPJf02aRXQX7dCieZRc8uDt1CoRu/oR2vTgM1896+P0EZW+fVFZW8MSU/elt3kDre6G+NzuigG4sSphe0L32tu9/fZrqf2w3TUDcGMwkef0a+xW0L32tmpME6THf+3wovnE67zu9bcbm/Zs3KA/pVoV0b32XWqGHkeI9+N7uXp3aq9LA/jGD5KoEkKLNKuq+F57S1oh9QvmI98O8d093lgTbZDQJ3CjX3mrI4ffr00ID1vfT+lT55DFpTfQ3jRAK4wQI38Q0W/cMw3fmfZmEj6455vfbnTtY5GljyFk+pP3mOENNpjY3NIfQLv+/rFF8zi9ye077tKyZohiBJEMPYKY+cNWGWLlHmPUmmKpLcM5+5xehQCdzxr0+LHOt2fb77b9Z57506sxrvcqAAAAAElFTkSuQmCC
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAeYAAACWCAYAAAF8wRssAAAAAXNSR0IArs4c6QAAAERlWElmTU0AKgAAAAgAAYdpAAQAAAABAAAAGgAAAAAAA6ABAAMAAAABAAEAAKACAAQAAAABAAAB5qADAAQAAAABAAAAlgAAAACcrTCyAAA4H0lEQVR4Ae19C5Ad5XXm33dmNBoEmpEwG80gQMAGDJIdg4nAsligHHAMFWnEAjYiMZKcTaqcILkqW2sgmEwwCzibbEUiSS0uRxLEiICJNJACP5QEKRIyqMBggzCwFrJAzCiLNUi85iHNvfudO/fc+e8//X73zOmqvv/7PL7Tp0/3f7v/Vkrblu3cMqwVPbNzH+h78WPf6XvHs2POOlgkT/eOLRVTrt6Ll1XbzPp6eW1f45g1Xe796wOzz5ScRLj66d6vOrUpU2HqaFfnSCDbhpLTIV0uV/7WTrQbdxgWtuuU87rSlsXLWu1ktCy11ayfDAqTTo6HN8C4QldaV/jG8/WWsfy8WdYPJ9bms6aqNJ20SiXrj0hEsrB5Evvkn/ys8kLvrxo00BW/8Xxr9y+/3PnbDR20QqVSuQX7Kq2qmkVdD2U4rVbWflD3DeyfcWnv4TYab+w301jst9fI1RPq53nGJYXrI5A5r/tjehF5a/f9F3deaFQ2FIlRreJNy7LWU57rUK62VYUZz5OwJbs2HsttVHbaajzK6HsH9WEejoc3dTIVprpGi3srTGNoqwl5KhivZOZjLWO/1E712BsU1vtQ3m6s2YfLNZ4loqmPa+YOZmqnMPchxc/rPsnTwtyfU1asJgxX11Ovdgg+ij5N9QHIkDJ6uZb/X+j3IeXtaDoqbUOoXtU6a1gdUc8srFcEyJAQAbqbXb9JVgON6uFKjWHoOR7eP/urT9r6Oyl88iUHqsLYXcmZUsZZrilYPVyj0HVUmoiaiusKM9MiKj5uTf0y0riOJv+2U5gVp9QMc3qbUx6H6s2w3j16O+o6Uddv1DWhbtSoq4618+naEVHvbtIcU1pXmLsaivuxaBjFmV2aaUmt67/XlqEBRFEUstXFqCzhnH+2UedYnCyKl9SaroZr7LrGxuHN9ZNB8bGz9wQFS7eyknapneJ2dXZjc1XXvbN3He6tA90ple7tL+dKCZ/CVM/e5pnZ02rGSa7Ka8LR4lOCDLqVTIVJBrs6lk2/r+Y6Ss988OBDejnPedcrMlNwUvgfXjBrx8p7f1X+kn1L/mp9K80W/r3z7JU4cYY6ZN+Sv9qSrf9ajWfvG/7tzYaJBDs1Dv1+lzm7YNctF3X1a2/2YxMEvq/+xFUdqrll/E70VUzxP/uWUp0nKNW/yn3Om66Pba6HabKAJh8vwf4O2v9eR0Qfo+epD8r62On6OMoTL3MM1aNuFZJfqytNlebGCnO9qTjV33+xu8LUhwSglBWvCU2utR11T9XaG6aSuC+No3Yu81guU7vTZowjhU+lcY5KmwozYV1xPwrTOGZOKYoU26vzXyhfBiGeQpmBeRPZqmBUx5s2nixcnzvjdre0xrOBLqE9YXNSmDq+9MRhdezoMV8WNgnXrGMrdK1tgsJMA8IfQ75hLOpmkFLmzmMotaM77qRaz5MvbJr/9rOje7SqhuyHLc+ra5/b2v69Cy4/0tDgo1ATwkfPxi4Y10zK6bWoo3mwhjq93Slva+nvXzf/FVLcbtAZ3Xur1UcHPzhMitv1SaqOADMVD8PLVmkiZKc4K8yMiqr42InMvJbWrqO/8Miec+lQNxVmxSltaTu+w+1Qh3VugpXsJys0Quh3Kfpt06qqWdR/GfUPmPVUtrM8HRF6X5Ou5fgXq6Y4HcZkVZ2QmTfju9mep7Lj4a0LSVYka+p1Zp4vbsz6PJZ9KU2C+1E8jwrayeRbaS/Fi3V4a75bR8WurtZIFp+goHGDUqeT00zDZaibX05QNKxCZqTQ6biArXeTfHAEqoZ2M7BJMrTB3QxsMhGDm4hELpeu3rnF8zpJ5xLkoKBxNMn08U0BH8IKclDowkneEYFmzHz5/iPLkYpNA88iUtORIZsOUpUqArGfunUD65rc/xO95JGXU7cHQMGbfV+MKVxl9i5eercTC55S0+cM7fq6GXzBr1lvvfylzlPtxkldNAQaDB2GFBvYHOtl8Mb+/p85bBw3XjLmTt7EvMn68dbxHPpVJ5BrNdvRT598pmpfY23mZXposFlPdbTpfPU+qL9srIf7L8tZo9VT611G/R12I0F3FeqrTkP8QhvaycAmU3eDRzcw84NiPZQnpTiP4n6UN1A96uoG1vpsR75qaOpDmza2bnBz7FjPxl8eR7T1Fj9j9f5B8swTY+oGR12DgZleYEP7NTAz4LTR4PEZmOmz0jrQXMd9bNq2o67B0NzXbSz30VPuzzxQbjiw9L5x55k302UZuEyp7b85egfO87Q3l4Om9NcXPWE577cPu06NB6Xr1t9OYbf+ehuNZQCD0sG4So3Wn2Gs7amV2tFtGZLfqPX1Sn4KWlvsOvmR1beh6c8dMLHCGFx/hPbooDqMe3HP/0LsFCpKHYCvninpQKEdctdPrboONcPZGk/vF0fet6GZWRCD6wbm8ZzSf0NTwOA9pK+XwRmTJFN7Q9/bv06VK3+oLLVNre76vJ0AbgZ3M7BJa4oa/J/gzS/hALgJeJxoYuJQPoQxgWYxdTrjF2N+ph1dJjLolP6r1z/aw++x6EyC5EPPpQdhMgX7jhnaj5EZHHoL86bOv+Oimfr5y94cY5bpTc/Nn+125GH2l7I3AvS8BS18MM27q9bDxbO5V1SDi2czkvGk9KJKa0BSW/305z/rvZ5NsaNl91a+XT+p849AsBit8Nj3mjmO891ubH17uMecuhsPaXNGYNzQ3Ofe/q/iiltf3GOr4+tpPCZgumxH7x9VVOVveBh5sLnMBLdJGg8CEwxNnnds8IOf4NaqvVJquql30ZKH4mE1TmVB76FT9vWP7D1arjTNm1X629eXz1k93iq5uBGoG/nqnY8tKVfKj9kxgLcNwNv83uvZkajWnb3p4J2vvVP+U7sO05qs8sgfdzYs5mDXT+qCI1A1Mt4ffRDTNsu9hke5Ap57f/87Bw5XvF/P8nEl7yWntDciUKoWfRiY+iGeNizJ0EjKuXTjjv5nfRkYJE65v//HzpSkJQwCtu8IOxHCBdPXndqc6snA9/+k4ntZm7cOVy5yoiX14RAY8+RwYz1HkYExfe/bwJ4EpUMoBBIzshg4lD0SGZSIkcXAidgqNNHYjSwGDm2LxAaWSi2tp/iljvvlQbe+Tga+ZoHbqMa2Jqx71VgjpagIlDZfdOUBv0QwIXKcU9+Fdz6P5QbsL7JmBPjPa/SmrtjPLk4yT5X6+owXJkTKmBCpl00A3CZCyMBD77ZUZ6smLnY7TsntgfxqL5kIGQcrxtwEo2LltBE8k9jCPOh07ubtuoF5jJuhqc8DL9BzUdxbKTqdP/o576VsxkdMzNUeqnN8IF4fYfY1y3pfM+/Ut1Y/jMd3HP+tM8dy2eRhVwbdHqrnMVy268t19b5cESa1MzDT8TI096PU79I9+hgzzwpRvRsAdv1QtwLD5mH3O/YR8HiF+vPGdJ14czv618eijt6KOJNpuKR7QfdNaseYc5FcR3knXtSm8ds/wZOpg5/NzcA83o+h4zAw8dOUqrK3A8CtD9pWYOA8Guwxtm4k6ssb0w4zlmn4TcHL1dAsC+jthzwbQl3k+DEwCdy4LvtEFeIysEGZj/gevV5T/BG9nvMAYyPyv6Sy1peKetnWwNVODj8arcBjHUjSQUhnkaoeGv1qd61cNTBVBjayXwNXOeLHydAJGZgAWA+2DYbWFHcFumbo/SQ7j+EUVa5jaYy5RRlr0jLLdobW+NUNTOMCGTmogVkw09BJGZj52Rkabb6MhLEb0LfB0H7HMn9KNcB98dXH+s3bGRpjGwxMtOwfvLfhEtbATGrsyxIfi+Uii2m6pWRoAL0Kfeji5ns1QNyG1NvQdwPGfgUVNFH0MMo/rzf6yGAs3Tv8OXZXA6Nbjw9y1S6QwbYv6QU6dOqmi7EDJHt1gPbj28h8H6yNDZw9ovCnVIobFKZTd9iNljY8BTSCGpgfZfo4GSAs84DjWMZf2I3zbWT6OEbYV1yJMS8WSIvTuE2s2AlZpDoYdh08CzMB6nPkqSj3OMnv1uY0Jkx9oJhsfgXFL0M2MPcPugoRjytKCuPtgKy2V79Z6BDIyCRgUEObBmYlp4ChHW9zGIO00sBGJsH8GtrJwKycGJqRSDYNZWQSycvQXgZmtaaIoR8mfYNcTTM+caQTL7zuG2hXQ8N4uL7Sjtvom9TqOY4P15Oh7S7G/BqYFSBDT/KLsZ/DwGToL+oXY0GMHuUibdyT7z24pLrC9NAQVo+unIG/7k9UlfKmat3aPsdveJgeHdTAuqE5HzJ9A+O+6XPsfei3za0vQKX2IGsR0gvkPU400Ua3OSZfktnP5toPtOm+fKgm8wR6VrVmbd+DSD0frsd7UWP9J5AZ+6ZoWAPr5CazR+t6pplnT/Y2MEm1rt/x4XrTo8MqEfYB/rD8psK4kuNHAOy0r7g/XB+HF4Z5gN9OVKkbR4A9ebwmYi4OQ0cUQYYbCMRuZKIvhjZQzriYiJHF0Blb1WCfmJHF0AbSGRZLyvL/cD3kHAwqa9BTt9cD/EH5S388s1YFwe/aXi73yV5g+p2+DHpQePGVdn78h4w3NmvijEkEAxNRMh68tOzMQC7Y3LCJ0jZxBmtd/whm0lvqROl0vvrEA/VyDJmgD/DHwHJKk5hoZA0OzD6tx+TESq3KNkseajW3nub2poXtwJQquzb2v9Z3pHKWJzuczRZ0tS18+ZqO5zz7SgdBIGcITHBmv4sBuenRMbejbePplwX5E8eNXKi2ORv63zj4XuX0UINrg844t7PjjcutwJ9ljsJTxgoCYRGoO7Pbkm1hiFO0xlvNTWHGRhlz8WP9r+34pY8o7JcJ3Xus7kx06sivKNJPEHBDoOrMfi+n3Qg5taU1y0FrWjy9v7LwF44PszhJ6LM+4oSBTy7STRAIjYDle23qkCwQoY8iQgdYQSQYI16YZmRUqYd+GmxskN5WycLnQyRCB8FM+qaLQHN1qesEeerLkcTJhp0YD5pWyf7zq3FSn0irUnZeQ2dib6kRBNJHoJnWrC/SgmmmEzNkRxGZZRMEpjICJfr4RBEAWLGzf/eNO/oQhu2XAlw4twhaiIyCQHIIlOgrMl5PckRhH2ThVjs+FInJibH9pl07150xm3PJpAtOPs6VfzJchaog4B+B+l9TeFrnEO5vY3WJjuPVrI3nLcMLlMG38cvpYGNpEowmw+Lc5p8x/bQ9vzP7zThpCi1BIG4E6s5MhFfse2r64QOHAz95bQqFB0Of3nJx92Kz3k9ZX03sE1d1qOaWiW/Re9EZxROj333Rq5d3++zj1PsD/61rpndP6SEIZI9AgzPr4tCLxEHeM8Wl+mD7DNUVNhLrTqzLQfmwTk1jn+9T6uWDlPO3NQGRa3/Dev4fL+m8wN+IeHvhdqITFP+wRvVNPM2+Pi4OoH07aFUfgAHdHp0u2k5FeVWtLm6+3wDd6gNEJl9dBspDDlp68Nxa/X3o31/LB0489NVxDkzbZcAEmSFHT61/Gfrc4TI2UBPorsSA02qD7nN05kBUI3R2c2KTbBSnNmnZl63d91/ceaF9Wzq1muF1hpGcSz+oNaLbcWA9xWX0uQT5y7hcS5Pg+xfg+5HBp1409Uffnnqjz4yDvg180edSkKM97m0bZN7GRMHnOOT/B5draSSnBk066dLJV9+2ZebMQZxYl5jy8Tt19k7MOsJQPZy3SQM5F2jVI7ENre046OrOzO0YswL5eVyupXHwdV1YmPmZ+gdxZgd9ffFl/kmlkI2uNuiqQ98COTVo2DnxfmC0gYim7sxRnFhHgfLRnTo/Tsy6mQcz6t/Ebp6F6wbkcXrqdFCjj34wbcdBMMGZmQ5orEB+HpdrqatTO/EFn1cMOo5FU3+M7XHsXGuIg68Xj7jaIWtgp8YYVydm2VJz5jidmIXnNLhT58+JWReng9mPQdHHLhLXI5NB29WZNXlWID+Py7W0wam9+BpjXYuGjPQBkh6nAXHydeKRVD1k93Rq9PHlxCxj4s6cpBOzEpx6O3V+nZh18DqYHQzMw/W07sRcadD25cza2JXIn8Zll3QCX5e+E5oMGW2dGX1cT1oTiOa4ArrYObWdxPtxYqteTts1Ul3w/32cKBn17MRD7xoNCRZfemLsL+2JTp1/J/YLCwy6nvriILA7a1NTJGciAnYbH0jg6+TUgT/UY8fHrQ68R9B+l9EnEX0NHokVgSvdgvS4OPV+xt5LiNidOQsnNpVkp17whVkvbvqtU84z2ydDGQZmp74U+nwG+0bUhf4bxy8mdGDhwCOetFc31PXUsokk4HcMhPnd+D9Dvoz9E+Dr+17cFAw0/zvqjjfrYyh/ALn+Migd0gUy/TnGkX68NcyMc6VTGrsz777t081feGTPuW8/O7rHiWnS9a2zhtXJlxxQHyn1KVpdrqXt+I7vXXD5pFwxBAfBNuBJ+6TdoGMzDnT6Gtta7PR9CHpH7jrUBZoNxpj6Rg6H8f8FFWfWK6Nn6NvJ/x6dTDgKsTszifH96+bTGdNK26nZiU0ojg5+cBhOrSazU5s6T7YynGQddKIv7+n3mCWUe1AfyqlrjpeZ88Vto0ScmYVMy6mdnJjl4FScmpEobgoHtLvHjOTUxUWjUfJEnZlZJeXUfp2Y5eBUnJqRKG4qTj3Rdqk4M7ONy6nDOjHLwak4NSNR3FRz6nOgxRdrmkzJSJ2qM/MhE9ap43JiloNTcWpGorgpnPrnkJ7+4vHl1OhHs+P0Akjc2zchy2jcRP3Qc3fmtf34+8N7EXzMdZWVNe20oF9E8OvUSTmxCVBOnPoNyHWGKVsC5b0RaNLYSyOM9zuUsAi0uTj1KWh7SyN2g5aPM0t0HwhDEPLhHFPRhway0cQnwPx+tFdnaeZndraplVbgRfDN2e+0nNgUn8sy+81ISFoEBMadmT6tXi4/Fp/QiNZrOvmP/kBkyalbO1/P7H9qXdisFvPXZZC8IOAHgTFn9n057Yek0SfC4vFJr+ltSOpaTGsxf1chpFEQcEHAUvcNtKuhoVDrdLnQHW+yrKP4vEukRfDz4NRJL+Y/DpjkBIFwCDSroeGfhBvqc5T+2VCfQ8xutUcxE//6hslXLye1mL/OQ/KCQBQE8Jn1SnsUAmmOJaemy12amEqTr/ASBIqAQAnruxViEXwdTHFqHQ3JCwJjCJTU6jkPVf8nTgoRq/WUpEin6dRRF/NPCgOhKwgwAuN/Ta3to4+hxroIvprZNkutnJXc5BprUUuTmiiLspi/IaIUBYHEEBh3ZmKxoTJdvdcfeRF8LBP4tFrdFWoR/Dg0jcupoyzmH4ceQkMQCIJAozPrI9f134O1ab6uV3nkBxGJu9KMxB7yVJvTXszfj0zSRxBIAgFnZ9a4de96/HqrPLoCVZ/GfgI+AXugYllPtEyf8Y3a30Za7/xmz9p0cN27g+XlR4bUrGN4nb2tWR2bdVzllY721t95uftE/bnd/CohkgkCDgg4OvPVzzw5t3JseD/+X8WMt/uGy9EN+LbUKvde2bQuePTwBS/3De7GVYajriwZvir1f/tWdp3FZUkFgSIhYHuAh/0iZMkqLd28eOnjeQFg2t/0j46MVjxPRqa8Z59U+p+vLZ9zm1kvZUEgzwg0OHMsX4G0rE29i7uTer3MF5ZnbK20v/FKf6RZ9DknqF8eXNV1ui+G0kkQyAECDVErjs+54nJ2effO3gez0u0PnhuI7Mgk+8H31bw56/v2ZaWH8BUEgiJQd2ZcWo8GHezYHw599c7Hlji2J9RAjvztp+N7aYQc+uxNB+9MSFwhKwjEikDVmat/3/iY6ArCuVyJ891ob87kyLv2xufIzPG1d8p/ynlJBYE8I1B15iAfVQ+iDE4SWHYo+Y0ceXhw6HCQj6oHkaprQ9/rQfpLX0EgCwRKVz/d+9WkGOMksTIp2kyXHfnVd7gm/rTvPfXr8VMVioJAvAjQkqR/HS/JRmr0aGVjTXwldmSiuPtAfHTtKC3oPZTYCyN2/KROEAiKAJxZtQQdFKT/0aEPvxmkv9++uiPTmMZFDf1S8d/v8JHhf/bfW3oKAukjUJ/NToo1Fg+9Km7apiPHTd+O3rsfWfSNI9kEgdwikLgz4w2quXFqn4Ujk/yDx5L7lnWc+AitqYtA8s6s1PtxwZuVI5P8zXRDIpsgkGME0nDm5+PQP0tHJvnbp6t349BDaAgCSSGQuDNXSk0bowqftSOT/LPaSpui6iHjBYEkEShhPeitSTLoXbQEa4yF3/w6cucJ4Xn4Gfn68jmr/fSTPoJAVgiUrObWVUkxp0+7RKHt15GJx2dPi8LJYyw+6OXRQ5oFgcwRKG2+6MoDcLro637ZqIITRWgXC+LIxHoGvpnR1PBCp41AIasWdLUtDDlUhgkCqSFQvWdun6G64uaIE8QAnSjC0A3qyMzjuk9yLr50WpNVfvmajufioyiUBIFkEKg688bzlh1WVunWOFlsWbzsxDD06AuQL/5gX6iFBabhm5PnxXxaGvnjcF+yDKO7jBEEoiBQn83uXbz0biyGvysKMR7bMbejjfNBUv4+89C7Lern2/uDDK33/eQcpU46vl6MlDnj3M6OSARksCCQIgIT7jK7dz52i6qU7wojA014ISKH/ibz28+ONnyTefqso+qcSzrDiKJ+dlCpF/pCDa0O+oPPTu/49gWzj4SnICMFgXQRmODMxH7FC1s6jnyo+vDMk+8IixU6v4UVOm8OIz5HZLuxURx6BGunPPIzpUYDzEUvQGRfdGZ2joy32G4HDnzFdLdlWcN2uAStA116tvy62rhXQPcRnQbav4Eyn4jj5Hs26F5f4/Vz8H1Y52vmIUdPrW4UfUO/pBNQX1OMsOUJMkMOwpyf638EOr0Slrg+DnQx5av41rjKlw8avZ+ie2hE2OPo+0qIto7/Q6PtaKlk/RF9mTEJRyaholxy0z30756n1DULlHL7Hxp6qAvxguON52fryDUj6Da5BUZrbTBOiIJxYBMFPrh0auzIVBcXX92Rie459OO0Qc7PaG26PFq1dzaEvt5E/fWwk1nH+rqabP6oOfQCDTom2JGpV5Vvs0P/anVtNvoKtz5R2twisk6XHTrsJTf9bXWFj+UFWtuyi8i6vkaeHCt0pLQ5sA3yjsWofD8Oyl8yqH9klM3idLMiaNlBXy++QdkE6U+8j9MGkEOHjtAYS458i0avnrW9zK63Jpjx68i6CFEuuXU6dvm8ODKM1WMnH+ruwiXaiEObbbXDgV3tC1o9+iD01S/b9KbAJxLQsnNkfEPEukMnbOYx7jLUXcL1poxc75Q66OvIF/3pSiDyCaQmzxDk/bGdbOCj3zpxl8AODTpOjlw9NjJx5jCOzAgk4dB5cWTSEQbrYV1tUt8ODTp0eXedDY1qlZ2jYExkhwaNUI5MQmFsaGd20NfRkZ1wSaoe8kVyaIx3dWSSW78/S0qPBrpRHJkI8SV3A9EIhTw5sg81boVRyeFcN4cD23UMNcLBKfLfZdPR1z00+NI9sXlpnbhDOeibOF8bnByrgC1dlZiPN/u6h4Z+no5MjFN15qiOzEjF5dAFcORdrLOWujq004GtjXfNhnXomiN/0SCeuEM56VtzHkOcbIthHNqvI5NmqTlzXI7M5ojq0AVwZFL1KHa7SGnr0HEd2EEdWhyZj0rvNIhDB3Fk4pyKM8ftyAxZWIcuiCNX1aw51t2ss5Y2OHRcjsz0/Tp0ja9EZAbOR+rHoYM6MrFN3JmTcmTGLKhDF8mRWUcYfxh5R4eO25E1vq730EnxZf5OaVZ8neQJU+/m0GEcmWRI1JmTdmQG0a9DF9GRWUc3h0Yfc9Y6tntV8HV06CT5st5mOhkcmXVycmi02/2P7PlPRmLO/PlH98w3n7VmJZJIvRy6yI7MeLk4NHehNDZHZqIuDs1dEuGrE6f8ZHJk1s3BobmZU09Hpo6JODM5cv+PR19mSdJKnRx6MjgyY+jh0LE7ssbXKUJTl8T4Mn84Mi3bRP/V6lvifHVmSeU9HNqXI5Nsro9zhhE+K0dmWdmh+dHPyeTIrCM5NA5uuofWL8cSP7DBdwR8aXb9VpaF0trBqFfFmq858toaUXpR41XskfQFzTWgMatGM67kXWDBcgaiSRhCph5jkG9HpnGxRuasHZmBYIeejI7MOsL4NCn2TewD2N9I2qE0vhShU9sMRya+NHN+dgz6xu3IJFusNKFjIKxjdeYfXjN/Dx63xIuH2W9zFh1Q7wxu/1H2kiQnAYxNr76tw/5AclyypUz6QQL9mKKnqF6Dk8/PVrL8cY/9Mnv3bZ9uXnjn88cQHe1eB0sFgXlX7VOllrLCa8wLl+3Y8uyWi5ddmApjYZIIAnDoZjjvMRCndwnoaoS2a1FHl/gNC1qMNfn6pduUq7HH9qIFaG32xTmhTrE7M8mZpUOzIzNe4tCMRLHTmkObLyuQQ1fQ9kpQ7TCGblMeCjouz/1jvczWFSWHTvuS23RklocdmsuSFhMBOOAdkDzUywrF1DiY1Ik5M4mRpkM7OTLDIQ7NSBQ7FYd2tl+izkxs03BoL0dm9cWhGYlip+LQ9vZL3JmJbZIO7deRWX1xaEai2Kk49ET7peLMxDYJhw7qyKy+ODQjUexUHLrRfqk5M7GN06HDOjKrLw7NSBQ7FYcet1+qzkxs43DoqI7M6otDMxLFTsWhx+yXujMT2ygOHZcj8+ErDs1IFDsVh07gRQu/hwQ5dNAnxeJ2ZJaVHVqeFGNEipmSQ+MZEvPBElo07yG0vaZrhTp6B1xfoF5vDpuf8KWQsITCjPMXmdcdvF6t6/sh9l+ptX3Dam3/XnVv/zp130B7GKY8JkiETsqRWRZ2aC5LWkwEHCL09TbaxO3IxCIJmjai21c5O/O6Q3PhtKNw3go+JLcJDzpfgZ0+0zoNr4mfocqVm9TQ0OFq+9r+9fbkvWv9OHTSjsxS5tCh97JsMaRvxEDDjkScdGPR18Gh7WTPW10kLO0XwV/bdwhazg6saam0VN005/HA4zDA6ZI7LUfWZQYou7O65MblXydkuRH7Mzgot+lyRc2D9pdBg66m/g609TeRApEGHXqJ5qvYj4DOA4EGe3QG7UvR5SLs94N2v0d312bQ+j10oM/yTtAXbYTzCuyt2OPYhkFkYwwyh7ZRozNvqExX7/UPRtRsk1rTdUMYGqZDZ+HILHeWDs0ySCoIBEGg8TI7uiMT7+W49H4wiBDcV7/kztKRSZ7qJffO3u+ybJIKAnlHYDwy0/2xqjQ6dxTpI1xyL/2Xx16wWsufisI+rrElq7R08+KloW4d4pJB6AgCfhAYc951/ffE6sjEuVx+zI8Adn0e+62l59Flrl1b2nXlSng90pZV+E1tBMacuVL5eiIwRJjlpgmovDj0sh296xPBR4gKAjEiUML/xTQrmdBWWRmFcF4cGv/NRdIjCgYyVhDwi0AJMz1/7bdzqH4RHyzJi0Nf+9zWSA/IhMJOBgkCARCAM1daAvQP3nVkmBdgCz62NiIPDj069MGdoRWQgYJACgjEN3vtJGxZXeXUFKQ+a4fGQpBXBpFX+goCaSOQvDOryty4lMrUoS0Vmx5x4SF0BAEdgeSd2VLv6wyj5jN06Fj1iIqDjBcETASSd2alnjeZRi1n5NCx6xEVBxkvCOgIpODMpY06w7jyaTt0pdSUiB5x4SF0BAFy5q2JwrB6zkNJ0U/ToXsXLUlMj6TwEbpTC4GSslpXJaeyVU6O9hjlNBzasiZ8RSFptYS+IBAYgZJafeIBjIr62qM9Y2vaafYN8dYm7dBWc2sqesSLilCbagiM3TPPbOtKQPGB2okiAdITSSbl0IjKA5svupJOeLIJArlGYMyZV846jO+u3xqrpGu6aImhVLckHHrL4mWp65EqaMJs0iAw5sykzpo5d+Prt7ti0WxmZ1ssdEIQqTq0ZT0TYuiEIR1zOzLTY4IwUiEIeCCAtwyNbe3BW/Ay8l1Grc8iJrzWdNL6UJlvy3b23ox1nu4OIwhNeCEi50KPMPLLmKmJwHhkZv0pQs9sm4VisEkxy/pWXhyZVNmyuPuejuPVLDhmID0sZX1LHJkPBkmLhMDEyKxLT8vtVobpxfzL9ep63rKO4tL8a+qmzr+r1+Uwc/UzT86tHBtej5clbPWAwx/Fqopf2/zZ7lzrkUNoRaQcIeDuzB6CkpOo0ZEluJztRtdL4SyBXqckJ8K4bXCkXtU07XGZNfYA3KN5waOHLxgcHvqTw4PlywcGrdmVciWQfa2SVZndVhnoaCttbWud/lcvX9PxnAdLaRYEBAFBQBCIGYFAJ+4VL2zpOPKBdbOyKqsRhBOZ6K3e4lasde3HV+7ZeN4y/GMmmxMC8/954NT3BoYf7nuvcuFoGfc7CWxNWL2ia6b17Myuji/uubztzQRYCElBQBAQBAQBDQFfJ/PunY/dgv9q7kQwnjj3rRGLO4sgXQbL23oXLw31B1Pc8uSF3rwH+n/wy8P05a9gd8SR5besyukd6kf7vtz525FpCQFBQBAQBAQBWwQcA/OKfU9NP3zgyL9iZfxFtiNTr7R2dcxt/9zG0y8bSp11Dhgu+uH7/+nVN9//xcBH6oQciKNmzbDem3XanFPfuNw6kgd5RAZBQBAQBCYLAraBme6Q8T3mkI9zJgyNVbp1Kt1B/8FzA+27fjH80sv/UTklYWRDkT99lvVDuYMOBZ0MEgQEAUHAFoGGwFz9D/lDtRdT1sG/sW5LPplKTHEPtM9QZ07m/6ApIL/34fC/bX6pcv4IPs2Z521ak1X+9bM7Tpf/oPNsJZFNEBAEioJAPTDXXkN4PamHuuIGhB4Sw0I+Z022J7kpIA8PDv/ow5HKwi17lBrF996LsNFDYud0HrdQnuQugrVERkFAEMgzAtXAXAvK+9N+uCsqMPRwGK2yNxmCMwXkkaHhrXj17Dc/HFHq0ZejopPBeDwctqCrTYJzBtALS0FAEJg8CDSTKrUX9lN94joOCKsXElhsALSuiINeFjT4Dnl4cGgh8396P+cKluIp8f7DH/0AUn+sYJKLuIKAICAI5AaBUveux69HgLNdRSc3UroIQrKTDi5dctlEAfnGHf3PIiDjXe1KPSi/MaBUf4E/M3noQ3XiWZsOrssl6CKUICAICAIFQKBklUdXFkBOVxGLpINTQGYFf3GIc8VND31UXl5c6UVyQUAQEASyRYCmss/PVoRYuOdeB7spazvNBwIt7W1HIfu694cVLbYumyAgCAgCgkAIBCgw52LBihCy60Nyq4PfgMzKHM35q1Esp1t6rIzH8mQTBAQBQUAQCIVAs6oo+tzwGaFG52XQmA55kaYqR9CAzMIfN02pD4a5VMy0rVkd+7CYoovUgoAgIAhkjkCpYllPZC5FRAHypIPXf8heqs5t9+qR//ZZMyqv5F9KkVAQEAQEgXwiUGqZPuMbmHikzy8WciPZSYeshY8akFn+8zqVKvJEMH06smNm6++wPpIKAoKAICAIBEOg9L0LLj9CHxYPNiw/vUl20iErieIKyCz/tCalFs7lUvHSM2ZbD7/cfeJbxZNcJBYEBAFBIB8I1B/SWbajd31FVQr16pSlrA1bLu5elQWU/B+y/g5ynHLQIiNFe3Wqq916vW9F59lx4iC0BAFBQBCYagjUAzMpjuB8D4Lz14sAAoLytxCUb05b1qQDsq7P831KvXxQr8lv/pQO65m3buz8TH4lFMkEAUFAECgGAg2BmUS+eudjSyqqvCWv62bj/9eypUrLNi9e+niaEH/+0T3zT5w987stLU2fSpPvm5ikf2pvmhwD8sL62Gd/zLrrteVzbgs4UroLAoKAICAI2CAwITBzn+6dvQ+qSiVfKzhZ1qbexd03sIxppF94ZM+5h14f+tnQuy3491ep6bOOql9fdJJqbqkuM56GCFUe/75PqX3vpsbOF6M5M619B1d2FvtVO1+aSidBQBAQBNJDwDEwkwgr9j01/fDbR/4+8wCNgNxxcvtXNp5+2VBa0JgB2eSbRYAeLStF/z1nHaDndli/OnXO8fN3ff6E/2fiImVBQBAQBASBaAi4BmaddG2KewOmuGfr9UnlMWU9gCnrlWlPWXsFZFPfLAI0yUBT3E//UqmRlFYKo6fFLzzFev2ck1sXfvuC2Zk9BW/in0YZn+LES2zVD72cjJTWTvkZ9h14IyAl9MEt4BZFZpuxL4E96XssoBipdU9KZtClmbKLsX8C+wzsb2P/F2DRjzSzzUZf38ekMbY1MyWcGdMSS7TwlS+cNRt9EmPYRluztpGzenhkePy4spXZd2DWmVS/33x05A5lVW6M679o+u9YVaz7rZZpt2fxfeWgAVnHg/JZBWjiTd9vfhGnibif4v7PJyr1KYSkGdOs3a1trVdMtYBM2MKBvozEabr+TbQ9iBMAnUhysUHecyHINdhLDgKth7wkt+3moS+9BvfdnOlLbwFch736V5ONUq762vSvVwGLU1FYVa9ozLwBHB5orEq+lLB9k1cgOIe9wPkfnIZ52AhzjOpRjM/NgkeQF2s7qt/FTseW3VY9rkIFZjtq1z63tf3oyOCVpfLooopSZ2OpzzOVpWgdK17H+n3UHUHdXjB9rVxq2tUyre3JLN9BJj2iBmQTiywDtC4L3UkfwH3tO7i/O4I/AN5H8KZ1uHktbvrHnPYTcJi0T1fqJFxn0qpjdGc8vk3dgMwYwJF6OO+SUqDLNED7OGGz+NtxonqKC2YKOqtR5zUrlgd9Pw45r8XecMSa+qD8T9CX7vgDb8DiMgy6xGkg6PY4tcVdH8C+myEX3T3bbqBzExpwyV2Y7RD0uddJWuhDd5xXO7XX6jMP0JCTZibo+SingMwqDEDfdbEFZqZalDTugGzqnZcAbcrlrywBmXGCQ/Vw3keaesCCfF53yKbY2+H4boGZAt3vYZ9nDrQpv4W6VO+goS8FZLpDLtnIo1fRyfhh6PqaXhkkD16ZB+YA9iV9/xH6vu6mI+iRff8rdjpu8r7RnS5dWOGWwnmDTmeh9UvY/RwTqd5BQza/AZkU3I/9AdJ3ygXmpAMyoatvxQrQEpB121EejtVj1vkoU4CmgIV5imQ2yBU0ILMg2yGXY2DmTqBPU27Lsc/jOpc08QsSyBMkIMdy8gXPzAJzAPtmfjfoclyk2pQnzCBL0IBMM27188WUCcxpB2TziMx3gJaAbNqLy3CwHs6HSGMP0AFOPk7i+grMPBj8Mg3Q4H8OZKEp69TvhsA79cAcwL4SkPkgNdIsMQTvSAGZVZn0gTnrgMxAc5qvAC0Bme3ilMLRepzaUE8nR6+AQcMjB+iAJxs3mQIFZhKeNvBPNUCDX2YBeUzjqs6pBeaA9o1lRoD1nKxpmpiCVywBmW0xaQNz3gIyA85ptgFaAjLbwSuFw/W49NmOtqexuz1lqQ/fj0LDlJXeaJcPc3LxktnPVLadLFQH2okGaNDPPCCz7pAl8cAMHn7/kpA7ZDZMwDRJjEE71oDMqk26wJz3gMzAc5pugJaAzLj7TeF4PS5963efcTtolJOJX5ld9PJsAo9YA3QUfT2FDdkBMiUWmPOob0iYCjMsTsxBK5GAzGBOmsBctIDMBuA02QAtAZlxDprCAXtcxtQDM/eJ6rBxnDyCysyyh0nBiwL0DdhP8zGepvQbXiuLQ18ffEN1gWyxB+Y86xsKpAIOimIDjE00IDOchQ/MRQ/IbAhO4w3QEpAZ17ApHLHHZeyEwMx9QzjwTzB2KXa3/4eJvOeUZliZiXjYDTyDBmjSdwn2yPqGldlrHHSKLTCDlkxZewGecntAmzwO8c7HfqoPMfejT6C/rEyahQ3Mky0gm4aJFqAlIJt4hi3DeXtcxjoGZh6D8UGusHmYXeoZkHlQVJmZTpgUvIMEaDcWvvV1IxKlDbpEDsygIQE5ihFSGBvARl7SRA7IzCDdTyQx1wgpfX7x3VeHfvr2s6N4Ub4lAqV8D8XXrNRLTxwOuNSnBOS8WdUaW65zPZw/bIDOPEAFwRT60ruYG6Bv2ABdKH2dsIH+F6ONAntuZwScZJ9q9ThmaSGTO2AzvxdRJkSxBWQmXJjAzAG5/8eTOyCzYTj1F6AlIDNeeU1DBOhCB6gQAZr0/R7G/TyvNvQjF07uq9Hvf2OnFbaqOiF9Fbu5ZWZfyEgXiQuxz8WOBXlzt9FXBOkjFrtrfpOKgOAVNEDHHpBZUYszeU05IPP3kPMqZ1pyNU5xS0BOGnecxHpceGyHM3uuomU3vnZypIemTjXa6YRNyxDuMep9F5OS2bcANh0h06Wopt12g749tg0ZVkJmuuO9xEkEXWb01QOyOUQP0JkFZBIKci5D8humgDku/xQ4b0lbPuBEsfHPXPhug1zbXNojNeX6jrn6PzKmrSUoj9uY7qBf3/UfquuivhendRx3xf0XXD6lPsE4jkSxc3Bq+iLV+mJrIdITAh5BmbrQdDatXvYI9jthe7ozy2o7MyvGIfkWTd6QajYO8/r/o7F3yqXvXzf/ld23fbr55Aub5uNO0XUh85RFy4Rd66xhNe+qferkSw4oq7X8qaODHxxetmPLs/Rlr0wEEqaCgCCgEGjXYaebnDXYzfMU3SE/jP2b2OmDGtcikN+OfT7yWWz/B0wPZ8E4BE+Sk+Sdcluu75jZGhSgkW+e7E9is75mSgG5c1GfKrWQjzduFfxXVAvQu5vbjr8i689oNkonJUFg6iBAARrarqvdQf8l8pux2/2/XL2DRj/6ylOqy2tCxg/A86+xy5ZjBHJ9x2ziNtXuoPU7ZLugrOOjBWi5g9aBkbwgkDICtTtoeir9DuwTr6bH5aHz73W1O2h6Ilg2QaCKQCHumE1bTfY7aLc7ZBMLs6wFaLmDNsGRsiCQIgII0H6f8uUATUE81TvoFOEQVgEQKGRgZv0mW4COEpAZE04lQDMSkgoC2SIgATpb/IvIvdCBmQEveoCOMyAzJpxKgGYkJBUEskVAAnS2+BeJ+6QIzAx40QJ0kgGZMeFUAjQjIakgkC0CEqCzxb8I3CdVYGbA8x6g0wzIjAmnEqAZCUkFgWwRkACdLf555j4pAzMDnrcAnWVAZkw4lQDNSEgqCGSLgATobPHPI/dJHZgZ8KwDdJ4CMmPCqQRoRkJSQSBbBLQAfQ4koZXCnF5nlae4szVV4tynRGBmFNMO0HkOyIwJpxKgGQlJBYFsEUCApg950NeOEgvQoH0qeJyMPbcfsQAOb2Vriey4T6nAzDAnHaCLFJAZE04lQDMSkgoC2SIQIkB/BIn/FuM+dJIcAflStNGe+w2ykoyJfiwiryBEC8zrDs1V1sgSVa50Y8HYS7Gae7APJFvWUYzZpkpWr6pMe1ytPvFAmkDFHaCLHJBN3CVA1xGhj03QZ/LsNvo8XR63PMpMMjlt9A3nPG5u9nXTJ1ZdAgTo48D4E9ifcRHgIpe2PDaRvNvSFgyY47qgQsclreBmtyVq/2Cffdzwbod6f+hmBFP6xFmbnbQx1A0iyK9TJ0y/R62clepi62HX4p5MAdnJfjhQpuRKYnDOTmDy+9ibDGxegfPS14Jyt+VVZsh1HcAyl56k1a6+Ayz7cgckBHKQmT5UQTL3ZyEzZHKa4vY8Jl2OjSxU8eKZNc5dEJB83/yv3xNnL8W82v0F5rUHb8Eheid2U0Av+hHbLTitdZtaM+fuiIQCDfcboKdCQDaBm6oB2sRByoKAICAIJIWAc2DeUJmu3u//V1VRi5JiHoiupXapEzo/p1ZabtNLgUh6dXYK0FMxIJtY4W7hmfaT2y/bePplqdnDlEHKgoAgIAhMRgTsA3P1Drl8Vz4VLt2a1R10RZWbnD6/mE+skpcKAfqWLYu770mek3AQBAQBQWBqINAYmOk/5PcG90L12TlXf0DNbDsz7f+gr31ua/uxwQ9+RA9G5RyfVMWzLDXQPP34M+Rb0KnCLswEAUFgkiIwHpjpCevK8OvQM6mHuuKGEA+JtZ6V9pPcpIQE6ImmRHAetJpbz9p80ZWpPlk/URKpEQQEAUGg2AiMBeZqUB7Zn/7DXVHBw8Nh1rTTsgjOJLkE6Eb7ITiXEZxPk+DciIuUBAFBQBAIgsDYU9aV4fXFC8qkJp4Sr8oeROX4+tLU7ZaLl13Y0nZ8B65wdsdHuZiUsB5AqXKMjiXZBAFBQBAQBMIiYKl1B69XlfKmsARyMc4qLVer5zyUtSxyB12zQFPT8t5FSzK3R9bHg/AXBAQBQSAMArjjLK8MMzBXY3Kig9xBjx0VVnm0+MdUrg5wEUYQEASmEgIlZanzC69wznSQAD0JjqnCO4UoIAgIAkVFAHfM6oSiCl+XO6c6TOEAXfxjqn5wSUYQEAQEgXQRwMNf1iR4vSXfOky5AF1Rk+CYStcRhZsgIAgIAoxACctzP8GFwqYF0WGqBOiKZRX/mCqsM4jggoAgUHQELHXfQLsaHn4n8Ccb86I5fTqytfUk9Yezj+RFJL9yTManuPEu81GsAnYSXYT4xUH6CQKCgCAgCIwjUKoGNEt9bbyqYDmSvYBBmVCejHfQWDv7axKUC+ZDIq4gIAjkCgGsi1Hb1vbTIiMFe83F2qDWdK5iFYqeFv0O2lLWhi0Xd08aexT9eBL5BQFBoJgIjAdmkn9d/z2Y0v56IVSxrG+p1Z03F0LWgEIWMUAjKH8LQXlS2iOg+aS7ICAICAKREGgMzETq3oNLVLmyJb9LdGJ97JK1TN005/FImhdgcBECdHV9bFVatnnx0klvjwIcMiKiICAITAIEJgZmVmpt34PILudiTtJNak3XDTmRJTUxchugLWtT7+LuKWeP1AwvjAQBQWBKIuAcmAmODZXp6r3+v0cu6wC9Sc3s/IpaaQ1NSSvVlF6x76npR94+8p1KpZJtMERA7ji5/SsbT79sSttjKh+LorsgIAgkh4B7YNb5Vqe4yxtQNVuvTjA/oEqllVNhyjoMhlfvfGxJRZU34ItOqdgDU9YDliqtlCnrMNaSMYKAICAI+EfAf2DWaY59v/kOVN0Y33/R+O9YqfvxfeXbs/q+sq5ikfJXP/Pk3MrRkTuUVbmRPr0Yh+z037GqWPdbLdNul+8rx4Go0BAEBAFBwB8C4QKzHe3qQiUjVyJQL8KT3Wdjqc8zESja62txW+p9nOix6ERlr7Ks19C+S7VOe7Ko7yDbQZCnOvpf+ujI4JWl8uiiilJnww6wh2qHjLyONeyhjqBuLw6C18qlpl0t09qelHeQ82RFkUUQEASmIgL/H+dxjAl7qEdvAAAAAElFTkSuQmCC
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAASwAAAEsCAYAAAB5fY51AAAABGdBTUEAALGPC/xhBQAAQABJREFUeAHtfQl8G8X1/8xKtuNY2lWuQilnSxIgXIXQI5wmtgyl9KClFHoALUeBktsBwhUIEAhJSCil0JYftP+WAj1ogZZadmLuUgg3gRy0FAhQSkiklRQnlrTz/46IgmMsW8fualZ6+nzslXZn3rz5vt3vzryZecMZfQgBGxGIdwX2sTJsCeOsh9VpM41m8zUbxZOoGkeA13j9qfo2IRB7Qh/J4tZcxsU5QjC/FIubq1dwtsTQG67mX9hg2lQUialhBLQarjtV3QYEhDjRF+sInAuyWiuYOD9HVlK0YKwe/2abZu8aszP4AyHm0v1mA+a1LIJaWLVs/TLrHu1qauEZvgRENaFAUc9qmjZVb40/VmB6SkYIbIcAEdZ2cNCPQhCILjM+w9KZhWhDfa2Q9P3TcM7vqud1FzS2bnyz/zX6TQgMhgAR1mDo0LXtEBCPjQ7GNvVczAWbnu3ubXe1yB9wynPBF+ij9AV84jubisxNyWsUASKsGjV8MdUWQvB4l36asKxrQFQ7FpO3gLRvccZnG22JuwpIS0lqHAEirBq/AYaqvhkJHmoJaynSHTxU2nKuo5v4uBC+qaG22DPlyKG81Y0AEVZ127fk2m16eOQuqS2916F1dXLJQorMyDlDcex2f/3wiwPN7/+3yOyUvAYQIMKqASMXU0XxxM6NZiLaDua4APmGF5PXvrQ8rnF+VfBTuy7hE1b22ieXJHkdASIsr1vQRv2jXYGTmCUWYO7UrjaKLVkUfFv/Qldxhh6O31eyEMpYVQgQYVWVOUurTHKZcVA6k1mKVtVhpUlwOhfv8tWxacGjEyudLonkq40AEZba9nFUu0RX0w5pi12NaQqnY/RP6VnouFEzjPOfsYB2uTHJ3OAoMCRcWQSIsJQ1jXOKiZUT6uPvvDnFssSlmPypO1eS/ZLRTdwAar1c90+8hTc/lLa/BJKoMgJEWCpbxwHdzI7g8VhKsxh/ezog3jWR8G29IjQxLdSS7HStUCqo4ggQYVXcBO4okAv7AqJqdadEd0oBcd1HYWzcwVqFUoiwVLCCgzoMFPbFweIqIho3ca/Q2FIj2HAVhbGpiAlcK1RpR6trKFRhQdmwL5HAeQOFfam26mbXNVqsncLYVJtlP14famF9HBPPnykh7Ivn69yvAhTGph8g1fKTCKtaLIl6yLAvPJ1ZBD/VV6uoWiVXBf4tCmNTMnpqZiTCUtMuRWlla9iXokr2QGIKY+MBIxWuIhFW4VgplxIz050M+6JcfctUiMLYlAmgCtmJsFSwQgk6uBX2pQTVlM6CbiKFsVHaQoMrR4Q1OD7KXa1E2BflQChTIQpjUyaAFcxOhFVB8IspWo2wL8Vo7IW0FMbGC1bqqyMRVl80FP2uWtgXRWEqWa1sGBuNz8RuPn8pWQhldAUBIixXYC6tEPXDvpRWL3VzURgbdW3zoWZEWApayEthXxSEryyV8EBQGJuyEHQ2MxGWs/gWJT0b9mXdm1MtJi7xWtiXoirqgcQUxkZNIxFhKWKXagn7ogictqlBYWxsg9IWQURYtsBYupBqDftSOiJq5qQwNmrYhQirQnaohbAvFYLWsWLxsFAYG8fQLUwwhZcpDCfbUtVS2BfbQFNEEIWxqbwhqIXlog1k2Bdm8RuwXei+LhZLRTmHAIWxcQ7bASUTYQ0Ii70naynsC0bXVjOuzdC41ZgR4nrscbiHvWiqJ02GsalrqJ89/MgNb6mnXXVpRITloD1rKuwL51EuxJX6qL1u4hOfSUlYxdo9G2KvvzcT3y5CqzLgINSVF01hbFyxARGWAzDXUtgX3EAZtDB+yer4JXpzfP1AcCYfGf3J9Oae+bj2fSFYtd9zFMZmoJvApnPVfvPYBFPhYmTYF8GsJXgwJxaey6MpOV/u52JaoDX5UiE1iEaMiVxgh2kmJhWS3stpQOIUxsYBAxJh2QRqTYV94fzfPs7ag62JP5UCX6yz6RRhsWuRd5dS8nslz7YwNj42J9CSfM8requsJxFWmdaprbAvPM40fo2x+w438LGvbSkHOrFip+HmBvMCtLba4ZhvLEeW+nkpjI1dNiLCKgPJWgn7IlsKgOlXvrrhFwWa3/9vGZB9LOvWlukC+P2+/bGLVXaCwtiUb1AirBIwrKWwL275YsxlwUkiYy2tCd8fozA2JTx22SxEWEUgV1NhXzh7kwt+gdGWuKsIiMpKWmujq4zzW1hAu8yYZG4oC7gaykyEVYCxayzsyyau8QV6U2gBn7SupwB4bE8iuscE4r2bLkY/dDr+GmwvQCGBFMamOGMQYQ2BV62Efcn6qQT/XV19/QXDmzesGwIWVy73dBh7bOGZRZh0+nVXCqxgISCulcInpodakp0VVEP5oomw8piolsK+gKye5po2VW+J/yMPHBU9DVs0ZzJsCWbM719RRVwoHD7D+1idNtNoNl9zoTjPFUHRGvKYTFh8BIbcR+W5XBWn8bZ6V2PaaXpr4vOqkpUEOtiS6DbCsz4Ln885aIm8XxXg56uEYGNEiofyXa7189TCGuQOEGKuFu9a9EM4g6/C3ycGSeqpS2hRbYbhbwjWDb+GN7+f8JLyonOEYbL05UxYP8aIYp2XdB9UV87ehk0uxMvjt2hlyWkk9BkAASKsAUDpfyr7kIj0ZYxZ53v/IeF/bKj3z2psjv6nfz299NvsCo4TlnUD7PElL+ndX9cPXx58cVA0XcPb3kv2v06/t0eACGt7PAb9ZS4Pjhfp7ENy7KAJVbzI2fM+xqcFw4mHVVSvVJ1inXobWlsgLrF3qTIqlo/zexuEb2ZjW+z1iungsYKJsEowWCyi462efUjGlZDd1SzS54MACZcY4Zm/5Hyu5WrhLhUmuo/ym70rzkU/ai4c8yNcKrb0Yjh/ySfYtGBbYnnpQmozJxFWiXYXKw6ui29YNcUSHF1FoZcoxrFs6GqkBNNuNLh/Hm/dGHOsIIUEo5s4Ci2tK5klzgZ5+RRSLatKds4VZ5fprcfewvnvM6rp5wV9iLDKtFK8I/CJDBfXwE16Oh4SJUZdYdQHGPfNMMLm2jKr58ns8eWBCZlUdhpEiwoVgD3k5qw0q90GYxBh2QCiFLF1feGNeMMfapPIosVgdOkVwXzTQ+FYpOjMVZjB7Ax+VVhiIaan7Fmx6nG+zOdnU4NHJ1ZWTIcqKpgIy2ZjxiJNJ2PkagHE7myz6Lzisl0Njc3V/RN/xpsfSudNWIMXKrasCjHDNMZn6eH4vTUIu2NVJsJyANqtsZ4uhG+rHeQ1zIEisiLhpwI5Zbsal9MC2sFRdq3rznmCCcQM+/QOi8uNGTZ4jWrzKhGWg3bvWRbabUsmvRBr4b5pdzEgq4im8emYBf6K3bKrWV6yM/TZlEgvgU2OsLOesAdcmOw3ftZ4YVN4/Tt2yiZZHyFAhPURFo59i0cCR2LLq6Uo4IByC4Gfai3CvszU2+L3lyurlvNHI4ET0QKW25DtVi4OeIieYppvqtFqPlmuLMo/OAKeJqytUwsw+5x/08fFpYFwctng1a3c1eyOz50PngnA58ExP7poTTiPaUzMC47c68bcNlpFy3AhQ0/niF17Rep6kEGPf1jjRU1HrH/XhWJLKkJ07z7M7F0/S3BxIYirqVghsOW7nGkXBcPmr1VeTvPhvMHMZYLzXxktx/7cy1MqPEtYsQ4ds80xeZOJ8dtuNM7/hJnDs1SeOSy6QyEzlb4CD/S58G/5t+me5wsMZGHi522YVHQJJhr+L0+yip/OxrZPRmeDjC/Aw/9hjHbpz2H8KmOPHZao7M9JRkbvlGY91wLE78ImQz4TSNArOLvBGN54NT9sfbzi4OdRILsyI4UdnBg7ZlsSOWlVw6glFpRvO+ehL0MaR7W6DLWGDBXagrfdItXXZsU7A3tbQsjtwMJ5Meb8YT/zTwuEo8/nTaPAhWxs+wy6V3l2wcEo5r9gkxkYMbtPAXXzqoCX4OcZxzZkgn0+XyLU4z7h880ITY79K1+aSp8vbO2rN9eUeoawxJMj9ZiZuowzawpuqCFX6cMJKh2fF6i++h37GH4FrZJF/eYK/Qfr/trRovpDpW/+wcqXDuy0lZb7DB4+WLrcNRBXp+bDkhSFBwpgC252Br6DVsm1aCl+apvuco6bJqapHGBvW3QRS1wNm4zJ6Z7viGdkMya0LtStpmu9svBaecLKGiGy6HT4Ga7BzVR0iBe8EZ9kmjbFaDGfzme4Sp/PzhV6+81pQljTBNduMupGLebN/9lcab3ylR9/JDAm08OuxsDYD/FgFzW7Hw+JnIpxs2j0zQ0dHtuYr4xKnxcdOzSZWhK+LfEDTFO4Tq+feLPKc9zQ8zjcsqylINnPFo2dDG2j4eU+OXEnnheYVN2P0oQld1G2hHUj4DuoHAi3Djk7sk1VOXr1zyvf7irfMHKQw/xg1Y+h5eV4kI3++hfzG/X8AE/GJUbrsb9Q2Qmsuk3s3CYNLeB/CO6bgpUSK4qxpZtplSSsTd0jd06leuVedSfbCwZtaFkqnrEu/RiWkQ7cPoMcpQrbLh9/MesEbk08tN1p+jEoAgMOcgyao7CL8uUOl8vtfkV3q1aKsLbuojwLiGGWOBteGMTFp8Kb5DX8zaC5TENjt3WQYzFu4uOGTl1GCs7/0FDnb/d6YMEyECg4a7Qz8C3QipxDtmvBmYpOiJc74/OCO++6lE9Y2Vt0docyKENYWDrxTUQ9wKzw8ifyFYoV3iYRjSOoXWvi1ULz1Eq67CBHbMulwGhqIYMcduCCsuC349frI/Vr+cR3Ntkhs5pkJCKhA9MsDT+VvbP0B8MIXfe12PZtBmL+PzBYOreuVZywEstDB6TTWSMc6Val+5aDh0Q6gX+q1/nn8uZotO+1Wvy+daTpNLRy5SDHDhXCYJ10AhutyTsrVL5SxW4d5LgKvbUzih3ksKsieE46eJ02TW+Or7JLZilyKkZYZndwtEiJeXhbnFUpI/QFDG+S9VudwIjMWZvB1bYOcsglRAf3xaZS39FtfwLhcqaE2mLPVEqHSpabHeTYuOo8jMXIQY6K76STfbkLfpNe77+iUi931wkrG8429fR5mFA8VwUjDHBDvuDjfGq1xT4foJ7bTmUHOXp7r4ND/ZRtJxX5ghsUM/3ZHao6gZ2CKRur3soOcuzlVBmlysWLpGJht10lrGjECHOWwexuD2wYgGZWgw9O4MnRN0o1rOr5tq2lY+Ii6OrYIIc9OHAT0SnmBXfa9UaVnMD21O0jKVj3N5aJzGKQ9Jc/OqvoN7mxicDLvS3xiFsaukJYsW59T5ayFoGovuJWxewop5qdwNlBDhmtgLHd7cDKLRnSCcy4Nh2REf7qVplulJMd5IhvuYRbGORgrN6NMu0qAza5p57XtTe2bnzTLpn55DhKWOKx0cHYpp5LMHd2mteM0A+wdSCv2UY4+bt+5z33M9HVtH/a4nKk6SjPKd9HYdy4f+f12vRKO4H7qFTSV7zEebxLPw3H+fir1CBHSbpvl4mzHoQ9WqCP0hc4OcLrCGFljdCpn4qlJvNBVDtuVzEP/8Cb5HG/zzelaXLsWa9VI7ujTAaDHCw7yKHcjjKl4ImXSAqtrZt0BiewB3cGMpcFJ4mMJRdbTyyl/ormeYv5eHuoJXG3E/rZTlhwFn4BfXBsxsAOcULhSssEYNjZi92OvvsclcO95HDy3J59OcWLOEonMOYKXRxsmXmbF/Ze3LRs1KdS6S1ykOM7RVTTU0lhk0f9mn9qU2v0OTsVL2rhakEFi8wT1UpWsv5oMQIzPpZrHmm+p19oQoSncZjDo9zeiQXdTwUlEgYW/o5jkZ99GIeroDyVS9SbSX+S8Qru5ONC1UHGhyMUdbfdRdnewop2NOGZrtIPZ28iHEd7qDVxj9dqmN2rL82k72qy13QfTF90C+F890332h6MWbdJRP++YFm3yScHq6N3r3Ez1JYoa5F8/7oTYfVHZODfm9DlWKA3hRbwSet6Bk7ijbOYHPp1i8klUOLT3tB4YC3R5VjFfBgtbDH/PnAKb5wV3WMC8d5NF+MtPx1/Dd7QulAtibAKRcq2dHgw7q4bVt8+/MgNb9kmtMKCxNo9G2KvvzcTHdyLQFyBCqtTXPGIbc+FuEIftddNKse2L65SjEW7jE/zjJx/Jb5abF510xNhuWcbzp7TuDZFb40/5l6h7pZUbCxzd7XbvrTsYIeMbd/ILg4ekXh/+6vV8yva1dTCM1yG8Zng/VrZT1j2O909jjKmLvxP07SzjNb2idVMVtJMcv88zC37PuO+SSCEp1Q1nRxx8vG6g+EPOauayUrijxDMXYhueiBcEFMwuLNRVZtUSi/yYW1F3utzesq9gfrMnbsGvhQ1nMBykEPjs52a01MuZk7n9/7cOftbWERYuOtAVg9yP2ZNHx1f7fRNqLr8rasTLsbqBOkErswSkdys6WDoOq8Pcthh70Rn037Z1QlMNNshzz0ZRFi2Yo3u3xrMlJ5RbevS7AApusz4TNYJ7PL6TzfXpdmBk5sysDXcNzIWRng9s/7TfsKqUR8WVv5zNksfOX5fIquBHzm5754RTnyV+VgYJPLKwKlsPCsHOXzaESjzJDcW0dqouWuiEBn3j0b9mL3h07sUk4GTrhWsUEE1RVjo/1owtNxFeaweTi6qpmFxp+4puQ+fXjfxADwkU51wAkMuRvy0s7ODHC3xR52qR7XIldu/GW2Jq+p9w8YDu5qLyFozPiy0Ejy7cFmVhy3rBLbEVZi7dSb8W+D90j+1PshROnLb51R7AbX9XcJaICxPhIYBGXxNZMQMNHlvVH3H53JD1OCmUz40jBw1/XAHaH4m17T5Ks+oz47wdumn41jJOPzbM2n2FxHWAKAMfApvcE/swIJAevtmOFuy3Ro/zh+p4/5pdq90Hxip0s8WGwQQrVyldmDJV/OtEUcQGZd9PpcGJPsA92kzsXvMmtw51Y7bdjpibErFRni3A4UIazs48v6Qe9z5/LNUDm8ce0IfyRLWFSCqcwbqXuEBQSxzzOzG7sgqh7HJhllOrW/H2/1C2CNPmGVvhDfOhn3JbJ6PenwXZPWx3ofsxuL8UsNomMe/sMHMe/9V+II6YZaJsIa6FZTfQEKIE31m5MGzUZF5WH4xcqgKwdGNEU1xZfBTu/9E5VjmA+3WjQccPKbuLsI57LMb+MajMwUH6QrWlDuf74iW4nv4m4P4W3eoHH9r627dN+A+q9BGFkRYA95DuHnkFl2XGq3H/kLlLbrQhToa3T8Z4mXfASsyyEmMCHlit+rcVmHQd4sXtuiKRgInYhG43EV5t0Hgz3fpGaw3naqH44/nS1Dp85XdKowIa0D74+E4GUO9dw14UYGTPR3GHlt4ZhGI6uvlq8O7fHVsWvDoxMryZTkjQTqB8cE7RN1PcplxUDqTQXhicVi5WsrpBXX19RcMb96wrlxZTuWPdgTPgpfhVqfkDyzXfsKqinlYQsP8KgU/omOHJjMSuLqXpV+1h6xkJUWLlRIvxCKBn8hpBgpWG0ud1CUrjHDuEI00/RK7jT9tB1llLYL9HHt7t6yOdQQukT49FW2iaTJYrvc/VUFYqplBtjBikabvmjyxxhJiDu4UWwOzQZ4PZfzYyoi1sc7A+TJuu2oYqKaPWDmh3uwItqcz2CZMsB8CQ7vv/eHwFc2L9b7/qlxCo1r9q0Ufu41WLbiUXA84Og8xO4Myrv3/w99OJQsqKKMYISxxo5la8WJ2p+CC8tReItjjq+a6N16xmLUALdSgwwjsjvV+f4BvrFvOV3O4rJoTT4Rlk8kT3WN2RKvqdmZl/onWzxdsEluQGJS3t7Ayf491NN2PbuK4gjLVQCI5xw3E0YUNKv6M1s9nXK0y9n3MZNiz6CberGrX3VU8bCqMCKtMILNdjUhwdrq3Zw1aVKfh72Pzd8osouDs6OZ8WVjWy9FIcKHoHGFr8P+ClVAgoSQIdJV/itj1z8N3OLlSKmW77kycQ113+yxAhFUGlvCJHI+uxkpLWNe50NUoSFMQZh0T1kzTSq2VI0NCzK0ZG0tfHlo0UyRBoKt8riSMgkBzPNG2rvsLCIHc6nhxVVxAzdzMdtoQTtW90f3rgE/kPnQ19rRTtl2yoNcYOYwdi1z/LPQ9yi65qsqRkyTN3hUvod5L8fIYoaKe6LrvwzIsAlL9s4w3pqKOqutEhFWEhUR3KITpBEsw8vciWjLhIrJWMukBcAJ3RzsCf5DzwSqpiBNlm8uD4/Hy+KvIZB4EWVVoRndxNYOeX+Xp9EpMr7hWbvNVXO7aTk2EVYD9ZbcKztuzzVR6Ld6SU0FWHpxGIL4h54OZkaZrquEhyb48OoOLRdp6Cfb4UgFmVCoJuqsNmF5xgdm7aQ1cC6fivqqY71MpYIZQhghrCIDikcCRslsF5+0tuKlGD5Fc6cvyIcGK6ou8/JDItZh4efwo+/KwrOlZn53SqA+uHGzySbgW7sAE4ydjHfq26BCD56rdq0RYeWzfsyy0Gx6MezJCPIQkB+RJ5snT2x6SzsBTMgCcVyoh12LGOh98Di+Pn3n95dEfc9jkc4xn/oHu7a/lfpH9r9PvDxEgwspzJ2zJpO/Hg4GFsdX7QetkopW2Hodf7s5ND4/cRdWayl2R8fL4U4aJZbDJfqrqWa5esAc2tWbfS7PNd5crq1rzE2HlsSxWw9UMNmitnNy7ecsqzF26XIZayQOJ66fllmNmR9N8nkm/AqKyYeG461UorcAauveKBahmHspiganB9MMxd2luLL5RLuL9diXrLx3QWE5zupnsWYNV7RdK31sl9aGy1UGACEsdW6iiyS4Ydv8dSOvxaMSY6LZSMp4WuqhPYznN/4GodnS7fCpPbQSIsNS2T8W0A2lN4iz9lFwfmXxktONb1/d0jtgVRPU7rBp4DJU+uGIVp4KVRsB2wtI07QeIh/Se0rUm5QpCYKsT+LTU5s1rop3BC8XaPW3vmokVOw0HUV2xRfSuQlewol3RgkChRIUisA4Ty2QocFs/thOW3hq/XR8+bCy0XAiFe23VloRVBgEhAsyy5sdef1fGejrBLiVinU2nxD6IrQZRXYZJlMo4++2qX03K4awHDZZ5xihjvBNRgG0nLGkkftj6eKgt2c64b1+Q1gM1abhqrLRge2CZzx+xzGd5ObGeZMww+MieEBb7LWDauRqhqsk6ZXerqtvbCCcu4xPf2eQEBo4QVk5RI2yuNdqSx3PNdwziXq/Knaej1xEQzTLWE2Zn3xJ/JIBF1oV9pC8MPrE7sjHDmPhiYbkolQcQkLtVHRUKJ050ems9RwkrB7TRanbo9RP34xqbjoDf0dx5OnoXAYzg+bAI/OzMZrYWgQOny91Z8tVGxjlHjK450hcGv9ip0jeWLy2d9w4C6Pqtx/N8jhFuPygYTjzshuauEJasCG9+KG20Jpf4hjFExOQ/xx2r5MYRboBeVWUIYYC8FpsbVr+MMM3H9a+bjG8u45wjRtfVmPxJkQn6A+TB39hvMg2yulGv849Fq+oWN/dmdD3qQPCIxPuw0dmJSOhnaZaWe/Qd4UGbkcr9EIDjfBwTmQfQ5evQOJ/Ohb8B9l0Cn9eR/ZLSTw8jALKKwL7Tgq2JVytRDdcJK1fJQDj6PL4fGe0MfAukJTey3DV3jY7eRQDdvTaEJn6RiZRsvbvWgvcuYt7QHD7oDzfyDcfvr6TGFb+hQq2Je4zAiL24xucCCEdGFioJcC2WDdLyo5tY8XurFrG3v848zrh2ob7zbhP0tsqSlaybEjcVn7Sux2hNXFE/rGEvMDmtVLf/riOJhEBRCKDrh+272R3++sZxoXD8Oj5hpRJzKpUgrBySw4/c8BYmm31b82lHYBzpudx5OhIChIB7CMCh/iTTfJ83wsnTA83v/9e9kocuSSnCyqmrt8QfNVrbJ2KZz1locUknPX0IAULAYQTQonoHf9/DapVJRov5tMPFlSReScKSNZFDpQDuF7pWN5Zr2g0AMlVSDSkTIUAIDIoAphhtwcjfNboIjEOr6jdoYcEFqeZHWcLKwcVbN8aM1vgM7tf2A2k9mDtPR0KAELABAc7vrWf+vfVw4mLe9l7SBomOilCesHK114+Orwb7fwnLfL6MN8Ca3Hk6EgKEQAkIcP6yj/HJmPh5QmNb7PUSJFQki2cIK4cOlvn8VR85fl/4t9rRcTRz5+lICBACQyMAn/AGvPB/bLQee2CwLbF86BxqpfAcYUn4+MRnUvBvLcQ+5GMxmnibD/skqQUraUMIKIeAXE7zUxbUxiKawk85/31GOQ0LUKgqFqHKjU7tXs+E8CcvI+rmhAIwpCSEgK0IoBX0BKb3HGqnUCeeETv1K1SWJ1tY/StnN1n1l0+/CQGvI1Atz0hVEJbXbybSnxAgBApDgAirMJwoFSFACCiAABGWAkYgFQgBQqAwBIiwCsOJUhEChIACCBBhKWAEUoEQIAQKQ8B2wsJ0gBujjxojCiueUhEChEA1IhDvCHwi1hlcbHfdbCcszF06n/dk1iKS6DlCnIi5nfQhBAiBWkFAbkYiNyXJcLZGWOKHdtfbdsKSCiK+9yhmiZtjnQ8+F+8KNNutNMkjBAgB9RCIdejHmh+sfgmhHhaDBAwnNHSEsLYpKsR+mYxYjo03/9DTHdp923n6QggQAlWDgNkVHIfNRx4QLPM39LDGO1kxZwlrm+biG72p1KuxzsA80bFD07bT9IUQIAQ8i4B4cqQe7Wi6XljWy4jjf5wbFXGJsGQ3kQ1Dn/aSGE+sjnU2neJG5copg/v4hVjT9a9yZFBeQqBYBLBA+VXhE5cXm8/N9HJdotkR/KFp9q5FubPwbOfdRNduvWxf/AzGLShaoVzgKbhvaigcW2F3peySJ1ZOqI+9/eZ0sO3FoNygXXJJDiHwcQT4RgT6vEKvO+SnctPhj19X44wZCR5qCetGaHPQ0BpxM9SWsNWXVTHCkpVFBFH459ntfh+bE2hJvjc0AJVJkehq2iFtsfkIHHsq2Ni1VmllakuluokAHsAM0/itaFldhr0MPnCz7GLK2tQ9cudUqncBHtiTC89XZYT1UcW5qWl8XnCnXW9UZTuhj3T76FtymXFQOpNZCqMd9tFZ+kYIlIoA7/LVsWnBoxMrS5XgdD7RvfswM7W+Hff8hShreHHlVS1hfQgD3jJrsaHqDLxpHigOGHdTR7sCJ2HaxgLardpd3KulNLhDXsN9PgtBKP+icp0w+fObGS4W4j7frTQ97Scspbo3YPGxVsa6HxPPHjS7g3uVBpLzuUItibuzu1VzLp2jtFu185BXSQnoSTBtdnYXZYXJKrE8dEA0Engow8TvSycrZ0xWUR/WYFXKbuvFtZt0v+9K3hyNDpa2ktc2LRv1qVR6y3WMi1Pgj7Mdz0rWjcq2BwHcFJbg7Haf4HMQR/1/9ki1XwoaCaNFSsyDZ/lM+GptWKVS5S2sviaQQ6WY3zHd7E2viXYEz5JDqX2vq/J9+OQP3kY42+8y7puEG/MpVfQiPRRBgPNH/FrdxFA4eYaqZCW6j/JjDfAUKyXWopfzI3vIyhn8bW8RFDqtoejqcPY83lBTYfRHis7rUgYYm5tdxveYyMwH4e7kUrFUjIoIcPYGhsFnh1oT96ioXk6naMQIc5a5AffuPrlz9h1rqIX1MdAEOxB96odjkcDdPZ0jdv3YdQVOYNBAYBuyX8sddOVOuujWblZALVLBTQQ4S8KpfqlRN2Yvlckq1q3viWfpL0ykO5whK2dA904Lq2/9Oevhgi/Qg6Hr+KR1PX0vqfRdrp/ckkpfD5/AN1XSi3SxHwE5pxBT9H7rZw0XNIXXv2N/CfZIFI+NDsY29VyMOYXToXC9PVLzSbG/heVNwvoIn7eYj7fLUbuPTqn3DcPDR2B4eClu6QPV0440KhcBtKyfZEKbZrSZ/yxXllP5pbsi3qmfKoQ1H0S1o1PlbC/XfsJS0pG9faUH/bULy4i74p2BEwZNVeGL0u9mtLYfrHHtTNzcyo4SVRgm7xXP2dtoWX0P86kmqUxWElhJVlhSc7t7ZOWMOb1OWFlUsIWt3xl47JMq94XTw/Ff6nr9WEhdiKZtr33SSZKrCEiXhMavMkRgvBFO/kb6Ll0tv5TCuHsLlEtRr9A8VUFYhVZWhXT8CxuwIDTZzup9E/B2vl8FnUiHwhEAOd3T4Kvb22hNXMrb3ksWnpNS2oEAEZYdKJYgw2g2X8Pb+SuYnodhZa7sWrISqlatWZ7VfNoRRjhxUuPk6BvVWknV60WEVWELhVqSnXr42APQxTgfxLWhwupQ8f0QQIvqPSynOcMItx+CNa6P9rtMP11GgAjLZcAHKo7z32fQxbhJDPftCdL6CbqKysZDGkj/ajyX9TFq7Hp9+LCxelv8NumDrMZ6eq1ORFgKWSx0eGwjlvlMwaTT/UFaHQqpVlOq4KXxF+H37xNqTc7mh62P11TlFa8sEZaCBgq2Jl6Ff+sY+EyOR5dkjYIqVqdKnL/s56wFL42vhSbHKDy2glYmwlLQKDmVZFwwfeT4fTXOZmJdWix3no72IoCXwgdoVZ1ntB57YCCcXGavdJJmJwJEWHai6YAsPvGZlB5OLvYNY5i/xX8O3wr5UmzCWfoKQVZLRaNvLFpVN0tfok2iSYxDCBBhOQSs3WKDRyTeR0D/s311dQehtfWQ3fJrTR6I/++8TtsP0xSmSd9hrdXfq/UlwvKY5QJHR18IhRPNPo1/E+ECX/eY+hVXF12/1Zz7jjPaksfqzfFVFVeIFCgKASKsPHAh9MalychoZWNawTH/R2OPT+6NCAFz0OJK5KkGnc4hwHmUa2y6Pmo8WlXm33KnVTvKCB/RzqDc8IE+AyBAhDUAKNlTgp2UYj1ropHgHLF2z4Z8ySp5no99bUuoLT6/btiwcfDH/Ap/6q9pcxkwdP0y8FPdotXxsUZrcon0CbqsQkHFyR3R8ZK8Uu6Qzi1xfEGZajAREdZgRhesiQnr6tjr776KDSS/PljSSl5rOmL9u5gGcRrTfJ9Hl+eJSuqiVNmcL/f52EHwU52D7t96pXTro4zcCV3uiI4QMJciUu2wPpfoaz8EiLD6ATLgT8H2QGiOP2EnkWWIbbXvgGkUOGm0mE9jtOtQtLROgTpvKaBSZVTg/N8I5XMCfH2TsUHvi5VRYuhSox3GwYil/riw2G/RNv7U0DkoBRFWMfeAEEdbTDyPpvtNsSf0kcVkdTMtWlu/M0YZe6G1dQUc88pGZLUfEx5nXLvQ2GPHfRDK51775dsjUe4kjr0PsNwn/bRgYpI9UmtDChFWkXaGk8iHpvt5LG6tBXGdJ8SJNmyHVKQSBSTnE9/ZhNbWXE1o5xeQvCqSwBA/CIXj10nfnooVEisn1JudwVnpTHb1wg/Q/YOLjT7FIECEVQxafdLizTgSxHVTrPPB5xORpsl9Lin1VWhcSSezEyCpXNdYp36c+fYbL1uWdT1jQnei/rUgkwirXCsLsW9asC74t/4U7TI+Xa44yl9dCMgdzOVO5sLKPIAXnIw2S58yECDCKgO87bIK8XWeSb9iRgJXi+4xge2u0Y+aQ0B0jjBincHFImW9CDfCMTUHgEMVJsKyEVjcmA2WEHPM1KbVsYj+PbxRyUdhI75eECV3KIef6kzTSq2VO5fDT1XnBb29oiMRlgOWwk26kxCZX+PGfSK2TP+cA0WQSAURMLuCh8c6r18BP9XP4eMco6CKnleJCMtBE6KF9QWWyTwZizTdnuge49JecA5WiEQPiIDciRzzqe6yMtYjmE/12QET0UlbECDCsgXG/ELk0DX+Tkv3Zpf5XCCHtvOnpiteQkA8sXNjrDNw+RbRuwotqpO8pLtXdSXCcs1yIohlPtea696AYz74FdeKpYIcQSDaFTgplti4SlhiLlpVjY4UQkI/hgAR1scgcfYE3sSfwTKfv6ALEYl3BfZxtjSSbjcCiUjoQNjuEbnjOIhqV7vlk7zBESDCGhwfx66CuFotS7yA2fJLo48aIxwriATbgkD8kcCYaEfg1oxIPQPbHW6LUBJSNAJEWEVDZl8G+Lb8cMxP4T0ZhLEJ/EjVZT721dh7ksSKg+sw8XN6ZjNbixnqZ2HqCj0zFTQjgV9B8HNFg7RGMyF+Fut6kAK35UBR5BjbuOpqkNRi2MdQRKWaVoMISyHzc8GUDBSoEESuq8IFp1Fd11HPXyARVn5s6AohQAgohgARlmIGIXUIAUIgPwJEWPmxoSuEACGgGAJEWIoZhNQhBAiB/AgQYeXHhq4QAoSAYggQYSlmEFKHECAE8iNAhJUfG7pCCBACiiFAhKWYQUgdQoAQyI8AEVZ+bOgKIUAIKIYAEZZiBiF1CAFCID8CRFj5saErhAAhoBgCRFiKGYTUIQQIgfwIEGHlx4auEAKEgGIIEGEpZhBShxAgBPIjQISVHxu6QggQAoohQISVzyCauAa7oP4332U6XzMIuL0Z7luc84U1g26RFSXCygOY0Zq8U29qHIeAuNfjju3Nk4xOVz8CCDjqwoezHhDVlcYoYy89HL/XhRI9WQQR1iBm44etj4dak7NZvW8CSOuBQZLSJUKgdAQ4/30Dr9/LCCcu5xPf2VS6oOrPSYRVgI2NZvM1oy15POP+NrwFXy0gCyUhBIZGgLPnfYwfGQonvtXYuvHNoTNQCiKsIu6BUDgW0esm7s81Np1xHi0iKyUlBLYhgJfeetw/PzJa2w8OtiUe2XaBvgyJABHWkBBtn4A3P5SGf2uJVsfHapzfiq6itX0K+kUIDIwA5ywNslqq1/nHolV1K+dz6d4ZGKq8Z4mw8kIz+AW9Ob5eDyd+5KurOwhvy4cHT01Xax0BkFUHXnD7w081jTdHqXVe4g1BhFUicLlsgaOjL+BteRTT+EmMszdy5+lICEgEOOOvaUz7ihFOHhNsTZD/s8zbggirTABz2UOtiXuMwIi90eS/HOdopCcHTM0eeVzj2gX6zrtN0Nvi99csDDZXnAjLRkD5pHU9aPJfWT+sYS8Q1102iiZRHkEAXT+Bvzv89Y3jMJ9qAZ+wkubw2Wg7IiwbwcyJGn7khrdAXCdrmnY4zj2bO0/H6kYA3b9/COb/HLp/pwea36dVEg6YmwjLAVBzIvXW+GNGuP0QdA3ORIvrf7nzdKwyBDh7G62q76FFdSimvqyostopVZ3qICzBzsIMqbFKIbtVGTl0jRv5lzqvG8e5thg3dkpFPUmnvAhg5srAH9hyM1pVVxsiMB6tqt/gpeTOMp6B1cl7Nr48MEEIcWreBB66UCWEJSYzkXk52tF0vXhypK4i/rx1Y8wIx2dyv7YfbvQHVdSRdBoQgYFJiPM/1Qv/PkZb4hLe9l5ywJwVPml2BUfFIoGfWCnxAgjr0AqrY0vx1UFYgAJ3VT0Os0yzd60ZCZ4hxFwl66YfHV+Nt/GXOPcdhzfyGlusSELcQ4Dzl7CcZjKmsnyjsS32unsFF16S6D7KH+sMnG9lxFoQ1Y/xbPgKz612SiUf6nIgg4E+YQnrF7HO65+JRwJHliPLybxG2PybPnL8vhpnszBbx3SyLJJdPgJ4uXyA7t95Ruuxn8VymuXlS3RGQqxTbzNTK14UlrgRr/ERzpRSOalVR1jboBTswIwQD0UjgXt6ukO7bzuv0Bc+8ZmUHk4uwutvLGYY3oZmIi3VUMg+UhXBuFxOcxMLaOPQ/bsZgRUyiqmYVQfdv3Gxjqb7hZX5O17ae6uoox06+e0QorQMIU7sTaWONyOBxcG6xvm8+f2EavrijS1HEM8Q3bsPY0w59VSDy1V9jLpRl/Dm/2x2tdAiChOdIwxTpC8TlnU+un51RWT1ZNLqbWH1MYcQbJglxBwztWk1RhO/hzdQ3pGfPtlc/6ryg+E6GIoUqKpNpI822hE8y7RS8FNZM3CPVz1ZyVuiJggrd+/DqDsJkfk1WltPogn9xdx5OhICXkIg3hk4Kha5HhOSrVsFE2O8pHu5utYUYeXAQtP5c2hCPx7rCPxmU/fInXPn6UgIqIxAT4exR7Qj8IeMJbqh5wEq6+qUbjVJWBJMtLYwy098p7d3C7qJgUvFEzs3OgUyySUEykFAdI8JmJGma3pZGtEexDfKkeX1vDVLWH0MNxw+rStjiY2rol2Bk/qcp6+EQEURkL5WsyN4qtm7aY0l2EXoGTRUVCEFCifCyhlBsF1ZRtyF1taj0Q7j4NxpOhIClUDAXBacZHYGnrKYdQeI6pOV0EHFMomw+lkFb7XDEMn2KSzzuS3RPWbHfpfpJyHgKAKbHh65C3yrv7XS1uNwW0x0tDAPCifCGsBoeKNJXH6Q7u1Zg2U+s8XaPWu+KT4ATHTKRgSkDxXLaS7v3bxlFXyrp9gouqpEEWENak4RxDKf68x//3clpkF8bdCkdJEQKBEBtKi+HYtvXI3lNHMhYniJYmoiGxFWAWbGG+8zVsa6F8t8liU6m/YrIAslIQSGRCAaMSaCrB7H/fU7JN5lyAyUoLYmjpZtbyGOzljsOdxkN5vdwdFlyyMBNYlA8pHRn4xFmm6XvlKQ1aSaBKHEStvewsJC0SuxkLenRH2Uzwb/lg832TmIMbQ21tk0Taw4WOklEfXM9xDib3UoD2yZCuK+u0/zD/tnmWIczS59odHO4IWpzZvXwKF+mpwL6GiBlRTOeUJj/Cq7VXAEsJ7OEbv2itT1GHH7lt0KqyYPIUdWw0c/3WgzlQ7Kh/k8x4NoF+NvT9UwLEcf4L9S+MS0UEuyqxw5TufFcpoTED1kIcI/7OF0WZWUj5cj3uns1/5hjRc1HbH+Xbt1cYSwckqancHDLMtait8H5c5V61FGEeV12gxssLpK1TqKlRPq42+/OQ0LwS/BjOmgqnoWphffiJt3rl4/8Wa5G3dhedxPlehq2j+d4UuAd7P7pbtbIl4e/2A+barRYj7tVMmOEpZUWq4qj3cu+gHe7FehxbWDUxVRQS5IK41Nnm7S6/1XqLy7r5xflkltmg/MTvVatwQ3LOJR8Z9zH79Ub4l/oILdB9Ih/khgjNjM5uGeP0O6EQZKU0Xn1nEfu1CfnLgTXXPZwnLs4zhh5TSXsdZjsS2XosApqJEMZ1y1HxhtPQLYXGa0HPtzVQO+SfDlKBUXmRvxMvFI5Are7Uf3L9CSfFHVm0f6NM0PVv0YmxNejre1oaqetugFXzXu9UX6CH0+n/iOK5sHu0ZYOYBi3fqerDdzA0jry7lzVXtE/G8/E9MD4eQyVeuIFgDHEpDvwB7XwvvwKUX1/A/iqLcj0OEfFNUvqxbCEx/HhLUYmI5TWU9bdMObuMHnb2+cHH3DFnkFCnGdsHJ64e0e5gzEJcQ+uXPVe+R/Zn7frNDk2L9UraPo2KEpzpNz0NqSweAQ+VSBD2dJLvi1ev3ohaoG0pMowaG+N/yCuJdZmwKoOasCZ8/5BJ+Gl8cjzhY0sPSKEZZUR+7uYfauOBdv97n4VXUB8/tCDqB70U1cYgxvvIoftj7e95pK32XMpS08g9EscUIl9YID9846f8Ps4ZM/eLuSegxWdvRRYwTvyczFvXsuyKqqw42j6/c//F0SbJl5m9xrczBcnLxWUcLKVUzun4aW1pXMEmeDvKraQQmjv4e/OTD8HZU0fA77fMd4R+DoDAgWxOXqzH4MXKzgGGnSJ8efyKdbpc9jmwCf2fngj6DHFbhvR1VaHyfLhz2w8a/2E12vu4J/YYPpZFmFyFaCsHKK4iHZd+tDMjl3roqPz2oaHkxsZ69qHbc9mIJdia7iSCf1/IjIzdvxHe8tNT/RrqYWjmkKwGOCmhrapxXI6q9oP0zHlnRr7ZNaniSlCCtXFbnQWGTEQtwUn8mdq9Yjuj5312t1sxtbN76pah1jT+gjWcK6Aq2tc+xuAWe7yozdaBgN81R4g+ezQXawKGUtQovqK/nSVMt5vDBeZRyToVtN5VZIKElY0vByGUPs9fem4SG5GL88PslxiFtZDg8zvlAfqV/r1vDwEBoNeDm+PDAhk2ZLYRNbWsAqvsH7Vzw7HSe+5RJusakg66qejoP5bRvRuL1Crzvkp6pOxlWWsHI3jpcnOebqUPCR84exBfpRBaevUELZArYssQjE9elSVAA5r8KM6OmYEf33UvK7mScaaXoO0z0OdLNMt8sCCXhiMq7ExfbFz3aDHWh+/79GOHk6BmE+hxtdWUesLfUW3mhJYob5n409dsR0FG0OwyLXguvOeQwPxwx91Pj9vUBWsl6YVhEouH5eTMj5cp/GPotdrc9VeeVADlrlW1g5RXNHREg4RVjsOvyuxu25ng21JT0VTz4ZGb1TmvVcC3t8N98yH9xk2EOB3+ZrZBcHj0i8n7OlF44IJbQWvtSqWjCexZ3zfyOawiw9HL/XC3bI6ah8CyunaO5otCbvNEYZ4+EYrOowNrn6qn5sCq9/By3g7zPh+yKI6an++qJV/KiP1x0cakuc5TWy6l+XqvidbRFrc2QL2WtkJfH3XAur701ThWFsPNfC6msPjKDxeET/vmDWfEySTTGNzw61JO7um8Zr36ulhYUBDjlVxLGwL27Z1dOElQOpisLYeJqwcvaQG3+yhoYMn7TO84EcQViveX16DVq5jod9ydne6aPnuoQDASInXxrh9kM0rp2JruL/BkpD59xDgDe/n6gGstqKmLKTWIe0KGdvI+zLd9H1O9TJGFVD6mFjgqogLImHXOYCw/xS1+vH4udCNB17bcSJRBECnkEA3b/NXONXGSONcUZL8rcqrxwoFtSqIaxcxeVsaYy0tTPu2xeGuz93no6EQE0ggLAv9b66vYzWxKUqT0Iu1RZVR1g5IOT6J4xefYVxfxveMK/kztOREKhKBGTYF8aPxMTjb7kdo8pNPKuWsHIghsKxiF438QA4HqfKpQe583QkBKoBAemzxSL6s4zW9omVilHlJo5VT1gSTLkuCjN5b9R8fCz69jfDv4WlCPQhBLyLANwdKSxQXqTzunEYdPqFyqGK7ES5JggrB5hceoC+/XmY4XsgvPTKhi3O6WvHsWdZaDcZTdQOWSrLEJ0jjE3LRjkR4lm5qT9Q6AGuafuGwvFZvHVjTGW72K1bTRFWDjw0nV9GX79F82lfR1dR2bDFOX3LOfZa1pExnlgd62r6jpzYWY4sFfPKXZmw5+IPTZFak7Z6JzqgozLTGtD9e5VrvmOMtuTxePmucaCuyousScLKWUUu4tU/veMENK0vRMdR2bDFOX1LPmJzCZFhvzEjwcdjXfohJctRLKOcMByLXP+0xaxfgow/oZh6Nqojw76wafDF7q9ijCobKzqkqJomLIkOH/vaFjStr/PXN47DTYGwxdklDEMC58UEmLH9RWZl/omQKf8nw/Z4sQ5S500Pj9wlFgnciU16H8XPg7xaj6H0lr5W9AB+Jn2vGPFeqmqMqqHqYef1miesHJi1EsYmG1FBsNPTvT1r0JVql7tB5zBQ/Sie2LkRRHVZ7+Ytq9CiOll1fcvSz2NhX8qqaxGZibD6gYVpECswongo19h3cGldv8tV9FME0ZVaYK57YyUC8im/R2Q0Ejgxltj4KojqChhheBUZYvuqyLAvXDsBPtbJgdbkS9tfpF9EWHnugVoJYyNjPVkZ6/5YpOnvcn+9PHBU7HRieegAkNVDiG56Dzrru1VMEacL9njYF6fhycknwsohMcBRLm0wwonLG3j9XhihuWeAJFVzSm4Cis1AX0R0ghtEdyhU6YqZ3cHRZiRwSyaVehZkdWSl9XGqfOkzxd+v6oYNGxdqi8+XPlWnyqoGuURYBVhR7mgD4joJ0yCOQPJnC8jiySRyM1C0uKaZqfTaaEfwLDllwO2KyM110dqbaqXEWhCo3KfSdR3cqnM27Ivm+zwc6qc1HbH+XbfK9XI5VXszOGEUTIN4tBbC2MBPNBpRjW/FlIFnsVekJGlXPtEIVoCmVrwI4pQbuFa8ledYpasw7ItjWPUTTITVD5ChftZYGJsDMkw8jJG5u2V016GwKfW63PMPrar7mEh3gCyV86OVWq/++dD12wzXwrxqDPvSv65O/SbCKhHZWgpjAxL51hbRuwrEdYVYsZNtI3TisdFBzAm7jvVmVqJVdXyJpvBGtlzYl3DismoM++KWEYiwykS6ZsLYCNYI4ros9kFsFRzz3y4HNsjhmHV/mpnsWYORv9nwU3lmLljR9ebs+VoI+1I0LiVmIMIqEbj+2baFsdH4lCoPY7MLHPO/Q2vr0eQyo+hZ5pjz9UWzM/BPS1i3g6g8O9u+v/37/+4T9uXgWgj70r/+Tv0mwrIR2WwYm9bET2ohjA1aSYel0+mnMUfqF3DMD7mOT0ZSiEWC/09Y1uPo/lXNesb+tw/8VDUZ9qU/Dk79JsJyANlaCWOTnXIgxBlY8LbGjDTNECsOrusPp+jefVg0EpzTm9m8Wggr72ar/fN58TfI6q+1GvbFLXsRYTmIdM2EsRHCwNbOi8wPVr8U69CPzUGKmfMnxFLvv8KEdTV8VVUbk2tb2Jdw8su1GvYlZ3Onj0RYTiMM+bUSxga+rfGCZf6GKQp/RVdxWcYSfwRR7eECxE4WMUgMMQr74iTwA8kmwhoIFQfO1VQYG8G+hImfRzsAYyVEoue7/YfCvmyPh5u/iLDcRBtl1UoYG5dhda84CvviHtYDlESENQAobpyqnTA2bqDpQhkU9sUFkIcugghraIwcTdE3jA2ct5scLYyEF42A4CKB9ddzjD123Ac7i99btADKYCsCflulkbCSENi6VONy8eTIRSUJoEyOIWDoDUfKZViMVW/If8fAc0AwtbAcALVUkR8+GKXmpnxOIEA2cQLV0mUSYZWOHeUkBAgBlxEgwnIZcCqOECAESkeACKt07CgnIUAIuIwAEZbLgFNxhAAhUDoCRFilY0c5CQFCwGUEiLBcBpyKIwQIgdIRIMIqHTvKSQgQAi4jQITlMuBUHCFACJSOABFW6dhRTkKAEHAZASIslwGn4ggBQqB0BIiwSsfOEzk1Zr3JOOvxhLJlKcnjltDeLksEZVYeASIs5U1UnoLB1sRD9Q0N47Et+t3lSVIzN+KoC/z9yl/fOE6G7FFTS9LKLgQGCf9qVxEkRxUEsMXW4ZZlLUXY4s+qolM5eiAcz5NM06YYLebT5cihvN5BgAjLO7ayRVMh5mqxyKIz0DC5CjHYx9gi1GUhaFG9w5jvQr019huQ1sdCGLusDhXnIgJEWC6CrVJRonOEYbL05djR5sfYJ/Bj23OppGtOF9ysW0BWi4MicDVvey+ZO0/H2kGACKt2bD1gTc3lwfEiZS1BM+WYARMoc5L/mfl8M0MtsX8roxIp4joCRFiuQ65mgbFO/Ti0thZjR+dxSmnI+ct+JqYFwsllSulFylQEARolrAjs6hVqtJp/1UeO31fTtHbGOEICV/aDUc0NXOPnG63HHkhkVVlbqFQ6tbBUsoYiuiS6mnZIZ9g1uDlOy25H76JeKDPDNH4ra9IuNSaZG1wsmoryAAJEWB4wUqVUjHYYB3OeWYpu4qGu6CD3/BNsarAt8bIr5VEhnkOACMtzJnNf4Vhn0ynCYteh5J0dKZ2z132cz8Ik1z85Ip+EVg0CRFhVY0pnKyJW7DTc3GhehC3oZ2EaxDBbSuMMUxO0a4w9dljEx762xRaZJKSqESDCqmrz2l+5nu7Q7lt60wsZE98oVbpcTgOi+q2fNVzQFF6PSaD0IQQKQ4AIqzCcKFU/BOKdgaMyFlsK4tq/36VBf4KsnmbcNwWjkk8OmpAuEgIDIECENQAodKowBIQ40RfrevAsLI6ZB8f8qMFy4Ub7L+faRcFW81e0nGYwpOjaYAgQYQ2GDl0rCIHoo8YI3pOZi9bWufBv+ftmwg3WKzhbYgxvvIoftp72e+8LDn0vGgEirKIhowz5EIh3BfaxMgzLfESrTIPu3/2szjfDaDZfy5eHzhMCxSZs1a8AAAAISURBVCDw/wECLJVpCeJX2AAAAABJRU5ErkJggg==
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAMkAAADICAYAAAE1nfU2AAAABGdBTUEAALGPC/xhBQAANSJJREFUeAHtfQmAHEW5f82x972575CQBCLGcEggQkAERCBRziTIqaJPBZ8KPPnrX59Pnz4RkUsfCmIwRCAcolyCoiIICkTAEEjIQbK5yLHZ+5zz/X41XZ3umZ6Znt2Z2Zndqt2aqq6uruP3fV/dhxDDTXniMuQb9emLQ3FuA3o8cPeqUnwYVB97lQWmP1uRMEyEFYBRQTuVmSO8iMacsvuLnMk4VI782Q3eFloVn1QE5bZXlodoNCqigaCI9PYIj9crPJWVwutXn1k8JrfW41W3+sKE0Oo/0t8vXrnxVquTtN/wqxXikQ3rhNfnS3jn4GCDLuF9pK/PMRJ6/NplV4hX/ucmEY1EEr5L5qBoZHtPuF750W02N6eHcw9/v5OzkHAjEdaEOEfU1+8YQLzj1y65TEQYIOlIMxQSYcAdae8Uwd17RGDLNvMTRSPTgZZwR4ft2frAQBl4OBwWIQbc0SVECMzS0Slqj5kv/NXVVu+i6/mX5LNjRFafDJiBhhFoH1Lb1toqdu3cKXZsaxJ39hwQ9fPmWr0ntdsiYqBU3poa0dPTI3q6usS+ffvEjqYmsXpXk2gSAy+dzIgi/QHIS0CEO7tEBHrxql8kTd1AXpgR1cyaMZDvXX/jyHWuv87Ao44oA7DsXhV0rKRypXoYsIrIXZkzsKS0WSMS2//zB+MHFk7yrxDm4Xgri3iVI/reixeTk3+W2Rsjkg3qK6cKj2510PbSUX2R3uyFl1Zo95VV+jALyIcNssbl516DRsePspC+NjSvGlQ4ZiS5aMvFt+NkW0vFnEVTiojMSS5yoRLK3Jj1jnKMN9m4iPT0imgwKDzlZcJbXi48HhPleO+Oz0kjYdUd2LZdvP7r1QkfHvP5K9HqN+ma8D7ewSr55jtG8JkFCx0joKc1d9wlAu/tNf2nszhGEm7rEFcuOSflt6/d/SsRQcsnXjGBUrMNB03lGMman/48/lvn5737DwaICEk30i/UfEAEtjaJykkT5XdJaeIcKgolMgI0225//PFt4tRvXY/WULdsEY0+/cOOn6WMhNm2tjK7Oztlu237tm1i1XtNYg/Kwdoj0jcIbZEwUORf9KNXwBZmR3u72LV9h9ixvUn8rKvZMZVuHGUk0VBYRIJoCAJPNgQ//J//T1TMPMTN9678yEiqZ0xz5Xmgnhy5a6CBJftOR5IMGUf3GFzRaC7bYbFiZfu3b5jjmIRBOqJ59EEGoQjfFGw+8Oogw3T6/DU6WmsfRnjO1P+6/mEn35m47f35PVf1795zJ76RI1DWSFQ4HJ4aBe1q2EJ9ZJgs21ug++Lch8+jE2LxufPXLTlzvn9MYy54Iz4ux+dooP87Lfc+9D28JJmTDvcly0yJMXjoGPhQO6JFxyap7NtZ0xKfGU/DeR//ure+5r+tngrVjkyVIG3mII4qYmR6q44/9vRiyQgTDO4h25kFiDUzFeVzZz8tc1VcP40qudaWmNWu3ic1zRZwdw8aqi3imksvExefcabNfwStumOXni+idTXCV18nPKWlGXdEbAE6P5Qp54wywI9kexYtwxOmTBM3f/U6FY6j6UUPas2Dj9jeHfWpS4V/3Bi3o+K2b9M9ZJQZ2U/ZuVu8eu/96cJN+v61X66U74750ueFr6Z6wJSS7fm4WKwyE/fK/siMLJ13lHhlEBmxhrjmtjtku9/qpuyShcGiJiuzQ8f+F7pLHDwO9/aKCNg70t2tPpGma8pEMAh/zfJP2j4eyINClObff3y7WPiN64QXM0DsNUXD7IWil4qOjuw4YoYoil5UFBkomzhOVM89LCFKOb5nuLrOTBRopFPWhNKuOqCkagg6iOH43t4+0dvTLdrb2kQ7unqc9igbO1rUzHeeh0kXp/W968yIyvIY2Q3yq4SyPx8E+UPogvehP9oN0ndh2qUVsx4dSPCmjnbx+5CdHawJSNartvpxa7dlRiKLxEpFkwmX/IpGKubktm7ZIjvORJTIbm9vE48GMQdUIMqWmXBbuxQs8ilVw6KFwmOZWLzyz08VSLKdk2HLTN0HjnD2VSSurovmYsiPzkyhUslKmWKdLDHTbc1MH8ZRTipU1J3ShaHlzXDnwIZU1sxwtPvlXd+/cbHxrqANtMs277zh1mORSHOEJr7bzAwwg9PGfeaSO8umTDqVDoWmwEFHI01vQstxLJU+p8xY31XiYRr0rKoj33981XFHX4KZnthUgfKVQxNLK1r6Nm19uv0Pf/kdonkXegt0O7QpJ7BrpRHQCGSAQCqhZzAszcpGXb78KTT7T6ZDvhXGQXqbf7FqLOLlqGVSYU+VkQoMqvHjglHhR55oaGtDv8RhfNkpI56q6dPHlX/khPcKJgeWhESDoSdbVj6wBE426phDmBa/jbXnnb3P8lxQVo/PO7ti7uwpvW++/QQSZnR/D05ZqcSSnQ6oh0I1PeXln0LaGqzps7a9vA3LznW5YMAaxNDYAThn5s2esDUjZd6qykuGJlkDjpUro6WyZoQLw4pKXX311R9FgmWBZc2Imbtiyc2CBQu+g7TKPJg8Bgdz/X8mGeHYmRzXxaCegOaQKTHy+EuEp4QaUaBWy3SNlJs0lJeXz4A/SRFrRqzUSRuOzABXMqN+8mC1+CurHxacjrCqVU8/JW5a+SvhH90oPFWVsR0CcX6s/gdjt2bEdTgcA45g2dUFxy2Ui/yTfchJJDWRdOQnl4qSiVhal5uJI3PpQ7K0JLjLgWws1+IiNO5UcKu4Wu5DEybHluWpYVy3H7vwlxk7Ydw4tK9ZqAkfF+HbvHCm7LMf/khsmiHLmXGdEcpEuKtbcJXeYJRcBcgFeABlMErKqAUM9xlBxBd88LjBxG1+y1kzTjoxMW6USrQ0OZtAEPAtp0OUcp0RTpVxj0u21PITFjlSxTHRTDCn7rh0khpzN0wP52+UcpURBu4FW2VTySlATsshbFMbSANqI+Gcc8RmIK5TxJ6dUEubCO3ZJ4K73hO+shK5ylKlyVXxS1L+Y5CyoSI0E40MhJFAfylWd8DOBnlEzj0yE0AddVS0HxnFjqgINh81nni8XHyswqEZZCVsKFcZIULxlZ0KIJXJRFOpxKspPjUXGcGeowjqlWgoAOQtk6aYz689an6qoBPeuctIwmfODirBymTCSc0wNCdQ+4Fub1+v6MS8JNfKhrH6IoJJ1fpjjxJ+rLIYjHKXEYdmRTK0mXA1odqLGeQeCCQTLecpW9vE+o5W8Ww4NrM85pyzBpN227euM6ISLlEGy9jQBq8GIZS9KE2IdjvaX+1tmAlu7xBPdreKnYLj5blVjhlRiZZRG3y+8g+/F0sXfdicZ+f0NffWdQLtViDdgRnhrdCPp5i+zmVWbBmRGTASLiIsSYg80AS73PrQg2LBlOmiHYnGkIxM+LNdrWJzHtB2A4A9I8EQhBMJl5UP7CwCWdZDSKM+j7jqhWdF1N5SdxNHXvzYMhJuaZW1JteNVMycLipnvM+WiFhhanMqmAdbRlgMFqty1UQphszpjBQalTRFNEVyhIBmrRwBm2mwZs/KSpHcN1EzTWYa/x0dHXLLEL1ZM5LdTnmaRGTj9R133HE9wpFDKdaMcL94Uamuri7OcyZkpOPArx+6rGhyEpX7Ufao9FopEuzeuOV59aLQze3f/sHxSKO5tteaEbbSd2E50YmFnold37vxXKRxA7RZQFkzwvSzOHsNmTmND4WokIll4UD4BaTNVjg5zbMzM++1P/e3xypmz5zjq62ZVhAZgkyAnc6IhqPMBAsmWz8vVceVna7R0LOgp4+64OOXlUwYexzWpHA3Wz5UKNTa/k7rA4/eGu7r244IN0Lvgg44RZ4qI8o/qcbDt7iqjrtG3XwDb1lR5A6uh+FAmLlrLish60A0AhqBYkYgm+UQq1ilWd7RrsJXZjFjZU07azKl2cZg81VpWy1n/citfaBg8TsCX9Z4yYU3Yz/slW4jHO7+MKfUG9nadEzLn17YgryyQpT9jUzynQlRFCEqsZJtJyKpySSikeo32tnx6ZYHH7sP+WczyxWB3BCFfvyV06aNrjj1xN0jFdxB5zscfunAPfefjnDYjExJnHREYRFVpSVj0CQxAwhsfndh519f4sAWJcex/klFFPa2RoEg5vCFGbK2DAqBaG/fAy33PfwZBOIoNZQEJ6UJ4oRKltywIveI8ulTon0bNv0DQSb0iNlsjVd0q268+AJuRtMqRwh4Gxu+gaDHQJfER+FEFEpJg6esbEG8Z/2cXQRuv/327yFEjl3Z6GB7MKIk5YakuctVP1JjlQ8XhknNhTNWrdxpGv6NdBedMXbs2LORaG5asNXtlIp4RUIliFS8p8E+y2VXCITAywNjcNSJOiyGK5ciWM2E4+NjK5pUGwVJ93hRDeKqAS92SshDnMpwkFNZGXZQICt+n9xswLTlYgfFYPMc/73P56uFG+v1tESJ/zZrz5IQ5G5yPlZcRbDkmCezXrJ4sbjm4ksHFc9Nq1aKex9/HGc4VQlvdRUIBWLxdBV0sYuBQNbMO0mK9X1W7GaRRAnA9hovFo6/ct/qrIJFoirCMr5jL1oqwtim48XRaFKieKGHw7rarGQwy4HklCgmMbDulqc0f/4T56Q9qTkb+SP4r97/oAzqrsceFXf89lGcWVcbK+aKgDhOFX02cIlVwtxSgeW4J049RO4aSnd0dlYijguEcXLH0glYGsy0cKuHLEbj/BXSY04kRUoIpCN0oFX8E4AUQrFx81eulcQ4mgci8gR4Ng5yXJylIz5X8juprEtKjCABeQzmayvuzXnGnTKVzI1EYJp4RCcbGulASxYO3WU+VRNemdbmOgFXmnts0biJHUuIFiXXyaNlad3+Y40rq5IiE4rIwtin8do9q6zxFJSdaTv6yiuErxEbtNGUjpcYR2IBeJtSz9IZP/wnUWjhzgppkhhwiZAIJFKsz+Xhe7QMDxxwPjwhq0QB+8gdbl+5cJkt/YX0oAD/8gVLxS1P/k74cMUaTtok6x9MprJLJ/zwPxrrrDoCTkng4ZxSGti3Us8hNNFrROW0KaJ0wriD4Rs2LINMcKNDVokiOQUbhS4+jecG5F8pwFXM6pmm0nzHsvzCRSeLmx+6X0SxbV/4vPJ9IuAG0OxXAXS5LUcVQzB9FRWifPpUUT55gooyI1OlL/6jrBJFclsgYdAzPs4BPcdnQD0rsNWzrDwNIvAYZz7zGjjunuR1ItzTRzOAPlO4FZyK4kUqFj1wVxzvwd5VTOyJ8qmT4/rbA0p+Rh9llyiM2jZg4C4tClDlWz1bTdpNTQDxzN2eBF0Bro7PZQXaj4q8vx+3pWDXpzQhwQFo7lNsR8twbbBXjD71pFjRpSIuEDO7RGETs4SL9Q4qBaxyUc9Wk3ZTWwCnm9wfDA7mLYo8BpgcTt0PYHlFDUGmGdP9olMC3i3exgboYDoGYV1SgGpQRFHAmvlibxnXTrGI4MZtE2gFugG4KlYU4GGU1+TuQKDfBDwg9zrHwO7DnucAwO6GXtffI9ZFcUYza99UKh1BUn07xO9SEiUBdCYWANuUeoZJHDgI+KEvfk788YabYneEEnDJ5QZ3A1gWI7yEqRfb/Fm0SK5HcbOuv1usiwSw6jwuDluEw/8hKVFks475J+gSo5hpa4uzvQ3uR1vQmPNAWY+OEU+s+OatPxZnzD8G4KMsB+AbwOFvRnDf6ggH3A1LJScKd2Kz+Qcdm2QC4OGDrRPpbrTNS0ePFlUzptqOUHgLsb+1d5ubNGg/cQgkJUpofzN2mveLkrpaUTEdnZ/RvJ9Jq3wgkJQoDR/SU/T5IIBTHIXZJnRK6Qhy00QpQGJromiiFCACBZgkLSmaKAWIQAEmSUtKkRCFgypyYKUA0zuskoRB2L1OGXKSFAxmidglbk5faLesIbBt27ZfIzDui7QJgRNR6Kmjr2n7PTC1yiECK1eu5F7IhGtQnIjC+dzWfb+87xaMEGuJyRFR9v9y1fkImqcVcTdXWkmhB1Jv+/Zv37AI9wKYh+rATassIACCfLK3aSf3PXKNEYXAppJtryNhuFGys+OvLz7qq6rqK500ITtnpNuiH3kPOE/p9FC7PGGNe0kHdFoOJxPLoMdCz5r01S/8xFdXexjsWmWIwHu3/ezS4IG2tfhsOzQXfGGyylm5nclm3cMdR9yjN73isJnHjFl+wY3OQWpXhUCks2vrzh/95Kt43gq9C5pXgbG4stUheLYpt0RRH5E43OVVDU0CcRXauNHnLf5E5bz3LYV9RKtwZ1dT86rVP+rfs78JQLASZz+Ep5KxMmdXIyUx8F6qTImivqNJAlGzeKMUkVDcK8lTzfjMtUacRKOf4aYILosfdh/YQu02dKdh9sGkRLgmBPyaajBEMQOxWBie0nTOdviWqArCSuJYdUEkSidCI6AR0AhoBDQCGgGNgEYgGQLZap4yHNVHoamOsbA2hZOlodjcVWePJvsc7JvQVBrWgavBEESBzY5gaeMlF1znLSu7Duu+2UEcWSocfi7U0n5d+2NPcak0O44DJs5ACUIpKGn8yIkzvYdMWzMiiZCE5XCgz10t9z74Fbxmb57SoyQqyRd250wJQv/++vr6Kt95Z2+FvegunbZnP3dP0Z6ea1vu/83/IgYOvycd8Y1PQSYEoVSUNl645CJPTe3d8QHpZ0cEOg/cvWoy3nBC0JW0uCUIiVHeeOmyB3Gu4VmOUWvHpAj0/elvE7q3bVOzhymLMDcEITEqRl2+/A84+WBh0lj1i5QI9D77wsSepqZmeEo5R0KwUym+L2v85Pm3aWKkgin9O+PgbE5VJJtSl4GkIgilp6TmpIXzPeXln0ofpfaRDgGc17wNfngoZ1KiJH2Bj9i/qK059aR3YGqVHQTKymdM6+5bv/EVBOfY8komIbGi6qLzf5KddOhQFALe+rr/hl0dyqmcTTMVQWo8FeWFe5yQmYXiszQsO5eLRjgNnoB/ggM8se4oazjnrKtgapUDBLxVlZcgWK5HSMA/wcHwVGEc152D5OggiUDV8cfOh8EVPTblRBBW9KSeVjlEoGzmtP9C8AnFVjxBZFO39uSFJ+QwLTpoIGCc/V8Oq40Gtgf6gy7xjRnzMZha5R4BTlXYaGB7wEtJEE9lhV50nXtiMAYWWba+IDt/8cqPg/h552pele2oKZ5uRKXM2FPsV533q0y4xp9oavVe4Hau9LQJRTxBKCFenHDGjktelCQEgJcmj5HCyaJRHOUq5JGuPDaQk28x5fEg7Txtzo/D2Hh7Aw7MlM8kDnQREobSQcxNFU8QvrB5MH1m2WISggQIYdaTZ3jxcGUcnBblkVM4VE0eLUUiGcpDYuAANl6Z4SktkefKe3EzQ5RXahgnmhYZYZAhO95OBFH5z4lpIwQOUYvg9Loobm+I4GDM4z/wAfHlS68Qc6ZMSRv3Ozt2iFtWrhB//9e/hLeiXHh4M0M5zBI07Sk5xSkx2T0rOB2KJIY8BQ8SEMFZjRHcZ1IaDIuHb/+JmDyaux3cKxLtjm98S36ws3m/OP/qq0SgpFt4eadJORovkCAWZ8VWjOVFQqRUALrY5TK4RqMDpzZ2dIoXVv5aVOMA5MEqEvMf968Wnb09YtGlF4tIbY3w1aJvW4ZGDC+agSoWwrAMy6kyicHiCUVTeP8Bce3Si8TrD/0mK8SwJr6molKGy/AZD+PjNRlUKh1W/4Voz6mEKBAICsHhFRov3nOvqEJZn0t10ekfFUtOXCROuCJ2PQYG82TdwvQUuqTkXkLYepLEaBFvPPBQzomhCM2ikPGFDrQYksKp7MJXOSMIuZF1BivvUEsbwHl4SNBgvIyf6ZB1GNJVyConBJHE4EnZ6FdEcA/W67iQbCgV42c65CUyTFcBEyUnBJHgo2OHXapi1Xe/P+TlNusNpoPp4Z2NQ6Uko7LkMLRTOrJOECUd7OjNnTBRzJ023SnevLsxHUwP0yVP/s6xlCjQraabTGedIDJStqpwkSW5spAU08N04XaBrCfLCjztUtFMpR1SkVWCyEShjOYp259e8nGH6Ibe6VOLl8j0DUZK4sFPSwCOx7Hu4pHvxrHvOPTHEYysEkTGgDI6glsVvnjuBY4RDrXjVeddKNOXSV0STwCZh3jOJ+h0U5cfyEFTtDKJh3H5gRw0xbUfUTAs7v5whCKrHUPJdUjAvOkzHCMrFEem763W/RjGxyixMbSi0mZyu3JQJsG2KvVsmHKMjiUUt4NIiTBMYzpBNrnpjmc5nF7KqZBElXUJYdPy9uv+IzGmAnJh+phOqqxxP+ol2azuxaApSojYZdBdGLfrkFcYRnCNIZvePgx4Vs6cLuqPmueISNYkRHIWOIBzGhxTKkSluL8ao8FhFBueakyEcZg+PrFx3E+ml9Jvcj8+4CQa8hvjfNYN4H6UDnxWF5lFPdjfN2miqDhkmsB2v/hYHJ+zRhAZOhJY6UtYauQYcT4cFQFUXOqZZqXXLwIETxVZAJ0FjvxPeldi7I4WBbgkAIsho6L2YcyscuYhomzieBVlxmZ2CYIMLj7ppIwTka0PFOAMT9mtJu1Kn3nCCeK3r2HNs88fc7NxPytoo0XEm0HJ/cib9Ro/hlOOSyrJ/SREtlRWCUKxXjjPuWzMVoJVOAro+GcFuHqf7B7Fow49VDzy979hDguTWBQMSgtBl8AftCvu9+JCtcppuLhy6iQVZU7M7BIESZwzZVpOEqoAZuDKbjVpVxoWFO8o3+HXvMQSQIfQ/JQXoGEOv76sQvbaSQS5sALlv6wT4IeMVTZ+DG4rwvVQtXlb7yFxyypBiEAD7pwdrFJAq3DUswk4Xii7rGwNYiS71NK8Y5G3z6Ey581z3T2Yx8espeACCdzxyKuiKqZOwbRvQhWvkpEXM7sEGWBeFOAqxwpsPiu7Mp24n9IgL7cEd4fA/UHLBZd9kggHL7jkFYBbcBvd2lCfGHPmaSrKgjGzShCOqrag3T2uAZfYJ1FO4NOrclfAmyaLHkgAuZ+muvDSesMor3TlxZe80pVXAPahL8C7GOnejue1gV7xNu5fDFsZxmpPktahcM4uQVBBbty1w0YQgmhVCmi6Kbsy4RADnQRA2W69U5dlf+zGUVyACbB5u6j9etdYcdTU3yvWhvtwIiVaRlZVoASwJpH2rBIkipWFL765VpzwvvfLeBQxrKYCX5qK68n5sNu5nzdI26977cGsn7pfN3bdawDc3yXW4X7dQJEAHk+A+OdBEUQBbQaKBWpPvPQ3cd2Fy1NyP8E3Wz/kfGgWQSzfCTQ1i5+YBPD6V1543C92gvvfRNm/PX6/5DAhBnHMiCAJBGAIcUVSL5uXANds/cCLAp/u6rJjVr6scOUN02bZz3I/VgH3ovxfF+Ddu0GcS2Ev9hjtcFVJCeIIPlGII4B8lnjhB0PPHD1tbm0VlRjNVBfYkxDWlg+5vdcofiRRIAHvgTjk/ncTz64frtg75suRICYxnMCXRDF+QAMpCcawQzSMShnF0TW33iy+e/mnYhIAoHnzNIHvNySBFyG/Te4PoxU0grjfkQJxjo4EMaVAEYQm/50G3SAV1mEHTsisx6rBdzdviRU/IEYzpGFtqF9sRPGTOLQal6IR/picICCCqgdis2AskoxBN9QTnIKUhDBGOjkEwcE3TlGWjh0tbtm8TgSwKt2mhlHla8tXFh8cCaLmfeWYvzEVyU00vIddjvcA+BgBwhh28IuKaRh2gJabZ4zEOU9QZjHlwzQoR4JEUMxwzjfCWTASQXJ/bCS0dFSjqDhsFs73S94bH6ZY5SVbjgSJovLlelxWHOWTMeOFUU/uWtIq9wg4olz/wSNzH7OOwRGBrC9ycIxFO7pGQBPENVT58agJkh+cXceiCeIaqvx41ATJD86uY9EEcQ1VfjxqguQHZ9exaIK4hio/HjVB8oOz61g0QVxDlR+PmiD5wdl1LJogrqHKj0dNkPzg7DoWTRDXUOXHoyZIfnB2HYsjQTD1nf2N3K6TNLI9OhIExym1jGxY8pZ7rByxr4NyIkgEG/+35S1JIzsirggnUUwVTxC+DAf27H/R9KEtuUSAVUNaggRbfvvk47lMhQ6bZIjy4kmulsKeuoPKSUKCoa6ujoNetC0XCPRt33E/wu2Dtm1kcSQIPHXjNILNuUiIDjOGwL5f3rcCtl7olAShb6yME50HHnjkej5olQMEYsVVO0JOKyGMnRTr7m3a2YTqhsTRKssIHLjv4c8iyDZo1iEpK3VGTYKQcgf2r1h1GR20yh4CWKTe1b1xywaEyHo6geHj6xAVMz22QUo2Rrq7NytHbQ4egd033LQcoeyDjq3VjQsyGUEoJfxg784f3v6FuG/04wAR6Hrl9VvC/eGd+LwVOqEPwmCTEYTlGj/ghzt2fe/Gc2FqNQgEgs0HXm158plHEMR70GR2W+tKBW27bkc5GiaJwk5LCFvVIj1vrv97zYKjz4nzox9dIBBu79iw+9afXwOvW6E5Tph08Dbdnia+5wr5OuipvlLfrEnfuO4B2LVyiUD/jl3P7v3FvTfA+xbovdAJTV1rUOkIQr9WokzC8yGTr73qx96a6kOsAWl7IgL773/out4NW9bgzTZoHPKY2BGEm025IQg/UEThhZPjoKfg1LTZ4z57+S1447jHhB+NVBXY9d7ze+781W3I/w7oXdAspjh25VhvwN1UbgnCD+iXjQDewML9bCTMBJwrNW30xUuv9dVUT8PziFY9a99a3fzI478FCCyaWHlTKnC+uawz0hID/iTINDNRJAqlogq6HnqUoet85eV11YuOP7lk4vgP+KoqJnhKS3n61/CToHC4G/sv28PNrev7Nr+7pvv1N99CPtnRoyQcMEwcxiWlgg0jNpBcqUwkxBqgkhaCzb3PJA5PLqNJXQbN0zATroWD23BQ5HZ2njn0wQFCnF8uSABKA59V8eRKKuDfVAMliBkALJQYJTUkAk8IJqFIDLoPR0WOV0RhE1ZpSgPdXUsE/NpUNghiDZDhWbX13XCzK9BpKj3c8qjzoxHQCGgENAIaAY2ARkAjoBHQCGgENAIaAY2AiUC2h1HMgLNkUUMyDM6aVqs9S1HpYPKIgBqCYpTKXrBDUYXAbEoQlKkGk311U6eW+hbMP0aUlM3Fec2zcOPZLFz3MQXAVuNuL05mcuTf+To6vNCqoBDgzEU3NgFwxqILB9/uwA0Ym3DQ7SYR7H87/PIba9q3b1ebAziArgbRlfAoYcp7pvItJEoQlMlZFH/9yceN8U2cvFSUly4VHq8+AjLvbFCAEUYjr4u+wOrw7p2r2577x36kkFOEaj42r4KTDyFRAqFqiJK6hQvH+w+d+k1cCsXFr7omKEAeLcAkBXDZyf2hzdu/2/7SS3uQPk7dxtc4OUl2roRECQZNzruX1H30lNn+iePvwjHlR+UkJzrQkYVAJPJaaPeeK9uf+fNGZJwCw5omJzVMtoVECYdsRtXW1lb4P37GD7B068qRRUGd23wiEA0E7gr97unrOzo6uDorvlk26KRkS0iswlFafvjho6sWzL8P9zQvHHQKdQAaAbcIhMMvdb/8xkV969c34xM1CKBqF7ehJPgbrJBYhaOkurq6qvScs+7xlJacmRCTdtAI5AmBaCD4VODRJy/v6uriGmA2xawd/oxTMRgh4bfsjHPNb0XDuWde6G1o/FnGKdAfaARyhECkteXfWn/z1IMIns0w1dHPeCh5oEJC4WC/o6yqqqq67IIlv8c8xnw8a6URKCgEMA/zRv9Dj32su7ub8zPcTaI2MrhOZ6ZCQv/UrD3Kq444Ylr5gg88Dyfu59VKI1CgCETb+17+16LudeuakEDul2at4rqvkomQ0C9rEA7pVtYePW92yfx5L8BOgdFKI1DoCASDb6w9seOfazlkzGM3OAqmZvVTpp1M71ZRSKSAVM49dHrp/HnP4VkLiFv0tL+hRqCEPEveRUIqocnLrioJt0KiahDumq4t/+Ax96Kuol0rjUDRIECeJe8iwTxygfxLQUkrA+x8p1OUNtlJh1lTf97Z13orKxen+0i/1wgUIgIer3ds2Yypnr71G19F+qwTj0mTm1aK8KVZi5RWVzf46+s/lzQ0/UIjUAQIkIfHjx/Pk5dc1SbphER11tn3qKg85YRluplVBFygk5gSAfLwVVddtYw8DU3ephwk7Z9kIiTlOBXwFASmlUag6BGYMGECeZk1SVohYccllVL9EQZU6ikpmZHK83B9F42i7Mmy8niSFlxZjkkH54RAZWUleZnbNMjb7HOzf+Ko3AjJQUHx+XhI47BUCYJgFQzY5XvlFqHQQMv/5ALkYQ0uZQE/XmnBM1yho1YhsdoRshag3LOY3+8nLysBIXEMAiXGnU5I+AU/9hqagQ4LZRMKg/mjEcwt0Q5T2ikMYdrDxjPe41m+N/xJMPhdvPISMiiYkun57IPms9QovOQzhIbvqClAMGXaLIKjhSYGZTZ/gSl5GaCn7o8wTrdCQr9JJY0vC13FC4V8phBQACTjwwyFRDRIE6sWgrDzOYylPqGwqCgrE4fNmiVmHzJDzJg8WUwcM1aMbWwU9dU1oqayApssS0SJzyeC8B/E9509vaKtq1Psa2kRu/btFVt37RIbt74rNmzaJHr7sYTI7xNY7yY8fpCgxA+zRHhKjGcv31FwIEisgSgwWmhywWKKp5XpGIcbIXH8sBgcrYJhqyXI+BAGnHUNMyiwaUdEArBDz5t7uFhy6mniowuOEzUVnJjNTFFQqCvLysW4hgYxZ8rUlAF09vaIZ17+h3js2T+KtW+vRyu5RHihsVENwgM7dJTCgzBVbSNNI1Rdy6SENysvh52QWAWDTScpHGwyQTBwi7MUiGhfv4j0B0QVGHDZ4iXikrPOFvVVPHwl/4qCeP7Jp0itYm/DgtV7n3xCPPD4Y6IbafaWlQpPeZkUHAyeoJkWa6rJppn6CKYWGAsYWbQOGyGxCofqT8hmE5pMETRvon2oLXr7xBEzZ4pvfv6LaUv4LGKccVAU2KsvXCY1P35nx3bx3Tt+KtZt2SK8FeUQmFIITpmIoqnGZhqbZGZfBv61sGQMecoPil5ITOFgrcHOtKwx2LcISqGI9PWJSQ2N4sZvf0vMnT49JRiF+pJNtlXfv0Em7+1t28R1P7pB7GpuEd7y8pjQsHZBv4Y1DAUEKEilhcUAYpBGUQuJEpBYk4rNKQgHmlEUjEhPj1j2sbPE1y69fFiVrBT0J39yhywQblh5j3jg908KrKWTAuNBs8wUFmOUTAvKICUEnxelkNiEgzUI+xoUDowoUTi+/tl/Exeecurg0SngEMj81192hdQP/vlZ8f07fxYTFoy0xYQFtQtHxDi0DKWFZeDEjCE48O/z/qVNQNi0Qj8j0tklwq1t4kJ0gN944OFhLyDxoLNAkPlG/okD8SAusulpzOEo3OK/1c/pESgqISGh2bSScxcYro1094pwR6eYUF4p/nb3r8T1aFqNZMX8EwfiQVyID4e15cgecWOfTauMESgaIVECImfA2bTq7hbh9nZx7UWXiCdu+6moQidWK5wgDhyIB3EhPsSJTdHYyoHhKSiSN1iAZqjd8ktR9ElsAsKJP/Q9ot094oEf/LCgh3LdEiEX/i467XRx9GGHieXX/4fwYGWBl30VTFDKugT9lGLpo5D2GSmX/iNGM9RN2AVfkzgJSAWI/vwvVmgBSUNhDh3/9Re/FMRLFiwoYAqtRklX+tuySAFIpcn41vdy2RG+UablXSbCV9BCIjPCjLE9zRGs3l5RisnBJ269XVRXcL+MVukQ4Iw+8SJuxI84Ek8yUyaMki4ep/fpBMAWv4WBbYyu3K0CIJkeeaAbNdfeqVUVWGcX4QSy1Oi3Yh2d1MEAVluAh8hHmCoIsMBwqQq2uaUAlCYJjFnzMJpZv735tiFbQuIS04Lzxhn8h354k1j8lS9hvhETjpihjxpNLuI7kKaXoo+rzJLRUynre9OrYVFGFIIAO0Q7FhIFxbTTiQJDk56MvpcpYLFv5C/yzWHxXhQYblXBConMLksJlgiQfi4p+f9Xfk5MHj3Gbd60PwsCxI34fW/F3XIFsheMIpe1kGniVGEIABMFtpaMHycAFBAKDUyZVvBJVNUuhmDICWbalV8G50FfDKurfTU1orOzky6uVEEKiUkkKSSYC8HozIL3HSHOW3Syq0xpT84IEL8/YsXxK5veAb9gkSQnG7mMBczkWJuQyVIp63vTq2mJFeqONQADJQPTdCEAjIdNKprQsbV5xjObWRaB4WLQkrpaUdJQjyvU6oS/tiaWT0ZlUcOjuUUBgWbbMtofFF9ZdpEli9rqhIBZuDi9hBvff3npcrH8m98QkdIQtqv4sEMyLBdHJnxChrQq+Whxk/xKRuW/4S6ZmB/hGa9iJt/RE+kJw8LQdIstKZIv+NIuAJYagmnntgG/FIA6UUIBqMPpumrHJ6PLQIUxEe1WFWRNYiaeVSWE5Kg5c8TsyVNM55FocSMACpd4v+qZ5swJE8WR2Dz2rx1NaHaB/NzcRZw9ZGZDkafJzIaTKQT0JxmeBuzms7MAyOaQUdglFQApKEoAaiTjl9TXylpA7qFRaRpCs3CFxAA3itGK0447fgghyn3UiomTxWR9b7XTv3pOZkrmJEMbfmlbdOTR4vXNm2K7IunOXZLSS8xfrB0PO7+TJT8M2SxiSa/cYOc71QxiqS8FhwJDAYvVCvTvQfgltWB81AL+BtYC9dKNaSoGVbhCAvQikkARlHxzigFLxzQq5nV8CUfre6ud/tVzMlMyYpwA0K+aKJOm8Uw7mzZh6FmoTdjPC4N5vdi+LILon5CpGRYZHIx90B5jetsz/dIf/aNv46+pBuOz9K+XfQEPl+0PI1XYuQENSIjJYwpzREsyTgpmiH9vfVb2ZCbzbX0XgyLmRncnAYiAucNg+ghKdxYwIYwKUijCaLKyDR7iSCHMKFZKc8WCXNPF/fXswJPhDcY3awuMBlEA/KMa0RlGH6CxXm4tTpHlYfmqsIXEgLwSu/CGQikmdYo7/p31WdmTmU4CwDhkae9SAMjsIWoKAkypIQQhTJRRGELhELbvQzikgBhutMtn+Meem1IIQOnoRjB/g6wBvNgirFUiAgUtJCzhOOnVg4nEbAuKYuBESFiostw+qKzPyq5M+qLdfLbYpbsRzEAEgAxNhlcCEHumcFAAglIgwrBLobAIQAD2Zuh9kYDYi9phP85d4zVPVjXu/CXWR21PgUDhCgkERJ1HtbN5v5g9aXKKbNhfmQxrd5ZP8e+sz8quTH5Au/lsCI9yU6LkSgDQFIrIppBR6rMWACNLIYBpFQDlzlpCvjf8Sj+wt8D/HgoA7Ptxu1mHGoZyyK92GjwCBS0k8oADdC7f2LTRFBKTYR3yHv/O+qzsyuTntJvPGQgAv2Fzx+wDsKMLAbC2/1n6x5o7aA5JYYjVAAcFwBAMoyagnzD6Ei2hAGqAIIQgJPajX9GmBcCB0vl1KighUQwrmZc4sEPp84tnXn1ZnB8326780puTXblJM04A5Df4UTUA/XC0Rj1nJAAQhhCGqa3NHjaFYoJhbS6FRRsEYm+YQhAW+6Ih0QoBULUR06RVYSKQNyFRTOsGBoiGVDwv1+P3yjF9Hqtz6MRJMXcL00NCTDcVB10UwysBoCndONrDpQz4I3NbawC+tzG8bO7YBUA1j9hBlrUFV5kivA6sMt2DGmCvrAHQJEL4GCTVahggkBUhUczpCg+DqZP6Ve9pypoEY/k4W+qWh1aLW75wtSx5nQRACoFsAnH4MyYAkAA5AsSagQxtFQCW9LI5ZOn4KgFQzSMeV0oB6IK5N6yaQGFxAOGGlSQnzYh+MVwQyEhI0gqDYvBk6MS/l5VArCaQn8BqXQ7BWoLNoCjW57y64W2x+k/Pio998FjJ8HTnEGi8AEhhMGoAjgIpxreaqhagWw+bQBQC1AL7o+gIU7DSCUC698nyr92LEoGMhCTGyBamtmY5QwEwW+Po9EI0YiEpO006UUDAtDy4WoSj4pb77hUTKqvEKOyPCLImAHOrtr/djI0c9aHtvxcdYQrAPoTVDCEIpGPwdO+tedb2EYFAZkJCQVDCIPla/pg8rmoB1wKg1gMxTDBxsuUQrC1QfciT3r9+283iS584F6sh/GKf0QzaK2uAsOhPx+Dp3o8IkutMZopARkIij/IxhEOu3WFsUnBoxphc1gAs/Y1n2USjHTWBtEthoF/6QWDUaPfTlGHyW/RF/NVYD4Q9ASVYEOeHybNvlVoZxNQYdqHalBYAGxz6IXsIZCYkaOvL0l4xumRuMDUZnk0kupPp5bNhtwkABAHLTf1oMvlHYSkE1gNREHgItFYagUJFIDMhwXofed4uh05VE8giIGxm+XEurd/YD8Al0b6qzO/4KFSwdLpGJgIZCQkhKsF2SH81agLUAj6YWmkEhjsCGQlJ3fx5wx0PnT+NQAICiUdlJHjRDhqBkY2AFpKRTX+dexcIaCFxAZL2MrIR0EIysumvc+8CAS0kLkDSXkY2AlpIRjb9de5dIKCFxAVI2svIRkALycimv869CwS0kLgASXsZ2QhoIRnZ9Ne5d4GAFhIXIGkvIxsBLSQjm/469y4Q0ELiAiTtZWQjoIVkZNNf594FAlpIXICkvYxsBDITkki0Y2TDpXM/XBDA2W2uedmNkGDTeuyAn2gw0DJcQNL5GNkI4GJR8jIOYogdXZIKjXRCYgoIAgmHWtv/mSow/U4jUCwItLW1rUFacU5VekFJJyTMM6UNp8OJQN+7256DqZVGoOgR2Lx583PIRACavE0eT6rSCQlrEkobT7nqb33mz2vCnV1vJA1Nv9AIFAEC5OFnnnmGraJ+aPI2eZy87qjcCAmljAH1Qnd3/PWl2xxD0o4agSJBwODhbiSXPE3eVn0Txxzg2lXXimckegO73+stmzwhgssmj3b9pfaoESgQBPo2bbmz9ek//QHJYcedt+SxNklZk7gRkvhqyNO99u13K+YcOs5XUz0LEWilESgKBAK79zy1d8V9/4vENkO3Q7MmSdsncSMkCEcqNdIlhabrn2+srZw7ZyIOqJupPGhTI1CoCAT37v/jnp+t+CHStx+6FboHmh33lJ12vBeZCAn9M0Clo12vvv56ydhRgZKxY3TTi+hoVZAI9Ly1/q5999x/BxK3D9razErZF1GZyURIVLOLAbMNx2oq1PPWO5uDzftfrTxs9inC6y1RAWtTIzDkCITDvc2P/O7f2//y4rNIy17oeAEhL6dVA7mwgN9QuCgQPA27HnoU9JjxV156denkiR+FXSuNwJAiENi5+5k9d628HYlg8+oAdBs0m1hph3zhx6YGIiQMQI50weRZwrw4pAa6AXq0r7pi/PjPXvEtX13t4XjWSiOQVwTC7R3r99y54jvhrt49iJgddPY/OqE5iqU66apVBKf0aqBCokLmPAs1a5UK6FpoCssoX1XFmLFXfPKakjGjdX8FgGiVWwSC+5v/uW/Fr28Kd/eqmoPCwUWM1rkQV82r+JQOVkgYHsOgZhOsFJrCwpqFzbBG6IaGM079cM2xR14hfD6+00ojkB0E0OfofOX1Fa1PP/sXBEihYJ+DzSrWHBQOjl6pOZCMag98Z6psCIkKzCosqmbhBSasXSgwdb5SX33D4jPPqJh72Dkev4/vtNIIZIRANIS64u0Nj7Y+/tTT4UCYAsH5DpqsNayz6IMWDoQnVTaFxBomw2UzjH0WVbtQKFjDUGioqyumTZlU+5FFZ5dNmfwh4fXQn1YaATsCkWigf8fOFzv+9PwTvU07duElZ8kpENSsMZRgWBcrstYYcM2Bb20qF0JijUAJi1VgeEEim10UGqU5SkZdXnn4nKmV8993TOnYsYf56+tmaOEBKiNBQRhCbe3vBvbt29Dzxltreta/sx3Z7oPmiBQ1hUFpNqX4zioYruY88E3GKtdCYk0Q41JCw/6LqmVYg1BwOEpG4VF2PvMdNf1S8ztqCp0KL595QLRaDRABVbrTVHNt5nwb3Mjw1ByFoqYQUBiUXb3nCBW/U0KRtRoDYTqqoWIwxeBMFBmeWgmAEgia7NuoZ/VeCwlAKUKVTEisgsI5DDlJbZh8pwRCjUypcPIGwVAJSbIMKuFxMq21B7+3pt1qTxa2dh86BKylvbIrZrfWCMrNag5dqnXMGgGNgEZAI6AR0AhoBDQC+UDg/wBJUzozg7qlTgAAAABJRU5ErkJggg==
📡 API Calls Detected
- stats
- POST
- 0x3b3b57de
- logs
- GET
- https://api.blocto.app/networks/evm
- proxy
- https://api.wallet.coinbase.com/rpc/v2/desktop/chrome
- account
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 242730 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 242730 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
