
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
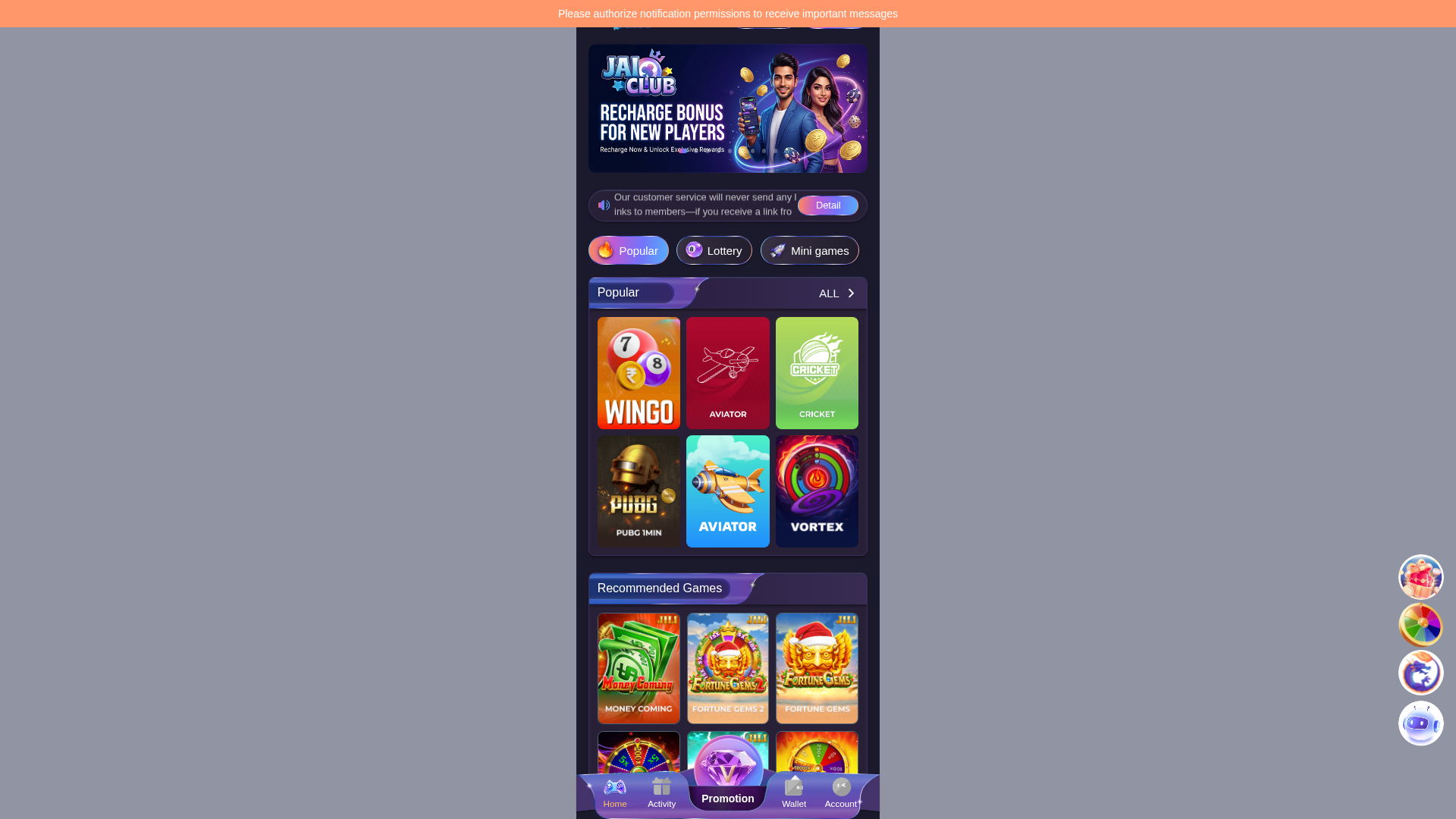
Detection Info
https://www.jaiclub23.com
Detected Brand
Unknown
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
9586e08f-358…
Analyzed
2026-04-08 09:54
Final URL (after redirects)
https://www.jaiclub23.com/#/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T166251AD463B8A2FCF406E3FCDB26B870362A28FE7A41C558C7A81D54E55109E9C5ADC3 |
|
CONTENT
ssdeep
|
3072:eVor2x8jK6OsC2cfXp81krrwXfMhwOwtqdwuIMpK2EQbFArTaQUysE6wlC5qZc:ir6EqjtqNrwlCh |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b36699ecd9896688 |
|
VISUAL
aHash
|
e7e7e7e7e7e7e7e7 |
|
VISUAL
dHash
|
4d4d4d4c4d4d5d4d |
|
VISUAL
wHash
|
e7c3c3c305052727 |
|
VISUAL
colorHash
|
06400400000 |
|
VISUAL
cropResistant
|
4d4d4d4c4d4d5d4d,8b7c70f0f0b3e071,c0884ed0780cf4d4,e92ececd2bceacac,cc5e8cccb0f3f6f4 |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- document.write
- base64_strings
🎯 Kit Endpoints
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAgAAAAIACAYAAAD0eNT6AAAACXBIWXMAAA7DAAAOwwHHb6hkAAAgAElEQVR4nO3debRlVXXv8e+k76SVJkigaARRpBWksQEUQQ0SFZQYUQlNBGMSXxoykvASow4bYgx5ihqbKDYYCCgqmkIBjaCAGEMjQWmkFxAoGmkKCub7Y5/Ssgqpuvess9feZ38/Y9zBGJEz17zk1l2/WnvttUCSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSNBtRuwFJk5WZawEvBnYFtgOeDqwLPGX0r9wP3A1cDVwBXAx8MyLua79bSZI0a5m5cma+PjPPzcxHcuYeycxzMvN1mbly7e9HkiQ9icxcNTP/KjNvn8Wk/5vcnpnHZeYqtb8/SZK0mMx8bWbeWHDiX9wNmXlw7e9TkiQBmblmZn50ghP/4k7NzHVqf9+SJA1WZm6ZmT9pcfJf6KrM3Lz29y9J0uBk5i6ZeVuFyX+hn2XmTrX/O0iaHV8DlHooM7cFzqd5na+mu4DnR8T/Vu5D0gwZAKSeycyNge8Cm9XuZeQGYM+IuLV2I5KW3XK1G5C07LJ5Fe+LdGfyh6aXr2bmqrUbkbTsDABSv3wQ2K12E09gJ+CjtZuQJGnqZOafVNzwt6z+uPZ/J0nLxj0AUg9k5vOAc4EVa/eyFAuAl0TEebUbkfTkDABSx2XmZsD3gfVr97KM7gZ2jYjrajci6TdzD4DUYdlsrDud/kz+0LyaeEZmrl67EUm/mQFA6qjMDOCTwC61e5mFHYCTR9+DpA4yAEjd9ZfAobWbGMOrgL+o3YSkJ2Y6lzooM/cDvg4sX7uXMT0OHBgRX6vdiKRfZwCQOiabS3YuBp5au5dC5gG7RcQ1tRuR9Cs+ApA6JDPXAL7M9Ez+AOsAX8nMNWs3IulXDABSRyyy6W+72r1MwDNwU6DUKQYAqTuOBw6p3cQEHQT8be0mJDVM41IHZOYraC75mfZQnsAhEXF67UakoTMASJVl5jbARcBatXtpyf3AHhHxo9qNSENmAJAqysynABcCz6zdS8t+Ajw3Iu6p3Yg0VNO+3Ch1VmYuB3ye4U3+AFsDX8jMvp9zIPWWAUCq5x3A79RuoqL9gbfXbkIaKh8BSBVk5itpLvkZ+p/BBA6NiFNrNyINzdB/+Uity8xtaZ77ezBO4xfAnhFxee1GpCExAEgtysx1aI753ap2Lx1zPbBrRNxZuxFpKNwDILVktOHtczj5P5E5wCmZuULtRqShMABI7Xkv8NLaTXTYi4F3125CGgofAUgtyMzX0fztX0t3eER8qnYT0rQzAEgTlpk7AhcAq9XupSceBp4fEZfUbkSaZgYAaYIycz3g+8DmtXvpmRtpNgXeUbsRaVq5B0CakNGGtv/AyX82NgXOyMyVajciTSsDgDQ5HwD2rt1Ej+0F/GPtJqRp5SMAaQIy8zDg5Np9TImjIuLjtZuQpo0BQCosM3cGzgdWrd3LlJgPvDAiLqrdiDRNDABSQZm5Ec2mv01q9zJlbgOeExG31G5EmhbuAZAKycwVgVNx8p+EjYDTMnPl2o1I08IAIJXzQeD5tZuYYnsAH63dhDQtDABSAZl5DHB07T4G4I2Z+ebaTUjTwD0A0pgyc0/gPMB31tvxKLBfRHy7diNSnxkApDFk5m8BlwAb1+5lYG6nOSnwptqNSH3lIwBpljJzFeBLOPnXsCFwZmZ6v4I0SwYAafY+BOxWu4kB2wk3BUqzZgCQZiEz3wb8Qe0+xOsz809rNyH1kXsACsvMdYFtgTmLfG0APBVYb/S1PM2GsdVr9Dgw84F9IuJ7pQpm5r7AXGCFUjU1lseAl0fE3FIFM3MPmo2dQz93YD5w3+jrntHXdcAVwI+Ay72xsb8MAGPIzKfSvJu8B7AjsD3wtKpNaXFFz5HPzM1oTvpbv1RNFXE3zabA60oVzMwjgY+VqjfFbga+Nvr6ZkQ8ULkfLSMDwAxk5urAvsABo39ug/8Nu+zDEXFsqWKZuSrwHWCXUjVV1KXAXiUnoMw8CTimVL0BmA+cSxOcvhwRj1XuR0/CyWspMnMd4JXAa2iudh36kmBfnA/sGxGPliiWmQF8Hji0RD1NzBnAwRGRJYqNjnf+BvDCEvUG5laaIPDBiLizdjNakgHgCYz+0B8IHA68BA946ZubaS6Oub1Uwcw8DnhPqXqaqOMi4n2limXmhjSPfX67VM2BeRD4f8C7IuL+2s3oVwwAixg9330z8Caay0fUPw8DL4iI75cqmJn7AV+n2byp7nscODAivlaqYGbuRLOq5LkDs3cr8HbgEz4a6AYDAL/8w/02muXdFSu3o/EcERGfLFUsMzcHLqZ5i0P9MQ/YLSKuKVUwM98AfLpUvQH7LvD7EXF97UaGbtDnAGTm7pl5NvDfwGE4+ffdiYUn/zWAL+Pk30frAF/JzDVLFYyIk4F/LlVvwPYELs3M36/dyNANcgUgM3cE3gm8vHYvKuZcYP+IWFCi2GjT378Dh5Sop2rOBF5ZcFPgCjRnQOxbop74N+CYiJhfu5EhGtQKQGaul5kn0lze4uQ/PW4ADi01+Y8cj5P/NDgI+NtSxUY/Y4fQHIaj8R0O/GdmrlW7kSEaxApAZi4PvBX4e8AftOnyIM273/9TqmBm7g+chZv+psXjwO9GxFdKFczMHYAL8DTPUq4ADoiIW2o3MiRTHwAyczvg48Bza/ei4hJ4XUR8oVjBzG2AizAoTpv7gT0i4kelCmbmoTRnQ0z979GW/BTYOyJurN3IUEztI4DMXD4zj6fZ4OfkP51OKDz5P4XmIBkn/+nzFOCMzFy7VMHRz94JpeqJzYGvj+5TUQumMrmO3uc/GXhB7V40Md8AXlrqfeLMXI5mw9jvlKinzppLc3FQyZ+brwAvK1FPAFwIvCgiHqzdyLSbuhWAzDwYuAwn/2l2LfDawoeJvB0n/yHYH/i7UsUi4nHg9TQ/kypjd+BTozdxNEFT8x94tNHvXcBfMkXfl5bwC5pnuVeUKpiZv0uz9O/PzTAkzVsjpxYrmPkMmr0jxc4dEG+NiA/WbmKaTcUvvNGFPacBL6rdiyYqaS56OaNYQX9xD5VBsvvmA8+NiEtrNzKtev8IYHRU6wU4+Q/BOwtP/uvQPL918h+eNWhOCix2ymNEfIlmFVJlrAx8fnQNtyag1wEgM3cFvgdsW7sXTdxXac5xKGK0eeuzwFalaqp35gCnjB4flvJ3ND+rKuOZwN/UbmJa9XapKjOfT/MHzb+9Tb8f0ywF3luqYGa+D/iLUvXUa++LiONKFRu9TnohzeSl8T0MbOvlQeX1MgBk5j40l7SsUbsXTdz9wO4RcWWpgpn5apo9I738+ddEvC4iTilVLDO3ptlbUuzcgYE7LSJeU7uJadO7X4CjY1rPpHk+pOnmEa5qy0PA8yPiB6UKZuaBwJfo+aPWDnlBRHyndhPTpFc/mJm5J3A6Tv5D8XeFJ/91aXZpO/lrcasCp2fm+qUKjn52/75UPZW71EmN3qwAjDb8nUNzpKem3xk0r/yVvMb1bGCfEvU0tc4H9o2IR0sUGx1m8wXA5esydvS1wHJ6sQKQmXNoXtdy8h+Gq4DDS03+I/+Ik7+W7nnA+0oVG/0MH0Fz253G98e1G5gmnV8ByMw1aZ7Zble7F7ViHrBbRFxTqmBmvh74TKl6GoQjIuKTpYpl5lbAxcA6pWoO1Hxgs4i4vXYj06DTKwCj93PPwMl/KB4Dfq/w5L8T8NFS9TQYH8rM3UoVG/1Mv5bmZ1yztzLNf0cV0OkAALwbT/gbkr+OiLmlimXmhjRvjKxWqqYGYxXgS5m5camCEfENPNSmhENqNzAtOvsIYHSr36l0uEcV9QWad7FLbfpbkebK4BeWqKfB+i6wT0Q8UqLYaFPg54FDS9QbqKR5DHBT7Ub6rpMrAJn528C/4uQ/FJcCRxbe9HciTv4a357AP5cqNvoZ/wOg2HkDAxTAq2o3MQ06FwBGZ7R/BjfLDMXdwKsi4oFSBTPzjcAxpepp8I7JzKNLFYuIh4BXAz8vVXOAXlK7gWnQuQBA84zMv7kNwwLgkIi4rlTBzNwDN/2pvA+O7h8pIiJuoHkMsKBUzYHZc/SXRY2hU/8BM/PZeNrTkPx5RJxbqlhmbkRzxr8nRaq0FYFTM3OTUgVHP/teSDU7awPPqN1E33UmAIzS3EeAlWr3olZ8NiJOLFVstOnvNOBppWpKi9kIOC0ziwXMiPhnoNh5AwOzZ+0G+q4zAYDmhCf/HzoMlwBHFa55Es0pbtIk7U6zQbmkt9D8mdDM7FK7gb7rRADIzA3w0oyhuJ1m09/DpQpm5h8BR5aqJy3FGzLzLaWKjf4svAK4tVTNgdiidgN914kAALwLWKt2E5q4R4HXlnx/NzP3At5fqp60jD6QmXuXKhYRP6M54KbIeQMDsXntBvqu+nv2mbkjzfLX8rV70cQdGxEfLlVsdF7EJcAGpWpKM3AXsGtE/LRUwcw8FvhQqXpT7hFg1Yh4vHYjfdWFFYB34uQ/BJ8uPPmvApyOk7/qWQ84IzOLHTUdEScBHy9Vb8qtBBQ7qnmIqgaAzNwVeFnNHtSKC4E/LFzzJGDXwjWlmdqR8psCjwW+U7jmtPLR8RhqrwC8iw48htBE3Uqz6W9+qYKZ+X+Aw0vVk8b0+5n5tlLFIuJR4DXALaVqTrFVajfQZ9UCQGbuAuxXa3y14lHg0NEGpyIy80XAe0vVkwo5ITMPKFUsIm4DDgaKBecptWrtBvqs5grAn1ccW+14S0QUW8rMzM2AU4AVStWUClke+FxmblmqYERcCBS7g2BKuQIwhioBYPSL/OAaY6s1H4yIj5UqlpmrAmcA65eqKRW2Ls2mwNVLFYyIk2n2u+iJuYF8DLVWAN6Mf4ubZhcAf1aq2OgO9X8Ddi5VU5qQ7YGTRz+zpfwp8K2C9abJPbUb6LPWA0BmrgC8oe1x1ZqbaDb9lTzQ5K+A1xasJ03Sq4DjShUbbQo8GCh23sAUMQCMocYKwEH47ua0ehh4dUTcUapgZu4HvKNUPakl78rMl5cqFhF30QSLB0vVnBIGgDHUCABvqjCm2nF0RHy/VLHM3Jxm05/P+dQ3ywGfycynlyoYEf+DmwIXZwAYQ6vv4GfmOsBtTPeVv98DPgt8G7gpIu6r3I8kSUtoeyPeK5neyf8+4KiIOLV2I5IkLU3bAeCQlsdrywPAiyLCO70lSb3Q2iOA0buxdwErtzVmi46KCC/wkCT1RpubAPdlOif/q4FP1m5CkqSZaDMAFDsnu2M+633UkqS+aXsFYBqdX7sBSZJmqpUAkJlPBbZpY6wKvLJTktQ7ba0A7EnLZw60yENqJEm901YA2KOlcWp4Wu0GJEmaqbYCwA4tjVPDC2s3IEnSTLWyLJ+ZtzC9FwDdDGwxurFLkqRemPgKQGaux/RO/gCbAMfWbkKSpJlo4xHAM1oYo7b3ZObzajchSdKyaiMAzGlhjNpWAeZm5hszc1rfdpAkTREDQDmrAZ8CLs7MP87MZ2fmmpV7kiTpCbVxG+CcFsbokueMvgDIzIqtSJKexCM0t7nOG/3zduAnwFXAj4EfRsTP67U3WRNfrs7MM4FXTHocSZIKS+By4DzgHOCbEfFQ3ZbKaSMAfJfpPghIkjQM9wFnAicD50REr5d42wgAVzG99wBIkobpOuAE4N8iYn7tZmajjQBwO7DBpMeRJKmCW4H3Ax/u2+OBNgLAPcBakx5HkqSKbgbeFhH/UbuRZdXGa4ArtTCGJEk1bQKclplfysxNazezLNpYAViAV+ZKkobjPuDIiDitdiNPpo0VACd/SdKQrAmcmpkfzczOroK3sQLQ69ckJEkaw/nAKyJiXu1GFmcAkCRpsq4EDoiIm2o3sqg2HgFIkjRkzwS+k5lb125kUa4ASJLUjpuBvSLixtqNgCsAkiS1ZRPga5m5bu1GwAAgSVKbngWc2YW3AwwAkiS163nAe2s34R4ASZLal8CrI+KLtRowAEiSVMc8YIdarwf6CECSpDrWAU6sNbgrAJIk1XVgRHy17UENAJIk1XUdsF1EPNTmoD4CkCSpri2Ao9se1BUASZLquxnYKiLmtzWgKwCSJNW3CfDGNgd0BUCSpG64Btg6IlqZN10BkCSpG7aiOSWwFQYASZK647C2BvIRgCRJ3XEv8FttvBLoCoAkSd2xFrBvGwMZACRJ6pZ92hjEACBJUre0sgLgHgBJkrrlcWDDiLhzkoO4AiBJUrcsB+zYxiCSJKlbtpn0AAYASZK6xwAgSdIAGQAkSRqgjSY9gAFAkqTuecqkBzAASJLUPQYASZIGyAAgSdIArTzpAQwAkiQNkAFAkqQBMgBIkjRABgBJkgbIACBJ0gAZACRJGiADgCRJA2QAkCRpgAwAkiQNkAFAkqQBMgBIkjRABgBJkgbIACBJ0gAZACRJGiADgCRJA2QAkCRpgAwAkiQNkAFAkqQBMgBIkjRABgBJkgbIACBJ0gAZACRJGiADgCRJA2QAkCRpgAwAkiQNkAFAkqQBMgBIkjRABgBJkgbIACBJ0gAZACRJGiADgCRJA2QAkCRpgAwAkiQNkAFAkqQBMgBIkjRABgBJkgbIACBJ0gAZACRJGiADgCRJA2QAkCRpgAwAkiQNkAFAkqQBMgBIkjRABgBJkgbIACBJ0gAZACRJGiADgCRJA7RC7QYkaSnuAM4DLgSuAq4Dfg48EBGP1GxM6jMDgKQumgecAnwGuCgisnI/0tQxAEjqktuA9wMfiYhf1G5GmmYGAEldsAA4CTg+Iu6r3Yw0BAYASbVdBxwaEd+v3Yg0JL4FIKmms4Cdnfyl9hkAJNXyWeCVEXFv7UakIfIRgKQaPg0c7u5+qZ6Y9ACZ6R9wSYs6C/jdiFhQuxFpyAwAktp0I7BTRNxduxFp6NwDIKktC4CDnfylbjAASGrLv7jbX+oOHwFIasNtwNYRcX/tRiQ1XAGQ1Ib3O/lL3eIKgKRJmwds6tn+Ure4AiBp0k5x8pe6x4OAJE3ayaUKZeazgCOB/YA5wOqlaktdExETXaX3EYCkSboD2GjcE/8ycyWaa4KPAZYv0ZjUdZMOAK4ASJqk8wpN/mcBLy7TkiRwD4CkybqwQI334+QvFWcAkDRJV43z4dEz/2MK9SJpEQYASZN0zZifPwqf+UsTYQCQNEnjnvu/X5EuJC3BACBpksZ9/3/TIl1IWoKvAUqamHFfY/L3h4Zs0q8BugIgSdIAGQAkSRogA4AkSQNkAJAkaYAMAJIkDZABQJKkATIASJI0QN4GKEmT8zPgMuBy4ErgWprTEe8G5o3+nXUX+doKeCawHbADsGHL/WpAPAhI0sQM8CCgBcC5wFzg7Ii4Ypximbk98BJgf2AfvBdhUCZ9EJABQNLEDCgA3AR8HjgpIm6cxACZ+VvAG2guSNpyEmOoWwwAknprAAHgKuDdwOci4rE2BszMAA4G3gls3caYqsMAIKm3pjgA3An8JXByWxP/4jJzBeBNwHtp9g9oyhgAJPXWlAaArwJ/GBG31m4EIDM3BD4EvLp2LyrLy4AkqRvmA4dHxIFdmfwBIuL2iDiYZm/AI7X7UX+4AiBpYqZoBeBO4OCI+HbtRp5MZu4JnIGvD04FHwFI6q0pCQA3AntHxE9rN7IsMnNL4FvAJpVb0Zh8BCBJ9dwC7NuXyR8gIq4F9gU685hC3WQAkKQndi+w32hC7ZWIuBrYD7ivdi/qLgOAJC3pceD1EfG/tRuZrYi4EjiM5nuRlmAAkKQlvSMivlq7iXFFxJeB99TuQ93kJkBJE9PTTYCXArtGxKMVxi5udGDQxcBOtXvRzLgJUJLaswA4Ylomf4CIWAAcQfO9Sb9kAJCkX/lIRPygdhOlRcQPgU/W7kPd4iMASRPTs0cADwFPj4hbShfOzA2AA4AXANsBmwFrj/7ne4DrgSuAbwNzI+LnE+hhY+AaYNXStTUZHgQkqbd6FgDeFxHHlSyYmXsAxwEvB1ZYxo89SnPfwHsj4qLC/XwA+NOSNTU5BgBJvdWjAPAYsGVE3FCiWMELek4F3hoRd4zfFWTmFsDV+Pi3F9wEKEmT99WCk/9ewGWUuZ3vNcClmbl7gVpExHXA2SVqqf8MAJIEnyhRJDNfDHwT2KBEvZGNgHMzc99C9T5WqI56zkcAkiamJ48AfgGsHxEPj1MkM7cBfgCsXqSrJf0C2Hl0zO+sZeaqNLcbrlakK02MjwAkabLmFpj8VwROZnKTP8AawCmZudI4RSLiIeCcMi2pzwwAkoZuboEaxwO7FaizNLsAf12gzn8WqKGe8xGApInpySOA7SPi8tl+ODPXBG4E1irX0pO6D9g0Iu6dbYHM3AW4pFxLmgQfAUjS5DwAjHvj37G0N/kDrAkcNWaNy2gOPtKAGQAkDdmPRmflj+OIIp3MzJHjfHh010FvrzpWGQYASUP203E+nJmbAlsV6mUmtsnMTcascX2JRtRfBgBJQzZWAABeVKSL2dlnzM9fX6IJ9ZcBQNKQjXvpzrOLdDE724/5+duKdKHeMgBIGrIHxvx8yRP/2h77wSJdqLcMAJKGbMgBYNzvXT1nAJA0ZOO+Z/14kS5mxzNWNBYDgKQhG/c8/HH3EIxj3CuCJ3lssXrAACBpyMadBGsGgHHHNgAMnAFA0pCN+xz9siJdzM6lY35+wyJdqLcMAJKGbM6Yn695q955Y35+Tokm1F8GAElDtsU4H46Im4CrC/UyE1dFxC1j1phTohH1lwFA0pA9KzNXGLPGx4p0MjP/Os6HM3NFYNtCvainDACShmw14Flj1vgIcE+BXpbVPODjY9bYAVi1QC/qMQOApKF77jgfjoj7gRML9bIsPjAacxxjfc+aDgYASUN3QIEa7wQuKlBnaS4B3lOgTonvWT037ilYS5WZnlYlDVREjPU7pqXfHw8C60fEWGfjZ+bTgf8G1ijS1ZLuB3aOiGvGKZKZq9GcITDuIUiasHH//CyNKwCShm41YL9xi0TE1cBBwENjd7SkB4EDx538Rw7AyV8YACQJ4IgSRSLiXGAf4Gcl6o3cCuwdEd8uVO/oQnXUcwYASYKXZ+acEoUi4iKaXfZfYLwLexL4HLB9RHy/RG+ZuQUFVjs0HQwAktT8LnxLqWIR8fOI+D1gd+B04NEZfPwR4D+A3SLi9RFxV6m+gD/B3/sacROgpInpySbAhR4Gnh4RN5cunJlPBV4CvJDm3IHNgXVG//PdwPXAFcC3gbMLT/oLe3gazamFvv/fE5PeBGgAkDQxPQsAACdFRLGVgC7JzI8BR9buQ8vOACCpt3oYABYAe0TEJS2PO1GZ+VzgAmD52r1o2fkaoCS1ZwXgE6Oz8qdCZq4EfAInfy3GACBJv2574PjaTRT0D4x/34GmkI8AJE1MDx8B/HJo4JCIOL3S+EVk5kHAF2nhd73Kcw+ApN7qcQAAuI9mP8CVFXuYtczcDvgu8JTavWh23AMgSXWsCZybmdvWbmSmRvcSzMXJX0/CACBJv9mGwNmZuWXtRpbVaPL/FrBx5VbUcQYASXpymwAXZebetRtZmszcCzgfJ38tAwOAJC3desDczOzsQTqZ+WbgPGCD2r2oH9wEKGlier4J8Df5GnB0RNxSuxGAzNwIOAl4Ze1eVJabACWpW14GXJaZR2XmCrWayMwVR3/r/1+c/DULrgBImpgpXQFY1PXAu4FPRMRjbQyYmcsBrwbeBTy9jTFVh+cASOqtAQSAhW4GPgd8JCKun8QAmbkxcBhwNLDFJMZQtxgAJPXWgALAQo/RvII3FzgbuCwiZvU9ZGYAO9BcI3wA8AI8z39QDACSemuAAWBxdwCXAlcAVwLXAneNvu4e/TvrAeuO/rklzbn929FM/uu33K86xAAgqbcMANLs+RaAJEkqzgAgSdIAGQAkSRogA4AkSQNkAJAkaYAMAJIkDZABQJKkATIASJqYzFxpzBL3F2lE0hIMAJImaY0xP39jkS4kLcEAIGmS1h3z82cX6ULSEgwAkiZpqzE//3GaC3YkFWYAkDRJzxjnwxFxJfChQr1IWoQBQNIk7VGgxp8D3yhQR9IiDACSJmnv0b32sxYRjwIvB04EFhTpSpLXAUuauD0j4nslCmXmM4EjgJcAcxj/LQOpsyZ9HbABQNKkfTgijq3dhKRfZwCQNGn3AJtGhIf6SB3iHgBJk7Y28ObaTUj6da4ASGrD7cDWEXFf7UYkNVwBkNSGDYG3125C0q+4AiCpLQuA50XERbUbkWQAkNSuG4GdI+Ku2o1IQ+cjAElt2hT4TGauWLsRaegMAJLa9lLgE+OeEChpPAYASTUchisBUlXuAZBU01zg9yJiXu1GpKFxBUBSTfsDP8zM3Ws3Ig2NAUBSbZsBF2TmyZm5Xu1mpKHwEYCkLrkD+CfgJO8OkCbLACCpi+4B/h04GbgwIh6v3I80dQwAkrruTuBbwPeAq4BrR/+3+yPikYp9Sb1mAJAkqYMiYqJztJsAJUkaIAOAJEkDZACQJGmADACSJA2QAUCSpAEyAEiSNEAGAEmSBsgAIEnSABkAJEkaIAOAJEkDZACQJGmADACSJA2QAUCSpAEyAEiSNEAGAEmSBqiNAPBYC2NIkqQZaCMAPNLCGJIkaQYMAJIkDVAbAWB+C2NIkqQZaCMAzGthDEmSNANtBIA7WxhDkiTNQBsB4K4WxpAkSTPQRgC4vYUxJEnSDLQRAG5sYQxJkjQDbQSAn7YwhiRJmgEDgCRJA9RGALiqhTEkSdIMTDwARMTdwM2THkeSJC27tm4DvKylcSRJ0jJoKwBc2tI4kiRpGbQVAL7b0jiSJGkZRBuDZOY6NEcCtxU4JEnqtYiY6BzdyjeImy8AAAU8SURBVIQcEfOAH7cxliRJWro2/0Z+botjSZKkJ9FmAPjPFseSJElPopU9AACZuTrNPoBV2hpTkqS+moo9AAAR8QBwXlvjSZKk36ztXfmntTyeJEl6Aq09AgDIzLWB24CV2xxXkqS+mZpHAAARcQ9wdptjSpKkJdU4mOdTFcaUJEmLaPURAEBmrgDcAGzc9tiSJPXFVD0CAIiIBcCn2x5XkiT9SusrAACZuQlwHbBijfElSeq6qVsBAIiIm/GVQEmSqqmyAgCQmTsDP6g1viRJXTaVKwAAEfHf+EqgJElVVFsBAMjM5wAX1+5DkqSOmR8RE707p9oKAEBEXAKcVbMHSZI66P5JD1A1AIz8DfBY7SYkSeqQ6Q8AEXEZ8PHafUiS1CHTHwBGjgfuqd2EJEkdcdukB+hEAIiInwP/t3YfkiR1xI8nPUAnAsDIh4ALajchSVIHDCcARMTjwJHA/Nq9SJJU2XACAEBEXAW8o3YfkiRV9Djww0kP0rkDeDJzOeAcYO/KrUiSVMMPI2LnSQ/SqRUA+OWjgMOAebV7kSSpgnPaGKRzAQB+eVvgEUDW7kWSpJad18YgnQwAABHxReC9tfuQJKlF9zL0ADDyt8A3ajchSVJLTo2Ih9oYqNMBICIeAw4GLq/diyRJLTi5rYE69xbAE8nMzYALgY1q9yJJ0oRcA2wdEa3sf+v0CsBCEXED8DvAfbV7kSRpQk5oa/KHnqwALJSZewBnA2vU7kWSpIJuBraKiNZOw+3FCsBCEfE94FV4XLAkabqc0ObkDz1bAVgoM/cDvgSsVrsXSZLGdC2wXUQ83OagvVoBWCgivgHsT/O+pCRJffYnbU/+0NMAABAR5wMvAm6r3YskSbN0RkScVWPgXj4CWNToFcGzgGfV7kWSpBm4G9hhdPx963q7ArDQ6BXBvYC5tXuRJGkZJfCmWpM/TEEAAIiIe4GXAn9Fc4+yJEld9k8R8ZWaDfT+EcDiMvMg4FPA2pVbkSTpifwX8OKIeLRmE1MXAAAy87eBzwAvrN2LJEmLuAJ4QUTMq93IVDwCWFxE3ETzhsBf46FBkqRuuAHYvwuTP0zpCsCiMvOZwMeAPWv3IkkarBuA/SLi6tqNLDSVKwCLiogrgecDfwR0InVJkgblcmDPLk3+MIAVgEVl5lOBfwCOBpav3I4kafr9F3BQRNxTu5HFTf0KwKIi4s6IOBbYETiT5j1MSZJKS+CfaHb7d27yh4GtACwuM58DvB14We1eJElT426aQ36qvue/NIMOAAtl5o7AnwGvBVas3I4kqb/OoLncp9oJf8vKALCI0fkBfwgcDmxcuR1JUn9cC7w1Ir5eu5FlZQB4Apm5As1jgcOBA4BV6nYkSeqom4ETgH+tcaXvOAwAS5GZawEHAYfQHC60at2OJEkdcA3NxP+piHikdjOzYQCYgcxcleZ44ZfShIFtGdibFJI0YPcAp9EcNX9+RPT6TTIDwBgycx2aEwb3oHm18NnAplWbkiSV8jhwKXDuwq++LfM/GQNAYZm5NvAMYA6wObAZsBGw3iJfK46+1qjTpSQJeAT4Bc3f7O8Hbgd+AlwF/Bj4YUTcVa89SZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSVIX/X8GzPzs6d3fGgAAAABJRU5ErkJggg==
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAgAAAAIACAYAAAD0eNT6AAAAAXNSR0IArs4c6QAAIABJREFUeF7snQfULEXR9///7nn0RVSCivr6qYAkiUpGQAQRBclBVIIISBIJioIEERUJiuQkiqCgKEGRKFmQbEAERIkGRFQEERDY6a6Pnt3rey/c+3TPPrO7M7M15zzn3nOmurvq17MzNT3VVYQeSkAJKAEloASUwNgR4NhZrAYrASWgBJSAElACUAdALwIloASUgBJQAmNIQB2AMZx0NVkJKAEloASUgDoAeg0oASWgBJSAEhhDAuoAjOGkq8lKQAkoASWgBNQB0GtACSgBJaAElMAYElAHYAwnXU1WAkpACSgBJaAOgF4DSkAJKAEloATGkIA6AGM46WqyElACSkAJKAF1APQaUAJKQAkoASUwhgTUARjDSVeTlYASUAJKQAmoA6DXgBJQAkpACSiBMSSgDsAYTrqarASUgBJQAkpAHQC9BpSAElACSkAJjCEBdQDGcNLVZCWgBJSAElAC6gDoNaAElIASUAJKYAwJqAMwhpOuJisBJaAElIASUAdArwEloASUgBJQAmNIQB2AMZx0NVkJKAEloASUgDoAeg0oASWgBJSAEhhDAuoAjOGkq8lKQAkoASWgBNQB0GtACSgBJaAElMAYElAHYAwnXU1WAkpACSgBJaAOgF4DSkAJKAEloATGkIA6AGM46WqyElACSkAJKAF1APQaUAJKQAkoASUwhgTUARjDSVeTlYASUAJKQAmoA6DXgBJQAkpACSiBMSSgDsAYTrqarASUgBJQAkpAHQC9BpSAElACSkAJjCEBdQDGcNLVZCWgBJSAElAC6gDoNaAElIASUAJKYAwJqAMwhpOuJisBJaAElIASUAdArwEloASUgBJQAmNIQB2AMZx0NVkJKAEloASUgDoAeg0oASWgBJSAEhhDAuoAjOGkq8lKQAkoASWgBNQB0GtACSgBJaAElMAYElAHYAwnXU1WAkpACSgBJaAOgF4DSkAJKAEloATGkIA6AGM46WqyElACSkAJKAF1APQaUAJKQAkoASUwhgTUARjDSVeTlYASUAJKQAmoA6DXgBJQAkpACSiBMSSgDsAYTrqarASUgBJQAkpAHQC9BpSAElACSkAJjCEBdQDGcNLVZCWgBJSAElAC6gDoNaAElIASUAJKYAwJqAMwhpOuJisBJaAElIASUAdArwEloASUgBJoLAEReQmA1wF4OYDw/ycA/JPk4401akiKqwMwJNA6jBJQAkpACUydgIi8AXDrAFwD4peBYD5Ashf1TP4d4B0gfwqYywDcRFKmrkF7elAHoD1zqZYoASWgBFpJQEQIuHUB83F4tyYgtrShNPeBPBUwJ+jqQJeeOgClryJtoASUgBJQAsMiINJZA2KOgLi3VTMm/wVjvgKYr5J8tpo+m9mLOgDTzZuITABYCnALAVwAwOwA5gTwdO/vz4D/PZD9muQ/mjnlqrUSUAJKoP4EROSVgD8W3m01kJdV8ndgtg3Jm+pPYzAajr0DICJzA/4DgGwML+8AJDz0Y4eA9k4QlwDmDJK3xxroeSWgBJSAEkgjICKLQ/JzIbJQWot+pdiBMZ8m7dH99tDkdmPrAIjIIoD/NLzfApCXTmkSaW4BcRhgf0TST6kvbawElIASGGMCIrI8JL8YIq8aGgZjjwPM7uN2/x47B0BE5gL85+H9x/sKJJnsiqT9FWh2JXnD0C5cHUgJKAEl0BICIrISfH4FIC8buknGHkfaTwx93BEOOFYOgEjnPRB8GyJhz+igDg9jvwqY/Ul2BjWI9qsElIASaBMBEVkYkl8/1Df/FwI0dh/SHtYmrpO+s46LoSJuP3j3BQBmKDbT3AjaDVjsRdVDCSgBJaAEZkVARP4H4m+CuKVGTMnDcC1y4soR6zGU4Vu/AtDdP+qPg3e7DIXo9IOQ94DZWiQfHPrYOqASUAJKoCEERNxR8G73WqhLPgRmi5H8Vy30GaASY+AAuK/Au70GyHDyrovkE3ZVkg+PTAcdWAkoASVQUwJFxL/PfzXTbH6j0tnYI0n7yVENP6xxW+0AiLhPwLtjhgVzluPQ/LznBDwzcl1UASWgBJRAjQiI5JfD+zVrpFJIO5DDZIuQvK9eelWrTWsdgGIric+vA4pCEaM/jD2ZtDuNXhHVQAkoASVQDwIishx855Z6aPMCLcbgnt1KB0BEMoj/eQ0CSma8orrBJZfX8mJXpZSAElACQyYg4r4D77Yc8rCJw/EZmOz1ba4b0FIHwH0a3h2eOMvDE6O5F7QhuOS54Q2qIykBJaAE6kdARGaHz/8KSCjjW8/DmO3J7Jv1VG7qWrXOASguKskfgMhrpo5nAD0YswOZnTKAnrVLJaAElEBjCIjkm8D7c2qtsMkuIc06tdZxCsq10AFwu8G7+uZ1prkftAuOW8rJKVyj2lQJKIEWEhBxodDPrvU2jU/CZHO3Nalb+xwA726r3bf/F17hhmuOS6KJev+4VTsloARGRUC8C3Fay4xq/ORxzcTSJH+VLN8gwVY5ACKyGHznjtrzN/ZbpN229nqqgkpACSiBAREQ13kCkFcMqPvqujXmQ2R2VnUd1qenljkAbnd4d1R98M5CE/Ihmon/V3s9VUEloASUwAAIiMg88J1HBtB19V0auz9pD66+49H32DIHwJ8Dn28yeqwJGpiJEAdwb4KkiigBJaAEWkVARBaE7/y+EUYZezhp926EriWVbJcD4Dt3QeStJRmMRtyYDcns/NEMrqMqASWgBEZHQESWgu/cNjoNSoxs7ImkHX4tmRIq9ivaGgegKPrj82dqk/kvNiPGfoa0X4mJ6XkloASUQNsIiMii8J07G2GXsUeRds9G6FpSyTY5ALPDd54saf/oxI09lLSfHZ0COrISUAJKYDQEROSN8J0/jmb0kqMa+0XSfq5kq0aIt8kBaE5QSbg0jD2BtB9vxFWiSioBJaAEKiQgIi+Bz5+qVQXAWdln7E6kPblC82vTVZscgDnhO4/VhmxMEWOPJu0eMTE9rwSUgBJoIwHx+b0Q/5ba22a4Bjlxde317EPBNjkAFr7TCXUc++Aw/CbGfom0Bwx/YB1RCSgBJTB6AiL+B/D5ZqPXZFINPMzEa0j+s+Z69qVeMx6WiaaJ7zwEkf9NFB+tmLE7k/ak0SqhoysBJaAERkNAxO0K744dzeiJo9LeRmPfnijdOLGWOQD5lRC/RiNmwXB1cuKaRuiqSioBJaAEKiYgIvPBd+6r9aqtsYeQdt+KTa9Nd+1yAMQdAu/2qQ3dWSpCB5O9us11pus/B6qhElACoyYgPr8B4lcatR6zHN9MLEGy/unl+wTYMgeg8x54uaxPFsNrRnMrTbb88AbUkZSAElAC9SMgkn8E3p9WP83CuoS5iSarr3NSAbSWOQDyUvj8L4DMXQGbwXVh7OdI+8XBDaA9KwEloATqT6DYDij5fRCpX20UYzYgsx/Xn2L/GrbKAQgYRNxx8K7O++sFZmIBkvf3P23aUgkoASXQDgIi+bbw/pu1sobmZtCuRFJqpVfFyrTQAZC39koCm4pZVdOdyS4kzXrVdKa9KAEloASaTUBEDMTdDPHL1sSSsPVvRZK31kSfganROgegtwrwPXj3wYFRm0rHZmIFkrdMpQttqwSUgBJoEwEJRdx8/gtAZhu5XS2P/J+eb0sdAHkTfH4XILOP/GKaXgFjv0vaLWqlkyqjBJSAEqgBAZF8e3h/ykhVobketKuTDEnlWn+00gHorQJ8Gt4dXp8Z5D9hssVI/rU+OqkmSkAJKIH6EBBxX4F3e41EI/L3YLYyyX+MZPwRDNpiB0AMIBfC52uPgOsLhxQYszGZ/agGuqgKSkAJKIHaEhBxR8C7Tw5VQfIeMHsPyT8MddwRD9ZaB6C7CiCvguQ/g8giI+Vs7IGk/cJIddDBlYASUAINICAiBPz+8O6goWQJpLkFtOuTfKQBeCpVsdUOQM8JeCOkcx0Eb66UXGpnxh5H2k+kiqucElACSkAJhBe4fH2IfBMirx4YD2NPBMyeJJ8d2Bg17rj1DkDPCXg9xF8McW8b6lwYewxg9mj7XtKhMtXBlIASaBwBEQkvYB2SfymjvIi8HvCHw7sQPF3d86r43o9dyIkry+jTNtnqgNacjIjMAcg34PNNB68qn4ThLmT2ncGPpSMoASWgBOpLQETeCHHXAHwcNKuQ/E9ZbUVkeUA+C5+vD6D/HC8094M4BLCnj0uk/2Ssx8YBmAZBJN8OXg4fWLrg7jaSbRk8TD2UgBJQAmNM4L8Pf/HzFxiMPRMwW/W7KlpUEIT/MEQ2hMjbAbFRvOSfQXMZ4M8EsmtI+mibMREYOweg90ngVYA/EN5vX1niCZr7QBwIhL3+5dJHisgbAH8AYD6hXumY/PLUTCXQcgIS8vuLuxriF5jBVGOPJ+2uUzVfRF4J5MsAZiEAbwIQ8r68BMATAP4ByD2AvYNkKDmsx0wIjKUD8H+rATIP4HeC+C0hsmD5KySU9bVXAP5UwJ5L0pXtQ0QmIO4qiF8FJrsY4MbjGpBSlp3K90ege+NEeHMKS6nT3obC99kn++tRWymBGQkULzWSXz3L+6qxh5G2AaXb2z2zY+0ATD+1IrIU4FcHuEqxbbDwWuWlM0x/kSCC94K8DZBrAXslyb/1e4kUObDDstT0aYtNdknPCXim3361XbsJiBTLnqF62psB91qArwHwKgAhWvpVAF8FkdcUn7lE5uzReCkgL0sjw6cBhKhoAflPAI+C5lFAHi3+/98/+QdgHwLwAMmH0/pWqbYTEJH/7T38w5v5rA9jT+iteuqS/IguCnUAJgEvUuSlDn+hItQT/bzhz6r73l7XULlwlxfJmOwCgJvpSsCIfhU1GFakeFgvBri3AJwPwHyAzAfBfBB5EyATNVBzOhX4DIg/gPZBQB4EEP59ALB3AbhbP23Va7YGpY2IzNN7+C+aNIbJLgX4YZKPJcmrUKUE1AGoFGdaZ903OH8CvNthli26P4yNSOpKQBrWxkoVb0zIFwXMYgCWgfhlIFg4KcCpEVYzB/lH0IT6HKHgy509x+CusvEyjTB3TJUUkdf2Hv5vLYXA2G+RdttSbVS4EgLqAFSCMb2T7vdX+U5vO8vkDbsxAZuoE5DOt+6SvcCllQCzMkTC39LAf5fp665+xfqF+hj2RkBuBPz1QHYryacqHkS7GwIBCZ+cxF8FcYuXGq67a2ptkv8u1U6FKyGgDkAlGNM6EZFFIfnZCP+mHib7SW8loPTe2dQhVG5wBLo7PNyqAN8BwaoQv0R73uyr5lasFNwG8oauU2CvHsf0rFVTHXR/vYf/lRC3RKmxaG4A7fv04V+KWqXC6gBUinPyziS88fn8EkBeUWpYE/aw2g37SaBRahwVnjIBEckArAj4dSFYE+KWmXKn49xBkbiFFwL+AiC7TuNi6nUxiMhcz+9gugLili6lGc2NoH2vPvxLUatcWB2AypFGnYB39JyAsBUr/aD5KWjfr0uk6ciGJdlNc+rXBrgOvFsDkLAfWY/KCfDfMPYqQH4CmEtIhmBDPUZEQMIOk+7Dv5yT2334hzf/sF9fjxESUAdgBPBFpF8n4NqeE6D7tUcwb9MPKSJvBfzmEGwKcSF4T49hE6D5OcizAXMOyfuHPfw4j9d9+LvLIX7ZUhxofwGaUHZXo/5LgRuMsDoAg+Ea7VVEloHPLwdkrqjw9AI06gSUAladsBTb7/xGENkM4leurmftacoEyLtAE5yB75H83ZT70w5mSaD38L8M4pcrhYn2l6BZUx/+pagNVFgdgIHinbzznhNwWem6BDTXgXYdzdw2+MnrpWneHCKbP19RcvnBj6gjTJlA8ZaJbwPmDHYTGelREYGiqJq48PAv91voPvzDm7/OR0VzUUU36gBUQXEKfUjYBtZdCZi7VDc0P+s5Abp9phS4uHA3Q2O+BmB3gHcb1i/pTtwGlQgE+CyM/THgvwPYi6tM5DWOfKfw8P9V781fH/41u3DUAajBhEioaiX55RAJ6VzTD3UC0lklSPZqj28NkR0hPmTf06MtBMiHQHMGYE4m+UBbzBqWHUX+iu6b/wqlxqS9DTTv1jf/UtSGJqwOwNBQTz6QiLyt5wSEfO7phybSSGc1E8luSmb3PsDsCO/eDxTb+PRoLwGPbqrtI0n+tL1mVmeZiMwOcRc/n+jnnaV67T78wzf/UD9CjxoSUAegRpNSFCSS/AqIlHUCQkKNkE1Lt9UkzqeIvARwH4TwMxrFnwitbWLFAwonAubbmm1z5pPbe/hfBPGrlZp+2l/33vz14V8K3HCF1QEYLu/oaD0nIHwOCBXe0o9uVi11AiLEuql4/Uchfi+EeuV6KAHyEdCcBJjjWFT81CMQKApSiQsP/3eVItJ9+Ic3f2VZCtzwhdUBGD7z6IjFHnPJr4LI66LC0wvoHttZ4uol69kd3m9fOhNjqUlQ4eYS4NMw5hTAHDbu5Y17D/8LIaFEeomD9vbem78+/EtgG5WoOgCjIh9/U12k5wS8vpSKXSdgLQ266VKT4i3ffxre7wjIS0uxVOExJcDnYMxpgDmI5F/GDULv4X8BxK9RynbybjBbneRfS7VT4ZERUAdgZOjjA4vIwj0n4H/j0tNJ6J7b8OB/NeD3gve7ATJbKX4qrAQKAmEboTl9nBwBEZkN4sKbvz78x+BXoA5AzSdZnYByEyQS8ikUb/yf0Jz85dip9KwIFJ8GQrDgIW2OaC8e/nA/hvdrlroWQubF7pv/w6XaqfDICagDMPIpiCsgIgv1VgLeEJeeYSUgJOAI2bdaH4lbRCvDfwrefxKQOUpxUmElkESAj8GYL/WCBZ9LatIQIZHweUzOhc/fX0plffiXwlU3YXUA6jYjs9BHRBaE5FejqC9f4hiDvbgi+XoQfywEby5BRkWVQH8EaO4FsS9gQxEi6a+T+rTqboktHv7rltKK/H3vzX/s4iRKcaqxsDoANZ6cF6omIvNC3NUQP28ptbtOQFgJaFVkbjeDojsa4lctxUOFlUAVBGhuAu0nSd5YRXej6KP38D8HPl+v1Pj68C+Fq67C6gDUdWZmvRLw5p4TUC5VbYv25orIPIA/GN5tC8A0bApV3XYR8DA2BAruTfLvTTKt9/A/Gz5fv5Te5D1g9q5x3CFRilMDhNUBaMAkzWQlYCydABGxgP8EvP+8fudv4IXbZpVDnA35KcCGrIK1/yzQe/j/AD7foNS0dB/+IeDvoVLtVLiWBNQBqOW0xJUqatN3PwfMH5eeToL8LZit0bS9uiKyOMR9s3QZ0lJwVFgJTJEAzbWg3Ynhd1bTQ0QmAAkP/w1LqVjEPtjw5q8P/1Lg6iusDkB95yaqWc8JuAri3xIVnl6gQU5A92blPwnvD9JEPqVmWYVHRoAdGPM1wBxI8tmRqTGTgXuraGfAuw+W0ov4AzgRHv4PlmqnwrUmoA5AracnrpyIvBHighOwQFx6hpWAkLUrrATUdu+uiKwA8d+AuMVL2abCSqAOBMi7wGxbkjfXQR19+NdhFuqlgzoA9ZqPvrQp0t12Pwe0wgkoUpHCfxHe7w6E7/56KIGmEmAOYw4GzJdI5qOyovfw/za8+3ApHYg/9t78HyjVToUbQUAdgEZMU1xJCYWDJL8SIovGpWdYCQhZvMJKQC328na/9fvvQtwSpexQYSVQZwI0t4J2K4bEOUM+eg//0+HdFqWG1od/KVxNFFYHoImzNgudReS1vYyBjXMCRISA3w3eH6bf+lt0Uaop03vb/4ExnwXMMcPaKdB7+J8G77YsNRXdh3+I9r+/VDsVbhQBdQAaNV1xZbtOgL8S4haLS8+wEhCyeoWVgKFH+BarF3Cnw/u1SumswkqgiQRMdgnAEBsw0Kp5vYf/t+DdVqUwEX/qLfvrw78UuOYJqwPQvDmLalwkyuk6AeWC50awx1eksxYEp0GkXNnjKAUVUAI1JhCSBhEfJieuGISWImIAHx7+W5fqv/vwD2/+95Vqp8KNJKAOQCOnLa50zwm4ovS39K4TEFYC/hwfpX+J3va+r8C73ULd1f570pZKoKkEigDB/QFzeJWfBHqf006EdzuWIhN+890Mf/rwLwWuucJ6423u3EU1F5HX9FYCygXU0TwI2vAWMJA9v1293PchfvWoESqgBNpOwGQXAtya5GNTNbX38D8B3u1Uqq/wOaKb4e/uUu1UuNEE1AFo9PTFle85AWElYMm49HQS3cQf4YZQ6fYfEVka0jlPK/eVmg0VbjuB7u9tM5K39mtq7+F/PLzbuVQf5CO9h39tsxeWskeFkwmoA5CMqrmCIjIXxF0G8cuWsqJiJ0Ak3xZeTtAo/1KzoMJjQ4D/geFOZPbtfkwWyT8M788s1TZs/+2++f++VDsVbgUBdQBaMY1xI0Rkzp4TsFxceoaVgClvBxKRDPBfgnd7lxpbhZXAOBIw9hjA7EnSlzG/twJwVC+uJt60++Yf4n3uigurRBsJqAPQxlmdhU0iMjfEXw5xS5cym/ZO0CxZ9oYUxhCRV0PcDyF+lVJjqrASGGcCJjunFxfwnzIYek7A1+DdHpO2I//We/jfWaZ/lW0XAXUA2jWfUWt6KwGXQvwKUeFCgM/CcCMy7F0ud4jIfJD8EogsXK6lSisBJQDa20CzXj87ckTcl+HdZ2dKUR/+enH1CKgDMIaXgojMAXE/iTsBfA6Gm5AhSrncISLLQfILEBIT6aEElEB/BEJiLmbBCfhV2Q5EXPjstt8M7Yr8A8Wy/x1l+1P59hFQB6B9c5pkUc8JCCsBK868QShpyk3J7MdJHU4nJJKvBy/fA2T2sm1VXgkogRcS4BMw2IycuKwsGxH3BXh3QNGu+/B/N8nflO1H5dtJQB2Ads5rklUiMjvEXQTxq83YgA6GW5LZWUkdzfjw3w5eTgJC4J8eSkAJVEOgWI3bisx+ULY/Efd5iN9FH/5lybVfXh2A9s/xpBb2nIALIf5dPUEPYz5CZmeURSPiDoZ3+5Ztp/JKQAmkECgc8x3I7NQU6ellQo0Qhqh/PZTAdATUAdDLIUTqh5WACwonwNidSPv1MliSI4/LdKqySkAJzIyAwNjPkParikcJTJWAOgBTJdiS9iLycsCtSWY/KmNS7+F/DLzbtUw7lVUCSmAKBIw9jLT7TKEHbaoEtAiLXgP9E+hVHDsF3m3bfy/aUgkogb4IGHssYHavspBQX3poo8YS0BWAxk7daBXv1Rr/Jrz7yGg10dGVwBgTMPY40n5ijAmo6VMgoA7AFOCNa9Pew/80eLfluDJQu5VAbQgYexRp96yNPqpIYwioA9CYqaqHor2H/5nwbvN6aKRaKAElAGO/SNrPKQklUIaAOgBlaI25bC/g7yR4t8OYo1DzlUD9CBi7P2kPrp9iqlFdCagDUNeZqaFeIu5QrehXw4lRlZTANALG7kPawxSIEkghoA5ACiWVgYjbDd4drSiUgBKoNYGQJ2BX0p5Qay1VuVoQUAegFtNQbyVE8u3hfUgOpNdLvadKtVMCgYDAmO3I7FuKQwlMRkBv6Hp9TEpAJN8QXs7W3P56oSiBJhEo0gZv2E8lzyZZqbpOjYA6AFPj1+rWIp33wONCQF7SakPVOCXQSgKhimC2ilb/a+XkVmKUOgCVYGxfJyKyCHx+EyBztM86tUgJjAkB8iEwW5Hkn8fEYjWzBAF1AErAGhdREZkb4m6G+AXGxWa1Uwm0lgDtL0HzTpJPtdZGNawvAuoA9IWtvY1EJIO4n0D8Gu21Ui1TAmNGwGQXAdyApBszy9XcSQioA6CXxwwERNwJ8G5nxaIElEDLCBh7BGn3aplVas4UCKgDMAV4bWsq4naBd8e3zS61RwkogR6Bbo4A/Y3rBVEQUAdAL4SCgIisCp9foRH/ekEogTYTYA6TrUHyujZbqbalEVAHII1Tq6VEZAH4/GZA5m61oWqcElACQHdnwNIk/6Y4xpuAOgDjPf/hzf+lEH8jxL19zFGo+UpgfAjQXAXatTQocHymfGaWqgMw3vMfcvwfB+8+PuYYWm4+/wXy7wD/1TVU/g0iL1LGdg9CkAF8Re/8HBCZB5BXthzMeJtn7IGk/cJ4Qxhv69UBGOP576b59edpLEiTLwL+G+RvQT4A4MHun38AyELil0fDH8lOPxaKyASAV3X/8jcCZl4A3T+R+SHyVkBe3k/f2qYOBEK6YLyXnLiyDtqoDsMnoA7A8JnXYkQReRN8/iv97l+L6UhTgnwEtDcCchsgtwP2dgD3k5z2Jp/WT0VSImIAzAe4pQAuAfBtEPeO7uqBHo0gUFxT2dtJPtwIfVXJSgmoA1ApzmZ01kv2cw3Er9wMjcdUS/Ie0FwNyPWAvYHkvU0gISILAu4dAFeGyOqaUbLms0bzU9CuSTJ8FtJjjAioAzBGkz3NVBH3JXi33xiaXnOT+TSMvQaQSwBzaVMe+DGoXYfArw3wffDuXYDMFmuj54dMwNgvk1bvCUPGPurh1AEY9QwMeXwRWQ0+vxIQO+ShdbiZEuAzMPYKwJ8N2PNIPtlmUCLyP4B7D8DN4P1GGkNQm9n2MBOrkfxZbTRSRQZOQB2AgSOuzwDdIj/5HRB5fX20GkdNQvCVvRTwZwD2gnEt0iISAgjdeoDZCj5/L4AQU6DHqAiQd/fiAZ4ZlQo67nAJqAMwXN4jHU3EnQbvPjJSJcZ5cPIvoPkOYE4iGSL29egREJH/BfxWENkJ4sNOAz1GQcDYr5D2M6MYWsccPgF1AIbPfCQjinTWgpefjGTwcR+U5hoQRwL2Ik28MvnFIBI+Tbl1IdgT4lcb90tn+PaH1alsFZI3DX9sHXHYBNQBGDbxEYwnIrND3O0QP/8Ihh/XIT1MdjHAg/Vm2t8lICJvB/ye8P5DgGT99aKtShMgf9f7FPCf0m21QaMIqAPQqOnqT1kRdzS8262/1tqqHAF2YMxpgAkP/j+Ua1udtIiE3/Zr/i+Rj+sl9GF4kIbkPSHJz/RHSBb0JCBZAmx6AAAgAElEQVRhK9ijgC2SCPUSCY00Z7yIzAv4/eH9R9QRqO4ambQnYw8n7d5DGk2HGREBdQBGBH5Yw4rICvD59Rr1P3Di4Y3/XID7MezfH9IhRdKdfEnALAlgQYDzQtx8kJCxT15ajRp8BsSDoH0QkJBx8F7A3w5kv2aRYng4h4i8GfD7wvtt1REYOPOwK+CdJK8f+Eg6wMgIqAMwMvSDH7hb6Cf/JUQWHfxoYzyCyX4McG+GKOoBHt2o+XwFwKwMcKWigJPIawc4ZLxr8q+gDZkJbwD89UB2y6C3Mko3BfHh8Pm6cQVVom8CRYrpIkvgs333oQ1rTUAdgFpPz9SUE3FfhHf7T60XbT1LAsW2KX6KDN/6qz+KjI3ASkUSHcFaEL9U/d98mYO8DeRlgLkEwI2DCnwU6bwbYo6EuCWqp689FgSMPYC0X1Ia7SSgDkA75zWU+V0EPr8dKAq66FEpAT4OY/YHzMlVp08tAjZDFDzMJvAhYY7MWanqQ++Mj8GYywE5p7cL4ukqVeg6SX4XeP8FQOaosm/tKxAI2SmzxXTbajuvBnUA2jmvEPEXwufvb6l5ozPLZBcC3JlkqLZXySEiL+k+9Lk5vF/3+eXtl1XSce064VMw5kJAzgLsxSSfq0pFEXkdIMfC55tW1af20yNgsh+RZiPl0T4C6gC0b04h0nkPvFzWQtNGZ1KolkZ+nMx+WJUSvRz520H8R8evgl6xMnA2YI4leUd1TPNNIXIsCodAj8oIGLMOmYVPOnq0iIA6AC2azGBKkUhF/G0Qt3jLTBudOcaeBZjw1v/4VJXoltB160GwRy/Rzbj/BgUzJkryFTCeC/AnwbsPTLUvbd8j0M0NsATJsF1Uj5YQGPebT0um8f/MEHE7w7sTWmfYSAziEzDm06T9+lSHL3ZkwG0OkX1QRLHr8SICNPeBPBYwp5CccqyASL4ZvHy9+XEUNblWjN2NtMfWRBtVowIC6gBUALEuXYjIHJD8HoiEBDB6TIUAzfWg3Ypk2Pfe99GtfudDfvvw4B/tlr2+rRhyw2JroTmkF2Q5pS1oIjI/xJ0J8SsO2Yr2DUf+A8wWrGIlrH1wmmmROgDNnLeZai3ivgrvPtUik0Zjiglv/GbXqSx3dgP7/PYQvy9E3jAaQxo+KvEn0B4MmFOnOBdhp8CX4J1mtpvqJWHsV0n76al2o+3rQUAdgHrMw5S1EJG3wOd3Vpf9bcoqNbCDEKXOHcjsu1NRXqSzJgRHawKmqVCcrm3IrMiQYTE7eyo9iuRbwsvJ7d1lMRU6qW35LEy28CjTXKdqqnJxAuoAxBk1QkLEfV+DnqYwVTT3g3Yjkrf320uRewFyBHy+Tr99aLtJCBhzJWD3JPmbfjmJyNsg7jyIn6/fPsa+nbGnkna7sefQAgDqALRgEovUqL4TtlKZFpgzfBNobgbt+iT7KnojIrMBfm94v68mXhr09DGHMScAZl+ST/Uzmoi8CuJ+BPGr9NNe2xQlgxcfdOpr5Tx4AuoADJ7xwEcQcd+Fdx8a+EBtHMBk5wEMwX59RZ2LyKqQ/BSILNxGPLW1qdgxIDuSE1f2o2MvOPNb8O6D/bQf+zbGnkVavec0/EJQB6DhEyjhwdP99m8bbsrw1Tf2CMB8hmTpvefdlL3+CHi3Q8iXOnzldcSQ9gLGngiErZrlHbhuToZiDvdQmqUJhGqBoVBQ35/MSo+oDSonoDeuypEOt0MR9214t9VwR23BaMYeRtp9+rFERJaB5GfqW38/9AbQpijKlG1B8pf99C7i9oZ3h/bTdqzbGPt90uoKSoMvAnUAGjx5vcj/u+tfIa5WkMNb46dIe2RZrUSEgP9Mr/DMS8q2V/lBEuBzMGZfwHyNpJQdScR9HN6FJDd6T0yGV8QChEJBv0tuooK1IqAXe62mo5wyIu5UePfRcq3GWtrDmJ3I7JSyFETkFYCc9nyFxY3LtlX5IRIw2QUAt+4nWY2I2wHenajBtCXmy9jTSKv3oBLI6iSqDkCdZqOELiIyH3z+O406T4YmMGbHPh/+i0Dy8zSFbzLr0QoWeQOyjfspMtRzAk7SlYDUKWQHJltIywWn8qqXnDoA9ZqPZG1E3Mm9ALTkNmMtaOwepD26LAORfAN4OQOQl5dtq/KjJMB/w/DDZCjfXO4QcXvCu6+VazXG0sYeTVoNpGzgJaAOQAMnTUTmgs//rBnNEifP2P1I++VE6f+Kibjd4f0RusOiLLm6yIdv1GbPfgrYiLjPwbuD6mJJvfUIzlb2pn4+u9TbrvZrpw5AA+dYxO0F777SQNWHr7KxR5B2rzIDFyWV4b8G73Yr005la0rA2GOA4AiU2+4p4o7ULYKJc2rsXmTYVqtHkwioA9Ck2Qobn8PeZXH3airThIkz2bkAP1Dmxt97+IcEMbq1MgFxY0SMPQswITgwuZ59N0+AnK2BnwmzTP4ZzOYvwzehVxUZMAF1AAYMuOruRfJ14f0FVffbuv5obgLtGiT/k2pbt4KfnAWfb5TaRuUaRMCEeABuRvKZVK1F5GUQdzXEL5/aZmzljPnAVAs2jS27ERmuDsCIwPc7rIi/GD5fu9/2Y9GuW9hnRZJ/T7W3uNHD/RDer5XaRuUaSMBklwIMOwTKOIavhbibIH7eBlo8PJVprqbJ1hjegDrSVAmoAzBVgkNsLyILwHdC0g0t+jNL7vwPTLYyyV+lTk3vzf+HWsUvlVjD5Yy5HLDrkXw21RIRWRI+v1EDbyPEzERIDHRXKleVGy0BdQBGy7/U6BqUlIDLmG3I7PQEyUJERCYAOQc+Xz+1TcPkPIp98SY4RPcC8kcADwHyHJD9q7vfPX8lwNkA/j8A8wJ8CyRfFoI3N8zWdHVN9sNefEie2kgk/zC8PzNVfizljD2StJ8cS9sbaLQ6AA2ZtGKJ2ud/AmTuhqg8fDVL3nx6AX9nwrvNh6/sAEcsPoHwYkAuAex1JP/dz2giMg/gVgW4DsSvA5HX9dNPbdsYe2YvMDC5GJSIOxbe7Vpbm0auGB+Hyd7QT3Gmkas+hgqoA9CQSRfJt4X332yIusNXk+Z60K5eJgpZxB0F73YfvrKDGJH/gjFnAOZMkjdWPUI3Ij5fEzDbwfsNAHlp1WOMpD9jv0raT6eOXawYibsW4ldMbTN2csZsSWa6UtKAiVcHoAGTFFQUn18J8RpgM9P54pMwWShNem/qdIq43eBd6cyAqf0PTa7YfmWOAswpJJ8Yxrgi8mrAfxze7wnIHMMYc6BjGLsLGcoKpx0iMj98/itAXpnWYsykjLmMzN47ZlY30lx1ABowbSLy+t7yv22AusNX0ZityOyM1IF76X3PbXaGv7DUag4FzDFlItpTGaXIFRkp4feC97sDMntKm3rKhIyB3IDMLkrVTyTfBt5/K1V+zOQ8zMS8JP80ZnY3zlx1ABowZZqbfJJJMtk5pNksdRpFZPFeNHdzc/sb+z3A7F5mm2Mqn37kRGReINSmaPIWyiKd7fIk705lIOK+B+8+mCo/VnLGfpa0h46VzQ00Vh2ABkya+PxmTUQyk4kiHwazRVNzkIvIHJD8Fogs1IBpf7GKIa8BuT2Z/biO+ovkH4GXoxv7WYD8LZitkBo0WayASH5X64Ijq7i4yLtpJt5aRVfax+AIqAMwOLaV9Cwib4Hv3KPlSWeC05hNyOy8FNAiwt52v41T5GsnQ3MraENa4wdrp9t0ConIghD/Q4hbrM56zlI3k50PcCOSkqK/SL4ZvP9BiuzYyZiJEJdz29jZ3SCD1QGo+WSJuAPg3Rdqrubw1TPZuaTZNHVgEbc3vGvmkqSx3wLMjmV2OKRyGYScSAiOk+80NreCsZ8ibXI5YAkOj883HATLRvdp7JdJu1+jbWi58uoA1HyCxbs7Gvs2NTC2YctbFjKOPZQyhIgsA5/fAIRc/w07TChjbPZPfSOti3XNLqrEZ2GykEo66e21F6R7FyBz1oV/LfSguZ8me0stdFElZkpAHYAaXxgishR8J+kmVGMzqlfN2F1Je3xKx91iLvkvILJIinytZIz9PGmnXJNeRF4LuHcADH8LQ2Q+wL8eUqSUngDxb8D8E+QDgNwByC8BexXJR6fCo/vZxR8H73aZSj8jaduNB1g2NaGNiNsd3h01El3rPKiZWIbkL+us4jjrpg5AjWdfRJZ7PgPA5+DduwGZrcaqDk812jtAE74tJqVwFXEnwbsdh6dgRSOVTFDzwlFF5FWA3woim/WS1pSsH0EH8laQ3wXMGSQf68eynhMQouWbl23R2ONJm5T1r5sgKP81RDTwrbhQQk0OeyXAL5K8pZ9rR9sMnoA6AINnPOURepXq1gS4IbzfDJDmbmGbKg3DtciJy1O6EZHV4DtXNy6AspunfpN+lv27W/L83vB+6+oK1/AZGHMaYA5mSDxU8hCR/4G4qyB+pZJNRy0uMFyTnLgqRRGRzvvgQ/rlcT3CVkpzNiA/AuyVqasn40qrDnarA1CHWSihg4i8AnChXv1W8H7NEk2bL2qy80mTFGwlIrNB3O0Qv0CjDKe9HTShmuGTZfTuXhd+f3i/GyD/U6ZtumzhCBwNmIPKJh8qPkNI/nOIhIJDzTnI34HZ20g+k6K0iL8QPn9/imxrZGh/AeLrgPle6hbK1tjecEPUAWjwBIrICoAc0Ctj2/K5DNnaisC/UA45eoi4w+Fdco73aIdDEeDTMNnSqTZOU0lEVoW40yF+vuGoGaoLZtuQvKHMeIWevnNN48pZG3swafdPsVVEFoXPb292lskUS0MESXYhwC/pEn8Sr1oKtfyhUUvmlStVRLkXsQL5eo1b7k6lYezppN0mRbyX7S/kas9S5GsjY+wnSHtcGX162xu/PPyHKjswIRtheg79YFczS1oHW7OlGAIDEw4R9x14t2WCaBNFwoM/5Er4AslQYlqPBhNQB6DBk/dC1btvgv44iFuyRWYFnybcgN9K8r4Uu0Tyyxv3eYTmZ6B9Z+p3/942u1Pg3UdTmAxMxtgjAfOpEnqHeIA7IL5Z28NMdglp1knhKCILwOe/bZwDGjOO9teg2ZXkz2Kier4ZBNQBaMY8JWspEt56i0ptBzU2JesLrTX266RNiuTvFvrxP0oGVg/BUDwl7Du/NUWdbmlef3pt3jJN2JJpPpHuBOSbwPtzUmytlYwx7yezi1N0EnGnjtw5S1E0SaYoNX0gYI5P3X2T1K0KjZyAOgAjn4LBKCAh2Kr7XbjhJYSZw2QLkPxDjJSIvATi7mxc4J+xp5E2+U1exB1fu731xn6OtF+MzdG08+LzayF+1VT5Wsh1AwKXSMnI2CsZ/PvGxwIYcwVgP0LyL7WYA1WiUgLqAFSKs9tZd3kW8wJ4DZC/HGDIEBb+fQkgjwPwgH0YwB8BPDwor7q3B3s3eH94I7PgBZjGfpe0W6RMk4jbGd6dkCJbH5kiuDF83gj1HqKHSL49vD8lKjh8AYExm5HZuSlD9wICr02RrZWMMTuQWRJ/Efd9ePeBWumfrEwR4xGyUIZv/T65WQnBIncC8AYAbwTc67pxLJwDkOcAPNm9V2ZhN8zfAPyBpCvRvYomEFAHIAHSZCK9i3gFwK8O8G0QWbj7BiovTeuaHdDcBeJ2IPyZGwHcXKVTICLLQjrnQcIPrWGHmQjZ2H4R07q71zy/p3HbzIw9i7QfitnXcyyXeH6L2a3p11ZKr1XK8HGY4g05KVdAI6tcEn8EJxYi+WyMnIgsD9+5OSZXu/PEH8CJjavM4CcS7of5yoBZHsBSEL8kBAulx0nwWdDcAzKsqtwGmJCb4ZaU1Zja8a2RQuoA9DEZIjI34D8IcH14twogs/fRzSRNwo3UXgH4SwB7Lsl/TbX/Il+5uPMhfrmp9jW09jRX02RJnzBE3B7w7sih6VbVQGbiHSSD0zfpUawqibse4leIyY70vDGXk9laKTqI5B+G92emyNZKpsRuDfH5TyH+nbXSfzJlaG4G7YYk/zpVnUVkHsBvCnBteLf6AO6TT8HY6wA5HzDf7zdb5VTtbHJ7dQASZ68beOXWBcxH4N37h/cWFlJqmvMA/y0gC/nZk8qUzsysbkZBOR0+T66il4hnMGLGrE9mF8Q67yb9yR9AkfO+QQf5O5qJpBoFIm4HeHdyI6wzZiMyiwZi9tLnPowibXGDDvJhMJs/JTlQo4JSjf0+YD5aNsnT9DPXDUJ2awNm2959MizzD+EIBZzshUVwLOxFg/psMQRDhjqEOgDxN68JwH0IIvuMPM837Z2gHA7YM/v9HtaLCzix9vnxiT+BE/Ol2CnidoR3Jw31l1PFYMbuR4Zqf5MfxfKpdO5pzCecsEzLImlTtF6DiPsGvNsuxqB25435GJl9I6ZXd+Umf7D2n6ZMyOdgPt7vC0b3U2hxn9wfIgvGuAz0PM19IA8HzKkp1+BAdal55+oAzGKCug9Ktw0En4P4ENBXn4O8G+SBZPaDfpTqOQHHwLukQif9jDHlNsYeRNrPx/opbJH8rmZW+5sI38vviNvodoJ3J8bkanW+GxAY3eon0nkvvFxaK91TlOnuCFg05U1TxH0R3iVlEkwZunIZY0Ma3536efj3Vka3hfgDIHhT5bpNpUOaB0B8HrDf6ce2qQzdlLbqAMxkpkRkSYg7AeJXnvpE8rFuIRX5ebcvLgfvt6mkdrgxVwKhNC7vLqtnzwkI28l2Ltt28PJFZHx4+/9TbKxGLbFObwz5Z5qJpKBM8e4XELd0jEWtztNcT5OtEtOpeHP0+aNAqGXQsMOY9ciQDnfyoyjQ5DshiVXJioyxnis4b0LmSbNbPw/IIgNp9z4ZAvumeAzwPklzHWh3SXG2p2hE45qrAzDdlHUjVf2X4P0e6dGpk8w5zbWgDVXd/jG9lIi85vlsfedBfPQGGb+i+ByMOQQwISd3dMn1BXoQkO/D55vFxxmihMkuIs26KSOKz6+G+HelyNZKxthvknb7mE4ishR857aYXC3Pm4mQvyGavbGRmRsDcJqraLJ3p7AX8ZfC5+9NkR2aTPeb/4fKPvyLHTfwh/VWEKfu1AznPhm2NYaslQeQDNsM9Wht3vg+prZI3BH27Ypfto/mL27S3S605Kwi+EVkTkjn9sq+63ZTyW5BMuQWSD5qWarVmA+S2fdjRkjYcuk7IT978xxZE4KtstPiNrrPw7sDY3K1PG/sZ0l7aEw3EfcFeHdATK6G5wVmYuGUHA4i+Zbw/ju1sYHm56BdrWzJXhFZBOLPgrilKrFl+PfJW0C7OckHK9G/4Z0078Y5AOAi+cbwcmqlqXON3Y20x06mrojbHd4dVZ1J/CcMtySzUjXJReTVEHdTPfKzFxXxXptSDlfEfQXe7VUdvyH2ZCaWI9n7LDTrccXnN0L8ikPUrLqhaK6lyVaLdSiSrwPvL4rJ1fK8sYeRdp+YbkW5Zp8/AshsMdmBn6d5ELQh9fQjZcYSyT8EL6dUup1vNPfJx2C4bcpOlTJ8mig79g6AiPskvPtq5W+RJh7gJSJLwHdCAqAKj5A6N0TzhsCe9ENEln5+ifLGkWcMNPYHpN08pnk37W/+JxR7jRt3hNz/ryT51OQOorwMPn+iuelkwxbWbI5YspZu8ZxOUibE2s10eIgye2PMxqC3iD8PPt9otDaE7XLZSmUr+Ym4feBd2LFS7TNjZPdJeBj7SdIePdr5GO3o1U7maG0pNXovCO5QePeZUg1Thc3EG2L5s0Xkf+E7D6V2WUrOhO1lZv8y3/dE3Kd6zlCpoSoVNmbTlHSy3VUbn5R2tlL9quiM5kGabL5YVyKyHHznlphcrc+biaVjD5vCmfP50411dIzZgMx+HJsHkfyD8P57MbmBnjd2T9Imrzr2qk6GYOGkYlyldR/9fTLET+1X5j5Z2sYaNxhLB6D38D8Z3n1sYHMz6gs7GGbsV0n76VQbu1zkYvj8faltqpUrlv9fk/JdstF51mlupcmikdMi+UfgfTROoNo5qLi31O2A/rk/VhYPU7EJ0e6M/R5pPxyTE5GXw+d/B0IQ3QgOEyoZct3Uh13vPhnyNGw7MG3rcZ88GTA7p3IZGIsRdDymDoA7HN4lPxj7mpc6XNhdJyBpP/00G0XkdfD5XYDM1ZfdU2lksotJ8/5YF0VGQ5//rdJvkbFBqzxvsktJs3asSxH3GXh3WEyu1ueN/TRpwye2SQ/x7tfP74xZMiZXz/N8qhe3MuknnaC7SP4TeJ+UKrlaW0N8UFF0KhTWSTpE3Ffh3aeShPsVqs998hDS7tuvGU1tN3YOQO+b/xEDm7BizylOBMK37Hj1KhF5J+B3gPebDOzNwNg9ynzrEnG7wLvjB8ZoVh0n5lgXyTeH92cNXb+qBkx+Y3Rhq9VgPlFVZUusH2O/QNroLoZGFgaa3vbkT1duT3j3tRi2ys8buxNpk1NJi7jPwbuDKtej26Gg2PqHkwB7dlPvkwNiM9Rux8oB6H03DtnJqreb9tegCckmbuhnBkXkzc/vQjhyMEFCITAQa5MTV6ToVmT3Eheiz6PL1Cn9JcuYiQVJ3huTF/E/qF3ugpjSMzwsQipnu2WsiYg7Et7tEZOr9Xljv0LaqBMjPr8W4lettS2TKZfs1Mlb4Tt3DdXO7pa/FVKyFhZPZ8k3hPfnDeg++YvefbKv2JbB3idDYKDZmMzOH+r8jHCw6h+EIzRmsqGLff4+/2WlW/26A4Zo0gMBc2jZRDwz07eb2U6+DcgrK0VJPgpmy5O8P6XfXgDaTUPLXkbeQzOxUEy3othI9zvqnDHZ2p432bmkiRZkEnGHwLvoFrPa2hkUS90m13QHAMUS+zxJb7M+FK4aWnrxsOMkPPyjW067D39Z9PkYoJuqz8wYsnuafQBzZAqj2DU9sPskQkbCLASujkWegLFwALrFVNzPKkvy89+rM3z741Zk9sPYBVvmvIgsBnEXQHw0UrxMv+i+CYQtQEkZA0X82UOrHGjsyaTdKWaPiKwK37k2Jlfr8ya7kDTrxXQUcfvBuy/F5Gp93ti9SXt4TEfx7jcQt3hMrtbnzUT4bQWnedJDxJ0K7z4ak6vkvLFnkfZDKX11k4Llv0BwAio9+G8Ybl42P0lMhQHeJ0NJ5HeOQ8bAMXEABpEwhh0YrJO6rB67mF94vljqkpAERl5ftu2k8sbuT9qDU/osfmDdPAVTT/cZG9CYrcksmilNxH0Z3n021l2tz9P8jCaLLneL5FvB+2/X2paYcsZsR2anxsQkbIcN22KbfKTGO0i+HbyPVhKsAEV4+38byd+k9CXiwrbovVNk02WKvANrkvxZept0yQHeJw8lbbPvMwkYW+8AFIV9fP6LSnL7Tw/UmO3J7JsJjPsWEZG3IyyNQl7edycvahhqB2TLpt8UhrQKkJo33rufP786skx1PEbQU2IhIBFZBb5z3Qg0rG5IM7FyLC6m2G7WzQMwmu1xVVlLcxNNtlKsu14K69IFvGL9vuh8ubf/FeDz6yvOxSAwZgsyG2jugwHdJzsw2dtJ3lmae4MatNoB6JaKdddVU9Vvulkt8cOa6rUg4j4B746Zaj8ztE+s1BbaDKUYDfkIzcTrYjb29lE/VrkzFxu4+vPhzexlJJ+drOte+thgr61ehaH0GHLlzzWrehjTNBCR+eA7SbEpQ9G670HCqmA2ZyyPRa+E9SMIRcEGeSRk2ev9xg3Eh4qTb6tUHWO/RdrB5RCYTtkB3SdDMbd3tTk/QMsdgHwbeP+tSi/qbpBI2E9bKo92vzr0IvJvgPgV+u1jpu2M2YTMQqRv9JDwZiD+HVHBfgVM9iPSRFOkinTeDS9JOxn6VWVo7cxEuIaib4Hi3a8qvzEPy0ja39DY6N5+kXxdeH/BsNQa6DiGq5MT18TGEPHnPx+UvH5Mru/zNNfRZO9MaT+QT03k38HiPvloig5TlRngfTLp0+RU9R9V+9Y6AEWdcXG/rzza1th9SXvIMCdsIA8+8vdgtnhaDvMBZ6Qz9kDSfiHGVMQdCO8+H5NrxHljtiGz02O6igwhaVVMiX7PG3sEaaPFmkTcZ3t55vsdqT7tEmNsRNxB8O5zA1PcmBCcfEas/27gX+duCN4cky113ti9SDu4fCszUWYw90lzH2gXSQ2cLsWoBsItdgAG8dDiMzBF4Y9/pMydiLwW8LtB/Ea9H1hIgPEgiB8A5hiSjyf2Q4gPUdKLpcgny6QGaInMBp//GZC5k/suI2jMRimVuUT8JaNLU1zGoARZY79O2mh+dRFZHr5zc0KP9ROpy9vwMMkkZ7PMN4X3Zw9GNT4Ok4VaJE/H+hdxu8K7SauWxvp48fkipff/I/lYStsG3CeTnKkUW+sm00oHoLsclN+FUC++ysPY75J2i5QuRTrvg8d3Z5lSl3wYzDaNBUhNG0vE7QHvjkwZO1kmcYk29CfiToR30W16yWNPL5gcANh5GCFVcRsO2jtpbHTbW+978e8gsmCjzKa5F7QLxb6f9goB/aP6fecjokX+hWbiDbHRRWQh+M7vYnJ9nTf2BNJ+PNa2d5/8LYIuVR7Gfoe0W6d02Yz7JH/bWy31KTY1SaalDkC+PryvPpuTMaGGdDSmQERWgs+viZfWLXKIh7rcd8QumsGUDg4b/LgmOXFlfPzg0MglMbny58Me4aJkrEzWVkLAlO8k5zEvr8cIWiRnPhzEW9qA7U3d/y+dd8HL1QPWZrjdm4mQEOjvkevZ9Eo9z165coZrkROXx/oVyd8P7y+MyZU+n/x5q0n3SbMemVXPqjTcahu01AHw58LnG1eLKjwsJ+Yn+UD0hy35b5KTadDcAtrgBMQegITkf4PIqyu1y2Tnk2bDWJ9FMqVuBr5XxGRLnae5hSaLBjiKdNaEl+hNrdTYoxY29rOkPTSmRrH7QUL2uIrnPjZwv+e7WSfDb+WJWBdDKTgTU6Lq84bvJieuinUr3oXI+6VjcuXO81+9jITPxdqJ+FD5M1qUKtbPi86biflimfR6qw9Nuj1J+2wAACAASURBVE+eTZoPlGZR8watcwBEZG74/C+AvLRa9nyGdmK2WJ8inTXgJfpGPUM/CXulg7z4POwGiO4zjuk44/kiL8BrU+IRBpKDP3FL5cCLOJWDVo007S9o7LIpnQ1km1PKwP3IJL/9SwbJ/9SazzrTWCUW3xLx58Dnm/SDeJZtkn9P8mr4/OHqt9S29j4Z4r9en3KfrHQ+B9xZCx0AtzO8O6FybsnJW/qoopUcOTygrUPJS3b5tvC+2uRHqbniBxmDUPnFUqLDbp72aGGU7q6W/NcQeWuJ3ocvSt4FFrnUJ81xUDi0MqBPdcO3esYRjT2etLvG1BAZQIbS9N/yx+D912M6lj7f6vuk3ZG01TMrDbm6Bi10APyl8Pl7q0PU64n2dhq7VKxfEXcsvIv++GdcAbAnkXbnhL6/Be+2icmVPm+yi0izbqxdt1BIp9rMWIllSkUGNK8xowd9vlRgqSzXy9Y2MWi1+uw/JDhaheSNKe1F8svg/XtSZBslk7wTwH0c3h1XqW1mYmGGLb6RY2Ds232fvJg074+xbdL5VjkAvYjifwJSfWANeTfNRPTtS8R9Ed7tX+oiSH4AD+ibHfifXgazSb8b9lK2Br7VVeIzfB858ZMYL/Fhr3LFuzpigw7lfJE9Lnwv/3PKcCJuX3iXVMshpb9KZYzdj7RfTulTRJaF79yaIts4GfK3NBPRgjoi+Trw/qLq7Cu2/82dEE8UtvU+Hg9S7kOzdt8nQ8By4JtUTK0PekNv0jYHYHC508l/0ExEU3f2F1nLJ3v7Zv81qytARObs7cWv3rkJg5qJd6S8uVX+5mAmQjKiSVcVWpMrflaTa+w3SPuxlF9/wQL+e/Bu8xT5ocmY7ByAH4g9fKbpI+J/BJ9vMDT9hjpQ4VDPHmNR+c4eYy4js+jqp4i8E77z04Eg0fvkQLAOqtOWOQDuAHgXzSjXN0wz8SqS/5ysfbEKIZ3fl86sZeyJpN1l1g6AOxne7dC37rGGxn6GtF+JiVVeo95MhMCav0aYtm8L4AwGh1rpReGRxKptMhvEXQzx74rN11DOG3MZYDcg+UzKeNLGrX8vNNxMvDqWBldC9cNQBbGqw9hDSLtvrLuBZ15s930yuZpqbB7qcL5lDsCAtv9Nmylj1kmpaS2Srwfvf1S6jK6xRwNm3+kzeImEzxk+lOksF1dQ9upKzsefVxk8FIrFvDSWjlhC4Jvv3FXWpEbJG3M5ma2VqrOIvAxw58P7NVPbDETOZJcA3ITkf1L6FxHbKzwTjadJ6a+2MmYipI+dNNFP95NlJzhN1dyHEyuUivgfP18hdb2BsWv3ffIc0mw2MHZD7riaC2/ISs/yLdm7OypPlzv9YMYeRdo9U8wVCQ9KOR6QcgFbRRENExLuPAzg9RC/zlD2fyd/t6xyPz4fp52YK8ZTRFaF71wbk2v8+cQb+DQ7i9wM8MfBu+1HYrsJEdFm15gDN71uA3/7HAmImQyaurXXdZ6oLLdGcv6BTsgsWW32v7G5T6YVuKrLZRjTozUOQPFm4fOnqt//Px3CbvreN6UGgRSldCGhgM3a9a91XtQ5CN8tJ013KSJvge/cG7uwks7T3EuTRVPciuQbwvsfJvXZaKEiM+TbSJbiK+J2hPdHDCT4daY8Q7AZdyWzM8vgFpHF4POf1/+3UMaqWcgasz6ZRSscis/vh/j5KhgxNVFZuE8+PZAAwGlG6H2ykukcRidtcgDmh+/cN3BoxnyIzM4qM05RcQtFta25gHxOwMwLYMniG26d9nWbiTeT/ONkthX70bvLlqYMg5k/R+yvaGw0E5pI/lF4f+qUx2tCBzQ3gHZ1ktFMbjO+Wct8gDsJ3id/RugLhwklpLkHyT+VaS8ir4TkN9Xqei9jQFnZ1P343t0GcVV8DglbMP8nthojIvPCdybNZlrW1JnKt/s+Gc10WAnDIXTSJgdgJfjODQNn1k10Et7SOlWMVbwVwW8P7z82vDe4Wb21FHu4r4/ZJa7zZCW60txMk60YHU/cLvDu+Jhca84bezpp+8r3INJZC8IvQvzylfKguQYMZZtZ+lNMkfYVEqL+B/fduVJjK+jM2J1Je1KsJ/H5LRC/XEwufp7/pp14ZUxuaJ/T2n2fDKnbm1mh8wUXSIscgM5a8BLdTx77gSSdT0x1mtRXT6godgP/ZXi3bSVv12UGnyabvif/EYjM088QM7ShuZYmWy3Wz0AqIcYGHfX5xDoBs1JTRN4B+BCwuSkgL+/LnG48yrmAOZnkbX310a0keRS8273f9o1sl5oO2OfXQfwqU7aR/CvNxOtj/Yjka8P7i2NylZxv733yPeTEFZUwGnEnLXIA8k3g/TnD4RmStyAksIkW/CirTzc5iIQywnOUbTtleWM2JbNzY/1U9t3SmCvILJoJTsTtDe+iRXNiejfsvKD7EDlmKnp3AwXzlQHzHkCWhsjiCNvPXnQwR0hGRPNbQG4ETHjT/xlJN7Xx3Rfg3QFT6aORbVO31fr8SohfY8o20txHky0Q60ck3wze/yAmV8351t4nNyazVsQktckB2AbeR0v1VnNhh174T5gs5HEvFbCVMn6RIETc+ZUFB6UMGmTSv1veDnFLpHY7S7n0lKn7w7svTnm85nUQnIBPkfbIKlUvtp8V8SiYllTqKQCPpga3pujSS1gUHv7lsmKmdN4EGWMPIO2XYqpWVpEvOQVvrvfJ2KTEzifeJ2Pd1OF8mxyAj8D704YKleZe0K4VKxHcj05FsI6E74Ph08CQDmM+SmZRhuJdVQ7AJaRZJ2adyIATPMUUGPV5Yw8GzOdiOzRGrea08UUkA3xIXBU+Z43noQ7A/817++6T25DZ6W24sNvkAGwM76PL15VPGvkIiC3IiXIlgBMU6Qbs5FcMdMvO9HoM+xMAzVU02btjKETcPvDukJhcq893E+5sQfKxOtvZjWVx3x15gqJRQ0r8/i0+vwriV5+yuumfADaF92dPebyyHbTrPrkJGXbDNP9okQMwxCDAF8+7h7EnAOaAqutFi7jd4N3RQ7nUhh8EeD1NFg2AEnF7wruvDYVBnQch7wGzrUneVEc1RTprQvBtiESD0eqof6U6GbsnaY+K9Sk+vx7i3xGTi56vYxBge++TGgQYvSCHLCAiw9kGOKldIUGKOQ4wp8T206fi6aVOvQXiovvlU/ucpVy3lOswtwH+nCaLboEScbvCu2OnbF87OghxAacA5lMkn6yDSSIhYNUfDu9CQaPWvFRMia2xu5D2xFgf4t0vqvltJ28DHFzBtJix/z3f+PukbgNMnushCYrIcBIBpdnjQXMLyCsB+TVgQ+KNUEQoBFrNsuLfrLru1Rb4cdrQU5AafiKg39DYJWMaj1UioBiMaedpHgRxIGDPnGqkfuqQL5QrkkLB7wDxBw41VqVfhYfZLjFQTLz7DcQtXoFq9UoElGZQU++TmggobX6HJzWUVMCVmMPHYMyPAXNIrFjItOGKiGrJQ/7uaNrc/lWsdSrgDXrFlfo3r60tybtBHgTYc6qM4p8MVzezpd8a4vca7DXZ4ElLTwV8L8S/pRJLzcRbSN4fmbvBp0yvxJja3idDqeeXNyUgNzYVrVquk0EXA/q/JSyH8B02fJMF54J37wQkWtRmxsngczDchcy+GZukcF7EhZoCn0+R7UtGiwH1ha02jci/gOY0wJxKciApsYuqjPBbQfx2lSSCqg28ASiSXgzoX4BEM/glaWi4ZkowsvjObyGySFKfUxJiB+TPQP4B4Gvg3Wrlk1LV7T6pxYCmdEkMsrHIgMsBB+VpbgLtRxnevHqHiMwG+P3gXajFXcapEhgTIkqjSSVEZEX4zo0D4zeacsChgEnIX/5s5K1lMfjOHQOzvV0dS+/z08WACRnfftXvJ4Ludj4sD/j3QbAOxC3TLlQDtMZMvHX6e8TMRipWUnwnqYxykqbGfIzMvhGTFfEhLfMGMbkpnTfZTwDuMH0sVC9W5BB4t3PJvut0n9RywCUnb2jiIm6wCWNobwNNCJQLiVNedIi4z8C7w0oZ3K2cteCs+pzOych61Q5DEpfqj9RtS+LCD3ifyhQwE/+P5EMRB2Ae+M4jlY05Vh3xKZC/LP6A+wF5ALCh1HS4hqc5XrMBeDng/hfgmwAsBJG3o1vN8mVjhasqY83Eq0k+Grmu3wjfmbT4Vil1jD2UtJ+NtRl4Zk1jrgTs+2b1Saqv1ND1uU/uR9ovxxg35XyZt9Xa2yQiK8N3fjYwRQ1XJyeumVX/3Yj9/E6ILFxKB2O2ILPvxtqI79w1sGpqqUuWkl8B76N792O2/Pe8mViG3YfTLI8iBqJb6jk8qPRQAjUnwKdoJ6L1F0RkWfjOrZUZk5xae6D3SUF39eN3k9wnXwbJHywdOFqP++RKdd2G28911DYHYAI+/2f570wJ6IrCKNlrScrkD6s+3pCNPYm00WUx8fk1EB8tnpNgzQtEigDAOROW4g18/lhl3yyDFoZrkxOXxnQW3/m9BpzFKOn5WhCgvZPGRiP7u3U//EXV6cx/wWRzxwLUivoQPn8cKMqUV3sw7Ru5iDsd3m1davDR3yefgMleNaxg21Js+hRulQMQGIj4S+Dz9/XJY9bN0i/sHeDdyaXGN9m5pNk01mZgtiXn5JfF4Tu/ielZ6rwxO5DZKbE2IvnlY59dLgZJz9eDgMkuIs26MWVEXPl7RaxTM7EYQyneyFFZDYIXjmOyn5Amev8VcZ+HdwfG9JzhfPp98mL4fO1SfacIm+xC0rSqpHULHQC3E7yLJuBIme8ZZIg/0rzkzbF2Ivm68P6CmNyMF7b9Oml3jLURn98I8SvG5EqfN2ZbMosWUhLJt4P30SCjUuMbezhp9461EXGnwLvtY3J6XgmMnICxx5N215geIi4kT/p0TK7UeWO2I7NTY21EBlQUiOYmmmyl+PhuR3h3UkzuBffJk0m7U6xNZdkVX+TcpAVZxvSr0/kWOgAyF3z+MBDKoFZ58GnaiWnV02bZsYjMDZ8/AhQR1GlHchGe/D6Inz+t01SpULIzex3JkKho0kPEnwOfbxKTK3XeZOeRJtqniPskvDuiVN8qrARGQcDYj5MhNXj091R9NL7JkqLURYr75F8rrzNCcy9NFs1XIiLld/YYszWZfSfK1XfuLh2HFesUxWfScJ8sncgt2vUIBVrnAASWIv5s+Dy6pF6au5l4A8N+6+gP230b3m0VkyvOh0hhZvPG0rp2twwV3+2qdWwSl7V63w3/DsgrkuxKFUouYzrSWg+p1qicEghbW99F8qcxFOI7IWB40ZhcufN8EiZ7DclnYu1E/Pnw+foxuXLn0+KJivu0z38K8e9M6p/8G5jNn7Bb6iW9OKVqd68Y+wPSbp6ka4OEWuoA5OvB++pT5xrzYTL7Xmx+RWQeSH5bUlEUY7YiszPifXbeBS9Xx+RKn08tACT52vA+7Cuv+ODTvcxakeBKeQN8588VD67dKYHqCZiJ8AD+x2Qdi0gIqH1yIDtbUgNrpfMeeLmscgBmYjWS18b67a4C5DcDEltZDXkAPkBm5yT0OZidYMasS2YVBmzGLBnO+ZY6AGIg+R2Vb5kz9hukDQVPokeRNU3chbNesg9L72Yv0h4T7aybCfAgePe5FNlkmRAsxGzx2M6GwlsXdyK8i35/Sx57ekEzEVZA/hBrK67zKCBzx+T0vBIYGYHkqnwyH3xn0rS9fdtgbNq38iLFuA+1CBbre6yZNTT2INImZS0VkdUg+TkQefXMdeCzMNw1JcFR7z5VfS4Y2jtBs2Rsd0WlDIfUWSsdgO6FkG8N70+vlmOxzeaNJP+d0q9IWC73u0P8FhC8EYAH8TRofgKYr5JMiqjv5hfo3AdBNAgxRa//yhi7I2m/HmtTZDr0+UPl0x3Heu6dN2bjtGyI/lL4/L2JvaqYEhg+AZOdT5oNYwOL5JvC+7Njcv2dD9X2svC58ulYe5H8Y/A+eg+I9TPDeZoHQBuSm7mUdiLyWqCoK7FJLzeAgHgKDJksi/vkbxP7sRB3D8TPlyKfLGPMlmR2ZrJ8gwRb7ACEh6a7G+IXqHQ+jN2VtMdX2meks4HcLLo/0kVIPhezZWARw9MGNvZg0u4f16OPrUOxTmt/vkiTHLL5PV57Vf+roLcQhvz2rwTENkfvCjQ19rOkPTTWk1SdUfOFA6ZWIwwVHbvJy6KBezGbZjhvzIZkdn6pNlMUFsk3hPfRtOqlhqG5r3efzEu1a4hwax2AwH8gqwDkn8Fs0dRVgKleB0U+dvGhZni0bG6psYz5IJl9P6XNwLYf/tcByC4lTXTfrgwsDiGFwqBkmPdS9f4awO8B+R1gQxa1vwN4IvUtalDaTbXfbuVAhICsNwFuQYALAVgY4pet/BPdVJWton0kW+i0IQae14LmBpps5RSTBvOCUaRNX25YSXOK0tTd++QSKTYnyyRmH0zur2aCLXcAwjcuFyJNV62Uu7HHkna3SvucRWd91ReIKUZzC2hXTPv2L2+H70yaqjc2XPQ8+XeaiXlict0tlp3/3965wF8zVX3899szf12QVN7eCkkouSQldJEKKUpEQqVUcknekEgptyK6SRcpSbnkkpR7knKpt1wiVLoh3d63yC3e/rP37332nHnyPDzPc2bOmTlnzpw1n48PH2fvtdb+7vnPrNl77bXii9H1a9vq3/MSvu4cQJcCyWUk7261vQ0ZJ+k/Ab8hwA2h8JpSQbMN2VKP2PxI7dIlItVjee//hfT4evQuRIqbWYtkdCwXefXKjfsra88x4pJ9yeTIfvrr+F3y+yP4enP0030fTF5e5jlZxxjGIaPTDkAEKsXsddk1gGZqBBzg3KvJtIGo+AetlLQ2QnZZvQVZ8ofUuiSvLcNjJBUWoyFu5mkkb+lnk4K/BvLP6deufb/zDjh3BuDiOeYruvxQGYR9HhUPvCAvNxzCdrUfNx3EqKp96C6nS/t+bEhaEWG2kZLN85lcMidA8Zx8NkL2k3rzAuQnfDYgeXVVlFXaS3oBQva9elMbxzLEaXSgSsUfVLG3TW077wD0bm5/BILft17w+XnbeNylka9jSU+FYuY/PalWu11yMJmUSsFZJOu4fiRf3KX3LJuYy1oJzy+MyQ2gjgCSU0e1HNrgaEYiugiefScU3gPpySNRWocSl3yITA7uJ0rK3ooQ+mbr6yenxO+xMM9zyqwCFM/JAxH8QSXklm9C/gVMYwGdvs59eaHzfSQ9A8quqH01xSUfIZMDBrFpkvpMiQOgxSB/GRSeX+vk9AoEbUnyijrlSloF8ufWHsDI5Lo5kbXPLxP413sgNJD5b2GgXHIimezYj6M0uxGCvtuv3dh/p/spiEOA5Bz72h9sNvLkUwg7QtofCisMJmWEvdzMC0j+qJ9GyX8dwe/Qr10tv1dbBYj76D+G/Nq16J4rpBdI9+q6v6YlPRfKzob0lJrt/RGYxI+72VrltlDYVDgAvZeZVii2Apaudx7yc6q7lsmlX0avNPtyBJxW/3n3/GhQXPq/uZwdWhdh9sqRfP1Hg8g/0s0s28+2IiNizAdQb6avforL/p5nLOP+QHJCF88Nl8VQZ7v8GCrCfghh33qXeeu0knfCpf/Rb5Wnt9+e/bH2lb2FDyWuAsR4n5+UGa2kpxdbATXn24hHqBnLnteSTEfKtkPQl+p/DsStujSumtxWhtekt5kaB6DnBOTHRM5s5KXm3MVAPCK48DrYi7pZJC0DhLhV8Zb4Oqz5xooxC68p+8eX78fKx8JD9a6Y9BuUm4nHEhdaR3xu95HFJfSzd/7fBRePh7oPcqKO7FUb5Dhb53vn0NEI2WbjtGOBukuvYOlZiCmAR3kxuaZY+St5Lj+m3cZ5jRzhdOnpAPcm+YdBEEhaqbgH+p4aGkB+fE5uQabnDNB3IrvU/aJpPQTJ74ngP9WMoXl2v7OA8Hly5tIyOvLlfoRdEMJOgJYq06dyG5ccQCalI2QlvzuCP6aynmE7lC6ikr0RIfQtCjKsOaX7977639p0UGhpezresHe8V5+v/+tvCHA9B7tvFVDJ74HgS2X/HMKah3etmL+k2eJbvL8IiD2O5GVlxplnDETYFSFsWW+g4jzaXbIHmYz+uVcGQENtps4BiBwl/xEEv39DTHtiSxQOyo9BhdlYXKi5eXDJx8lkn7JjVQw6DNlNgB5btk9t7UrXEtdSCNn/NPYgqDKg3srPm0n+uUo3azscAcUiOgqn1n7ueyCzqhTgyS5CCBsPpGaoTvkW4KqMQXklL8kfiuCbDYQr95x8MsLsH0uaPVgzlxxCJvWmWh/MkpH2au7FM9JhVFOW78MhfAHB71ytZ4XWbbixXSxJ6uK2xCIL7cwdVY+LvjO+Jdb8iOITSd7Zj7QUzp2zV/mqfu0a/d0lnwDce5vY6++dkUfMjbA4kC0OsObYlUbJeEB3A2nMb3AvgD+XmdOqFklaAlCs/Llp1b61tnfJKWSyfT+Zkh5blApfrF/bRn537iIg2bTs8yDaIPlPIPj3NGJPFNqO5+TnAbd7FS6N8Rix4Kl0AHo3du4EHNbYSsC4b2yXfApwe1W5qSW/D4IfSeKOhd7nZWt+K9sWIZw64r+Xf/tKcMl+ZPKxOvQrj2L2LwP4UsS8FdIzAMVUut254okZ8BcgfwboEiD5QR2xEnmdDITPIvh3jg1W6ep72Y4I4YSx2Zm/cJNYgOzjZW0onpOH13+MurBg/M/Jw4q4nVIfSWW5TUq7qXUAHvzqzWMCPlF7YKCbWYPkDYu6ESStiTDbN1NXxZspwCV7k9EBKH8VSYd+NPZldZeeRbqt+llenAb4U2MFihZqQFylYCwOclo/G/vM/bJAeCOEHSC/+jCyJrMvPeLxWeJEIDmD5F2DjqN4SR2M4PvWkxhUx8JvB/4JTJcvk7JZCmfPOYn0mtptqCQwX2V7Mcn/rtJN8rshhKNrDwwc73Nyz2nb83/onE+9AxCBSNkWCPpKrS8Tl8Sba5HBPpL/LwT/ySp/iItuy7vh8mC0b1aRmVfjkv9xO85a59nD4nGq+/qNodESxQtWHqOE30SmJ/ezbWG/51nLoP2L7YvJTmk8KISH9cuDwk4C3OEkB86Q10zCrz6DdMkRZLJfPxT5dkUvbuVR/do2/jvdLUUq8L9W0SVlmyPoa7XGB43nOXkHHHecpmj/hc2zOQAFmTxPgPypUFi3yh/Fwr8M8AdwJtaQXmAVN0lLQ9nPa0tikSeeSbar+gDNz1jLX1J7HvBhIDoX/zhP7CciTwQSZq/q166m3+Mxv13KlE9ekD5J60L+cChsWJM9HRRDD+dOBdwBJG+tOsBiJeBYBP+Oqn0HbB/P2MfAuhJHV7O3IISvDKin/m50VxXJbvqWDJ5XefGcPBkK69diFEf+nIxJft4wLef8+82ROQDzEJK0GBAOQgh711I7gO5yMNmK+f7ng1fxxX0mFEpV61r0JDKDczEYLZ4/71va9yF2xDiIkxD8dv1ulJH+TncpXfrSMjoVYhrQ8IIybYdq45IPkMlhVWXkjh7ChxHC7rUvn1Y1ZmLax1UgdyTgPkrm5ZBLX72YgDwwcMvSnQZt6NLzSVcqEFUhi0XJNhhUVSP9XHrGnLiMbasGseYVSnv3dEzMNHyNldE8J+MR7XhPfXgaMvyVvV/MAVgAqTwHvvzn6vmDjcdv3FcB/bSnis9HCDvWcuaf7gow2Y1kzNdf6RrJSYhKFs3XOH5ZrVxmNUPK3oAQThlcVYmeLv02wNdWCaiMUqXZjSF8DXGLxa7qBHqpq+MLqu8X9rzC8+V2Zf+NeFSwyctxU3Lmwn4q8uQ1YTZm4Gzf87biSaGHcI7Pyc9C4SX9GPT/vdHnZKzqF6P8O13Ypz/jh7do3w05yCga6NN7QfodIBwEhRUbUDG4SLrfgTgISL5W9aXUezHlJyCOQfC7DW5Ewz1dciiZfLCfll4d8OyWxorGxNTJTGP9hNJBakVk+kHFCRPb5+83iYv8PZ6x5y5kelIVMb1CVtmPgXhUsIErL+mcPqvM35/k42mj9zdgRT0iXXIc4HapuhLw4LPEb1c8J1eqx6CapND9BsSBRSGuqYzy70fSHIA+hHplSv3rIH248S+KvrMVX/w8AnDH98s5vjBRvfGEuE/69n7qxvp7b29wxTLjlPzeCP6o+u2NdR7SdUj+vKzsXgEbfR0h27psH2tXgkDJYLt5JUkNZox07u1k+uV+lufOoLJba4v16adw0N9dcizgdi3j0CxIxTzPyYMgrTqoGbX0Y3IjqI8Bycllnh+16JxQIeYAlJy44gZ/FeDejOBfPbqiJPEl5M4GYvnQ9LuDeOlzh5gfnUP4CoJ/Q8lhj7eZc68nY+7wRV+SFoey3yOvp1DjVbK86zx8lwD8WQhhoxqtMFFzCbjkBMC9o8pDvZGjd8RtYL5F1TfmRspejxC+MRGT2IsJ2JFkpcDA+Z2u+IGRbQS4WPL4tSN8Tj4A574NKB4rPX+Y5+REzFVNRpoDMADIPKMXwusBvgbBbwBoyQHELKIL74FLvgfoAsDFM9J/H1a+Yl11+bOh8LxhZY2sP91P6dJSBYkk/0EE37cWe2nbe0u8a5UNQitOU1wEhReV1mENqxNwyXFkUjqDp6Tl56zG3FDr36iLcTfJ58sYr5DFolrrlWnbijZ0/w0mMd6ldMrghdkt6XFA2Brgpgj+5fUnt8qfkz8AwtlAcnqVbbpWsG6BEeYADDkJvYhYrAOEmMltLcTiPgoxk9sjyolmBrpfgYgJga4DXEzQcWWdkaq9I2jZma1fhlwQMDfzQpKxLPEiLymvD/C7msooxyDEqLdvbfdoVB6HAH1r7KmJ+0Hqyu8V87ZL/t0I/tO1DJ+8HUxXKuMYSlq/KKldi+qRCemtcGxJ8pq6dPb+RrA+kDtDz4biP/lzMj4/S1x8AHQ3Iy9nrmsBdwmAq6qsBpVQMnVNzAFoYMp72wV4KoBlNfSG9AAAIABJREFUgOwxAGOVvyUAxv3hmOdeQBI97FgS8091vuznHU4R7PduhPCxsWf4G5SzS88kXan99NpiAVx6Bum2KWuy4omR4Hct297a1UCgZK6IwkGL+/A35c75sJdzO5FpqfP8UjgDIXvdsCrH0z8/XhzT5B7c1HJ64RQ8GcBygI+1L9ireaF49PNeQHcV9ST+B8BtTdkxHr7t0GoOQDvmoXYrJC0H+RMnP/FMTA6TVzH7dT9IeR4H+V8MeWojwM08p+zRSinbBiEMlRa437js9wUR4H1w+emMm8rw6ZUQDl8t03ahbZj8HHTx3vD95EhaESGLX6tJv7at/r1X7TLGBcSqpXZ1jIA5AB2b0CJJx+4I4eD699zGBMvF447Jm8tol7I3IYS+WQQXKsvFyOFkh3K68of8tZ3hXGbQbWqTR3u755F8oJ9ZRTT+jb1CSwNezm1GpueV6S35ExD8jmXatr9Nfkb/w4A7pozz0/7xmIVzCZgD0KF7QdIGUDimHTXS6wSbrwLE4kp9E3nk2y/ylw+cqtTNrE7yxjLWS+Gc8ZVOLmPhFLRxyUFk8uEyI5WGqMbn0gtI98pyerQKQnZj+f3tMlJb0KaXmCkm1LmiBdaYCTUQMAegBojjFiHp+YA+WLyMujmnLj2ddK8vw1rSGnOqrl1T+QFMdxldWipdq5RtjRD6HlEsY6+1GYZAnqvh2WWyBeYnNUL2x+pFv8rriCNRrCkS/LbDjKrFfTWH91kAD2Fe2tmuSSbQzZfFJM9IBdvzKOPei7/Ul0kF0W1sGvfm1yZZqnyy5D+D4N9VaSC9Sn9f79enF2swezOUB3raNW4CJUtIFy/nAe6L5GAy+VCZYUp6NsJsjJ7vegbI6AjEFNnREbi6DBtr0z4C5gC0b04WaVF+3A1hewjvmHOu/zkTZv5w5rr0QtJtWkZIzklZ3PN9Spn2AO+AS59Sbj85extC+FI5udZqBATisc24CtA3Y2Pxgi7/5Zqnk01iVc/7y4xDCudNiUP+II48dwCOA5JvkLy3DCdr0w4C5gC0Yx76vfQXB/zGALdECK8DtPgEmN2Mic5tQcYvj/6XlL0KIZzbv2X8Xku+SiZv6de2CCar50hZP2X2e3kCLjmFTLYv00FhNs5fmXS1cdXpJSQvLyVX2eYI4Ttl2nazTUzM404DFBPzXFzWaeomi8kYlTkALZ6nB/f28yxaj2qxqaMzje63YLJamUQs0SjJfxnB79TXQBerzqV9j/NJ2WYI4Zy+8qzBiAnEc+vpcmUy2En+4wh+r74GuuTjZLJP33a9ZFCLQdkNkFYu0777bXg/XHJxsUVQVELt/qgnbYTmALR4xiQ9F2H2qhabOB7TXHIAmXykjPLeVsDs9RCWX3j7/OWxDMl/9JPZ8QCvfsNv9+8u2ZtMPtHPSGl2IwR9d5HteqmgY8xJyaV/vx+C/2g/3VP3e29rpnK58qnjNKYBmwMwJvBl1Spkv4ZCu8psljW+sXaxRGxeijVmUux7SXohQnbpQk8FlIz+L9IN/2V0BU76Ds0azEuAyc/okr5xMXnFxpD9beGlgvkAXLp+2Sj3vM5GyH5Za72BLswskxvpktW7MJSujsEcgJbPbOtriY+LXy9D2SZly5dK/v0I/rAFmuuSI8lk335Dsax//Qi14Hc3swLJW/tZopD9AAoLPvLpkt3J5HP9ZMz9XQrfRMi2LNt+atpVWKmbGiYtG6g5AC2bkIeaI2kthNlrW27meMxz7i1kWiq9a1HO+XyEsMnDjC19/M9y/o9noitode6tZHpCvx4LPSZaofZE1CFlOyCEvkdH+9nTyd9dXjL5N50cW0cGZQ7ABEykwuwvID1zAkwdsYm8Ey6NAYF/LqM4L08q/xMoPH2+9iWz/ynM/nKoVLJljLQ2wxEomTZayt6OEI6bTxn5KzBdt2xZWUlPLI6aPn44ozvYm+7HdOn6HRxZp4ZkDsAETKdkAUYLnSaXnk2615adxiJL4JUP7v/mWd6W6FdWVNKSCLN39SqW2dVaAuRNdDOr9bMvP2ETZmPp7eKK+e7zl//N/frO/V0KpyNkpSpVlpXZmXYu2ZNMju7MeDo6EHuYTcDESloWIbtl4iuLNcXaJe8kky+WFS9lWyGEM/KXOXEr3WIr9OtrJzL6EWrL7/wXXLp4CYfuiQizsSR3vA08HDYnZy4oO4qhi06VVTSR7fLaHTGp1l8n0vwpMtocgAmZbCm7CCFsPCHmjtjMPGp7vbJpgqNxkt8bwR8Fuqvo0nX6GWx7vf0Itej3EnvPedXMMBvrzju4ZA8yOabsCCSthJBdbVUgF0KsQsbOssytXTMEzAFohmvtUqVse4RwUu2CuyIw1oVnXh/+vrJDkvwnAK5Cus379ZH8vgj+iH7t7PcWEHB8KTlzaT9LFGb/BrrjyGT/fm3n/i7pkVD4EeTXKttn6to5tyOZDl6Se+qAjW/A5gCMj30lzUUls9sBPa5Sx2lq7JLjyeRtZYdcnAzYvExqYckfguA/UFa2tRsjAedeQ6Z9U/JK/gDAfaTsUdI4Iskfg+B3H+PoWq46D8xdluQ/W26omWcBTZN1D+RfrMG/Z7KsHrG1zu1MpvNHd9dgguQ/heD3rEGUiWiagHM7kOnJdauRsm0Rwql1y+2UvJI5NTo15gkejK0ATNDk9fYeZ2OUss3bQueNs3DYpMwScJWpl/yxCH7nKn2s7ZgINOAESnoOQnY5oEePaVSToDYWT1qJ5O8nwViz0V4kE3cPKGTfg8LLJs7wURpM/r04z/3butSaA1AXyRHIqXgqpJ9Fkv4Tyn6KeBrHroUTcOk5pHu1IZocAvYlOTlzlVsqZVsjhNMnzOzRm8vketC9sK765OYAjH4KB9ZYowPQC/rzl0Jh3YHtmZaOzr2KTM+fluF2YZzmAEzYLObHl+RjgaC+Z9cnbGj1m+viw4hbkJwdVrg5AMMSHGH/mhyAXpBoOAXBv36E1k+mql6Z7lVIhskcwHRabQ7ABM675PdC8B+fQNNHb7JLTgHcG4d9MJkDMPqpG1hjbQ6ABX6WnoOSpZhLy7OGIyFgDsBIMNerpJeWNvsDoKXqldxRaS75HJkMdXTLHIAJujdqcAAkfxCCP3CCRj1GU3l/cfTvjjEaYaoHIGAOwADQ2tDFjgRWnAWXHEgmh1Ts9e/m5gAMSm4M/YZ0ACS/O4IvnRlwDCNsl0qXHEsmu7TLKLOmDAFzAMpQamEbScsjZL8GtFgLzWunSS55P5l8dBDjJP8FBP/OQfpanxETGMIBkLK3IYRYV8KN2OoJVReP3aZx7/+WCR3AVJttDsAET7/kv4zgd5rgIYzedJccQSb7VVUs6bFAiLkALCCsKrxRtnfpGQB3JnlnVbVS9g6E8AV7+Vcg55Ivk8nbK/Swpi0iYA5AiyajqimSno6Q/RJQWrXvVLcf0AmIzKTszQj6vCWEadsdFPeh3f5k8ulBLJP8OxH85y3JVhV6edW/VUn+ukova9seAuYAtGcuBrJE8icj+O0G6jzNnVxyFOD2rZIHfi4uSc+CwimQX3OaEbZm7EyuBt12g76IisqQR9rLv+KMuuRrZPLmir2seYsImAPQoskYxBRJqyPMXmfLlgPQc8nJgNuJZCwLW+nKE8QgHIHg312pozWuk4Dgks8A7r0k/1VVcHHO/2MIfu+qfa19/vW/GslfGYvJJWAOwOTO3b8tl/xJCH77Dgxl9EOguxJMXsOYPniAS5rdBMIxkFYeoLt1GZQAkxtBtxvJHw4iQtIjgPAVWz0bhF783EhOIRN75gyIry3dzAFoy0wMYYfiyydkN1kswIAQey+TV5G8bRAJkmaAsBtCOBTQEoPIsD5lCfCfcO7Iooxv5a/+qEXS0pA/CwovKavV2s1HIBb9WZPkjcZlsgmYAzDZ8zfvKsBxCN6icQedT/KvYLoNycsGFSFpRUBHI2SbDSrD+i2CgEvPAfgukrcOyknSqlB2FqRnDCpj6vu59AzSbTP1HDoAwByADkxi8VWzHEJ2MxD3pu0ajEA80+z2JJMYDT7wJWWvhXAUFJ4+sBDr+CAB8mYQe5IzFwyDRcq2QtAJgJYcRs509+W/4NLVBw24nG527Ru9OQDtm5OBLZJ8DErbd2AB1rFHwCXHA24Pkv8cFEkvwMy/DtJhFh8wIEW634M8HHDHk8wGlBKX/FMgHFr8bdgzb1CQvb+NT5LJXsOIsL7tIWB/DO2Zi6EtyWsEKPs1pCcOLWzaBZC/BNNtSV4/DIpefIDfbk4CgQ+YI1CSZE0v/qgtz5gZg2QVXlRSuzVbKAHeCZeuRNJy/nfkLjEHoCMTOXcYlse8zgnNk8v8F5nE1LBDXYUj8CYIB0BhxaGEdbVzvtTPQ4HkZJJ+2GFK2bYIOtaKZg1LsujvkneT8dilXV0hYA5AV2ayGEe+3KnwM8iv1rGhjW84Lr0A4DtI3j6sEb2tgexlQLIzgn8tEFcIpvyiuwLEp4HkrGGW+h90gvO0zXE7bOcpJ1vf8HsrYjHyf7Y+oSZp3ATMARj3DDSgX5rdGEEXNSB6ikXyLriYOXD41YB5XlRPBsLbIP92CMtPFdz81IX7OuCOqzOZjJRtBulYSE+ZKp5ND9a5zcj0vKbVmPzREjAHYLS8R6ZNCt9EyLYcmcJpUeTScwHGAMHf1zVkSQngNwXcjgh+s+7WGYhn+JNzgfA1IDm/jq/9eZypp8xZ6v8kQmbH0+q6MefKce67ZLpJ3WJN3vgJmAMw/jloxAJJTy2SAz26EQVTLTSPDTgMcEcOkoJ2UegkPRrwrwS4NULYZE5egcdNNuoYOOYuAHRm8dIf+GTFgjgUEf7vRggftuN9Tdwpecrf55D8eRPSTeZ4CZgDMF7+jWqX/AEI/tBGlUyz8JgHndyHjAlq6r96KwNYDwivhPQySM9rf8wAZ0FeDfJiIL748eM6AvoW/PKf3Qhyn4D8GvXTN4k5AZccRSbvNRrdJGAOQDfnNR9Vnu9c4WoLCGx4kum+Dyb7kLymSU291YFsPcC9GOBzIb/22Pe6yT/NqaVwDaCrgHAZkMYXfq1f+Q9lKmnNOdskH0PIXtEk76mXTfdbMImBf43O59RzHiMAcwDGCH8UqiU9HyG7Esi/Ju1qjkCAS06d88l0CGPE9Igu5TkfsjUBF1PbPhPQKsjPvmO5+mIJ+E8QtyGvlcCbAfwKCDcD6fUk/zKioUaHdiUgfBDBv9GqXzZOXXDciJy5pHFNpmBsBMwBGBv60SmW/OEI/n2j0zjVmgJceibAA0fpCCyIeF70BojR8EsDPv730gBjqujHLmSG/gHofgB3Ask/AMSEL38kGf97bJekpwFhP4SwkxW8GtE0uOQ4MrFjlCPCPS415gCMi/wI9ea165VdC+mZI1Q75api8FTyTYCfJPmjKYcx0PAlrQuE9yCErW0FayCEg3XKt3XS1cbt+A1mvPWqQsAcgCq0JritpPUQssvtQTqGSaT7EYhPAMm36jz6NoaRNK6yF9XvYzGl90DhBY0rNAUPJ+DcVmR6lqHpPgFzALo/x/8eoeSPRPD7TNGQ2zXUuF9O99Ui+c1v22XceK1RnrgnvBHyu0J46nitmWLtLj2ddK+fYgJTNXRzAKZouiU9Csp+BmmVKRp2G4ca4Nz3AJxUrArc1UYjm7ZJ0lKA3wLADghhIwvsa5p4H/nk38G81O/IAjvHPOKpV28OwJTdApJeiDD7Q3vYtmXi+QBccj4QvlEkyrm7LZY1YYekx/QSHbltEeK/FYMS7Ro/AcG5Lcn07PGbYhaMioA5AKMi3SI9diqgRZMxnyn8Fxx/CPBcwJ1D8jdttbSKXcXxvc3n5ArYHEEvBrRYlf7WdgQEXHIMmewxAk2mokUEzAFo0WSMypRexUD/fauRPiriA+rJz94nlwK6FEh+QPJ3A0oaabfeC99vAHBDyG/Yy0lgV2sJMLkOdOuRfKC1NpphjRAwB6ARrO0XKmlZKLsG0jLtt9YszAmQ/wsmV/Wy7sV/khsA3EIyjINQr7QxVgD86gCfN2flYh3IPw/SE8Zhj+kchADvg0vXIfmLQXpbn8kmYA7AZM/fUNZLs69AUCzxGR/kdk0kAT4Aul+CMTsf4pbB7YBuB5JbAcRgrjsGzcVf1CKIxYieBPjlAcYv+WUBrAThGVB4hu3hT+RN86DRzr2NTI+f8FGY+QMSMAdgQHBd6Sb5QxH8AV0Zj41jQQR4N6iY3S9m9guA7gLjv6GiNaHoBHIpALE08dIQlwZiwJ5dnSXgklPJZLvOjs8G1peAOQB9EXW7QW8Z11+EEF7e7ZHa6IyAEfg3AbrfgcnaJKfyCKrdCT0C5gDYnRCLrDypSBX8RMNhBIxA1wnwfrj0xYxlm+2aagLmAEz19D84eGl2IwRdaPEAdkMYgU4TiOf9tyfTUzs9ShtcKQLmAJTCNB2NJL83gj9qOkZrozQCU0jAJYeSyQencOQ25AUQMAfAbov5CEj+swh+N8NiBIxAxwi4mOWPW43r2GjHaHZiOOYAdGIa6xtE7+iXvoWQbV6fVJNkBIzAWAmQN4Hp+iQ7nWp6rIwnULk5ABM4aU2bLGlJKFwB+TWa1mXyjYARaJhAr8jPuiStAmXDqCdNvDkAkzZjI7JX0gpQ9mNIdjJgRMxNjRGonwBn4fAKcub79cs2iZNOwByASZ/BBu2XtC5C9n1Aj2pQjYk2AkagGQIx4j9m+vtKM+JN6qQTMAdg0mewYfulbGuEWKrW0gU3jNrEG4F6CbhkXzI5sl6hJq1LBMwB6NJsNjQWye+F4D/ekHgTawSMQN0EXHIkmexbt1iT1y0C5gB0az4bG43kP4jgD25MgQk2AkagHgIuORFwbyE5t9ZDPXJNSucImAPQuSltbkCSPwzBv785DSbZCBiBoQi49NsAX0cyG0qOdZ4KAuYATMU01zdIyX8Mwb+3PokmyQgYgVoI0F0KJq8k+UAt8kxI5wmYA9D5Ka53gJIIhJgtcNd6JZs0I2AEBibA5DrQbUjyHwPLsI5TR8AcgKmb8uEH3CshHI5H8DsOL80kGAEjMBQBJj8D3cYk/zaUHOs8dQTMAZi6Ka9nwL2UweFrCH67eiSaFCNgBCoTYHI16F7BmO3PLiNQkYA5ABWBWfMHCUiaKZyAbY2LETACIyZAdwWYbEbyrhFrNnUdIWAOQEcmclzDKLYDPo/gdx6XDabXCEwdAbrLipf/PVXGLunFAC63I4JVqHW3rTkA3Z3bkY2sCAz8KIJ/38iUmiIjMK0EetH+ryZ5bxUEUvZGhPBVuOQrgNvZygJXodfNtuYAdHNehxqVpEeT/GdVIZLfD8F/BIDdV1XhWXsjUIZA75z/tlWP+knZlgg6DVCaq3HJ8YB7hzkBZaB3t409qLs7twONTNIzoexikPuR6derCpH8OxH856x2QFVy1t4I9CHgki8DbpeqSX6k2U0Q8G1Aj5hPg0tOAdybSHpjP50EzAGYznlf4KiLl//3If0nQA/HWEnsq1URSdm2CDoB0COr9rX2RsAIPIyA4JL3k8nhVdlIsy9DwLkL/Vt0yamFE2CZA6vC7UB7cwA6MIl1DEHSM6AsvvyfNI+8+OB5F5nEL/pKl6T1oOxbkJ5YqaM1NgJGYB4C/BccdyLTk6pikbQ+QnYRoCUW2dcl3wDcG6uuLFS1x9q3j4A5AO2bk5FbtJCX/1w7ohPwX2RydFXDJD0Nys6B9Kyqfa29ETACvAcO25AzF1ZlIWkthOwSQEuX6uuS0wC3gzkBpWh1ppE5AJ2ZysEGImmV4sv/yYuQEJ2Avcnkk1W1SFoK8KchhE2q9rX2RmBqCRC3gTPxjP8NVRnkSbqU3Yi4qlflspWAKrQ60dYcgE5M42CDKPnyf1C4Sw4kk0OqaiuyBn4Kwb+ral9rbwSmjkDvjP82JP866NglrQpll/TieSpcLj0D4PYkZyv0sqYTSsAcgAmduGHNrvzyn6vQuW3J9LRB9Et+D4TwcSBmELTLCBiBhxFwyacBt08dS/FFUG90AuaN6+kP3aVnAtzOnID+qCa9hTkAkz6DA9gvaeVi2f8plbq79DyAW5H8v0r95mksaR1o9nQITx1UhvUzAt0jwAfguCuZnlDn2IZwAs4F+Lph/tbrHIfJaoaAOQDNcG2tVEkrQLOXVn4Bu/R8gFvW8UCQ9ATAn2RxAa29TcywURIg/gDOxJftT5tQWwT5xpWARcX5PFx1DQ5/E+MxmfURMAegPpatlyTpqZC/FAorVDLWpRcAfG0dL/+5eou4gIMR/P6WObDSbFjjLhFw7iIgidH3jZbyHcIJiI5/XPV7oEvYbSw9AuYATMmdMOTLP375N/IAkLLNEHQioMdNyVTYMI1AfPRmcO4wwB08qnS8RdxPXAmouvUXPwAaewbY7TA+AuYAjI/9yDRLWr748n9aJaUuvbD48m/k5T/PakBcmTgRChtUss8aG4FJJEDeDKbxq/+qUZs/RPzPSJ4Fo+Yx7frMAej4HTD4yz9fmtyiqS//h2IvKgq+GyEc8bCc5R2fIxveFBFwydcAt1vVSn51EiqcgLgSsGwlub3tirgVeH+lfta4tQTMAWjt1AxvmKTlii//FStJc+67xct/5H/oklaDwtchv1Ylm62xEWg1Ad4Nx90GSenbxLB6wcD++5Xjgeh+ACYxQdF9TdhlMkdLwByA0fIembbi5R//wJ9eSekYX/7zbAk8EggfQfB7WlXBSrNnjdtIoPflvDPJW9tk3sBxQXQ/LJyAe9s0HrOlOgFzAKoza32PgV/+vT/sV7XFu88rmYnHQaHaCkbrZ8gMnA4CvAOOew1SUXNUfAonIH4oVIsP6mUrjM8KcwJGNVkN6DEHoAGo4xSpuK/XO+pX7cu/9wf9yra8/OdZDXgUEN6HEPYHtNg42ZpuI1CagEvPAbgLyT+W7jOmhkM4AZcXTsA9YzLd1A5JwByAIQG2qbti3u9eSd9nVrJrArx5SWtC/lgorFdpbNbYCIySAPkXkO8iYzrdybmKYOG4ElBttY3OnIDJmeaHWWoOwARP3rymS3pi8fJftdKQen/A8cu/9Ut5khwQdkcIhwFastI4rbERaJQAPZw7DnD7k/xHo6oaEl44AZcMsHp4RfEMsZWAhuamKbHmADRFdoRyi5d/PNbzrEpq6eIf7qaT8PJ/iLOzLKBPImRbVxqvNTYCTRDoxc7sSfJnTYgfpcwh4oeuLJyAu0dpr+kajoA5AMPxG3vvIV/+8ct/Yr12SetC/pNQWH/sE2EGTB+BuL9Pvh9IvkZSXQFQOAFxJWClSmNicjXoNiZ5Z6V+1nhsBMwBGBv64RVL+o852fMugfxqlaTRRW89fvlP7Mt/7nh7CYT81lA4snKBo0rQrLERmEuA98O5owF36KStnpWdwyKYOMYEDOIEbELyjrK6rN34CJgDMD72Q2ke4uX/IzB5RRde/vMClLQ4EN6LEPYB4n/bZQRqJxDgkpMBdwDJ22qX3jKBRVBx3FqsGFeUXFOsBJgT0LI5fag55gC0fIIWZJ6kZYov/9UrmU8XX/7xy7+z+3TKC52EAxHCWwHNVOJjjY3AggkILv0mwA+RvHGaIBVOwPeqxxcl1xZOwN+nidekjdUcgAmbseLl/z3Ir1HJ9Cnbn8sjmhH2RgjvtNoCle4UazwvAecuBpIY2T/ywj1tmYjB44ySn4FuI5LmBLRlMh9ihzkALZ2YRXz5D/Lyj0ty8Q9x6oJz8iQnCHuZIzBBN3obTO2dkIlL/T9ogznjtqHnBIT47KkYb5Q7ATEw8G/jHoPpfzgBcwAm5K6QtDQULob82pVMpu3HRV6SVgTCBxDCG21roNIdNE2NA1x6LsAjSV42TQMvM9Yi7ig6ARW3HpPrig8QcwLKgB5hG3MARgh7UFXFy/+7kH9uJRnM9+Hil78F4xTg8j1NhF0Qwh6AHleJpzXuKAH+C859A3CHk7ypo4OsZViDOwH8BZi+jDFTol2tIWAOQGumYsGGSHos5L8LhedVMpX50tvL7eW/UK5LAGF7KLyncurkShNhjdtLIJbodScA7mOTkLO/LRwLJyCuRlaMQ+IvCyfgz20Zy7TbYQ5Ai++AIV/+FnxTYm576YX9FhD2mrPF8qISXazJpBNgcgOIYwF3QlfP8Tc9RYMHI+dOQPww+VPTNpr8/gTMAejPaCwtipf/RVBYp5IBzPfb4h+YRd5WApfHCawKhB2hsBPiUUu7OkSAD8Al3wH8F8mZizs0sLENpXAC4krAmpWMIH9VrASYE1AJXP2NzQGon+nQEiUtBfn48n9+JWG9l3/88rdgm0rg5m8s6RGAfw3g3ozgXwkoGUKcdR0ngbinT3ci4I6z7bD6J6IXn5Q/qypuUfLmwglofbnk+qm1R6I5AO2Zi9ySIV7+1xdf/vbyr3FOJa0AhLdCejMUVqhRtIlqikCeo9+dDriTpvn8flN4Hyp3CCfg12D6Uou/GNVMPVyPOQDjY/8wzcXL/0IorFvJLOb7avEPySJsK4Gr1ljSakDYBorBg1q5Wm9r3SwB3gHnzgV0OpCcTzJrVp9Jn5fA4FuWjE5APB1wuxEdPQFzAEbPfIEaJT0G8vHlv14lk+zlXwlXHY17BYiwTs8ZUCxEZCsDdYCtKiPGudCdBYRvAOn3SfqqIqx9fQQGdwLcLWASnYDf12eNSSpDwByAMpQabpMXspE/b05+/w0qqbKXfyVcTTQunIHnAuGVkDZFLFFsMQNNoI4yA/LcFjgfcOcB+Im99JtCPZjcwgmIHzIV45dwKzgTVzHNCRgM/UC9zAEYCFt9nYZ4+cdI2vgHY2dq65uOoSVJWgLwLwW4OeQ3hbD80EKnWgDvhUsuBfQdwJ1r+8XtvxkG38rEbYUT8Lv2j7IbFpoDMMZ5LF7+50LhJZXM6B2jsZd/JWjjaSxpDSBsCOAFcxI6vRDCcuOxZEK0RofuzE4NAAAPDUlEQVSWyRWALgfcFQCuta/8CZm7ecwcaCWA+VbA60heM3kjnkyLzQEY07xJejTk48s/vhzKX8yPz8SXv52hLU+tNS0lLQf4FwJ8ARSdgvBsQGlrDBytIQH5NlZ80ccXfnIFyd+O1gTT1hSBSisBLr0Q4PZ2VLOp2ViwXHMARsv739qk8B2EbPNK6u3LvxKuSWicO4LAakBMpsLVAa0Bac3uJSLinSCvA/lzQNcDyXUAbiT5z0mYJ7NxMAJFcPMFUFh/oRJccjLg3kJydjAt1mtQAuYADEpuyH6SVoLCGZB/dilRzI/L2JnZUrAmv1FefhXZmoBbFcCKAFdAzEmQnzjQUu0cIe8B3e+RB3IpBnPFf/8aSG4g+Yd22mxWNU2gcALOh8ILHqbLJccD7h0kQx12SFoMwJMBPApAdK5jCfT7SP61Dvldk2EOwBhnVNKjAJ2CkG2xSDPs5T/GWWqf6jzxCrAC4FcAuCyAxz/4jx4P8QmAfwLExwNafLgR8J+g/g4kfwf1P0CeYjomm4r//jugvwJJ/rK39NPDke5y7yLe6Zz5tjxd+m2Acc9/4JwNkp4OhM0AvhgKa0NafsFbarlzejOIKwFdCiQXkryvy8zLjM0cgDKUGmwjxf3f8EUE/9YFqqH7DZjEL39LlNHgPHRZdC+1cf41FK/HAIipjWPcwZLF/7sHQHwIx3/if8frXluS7fJdMfqxSVqyOO78IvTSlq9P8v6qlvS+8v32EHapnDTt38ri6ZKYQ8J9muTVVW3oSntzABYxk5JWAfzqAGPWt/jVFZde/xWXlAD8YU452ZuBNEYp3zHMDdE7Sx6+guB3nE8O87OxG5K8ZRj51tcIGAEj0AYCvWOyOhngXiR/U8WmonLnWyAdAiku89dzOXcRkLyX5PX1CJwcKeYAzDNXvRss2whwsU78JpCeVGIqY3KS60DEc8onDhrFXHi15yCEjXOddL8rvvxvK2GDNTECRsAIdJZA/jEmf+LgX/z90DCDc58B3PtJPtCvdVd+NwegV4DnEUBeAnbfIdO6Ci69AOChJK+sepMURTWuBkJSfPlbVqyqEK29ETACnSIgZW9A0JeGj2cpgaW3NbENY9zVFFxT7wBIsy+F8AXky/01Xi49B+BuVaOfJa0dg6tI3lqjNSbKCBgBIzBxBCT/PgT/0bgmOjLjYzl1pq8m+eOR6RyTotFBHdMAF6a2F4EfPoPg39acabwTjm8l07Ob02GSjYARMALdIyD5oxD83uMZGe+DSzcm+aPx6B+N1ql0ABQDSBTOhfxaI8AsuORgMvnwCHSZCiNgBIzAxBOQ/IcQ/JifmfEDLn0hyV9MPNCFDGDqHABJT4P8xVBYcaST6pJjAPdukhqpXlNmBIyAEZggAlK2FUI4sxUmx5c/0+eTvLcV9tRsxFQ5AJKeAGVX1L7fX3ZSXHI4mexftrm1MwJGwAhMEwFJyyJk1wF6XGvG7ZLjyaTBreLxjXRqHID8mJ38D5s7RlJyEl1Me5l+qWRra2YEjIARmBoCUjgNIdumZQMWHDciZy5pmV1DmzNFDsA4A0rmnSc+MOeo4HqMhVHsMgJGwAgYgZyApBchzF7WShx0V4FJ3Aro1BbuVDgAktZHmL0cgGvFzcXkWtCtY3XOWzEbZoQRMAItICCFcxCyzVpgyoJNcG5zMj23tfYNYFjnHYA8u5/CTyEfz9e353LJrmTyhfYYZJYYASNgBMZDIK+OGmZvHul5/6pDdel5pGuvg1J1PK2GPcBgFtRFyrZBCKfVJK4+MbE8JdMVpintZH3wTJIRMAJdIiD5AxH8Qe0eU0wXnC5P8s/ttrO8dd1fAQjZT+ac+V+nPJIRtnRuZzI9boQaTZURMAJGoHUEFPw1kH9O6wx7qEHOvY1Mj2+9nSUN7LQDIGkthNlrS7IYfTO6n9Cl645esWk0AkbACLSDQF4DJcz+rTUxWovC4pKTyWSHdpAb3oqOOwD+SAS/z/CYGpTgZlauWhazQWtMtBEwAkZgpASk2Zcj6OKRKh1UGfkruplnDtq9bf267QAEfwPkV2sb9PnscckeZMwSaJcRMAJGYPoISH43BP/ZyRg5Z+HSxUnOToa9i7aysw6ApGUQZv/a+kBHl55Juq27cDPZGIyAETACVQlI/jAE//6q/cbW3s0sR/L2semvUXGHHYDZjRD03RpZNSOK7jd06crNCDepRsAIGIF2E5D8pxH8u9tt5TzWuZlndaVAUIcdgElZVqKHSx9N8l8T8wdghhoBI2AEaiIg+c8i+N1qEte8GDfzbJLXN6+oeQ1ddgAORfAHNI+wBg0dWlKqgYaJMAJGYIoISP4IBL/vxAzZzTyN5C0TY+8iDO2yA/ApBL/nREySm1mV5C8nwlYz0ggYASNQIwHJvw/BH16jyGZFuZmlSN7drJLRSO+yA/A5BL/raDAOqcXNrGXFgYZkaN2NgBGYSAJSthVCOHMijCf/QjfzpImwtYSRXXYA2p8DYO4EuZmnk/xdifmyJkbACBiBThGQtArC7K8mYlDOfY9MN5oIW0sY2WUH4AMI/pASDMbfxM0sQzJmwrLLCBgBIzB1BBRmb4f0lNYP3CUfJJNDW29nSQM77ABkOyCEr5fkMMZmvIvJzGPHaICpNgJGwAiMlYDkT0DwO47ViDLK3cy6JH9SpukktOmwA6DnIsxe1fpJsHoArZ8iM9AIGIFmCUizGyPooma1DCmd/DWYPoOkhpTUmu5ddgBShOwOQEu2hvaCDHHJp8jkPa220YwzAkbACDRIQJKD/G+g8LQG1Qwn2iX7k8nknFYoMdrOOgBx7FK4ACF7RQkO42vi3BZk+u3xGWCajYARMALjJyD5XRD858dvyYIs4D/g0nj+/x/ttG8wqzruAPidEfyxg6EZRS/eDZc+ieQ/R6HNdBgBI2AE2kpA0mKQvwkKT2+djR38+o+MO+4AxDrT2Z8APbJ1N1Q0yCUnkMlbW2mbGWUEjIARGDEBaXYTBF04YrWLVkf+Ckxj+t//a5VdNRjTaQcg8pH8FxH8O2pgVb8IN/M8klfXL9gkGgEjYAQmk0C7ntn8P7h0gy5F/s97V0yBA6CVEbKbAKWt+nNw6Xmk26xVNpkxRsAIGIExE5D0SChcAfm1x2xKXKXdnUw+N3Y7GjKg8w5AsQrQsroAzODStUn+vKF5NbFGwAgYgYklIOk/oOyHkJ4xtkG45GgymYx6MgNCmhIHQEtB2Y2tyTTlkqPI5L0Dzpl1MwJGwAh0noCkFaDsIkgrj3ywLjkacP/VpTP/C2I4FQ5AbxVAGyBklwBKRn4zzbfpklwPuphN6oGx2mHKjYARMAItJyBpGcifDYX1R2MqPZzbj0yOGo2+8WqZGgeg2ArYF8EfMTbk5P+C6fokfzs2G0yxETACRmCCCEiaAcKhCH6feHaqMdPJ28F0B5I/bExHywRPlQNQOAFHI/g9Rj8PvBcufXlXo0lHz9M0GgEjME0EJD0X8p+pfzUgxmS5zwHuQJJ3TRPTKXQARCAcgeBHuAfPO+HSzUleOU03l43VCBgBI1AngTxlMPxrIOwHhXWHk80H4NwJgDtyWsuxT50DMPeGkfy7EMLHAS023E3Upzd5E5huxZhMwi4jYASMgBGohYCkNYCwPYRXQn6NctsDvAcuuQwIZwLJmdP2xf9Q8FPrAPS2A7QulJ0A6Zm13JHzCxFc8iXAvYfkfQ3IN5FGwAgYASPQe5Y/HsieDbh4YmBZAEsAeDSAOwHcA+i3QBI/wn5OMjNoPQJT7QAUTsBiQNgHIbwX0GNruTHofgIme5O8vBZ5JsQIGAEjYASMQM0Ept4BmMtT0lJA2A3STlBYqTrnGEiSXAiEz5Lp+dX7Ww8jYASMgBEwAqMjYA7AQ1hLMUgQzwfCJoBeAml1SE98+JRwFsTvQHcVoO8Byfkk/zK6qTNNRsAIGAEjYAQGJ2AOQAl2kpYEsAyAxwCIFaHuAfBXkrMlulsTI2AEjIARMAKtI2AOQOumxAwyAkbACBgBI9A8AXMAmmdsGoyAETACRsAItI6AOQCtmxIzyAgYASNgBIxA8wTMAWiesWkwAkbACBgBI9A6AuYAtG5KzCAjYASMgBEwAs0TMAegecamwQgYASNgBIxA6wiYA9C6KTGDjIARMAJGwAg0T8AcgOYZmwYjYASMgBEwAq0jYA5A66bEDDICRsAIGAEj0DwBcwCaZ2wajIARMAJGwAi0joA5AK2bEjPICBgBI2AEjEDzBMwBaJ6xaTACRsAIGAEj0DoC5gC0bkrMICNgBIyAETACzRMwB6B5xqbBCBgBI2AEjEDrCJgD0LopMYOMgBEwAkbACDRPwByA5hmbBiNgBIyAETACrSNgDkDrpsQMMgJGwAgYASPQPAFzAJpnbBqMgBEwAkbACLSOgDkArZsSM8gIGAEjYASMQPMEzAFonrFpMAJGwAgYASPQOgLmALRuSswgI2AEjIARMALNEzAHoHnGpsEIGAEjYASMQOsImAPQuikxg4yAETACRsAINE/AHIDmGZsGI2AEjIARMAKtI2AOQOumxAwyAkbACBgBI9A8AXMAmmdsGoyAETACRsAItI6AOQCtmxIzyAgYASNgBIxA8wTMAWiesWkwAkbACBgBI9A6AuYAtG5KzCAjYASMgBEwAs0TMAegecamwQgYASNgBIxA6wiYA9C6KTGDjIARMAJGwAg0T8AcgOYZmwYjYASMgBEwAq0jYA5A66bEDDICRsAIGAEj0DwBcwCaZ2wajIARMAJGwAi0joA5AK2bEjPICBgBI2AEjEDzBMwBaJ6xaTACRsAIGAEj0DoC5gC0bkrMICNgBIyAETACzRMwB6B5xqbBCBgBI2AEjEDrCJgD0LopMYOMgBEwAkbACDRPwByA5hmbBiNgBIyAETACrSNgDkDrpsQMMgJGwAgYASPQPAFzAJpnbBqMgBEwAkbACLSOgDkArZsSM8gIGAEjYASMQPMEzAFonrFpMAJGwAgYASPQOgLmALRuSswgI2AEjIARMALNEzAHoHnGpsEIGAEjYASMQOsImAPQuikxg4yAETACRsAINE/AHIDmGZsGI2AEjIARMAKtI2AOQOumxAwyAkbACBgBI9A8AXMAmmdsGoyAETACRsAItI7A/wNFywE6E6gwOwAAAABJRU5ErkJggg==
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAgAAAAIACAYAAAD0eNT6AAAACXBIWXMAAA7DAAAOwwHHb6hkAAAgAElEQVR4nO3dd7RsVZmu8ecjZ5AkIjQgCiJZxASoiIEWoRVUMEfUthXt7mu43bbaapuurbQ5IyDmVhEMqGBEDCAoKMGEgiBRlJzOd/9YhSIezt61d1V9Kzy/MfY4Dtx7rRdO7ZpvzTXXXCBJkiRJkiRJkiRJkiRJkiRJkiRJkiRJkiRJkiRJkiRJkiRJkiRJkiRJkiRJkiRJkiRJkiRJkiRJkiRJkiRJkiRJkiRJkiRJkiRJUotEdQCpyzJzNWDt0dcaQN7mW64Ebhr970sj4k8zjKcimbkSsAlwJ2DV4jiavMuACyPi99VBFsMCIC1FZi4H3BnYArjL6GuL0dedaAb8tYAVxzz09cAlwO+Bi0f/+wLg58BPgbMsCd2VmXsDBwMPB1YvjqPp+zXwOeCtEXFedZhxWQA0eJm5AnAPYFfg3qM/7wGsXBTpfODM0dfpwIkRcWZRFs1DZt4ZOBLYszqLSlwHvAF4TUQsqQ4zXxYADc5o2v5BwENoBvudaf+ntUuAE4Fvj/48JSJuWvaPaBYycyfgizQzQxq2o4HHRcQN1UHmwwKgQcjMLYFHjL4eSPevy14NfJ1m+vHzEXFJcZ5BysyNgB8Am1ZnUWscHhFPqw4xHxYA9VZm7gI8EdgH2Ko4zjTdTDMr8DngsxFxbm2c4cjMY4BHVudQ6xwQEZ+pDjEXC4B6JTPvRDPoPxXYrjhOlR8BHwKOiogrqsP0VWbuBnynOoda6Sxgu4i4uTrIslgA1HmZuQqwH82g/3Bg+dpErXEN8CngfRHx3eowfZOZHwCeWZ1DrbV7RJxYHWJZLADqrMxcD3ge8Hxgw+I4bfdT4P3AYd5mOBmZeQEu/NPte11E/Ht1iGWxAKhzMnNz4J9pPn21ffV+21wJvAt4U0RcXh2mqzJzdeCq6hxqtU9GxIHVIZZlueoA0nxl5i6Z+QngF8AhOPgvxJrAS4FzM/ONmenMycKsXx1ArbdBdYC5WADUepl518z8NHAy8Di8xj8JawIvAX6dmYeOFk9q/pw90Vwuqw4wFwuAWisz183MNwBnAAdU5+mp1YAXAr/IzFeNFlRqDhFxJZYALdtvqgPMxQKg1snMlTLzhcAvaaarq7bkHZLVgFcC52TmU6rDdMSXqwOo1Vr/+rAAqFUycx/gbOBQYJ3iOEO0KXB4Zn4tM7evDtNyR1UHUGudD3yrOsRcLABqhcxcLzOPBI4FNi+OI9gL+FFm/reXBZYuIr4IfLM6h1rpVV14HoC3AapcZu4LvAfYuDqLlupM4KkR8cPqIG2TmVsD38PZKv3FccA+bd8FEJwBUKHMvGNmfgr4PA7+bbYN8N3MfENmrlQdpk0i4myaO1PcE0AAPwQO7MLgD84AqEhmPhI4HFi3OovG8iOa2YAzqoO0SWbuQLPtcp8fOqXblzTvZ8+LiGurw8yXMwCaqcxcPjNfR/Op38G/e+4JnJyZz6kO0iYR8ROah089Dzi1OI5m5xrgs8B9I+LpXRr8wRkAzVBmbkCzcvqh1Vk0EUcCz+nam94sZOadga2BOwOrFsfR5F0KXAic1uXXvwVAM5GZewAfx2v9ffMjYP+IaP2mJ5L+mpcANHWZeQhwAg7+fXRP4HuZuXt1EEnjsQBoajIzMvPNwP8AK1Tn0dRsBJyQmc+uDiJp/rwEoKkY3S52GPCE6iyaqTdGxMuqQ0iamwVAE5eZawKfBh5WnUUl3gkcEhFLqoNIun0WAE1UZm4MfAHYqTqLSh0FPD0ibqwOImnpLACamNGtT98EtqzOolY4Fnhcl2+TkvrMAqCJyMyNaAZ/d0LTrZ0APNISILWPdwFo0UYb/HwNB3/9rQcDR/sMAal9LABalMxcB/gSsG11FrXWQ4HDMtP3G6lF/IXUgmXm2sBXgV2qs6j1ngAcWh1C0l9YALQgmbk88FHgXtVZ1BkvyMxXVYeQ1LAAaKHeDjyiOoQ655WZ+fzqEJK8C0ALkJkvAN5WnUOddTPNnQFfrg4iDZkFQGPJzIfRbPTj3v5ajMuBXSPiV9VBpKGyAGjeMvPuwEnAOtVZ1As/Bu4fEddUB5GGyDUAmpfR/v6fx8Ffk7Mj8N7qENJQWQA0X+8A7lYdQr3zpMx8UXUIaYi8BKA5ZebjaW75k6bhJmC3iPhBdRBpSCwAWqbM3JTmWu0dqrOo184GdvaZAdLseAlAtyszVwA+joO/pm9r4HXVIaQhsQBoWf4DuH91CA3GIZn5oOoQ0lB4CUBLlZnbAT8CVqzOokE5F9gxIv5UHUTqO2cA9DcyM4D34OCv2dsceHN1CGkILABammcBu1WH0GAdnJkPqA4h9Z2XAPRXMnM94Cxg/eosGrRTgXtFxJLqIFJfOQOg23oLDv6qtzPw9OoQUp85A6A/G027fgNfF2qHi4CtXBAoTYczALq1N+Dgr/a4I/Dy6hBSX/lmLwAyc1+ah/1IbXIDsH1EnFMdROobC4DIzOWAU4CdqrN02M3At2m2Tb5g9M9WB9YYfW0AbAlsBaxSEbDDPhYRT6gOIfWNBUBk5oE0W/5qfFfRLJx8W0RcNtc3j8rWZsA2NLssPhjYFVhhmiE77mZgm4j4eXUQqU8sAAM32u//DJq92DWeU4F/iIjzFnOQzFwT2APYH3gMsPYEsvXNYRHxjOoQUp9YAAYuM58GHFado4O+A+wdEVdP8qCZuSrwD8CTgb1xoe4tbgTuFhG/qQ4i9YUFYMBGW/7+BNiuOkvHnEezSc3F0zxJZm4NvAx4Im7LDPDuiHhedQipLywAA5aZewFfq87RQU+IiI/N6mSZuTnwEuBghr1W4Dpgy4i4YM7vlDQnpxeH7ZDqAB10FjNeMBkR544++d6T5tLDUK0CPL86hNQXFoCBysy7AI+sztFB/xsRWXHiiDgdeADNFrmXVGRogadnppdDpAmwAAzX8/HvfyG+XnnyiMiI+DCwA3B8ZZYiGwH7VoeQ+sABYIAycw3AW6oW5vzqAAAR8XvgoTSLBG8ujjNrB1cHkPrAAjBMj8V7zRfq2uoAtxjNBrwReDhwRXWeGXrYaGGkpEWwAAzT46sDdNhG1QFuKyKOB3anJbMTM7AczmBJi2YBGJjM3BDYszpHh92jOsDSRMRPaUrA2dVZZuQZo22VJS2Qv0DD81iGfS/5Yu1XHeD2jHbJ2wM4szrLDNyZ5lkKkhbIAjA8Tv8vziPafP05Ii6hWRMwhMsBj6oOIHWZBWBAMvPv8FPTYq0MvK46xLKMHk60N3B5dZYpswBIi2ABGJbH4vbPk/D4zHxOdYhlGa0JeBTNQ3T6asvM3KE6hNRVFoBh2bs6QI+8PTOfXh1iWSLi28DLq3NMmbMA0gL5aXAgMnMVminhVauz9Mz7gZdP+8mACzV64uMxwD7VWabktIjYuTqE1EUWgIHIzIcAX63O0VNXAUcBnwN+DFwUEUtqI/1FZq4HnAZsUp1lSjaOiAurQ0hdYwEYiMx8A/DS6hwDcRPwJ5rd+a4AzqG5Ne8k4MSIuGbWgTLz0cBnZn3eGTkwIj5ZHULqGgvAQGTmycAu1TnEDTQP8TkCODoiZra1cGZ+AXjErM43Q2+PCB9tLY3JAjAAoyngi3HRZ9tcCrwT+J+I+MO0T5aZmwE/A1ab9rlm7NSIuGd1CKlrHBCGYQ/8u26j9YFXAmdn5tNHC/amZrRT4FumeY4iO2SmD7eSxuSgMAyukm63DYAPAcdn5sZTPtehNIsW+2R53OBKGpsFYBh2qg6gedkTODUzp/awpoi4DHj3tI5faPfqAFLXWACGwRmA7tgQ+HJmHjjFc/w3MLPFhzOyY3UAqWssAD03WgC4aXUOjWUl4KOZedA0Dh4RFwEfncaxC7XyMc1Sm1kA+s9PRt20HHB4Zj50Ssc/YkrHrbJZZvbt7gZpqiwA/eftUd21EvDJzNxiCsf+NvDrKRy3ynLAVtUhpC6xAPTf1tUBtCjrAB/LzBUmedCISJrti/vEywDSGCwA/ef1/+67D/CCKRy3b9vnblMdQOoSC0D/WQD64T8z804TPuYZNDtE9sXdqwNIXWIB6D8LQD+sCbx4kgccXQb4+iSPWWzSBUnqNZ8F0GOj7VGvqM6hibkG2DwiLpnUATPz2cB7J3W8Yr+IiLtVh8jMlWi2396GZl+HlWoTaQquBH4HnBQRZ1eHWaiJLixS6/jpv19WA55Cs5HPpHxrgseqtmHlyTNzQ+DlNH9HPptgIDLzLOB1wFERsaQ6zzicAeixzHwE8IXqHJqo0yJiYjs7ju4uuJr+fEpdbZaPWL5FZu4HHAmsNetzqzW+CxwQEb+vDjJfrgHotw2qA2jidsrMu0zqYBFxE/DLSR2vBWY+C5CZzwI+i4P/0N0f+EFm/l11kPmyAPSbO6P104MnfLzOXsNcipkWgMx8IPAufC9VY1Pgc5m5anWQ+fBF22+deBFqbHtM+Hh9KgDrz+pEmbk8zeC/4qzOqU7YGfjn6hDzYQHoN2cA+mnSG95M7K6CFpjlYPwE3H1QS/fizFyjOsRcLAD95gxAP016w5s/Tfh4lWZ5Z9PjZngudcs6wLQe5DUxFoB+cwagn9bMzFUmeLwrJ3isarMsAHvO8Fzqnr2qA8zFAtBvzgD01yRXnFsAxpSZ6wKrz+Jc6qxNqgPMxQLQby5O6q87TPBYN03wWNVmNQPg4K+5rFkdYC4WgH67sTqApmaS+95vPMFjVVt+Rue5CMgZnUvddGF1gLlYAPrt+uoAmppJLgT0KXpjiogbgF9X51CrnVkdYC4WgH67oTqApma/lh6r2izvaDh6hudS9xxTHWAuFoB+swD010My866LPchoJ7s+zQDMsgB8ALh5hudTd3w3In5SHWIuFoB+u6o6gKZmReD1iznAaCe7N00mTmv8cVYnioifAR+a1fnUGUuAl1aHmA8LQL9dVh1AU/WYzPzHRfz864B7TypMS8ysAIy8EDhlxudUu70iIr5THWI+LAD9dml1AE3d/2TmU8f5gcyMzPx34CVTylRpprsajh49/CjgtFmeV631/2iKdSdYAPrNAtB/KwIfzsx3Z+acD8LJzM2ATwOvnXqyGrOeASAizgd2B96Jt94O1fnAgRHxkojozO2hUR1A05OZ2wJnVOfQzPwROBz4HHBKRPwJ/rxr3f2ARwNPBCa5jXCbXBMRpRv0ZObdgKcBjwS2or//rQVXAN+l+X37yGg2qFMsAD2WmesAf6jOoTLX0MzyDWUQ+mlEbFcd4tYyc22cae2j67o44N/WLB+coRmLiCsy8wqaJ1NpeIb2MKhfVge4rYiY+SUJab5spv13bnUAaUZ+VR1A6hILQP+5XamGwte6NAYLQP/5pqihcAZAGoMFoP9+Wh1AmhELgDQGC0D/tX4/amkCbqCFiwClNrMA9N9P8YEl6r8fR4SPv5bGYAHoudG9qj+vziFN2Q+rA0hdYwEYhlOrA0hTdnJ1AKlrLADDcGJ1AGnKflAdQOoaC8AwWADUZ1cBZ1WHkLrGAjAMp1PwlDRpRk6OCBe6SmOyAAzA6M3x+9U5pCn5VnUAqYssAMNxfHUAaUq+WB1A6iIfBzwQmbk9bgqk/rkUuGNELKkOInWNMwADERGnA7+tziFN2Jcd/KWFsQAMy1eqA0gT9qXqAFJXWQCG5djqANIE3QwcVx1C6ioLwLAcB/ypOoQ0Id+PiMuqQ0hdZQEYkIi4Dji6Ooc0IR+vDiB1mQVgeD5RHUCagBuxAEiLYgEYnq8Cl1eHkBbpCxFxSXUIqcssAAMTETcAH63OIS3SEdUBpK5zI6ABclMgddzlwMYRcX11EKnLnAEYoNGmQD4bQF31UQd/afEsAMP1/uoA0gIdVh1A6gMvAQxUZq5GszXwetVZpDF8PSIeXB1C6gNnAAYqIq4B3l2dQxrTm6oDSH3hDMCAZeaGwG+AVaqzSPNwOrBjRGR1EKkPnAEYsIi4GPhIdQ5pnt7k4C9NjjMAA5eZWwM/BZavziItw3nAlhFxY3UQqS+cARi4iDgbZwHUfoc6+EuT5QyAyMzNgbOBlYqjSEvzO2Cr0cJVSRPiDICIiHOBw6tzSLfj5Q7+0uQ5AyAAMnNT4Cxgteos0q38GLhnRCypDiL1jTMAAiAizgP+X3UO6TZe4uAvTYczAPqzzFwVOBPYrDqLBHwpIh5RHULqK2cA9GcRcS3wb9U5JOBm4KXVIaQ+swDotj4GfKs6hAbvXaOnVkqaEi8B6G9k5lY0i6/cIlgVzgW2j4irqoNIfeYMgP5GRJwDvKY6hwYpgec4+EvT5wyAliozVwB+AOxcnUWD8v6IeHZ1CGkILAC6XZm5E/A9YOXqLBqE3wHbRsQfq4NIQ+AlAN2uiDgN+PfqHBqM5zr4S7PjDICWKTOXA44DHlKdRb32joh4QXUIaUgsAJpTZm5Mc1fA+tVZ1Es/BPaIiOurg0hD4iUAzSkiLgAOotmcRZqkPwAHOvhLs2cB0LxExPHAK6pzqFcSeHpE/Lo6iDREFgCN4/XAp6tDqDdeFxFHV4eQhso1ABpLZq4FfBfYtjqLOu0rwCMiwstKUhELgMaWmZsDJwEbFUdRN50OPCAirqgOIg2ZlwA0tog4F3gkcHVxFHXP+TSf/B38pWIWAC1IRJwCPBHvDND8XQY8NCLOrw4iyQKgRRgt4HoGsKQ6i1rvWuAfIuKs6iCSGhYALUpEHAEcUp1DrXYj8PiIOLE6iKS/sABo0SLincA/V+dQK90AHOTtflL7WAA0ERFxKPB/q3OoVa4D9o+Iz1QHkfS3vA1QE5WZ/wi8A8vl0F0DPCoivlodRNLSWQA0cZn5JOAwYIXqLCpxNc2Cv+Org0i6fRYATUVmHgAcCaxanUUzdSnN4P/d6iCSls0CoKnJzPsAnwc2rM6imfg58MiIOKc6iKS5eZ1WUxMR3wfuC3jvd/99Bbi3g7/UHRYATdXoUa+7AcdVZ9HUvA2395U6xwKgqYuIy4F9gP+ieQa8+uFG4LkR8UKf6id1j2sANFOZuQ/wEWCd6ixalHOBJ7rYb7gyc12ah4LtBWwCrF2baKauAy6keTT60RHxq+I8C2IB0Mxl5mY0dwjsUZ1FC/Ip4NlO+Q9TZq4BvAx4EbB6cZw2SOATwL+NLnl2hgVAJTJzBeBfgdcAKxbH0fxcCfxTRBxZHUQ1MvMuwNHAdtVZWuhKmlmxY6qDzJcFQKUy8/7A4cBdq7Nomb5P8+b2y+ogqpGZGwM/BDauztJiNwP7REQnFj27CFClRteQdwD+k2ZRmdrlaprp3t0c/IcrM5cDPoOD/1yWBz4+uszZehYAlYuIayPiVcCuNJ8w1A7HAttExBtd5T94TwbuUx2iI9YBXl0dYj68BKBWGa0NeC7NjMC6xXGG6pc01/o7MY2p6cvMM4Btq3N0yBLg7yLid9VBlsUZALVKRNwUEe8A7ga8HbipONKQXAm8EtjewV+3yMy74uA/ruWAfatDzMUCoFaKiMsj4hBgR+CzuIHQNF0L/Ddwl4h4dURcWx1IrXLv6gAd1fr/bhYAtVpE/Cwi9qcpAp/CIjBJNwLvA+4WEf8nIi6tDqRWcuHfwrT+v5sFQJ0QEadHxOOA+wPH0Fxj08JcDxwGbB0Rz2n7dUqVs3QvTOvfoywA6pSI+F5E7AdsRfMQGqer5+8i4I3AlhHxjK7tWqYyF1QH6KjfVweYiwVAnRQRv4yIFwJbAK+g2ZteS/cD4Ek0q5Jf5id+jekH1QE66qTqAHPxNkD1wmijkocCBwP74fbClwGfBj4cEd+rDqNuy8wf02zYpfm5maZwt3r2xAKg3rnVU8oeC+wNrFCbaGauBY4HjqB5QtkNxXnUE5n5BOCo6hwd8qGIeGZ1iLlYANRrmXlH4ACaWYEHAqvUJpq4P9AM+p8CjvEWPk3DaIbtm8Du1Vk64HJgx4g4vzrIXCwAGozMXA14EPD3wEOAu5cGWpjraZ5B/rXR1ylu06tZyMyNaNYDbFqdpcVuAvaOiOOrg8yHBUCDlZkb0NxWuMfoz52AVUtD/a3zgdNGX98GvhMR19RG0lBl5p1pHge8S3WWFrocOCgivlodZL4sANJIZi5P81jiHUZf2wJb0txpsOaUT/97msH+HP4y4J/q5jxqm9FM2r8CL2b6vxddsAT4CPAfEfHb6jDjsABI85CZ69EUgU2A9YENRn+uB6xG80a4ArASsDrNVOCVwHU0i/OuHP2zPwB/pBnsfwP8Djg/Iq6f4b+OtGiZuRbN5bS9aH4vNqxNNFNX0fwOn0Sz9qZTA78kSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSZIkSX8tqgNIAJm5NrABsPboH60JrAAsD6xVlWugrgASuBK4Crga+CNwRURkZTBJk2MB0FRl5prA5sAWo6/NgU2B9Udf642+VqxJqDHcDFwCXDr68wLgPOC3o69zgV9FxLVVASXNnwVAE5GZ6wI7AtuPvnYE7kIzuGs4ltCUgbNHX2cCpwKnR8Q1lcEk/TULgMY2+lR/X2A3YFdgB2CT0lBqu5uBc2jKwPeBk4DTIuLG0lTSgFkANKfMvDPwAOD+wO40n/CXLw2lPrgGOBn4NnA8cFJEXFcbSRoOC4D+RmauRDPQ7w38PbBdbSINxLXAd4CvAV+MiDOK80i9ZgEQAJm5IfAomgF/L5pV+FKlc4FjgWOAb0TEDbVxpH6xAAxYZt4B2Bd4LPBwXImv9rqCpgh8CjjOMiAtngVgYEYL+A4ADqT5pO+gr665HPg0cHhEfLc6jNRVFoCByMx7AwcDBwFrFMeRJuUc4HDgiIg4vzqM1CUWgB7LzLVoBvznAjsXx5GmaQlwAvA24Fh3LJTmZgHooczcCvgX4MnAasVxpFk7B3g38MGIuLI6jNRWFoAeyczdgUOA/fE+felK4DDgzRFxXnUYqW0sAB2XmcsBjwH+D82ufJL+2g3Ax4DXR8TZ1WGktrAAdFRmBvBI4NXATsVxpC5YAvwv8IqIOKs6jFTNAtBBmbkvDvzSQt0MfAJ4ZUT8ojqMVMUC0CGZ+VDgtcC9q7NIPXAj8D7gNRFxUXUYadYsAB0wWtX/FmCf6ixSD10FvJlmseDV1WGkWbEAtFhmrgO8DHgRsHJxHKnvLgD+L3Ck+whoCCwALZSZywPPAl4DbFAcRxqabwKHRMRPqoNI02QBaJnM3B54P3Cf6izSgN0EvAv4Ny8LqK8sAC2RmSvS7N73amCl4jiSGr8Cnh0Rx1cHkSbNAtACmbkbzaf+baqzSPobCXwEeFFEXF4dRpqU5aoDDFlmrpaZ7wC+jYO/1FZB81yNH4/24JB6wRmAIpm5M3AUDvxS13wMeEFEXFYdRFoMZwBmLDMjM18InISDv9RFjwdOy8w9qoNIi2EBmKHMvCPwBeBQvK9f6rJNgBMy81WjB3JJneMlgBkZbeP7MWC96iySJuo44CkRcXF1EGkcNtcpG035vxT4Eg7+Uh89HDg9Mx9WHUQahzMAU5SZawEfBh5dHEXS9N1Ms4/HayNiSXUYaS4WgCnJzK2BzwD3qM4iaaa+BBwYEVdWB5GWxQIwBZm5N/BJYM3qLJJKnALsFxEXVAeRbo9rACYsM58BfB4Hf2nIdgF+mJm7VAeRbo8FYEJGi/1eBXwQWLE4jqR6GwPfyMz9qoNIS2MBmIDMXJlmr/BXVmeR1CprAJ8Z3QkktYprABZptNL/WMBdwSQty9toHiiU1UEksAAsSmbeAfgicN/qLJI64YM0jxf2NkGVswAsUGZuCHwF2LE6i6RO+Tjw5Ii4qTqIhs0CsACZeSfgq8C21VkkddKngCdGxI3VQTRcFoAxZebmwAnAFsVRJHXb52g2DLqhOoiGyQIwhsy8M/BNYMvqLJJ64UvAARFxbXUQDY8FYJ5G1/y/AWxTHEVSvxxHs2ugMwGaKfcBmIfMXJumqTv4S5q0hwOHZ6bvx5opX3BzyMzVae7zv2d1Fkm9dRDw9uoQGhYLwDJk5krAMcDu1Vkk9d7zMvNl1SE0HBaA25GZAbwf2LM6i6TBeF1mPrM6hIbBAnD7XgU8pTqEpEEJ4L2ZuX91EPWfdwEsRWY+FTgM//tIqnENsFdEfK86iPrLAe42MvOBNLflrFydRdKg/R64V0T8rjqI+skCcCuZuSXwQ+AO1VkkCfgusKd7BGgaXAMwkpmrAp/EwV9Se9wfOLQ6hPrJAvAX78Z7/SW1zz9m5rOqQ6h/vAQAZOYLsWVLaq/rgQdExA+qg6g/Bl8AMvN+NHv8r1QcRZKW5UKaRYEXVAdRPwy6AGTmesBPgI2rs0jSPBwPPCwillQHUfcNfQ3Au3Dwl9QdewEvrA6hfhjsDEBmHgy8rzqHJI3pemDXiDi9Ooi6bZAFYHS//6nAmtVZJGkBTgPu4/4AWozBXQLIzBWAo3Dwl9RdOwH/WR1C3Ta4AgC8ArhPdQhJWqQXZ6aPKteCDeoSQGZuD5yMt/xJ6odfAztFxJ+qg6h7BjMDkJnLAx/AwV9Sf2wBvL46hLppMAUAOAS4d3UISZqw52am720a2yAuAWTmZsAZwBrVWSRpCk6muSvADYI0b0OZAXgvDv6S+utewMHVIdQtvZ8ByMxHA5+pziFJU3Y5cPeIuKQ6iLqh1zMAmbkS8MbqHJI0A+vigkCNodcFAPgX4G7VISRpRp4xesKpNKfeXgLIzI2Ac3DHP0nD8iOaxwZndRC1W59nAF6Hg7+k4bkn8JjqEGq/Xs4AZOYONA/76XPBkaTbcxawXUTcXB1E7dXXAfLV9PffTZLmcnfgydUh1G69mwHIzF2AH9LDfzdJGsNvgK0j4vrqIGqnPn5Kfi0O/pK0GfDM6hBqr14NlJl5f+DE6hyS1BIXAneNiGuqg6h9+s1qb/kAAA7jSURBVDYD8JrqAJLUIncC/qk6hNqpNzMAo6dhfb86hyS1zMXAZhFxXXUQtUufZgBeWh1AklpoQ+DA6hBqn17MAGTmFsDPgeWrs0hSC50O7OjugLq1vswA/CsO/pJ0e7YH9qwOoXbp/AxAZq4L/BZYvTqLJLXYsRGxb3UItUcfZgCei4O/JM3lEZm5VXUItUenC0BmLgc8pzqHJHXAcsCLqkOoPTp9CSAz9wGOrc4hSR1xNbBJRFxRHUT1Oj0DABxcHUCSOmR1vCVQI52dAcjMjWgW/61YnUWSOuTEiNi9OoTqdXkG4Jk4+EvSuHZzMaCgowVgtPjPp1xJ0sI8sTqA6nWyAAC7A1tUh5CkjnpKZnb2ErAmo6sF4HHVASSpwzYH9qgOoVqdKwCj6f/9q3NIUsc9uTqAanVuCigz9wROqM4hSR33J2DDiLi+OohqdG4GADioOoAk9cBawIOqQ6hOpwpAZq4APKo6hyT1xD7VAVSnUwWAZvX/htUhJKknHlkdQHW6VgD+vjqAJPXIFpm5bXUI1bAASNKwOQswUJ0pAJm5CbBddQ5J6hnXAQxUZwoAsDcdvG1Rklru/pm5fnUIzV7XCoAkabKWBx5WHUKz14kCkJnLAw+pziFJPfWA6gCavU4UAGB7YO3qEJLUU/evDqDZ60oB2K06gCT12LaZ6YesgbEASJKWA+5bHUKzZQGQJAHcrzqAZqv1BSAz7wz8XXUOSeo51wEMTOsLAH76l6RZuM/ojisNRBcKwC7VASRpANbC3VYHpQsFYMfqAJI0EDtVB9DsdKEA7FAdQJIGYpvqAJqdVheA0f7Ud6rOIUkDYQEYkFYXAJz+l6RZukd1AM1O2wuA0/+SNDtbZOYq1SE0G20vALZRSZqd5YGtqkNoNtpeAO5SHUCSBubu1QE0G20vAFtUB5CkgXHmdSBaWwBGO1JtUp1DkgbGSwAD0doCAGwKrFgdQpIGxluvB6LNBWDz6gCSNEAbVQfQbLS5AHj9X5JmzwIwEG0uABtXB5CkAVonM1etDqHpa3MBWL86gCQN1B2rA2j6LACSpNtyIeAArFAdYBnWqw4wY9cBXwKOAc4BLqZ5PvcmwEOBR+NlEUmz4QzAAFgA6iXwYeAVEXH+Uv7/U4CjM/NfgOcBrwTWmV08SQPkDMAAtPkSwAbVAWbgeuBpEfGM2xn8/ywiboiIQ4FdgZ/NJJ2koVqrOoCmr80FYN3qAFO2BDgoIo4Y54ci4hfAg4HfTiWVJIFPBByANheA1asDTNkbI+JzC/nBiLgIOAC4ebKRJAmwAAxCKwtAZi5Hu9cnLNbFwOsXc4CIOBk4cjJxJOmvrFwdQNPXygJA/19874mIKydwnP+ewDEk6bacARiAthaAlaoDTNnRkzhIRJwB/GISx5KkW7EADEBbC0CfZwBuBn48weOdOsFjSRL0/0OYaG8B6POL7+KImOTivQsmeCxJAvBZAAPQ1gLQ5xmAqyd8vKsmfDxJ6vN7sEbaWgCiOoAkDZjvwQPQ1gKg+cvqAJKk7rEAdJ8FQJI0NgtA91kAJEljswB0nwVAkjQ2C4AkSQNkAeg+ZwAkSWOzAHSfBUCSNDYLQPdZACRJY7MAdJ8FQJI0NguAJEkDZAHoPmcAJEljswB0nwVAkjQ2C0D3WQAkSWOzAHSfBUCSNDYLgCRJA2QB6D5nACRJY7MAdJ8FQJI0NgtA91kAJEljswB0nwVAkjQ2C0D3WQAkSWOzAEiSNEAWgO5zBkCSNDYLQPdZACRJY7MAdJ8FQJI0NgtA91kAJEljswBIkjRAFoDucwZAkjQ2C0D3WQAkSWOzAHSfBUCSNDYLQPdZACRJY7MASJI0QBaA7nMGQJI0NgtA91kAJEljswB0nwVAkjQ2C0D3WQAkSWOzAHTfddSWgKsLzy1JWiALQMdFxOHASsBdgOcC35ri6RI4GngSsCmwSkSsAawLPBB4PXDZFM+vbvg18CbgIcDdaF4fWwN7A28Bzq+LBsA1wBHAQcB2wIY0r+f7AS8BTqqLJs1OVAdYmsy8K/Dz6hxT8ouIuNs0T5CZDwPeTVMKJuUU4B8j4odznHs14BDgVcDKEzy/2u9ymgH0iIi48fa+KTNXBg4G/gtYa0bZoCmw7wReGxEXLfMbM/cE3grsOItgLfTFiNinOoSmyxmAHoqIrwD3Br45oUN+CthjrsF/dO5rIuINwJ40A4KG4cfAvSLig8sa/AEi4vqIeAfNa/TMmaSDq4D9I+IFcw3+ABHxdZoZgSOmnkwqYgHoqYi4DNgXOGORh/oa8ISIuHbM858EPBq4YZHnV/udCzwsIn49zg9FxNnAw4E5B+RFugl4bER8bpwfGr3mnw58ZiqppGIWgB6LiCuBxwDL/ES2DJcAj4uImxZ4/m8B/7HAc6sbltAMrhcv5Icj4jzgqZON9DfeGhFfXsgPRsQS4CnAbycbSapnAei50aesDyzwx/8rIv6wyAhvA36zyGOovT4eEScv5gARcRxwwoTy3NYVwKsXc4CIuBp45WTiSO1hARiGdy/gZ64DPrjYE0fEdcCHFnsctdY7W3ac2zoiIq6awHGOoikTUm9YAAYgIk6nuU47jq9P6I0T4PMTOo7a5RLgexM61leZznqRBU3939ZoYeNEjiW1hQVgOH425vf/dMLndsfC/jlzdI180UbrVaZxnf30CR5r3N8hqdUsALNXtffC78f8/gUt6lqaiLgBWOxaArXPxF4jI9O4G+DSCR7rwgkeSypnAZi99YrOu8aUv/92ZWYAq0/qeGqNib1GpnQ8gFUmeKw1J3gsqZwFYPbWycyKwXDTMb9/kwmee0PcFbCPJvYaGZXESb7mbrHlBI817u+Q1GoWgBoPnuXJMnNt4F5j/theE4wwyWOpPe6RmXea0LF2ZDqzY3tM8Fi+jtUrFoAaj5vx+R4FrDjmz2yWmfed0Pln/e+r2VgOeOyEjjWp49zWEyZxkMy8O7DDJI4ltYUFoMZBmbnNLE6UmSsCL1/gj79mAue/N7DfYo+j1nrZYi9pZeb6wAsmlOe2ds3MvSdwnEX/LkhtYwGosQLwntHgPG2vAO66wJ99SGY+baEnHj0Z8D209KmTmog70Tz6d0FG1/7fyXQX2L0rMxf81MHMfDRwwATzSK1gAajzAJo3pqn9HWTm44F/X+Rh3jN6NOq4514ROBLYeZHnV/s9LzNftMCffTnTv0S0BfC/mTn2HQGZuSvNEwEtseodC0CtZwGfXcynk6XJzOUy8+XAR1j8G9fKwJcy8+ljnH8D4CvA/os8t7rjrZn55sxcYT7fnJkrZ+Z7WeQ+/WN4CHBCZs77ToPMfBzwDaZze6JUrq0FYKFPr+ui/YCfZ+bzF1sEMnOFzNwX+BHNNctJ/f2uDHwoM0/IzN1G07ZLO/8dMvMlwDnAgyZ0bnXHvwI/ycwDbu/yVmaukplPAs4Enj3TdHA/4GeZ+R+Zecfb+6bMvE9mfgn4BLDazNK1y4KeAKpuaeW0VmauC1xWnaPADcC3aN4cL2L+v4QbApvR3F54h+lE+ysX0nwyOh+4ErgjsB2wG836BumPwPE0T4K8lOY1ehea12gbNoW6EfgBcArNMw1Wp9mH4IF4vz/ARyLiydUhNF1tLQArMp0Hg0iS5vauiPin6hCarlZeAhg9eev66hySNFBXVgfQ9LWyAIz4ApSkGr7/DkCbC8AF1QEkaaB88uEAtLkAnFMdQJIG6qzqAJq+NheAs6sDSNJA+f47ABYASdKtXRYRQ7wNe3DaXADOrA4gSQPk9P9AtLkA/AS4ujqEJA3MidUBNButLQARcQO+ECVp1r5eHUCz0doCMOILUZJm50bgO9UhNBttLwAnVAeQpAH5fkRcVR1Cs9H2AnDLgzokSdN3XHUAzU6rC0BE3Ax8rDqHJA1AAh+tDqHZaXUBGDmyOoAkDcC3I+JX1SE0O60vABFxMnBGdQ5J6jk/bA1M6wvAiC9MSZqea4FPV4fQbHWlALwX+GN1CEnqqfdHxBXVITRbnSgAEfFH4D3VOSSph24E3lIdQrPXiQIw8hbgmuoQktQzh0XEb6pDaPY6UwAi4mLgA9U5JKlHbgLeVB1CNTpTAEZeDVxaHUKSeuKdEfHL6hCqEdUBxpWZzwXeXZ1DkjruIuDuLv4brq7NAAC8D/hedQhJ6rh/cfAfts7NAABk5i7A94Hlq7NIUgd9HdgrIrI6iOp0cQaAiDgFeE11DknqoD8Az3TwVydnAAAyczngy8BDq7NIUkcksH9EfK46iOp1cgYAICKWAE8CLqzOIkkd8VYHf92iszMAt8jMPWlmAlaqziJJLXYi8OCIuKE6iNqhszMAt4iIrwNPBZZUZ5GklvoZsJ+Dv26t8wUAICI+DrygOocktdDvgEdExOXVQdQuvSgAABHxLuD11TkkqUUuBx7mXv9amt4UAICI+DfgZdU5JKkFLqS51/9n1UHUTp1fBLg0mfk84O30rOBI0jz9Eni4+/xrWXpZAAAy81HAx4BVqrNI0gydTHPN/5LqIGq33n5CHt3rugfwq+oskjQjRwIPcvDXfPS2AABExMnAzsCnqrNI0hRdCxwcEU+JiKurw6gbensJ4NYyM4AX0twl4CUBSX1yGvD4iDirOoi6pdczALeIiIyIQ4FtgS9W55GkCbga+E/gPg7+WohBzADcVmbuC7wN2Lw4iiQtxLHA8yLivOog6q5BzADcVkQcA2wHvBj4fXEcSZqv44DdI2JfB38t1iBnAG4tM1cCDgL+A7hrcRxJuq0EvgC8NiK+Xx1G/TH4AnCLURH4B+DJwN7AirWJJA3c74CjgMPdzU/TYAFYiszcAHj86GtXYPnaRJIG4jKahcpHAsdHhE851dRYAOaQmWsDDwQePPraloGunZA0cVcC3wZOGH392EFfs2IBGFNmrgpsNfraevTnHYE1gDVHf65TFlBSW9wAXAVcAfyJZrD/LXAWcDZwDnBeRGRZQkmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSpDL/HwyRd6h+auMzAAAAAElFTkSuQmCC
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAUkAAAFJCAYAAAAWit+oAAAACXBIWXMAAAsSAAALEgHS3X78AAAgAElEQVR4nOzd649d153m9++z1t7nUqeuZBXvoiiSkmxRUluWezrTQKbZQSNBA415RyFITwdOpmME+Sdkvw6QP8B5M0AG88J8O4AHMw00kQTdM91WO902ZUuWKYoUL8W6X07Vuey9nrw4RUm2ZetG1nV9gBJAsS6rzuF+9lp7XX6QZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZVmWZQeG9roB2f5hIz7+NyF4PcBFQSdAV7AtmNHCQk/ShD7+ug0DpLTmum44pbbPndtMN2+O+8qVhQRzhpcM37OE9+J3e1refJNw9erVcO5cO46NPRMbjSo+/rsQ+of++kqp+dH7ORgU9Zkzd2vYruGPkvS9tJdte1IO/ZuYfT4/+MG1+Nprm8XU1HhZlp2iKFQOIq1U1e0YaNWVGyEUjaBQgIIUPwqDqqodY13bqpM1iNH9WKb+1rYGRaPuN+s4GA43BzMzDG7cWBj+8R/fqPbyd31SbMLCwrUxu+i0Ws1JinLayRNVXQehgOLhv75cG4KNLHnTw/4a9NZDYPOv/orNN964Xu91E7+qYq8bkO0PL71EPHbsWLOqUhtiq9+Pbcp6MljTQWFSBWM2HRJNKzRcu3z8tUVQZcdKToOY6Mpx03XYbEZvymza6tqN7ocfDrauXm0n4FCEJFwNdtEpitZxR87UdTovwskYiwguOBKdkGBQMqqDvZDKxr1GjPd6IXHtWmsLOPAheQTexOyxneF0WORfjrE1O0FdjccqNEMITUd3HIoJqmpCii1bbZzGJY0jd6TQQmqlRMNOJdJHN1iJOuDKDkPjnuRtEbaMt1HYkr1te1tiA3ldodxIKW1XKW2r6He7C9VWSve3L1ygkvZ/L9Mm3Lx5rZiaYnxssvOCKV4IITwT8JmE5oQDEDka15d3PhJ4xfAIdC8pvdPr651GvbZ6Z26m/y19f7jXDf2yck/y6NBbb71enDx5sZiYaM06+nzl4hxlmCaEaexjMscIxbREE6sFsURuQChsF9hFEMFSAMJH3xhSIjjICVSBKjvVRhWkITC0GBqv47BCNVy2/ShG5tMgPuzMhPvHJy49gtizbySJff0s6+bNa8Xp041W7BQzrsqvgf8F9jOImWAmzeNnuzoCIenHzySNwjaJLYn5AnXa7bQF4zrPygqQQzLbXz6ehLlWzM+3ylarbgyHrXYqi3ZV1BeCwovBXMaeSynNScwCs6CZZBqCBhDwJ+Zx4FNnXbzzt/5kx0nh8VcYlATJZgOzguKCgu8q+W4Zw20FxlZXhy210npofWd9wVV/ljSE29V+nAC4cmWmWFzc6ngzzIbSlxXC64Kzye4IWkejA/nYJ35XkyRqwxIpLEX7dlLoDjeKbWBzz5r4FeWQPIRsdPv21ebU1FxzGMZmG2PFqTqFU7Gl2QLPuQ4nLZ8K0ixmXGg8mfEAY5ZK2RGsJ3ixCxwUaGJPISK4BZ4zXHDiVcdyWUMWBj0vhqCHj1J4EBrnHoXee137zc39FJTr63UrhHgshHjKcEwwbrklK372Vx92DjKF5XGTZol+2FB7ca9b9VXkkDyErl+/Fv7kT2jajYng8hnElRD1ddvPIV1QYHKnx9NAChYxjKYoIyY87hc+OR71ak0LaGBPGE6IUBnXQIXYTvheLLiXEj8vxE/kluuU9NZbD7Zh/wzBiyI2Jc+k5FMKOmZ7EmiBw9HqRf660ftsKDETdphLPc+UCs29btlXkUPykLDRPP/tWG/xxGRDmk6hOB1UnBY8J3MJ/FyQThlOg9ugx5ML4E+LxCd1sf/Kc7n4+Gd+/D+1818PjcpkxiWaUujYOlG0uP/888N7a2v/emlzc2t1a2t148MPt+u9XEaU0rDqp7gdlTbl0JeokWx/9OThCFMSrkF921tB9FLqH+gZ7hySh4BNgNfj5PbcTKMTnyWVz1HzNQVejISTyDPAtE1nNMxV2H+9HgXsySBKCB3ks3Z62eYDh/K26/Te2FTznU5n5oPLl8d7NvVeLUwfDAb9MoblyuFhDGHVpmeohAo+MaF19MjgBAyNNxxYGFqrodHs73XLvoockgfY43BcXv5au67LsRh1nhi+jrgSQngF8yryJKbgca+RX52I2UeipA7QAR/HsqAn6aztswqekGOKsTlY3GqtfrD6Z6t/7c3BVW7selgeO7bc//DD8bWy03hUhHKewDwQMW3brY8+UfvvRX7i/Cuv/VBiYGnBZkH2/Bj1ShqSQzLbffZ3yoWFlWanMzNBOXyuaIYLcriIuOTEc+DTRm0d4PV6QtFwDFkQAmiyUjxf1P7FhcmZXzQ3Z5YYv7YB17d3s103bmzXV6+Oby9uNZdcp5/i0MI+bzgBzOyskwz4qCwBko2S5A2jFUn3Jf849cPdrUFararNHJLZ7rt//35ZTJ3qbA6qE0UsrjjxX0lclDkHnDSUkks+Gv4dtOvVAsogjpkwKXwMc0H4RYu/KdUY9FN0vTY+BHY1JP/4j29UNvXmo28vz8zUPwmhWKys5xTiJZtzCYrR0PsohCQW1MK1xKNgf1in+i4h3l6me/fDn9/bunr1xoF+JnkU3sRDY7S059vNqalGM6XBaZV61oRLIegVWa8SOE3SccTkXrf1SZPog7eRloV/khI/CQrvUNfvDQabd0KIm8eOXd7VpUI/+MG1+Cd/wrjdmIixecohnBVhLqnemaA6CiFpQ0ghUCOvuK4XEiw0FZc6nfeWDsIOqs+Se5IHyI0bV+Prr/fHG404PaiLF1Pi95N5VeY00mnMuAJNH6pzdkZsF6A25jjoZYlTKdVnHdJUbLbKkHQP3u4Bg91q07Vr19PNm9e2Z2dD1Wi4X9cs1bXHJEadK4ojEJK1KXGdguvkfn9Yb1OW273N0PvfOzf2zbKtr+IIvIkHn41u3Lgar1yZa4XQeqZoNc8l888EfwS8BmoBbTgKi5kf3wJk4G2c/rOTfyTzs14v/ezUqYfrMF5JB//0mWx/yD3JA+HbzdevNsYHm2kuoN+rEt+I4kXgLNACyqMxtPs18jHBFYJaBMZL0VjcOH13K/UeASt73bzscMgheQCsrtKKbR8rpfOGbwTx3xjOODEp0Wa07e9JbiM8ACzMrK1JxFmSW7GIJBTLut0jh2T2hOSQ3MfsqwVcKJY2i9Op5yuIlyVdMZyTNC1R8tH6x6PiV3rMDUTDOAg951o9lGij/sbG/7o9Ph62YG5rP+37zg6eHJL71OjU67lWSvVYox0uEOIfSOEPhE8hj4MLW0d4d8fHhErEGYmGJDvW3b62tobbfnj/1sKAXZzMyQ6fHJL71M2bLxUnn4uTTXuursPzMt9Afh1c4KO+/e3XuQDNGWaE+qSwGlJjM1H55Mn+ik21syvnEM77Z09bDsl9xia8xXfi9EZvglS8SIqvRvk141OCYmff9RF7/vi5SBBJnpPCyw4UMZUalDPLy8t/vvDTnw56L798Pfcosy8sh+S+czWU89uNosVkjPFFy38MuixxEpTfr99qtBXQ0gnBODBrsVpU8b2U4vbsbKjJw+7sS8gX3T5zZ+3MxNmx9snkdNHWZaELEnOIsdFZj5B7kb/u48mc0YnqLgSVzSXF8I2i4VJ9/RLo7mEjswMqh+Q+02Rs2lQvhCK+qpQug2YN47Iae922g2F0BJzNmMRzRgOnOqYY1m3uAxy22t/Z05VDcp94XMlwbSvM2LpM4vcgXEDMYMb2un0HhwREiZbhHKKVUlgn8N7Nm9feazY3h/YPBzkos88rh+Q+YBPm5/+ibRdjRbM+G2O4hPS8xKzswnl4/SU4yOogO8png7l88lzzUagbj+A783BwS5xmuyuH5D5wg6vha51iLPV0jMAZ5IsKXBYq7DxZ8yUF5A6jbZvnHLgcU7mkVvD9+/eXOcAlTrPdlS/AfeAqF4r5YTjZbOpSQBcFc1hj+2g8mMCVzRCxhlkBr49qbFNJllEEF5KaNi3ZLaSWoOVR0bEWu7q2czTsBiKBYyFxSYTNVKcNTxy78wNf61/jesrD7uyz5JDcBxYJZdnwGazXBC+Apve6Tb/KttVD3sR+H+ltHG4peDslbwPRKbVsjYXAtGDGMCs8m2BWaAb4xAHAu918ppAuJttIH44N3fn92wtdLlwbQj4tKPvdckjuoZ3JGs1vDtuFyzOIK8BF8NQ+O9WnVmANNJ/MO9g/gvong0Ha7A3qzbF2XTiFMbkxQWDOSSeCdBp0RnAGcTrIlc1YgsYnFsXv1sG04zbnCJITZyuVM0VxaRPGukAOyex3yiG5h957708bs7Mn22WhWRNPAmeA4xoNTfcR9THvA/8QI2/H4HcqdD/GahBjvz9UERqNRrcIjTVXw9XY0AOn8D6hnkrmmFI4UyXOCs5IOs2oFkyH0aLvXTigQ0GBEtMhaC6ofraYTsMP17cewsEuUpU9fTkk91A9fbqx5eFkoyrmQqFTss8iHWf/vS+D5PQ+Kf2/GoZfFA3NT3d+vAwThjlDxVtv/WNotS6q01kI7XYjlmWMIZwMzUbV3k7FuajGWZNecuL3FEbDbom2vRsh6TgqyqWOYE4OF8rEZqPBOrD89H9+dpDtt4vxSDnbGrZTiCdTpWcxs4gxoNxvNbEFdZA2HJhP1WBpc9Ob4+Nv/frscA1v/cbX2lc3uwsXXBX1doQa0Y/SisRFW5fA04axp9t7Hk3i2DTBJwJ+PgXWXOvB0/uZ2WGRT5LZQ3VdjKe6PEeIlyzP8VFA7jvGDOsUthsNetsn4+d+jvfd795Iw+HiejtyvwzppkL1fyfSfzDp76z0C4l5wdbTbPxH5CJIcyHGF8qo82WsJ+1RPdRd+fnZgZR7knsoFWUHpzNSuKjkWQLlfqzVbBAiSHWxvT0sGhsbnzvIv/c90ve+9++3gC2bVbj24cICd9WeiIEwljBCDUbPKOPTnMwJUsQ+5kRAeh9p6r33Ljc+/PBcDQe/ql/2dOSQ3EOuU0dwmuALSDN4n74fprQ4XSi+3Gi3QwjN9/lyvT/fuLGQXn317Fas/T6xjnLYBtuixEwgTfCU/l3aDjYtpAmTpl15ZmLin09dudLbstmSyCeYZ79hf16UR0QMjNk6lcwF4XFpn1Y7FIXQKYtXrNDvpbQCPPzC30YYblR//ddXt77xjelbzdh51HdrQNK4xIyFBWN+ajcLSXLTo97qtChmxsaKaakwXO3B4SiBmj1ZOSR32ej517VyYYGG7UnEVEATSI2Pj0LbX4xL0Mmg8LWELYrmysb/ctJOVSwYJjNMKQzqNByoCN3YL7rd7srg3DkGn1ba9erVGzW83oWL/dQdu10F/5NRJPllw/jOxFXgiS8P8ujwC5BNB3ysqjwXQhzC3NqT/VnZYZFDcpddv34t/Mmf0I6xMVHj6WCNS2ph4n49cVyjw35PQGoFmJbCeUjzCqGbanVlb0aljRiKVQ/qh1XdezA93VqF3gaw/RvfT/jNN9+qr159y1eufPuhGvpxiNoQKgXPgJrg5tOpIy4BQbgNHKtVn6Rg/cMPj1pBtezzyiG5yy5evBWaza+P2eHYsA7ThDAGNEd/u/8CckcBzNiasZiTfMHWBmbdTutGq7JWDIsU8X1bY5XSg6Xt9oJ9bRlmKvh+9cl90qMJHdKP3Fg6v7CyWU92NopB+RzBiyKMGYQpn+yvIbHzIltqKzATFOec/KA819qXvfhs7+WQ3GWvv/6HYXGjO1kGTiV0PNjt/bUD8TPYhWEMiKODK5hEHMdsh8BGMueLMr7kFO7IvL+0Hj5QOXx4rP2dh592PNnrnK6ZWxksLoauGn7gFN4lWJjzjGa8nwrhhuRJiWOV3ImUOSSzT5VDcpfdv9+PzfE0ORiGM0Xh40atAxSRjOrsOAItwaSlBCQUElAF0TPugd6T+CdiGA+OAEt8yvFkOzWxh7/85bXu9MmpB5h3ZY2BZ4CTT+/XoIGZAh1vSGMVRQ7J7FPlkNxl5ZmVEDenOpJnSZqRaO7fUfanerwbKMKvPiCwbaBjqGRXRglCmUj1xka9Yf/rR7dv11vPPfdver/2PX3xIoPVVS+Gwr9IybOE8By/WgL2yb5KpmkxBczaodNdr/MzyexT5ZDcZZFGcAodRc+CppzcPFgZ+btJCoLCMCtTSmEC3K9hY6Vbl8ePp/vAr4ckMFOlNFys+3VRNMpzxptP9xmtGiSmDXMVjE8p5J5k9qlySO6ysFoGFamdHGYEE+hJT07sJWnnwIoImkJMGaZILDuxjBnUKWwwGnr/mu/XdX1txS4GwcVD0IbEEHh8pNoTbqobRpO2j2HGtsL2lwpJ+9rO70tcXJwoiiJ91COVBofp/veZ6lr1cLhQb28P6gsXqKTDsYsph+Quk9pKGpbCLaDJrpyCs4dMiXQ6FPFlO2wS63u/7TPn5hgsLFRIaR3FFeFVQ5udiaIn2y4Vwi1EB9wY1xfv0NvX4vr65JSdpiHOhJJjKcbJ0VKuFGDs0IdkRB89EinkzbI8u1qWrHa7cclm6TAEZQ7JXSYNpFqlg9p6amsB95FRT/m0TQO8iP1Pn/ppwnB9YDNc3fzLdfCqzapGq3ZafvILywtQW9Cx1IAv1euLdpp2DOdIfjYEXRA6DY47tYkOfUg6pI9CMkU/wuGuynSn75oOF9aAHJLZF7OhoTo0onBjZ6Z4Xx2L9gQ9/qUio8N1gwmzyUw/fPgXnZMne0O4Pvz1GjMSXlrXQNAVXk+4rZ0zNp5w87QTlKVIRb8/LGzC59m/bV+Lt28vlI8eFVNFU5dl/R6BZ0U4bZgFBYvdOnV9TwV//P7ZOiU4iYuTgnJtreotL19bmplhW7o+2Mt2fhU5JHfZJDDEcTSpweML89CSELjp0XbAqShPj01qemVlZvOv/upa/Wk1ZgqnKgVtgTbC6Nlm8hMv17Wzu0kETAyhFeFqePPNG3zve787KG/TKY8fb3cqlXOSXjK6KjiDPY7UHm09lY5CSFofD7cln8I6D342OeGCjVR34u1VFoAcktnns0FLLVJAKvBoH/Fet+lpsgmMjkJrYCZwnNruF1PNZl1du7bQ/fSvUW3TB7YZTd48hYqGo3G8TcTEoBTfe68dr1z57J81vhjKuojjA+lEQ+Ey4puIOXDAO/eFo8K/8acEOqUQ5hnyQUz1ZqdmY28a92TkZQ97IPL4hfeRup6Qo0UrxeFYv1834IUD+ds3Z6uGS02V0ccldyRHDvnN7gsQcsC0CZ50jJ0YdaBXcOSe5C6bAJKCwGH0BOzodDxsCrluYXeqmBrvvXd3X9ykgwCSLl+Gy5c/+/P7i0UzNqspJc06qiMrIh+Rd/GzWKPHF25JcTJRd/oc7GVuOSSzXTPaXaSZMoQTllYvXx7/lZD8wQ+IL730UkwhtYPCuGEC0+Ipj3iSIRD83nvw4x9/9ue3Wh72am9FeV2OW5YHQtXOSoUjHJYaDbflga1uVXsVh82ycXCfR0IOyV23AXScjJRINnoaM7f7k0dLbuYszmLmFz6xrGc02fGnxfLysebOCeUziGOjImFPLyQFRkrbdrp8ebv+t//2s59J9nrqFcVwsefifitqWXjLMBn0+Bns0TRaGeDKuOekZRIfVvajann4G8flHSQ5JHfdBjDuhK3R4RBPYVJi3xoDTmJdcGI+rbXurq7+D+WKG15ba6tb98blaryZdLoWJ4RmBO2ns0zK/qjnAym5Ttev3/B3v4u/973f/ZXz8xv9dpvVqbnGA+MHoPvCjBa+f7Lq49EagtsMQH2Zh8k8INT34mC4dPLsWA7J7POboPQQp2CGxrUUjkxICsYx5xFRIRSN0JqR0+qkNYC+W8TjpjhO4IUAz4E7oxPbn8ZSGiXJtdEQq2om1Tdv4jfe+Oyb1pUr1LdvL/TrUKyo1j/FUMrWaVKaQZqwHUY7bg7/EiB9YseNzRaqN1CYt/yPVR0fbYRBd/7myoFeUJ5Dcpd5onTYUL2ztKWCI1V8asKijZmVfJw6XbS0EtFGItYhcCaZswEdR56R1AHLOwsanySJlEwlPLCpUivUn7U+8uOvvV7bJHhpZWHhyj8Sx++GEE84+BROxxWISS6OQkia2gAB2cnrAS1Fp4XBdvWwrpbmL5/59z0dP9ijpRySu8xr23Yx1hdsCG1hV0flmSRQCBUSETglqYm0abMtqC1mg5gFjwHNUUGwp/PaJLsW2ga6Jg1M8YUuZAnbbw+73X+2Cu41p90tEmtlocm6rqI4KsuCRtsSVcigbhpW64mw3mho48SJdv8wVKDMIbnL0tR40hbb4DUSm3zKQbSHnSEixmUVmBmgsvHo0A+1dvZ7P9U97YKhYQunDYnemOsvfDGPgrI7BBLMVRsbK91Bv2z2VEvUOyV7DreWRzeXuoa6TsNmc2vQ7zNYXt4cTk//8MAHJOSQ3HVe7tpFqwdhTdKm8PAo9Dd+TcCMGY09/h+jgenuvRC2KqALYS049dYpv9SQcKcaZM1o293mk2xjtj8c2eUKe6WuBymFtI3qlaS0YelAryE7qCQPhNcNyymwlb5ETzI7GnJI7rLhcCYpecuwXMCacA7JPWA0QKyDl5XYqlIOyezT5ZDcZWfONOuGyjUl7teJRezt0Zq9xx/ZbhDuA2uKXqyDuuPT4TdOI8oyyCG5B35Sb6m32q+Gd02aR+qOFjUrB+QushlIXg11vahUd+v5Ye5JZp8qh+Suu1EPV3sbY0X9UCEsIrrgo7Zeco983GOX6DmxWtVeVEibw2Evv/7Zp8ohucskmJ+/VW1sDHuyt2Q2bG/Y7oPyhfrUKYEqTFdooQzc1zCur62Rh9vZp8ohufv8rW+9NTx37novKXUT3pDCmqQeR2sf915JRpVRt05e7HYHD6Tt9StXckhmny6H5B6RMKnsijAPfAisQr5Qn7Jku4e9hr0SIitjY6xPTQ17cD334rNPlUNyD4VQd43vJ/M+9rLtA30QwP6nhLSJWACW6lrrCwsrWzduLPxGQbIseyzvuNlDoVDXQz9Q5JbMCczw42VAh/9whN1mXAe0Dn5g/Ah5/fnnf9jf63Zl+1vuSe6hWPW7tav7VOl9JxYZbW1LeTnQU2JVyV5IKb1L5AOCDnSBqmx35J7kHup26RZF974bYw3RWAT1wYl883oqghiCHkn6eYj6oOn++l63Kdv/8sW4hxYXe0Npc2N7MFgyfmDSHcO8zYE+yXkfGhpvJXstpTRfD32n3/WjwaCztdcNy/a/HJJ76MqV69WDB+O9huMawfdkvYN9VzrYdYr3G+OhzIbwovBDqb7b73cXpqa2880o+0x5uL2HRgeSXh/Y/9vG5ubgfo1/LmnM9nHEqV/5zOwL+ngffIAtSwvA3YTv12X34bvvXl89cyYvuco+W+5J7gO3b29VfZiXuQm6pcBq3s/9JGkF/PO69lsk3ymHnd7Vq6S87Cf7PHJPch+4cKE7XFsrH25tp+1GZ+x0IKyNts9ZHIkSAE+TjLyM/TMV/F1ZxA8mmp3tw1BWINsduSe5L1xPU1MrW41GXCbontEvTPq54RGjYmHZF5ew1m0eOHE3mQ9SSne2hr1V+EkeZmefWw7JfUDC16//sHrw4Me9elg/BH5i6e8Qd0a1jLMvThViSfItBW7FkO6Wqffo5HhvA27kkMw+tzzc3ifeeIMa3q4Xt761UPfrd2IRItBBOg8U4AL0VItjHRJpZ9KmZ/NIgV/gdCui+xPT/25lrxuXHTw5JPeZ0NverGLzbqqbIUadBM5gn0eaASb3un37nyugj1gG37L9FuidwWB7da9blh1MOST3mb/6Kzbn5j7sP//82V5ronUmSs94VGK1qRySn8lQCbbAS8Lv1Wn4Iw/S3dnZtbW9blt2MOWQ3GfeeGNUovSnj66tzql1K9mTEaoAJaIjUdpqkJ8nf4INqg0VZj6J9yX9HPxOqP1we7C6Bpv52W72peSQ3Kd6d271w9e/fis6bDg1hsC00QnMOKP3LYfkR2TEIJge0p3k9HcpVX8fxa00k1bPzGwO8mRN9mXlNXj7n5bW/6d/HkPxZzZ/JDhpcUqoaRM40mFp75S8qIBVm1XB3yT5PxC3/ma9X27+/XR34w1dzwGZfWm5J7n/ufDwkc0/kELtEF4hKSQ4JtECmnvdwL2jGjGU2TB+N4ifJ/yPJO6sV+VmsdntX5vOJ45nX00OyQOgqvwoxuotHBeNZHFKUgOIHOGQlKhtDwxryO8a/z+xTu8WxfDOsbF/u840zlsPs68qh+QB8ODBoHf69ObScDijRru4GUIYF+l5w7OY04aWUIsjMfS2GZXfrVNiAbiTzC9B/1hSv1uW3G+3+xt522H2pOSQPACuXLle3bx5rXf2bGN5kNLbIaVuVFhQoCcpCmYMJUciJGWgsj0A3VXgbwPprSLE2/2u7vb7G+vt9kwuyZA9MTkkD4CPj1SjWlz8l7fa7eZ8xUTPjg2LJnAWExFj2CW/8r4emmPWanCyGSBtBLFup1+49j/0U/233eD1c7MbazoikzQ2AgL8abG4eLpRls1CGkgaClq7+J73PnqcUdehTmk+9XqxWllpV1euXD8UBdZySB4sXl0dDmAWNdOd4FAQvCD0vKTnbc4Bp4Hje93QJ07u2dp4vEjcTr8kcjNVvFeFuB42Y++7/8f1A39Bfh6jVQ1/1trYONYeKp4MZTibVJ2QQploNCTv4oiitD061k+lN1WfXRufYXlsrHoIf/oADn6htRySB8jorvzDwZtvMvzv/vLaB2cnyvlWWb7TSOX9umYtBPVIboOOjb7Ch6UXCVZPpEUC7wv/F5P+RsP0YcFw+W//479bv3kTf+97R+M55I0bV8MLL5AsnVsAACAASURBVEyMjY+X06niUlGGb5j0NVtjksa0q3v8gxEJOyl5wdK9wSB9kOyfLC+z/OabDA/6+3J4LqKjRzZaWLg25nLiUizCpWC9KPg64hJmDjFraAsVHKwbYj0qiKa+8SqwEqx7iDvJ6X3sn/S62z/tdldW+v3x3ssvXz9Su2nsb7dWujwvF8+DXnLiFYlLaDSBZ7OLIemdw6GdBCvAwuj0Kv9dUv1fStfzSxOh+5z+TW/32vRkHaQLJ/tVlrC90NvYaH+4XWszhPjI1gfJ4WIIftXW7wXpuHFnJygPBMl1ShpIrAneFX7Hwb+MQbcwdxzqpdOTwyV4pg/fPxLPID/p9m1aU8fjBRJ/SNALkp8FnQKicYF29Tm0GT12tGECMydxXNJmSFoaSjq2Hh8AOSSzvSHdqIAlYMn+nx+t9uoPw7C+i2Mt6Nj0JKaxJ4FCogCiR0Oy/TAbnkYTU07JqrErYEvyhtEjwU0rvJWSf1FJ7891/s8He93gPabWrEpqzjjqFdmXDLMSUzt/vdvN+Y0/2kxBumeF2wGvDcvhgT6BKYfkofJgsDkYXy89fq8g/b2JS0GcRT4l6ZThhM1J0KQCY5j2XrdYYmi7Z+gCy+BlwwNZ9xT4UOaO5DvUwwWGw+5et3cv2ej6dULRGxZqtRuGtkUT77dzRi2b0rjtpGYYep+174vJIXmo/HDwt5PXqpfY3GwuNxYnhuGf3IxnguKFWOiian8dqcJOThSS9jwkbYaGTYlFp3Tb4n3V6R3sn6Uht8qyt721sbS9uDg1vHLl+lEvZaGXXnopDmK/jG60RBxDtKzdfAb5eUjgEjOWTKsMzX3Wvi8mh+QhMpr9Hh21BgyAjQ/X/8e6LQ+Vym7ttBEV5o1OK2jOycclWjZtQWvnwX8DXDAalhe2InyyJ/A7n3d9cglOAtce7Y5JglrQN/Qw24YtoAtpDWklmcUYfE/4nkK6U1X1Bw8evDV/5cqVenLyPx65546f5rvfhe9+90RaXGwOHcIagQeYjnBAan3iU/dkQlaiAleGTdCqEgtFwWrVHxzoibUckoebz04sbH64Pv5grBxfx9yrEz+RmHXyCcGczWwMzIKOJ/s4pBlbbcwYqGm5qVEw6ostKXIN6gsGEkPD0PYqsKjgR1gPbR4EWIK0UtX1qqR1Kaz3+72NpaWtjevX366uXHn7SKx9/DxGS2lu8Jd/ea3fbrbmA7yroIYTbWBmr9sHVLa2DWumnpfqDypX81tF2trrhn0VeQnQEbS09OeTw2FjtmgzF1WcsXSGlE5LnLI5IWlcMJ6gI2hbagkHTARp51/NJ//t7ASZDVgoGfqC7VHP0X3LPZtF2fex74UY3q9SfbtopsXuYGltsPTTzQsXLlQ7E1HZ7/Dw4V902pPNV1yFV5F+L+FvCJ4HhB12dZeV/ImbmLtSWMO+Z/k/lQz+U0rcm5gIXeUlQNlBsr5eDo5dCKv1dqxc113MI/AtKU4Q07iTWyi05DRmMybUFmo40IRU2Crg4+dgghqTQJVhaHlg08PelrRtPBDuB7wZy7iWaq9ZWg5ltRwG6satQe/27dvVhQu3D/Si492yuNgbnm02HoSQqO1NhTAPfhvTGJ0OtZs7bh6vk8TJbNj1ioIfinCz12OpqtybmLh9oG98uSd5BI32/V4LMBNgEKGOy8spHjtWho2NFCXHXm9YpNRslx2NuaYTg8aS3QkqmkluiFh+9P1IdbAGdhokp+1a3qpSva262lbUdtnQoFGHQUqNKqWlVFWp7s02q3lmqluspJvfvX5kdss8CaP37zsFUK5sM5uGw9NBxVwQY7Y7IuziREmyIdU4RbRqvFg0vBiqsNrp3FuFHw4P+olMOSSzT6M330Tf/vbVxvT0dKss280Y1ZJarapKjUoqpfDRKMQDJztVKZXDKg56g2qrFxpFvzVcHRw7tj0A8jD6KbG/M7a1tTW1tcVkUTRaIRStSru55KY2DjZOw6rqNqjWpMHGzEynD/+mfxgOuMghmf1Wo+1t1yIQFxf7RVmOFyEUoasYguJHQ7ox18nu2a5SXVMPBq1qezvW3e7fpbfffrs+Svuqd5t9tZiff6bZbMYyxhRDGBajwpq7pTBAtwuDwdqwLFv9xcW3hleuXKmPyolMWZZlWZZlWZZlWZZlWZZlWZZlWZZlWZZlWZZlWZZlWZZlWZZlWZZlWZZlWZZlWZZlWfaV5FOADqjRmYIIrgaggLkCiOvrkzGEFLtUkipp50QYqXHg3mt74DEK233bVbLHUkp1qqpQDwaP6q2tuv7xj39YvfEG+bSZ7Kk5cBdONmIT4FqxsLDQaLVOt4bDVrsoGq3tut+KoWhICsIRRe2Utj5w77VJxk5FQZ1IVZHKoe1hXaZ+lar+1jD10sr97eeeu9H/6Euy7Ak7cBfOYWcT3nrrO/H48UFsNBZDWbZDjI0Qo2MIRYChtlSEIqqsBm4UITadwnjhMB6C2pUZk9RUdBxVPZRSnQKEA/heJwdUY2rD0CENkmNfIW0rpe2qHnZR3OwP+9stt1K7rdquU0pVSmmYqoq636fu9TbT2tqjdOvWWymfbZl9UQfwwjm09Oab6F/9qz8dP3bs1BSNNFkkjaVEx7Ecr50mg0JHUjPILeRGXakpuSHUsNVElMYNoUKyBAGk9IUrHe4Xj+unOGHVCq5sPS5bOsT0sfqGfpAGCmmgxFYK6ip5kzqtS14bDtUNIXSLwlubm7H3/e9/v5eDMvu8DuCFcziNepDEZ5/97+cajdZZKZyuCcedmAWdQD5F0BxmQmJCqGXcBJX6KAQl8+vV8h6H48F7q/Wrw+edsnwfBacZ1Q5IsoYW25K3sFYMiyY8GlVmrO4NKy+GpKW69nJV1Wtnz26v5lOzs8/r4F05B9xOEa4WzLaWt4edskqdFIuOUz3uVI8rxuNK4WSCOWAKM0VgRtZx5GnEGKaD1MCUHOmKlzaQdj56ow9tIFYFK8ksghec0ioOa6DVELVcUC+HEDdTSttFMewOh43NpaXB5t9f6A6vcT0dhros2ZOTQ3KX/ehHr5fnz79yPLbL41HhlKnPOoUzEieNTwUxaWscu4NoYJpAE9GyaYEL6XFJVwVgF8uH7je/2qtEqrCHMBqCC28D25g+om+0HfCSYSklFmTNK/jBsE53W3F4Z2npTvfChblh7mVmn5RD8ika9RqvxttQ9Bcny9ONZrlZxU50+4xicaYIuqDgi5jnFHRO5hnEGFDYR7mH+MQ97hkOBcvGy8B9iTuSblcpvVuHwbv1IKyMT6s7zuY2dCq4XcGNdNBLomZfTQ7Jp8BGN24QJ154vfHs9PPTITVnIuFkSvGMIicFs5hZW7OI48AxxLTENKZhK3Kke4hP3OOQrIEtwRawluxVYFmBecO8E49sP5KZrxLzLvsPGaf74VtvD771rbeGe9f8bC/l3spTcP064bXX/jSeGB9v9QeNk0bPphi+TuAV4Hlbk8AUUmNnmU4UROxiNOli5fvXUxEkxsAtoynBWaDC9GV6wD1Jv1ThXxQpvW0YDjd7PnnyYoIckkdVvhKfEBt9yLXWBLOt3lpvplA9a8UT0eE84jzWRQVdAj9jqy3RBu1iEfns0300+VMbFiXuYd21+GVQ/UvXfpCcHkV7IYTB2sTEu2vwVpUnd46O3JN8Yq7GxqNisi56xxvioovGiyQuK+iU4LTFMdCUUUd63GPM9gcJiJhJcLQ9Y3MuhfAy4k6kuBWDf1mF4hZ8bQATW/aNOgfl0ZAv1K/Ivlrcv/9CY3Jy2OnVPFOE4pzhCtZriK8jjgtmgXKv25p9bgkYggfAHQW/I/iZEz+p6P9TE5Z6vbXtD2bv9W5xMb2RZ8MPtRySX9LOARNha+tfndiuyvNyeV6B57CfQ3oG+SzoJKYjuZOH1geJDaqNK8EKsGB4iPkAfBv7tuX320X/br9fbk5PdzfysqHDKw+3v7wAl4uBGycK6ZXk9E1Zz4NeMJ6UKZFLdNTXMh5UjkJB8nGjqQDnDJcRKxD+0cn/uTtoDkPyPMx0IZ9EdFjlnuQX8HhoPTHB2FD9k5FwEuKLJL1q8XXgrKVzgubOl+TX9/CogW2JLdvvCX5i/DZBt23fbnbS4gbDtVP6v7p73dDsyco9yS/khUajsTVV18VJKF9zEb4BXJB8Fukk9rjya3pIOYCayUShZw1jNs+o5ucBnUy9+O6kq/eAHJKHTO7pfA72tfjee5tFa2ZutlUUp8sYLxr+a8S/EDplGMeM7XU7s11TAxWwAf6Z7Z8h/r+U6n9Yqzd/3ugyOHfuej/v1Dkccq/nM/z1X18t7m8U0yeeOTNd1+F5rFdqeCnYF21mbcZCcOF8vzlKBETbbaGzEhGnhhTHZppTxyl9B/78jn1vK29rPPhySH6Gc+facdxj0+7pPIFvIF8N8BqoKdxCjnZe83i0WECUaIHPAiesMBNgxuZ4sv5+aTuuHG/PDW/cuDqEGzkkD7Ackr/F3bvX2tPT4+Nu+Hhd8TWZrwXzqs0FpNnRZ+mj/2RHyUc3xbjz0ZQ5gVyRiFGu6AetDcZvv/RSce/NN1n47ndxXnx+MOWQ/C2mz42P11vxfD1IlyS9ZuubwDPicUBm2ScExrBOh0AL1EhFecKkHzcazXTt2ksrcKWGvJbyIMq9oF9jXy3gQrE50MV6EF9J5lXE61ivS0ztnOGYF4Znv83QsIhZDPLfGP/Hqrf5n2OsuzMzbOZF5wdP7kl+wo/8nXJpqXcixXSiKIuXZH/T1iuSzgm1RstA8o0l+10csDrINryQkreKZmciuX4HVn9uX93MkzkHSw7JT3idlWI1Tp4oi/BiSn7N6A+CuAI0kJtAGB1NmHMy+63CaBsqLcBBoWNxAogr2xP3Z9plP0/mHCw5JAH7WmNlhXavN368KMLztXld6CUFzuyc/cjjQlt729Js/9s5UWj0MWUZ2Qg9dNVYWN4Mt775zUsP4MbyHjc0+5xySAIrK7SrqjzR7fOslF4JIfwB0jNOPiYdxFKs2X4gueGkKQtjXgLVotEZiCGQQ/KAONIhuXOSj5aXxyfLdjzrxIuSvg56GTOj3HHMvgJbDYmGpMJwWaJhe1DID+2/uAe9IVwf5qVB+9uRDUkb3eZqk9Xp1mTJMyn5tRDjN0m+gNwgdyCzJyeCp+sEMbAks7Cx3RqU6txvta7dh+uDvW5g9tsd2ZC8zrXw+6vDViO1JijiM0KvYf4QaWqnjGuWPRG2C0nTQYzb3rK0GWqqbQ/VarUWgByS+9iRDclrdMrlwmftcFnwKuICMGvc0GgtZJY9IZJNCZSGOZnnjSpZm2trxYOFhX+5MDt7qid9Pxcb24eObEjevk1r+ni8lNAfBfES4gymiRVztcLsqTFThkvgpgILpvig8LG0vNxdBnJI7kNHLiT/+q+vFpevzpXlWj1DiJeC9S0TLpA8zUeH5eaAzJ4OSR2gg2mD3se+lWIYpIb6wPpety/7TUcuJF9//fxU1Q1nFMJlHC7KzIHHDY29blt2dBg3bF0Q/GFUUdaDtP2jH7F46xbpjTdyKYj95MiFZCrjlFxcDuIbNpeM5oAJch2abBdJagguAJOQBjHo9uuv//N3Xn99UNlvpbwsaP84MiH5+OCK9fV4AvGCxSuGc4g2PjqvQ7ZvxAQTmFIhnC8KLncHVx5sV2nxg7HXFyBP4uwXRyIcbMLCwlwrteuxQuF0JL6AeRkxrdGMY5btMiug0pKUfCopfF3DerNRx7dfh1XyJM6+cSRCEq4GqTnRUJxNKTxD4DnQc2DZDnmiJtt9ktlZFiTNkfxCTeijtHbv3vCWTW9nyJ3v4XvsSDyHu88LDTWazzjF35f8kvHxnSP4czpm+0GHoNOIS5bOTky0jy0v//n4T396rdzrhmVHpCc5tjpoqCifSfD7wEvAcY7IDSLb/wQd4Iwlgnkb6uMpNbuzs6Em78bZc4c6JO3vlAsLK80Q4mxCZ5V8icBpoJOPPcv2DVGAx4Bpi7OOel6lklKzJtfx3nOHOiQXKJrDonWskE5jn1XQWfAsqL3Xbcuyx2wCqADGgLMe8kpQGNqsAvN73Lwj71CHZL253W6E9ixB55R8GjgJmt7rdmXZrwlA2FmOdlrBXxdajsG/3DnOj7xucu8c6pBUzYQC522/iHxCo7t1lu1PphAcs3Ei3aVOswsL1zpra5tD+4eDHJR741BPXjSKOI45D34RdGJnyUWW7VMuDMeNLkp6BsJxu+hMT5cN8kqMPXMoQ9K+WthXW/WwOhbksyQuyMyEXAo229ckoBS0nTiGdTbG8tkYp2Zu3ryWR0F75NC98DZhfv6ZZj3Wbo81dcx1Ohukc+BxpJgHLNlBIDFu+RnC/9/evfTIdd75Hf/+nnNOXbr6wr6RFC+ybMlyRrSRcezNBFnQy7yAXgyQCQJkMItsAuQNyHoDeQEGEhhZDl9AdgGRRQwMoontmM5YoiVaokg2m2Lfqtnddc55fllU6+q2LMvqanb1/wP0gqyu6nP91fOc59Z5tU20i4v9J0R3oFMxdSXJ27dvpnam6c922gtum1XBJcY/c7ajJBnOBmtWKV0tCl5O0kqvtzd1BZqzYuoO/LVr/aJycSHv+7qTLiEPJBLxTCecIZb7wEWJa4VYoIgv+NMydSE5M3O96JR5QY2vkXQRNMMUlpjDdBP0MRct7cq+kNJshOQpmbrw6HSaoqm12KbiRdBlPh5d89FPCGeA1EGal7RMSksHHi0+evQ3g/GUf2GSpi4ky5VcqMiL4G8Alz0eFxvC2WI6xrPkvNTmvFIorYyKemF9/Xqs5DlhUxeSxe5hWSQWkK8Cq+O1REI4c0qhGZTmE1rMFKulZhd6vdlYZmTCpiYkbdKvvNapy16/dZrHWjKaV4oO5OEMM4XtuZS5VCQv1VXbO+1NOm+mJiTf5O+KG/SqKpX9JM0JliTPYcU3bzi7RErSrApfrMq0WNU5QnLCpiYkr63vd548qxbqESvY80g9jYchTs0+hnPIFBnmBS+IdqUoiJCcsKkJkH6/0y0OtZTGHccXEnRsCin6R4azy6KQNG/rak7FSptSPGOfsKnpTjAaudftpsUsLmHNZ9NFKhzDEMMZlkQyzIEvKbPcEiXJSZuakKwq91rSMnDZeF7S1JSSw/llkwR9oQuWZiscDZETNjUh2Rb0SHlZOb0Amidm/AnTIWUzg5Jxnm9TiobICZua0laSqmTNQl6Q6HmK9i2ca0JU2DOYXj1qOq+/TvpoxvJw8qYmSJomlc7qO2vOpquY0CJMBUtQSnQRXZVUa2uvlbA2Nffu825qDnRHLiR6KdGX3YlW7TAdJMaPxbqgrqTuxYs3OnfvDssoTU7G1IRkIxe2O7Z7QElcQGHKSLlK9iAlFpaXZ3u3bkVpchKm5iALpZSolFIXURpHSIYpk0qUBnQX5uvOQm9tbSOu8QmYmtZtiSK37iMPhDpoYtOi1cgjoUPjA+wDSCCXsjqGGfAAFK3t4c9iuwJm8Giuar13597q1BRynmfTE5KoROoZDcAdgSbSj1weOWvXsA08AT2BnJLUR8yBLwt17eiSFP48Kamw6RfqDRJtp3vjSZQkJ2BqQhJRGHqCPqICTnCVYvsog01mT/Ij2w8EDxAf5OzCTrPIS7IyMBAYKD1NxzxMlLNLQ68o8kxD7rzCpQjJCZiaG7ZtXSipst0TKn2iXYBkidqmBr3nnP838CvjTSeeiiRS7hTWYkveglRjXwVWkBZObrvCNLOU5FzWI3eSXdy/vxchOQFTE5JCSdBB6jJutDnJrpIeB6T3kd6T+Rmd5n/WLQflYG/fTztmfqR2q7qQqv7IzpUlg3pAhGT4SoSFXJYllRuKa9dOe4vOh6kISRtt7rYJysS41QROdoHtLBgaPhR+1Do/WurtrcNiAz9ttDz+4/Z/aIfD0YPWvCuxCH4heiaFr0wSTkXOuUxSevBgPy6mCTjzrWOvv066fZtCKNlO41LkyXb/EW5t7wgeOPtxqbQDt0bwk1afehJ6//5G2zTaanPxntEjo2cnuV1hytnJ2UVRUIASV66c9hadC2c+JG/cQKurryVQ+uyqiCfXBcgoI+0BT4DNnPO+RCuRP/17167RjjTaTUV+BPmp8cFJbVM4D6SUlHJW2UgpInIyznxIngZjsHPOZONspz9Yt+9S5bp2NimnCfVKCiF8fc58SK6tQbc7UosnNoOkhEnKKtSQipbO8SF55w6461yURZNE6xN+UBpC+Pqd+ZC8ffumyvKaaJOco1UkTLd89My9qmB9PRpuJuHMh2QIIZykCMmTdgClW+eccSy4E8KZEyEZQghfIEIyhBC+QITkCXN3ZKrWR+O9o74dwhkTIXmCbtxYNAcAydFHMoSzKUIyhBC+QIRkCCF8gQjJEEL4AhGSJ8y90jiZRPSSDOEMipAMIYQvECF50vahbmpyzjG9RQhnUIRkCCF8gQjJk9YvbCcbWYq+kiGcNVOxxs3z6y3nvWtt0S8PadIepTaxnwA9ST3bR2txHzuLegZq8EjSKJtaosXu2OoiKkHFOT6HwqNsjTQ+Ro1xM14p012kSrgElfaXLQzYoAy0wL5hH+w0LkyMlyz+4+ctTJlze4NNwu3b8OoP2nq27O4DWzn7MeKhYRlTjZecOH49HkG2vY+0a7Ob5F2bETAPXhDMGg10js9hNiPkLcMO+MDmQImexALO87b64OLLr5opg227Bj0F1sd/xh1Ez2jJphQSOGph58S5vcEmYWNj1S82Td0td/bVzj5NpPeQlmRG4xtPA6HPlQbdClqPBzRugB+BnxptarxGzjLSCmhV+BKoOgradD5KNjaoFTRIm7Y/ANYtnknay/aszIrEMvIKqMDu8AePzyc9s4wOhZ6BtxG/k3Qv55yV1MGelbgGyJm5lOjYdCa22+HUREieoLW1W/nevZuHiVXKUvdysrPTY4kb2LuCK7YvSrrwybu0n/E28mNJ/9fZv1KhD914X8lNa8+TNC+l78h8H7sy6gq6nOBC488PtcC2Ycv2W5B/6ey3kzRSSoc493Gad/JFO31f0l8aLyZUefx44rjPNONlgh/K/o3N3US+n7M/KFJRi1zams32K5JeFv6Gs64jLk5yz8PpiJA8QRK2bx8CI/jXB0+fLj1MM9VbHpXbJI1LRKIPfBySwvuSHgNvI37WMPofo7Z+OrDa3VyrV871cl30C7X/MiVdAF0RRlL15Z+9nWktZhvxgdGvWnN7e3/3zf6gn2fbJpdFUdUlvVyXLyQkpOsJ9TJOR6X242RDg/0w2/+A6/+VCz8a2Y8O24N6YQHa/ZkBtb8r8rrNAdKsiJA8DyIkT9jR9GiG/34IHD7y37SpTu8nymWJedlX9KkCoGHf9kYS77ltHxRzvfWr+m/bADa6c+e1ql25Vl0dXP0Al+8ncd/mBcZhO/3nU26wntq+J3PPrR58+4VbGx+9/Pd/v1Z8//vDcunqZdPyUOIR9oygAHrHfGC2fSjYBzYkv1cftu/Ue+3WW2893PrRj243AO++++/2V1bK39XZRSrSMvjbPtnl3cNzYvpvqpMjZyeE/pRa7iUuNE/Y25D8NuaSzGuffrutfciPLd1H2mo2NtuP/6Cw/esGLubtZ2zZ+X429yR1s1nVOahtO6tF/lDwWwru2+3w06+vrd3KQL3LX+97b/A00z6w08JRye/3HK2V/iybrSQ/aczGbnm4kVYHhzev3P742L/00r1mOLz+YU5dcP6mSHsnvKvhOXEeqmdfv/H0uUVKlMKlaL70cXzzzcN8MGqGB8/yY8wmGs84+RHJI8QutJtKflavLubPvk6WbjeprZ6R2VJKT0B7Gj+rm3oSrWDoxGMnbxaVPnf8sERuNufqnHmWnbYlDYH6uM+zjaEBDjLeQ3nn5aVb29/UTw8+PUnyj7mdd2Y3hwcePSZ703B4snsanhcRkl/BeMYKZrJZzpmFti2+dCvnwg/eT90qzRSdvIxZwHQ//bpQJWsWlxdym/rVxuax56hNTRdr0U2+BMwyrk6eBwmpR6sLZM2W6fjnjCkVyfZA9jLOC8J/4BxJQr2UmMeaL7Jm3n33Zs+++Zla1o9Z09zuUn+2owskzeoPNgKFaRPV7a9AkBAzwktZnv/DN+Dv692fTcwySCqWU9I8n3uvTQdpjsxSUWjGRefYkExJ3WwtJrGKmUWk8zDN0NHwpb7QQsqaHTXtscc+pb0E1UzGy5DGX0bHP41IiB5GSZrPSoO8sNq9xwCb9pPS5GKqy9zPB3kxpTQnRUieF2c+JG/evO27d18xxbesVHgyk0gokT0wWkZ60faNzb1/+ywVaVi2neFwmPPn31HMjcpy1OmMrIWy8l+o9Wvgl7DmP3PzygPMFQr2sv207He2trf/zYdVVR3u7e23VdXvtW3Zz7X/GfI3gEuGOXxOSpJSKVi1/Z0WH5Sq9h9v/3tXHepOdp2SqjoV/Tbny271LeGLQnPG1fHXhiVUWsLOl8Hfu9CZH+Zn2nigv9t48uSg1UyRdnebGaxvFkXxku3vQFqc9K4DJGTTuq4Tly71z8HX4uk78yEJeHt7Ia9cStl5Yt2pk8WMoJB4OSUNcTVPow/aIt/vzfnwM0/AKshtb+AqzxetVpV5zUmvCV2TWPjMlS7NGl7E9CQ1uSYpFQ9HOW+WvcGB0UpReSU3+i7wbcwli57OSXX7qJr7gkTfSqVBhTRw9vBZ9rDAc665iHU9iRtGly3PH/WTPJbHXzDCuor4K7Usi/ybXtH8U+52atVtt3axgPwa2a+lQi9hr55Ct1RnsFLKtCkCckLOfEj++Mdw8+abhn9uSEfdbT5yYpGZhHpAT3DdtnBaQv6tGy4cDSf8ZDsaC+d5YFHOl0i8CvoOeMHQ/czNZmYEM7bnMDVJ5bhPYHrsxDNlX7HTFSV/C+lFrKXpb9P+jBJYAa0okyRaW31a/Tk4dAAAB+FJREFUtgulLbIWJV0DXkR6SWIJ8wVFLonxCUhKrOLUU/KlQsVczlSyRyj1iuTFbL6npO86syTpmO5EJ0x2MlmFWsn5wTnozfA8OPMh+cYbGMjf/UGRS6kBmqNxtRNplHL2zNHIiwprAfyiVP5eS6qVezIzluaAVexZS5XQsdspqQQuMm59fcHWUGJkaR5YEFrGzJ7s3j33FsAvp6Q5wwH2gT3unC9xQbBk/wnXuKkEM4YVwV8kFfOI1qZqMzNKuoyZR3Q4jZK7lS1GWIe2mis8jdLkBJz5kAT8xhv4P/4n2oxbSc3RpA+Tabkfd+LuGJZtXgI1Om6lhvE8aR/NJlNK6WgbfWw/S4kSuGixhNVKbgFrXDUcfwaahvP31YkFoO/sbyAyFFlyAhWIAlwKFV++QUsleCDoObMg6RXAwklSYnxdVRqftzT56razs2tyPswqGhhESE7A1NxkqZNGbtuh0LatGfCAiXzbqwAKwR+/Z46Pw2P/4+g5WQHqHvd7UdECoASVnz0YR/8w+E8/Sh8FX6FxaXEw/shju6H/qZ/9Z7NUG++1pJ2q0sHdu+sRkhMwNSHppqkh7Rg/FcKozzlpzAjnhF1jhmVqtpphPnjlleu/14sifP2mpjN5KvIh5O2EP7TzM8aT1oZwxtnjUVa0QofA7mHTbldVtQ+bcY1PwNSUJLPTSErb2XyIuODx1FchnGlHS340R0Mn9yTt9Bc620OKg//MrahuT8DUlCTzQRqR2RZ6ItjTeAr+EM40G46mcTswfkbOu/94+7/sXOEnB28oakuTMDUhmVKxl+BhhnvZ+hAYAS3HtTSHcEZIbmxvGb0v8xBp50c/olEE5MRMTXW7KPKwTdx3kwckvQIeCflo1umoeYczyagRbJj8Fk7vK+fhH39X+DpNTUlyd45nzf7+utXeU2JdaBd0AI5qdziDbKB19gj8OMFbqvxeSuye9padN1MTklegZqUztMpNt34E/A57HfPstLcthD+dWuBQ0g7WA2feEvn9olCE5IRNTUhKP2lW+K97o93hU8xDw7uIR1aEZDh7JBrgUGjH+EFL+s1o7/D9wSBFSE7Y1DyT5Gi+cLvc39zNH0D5S+wCM3Dygj4anTFFXwxh2nxqedvMEPHA5i7ivXafJ9Lh7ptvzhw7w3o4OdMUkgDcuXNQX73aeT/nplWZSqSLoMvA0VDFaMMJzzsZsZmd7yb75zj/rt8vt+fmXjtYXX0jWrUnbOpKVTdu3KovXGjX01L+f7nwP0l6R/DAsI0U3YLCc0yWdAgMjdcFb41y/tWozfe3tzf3pDei688pmLqS5LjKfa+5wEsHm+hBa/+fQsrC3z2aDGEBq8MU7ns482pnP0R8IPh5a+7Y+W7RNk/ur7/TnPbGnVdTGRTS7QbTfpD/+kG/6RoVW06pTImrHq+9XDCl+x7OtBrxICV+6Tb/Iuf6Tr339t3766Pmhz98M0LylExvUAjn95u9rXrweHABJfuirYHkb8lcRawidY5WK5y6xw7heWePq9dk8I6tTcYjan7etO0vVOk3Ksr169d/tn/aW3reTW9IAnfvbtQ3b7IzHM7mw5x+XpTecsv3BP/iaL7GecZrpkRIhtOQgSZbG8K/lvzrrPTrbre8s1/XG+1uvX3aGxjOSVOvvVZsbQ3mnrmd75TVXxakfyXpBx6vpHfRpn+0Cl/5ydIPE1pSLJwDPhoeOx5Fg2ixauAAeV9wx/Y/FPY/1krvLM3Wv5V+enDaWx3Gprok+YlbeThcO8xz1W5fnXdy00roQSp03eI60mXwKnjZVl/jJRliwt7wNZElRrZGxkMy2+CnSPedfV/i3SLrnbrRe21bf8jsvXj++Bw5N6Ulj+fy1/37a12gX831FkT17aooXhG8Kvk7znxL0gXQoonF58PXpgXtIfbAj40/wNyz/Yuy9M+z2sdFnXfn5t7bAxrpdoTkc+TchOSnvf466W//9q+63fmXryr3rpXJ10l8Q+hqzixbWhZ0GS+2VSCXoNL+eAGoc3ncwhexkz6a/lEZnDG15JHhEGloa6jkDaN1t/mByG/Xaf/ti4Nm5zYb9Y8iHJ9L5/Zmt9eKzU1mc+7Pdjrl7Mh5viw8j4vlnLWSpMG46u2+rb6lvslVGi/uHVXx8Dm2UAayUZNEnc0QaUd4J9tDxC5t3ik75Xbd5h2ntHUws7l1l436JrdbiRjk8Bw6tyF5HPtmub5+fakt+0vdajTnzKBIxcDOsyTNSkUFuZRShGT4rNZ2ciaTLUYpcUj2tuGp1W6mshzu1fWwnPPB/Td/PfrhD9+MMdhnRITkp9ikjY21mZx7M1VVdoui6hRF7jRN022TuhKF0EdrMIfwMbv1uJLRuihTYxdNm3VQtH42GjX7nc7ocG9h53CTfnODWzG88AyJkPyc118n3bx5M83NvaqFhfdTWV5SWe4ppX0VxaIAUjqI4xaOlXPPAG3b92g0ynt7e3ljYyNvbKx6be1Wjip1CCGEEEIIIYQQQgghhBBCCCGEEEIIIYQQQgghhBBCCCGEEEIIIYQQQgghhBBCCCGEEEIIIYQQQgghhBBCCCGEEEIIIYQQQgghhBBCCCGEEEIIIYQQQgghhBBCCCGEEEIIIYQQQgghhBBCCCGEEEIIIYQQQgghhBBCCCGEEEIIIYQQQgghhBBCCCGEEEIIIYQQQgjh9P1/fBBHifNSUKMAAAAASUVORK5CYII=
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAgAAAAIACAYAAAD0eNT6AAAACXBIWXMAAA7DAAAOwwHHb6hkAAAgAElEQVR4nO3dedxuU/3/8dcns0PmzERknmdFpgbFV4OmXzqVRFSUOYQKmSlRNBtKqL4Vqa8iEUWGyJx5Dsec4XDevz/WPjpOZ7jva+99rT28n4/H/ah0X3u/b9c59/pca6+1PmBmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmZmaTi9wBzMymRdIYYEVgMWDx4j8XBV4HzAyMKb71tcDLwJOTfD0OPABcCVwZEY8MNbxZg7kAMLPGkDQTsB6wNrAmsBawHDBDRbe4C7gE+Dnw24h4vqLrmrWOCwAzy0rS4sA7iq8tSJ/kh+Fp4NfA6aRiQEO6r5mZWT9Jml/SrpKuUjNcL+mjSjMQZmZmVhVJr5G0laSfSXoh52g/DXdL+qQkz46amZmVIWkmSWMl3ZR1aB+dv0laO/e/OzMzs9aRNEbSbpLuzTuWD+xFSUdKmiX3v0uzOniay8wqpTR9vi1wNLBE5jhVuBp4X0TclTuIWZVcAJhZZSStCXwdeHPuLBV7FPhwRPw+dxCzqrwmdwAzaz+lVf2nkA7c6drgDzA/cL6kT+QOYlYVzwCY2cAkvQbYDjiGNEh2nYDPRsRJuYOYleUCwMwGorRK/pukk/v6RMDnIuLE3EHMynABYGajImlO0gK/T9Hf3yEC/l9EnJk7iNmg+vqX18wGIGkj4PvAMrmzNMBzwEYRcVXuIGaD8CJAM5suSbNLOhz4Ix78J5oN+JmkBXIHMRuEZwDMbJqKZ/0/BZbOnaWhLgDe7mZC1jaeATCzKZIUknYD/owH/2l5K+DtgdY6ngEws/8iaS7gu6QT/Wz6xgErRMS/cgcxGynPAJjZq0haBbgGD/6jMS9wVO4QZqPhGQAze4Wk9wI/AubInaWFBKwbEX/LHcRsJDwDYGYTn/fvA5yNB/9BBbBH7hBmI+UZALOekzQz8EPgw5mjdMFLwDIRcXfuIGbT4xkAsx6TNAfwSzz4V2VGYNfcIcxGwjMAZj0laSHgPGDN3Fk65ilg4Yj4d+4gZtPiGQCzHpL0etL+fg/+1Xst8D+5Q5hNjwsAs56RtCRwIT7cp04fyR3AbHr8CMCsR4rB/yJgqdxZOu4lYLGIeDh3ELOp8QyAWU9IegNwCR78h2FG4L25Q5hNi2cAzHpA0iLApXjwH6ZfRcQ2dd9E0oykDo2Lkk4kfBZ4FLg9Ih6r+/7WXi4AzDpO0rzAxcDKubP0zNPAfBExvuoLFy2IP0JabLghMMtUvvVW4P+AMyPiz1XnsHZzAWDWYZLGkNrVbpA7S09tHBGXVHWxYiZnf2AHYOZRvvwq4ICI+G1VeazdvAbArKMkzQCchQf/nLao4iKSZpd0IOkT/S6MfvAHWAs4X9LPJM1fRS5rtxlzBzCz2hwDvDN3iIo9C1xG6lb4D+Au4EFg4rPuOYG3kz4lL5kh3+TWK/NiSQFsBxwGLFZJorQ4cR1J74qI6yu6prWQHwGYdZCkTwPfyp2jIg+TZjJ+DlwWES9O7wWS5gLOJ//sx8MRsdAgL5S0BHAOsE61kV7xBLB5RFxd0/Wt4VwAmHWMpC1Ig1/bZ/guB44F/jciXhrtiyUtDtxI/u6Gi0TEg6N9kaSNgD/VkGdSjwBrR8Q9Nd/HGshrAMw6pDjo50zaPfhfDbwtIjaMiHMGGfwBIuJe4NRqow1ktQFf91ylKaZsAeCsYr2I9YwLALOOkDQLcDYwX+4sA3oa+AywTkRcUNE1f1TRdcpYfsDXDaMAgLROYbch3csaxAWAWXd8g/qeF9ftV8AqEXFSREyo8LpXAg9UeL1BLDrg6yo/P2AaDpK04BDvZw3gAsCsAyR9FNgxd44B3A5sFRHbRMTdVV88IkQ6CCenQVfvT+1wnzq8FvjKEO9nDeACwKzlJC0NfDN3jlF6CTgUWDkizqv5XlfUfP3pGXQGYNZKU0zfJyWtMuR7WkYuAMxarDgH/nTSJ7i2uAl4U0QcEBHPD+F+1w7hHtMy0DZAhl8AzEA6O8J6wgWAWbsdQP697qNxArBWRAzzU/ldQ7zXlMw24OtyLOZ8q6R3ZbivZeACwKylJK1NOvGuDZ4C3h8Ru0bEsFa3T/QwUOXCwtEa9JP8IpWmGLmjJc2U6d42RC4AzFpI0szA92nHfv/rSJ/6z8lx82JXwQs57l0YdDHfwpWmGLnlgU9nurcNkQsAs3b6ItCGBVvnAm+OiH9mzvFyxnsPWgBUdfb/IA6SNE/G+9sQuAAwa5lipfZ+uXOMwPHAuyPi6ZwhioY6s2eMMOh+/hUqTTE68wFfynh/GwL3AjBrkWIwuwR4U+4s0yBgz4g4NncQAEnzAY9mjPBQRIxqOr94n58kdTfM5UXSNs3bMmawGnkGwKxdxtLswf9lYMemDP6FpTLff5AZkCXIO/gDzAwcmTmD1cgFgFlLSJobOCJ3jml4CfhwRHw3d5DJrJj5/oMUAGtVnmIw75a0ae4QVg8XAGbt8WWgqee1vwyMjYizcweZgtz9ER4b4DUbV55icMdI8ljRQX5TzVpA0nLAzrlzTIWAnSPiJ7mDTMVbM9//zgFe06QCYA3g47lDWPVcAJi1wxFAUw9n2TMivpM7xJRIWhZYLnOMUTU5KrbfrVpTlkEdImmO3CGsWi4AzBpO0luAbXLnmIpvNWzB3+TG5g7A6I8ifhfpXP4mWRjYJ3cIq5YLALMGK7aDNXUl9s+Bz+YOMTXFaYkfz52D1PJ4NJpa7O0haYncIaw6LgDMmm1rYN3cIabgeuBjxTG7TbUdeU/Tg7Qz4rqRfrOkWYF31BenlNmAw3KHsOq4ADBrqOLT/8G5c0zB48B7IuKZ3EGmphhIm3CS3T9G2fzof4AmP2v/f5LWyx3CquECwKy53ktagd0kAraLiNFOaw/bXsDrc4cARtv2+JO1pKhOAMcWxam1nAsAs+Y6IHeAKTgxIn6TO8S0SFqV5rRJHnEBIGlJYIsas1RlQ+ADuUNYeS4AzBpI0ubA6rlzTOZGYO/cIaZF0pzATxi8A1/V/jCK792J9vxOPrx4zGIt1pY/bGZ9s0fuAJN5kTT1P5rn2UMlaQbgdPIf/TvRjRFx10i+sShcPl1vnEq9Hvh87hBWjgsAs4aRtDLNWwl+QERckzvE1BTPpL9FWkTXFKN5VLITME9dQWqyn6RRdTm0ZnEBYNY8X6BZrbovAo7JHWJqiv3+pwGfyp1lMueP5JskzUY7P03PSepPYS3VpF8yZr0naSHSyXFNeYb9Aqkn/D9zB5kSSYsDpwKbZI4yuYeAxSPipel9o6R9ga/VH6kWLwNrRsSIzzqw5vAMgFmzfJbmDP4AxzR48P8Q8A+aN/gDnD7CwX8BYN8h5KnLDDR4dsimzTMAZg0haXbgHmC+3FkK9wIrRMSzuYNMTtJ+wCE093fYyhFxw/S+SdJJNLfL42hsHRHn5g5ho+MZALPm2JbmDP6Quvw1cfDfEziU5g7+V45w8N+AtPivC46S1NRulTYVLgDMmmP73AEmcQlwdu4Qk5P0DlJr5Cb75vS+oVi4+B268zt4edq1jdFobgVt1iuSlgFupRl/J18GVhvJp9hhkvRu0qA5f+4s03Av8IaIGD+tb5J0MHDQUBINz2PAshHxeO4gNjJdqT7N2u7jNGPwh7SArTGDv6Q1JF0E/IJmD/6QFk1Ob/DfiOYcVVyl+YADc4ewkWvKLxyz3pL0GtLWv8UzR4H06X+liLgld5DikJmDSQ1yZsibZkTGAUtOq0uipHmBa4AlhpZquMaTFkDemjuITZ9nAMzyexvNGPwBzsg9+EuaTdIBpEciO9KOwR/ga9MZ/GcAzqC7gz/ATMCRuUPYyHgGwCwzSWcB78+dg8yf/ovjfLclDSCvz5GhhDuAFSPihal9g6SvA7sOL1JWb4uIC3KHsGnzDIBZRpLmojnn12f79C9pQ+AvwFm0b/CHtGVyWoP/LvRn8Ac4sni0ZQ3mN8gsr61oxsl/E0gH6wyVpNdL+ilwKbDusO9fkT9GxC+m9n9Keh/w9SHmaYLVSQtbrcFcAJjl9b7cAQrnRsRtw7qZpDHFVribgA/Q3seR/2Yah/lI2pL03H/GoSVqjsMkvTZ3CJs6FwBmmRRH/749d47CScO4iaQZJO0I3E7aBz/rMO5boy9ObcW7pHeRti42YYYnhwWBvXOHsKlra9Vt1nqStqUZp+3dBiwfERPqvImkzYBjgdXqvM8QXQq8ZUr/3iRtB3yftCq+z54n/dm6O3cQ+2+eATDL5z25AxROrHPwl7S8pF8Df6A7g//jwNipDP77kFoU933whzTDc1juEDZlngEwy6A4C/5fwFyZozwDLBYRT1Z9YUnzkab5P023BsMJwFYRcf6k/1DSrMAJwA5ZUjWXgA0i4q+5g9ireQbALI/NyT/4A/y46sFf0kySPk96tPA5ujX4A3xpCoP/kqQGSh78/1sAxxXnPFiDuAAwy6Mpi/9Oq/JikrYB/gEcB8xT5bUb4mfA1yb9B5LeA1wFrJ0lUTtsAHwwdwh7NVdkZhlIugFYMXOMu4GlIkJlLyRpReBoYMvSqZrrcuCtEfEsvHKI05Gk44pt+u4lLQj8d+4glngGwGzIJC1K/sEfUte/UoO/pIUlfRe4nm4P/tcAW0bEs0Wvgh2AG/DgPxqLA7vlDmH/4RkAsyGT9DHgh7lzkM6uv2mQF0qaDdgd2BeYo9JUzXMLsAVpANuKNOg3vS1xUz0NLBsRD+cOYv08ncost7fmDgBcNcjgXyzk+hBwON3uajepWYB/0t8Dfao0J/BVPHPSCH4EYDZExQC6ee4cwE9H+wJJG5Ceg/+Y/gz+kJoTefCvzvaSVs0dwlwAmA3bysBCuUMAvxrpN0qaXdJPgD8D69UXyXpiBtKJkJaZCwCz4doodwDgn6Ns+7shadrfa4asKptL2jp3iL5zAWA2XOvnDgD8cpTfv2EtKazvji1OxLRMXACYDdcGuQMAvx7l9zchs3XPMqRjoi0TT+mZDYmk+Unn/+f8e/c48LqIeGkk3yzpNcCjdPNUP8tvHGlb4LjcQfrIMwBmw7MB+YvuC0c6+BdWwIO/1Wde4Eu5Q/SVCwCz4WnCCvo/jvL7160jhNkkPiPpDblD9JELALPhaUIBcNEov9/7ta1uM5FOlLQhcwFgNjyrZb7/v4AbR/ma3JmtHz4qae7cIfrGBYDZEEhaGFggc4w/DtD8xzMANgyzAO/OHaJvXACYDUcTBtI/jeabi66F89WUxWxyTTgiu1dcAJgNRxMKgCtG+f2e/rdh8oLTIXMBYDYcuQfTF4DrRvmaFeoIYjYVSxbNsmxIXACYDccqme9/XUS8MMrXeGuWDdMswGtzh+gTFwBmNStO01s2c4zRTv9DOqrVbJhGu0jVSnABYFa/xYDZMme4aoDXeAbAhukl4N+5Q/SJCwCz+jXhk/T1o/lmSTMBS9SUxWxKHhjlMdVWkgsAs/rlnv6fwOgPAFoSmLGGLGZTc3XuAH3jAsCsfrkLgDsjYrRTq4vWksRs6i7OHaBvXACY1W/pzPf/xwCvWajyFGZTNwE4J3eIvnEBYFa/xTPf/6YBXrNw5SnMpuxpYK+IuC93kL7xMz6z+uUuAG4f4DUuAKxuE4AzgL0j4qHcYfrIBYBZjSTNDLwuc4xBCgA/ArA6XQjsERHX5g7SZy4AzOq1CJD7eNM7BnjNy5WnMINbSNP9v84dxLwGwKxuuVfTjwcGebZ6GPBixVmsv8YBuwGrePBvDhcAZvXKPf3/UESM+tN8RPwTOKGGPNYv44FTgOUj4hsRMT53IPsPFwBm9Zo/8/0fLvHaQ4BHqwpivfN7YI2I2CkiHskdxv6bCwCzeuUuAAZeXR0RTwAHVxfFeuIm4J0R8daIuCF3GJs6FwBmNSm6AK6UOUaZGQCAkxnsHAHrn4eAT5Ge85+fO4xNnwsAsxpI2pTUge8jmaM8WObFRXOWPSvKYt30IvANYLmI+O4ga04sDxcAZhWStKyks0j7nFfPnYfyMwBExG+A31WQxbrnXNICv90i4qncYWx0XACYVUDSvJKOA24A3p87zyTmqeg6e+KzAew//gJsEBFbR8SducPYYHIfUGKTKZ4bzzfZ16zA3MBMwBxTeekE4EnSL+mnSOdrP07afzsOGBcRqjV8D0maCdgZOAiYN3OcKXkSWLaKVdiSvgV8unwka7G7gX2Bn/r3Sfu5AMhA0iLACsDywOuBJYqvJUlHsNbxvrwA3AvcU3zdXXxN/N/3RMQLNdy3syRtDRwFLJc7y3R8OyJ2LnsRSa8DbgXmKh/JWuZp4HDguIh4LncYq4YLgBpJmhFYGVin+FqVNOg38RfoS6Rf7tcD1xX/eX1E3JUzVBNJWhU4Ftg8d5YReglYvYotWZL2Bo4oH8la4mXgB8CX3LCne1wAVEjSGODNwCbAxsAawGw5M1XgSVI/+auBPwOXRsT9eSPlIWlB4KvA9sAMmeOM1u8i4h1lLyJpFuBGYOnykazhLgR2j4i/5w5i9XABUIKkANYCtiZ9GlyX9Jy+6+4ELp3k66YuPw+UNCvwBeCLwJyZ45Txzir2Z0vaFji7gjzWTLeSGvb8KncQq5cLgFEq2rtuDvwPaeDP3eylCR4jHft5PvDbiCi99awJigLvg6Rnn0tmjlOFG4HVir39Ayv+vfyJNNtl3TEO+Apwks/s7wcXACMkaS1gLPBhYIHMcZruRuDXpKLg4jb+MpG0Nuk5/0a5s1TsMxFxUtmLSFoD+BveStwF40nP+Q/wmf394gJgGiQtBexAOs2tC58AcxgH/JI0Zfz7phcDkpYgfeL/EN38+/EoaVvgE2UvJOlU4KPlI1lGvyZN99+SO4gNXxd/wZVS7MPfDNgReC/tW+zVZI+TTg47m7QorTH95osFnHsBe9P+hZvTc0xElD7eV9KiwC3AmPKRbMhuAvYsTnm0nnIBUJA0J2nQ/wywVOY4ffAYcA7ww4j4S64QRcH3CdLq/oVz5RiyF4EVI+L2sheS9GXgwPKRbEgeAr4E/MBn9lvvCwBJ8wOfBT5HM09y64NbgDOB70fEPcO6adGw51iacWb/sP08It5X9iKSZiO9f4uXj2Q1ehH4Nmk/v8/sN6DHBUBxGt++wCeB2TPHseQl4LfAd4Fz6/qEIumNwJHANnVcv0U2iYiLy15E0seAH5aPYzUQ8FNg34i4O3cYa5beFQDFVP8uwP60e0931z0AfAc4saqVyZLmAfYBPg/MUsU1W+5aYK2ImFDmIsVjlL8Ca1eSyqpyJekgn0tzB7Fm6k0BUExVfpb0qd9T/e3xPOnxwAkRcfUgF5ikYc+BpOZK9h+fiIgflr2IpI2B0rMJVol7SL/nzuzyAV1WXucLgOLTyVjSARd+TtluF5Km7v9vpL/YJG0FHE3zG/bk8gDwxoh4tuyFJP2MtHPG8ngG+Bpu2GMj1OlDPCRtSZrm/AEe/LtgM9IagWskfaRotjRFklaVdAFpn7MH/6lbhLT1sQp7k7pO2nBNAL5HOt/hMA/+NlKdnAGQtDzwTdrTrc0GcwdwKHDaxAOGWt6wJ5d/A8tFxH1lLyTpKKD0GQM2YhcCe0TEtbmDWPt0qgCQNAOwO2m6f9bMcWx47gQOIx3R3PaGPbmcFhFjy15E0tzAbcD85SPZNNwK7B0Rv8wdxNqrMwWApBVJU/3r5s5i1kIC1o+IK0pfSNoFOLF8JJuCx4EjgOMjwo9brJROFACSdgaOw1u7zMq4FNi47MrxYm3G34EVK0llkBr2fAv4ckSMyx3GuqHViwAlzSLpO8BJePA3K+vNwLZlL1K0G/Y6gOr8HlgzInbz4G9Vau0MgKTFgJ/hKX+zKt1J6hPwfNkLSTofeEf5SL3lhj1Wq1bOAEhaF7gGD/5mVVsK2LWia+1JOt7ZRudhUmOyVTz4W51aNwMg6S3Ar4DX5s5i1lFPkw4HeqjshSSdRDqF0aZvYsOeAyPiydxhrPtaVQAUp7qdRff7tZvl9u2IKD1wS1qAtC1wrvKROu1cYLeIuCN3EOuP1jwCkPQh4Od48Dcbhk9JWrnsRYpGTodWkKer/gpsGBFbe/C3YWvFDICkLYDzgJlzZzHrkQsjovRpmpJmBv4BLFs+UmfcTzqw7LtluzGaDarxMwCS1gF+gQd/s2HbTNI7y14kIl4E9qsgTxc8SzrIZ/mIOMWDv+XU6BkAScsAfwZelzuLWU/dDKw6sddCGZIuBjYuH6mVJgBnAPtExIO5w5hBg2cAJM0HXIAHf7OclidtSavCHqSBsG8uAtaKiLEe/K1JGlkASApSe8vXZ45iZvAVSfOWvUhE/A04vYI8bXEb8IGI2Mzd+qyJGlkAkDq6bZM7hJkBMC+wf0XX2o/0HLzLHgf2JR3kc3buMGZT07g1AJI2IZ197V7uydPAOOCx4uuJqXzfGNJCyfmKr/mB2YcR0HrhRWCliPhn2QtJOhg4qHSi5hlPOsjnyxHxWO4wZtPTqAKg6CV+A7BI7ixD9ASpc9oNwO3F1x3AI8BjZRZfSZqNVAjMT3qcskzxtWzxn4vRsD8D1mi/iIj3lr2IpDHALcCi5SM1xrnAXhFxc+4gZiPVqF/+kk4BPpU7R43GA1cBl5Far14dEXfnClMUCCsAaxVfawOr4C2XNnWbRMTFZS8iaSzwowry5HY9sHtE/D53ELPRakwBUJzxfxENylSRfwK/Bc4H/hgR/86cZ5qKQ1tWATYANgHeQppBMAO4Glin7P51Sa8hnYK3diWphu9h4EDgexHxcu4wZoNoxGAraVbSNPgbc2epyM2kngU/jYgbc4cpo9iRsQqwafG1GTBn1lCW2/YR8YOyF5G0EfCnCvIM0/PA8cDXIuKp3GHMymhKAXAQcHDuHCU9Sdri9N0ub/mRNAtpVuB/gK2BJfImsgweAJaLiGfKXkjSOcD7ykeqnUhF/b4RcVfmLGaVyF4AFN3Cbqe9nyqvAb4BnNX06f06SFodeA/wIbozg2PT99WIOLDsRSQtDdwIzFI+Um3+SnrOf1nuIGZVakIBcCzwhdw5BvBn0pne50aEcodpAkkrAe8HxgJLZY5j9XqOdJ79PWUvJOlIYK/ykSrnhj3WaVkLAEmLkU7LmjVnjlH6A/DFiLgyd5CmKhZ4bQp8kjQ70Kb310bu9Ij4aNmLSJqL9HtggfKRKvEMqbg/JiKeyx3GrC65C4CTqe6c8br9jTTwe7vPKBRHyG4H7EBaTGjdIWD9iLii9IWknYGTykcqZQLwQ+AAn9lvfZCtACgOA3mYdIJdk40jTQOe4GnAciStBewGfBiYMXMcq8blwJvKPgaTNANwLbByJalG7yJgj4i4JtP9K1fssjiW9m61bIPxpMPc7iL9+b0QOC8ins4ZaqRyFgDbAafluv8ITABOAfaPiHG5w3SJpCWAzwCfBl6bOY6V98GIOKvsRSS9g3RexjDdBuwdEf875PvWplhYeQSwbe4sPfVv4CfAERFxW+4w05KzAPgNsGWu+0/H3cDHqjjxzKZO0pzA9qTGKQtljmODuxNYMSKeL3shSecD7ygfabqeAA4Hjo+IF4Zwv9oVayn2B3al2bsq+mI86cyIA6v4u1GHLAWApPlJe4lnynH/6fgBsFtbpnCqIGmBiHgk4/3nAHYi9YtfOFcOK2XfiDii7EUkrUg6FKyuR0TjgZOBg7vSsKdYdLsdcCSwYOY49t/+Ary3ietKcrUD3pTmDf7PA5+IiO37MvhLWkzSqcDDkm6WdIik1YadIyKeiYhjgKVJRYC1z36SXlf2IsXJmadUkGdKzgNWjYjPdWjwfztwHamvggf/ZlofuELSqrmDTC7XDEDT9v4/CLy7itXMbVAswNwb2JMptwy+DTgbOCPHUcaSfk7aPmjtcnJEfLrsRYrDwW4D5iofCUgNe/aIiAsqul52kpYDvko6d8Pa4QFg3Yi4P3eQiXIVAH8B1stx7ym4G9iiij7nTVec678tcBSw5AhfdhVpseYZEfFoXdkm1ZLT4ey/vQysERHXl72QpD1Jf07LeIw0SJ4YES+VzdQExbbag4Bd8E6aNroK2Kgp50sMvQAoGv88QTN+ud8FbBwR9+YOUjdJG5O2BK014CWeB34OfB+4sO7TDyUdA+xe5z2sFhdExNvKXqToOXED8IYBXv488HXgsK407Cm6dO5KWuQ3d+Y4Vs5XIuKg3CEgTwGwMmlKLrfHgDdHxM25g9RJ0htIi4PeW+FlbwROAE6LiGcrvO4rJM1NmgZ2K+L22Soizit7EUnvA84ZzUtIj6726VLDHklbA8cxWDFkzfMssGwTFgXmWAS4SIZ7Tk7A2C4P/pLmlnQ0abCucvAHWBH4FnCfpGOKKftKRcQTwJervq4NxdGSSi/yjYifMfJ2wVeQplY/2JXBX9Jaki4GfoUH/y4ZA3wpdwjIUwAsmuGek/tRRPwmd4g6SJpR0i6kT897ADPXeLu5SdP0t0r6SQ2rXL8N3FTxNa1+y5O2dVZhd9KhXFNzL2kL3PoR8eeK7pmVpEWKY9L/CmycO4/VYmxxDkpWfSwAngNKtzFtIklbkvZQn8hwp85nILUDvlbSryVtUMVFi4Vbe1ZxLRu6gyXNU/YiETFxEerkniH9PV4+Is7oQkdOSbNLOgi4ldQjZYbMkaw+Y4B35g6RowCYN8M9J3Vu1xb9SVpJ0m+B35Cm53MJYCvgMkkXFAu5yl0wzdT8X+lkNmzzUd005/6k56aQZgN+ACwXEV+NiH9XdI9sJL1G0keBW4CDaX5/FKvGZrkD5CgAcjfU6cxef0kLSPoWqQnF23PnmcwWpMY/VdiDtMXM2uUzkpYte5Fi3/RRwB+BtYvDuh4oe90mkLQecAlwKrBY5jg2XNkPBupjAZC1BXIVJM0iaW/Sc/5P09z9wFWdDvcP4LsV5LHhmpm0A3PjqjYAAB5gSURBVKUKh0bEpl3q1lf4C7Bh7hCWReWLp0crRwGQ+5NcUw4gGoikbUkr+4+gupPS6jIX1a3kPxDoxJ7unnm3pE3KXqQrB/mYTSL77+8cBUDuzlvbSHpj5gyjJmltSZeQ9jlnrxxHYYfi7IdSIuJfwGEV5LHhO7ZoWGNm/5H9MLwcfynvy3DPSc0InCVpSmfgN46kRSfZEvTm3HkGMCPpVLYqHAd0/sjmDloD+FjuEGb2ajkKgDsz3HNyqwHfa/KnEkljJB3Mf7YENTbrCGxWbFEsJSJeBParII8N36FF22cza4gcg8pdGe45JR8CTioa5DRGsSXoY6QtQQcx5W59bXS0pCoWK54DXFrBdWy4Fgb2yR3CzP4jRy+AmUmHeJQ+KrQipwPbR8T43EEqaNjTdJ+NiBPLXkTSOqRHIo0q3my6niPt3+/UORxlSGr9AUY2uIjI+jts6DMAxTTu1cO+7zRsB/xBUrYeBZKWkHQqaZ9zVwd/gK8U7UxLiYgrgTMqyGPDNRvwtdwhzCzJ9Vx5pA0+hmUj4Oqi+9jQFA17jiLt5/8o3f9EOy/VPcP/ItD6U+B65kpSEykzawAXAP+xIHCOpHOr2LY2ueLZ/psk7S/pF5KuAO4mnXVfZ8OepvmcpGXKXiQi7gOOriCP1e8+UoG7Xsca9vwgdw6zMrJ84ix6vT9Cc0+wmwD8AvgGcEmZRiPFz/pZUnc0H/WZ/DwiSs+2SBpD2iXRhBbT9t+eJR1YdUwXzuyH1LAH+BypP8GcZZ/heg1Av+VeA5Dt5pLOowHdkEbgTuAs4ALg8pH8IpO0JPAWYGtgS9zcY0o2iYiLy15E0sdJzWGsOSaQzrbfv0Nn9gewLelo49dP/OcuAKyMPhcAHwTOzHX/Ab1MOojmNuAh4LHin88GzAMsSeqFXvr8+x64GlgnIkr1hijOcrgSWLOSVFbWxcDuEdGkhb6lSFqXdAjVf53Z7wLAyuhzATAr8CAwd64Mlt0nIuKHZS8iaUPS2QBdX0TZZPeQ2v+eVuaRWZNIWhw4lLRTaIp/tlwAWBm5C4Bsp8tFxPPAT3Pd3xrh0OI5fikRcRnwvxXksdF7grSQddmIOLULg/9kp3D2YXeO9VTWP9iS3gDcRHMOBbLh+0pEHFT2IpKWJnVJzN5goydeAr4PfKlo1NR6xeOk7UjP+RccyWs8A2Bl9HYGACAibgdOy5nBsttL0hJlLxIRdwDfrCCPTd/vgTUjYqcODf6bA9cAP2KEg79Z22Wf2ipWzN9Kv/bC26udHhEfLXuRYsvlbcD85SPZFNwM7BUR5+YOUpWiNfghwPsHeb1nAKyMXs8AAETE3cApuXNYVh8pzvcvJSKeAA4uH8cm8y9gZ2Dlrgz+kuaVdDhwPQMO/mZtl30GAF450OUaYNncWSyby4E3lV1EJmkG4Fqg8tMce2g86ejeAyPiydxhqiBpJuATpNX9pWeKPANgZfR+BgAgIp4FPk7aZ2/9tAHpoJVSIuJlYO/ycXrvXGCFiNitQ4P/FqTi8GT8mMisGQUAvLKVy2e799sRxfkQpUTE+cDvKsjTR1cBb4mIrYtFuq0naU1JF5FO81wxdx6zpmhMAVA4iNTn3fppKWDXiq61J2mrmo3MfcBY0umMTWzWNWpFw56TgSuATTLHMWucRqwBmJSkhUhHu7pxTj89DbwxIh4qeyFJ3wI+XT5Sp/0bOAE4NCKezh2mCpJmIxWS+wGvrfNeXgNgZeReA9C4AgDSlB1wCTB77iyWxckRUXrglrQAaVvgXOUjdY6Ac0jb+u7OHaYKU2vYUycXAFZG7gKgaY8AACgaiexE+iVl/bODpNKr+CPiEeCwCvJ0zZ9IU/0f6NDgvy7pQ8NZDGnwN2u7RhYAABFxOrBb7hyWxQzA1yu61vGkDo6WGvZ8jNSK+arcYaogaXFJpwJ/Ad6UO49ZmzS2AACIiBOAPXLnsCw2k/TOsheJiBeBL1aQp82eAb4MLOeGPWY2USv+0kg6BNg/dw4bupuAVSOi9Gp+SZcAby4fqVVeIp2yeVBEPJo7TBUmadhzBLBQ5jheA2CleA3ACETEAcDngQm5s9hQrUB1q/h3pV9/fiY27PlMhwb/zYGrSQ17sg/+Zm3XihmAiSRtB3wPNw7qk3GkXvPjyl6oeFZcuulQw7lhzxB5BsDK8AzAKBQLA7cCnsqdxYZmXqp7/LMfad97Fz1CatizSlcGfzfsMatXqwoAgIi4AFgb+HvuLDY0ny0+BZYSEfcBR1WQp0nGA98gzZJ8u4r1ErlJmknSjsAtwD54xs+sFq16BDCp4sz4I6ju6Fhrtl9ExHvLXqQ4Je4WYPHykbI7F/h8V87sh1ca9nydlpzZ70cAVoYfAQwoIp6PiN1Iz3Qfz53HavceSZuUvUhEPAd8qXycrP4GbNyxhj0rSjofN+wxG5rWzgBMStKCpKndri/w6rtrgbUiotRq/mIr2V+AdSpJNTwPkPbzf69oe9x6khYGDgY+SToAqlU8A2BleAagAhHxcESMBd4N3J87j9VmddJJdqUUBcSe5eMMzbOkQXLZiDilC4O/pNkk7UPatbAjLRz8zdquEzMAk5I0O/A5YF9g7sxxrHoPkwbC0p3rJP0MKL2uoEZu2NNwngGwMjwDULGI+HdEHAG8ATgaeC5zJKvWgsBeFV1rb+CFiq5VNTfsMbNadW4GYHJFS9jtgc8Ci2WOY9V4DlihioFR0lE063HAPaRFiqd14cx+AEmLkboybkfHfud4BsDKyD0D0Km/jNMiaRbgw6SjZdfLHMfKOz0iSi/6lDQ3qaHMAuUjlfIk6bS7EyKiqbMSoyJpDGm2Zh9g1sxxauECwMpwAZCBpCWA95AWlK2ROY4NRsCbI+Ky0heSdgFOLB9pIBOAM0jP+R/OlKFSTWvYUycXAFaGC4BJSJo9IoZ6VKukFYC3AlsAmwBzDunWjwLzD+leXfVnYKOyU+WSZiSdLDns/ee/BfaIiBuHfN/aSNoMOBZYLXeWYXABYGW4AOCVlft7kqYLzwT2jIgnM+SYkbQ3fHXSL7DVgJWBOUpc9iXSc93bgCuAv5K2Pv0UWKtMXgPggxFxVtmLSNoS+E0FeUbiRtLA/9sh3a92TW7YUycXAFZGrwuAYkvQdqQFQpMu0Lsf2Dkifp0l2GSKg4YWARYtvuYGxvCfM8rHkPZqPw48DTwDPAjcAdwTEeMnudYY4HfAm4aVv+PuBFaMiOfLXqg4ie4d5SNN1SPAQcB3unBmP6SGPaTdFF+gh2f2uwCwMnpbAEjaEDieaZ/G9jvSbMA/hpOqXpJWBn4MrJI7S8fsW2z9LEXSSqTTBmcsH+lVXiA17Dk0x8xWHSTNBHyC9Kk/9wLKbFwAWBm9KwCKT8DHAp8a4f1fBr4PHBIR99SZrS7Fo4VdSIuiOrkaOrOnSIcD/avshSSdRGqrW5WfAft05cx+eKVhz/HASrmz5OYCwMroVQEgaUng1wz2CXg8abX0ERFxc6XBalIUOzuQpkeXzByn606JiJ3KXqQ4N+I2YK6Sl7oK+EJEXFI2U1NIWpF0uNaWubM0hQsAK6M3BYCkpYGLgCVKXmoCcD7wXeDcJj5LlbQ86fCh7YH5Msfpi5eBNSLi+rIXkrQX6ajaQdwP7Ec6p6BU06KmkDQ/6XCiz+Az+1/FBYCV0YsCQNI8wGXA8hVf+kHgNNI065U5T04rFgpuQzpbYMNcOXrugoh4W9mLFIdG3QgsPYqXPUv6dHxURDxbNkMTSJoN2JVU0Lw2c5xGcgFgZfSlADib1ACkTvcDvwT+D7g0Ih6r82bFc/3VSecHbAOsSwd7K7TQVhFxXtmLSHofqRHP9EwATgf2i4hOdKKcpGHPEcBSmeM0mgsAK6PzBYCk9wA/r/s+k98WuIF0UMzfi/9+fUQ8PtDF0ifC5YAVSAufNgDWp9z5AFaPm4FVJ916OShJfwI2msa3XALsHhF/K3uvppC0DnAc3qY6Ii4ArIxOFwCSZgBuApat8z6j8ARppuA+0uODF0lnsE/6rHYMaaX+gsXXoqTjTP3ssz12jYgTyl5E0tqkg5smn9m5g7SyfyQzBK3Q5YY9dXIBYGV0vQAY6TSqWZUeI20LHGjGZ1KSfgSMLf7nk8ChwDc62LBnb2C2zHFaxwWAlZG7AKj7mfXHa76+2ZTMR1q1XoX9SKc7ngYsFxFHdWHwl/QaSWOBf5JOJ/Tgb9YztVUfxQricfjgG8vjRWDliLit7IUkzVPFbEJT9K1hT508A2BldHkGYB08+Fs+MzP4Xv5X6crgL+mNks4C/oAHf7Peq7MA6P0xoZbdu4tja3tN0jySDgeuo2fd+sxs6uosABab/reY1e5ISb08n0HSTJJ2BG4B9gFmyRzJzBqkzl+Ms9d4bbORWoMeLkYtZj6uAU6mx936zGzq6iwAXqzx2majcYikXhzaJGlFSb8BLsCP4cxsGuosAB6p8dpmo7EwaQq8syTNL+nrpOf87tZnZtNVZwFwS43XNhutPYp21J0iaWZJuwG3kxr3+MRKMxuRGWu89pWkM/l9rKjlJtKJlK0/wGcKbqN8i20z66HaZgAi4iHg2rqubzZClwLrRcTY4s9k13jwN7OB1L096oyar282NfcCHwM2jogrc4cxM2uaupsBzQvcCby2zvuYTeJJUle7r3fhzP7p8VGyefkoYCujy0cBExHjgOPrvIdZ4WXSnvc3RsSRfRj8zczKqL36KPZf30raimVWhz8Au0fEdbmDDJs/QeblGQAro9MzAAAR8QxwQN33sV66BfhARGzRx8HfzKyMoVQfxVnsVwBrDeN+1nnjSJ3+jouIXp846U+QeXkGwMrIPQMwtJtL2gS4aFj3s04aD/wA2D8iHs0dpgk8gOTlAsDKyF0ADK1LWkT8EfjlsO5nnXMusGJE7NSVwV/S1rkzmFl/DbtN6h508zQ2q8/VwKYRsXVE/DN3mCpIWkHSecCvcmcxs/4aagEQEbcDJw3zntZaDwA7AesWs0etN0nDnuuBd+bOY2b9NvTnD5LmJp1fPv+w722t8BzwDeCwiHgqd5gqSJoZ2Bn4CpMdiuVnyO3m98/K6M0agIki4gnSL0KzSQk4m/Scf98ODf5bAzeTDsTyiZhm1hhZqg9JM5IaBa2U4/7WOFcAX4iIy3IHqYqkdYBjgTdP6/v8CbLd/P5ZGb2bAQCIiJeAfXLc2xplYsOe9bsy+EtaTNLJwF+YzuBvZpZT1upD0u+At+XMYFk8CxwNHB4Rz+cOUwVJY4C9gL2B2Ub6On+CbDe/f1ZG7hmA3AXAisDfgRlz5rChmUBqEb13RDyUO0wVilMutwMOZ4B+Fx5A2s3vn5WRuwDI8ghgooi4Efh+zgw2NH8A1oyIsR0a/DcFrgJ+hJtdmVnLZK0+ACS9jtQtcK7cWawWtwIHRMTZuYNURdKywKHA+8tey58g283vn5XR6xkAgIj4F2n61LplHLAvsEpXBn9J80g6nHSQT+nB38wsp+wzAPDKQSk3Am/IncVK61zDnmLb6vbAIcACVV7bnyDbze+fldH7GQCAoqXrfrlzWGm/B1bvWMOeLYBrgJOpePA3M8upETMAE0m6BO+dbqNrgN27cmY/pIY9pK2KtZ7Z70+Q7eb3z8rwDMCr7UbaKmbt8CCpYc86XRn8Jc3nhj1m1geNKgAi4mrgJ7lz2HQ9BxwBLB8Rp0TEy7kDlSVpZkm7AbcDuwIzZI5kZlarRj0CAJC0KHALMCZ3FvsvAs4hHeRzV+YslSka9hwPLD3se3sKud38/lkZfgQwmYi4n9RExZrlCmCjiPhAVwZ/SWtL+hPwKzIM/mZmOTVuBgBA0hykWYBFcmcx7gUOAE6LiE58WilmmQ4EdiD/aZj+BNlifv+sDM8ATEFEPEMadCyfZ4EvA2+MiFO7MPhLGiNpH+BmYEca+uffzGwYGjkDAK80WfkrsHbuLD3jhj1D5E+Q7eb3z8rwDMBURMQEYM/cOXqmqw17/oYb9piZvUpjCwCAiLgY+N/cOXrgVuADEbFFRPw9d5gqSFpW0lnAhcAaufOYmTVNYx8BTCRpaVKfgFlyZ+mgccCRwHHFccytJ2keYB/g87Tgz4ynkNvN75+V4UcA0xERdwAn5s7RMeOBU0gH+RzRhcFf0oySdiQt8NuHFgz+ZmY5NX4GAEDS3MBtwPy5s3TA74HPR8QNuYNUpWjYcxywcu4so+VPkO3m98/K8AzACETEE6QtaTa4G4EtI+KtXRn8JS0v6TzgAlo4+JuZ5dSKGQB4pSf7tcBKubO0zIPAwcD3unBmP6SGPaSDfHYBZswcpxR/gmw3v39WhmcARigiXgL2zp2jRfrQsKfVg7+ZWU6tmQGYSNJvgbfnztFgbtjTIv4E2W5+/6yM3DMAbSwAVgT+jj/9TcmVwBci4s+5g1RF0tqk5lAb5c5SBw8g7eb3z8rIXQC05hHARBFxI/C93Dka5j7gY8B6XRn8JS0q6WTScdCdHPzNzHJq3QwAgKQFSNsC58qdJbNngaOBwyPi+dxhqiBpduBzpGZQc2SOUzt/gmw3v39WhmcABhARjwBfy50jownAacAyEXFwFwZ/SSHp/cBNpKY9nR/8zcxyauUMAKQV4cANwDK5swzZhcDuXTmzH0DS+qSDfNbPnWXY/Amy3fz+WRmeARhQcXztfrlzDNHEhj2bd2Xwl7RM0bDncno4+JuZ5dTaGYCJJP2Jbi8Se5y0n//4iHghd5gqFEc770tLGvbUyZ8g283vn5WRewagCwXAGqR+762dzZiK8cAPgAOKNQ+tV5zmuD3wVeB1meM0ggeQdvP7Z2XkLgBaP2hGxDXAj3PnqNjvgTUiYqcODf5bAFcDJ+PB38wsu9bPAEDaMw7cAozJnaWkG4E9I+L83EGqIml50lbFd+XO0kT+BNlufv+sDM8AVCAi7geOyZ2jhEdJz8NX7crgL2k+SV8HrseDv5lZ43RiBgBA0mykWYDFc2cZheeAbwCHRcRTucNUodieuTOpfXPfD2qaLn+CbDe/f1aGZwAqEhHPkVrEtoGAs4GVImLfDg3+W5MO8jkeD/5mZo3WmRkAAEmvIZ0dv3buLNNwJekgn0tzB6mKpLVIDXs2zp2lbfwJst38/lkZngGoUERMAHYjfcJumkkb9nRi8J+kYc8VePA3M2uVThUAABFxGfCL3Dkm8SzpefgbI+LUiGhicTIqkmaXtA9wM7AjHfxzZGbWdZ16BDCRpKVJW+pynjI3ATgD2DsiHsqYozKSAtiWtK1vicxxOsFTyO3m98/K8COAGkTEHcA3M0a4EFgrIsZ2aPBfH7gMOAsP/mZmrdfJGQB45bz524D5h3jbW0lH9549xHvWStISwCHAdnT4z0su/gTZbn7/rAzPANQkIp4ADh7S7R4nNbdZtSuDv6S5JR1OKmo+igd/M7NO6fQv9aL5zJXA6jXdYjxwIvDViBhX0z2Gyg17hsufINvN75+VkXsGoNMFAICk1UlnA8xc8aV/BewVEbdWfN1sioY9xwKr5M7SFx5A2s3vn5WRuwDo7COAiSLiWtJWtarcBLwzIrbpyuAvaXlJ5wIX4MHfzKwXOl8AAETEj4C9KXdA0EPADsDKbthjZmZt1/lHAJOS9AngJGDWUbzsOeA44GsR8UwtwYZM0kzALrhhT3aeQm43v39WRu5HAL0qAAAkrQZ8B1hnet8KnAnsGxH31B5sSIqGPccBb8idxTyAtJ3fPysjdwHQi0cAk4qIvwPrA2OB66bybZcDG0bE/+vK4C9pLUkXkxYvevA3M+u53s0ATE7S2sA2wIbAgqRDb37ahTP7ITXsIbVJ3oEeFnxN50+Q7eb3z8rIPQPQ+wKgqyTNDnwO2B+YM3McmwoPIO3m98/KyF0AzJjz5la9SRr2HAUsmTmOmZk1lAuADika9hwLbJA7i5mZNZufCXeApCUknUrq1ufB38zMpsszAC0maQ5gT2AfRne2gZmZ9ZwLgBaapGHPV0g7F8zMzEbFBUDLuGGPmZlVwQVAS0hanrSyf6vcWczMrP28CLDhJmvY48HfzMwq4RmAhnLDHjMzq5MLgAZywx4zM6ubC4AGkbQWaYHfxrmzmJlZt3kNQANIWkTSycBf8eBvZmZD4BmAzCQdDOwFzJ45ipmZ9Yi7AWbmbmD95m5y7eb3z8rI3Q3QjwDMzMx6yAWAmZlZD7kAMDMz6yEXAGZmZj3kAsDMzKyHXACYmZn1kAsAMzOzHnIBYGZm1kMuAMzMzHrIBYCZmVkPuQAwMzPrIRcAZmZmPeQCwMzMrIdcAJiZmfWQCwAzM7MecgFgZmbWQy4AzMzMesgFgJmZWQ+5ADAzM+shFwBmZmY95ALAzMysh1wAmJmZ9ZALADMzsx5yAWBmZtZDLgDMzMx6yAWAmZlZD7kAMDMz6yEXAGZmZj3kAsDMzKyHXACYmZn1kAsAMzOzHnIBYGZm1kMuAMzMzHrIBYCZmVkPuQAwMzPrIRcAZmZmPeQCwMzMrIdcAJiZmfWQCwAzM7MecgFgZmbWQy4AzMzMesgFgJmZWQ+5ADAzM+shFwBmZmY95ALAzMysh1wAmJmZ9ZALADMzsx5yAWBmZtZDLgDMzMx6yAWAmZlZD7kAMDMz6yEXAGZmZj3kAsDMzKyHXACYmZn1kAsAMzOzHnIBYGZm1kMuAMzMzHrIBYCZmVkPuQAwMzPrIRcAZmZmPeQCwMzMrIdcAJiZmfWQCwAzM7MecgFgZmbWQy4AzMzMesgFgJmZWQ+5ADAzM+shFwBmZmY95ALAzMysh1wAmJmZ9ZALADMzsx5yAWBmZtZDLgDMzMx6yAWAmZlZD7kAMDMz6yEXAGZmZj3kAsDMzKyHXACYmZn1kAsAMzOzHnIBYGZm1kMuAMzMzHrIBYCZmVkPuQAwMzPrIRcAZmZmPeQCwMzMrIdcAJiZmfWQCwAzM7MecgFgZmbWQy4AzMzMesgFgJmZWQ+5ADAzM+shFwBmZmY95ALAzMysh1wAmJmZ9ZALADMzsx5yAWBmZtZDLgDMzMx6yAWAmZlZD7kAMDMz6yEXAGZmZj3kAsDMzKyHXACYmZn1kAsAMzOzHnIBYGZm1kMuAMzMzHrIBYCZmVkPuQAwMzPrIRcAZmZmPeQCwMzMrIdcAJiZmfWQCwAzM7MecgFgZmbWQy4AzMzMesgFgJmZWQ+5ADAzM+shFwBmZmY95ALAzMysh1wAmJmZ9ZALADMzsx5yAWBmZtZDLgDMzMx6yAWAmZlZD7kAMDMz6yEXAGZmZj3kAsDMzKyHXACYmZn1kAsAMzOzHnIBYGZm1kMuAPJ7MXcAMzMbuhdyB3ABkN9TuQOYmdnQPZk7gAuA/O7MHcDMzIbujtwBXADkd23uAGZmNnR/zx3ABUB+F+YOYGZmQ/eH3AEid4C+kzQH8BAwJncWG76IKPV3UJKqymKj5/fPBvQssFBEPJMzhGcAMiv+AJyZO4eZmQ3Nj3MP/uAZgEaQtCxwAzBT7iw2XP4E2W5+/2wALwIrRIQXARpExG3A8blzmJlZ7Y5twuAPngFoDEmzAhcB6+fOYsPjT5Dt5vfPRulyYNOIyH4IELgAaBRJCwFXAIvnzmLD4QGk3fz+2Sg8AKwbEffnDjKRHwE0SEQ8BGwF3Jc7i5mZVeZe4B1NGvzBBUDjRMR1wJrAn3JnMTOz0i4nffK/PneQybkAaKCIeAR4G/AV0n5RMzNrlxeBr5Ge+T+UO8yUeA1AwxXrAg4ExuLDgjrHz5Dbze+fTcGzwBnAEU1Z7T81LgBaojgx8F3ApsDqwFLA3MDMOXNZOR5A2s3vX++9CDxBaup2DWkn12+acMjPSLgAMGsxSS+Qrwh8ISJmzXRvwD+/WRleA2DWbk9lvHf2fub45zcbmAsAs3a7M+O9m/B8s+8/v9nAXACYtdu1Ge+dvZ85/vnNBuYCwKzdLsx47+z9zPHPbzYwLwI0a7Fid8hDDH+LaCP6mff95zcrwzMAZi1WDEBnZrh1M/qZ9/znNyvDMwBmLSdpWeAGYKYh3bIx/czBP7/ZoDwDYNZyEXEbcPwQb9mYfubgn9/MzHpM0qySLlf9LpM0S+6fd3J9//nNzKzHJC0k6Z4aB7/7JS2a++ecmr7//GZm1mOSVpV0bw2D3z2SVsn9801P339+MzPrMUkLSLq4wsHvMqWulK3Q95/fzMx6TNIskr4s6ZkSA98Lkg5TC5959/3nNzOznlN6Ln7SKAfCZySdLGnp3PnL6vvPbzYtPgfArAeUTsx7F7ApsDqwFDB38X+3tp/5SPX95zczMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzOzkfn/80tDAi2dYKIAAAAASUVORK5CYII=
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAUkAAAFJCAYAAAAWit+oAAAACXBIWXMAAAsSAAALEgHS3X78AAAgAElEQVR4nOy9249dZ3rm93u+tdY+1/lEFs8USbVIqdvd9NjIeAZTxgAzacAOkAs24sATOMHAyH9B6U+YWyMDBBggQcSLAIGBnjsVMBgkGDfHbVukWhJFURTPxTruvWuf1vqeXOyiDm12S2pVkaK4fsCGilTtdeJaz3q/732/54WSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpKSkpIXCT3vAygpKXm5sBFcCrCme/dalXq9nqVpmn32CzuZR71itFsbjh4+vJnfvHk1/uxnFM/reEuRLCkpeaa87UvJj+mkDZIk6cy0KGhmSWhUAEZR9CnyfrG7W3V3czPvV6ud0ZkzPx9K+Hkcb/o8dvpFxm+VMc/rIpSUlBw8T571G3RSNmarZLFSr1QmR7GYSZRMKo/KR4QkhFy1dKsZSCZPoH5/Qlev/mW0/yp/HhrxTCNJ+1ICnXSNVlZr59XhMK2laa1SBaAQJHYRR7EaR3muYbe7M/jP//mvB88z1C4pKfmd0dtvE06fJiwtXZqoVrO5EKqzkmdINCWYVlAT05RoEC0iAgpHdklCV4ptYCtN2ZLYGA4H66PRaP3RI4bXr1P87GdXDlwbnnEk2Um3tqp15dX6gOqk5Ek7aQ5UBPI0gKPEbgG7Q+gAO+fPn8/heoQyyiwpeZG4fBmdP38+mZmpp81mmJGqp0FnpHDE9mHDYVBFomK7ggQJYIwYSXFk05bCwzznYQj+OE2zDyuV/vDChaR94QJDOPgA6iAjSQG8885KcvLkybTZ7KY0mi314iSZJgLFbEIyA5oCBcmJrSIqdiTaiK04ZL0otJ6m3V6vNzNaXmYEmxGuxHJoXlLy3ebdd89Xjhw51yiKvJkkk69A9ntS+BHolKRjyMdBwSYA4fNv2gBCNrTB9zB3Ld4jxl9WKv2/7fd5LBU7/+7fXWm/9RbmAIOoAxHJy5cJb775l8mdO5tpvV6fdZosVVIvFoXmBbOgWdvNAE1JdaIDQSLaFn2Lvu1OCNosIlshsBbsh/bwUZKM2q1Wryv99e5BHHtJScm3Yyx6K6HTOTUzGOSn01QnYwyvhKBXQtArNouIWZs5xuIokL60BfZE0u5LbCFt2r6LuQnxps1HkH80PT34CDojaOXSwQy9D2S4vbKyEh4+vFWBqWqaxqWo5LyjzguWhZZslgQpUmpICQIQQQYiUASFHngniDbyx456L3H2nh0ettv1CJQiWVLyHWOcnLmYwCC1d2eSpPYqJH8YAqeBJY8/DaAqIRD204NAYymQ2Uxh6qCmxByE0+C5EELR6eT3W62sxziS/O6L5F72SmtrC7XRqDbbanmmKLKzScZ50O8hjggWgaXPg1j9o2h2/BcegrqSd21mJKUQ8CjUa5ll/0kPiuIg3yAlJSXflEsBaPR6tIqieiSE8Iqs1w0nEJM2k0CCvzg+/nUJ+FwTbDIgA5rgJtK00DLQL5w8zGPl0/ZWsl6N2gSGB3FG+yaSe2+Q9N69w1mzWVtoNNJzRcGrIdUrRJ2K5pgC0zG68Y9l8SlIwaaq8evmkEUeYYqUhV50a9iZUQjZdrfb3mGc5CkpKXn+VNrt+lKMOhbS5Acx5yTB87Imxs/zt5niU4jRVSBILNk+F6h1K4o3JG4AO/t1El9kPyNJjQXS1SxL5odDX5DCP6PgBGJGYgZTCYH0N0TXv06QqIBTTApM27wiMSUlilFdKb9XFK0RpUiWlHwn2NykkqZhSUn4AfiCEp0QmkM0xzV+1rdIhexpglJgMSicRU6JclqJj4Hb+3cmn7NvInnjxk+z5eXpqcFgNBejT4WQvCLprM1hmzqiBgT7a16gzzJeApwJNfei8HaM3pHUGw6TNElGu2+/zca1a/itt4j7dT4lJSXfDBt1OlTsOC+FU7ZeESzZtIBxOfS3yxXv6QEJeApxxCgj0d2RPf0LX8wucnrfq1/CV//K12P6zOHK7ojDDtULw1yvR3ws2lPGNeQUvq46Ph1jGSvimRD0CuifSJxNkrDwR3/0J9VLly6le6UEJSUlz5i33ya5du181m5njRiTuVhwDHPUZlo6kARxFTMzTgazUDjMLGy/2rrHTHWVlWQ/d7RvB19t96pW9VBE5xV0HnNU44na2ngidn+EXTAFfkViSdJjO9wYDucrMzMVVldXIqyW0WRJyTPm9OmL4cKF08njx6EGzBqOYh1BrnAwVTQ1cObIJLCYBKaTQs14Z1NH+/UCyPdrR9868rpsgk0ySl2PeB44gX0cNGerBkrG+/la6ZrfgPTkI1SVmADmJS+GwKGJicGhSmV3amVlIfvKTZWUlOwrNjp6dK7Sbvea41V0TEhqAQ2siu2DGOEFUCapJqmJmWpUatONuUpj4sz8voryt97Yn3IxucPptJanjYBmhQ6Dl4AJxouM9hWP5zVTYWJkyg6HpPpxqbi7vZ31gd5+77OkpOS3olptvpJllVYMniSqzrh0Z69Q/KD37qojE2I4F3ezvDrY30TutxJJG91iImlublaKMNdE6SzysuAQEGwn+3+NLCAxSNKkxFKS6CioF0JlfZ93VlJS8pVc0jCtVGPBhKwpWQ3wE5E8cGxVA54MzmaVFp1eL+zriPLbRpKa3DhSqc6qMewkLVl1oYxxBHlAb5DxsF1Cjq7JTKI4a9EMg/S5W7+VlLyMNNUPQyppzMlESIMkDjSK/Hz6LuDgQBJjkUlOWq18X/f7LUXlkrIsVvKdast4AqiBUo0XXR5omG1biIqhBUzHSGMQ8lIkS0qeAz1V5KFCIoLGz/63qYf8hkgqYoJJcAi7+WBfd/wtw+E1DRJXYjJshhBaEjXbe6U4T5ItB4cgEzSDNRnsehiVIllS8qxZXV2TKCTlAQgKB/vc/zrGYrzPoCyq2dzf7X/rOYMGqSEYZJBLC7OSkpeLlZUF5+04GuVxN0Z1MQN4dgs7BCOZXYl2UdCP2/trdPGtRXIXMMEQn7k47vkpmYCTRK5WklKgS0qeOVdcrWpYa1S7aea28UDSMzOdsRg5CbtKtZM0Qq9oVPetRhK+pUiurkJ0Ee0iz/OY41jYeOwH9+RzcAhFcGHIC4j9wUHuraSk5Dfg4XA0GuTFbl6Ejq1ejB4xLuiOB6MD/sxWEWuQ58Vuv3C72KWf5xvfnUhyZeVfxMqoN9Bo2EHakcKuxGj8FtGBR3W2hzZtR2+qoFvJ4uig91lSUvJlJNje7ozaDx73lfc7gWJbsI69xXiwue9Db0k50Ac62DtZEjZSaz1JBp1OZ3ZfdeBbDrffcqeTDULI2ilxG3mXwHCvV80Bz0nISAOgXVibMajbLbJ9DbNLSkq+Fj5z5uej7TOPeqqnbULYAm9IbIJ7OggzXLuQ3A9yJwS2C7z5OD7ceHc775482d1XkfxW2WAJ22ujW7fw3NzhTiySjoLatrpAFVRl31fd+Ek/i8J4V7CRZX4YgnZCSA/EdLOkpOS3Mw6Krsb790/36vX6hqy7JswCiqgpOfvSb/9OfHHYrp7NJrAOPCIWm2fnft5+8ou/2/afzj5UxK/GkyfJs0y9EMJj27cRn0reAh/A5K0KxNDQD9KmxYMYfScEb0xM5OWsZEnJc6RaZRijH9jhOuhaCLor0dvvKTjbO9gfA1dj5KbHQ/sDaQj2rUVy/AZZLYrCfdB6kG7LvgvaAh3A8NcRM5LoR7wV8P3RqPtpv7+5Ae1SJEtKniPdLsMkrzywuC7pms19RH+/ErlCFnKArQA3FflFSvyo5mRzP47/aexL8bWENzergyTJ12IMH1mqMbZZn5MUxvtx8u3C7M/eQh1gA7Mu6Y4Dj/J8e2tubmoEV8o5yZKS58jDhzfzcPjcVtqvOG2GepJwBLFsM4TP3IH2Fpz4ayw4+Wx6zUDfeBfoKoSbxHgD+wOn6aO60gPrTrBvK1Smp7uDtbXqwywjEQGCGo4s7F2IxvjzbdYpjYXSZkPSBwX+wIU/CC4eLy2tD2EqcoC9d0tKSp7KF59pX7z4J8XDhzd79Qk75MXdQlwzIViclXUy2qcQdUlP2rJ81eaNXGAiYhPzKei2Ha9F60OFeC9R3r7XvX9go8j9XMY3XFgYPOh02LZr0aosIE4i6ozdgOq/+6blvWx5BD2W4vvE+P8p6na1FtekqyO4um8nUlJS8rXQ5ctjkXzzTTxeiPxWtOnByqDdPk4MIXGM7YB2LAeJBaxEWP46+qO9ekgxQmwabhD8yxj1YZbGj1ot34Nbeat1cGbb+yiSV+Lq6kr/6NH6aGoqe5jWixuSponasXxY5rCkJlAD6oB+e7jtAjHEjIy62Du2dxR4t4j+IBJvZg3WB73BLsAvfnExW1o6nYbQ0+ZmPb9y5Upe9rwpKdl3dPkyWllZCefOHZ7OMs1kWdra2QmdbjfvNBqNXdgcAsOJidBdX49roVYU+ShJRagEERU0a3sSNAHObLIvtngwRKxccm7oy3Qtd7FuCV+T9F4RRndFZV363/oHfcL7JpLjcqDVAnC7/WebRR7fB3qgu5JekfQKeMn2oqQKKIw/v2kIrlx2F9OW430Ctwh8QowfyfGGiv59yHa3t9cGNlpbO12102YIrWR5uej+6Z9e3H3rraulSL5A7PVtB8b30/M8lpKnY6Nr186nMzOtNMuyY2kaXpV0tCh8L0bd7fWGD2NsbnW7bJ08eSuXjrRHxDxLg4PcdQy3IS6KsBijFyU1AzQFDQCPFxoX4F3bu0S2o1gLYi3aDwpzbzCM90aO2w1vd5/FOe+ra87ejV288879rddeq/TqdX0C0/dirG4rMEIaSaFiMyN9RXtJOzd0wRtCH+e5f+kk/q0KHuR5/nhx8coa4Olp/Pbbl5I/+qO0lrWSiTx3hSL13NwbA7harsB5MXgyZPv1m6EUyu8cK2FmppU2GmnFiY8G+AnWG0p4L7EaJLkqlRClra602rdpA51bt1a2p6en74xGWa1SqS4rZMdC8HHwLFGzNtOf+ZiLfK+kZyvih0i3C+l2TEabyWCwuzx3cxeuFjyj++NALI1stLq6khw9eieZn/+DQ5CcTJL0JPiIHZZtlpGrNjWkyrgOSQIc7XETH9ElejPARoy+bcUbvTi6kdWqW+x2O4uLVzoff/wXNaapTVbTlnKfSIKOO8aWCx6GkD+wtT415S24vS2tlpnvb8Hbb5OcPn0xLC1V0kbjdJZlSTYYxEqzmaXDIVkIyjQqUoUizZWkkpNcSarciTIFFSRQBAgaVzwoQBQkkqLy3JLCZ/ejHZ0kSYRiz2Uq2naEEMc/qxjfLhRJEnI7L5wmeZoVuUlyO8krZtT1KK8WHuV5MpyefjyE+yMOoO3o9529TqTqdv9sfjTS4RAqhyx+AroIOmfzieCToPhRnvv9EPjVcLj7cHu7Mzpz5udDQHAxuXOnktbrR2eTpL4YoxeTRBPBmjBqAU+KEgtwJ0Z10jRugh5BeNRqrXVheST91TMNfg7Ef1HCly+vxgsX8MWLP96q17lVq2kzTePNoghTSRImbbcSq2XTAAKEEIKjUd+O/SSEjlLvxJi3Q9DmYJBvTtT6GxPNtE9zZgiQznYbVaqzyr1EDD+09UPwnMQnkHwSQnFrY0Mf9/utHvvYPe1lw0Y3bvw0PXOmlT14QD2ErJnvJq1KGpvDXZoxhCZFbISQ1HGoC1UNtQBVpapQuDJuKp+m47knpUBiK4EYbCmEL/uPSsEQ9yoWXEgqpJDbziHJpTiyNSSEgeWBlQyC6eeDpB+CezEWvUHwbiV6N0TvhtGwvbZWb29sHOlWq2ujv/mbSyO48sycal5kxgI5FrhWKzkE6Rt2eANzGnEKvCiUYc9HayEEhRC9kwwrg/l0qbO6ulL88R+vFvbV4sYN/Prr/93OaERRqWTbeZ5UkyRWQkgrn++vcIwaxqhhrZb3trZGuzH2uu+/f3908eJfP/N/swMzqf08aXJlG9iGL1/sWu3wdMiTmTSrTUhpgvLERRJTRu3OMO80m0mn1+vvrq7S+9nPnn4zN/JKY0Q6X4gTWRLeQP4joWXgA/ACJLUkib1mc/KeTa+MHL4+X5wfBMLU1Fgg6/Vai5Fns1qcyQvNxuiZGD1DCJOCCcSkRBOpaWgSY0OiDtQkqraqQAZkSHt9ULSXxPtyOQlS3KuPzW1GwEjSwGYAYYDYJbpHoItDl6CO7E6Rx7ZFOxTaKmLYBraUZI8VQ5iersV2e0KXLv2qsD9P7JX3xm9mdXUlnDvXylqttBJjdihJuACsgGax55CmJM0iCptD2NvRvk3C+qjSzRcWFnaBfO8aR/h/2kD7t+70O8SzdvI2XI3b2+eLVmupV2lUNBqFAXKQQoCRQ5r0mlnSHw6Hg263mV+69L8/Lfmiy5dRrmS2kugU1gXJR4AmUAHmJY1iJEpJbge32//L3XbbG63W8XXprTKhw2dCKLhU3WGyPuqN6lnI6kle1Hd2knoMsR6i61GxnlbVSKxGUdBUomZOaCp1U1YzoKZE3XYdu25Uxa5KVJEqNhXJFZsUPI4kRfL5/p/e6mP8/40gWKSysKXxNqgAVQU1kScEA3Af6EvqAz1DL4hdi90Y1E5VaSdRncU6u53Oj3ZjfKMXgvo2/e5m0SuKUS8N6W4x6Pd6Cb3VVXrXrl3xy1olYRNWVwnnzx+eq1aTIzGmR5LEb9jhDGJOchPIQNFmB2sb4ie27hK85my4nQZ6Fy4cgMHFM+SZiuQ4A068cOG6b9w40ZuayvIs064NUl92xYOBin6/nW9vU1y4MCye8obX5cvoT//0YhKKMEvQKUkXYvTRvX7cVWA+Ruoaz3sCpEVRtGLMb8D9LZ6ha/J3lbEAXQrXrl1Ljh9Pm1SKmYxklsKzBWE2UswSNUMIM8RkOgluYJoOrouQAZkjFQWlwWQeR4eppVRS4rEYJuCASIwCImAFIDDuxfxVzaI0TnaSjJ2dnTDez9hHEKJN1Hj5a2GUgwtBLmk8NFcyGv+XofBQYhDtLlYnEtqO3sJxiyRsJEm2nudxQ5XGRjMWGz/+8fpoYWGlePPN1ZfOcX98f6yElZV60umks1HpqyGG33PkjIJPAbOM/y0qjCeXtxW4A9wE35H0aDRie3OzM5qZ+fkL/bw9854wezeb4ecD4BtXydtw5Qqq1XpKKrEuh1nBEmJyr94qAaYkpkF1SY7ETBCSJNmFzn37p7vQyqWXY05qL2ILV69eDBcvLoZ795Lkxo0iXVwkPXnyTDYYMO9YLAWlS8KHJA4FacnWkmERmLdpCppYVT/RC43/NT9Tj70pxfGfn2jfFzTwSzLzVTlDPWUD//g7+vIAnc9016Anv6+9nyz25jc7EXcQW0iPiGHN9sNCyX1SPdgrNalOT09paWlhcPPmpfzu3d5oOOzEkyfbBVyNwJMFDt9TVpLHjyfrtVpSHxQ6kkivSf5DiWVgFjS9Z2ATbfcQj2MRbkvhhuS7IWh9cfHKgS0VfJa8cI2znkSjV65c4MiRcJ8Q/y5ahdBZ4CxwxKY6rsWkalgIEFGSJ4lH29uQJIfuAWt7n+819uWwxvVGvVNrnLlQtLa6lclGo5iq15PJoogTdn1CSZhOYDqaGaMpocmIpzCTRCYlGqDKuI/6i44EZDINj1e6JqCmzWy0l0HbWFshJJtJJdsqCtqzs/Udqd6uVmd32u10ezD4UTtN4+6773Z3X3/9yvfKnm+cN1gJ7fbh6UZWO17k4XhqnyfoHLAoeWJvXhlQG7MdxBr4Wkjiu7Z+lSTxznDY7T3XE9lHXjiRhCdCeSWurV164LQeA9pIk9C3aWBNSLTGdZhUwQsoNG3SGCGEJLPVYDxc+96L5FXuJz/oTjUHFHMhTxZDZNnKjkgshRAWbBYTaBnXhepCFaAiqCAyUAWUipj4GTWbP1gsUEUiSCEDGhBnLQ2DNQSGlvrIvSB6BB4rJo9AjyoV7tn5vXo93B8Oiw3GFRPfG5F8MsQGUjuZHsFZ5ItC5wzHJRZt1RkPs8G0BfcCfGzpWgj8MoThh6NRv3PvHqVIPm/2IsqNx4+3usNkaishTGLNEdwALcboINECmrYnQIpW4RgyKRqK7vb2pbVeb3tw58768Pd//8UvPLdXUiCFhRSy7FHXlWq/1ygCi5mTxRi1bHFCgeMyyzaHgEOWa7L2vvvZGPWLG8ZfOTx+UZCA1OPz3WOs/Z/PBrhg3B6gwH6EdN/wAHkukk7luSejkodzc5XW2tqfbw6Hxahez0e93sxoc3Mzv3DhSv4iDsWvXr2Ynjmz3CqK2LJ1PMt0DvMjgk8IxgXfY8OJEVYf+SFwM0b9Sgnvj0bcmJn5D7ef93nsNy+sSO5RzM+Phnfu9DuebH4cgjIRtuz4GuNubUuM14rXwHUpLBIcJI1ikUQVrbRVad47d27uPlx9/JzP5Xfi8wwxarePT8WKpinijJzO1fBcHIY5wxwwa3suSLM2s4gpxKSjq0Lfkyhxv5AcSZCFmfC4mVXdMCU4kgRtJLCeNqvrSWA9rbKRpFqfbMaNynR1C1Y27dUR8EIUrD8pFN/aOtbMsvQk6DToVZvXgMOYaaQa4/usg7UB3hS+JvOuHa+HPN5xkr0wZT3fhBdcJK9EYHT06KVOtzv4uO90WzF5FBSiQph0jA1JYCpA3faS7RnsEFCiRNUYVI2xsgu8kCL55pvjTP/U1HaYXBhMh1HlaKJwVPZpSSdNPBqkSawpSQ1JFdsVmww707hWUULyd/95fkZYoCeZ+Ba4CprBfuKL2EdsI29H65GJn+QFt3D8pBj4zq3hdK9793y8fv06HER/l33nkoCkWq03B0U4paB/YnMe65jEYeEWkBjLqCv8YGxX5uuGX6YV3h0Oe717n/a+N0PsL/JCi+RnmXJfGX14/6dbxXS2O1uZHIlsnljMCGHHwxoPsZqg2l6h8zJmFE1GjCPwbrf757uNxmAX6Enf7cl4+2IG5ys7O/1qnlcaWZY3iiJpOFSOEX08KBzDnAJOyVre8/JsjpMvwBeyvl+Wxe/LkPrboi+WJj3p1QTs3Um4AHUluoZFESYcmcCarCRhKlNrYvLEj7eOvPJ73XZ7tDscdgazswykn3/XnPP1zjsryd27+VTaqk9VEx+TwznBa5LOGGbBkx6f9QBoY9+z9BHwPg4fhMCtVuvfP3jO53GgvNAi+RnCZ9zKAbcptoa97MMQHbHWsV6PdiJrfjzkVp1Iy3AYXJM0sDIPcqqDbu3TpPAdYON5n9LTuHyZcOECunXrWLPZ9HySNOdD0FKMlUMh+BDWfIEWbM0Ds1h7Bb+qUA6n9xEJuWLrST8CgaeEljFng7I1536kQvdzVx9A43GnE9dsHjMuHXruIfvly4SVlZVw4cJCLcuaxwRnKXzO4jWbY+DZ8UopBfAuaB20HoKuK8S/j/APMYn3FStbz/tcDprvh0gC0pXCJk5wfqed/+ij3ai1LK2uJ5EUaR5U1VgoaogmcgVr3hAlpzL1JBahiMNtvpsiqTffvKRr164lExOTzRDSQzHqFHAG+RwKZ4FWwC2sBjhVcAZKPC7cDmWkuF9YQplNGkTN9qTgiKBvadeRbgi6DfoA4odpGm72+/3R+++zefHiXgH8cxbKN9+8pBs3Oslo1KulteYxRy4GhR/u1UEuA1N7Apkw7m+9Fs0nQf5Vnse/T6aGvxjyeHiT9e/0qGs/+N6IJDzJeF8fPXx4oj2YavVn86RayZL3ZSaEu1hH99YJ1zQ2WajbLBEZCYcY6Utpr9f7HxmNep3bt9P286yDu3yZ8G//7aVqno+qrVat0W6nE8eO/cGkxCFbJ0LKCfBJoZPACZuaRMVQAX2h7VIpjvuLZI9bJY+XWo6H4/a4JEjy0JA9ceQvCqaSpD5z6tT/NLexoZ16PexsbQ06U1OtAXwwfJYOVU8Sfe12OjM9PTeXphxW9GsmnAWdtJmWaGHJdk+iB9w2fBCS+Cvj950Ud6b1fxxY463vGt8rkYQnQvnz/Nq1805O/mgj7/NBSMMgU1hnvJa3BkzbbiJlEhMShxkvtRtagdEobRRF7ZPl5fYtnmMd3JtvXkw6ndqEXZ2RkqU81wnbx5MkHAIvErVI0Kwjs8jjviFjI+OS50OQnMaIJGYVoIieVqJlKZy29VDS7VFMbsck3F3v9Tfn6uc24dmI5OdLUUmWF7LlLNUPhF7F4VXkEzZzEjWs1PZQYh28ZvyBxN+n8t/Z8V467nX90vC9E0kAiQKuF2+/y+bF5Qv9yay4HfPmdhKyaix8eM+uK2NsiDFh0wTPgYVddaAWgoskaT5kz8Ho+fBGEmM+GWN6WNIZ4EchhB/aHEZMGE/IpIgAhD1DiN9sZFxywFi29uzgyGxPBykCHZu2Qth29N878nd2IIwytoedXWD3WRzdlSuE8+evJTMzp9MkrR22wo8i/OF4Wa8OabzUUOAQgto264hPML8i6O/yvP83d+6MutevvwgZ+/3jeymST7h24Xp+ngu9zsNOvlSp3wuKvyKEGuY0cJKxgcKTRfo1xu5BQ3BUEvo5cbjd/4uJMNJWq/X3W+OGYweDfTlcvXo/OXz4XlYpWtO1RjbV3mQe0mNKdVTSCaJfkThsMwvUJNX5RwmZUiCfH1/Kin82BywZTCq7ajgdiAZPJKk+jbF2Z3Pzzx9C3LIfbd27d6934cL1Yvyi3x9s9Oab6J//80uzlUprIQQvWnojRs4EadliCtOQwKZr2A3Euya858h7Jr4vp/fuTY26r09/tys/DoLvtUi+Bb4AxemldYfu1Jry9HpQsR0dNoACNAlu2ZJEFZiyCY5UEIUUkjiKEzEffQTndw+yHcS1a9fT48epxDjTCLXsRBSnkU4RfETmqM0SaAaYGRt3OP2t7S9KvjOMV/e4ZpNgHTe0MEcNdwLcjcpuk/PRIF+8eaw0bsQAACAASURBVPhw9vjWrcWhvbovyZ0nXQIuXXoUqDQWSXwehfOGsyHhFDCPqYVAOjY01pbwo2jdgOJdS790iLdHDNevvxA1n/vP91okEf7Z2H26sCceQ2tne9s3o+ZGKJ2SObn39q8CjbGzCdOgGUECrhOphhB6Ozu9T4EDazw0NUVSq9WrMWpC0gngJ476IR43dwemgM+SMX66BWPJd5Mnbuy1PTu/4xJD2/eQ7irqBqFIakmylYzmO81mP8LlIby1HxlwLSwshJmZVpqGZDGIC0j/ArzI+MU7txdBYtMBtoA7SaIPipHf7fcGV48c+T/XeYn7DX2/RfJLrMZr187nMzN1Go2p+w7J39uy8CuC05gToAqiOo7SmBEcExpaSY84Uayv/893KpX8cavVX98Pm7WP/Re1rB2b9TRppITDRV4sW+FIgs/EyFnBIfDk3pRAyfcKBXATmLfGvpcEJmKFT+ph8t7Ozif32+3/dbvXW99dWLjS/aZR5edZ7D+bXV6uHg6hcTgE3ijEGexFoUnGRiaFoYPdCeIh8J7FdZO/L+luluV9XmKBhJdIJPfKg/LVVeKFC6cfZFlwDNlasLZtgsQEYsJ2onHWe9pQCSiVieA0STShUfIB47fttxbJsD2sV0NzTnlcMPoBhNcknbM9r8C88LRRTZC91Hfp95OwZ9GWgOoQJ4DjNp/keXwvhOS90SjeheYaXN79JlHlFw2Vl45ns1nQq0qSN2L0WZlXgCVwhfFqooi9I3jgwrdC0Lsw+lsx/Hh3MNxaWrr9XVsl9Mx5aUSSz1c6RHvtMSxsb24ObkWalb25vnnJ+biMhilwSzBpVAMQ1JBCYbp37+b3Pvzwp50zZ765ce+eHVUC9aTfr0z1yQ9T6IQd38DhJ4LXERWNlxBm8JK/xr+/BEQDaAimLC3IYWh7OQRVIBZJYtmOa2vXO/ZfDuBw8fVaj1wK9+71qkeP/l415mGJoHNE/gDpKPYiY1fxCETjPmhd9m3E+0Xu9zo9vXvs2P9192BP/8XhZRLJL7Aa4WLe7Z6m1Yp3Qgh/GyM90DngHHB0b513zXbFMIeI0QxJklGjMaPp6Xjn0aPBI+Dh19njk8Zam1yaTAbVhXyYLaYKx2VOgU8hnQAv2VQFqXG5QuYlweMeFakdAWYinAGlAS2ELD1cqUwtdDqjR3D7ydLG39a4TFtbo4l6fepYjOGY5NcUeHWvKmKacRUHoI7xDmgd+VqMvhakXxHz2zHmz6Qk6UXhpRRJiWhf9dGjp2On47tQ9O3wMEg9oBrtJjBlKxtHdJ5DNKQYDCihmudqpo1aATziawR7b76JLlxAf/QvW5PVhJNZkp7D8YzhjMwZRyaAibGjukW51volwgIlSLI9LXgFWLR8WLBYiNk88iHD3D//ORvXrn12v33pvnsyD7mxUZvIsvRUYS6K5JzHL+LD4+WqVMZfdBd4iOJtRV+Xi/8ah3ywW+Tt48fzA0tQvoi8lCIJT97EVwp7ZePOnUF7evrQep5PTFrJrAhNxr1eEuNJpLpxC4IYD9uryMOYs/7pp5c+Pnr0Zg5Xi6cZrdro2rXz2fLyhXqeU0/gmBLOFi5+FKxXxJ5bj77YraWMIF8uPquvDHvTPU3gEPaERY1IIyWEIksGf/zH/8P2v/pXofev/+3H/X969P/tj7/+uVheuYJWVooqwfMhJCeAE8ChvSklMW7P20V+pMDHET6Iid8fwQeH5v7Dx8/81F8AXlqR/JzVePToyujx46KXZfETx1BFsR2CfmAoxsMUNyTVbWrgeY07S61Vgu9kE7VDnc7pTqt1ugNXvuinp3feWUlu3KgnCwvT0zFWj1cqPh7hFRWcBc4qsGgz8bzOvOS7juoyS0hh7IEaGkoq80Pr9qnWq7c/ZPr+GXoFXi2k8Zy7TdzaykZK046tjWhvh7HlmYEesK3gLcx7mH9I4fogFp8W3eJ7aZi7H7z0Ijkeeq96fp5eu/1ntyV2YgwP7ZAraMJWXeO7rwqqgeZtJrHWon17VKSHpebaxvYwh8/7ethw40Y9KaazSlJlJrPPQbiYRM5YLCOO2G587lVYUvKPaABLOE4bTwjNE5JjqXw1yUfD2Q02mGUIl8y4HhgJd7thmBM7jslGEFs2fSFL3gU/Au5G/F50/rf5aPAPaTLqzi9n5Tzkb+ClF0n4bBI8t+9v3bmz0A3N2rAmzSVoelxoG49KCrYroJHEEBhhijSTC5vJqYrhiRX+JcFMdeZIfybvF7MJldOFfT7A6wQdx8zuDX/2rn85vC55Ktn4oxaQgGqIaXAvZJUuxcJga2u4aRebe4XglohFEYY5YTPApxGaQnWbuqQ1258g35L9fhzx8cLClTKL/RWUIvklVuPDhxfzpaXTnTjR+DhRwNYWcMEgQya8bWs7mveMPx7F/IGTfmfwWQ/xSylQ2djYmUmT+tk0S85izoagM9E6EmDaYyeiMjFT8rURqni86ioNhFeJJCFJ5/I8+SBNiw/W1i4V29udkf3z0cOH7len4v1imBRp0C5mB8d1m8dSvF3k8XYIvlur6aWxO/s2lCL5BcaJl6vxF7+gfWbi1ZuVJD4aDCrrUiJgRpAYHsjxgez3ijx83Otwf339ZnHx4tXCRg8f1jLoNKrV6izEV4OT/8b2D0BzQnOImiAp112XfEOqEqmh6agkiHnsYwGqRaGdomBzaqrF6upKsbLyH3q3bq08aLUm14eublQqtXU7PLDj4zzXndEo/7RSqQ/u3Gm/9IXiX4fyKX0KNrp69WK6tFRJJyaOL0Pjx8BPgBCCH9l6FEK4ned8MjPz7z954uBz9GivEuo+nIrDcnIqoN+H8Pugk0DD46xl+WIq+RbYoK6gi9lA/Bfw38SYX48xeZim4cHkZNKGzShdKTY2Lk01kurCMGdRJNuMdtYmDv3fT/rNl+sUvgblA/sUxnmaqwWsuN2ubhXF6MMQ0l2wJNox5p2i0ObOTrEDcOPGf8lOnZqt2smESF9xjG8I/SCiUxJLe2t0K6Uhbsl+IJFhNxQwcNYmDSGdT1PetV1sbm4WMzPNweXLeGam06dd33TIR8Ww6O8+TncpxfEbUUaSX4F9OcAnlc3NbtWueDRaK9rtJD9zplfAapSIDx78m6ZUbaVxNJ820n9h4oqkHxkmsSYYr3J4YohbXvOSb4H3psfxXtfGHeEdiVsSqyPH1SLJb4S+u7Ozw650JY7t0ghra/jSpeffX+dFo3xgvwZPuhQCPLnJxlnsi8mtWxPJ7OzJYx75eEiTkxY/Mb6IdAarylggy4i95CCIQF+ib/uR4Sr4qvH7JHw60+RT6O4CxX64Vr2slCL59fjiddor9fnLbG1ts1qtUrEbPwb9RNIPbR1HHAcWgVRS8qRpVEnJ/mIDOSIX7GA+IXCLyPsxxl/WasXf7u7G9dnZjYH08yHlMPt3ooxwvh5PubmGSa1Wr45Gw0YIOhFC+InEP2NcANzw2MgX25TvopIDJMWkhlRQsVkWnkkSdwYD36pUhp2HD+cLm2E50fO7UYrkN+CJFf7CwqOwtcWhNE1OpGnjBPiHyEei1QBVgIRSGUsOnC/KnoOhImNbi5C8ZtMfjeofZlnxyT3+5NY77gxXWY1vPcVjoOQ3Uz7I3wD7UnKLtazFZBba06+nSi5ift/ouNBx4+Vx24dyiF3yzIlAgZwLNm1/in3b4h9cxF+sD3q/WMvvdAZHq6M/foZ9vr8PlJHkN+DGjU5aWViuDwo160k4aukC+J8CE9GekFQvJ31KnhMBCFiZxz9XwIsywUGP62n46HjzUDTpLlCK5DegFMmvwRPD3E5nfmoQdVJJOJEo+ZHGCZqJsfFFeS1LvhsIgqEqBYMPK+p8s9rsodpNtga3bT6B32rcW/IFygf766HVVcLrr3smqYSzUvh94zO2Tggmxs3onZazFyXfBQyJRDVGUikcRj4fC+o2TWI2WF3lztra2FatFMqvphTJr+Cdd1bStbWF2rlzaS1N08PAGck/xDoCzAGNcaRZCuTXx194MPUVD+kXe+eW+dmvSbBVGV8tz43/ypOJtBtTPXzttf/+4x/+sNGHYR+uDJ/ngb4IlCL5Fbz++mS9Wq0uVyo6InEhotMiLCFPxUitfGx/ZwxYcrRtSb+ecdW4YJ/A+A1UXunfBZEF0ZKF4Xgg+UFWn+rkMdx/8KByD1j7ym285JQi+RXUalN1SI9Y+iHifECngCVDMwRSl4OV35W9zpVEpNz/uEVv4HO/zSc9f0qh/KaYCtIEUA9Bx8EdWTEkvqZ67FCK5FdSiuRTsNGNGz+tTE21MojzNickvwactbUseRJr7LL70j23X3otRJ6UnvjJyg/l4MIixy5AEVSAIxAl4p4gRsbtAYvxd35dJB2MUiBBDkQSaRxZemwUkgABHBCJUIKd2krBqXEqkUAI4C+UY71ssf/n5Wi2FzF9xteuFyOP19d/ujY72xvCwqhcuvh0SpF8KhfTiUO1KWX16f5Ap1I4LfQKcASYKmsgx0jKY3RfoofURe6AO8i7MrvGPeO+CH3jgewhaCg8sp2DCgKFiNEhfGm4LSzHsSjG6FRyapRKqtiuCFVt15Cre87bjb2Olk1Qy1EtoG67PhbLEkwTWGLseP6YhEfDfHrr8e7U5nCrswWULRyeQimST+HOndPp5EJ1Mo7ickjTEzHqFFGnbZZCcLo3V/bSE6MLiR5oB7wu+7HEY6xNyZvR2gqiXSi2Y+GOQtytJt6NsRjYcRRjZeSiiLkT12rh1yYuRH+YS6ooHw2yEEZZkmSVIoaGEzWSkDQDmrA9EeSpaM8EaRo0F9G8AvPYUVICrj2fK/TdQlLTpgLMCdYgPEzS6noxGIVmc7JHKZJPpRTJL2ATrl69mExNpU2G6WFJr8ac1zDHkGckNeyXZbRmSypsR9AI3LfpSxpHhdBXoGN7G7QNbApt2HFT8rYdtu1iJyfvSqEzgm4y6PaHaezt7n46XF5mBFfzr1OC8s47K+nJk6SD1iibLhbrlXpaK/K0IactO2nlORNJ4kmbKZsZYMYwC5oCT0lM7nW6rIGrkmqGulAFEfCTofv3G/tJzxzbZhnpbJaoZ7LgSPsXv7jYuXnzdPzZz65ESjOMzyhF8nN048ZPsxMnskq/n0ynVZ0I1g8lXgMO763JfrkwudAA2LW1JliL9jqwYeJGEFsK2omxaCvGbh7Vk+JuCPRjLPpJ4r6KMKwk+SCg4Yg8n56eHU1Pf1rs9Sn/Wg/i6upqXFlZyY8enTQTrahBe1hNW71hMewkSVFJ06Sa56oliWujUdEIIak7qBGCWpgJw2Q0cyGEWeE5w4KkeWAKU5WovmyjA4lZxNlYkCmEoVIenTr1g425uWxoXx5Kb5UiucfLEhZ9JeNax3/T6HTSRgjJ8aKI/xr03xr/wFYdXAe9THNbEbMr0QVv2nxsh5tW/ATp07wY3gmRdTVie7bebEMvh01D3dCJ0DKsxdVVWFtb8LVrVwzw1lvsGcb+zujyZXThwiUtLKxpZQXgnODTAD1BK4zbEfXV7abNPKk1Y1G0GIYT4OMhhOOIU8BppEPjeTo1Gc/TvSTYoB5yT+gx4j8S+Y8hDP9rv5/15udv9lSu7/6MUiT3sFfSzc1jy06S5QBnJf0zWf8cOIHYy5p+b6ONXHJuK5doR7sDtAWbiM2A1ovC92PkXox6IMVHeZo/yoN21N7o/dVf/XX/rbc+d5Z5+22SS5cuJffu9dJ6vZ6laZqFUE1DGKVSLdnZydNaTUHKw3CoUFUqiELpZ/fj0LkrjnFAbjuLWaYCYqxU0rzb7RW1Wn1UFIN8OLw3Wlioj6BX/PqD/eGHP63Ozs5W8zzWsyxbsuOSFJYIybISHRZaJHoGNIM9hWgBEzZVSU9WUX0PnxF7r+IgN95B+k84/qc8Fr+shOTeYNC9v7h4pfO8j/K7Qjnc/ox6EpNkSZHzBL2OdcJiApNhwl7rhed9kAeCRG6rJ9Ez3EG6Ex3vyH6oyIPi/2fvzXrsSrMrsbX2d86dYx5JBseMnMhK1ZAl9YPQ6pChFlBqt+GXENpSy13dFgrwS7/7KZnwv9BTQZZbdvLNXUACNgyxBKilhpsqdRaZzIFDkAwyGHPEne8959vLD+dyqFLWqAxmBVMLCGSSjHvuPtP+9rf32mtDOwCbIbDpnrcBdMpqdbLDdPB4cyN/3kECwNdXv5XsA5V0olrN8lodueqS191DJYSsUip5WUpSIE3SVIkIK6L0ZwnfFCG64ClKUQqZxKGErNtFP4Ryv99HD7CONeba6030rB3677wDf96W5eVGfuvWHsbGZmOWZZDYZsk2U/O7Ro7FiOkALkhcJHnSpdOklsw4Lqk2Ekx+SW+6CCBArFA4KfEriQXIGLxaOQTwj05yhH90kiM8wunQwHBOtDdAfBXCSTnGi77slxsS8qdVauoBoOugbsjxIGb9+9ev/x9bKysFx/HnOd4YZpO8068ipmMVaiqXTScJJvM8jpHWAEJdYhlgmURJYkIigT+L1AXlYMhQKNb0AfXN1AMKmlG5rMMc3B/0kqRWNTZrmV+6vDrAu1ee2jHi/UUUM9E7z50vr1yB/c7vrDYi6meA7GwI4VUahoRVJSQkEgnVz+sa/8ph1M1EoALoBIqhYomEg3Jauv1Fm/erhJdzlfwF8Pjx79br9YnaYFCZTcrJb9HxW6B9FdCUgCmIL9GLIgFwkC6hS+gAxAGEbUBbBLccuk/j/TzwQRzmu6l3d6anrzSfHkCrYXsb1UqWVJJqUsuTUHNP6u55zUxVSVXJ6jLUjVaXVAfUoFAXrUKhQqoMMBWREkggBRQ6nM8/jxFUBBAFZBKGADKCPdD7ReTLNog2HR3RO3B0JO+R3jOzrpm6SYJOjHl3OMz7u7vt/quvvj98djW+Xe71stnBIJ01sxMynSFwWsIJiQssRnBMAZwkMYEfbZV8SaAIYB/UPqi7gP7SFP9yMMAts6fDxL7UJPOXPkr62VioAzbHNJ6G47TIUxAWJFbIly2ZT5GKoiLFQ5D3KK05cM+F+4DfE3EgsQkNml0lvXy33X/+AGtr22mDS2NZOZ2Kuc3SNBcC54BkhvRpAFMk6iJqBKs0pBBKAlKjgsAERXRufKKBSPuMSZJS0a0jEXQSUUUxKScsJ5GRyARkIPqkdWnoAnYAwx6gvcy1MxxgOyps5+T+9PT0PoAnTlJAJ6tWcRCjDWMcNpWXNkKimy6cgngWwFnSzpE6B6AuIRDgy7UDJwHU5AygDyWedtfZNPVOjHH71q32AH+/ZfRLhS+9k6xMoD6IWDRLzkk8TfEEgNmXJ13/ZARpMTTKpQHBPqAtCXdiHq+T/smgP7z1H//j/3nrO9/BU+6iBGJy1aTvJGtrn4RmsxRqmml4ivm0xAWZn5J4JiqepvGEhBMkFwVVjaxIqBRpRj51f8V/P+vi/vjf8e/9/Y9/9LkGyQyOvqA+iW1Jj0ltGLnu4AOTaqVYLjcz8aOP/ju12x7ffruaA9sO/LPu2Ni7bQBbEnj5Mvjv//2/OmVmj8mw664haWWSU4LKEMogSngqunHsnxQDUCNRAywadUoWzkpsksrGxmb3UKQrvrQ47jf4l0aRkF+13Wb9Gwn5dQhfA/k6gNdHMmgvC6Kk0dhRHoB4RNNDiPfdfS1Qd93xOM/zzb/4iz/bunGjcJCXL4OHh38wrjLGFZMJKkxBmkLENGkz7polOUNiGoZpAJMEJgBOSCqNeKUvJBInkQvKIGQgWhIOCRwK2EPxswtwl6adGLEH+H6A7Q+H/cNqNRzu7Dxofve7V59uw//4j1cnq9XKQgjJvBnPAjgP4JyEkwBOApoHWCFR0UvFn1UTwMeEPibxQ3f9oNMZ/OCv/urP97/M87q/lJHkEwcJIKTAjIBXSLwlaQFg44u273OGk+xJOAT8gRzXXfoAEQ9C0LZ7thNC0u52D3q///uIT4oat259K5lbCpPKcMqScAo5zkJ2FkGLcEyYcYJETUJFQoVAyYUyqRKK6OSFcUqLPCFTQEGFEEYVwDSBEwAGIPpyHcp5mBh2Xbwv+r1SyR4Mh/kjYHK4soL86tWiOn75MtoHB8FLpexgMOAuyQckb0r2FoBfMyIBMSExGUWVLwtKgBYAUFIu6XGlYjcvXHjbgGv/UH7rscWXMpK8fn21tLAwKOd5uVKr1b4l2e+R/C0BVZJVqRgHe3whAcwl5SS6BB8DeizpVoSuRfX/i4bdR5wvd+ZwpXv5MvAv/+XbYWJi3mZmGpUsG1TK5XJNoXoOsvMgzxNchvTqjxCwdVxythLADogOqX133AZ0C9BtRawB8W6M2k1T73c6zcHJkyezK1f2/fd//0p88GC1yom8ZrHaqDH9Jpy/DuOvAViAcQHCJMlk1PJ3rAs6JHK5+qR6Ej4E4vvu2ftk7367vTlYWvrr/pcxmvxSRpJLS2k9y6pzIWg+Rpw2w7SAKoq5xce+q2YkYHtI4ADAFqDb7n4b0N0IrGWKu90k6wFZNgfo8h+vVjbTylgFsWGyRSuXT5BhkY5FJ07IuUhiDuAMxBqEEiA7TmssqcSFKkkHdZpi2YU5Bp1zJa+H4BuwdGN8fGqj2+0e/PZvj7UltIE7+ebmxX612peGWAtpCoE7Dr1C8QKJpaJfXFOjWUfHFhKsoLyxTGIcsEWyfEEylcuvbwNLQ+DLV+n+UjrJGL0B+MkQwisAT6NQRakBNB3zaAAAJAhQE8JDQHckfRBj/CDG4T3A2pjvtdbRG67gqpOQ9uvlWu6TCOkczN40+kWBrwucomMKxDiEMsAyoBJJO269zhJSI0xSSrECaJ60DoADow5AuyfxwyywjAEfqtoSgA5wLb95c0xzc3PZ5GRvLbR9NynjXlIt71Led8JJatTaeKydJCCqyCMHAJMQT7r7MplkZsiAqV18CSvdX0onWSqlDffkhMTXSZwSOCG8DLkl9QH0JXRouGfEpwZ+DPcPI/off//7Vx7fuAFdvgydxGq6v79a32rXqwewBZOWBFuicBG0iwBeJ1gDUf/RCImjqvLxiSJHFejnZ6FXAYJADmgOQJfguEvBolk0NMKgWt87/Ldp4u3O8jJ6S0tX+gD2ARzs7X1rL/hciqBAmgvIICSgcgkVkmW8wJzs54fiOhU/aghcZOAy3Lsxxv1r13buoyD3f6m23F8aJ1kUJFbtwoU7NhxyMgScJvGmhFMkGi/DXSd5IPExqQ0KN536iMStQc4NM7QLB7lKYNs225XJcrl0KolxycjTSuwMxTOiTkA4MSpglXAsX/afG8RocXTXQpGm4ERCnGbK+wy8L2usN+Lg4bVrbz9qtca0vX1Vq6sYHBwMN4KVUGzJ2QLYhXCOwCKKn+N+3coE5gnLYNZMU3/wyitJSVoZotiB/FzdVy8DvjROEgBXV+/Y+nopAWxC4hJgb4JqCHgpKtoF9UX3JP8IxHVFuxHZWxsMmoOTJ6uDy5chYNtu3aqG+fkwIegCZF+V/BWS50Ccg1gZCTw84QIeq231LwYZyWJ7SaQQJiCdl7BB8S6IU3Bet8hsYaG0ValsxZUV5MD7w4ODbz8+dy7bOzzkloSuhMGI4B4gzIDHu/hXRMOaK1oztUfq5nDoZaDaA1YFXPnZB3lJ8KVxkmtrK6VS6USj0VDDzOYBzKLQFkxxnLfaVA/FS9oVcMfAj8hwPc/jnRjjxvz8f9h/7z2ECxfetvPn/7BupqnZ2dKUOS646ZIZ35TsjICTEBYB2LGnR//cIEdb8FBQiEbbcMJAUEIFlHsoebW6bOVy3Gu1vrk3Nnajee5cJwOuDLLs38kdjRAURr1DCckqoTmJI5L28VtoJCUA6qPFY47kfKlUXex0yux20caXSADjS+MkJyfPVWKMc2RyQsISCuXqMqjjrUottAA+BPkQ0g2nfhiHfjNJbNddHQlcW1tJx8erpRDyOXr9NZCvOXQBzrNROgdoGuAY+fIqHf0iEFSFOAeoLCEBNBFCcoq0T2KMH+/vX1ibmsIQWB0eHGwMJydntsrlkGcZc3ihHcGAsyhmIlVwLJ+vp/nJEsgxwhfyvHwhzz3Uaskj/KOTfPmQ53k1ScpzgF8AcQrAFKDRlug4Owe25FiX/AaA66WS/bA++/BjoBeBqw68w0bjB2me16tJksw6/c3A8JsuXoAwDWCm6FHXcc+hfY5gtSjkcVrQJIwn5XqVtJrEdoy1rf194NGj/Xjp0vtDYHULwG6/X+/0egDg8Eg3Y5XU4vEc+SGORKYDgTEBi6WSnZdsECNaAB5/0Ra+KHxpnGSaplXA5921HIKdAjT+jO5z7B7i0UgF75K8S/JjM/6QtLV+f7DbaLw/KObCfLs0Pf1hLYSxU6USTwFcJnFR9LMjlZs6yQqOf5Hh88bzSj9jBAmiDPI1Ah1yWDLDw8XF6qP19dW9paWpHPiTbDD4g8M8T9bT1J6Muy1LGiMx7o46ydoXeE6/IDjqTQdcqtO44MIyqBacXxoHCXyJnGS/n9eqVVsw4zLgpwCOf9E2/QPQB7Rthk0Jn0jxprtfl8K+lDQhcAVzaROd6rBVnU1TvA63XxtRnpZcXKChXmg5Hr8V4kXCDMkotxgAvkKoRNq8iA/SFMjKGG5jv3fj6opWVkq9nZ38cYzqhxAMUJVgQ46TJBYAHCMn+Qwkq0W/OqJkW5B/isKBvgykkJ+JL42TTJJQdccCyWWA88e8ot0nse3CXTN9HOk3p8f+9PoTWoYE7u+jJIW6pZiRhzdA/iaJNyTUSNRRCKyieM7/0U/+JBTthkpROLgyyJMCz0uCyJ1qrOxYiz43Nzckv9sHsAFgo9n8164YGhAmaKSEOoj5L/ZsfklQVYALAusk7nkIY1+0SS8SL7WTlFaSnZ3xqjtqZpoHOE1iTMVQr2PSd/wUOaABwAGgh+76xKUPFHErCbaDkSAugACMlVkankuYnvOIwmtC2QAAIABJREFUVwW9Iec8CkGKMotxCS/AM0oAh4CGKFIEbUEdCF0QfYgDMw5dHkn+yHwaAqGosDIpxsF6BbAKoAbJOkZtpADSox3Q9uQ6CSN90QqpCQIX5Gq7WyPGeHdhoXz37t1v7587t5aTV2MIaHrEmoBEQFbYiXFJZRLl4zV9k6EgyQOCpgSfu7/9r07EpN/NJwe9V/n+Sy2l9lI7yfX1ubRarY6nqU0nic1JmATUKDpIeNzOPQLoSmiCeijwkwj/W4T4KGCwR0KfftpOzBqVycnBmKXpeQnfNLOvuHyJhlkAlRc7t4UCNBDRJnAo16Zgm5B2ABwCOoxCR4oDAv3i90efdJaZsGzyqsAJgJMApiQsQlgAMA2gAXK0MLwQBIBlucZJXCBZDsEmSSuR1pydjT1gbiDBgUGrx8raYBCalAfRJgmdADE+crzHx0kKwYrUjBGYCORsNS2fiEj3Ovup8JLrTR43R/ELobI0lqBt4x7jgoMLJKbc2SCPS4/tc7KyYAawSWKL4P0c8dNBu3v9r//6yuHqarHNnpxMS7VaqA+HnAmGC3J8XdA3QKtKqh1t9PzMVpJRkgPMQTTl2ge0BWCN8jWA6yK3A7idMTYHsddF0uu6sqddHNXyeFWdaj1JUHfXPMk5s7AIVwuGDIKDjMXXFTQbFWMgnlsAPs9omSzoQEgAppLOkpwHMOVAC/QH+/ulptmwNTGxOgSudL73PfTm5vDoa1/7N+MgTko8ZyaXVAZQPxo7jwRPWjrLACbcMQfnyTLp9bTS+VkfPu54qZ1kuZWXcnCaxjOSnyQ5PtpqftGm/dwg6AAcQEvCmstvgrgOC4/KZQxXV1cBwCRgeztd7PdLrzDhsjsvQloAUIGQgkcrckXCJYzGLGiHhi05tyVtEdgStCVxh0HbyPN9ulpi2tIw7zVKGAz67aF76amFnYNUMzNZnmUckCFLEjSlbAdMNiHckjQPYp7APIQ5AHMF6RllFZHlUXMTk0L0Q1MQl+FqpelwPM9Ld4D2bWC1W9waqN22nSzjx2YqyXGRRfQ7LsiIQh3jiG393ECyRmA+CXbBAod50P4XbdNR46V2kiF4CTGdErEEctEjxq1Ioh8neDGsiS1Aa4SuufnHluaPNu7fGM7Nfahr155oQS4smuEtCN8EcFrkAsEqgIAjVu2RKEg5gIzAY4gfCf4JyIdW5FC3kjDsxah+Wqr03Q+zLOtnw2HIZ2fjaKrh8Lkj/l0GXOoD6DSbWcssSYfDvBwjqtUqKlmWTFkhU7YE4IKA10nUBQTyiRDvkZ0tC0enMsBJiK/IUY7OBty9sz39eONwc7i+3osrK1cju//DLpl+7LSOBSYImJdwpqiYHy/6lYQawXlBFzzjvg98/Yu26ajxUjvJ4dBLgKZILAFaJK1xzCS+XNLADF1J26Lfi/QP825rbceS7pUrH+bl8rfSV14pV/PcqoCfBux1EF8lMS7HxNH2EEtFRZ2S1CXRBtASdBfEjUz+gaI9zEP/4ampP9959qknyvBbBswb0DAgBGDquYhqzoFtAVvD8fH5PnA1NhrPYmE9/qN6qxYeB+GxiLZEE1iX9IS50Cg0L4+iSPVk600AGgOwRMM4JSlgcxgHd2q1kL/2WqMLoLc/zJsT7OfddnJQma+elMKyGQ9cqKEoIh4bR0mqKmEW4MChex7CSzRN9LPx0jpJCWw2UTLTuGTzAGZGNIzjFElmILYkPCJxExEPSgEHCrFXPuhnly9D7c3ZiZhrKaGdhsKbAJYkTgKoHPXMcIJRUEYpM2BdjruA36Hhdsx1J0nDfeU8YJb3gSfOEQS+lTab4/U8/3otxryaJLFsViuTfLqAxVgdJMmFQYznBv0+O+6NzjvvfK9/+TJEQrdaO/mJxsKBGBhjhJmGcu0CuEDgvMALkipm9kQ1/KiuggmosFgxFkC8wkppr8qZMcZsHVhdX9q8k2Nppo+xGUZyg8CnLkwIOEHwBI5REafoZ+ckATfT1MhpFjPaXlLV8pfSSY5umpmlpRg5QWJB4iyI2lFvOz9nDCFsC/rUXR+RXO92dXDzZrO3slII5h5uhQkYLxjwVRnekHiqqKAiHH2EIoc4BNST+BDwHzD3/6wcW8Z8x5HtTk9jePXqdjb6AK9eXbGlpeny7Gwc96AZCzZBSxuUN9zt6fMoqeOOlgdrJfV8d9BMfWUFQxT5WSwvv58B3z7Y2+t1q1W0Bgq7dK7BbFsAUBR7CIlHTPcyK6L1RMA8wWXSMkKJl9I+0HiEt6/lwKrvXt2IY2+decwk3jILVTgFagLi1BHa9/mCKEOaAlA2w2Tg0970l3YGzkvpJC9fBldWwLfeGsY0rbQB7gKoEai6VBvJQJVG4qiGovDxK7LlkQA4gSihS/JxjLgF2KcSHi8soLOwcNWB1eTx48M0D5xLU56F4xKIJYIzo1EUR2gfRzR09iDfAbEN4NMo/4j58HqIg1ZTSff04pWe9J30zTcr5YOD/3ms1+vUvvIV1NM0GXdirgTOApqUY0zA2Eh5BgBgxjbJZgBahrBt45Pbb7317b39/dhtNvPu9nben5vbzKan32/fwGp/6TDtxBK3E6WJok0BmiOwAGKGo0hN+vHZ3p8LRmr2TAFNFjlSQkTfo289fLi9lmUrnbW17Xxl5ergsP9vdxD9rgtpKBTfTwKYVdEj/aukjO/AqBAnZCOu61COnpm6AHuSmhni8OpVcGXlaVfCS+coX0onOZp4p04H+4DfiBEws5MOTkOakTBbzGzB3IiOUf5VyQuxyO8NBQwI7EPaAOJdQPdiTPZu3drJl5e/XWpvxvGqlcctcMkjzoI8D2EKPPrWt1Fnj0vaB/mJqA/BeDNxrCGWWt0k7S+tf5hLYKvVH69WS1NAb3YwsJMhhJMqqtATgCYE1WksS1ax8MxBEBy4fACwJ/AwEAcqcU/GRzELG9Vqstnp1Pc3Nr61f2kZOSay/sFBXSHFI5iui4wx4iLJN0YzaJ6ImBxhJZklUNOkCGHPFB7UarV7MZZ3V1Zik0S72ew3gfLD6B5EO0VgF8AChIqeLdq/CnBIAwADQvsSd0hsk9qFsAfTnuQ3goYbKytPRzq8dA4SeEmdJFDkR+7eLR/OzeFGuWzrvV62aJacNMMpSRcELBddBHJ3Bv6KjAYdPWVDA9qS9h3YcPc7h4f9e2bbg+Xlqxn2/rChUJtk0IKE0zCdBXFOUJlgcrSPKkcdeXCAB4J/EmP8qwCsDSvYmpm60RzDtYgFCHiHMd4bA/KTgJ0n8aYZLrpw2oCqgBrJdFRMMzznwAS4GSMAF9AF0CW5x4gPafxwOGS5VAqYmGi0yStDCYO/+ztkb775R49KpRDNkm0yRkJTKFpRX8RuoWzktMRxUocg74UkPZWqos32MAfQHhvLmzs7nUGalgdQ/YJguyTao26W9FeHDSQHMZDUBrAlxdskb0laJ33dgIdp4gedTu9wfPzldI5PcOyc5LPk/+pzT9MVAUVC//nf/e53vztcXV3dm5rqNaemptsSWnmuQ4kdGFqQDiROk5oBMAWgDrBGolx8z5Fsz34WCk4ktAFijVEb7nHvT//0SqtQFgc65bRG+WKMeA3EhZFY7vioiHDEUA6g5Y4WyAcA7oU0v5vWtZEh75DXsmIMa7VWT9cbkVxOYMskXgX4KqBXjVyUVAZRkn5yBD/qLReAIYgBoGlQHoFgxork5Wq1xFZrdXt7G72VlStdoN9qtyuIUV0nlyCuE3gEoCGhUYg1HBmeztGRMAf4WY98E4hmgziQsA1cyWZnkR8c/PchwDcFPCBtVuAiCrL2C16sn5QxqeLesiOpa8QhoF0X9gCtk7YmYc1dG2Zxo9PZ2Wy17uQ/+MGt/DOO+FnvKDDKWx63As+vxBbz58GTYszY2NvJcPh6OhjkpWZT4fAwDXt78+H27RmeOLGB73//2Q24ehWYn7+EsbEHStMZz3NkErt5njcRsA3auoQ9EocCehBVRJRPBl89k4t6gWeaC3gA8BbJDy3gU3c++L3f+6+tkS3s97+2qKivEPomgddInkTh5F+ArewC3AC4Buqmy29WEn7aPWy15mrJ8N13P4z/y//6G7NVs9NBfJXAW5C+CvASyVMFfQQ1kAnAH4kef8p3Fn01xe8nFMdIjLmrBFhAlgTmZa80Xu1cuzbl9XpbaZrklI0TahAoF9RGVIAXI1dGcihAgCqC+mmS7pXLf/cIAC9fBk6ffivUp8oTFlgWmIyUdqZelH0/ZqujIH92ST0CeAfCTQk/lPQDEtcB3JZ8nRzuhNBvTk/XetPTJ+KlSx/6u+/+6OFWVlZCnr+ZdLulpN3uJd1uNz04+IY9eHCJ3//+JVy8+CG///0XfZa/PI5LJEkAXFmBLSyUklqtmvZ6lbTRqLp75jGOOwBcurTqz8/eKFasKxFAlK7FanWlC2xtP8KF+xVMJN0W0grDMoBX5XotBMsg1EFOEDpiQvJPPNMIcc+hOyb/SNJGr9frkdB778EuXIAtLw/HaeWzAL8m4RSAiRcoHDyQtCXHpwA+RWLr9zth/89n/6/Ou6NsQcVtItLORfgliZcIXCJ4DlBCMhQdMU+UaH8emxUgWqHGw6qkUwROAqxTLMmQMrHs0aOprW9+80+6EnIA3U7nf9yIkXdIG0NBMB8HMHskV+XHLRbGKJwFOCHpMCq7fe0awttvwy9fht+61c6clR243TayLIQpAee/oM22aIgAegAekbqhqI9i9FvDYXZrMOgenjs3lgE7ObDlwLUnRZ2/FxEWcemcbW5Wkk6nnyTJuEk9y/MsxtjNLlzYFQAfpWyOBX4lzJRWkrW1c8n4eFaKMa25s5amqJjFspuVzVRiRDqKHBLSEtKTYovgkjGaMFTgUELm4jC4DT1okPugb6n1+nmrf2os6wHf6+NZgpn7+3+0lFR4ymM4I8frAF8z8pyKl2kWQANCKJS7j/S25gAioDaEq6SuAvovpVLcrFSwBXw4PDx8vRGjN9K08jWJvyvxd0nMulAdRUlHZF9R0S5aD7UB8W8k/Y07P0xT3R0b21gDenETp8sVxBLa5a9D+Ka7fcOIs4DOodhOfp42NSHcBXCX0A0qXsula3ne35ubw5C8Muz1/qezee6vSFh2xz8B+BsgL44+f6SpFBIDSD1BfQh/CcT/p4/e/6uAdt5Aewnb2e7umQWvYj54eC04VwCsgDgLMSERjm6RLhgUKCrXQxI7AHZIPJLwMRwfS7gTQv6w2338cGHh/+4++eTa2krZrF6t1caqaWqVEMqVGFEhVXJXiURa/D9KgIWC+yoCcilkZsgkZSEgk5C5+8DdB3keB2ZZN0nSbquV9ZeWpvLLl/8kvvvuFz+V8QuPJCXw0aPXSmnar2ZZdTxJ4nySaD5JbEZKJs0wSaruVM0Sq1JMCiEDKx4gBkFwF4bKNQxkz4qcXtuGPEitsoNB3K2psbuzo93Z2e9kwJ9EPOV19Q+zXlC5HNoR1hLtsWD3Ab4J4E2JCaiSPRsadSRgMbN5QKIlYlfuG+7+aDgstSuVZra5ebFUqdg06SckOyNhnsbGSMIqeQGFRR+JVvQAbceY3yXj/V7PD8bGenFz83R5bCydcMdELp4B9CpNb0qYIlj/2Yf/xUCyBGLe5SnECAu7FcSHUEP7++2mhKzZRIvMHpKMZHIaRAtAlGQFhfJIg4QgoAIwgJgR7FRFtQsReFxvyTF2dZ/8wxa7ZbHMmkzbcDYJ9FT02x/tLobMJQzN0BJ0m6abLt0itJ7nvp4k2ALYXFjYfdIrSgCYmTlTx8BnEcIsjNMiZ2SYIdkgNUahRrJkASUJCYQnOxwBig5EAX05uhR7AA/MwkGpxH0p3cpzbqVp2NvZyXuXL6/03n336j86SeAd1mr3Sl2pXrFsGghnAbzijjNmWJRwQuIUiXGJ4yCMND6/yrKogA6NHDjQobADaIemDRruOXXfLEmjZ9n6+g8P/vqv4aurTxLIVw4lNIGVjXZ7alOq35bZPQmSOGeGCYkcTVU8MsgRaegTaMt9L8a48cEHf/ZoZQVOwg8O/qCekzMW7GyUnyU4j2L7eORtYWRR0ZYQaerJse2e393aenT/0qW5IXA1ZtXVcs8xERAWjDrjka+SvDjaVn/uzqigbnGBsDkScsejPCS3jd4rlSaGAFoPxpvthZ1Bhtp4M7gumaw9qsrzqOXiRopEI+UczpB2KkqvGOhZpiaJXel/b125gs4//affLlVqtk3gUGCPlEFHW8CREFlUr1sA7kD+N0L+QTmEvYmZ/X3ge73nttOUgKtXYV/9aq9O1RaMPCvHaXedoXEJ4gyLfPOExJKoEsDkOb6CzOgCZERbQotkE7DHkjbI8Ejmt0MiJEkyNEv81q3qEMUO6wvFC3WSEnjlCuzChbdtaenMVG1ybHKveW86LXG2FpM5wOYlLRJclDDn0iTAKVK1EQdNAg8JHQBogixDqAComKkEsARhDJQglERUQYwRXFTE2VTp46Tx5uPf+Z3Xd/b2uLu1pb0k6fRu3Wr3l5ffHzYaq91OJ3II2wDDTSNSOHcgnQFwBkCj4FMewdabaLtj06j7Erdi9O5v//ZT/hmSpFbyqDnCXyF5FsQUiv7hI0+ZFPqI6tDQhrAN6LBSSbrlcjUDEElot9uoB/eTEF+TcJrUBJ4WBo9K/VxEEbHVzbQI5+tM6LGfZ6iv7lwC4q3ZbJgctHsTNtWEfE/CDmg1jgSIj8CoEX7kvoxBPGVkS66OUm2MfkMA4vZ2PjCU9iQ8IHwc4CKJykia7XOERvl5RRIPIN2H4S7hH0SP9z0Z7g0GWada3ciAlbC9PV6NMVStOjGx18TMN34D0x6xSOMJkCcAzRo4C2oGo2KaxNKIeN4CfCCgT6APsixgEsKEoJRFn30KwATWih1HmJFwxoFNMN9eXDq53Rr8m91B1MFgf2//5MnvDfATcqFHiRfqJK9cgV28eDHMzs6kpVJtAcNwIQk87xFLlJYkzZOsC2oAqJFWllCRYCAEMFOherAm4B6FCUCTVlz8WUGzEuooXs46yQlIC5J1ARzCsEdgT253A/ipGW4B43vT06V9EoPr1zGcnd2V2QRZqnzkFtoG7JrZgOK4pHRU/bbPOxJhofKz4c47Ztgik+7z/9xsdivlcjpP4zLIcwCn8MLYCXIQHQC7NGxbosM4zAfLy+/nGLUJKuYNeXoK0EWCpwG8yBlCVcAW3fS6ZD2k3Ll2bcrefvtP8mWs5pjE4OBAbdJ2BW1DmHY97bh6AdCYiFOSCOmxFD9+/l/LZRvm8v0Q7L6KZ7rijll+/uufQ8gIDgE8cOJvo+uDQD4w53rsDJqTs9kQuBbX11fL1Wp1vFSK0wE64+Cr7limOAdgWsI0CjpVFc6qoFIxYVIOoA3XDsA9kgcuHQKYNODcSDmpJKACogKoTGBylLM+MxJJOYBjPct8HcZ7jLxjVh0Cq6Oo8kr87NM7GrxQJ7m6+q0EmC53Ol6NMT3lwEUKb1E8T+KcwCczQFjs8UZ/IAcu9En1AGwB/NSpD8x9nuA8iEUAgeAUiOLGPQVHa7r6ANuA2jRcj/KyhKGYh1qFQwkd4EpOYiit9vf3+71Ojo1q0mgCGDfqrICa/KmM//OCuL/k0/xMasOlNsQNd7/rrm2z0AOgJ9F3o2EVIMwCPCfptKD6iBLzIuCjkQu7AHbc0UrT0oB8LtKNqMP8BMTXBZ00ckxHWr98/tiqgliQBBB7VLz19tsdPmE36C9WMn690Ra4D2FHUIn2Qp14ncAJkjWSN2P0sffeQ7hxA3r3XXie93Kpup9D62acAjlLMnv++fg8njEJGYEeoA6kewD+LqTxP3VzdnoTO+1X+f7gnXdgKyuw5W+gajFOK6SnnPYGqW8Q+IaIaYH1n5JnbkNqAXwoah3wLQRuybUoWYnkHIEJCdXCSRqfWgeAogh0RNwleJfQeDTFer26d3Bg2eRkZzDK3b+wXOWRO0m9txrw9XayPeilzebUCal02gynAb4CYTm6zhsxO9o2f/YxhD6BHYrbIO5Qui3iFgw7JjwkfcFlAcA8gIXPOgZJk1AGCRKnApDJMA4PdwYD3Wm1/vB+nmP/8WPbB/63XmdqdeiH3a4lpW166RMJDYL7IM4BOAew9IzG8jmA7BDaMrN7ZNzt9dB/773VsL2N6re+VallCvPmmAYxRrIiV0q+GHaCRGdRpW2COjSyp2KcxFPicKuVVhyaADlPYfxot7I/bh9SFaNfoxzTEapfu9ZL3nkH+bvvwrEyJ9vXwIEWTfskJwS+uFwXmUiqgIyCptLEZv/Fv/jX87/+6+3e6mraHQ4reZrGQyTpQ4kzJM8D+ByjpaLXnsQO4fcArQG4Th8+6uS9TqmfDE6N9eL166ulc+eSqX4/mU4sOWHkeVHnAZ2HeA5Fw0LZisr7T4CGoDYIvy7HHUAHNBwASZvAWJEOwwkUbcGf+c6PZhtNklhSBBOy5AzTZvm9zn51PXZW1x/8p/Xe0qCc8bevHvl9PHIneeMiQtWySqM2XlGWnEXi33APXwcwL2rByJlnq8pnOx0CfQA7EO4h6m4MuBPD8HbMvJqGtGo550jNg3zjJ9khIIAqC0hYiBCMEzgPC/MGTFQqrOU51golbHQkDDFRi51Ouh2ljyM0JNmVs0TyFJ62kH0+jpJAx0yb7oP7ku8mSbe/urpone1hY9DWTKhyAdA0gHEVFcTworiRo1W7T+hQwqFkPbPMn+hC3rhxIywteZW0CVBzAhqjVMkLAckEQINEAmoqUVI7e3Y+XL68ysuXrxT7iBAGQd4UuO/CPKn8hY36kZLiRolyTLnb/DC3xYmJsd1zVWS3Wjv55MmJgyAExDALhCaA+Pnd25EeibAr8CaA/y9J7G6pVF6frOy3MdaLwNU4O/tHZak0VyrpAoRX3fUGDa9LXBjlG8dGu6ifluYZEtyQdF3KbuaBvTBkD0Dfk3SCjgkV4WMV1N/jrAoiyBTQFAsnOu7CDB3notvHkv4WaWyPnZrW+sM94AUUdo7OSY6ewBN77cpwODtV8tIUzJYp+zUY/wmoOmSj3ONnHmE0tkAusS1pO4j3AN0vRa03Jv5so5gOuJ/s7KT7oTR1ieIugHZBiWFSqKqMnJgYAIbRHyrA6AYJiYiEtJAkcMBbDx6stoFi4Hy9/u2DnW7/fhzETsJqKVg4CeK1YhOv0j9Mq5B6do5qg9xNU9+o1fpdoDwAhiGWQ8Occ4FYiIVEVR14EqW9mJdcgiAOQXTc0QbiEMi9MOBGmJ1NUrdYCWJjpGVZfmHGASg4haoBrEAYF73aL7VTAOHKqLfgn//zLIMlHQktEH0R8cWl/0fDyqRAYMKIOSRYDAj5YWXYWl5o9Pf2Dtt5bHgo1bYoHcLYR+EAnvS1/7LfHQENSQwBPJb0KbLsbzMle4NBtletvj8oeMrfLjcaNuHup4r57LqEQhzkDRQLMwDhR1MoT5dBjWzNSO4LegTpdqez9unm5jB/++1r+f7+H1lCn3FykrQq4BMgTmA0auPH2lMTgGMSxgBNEpgBcTqEUFWMnRDq226VYDPcf+cdDN5992hl2o7ESRYRxkpYA5IkmZlPkuS1AHstFy46cZbAmBxlUslPeZcioB7AHqgtgg9luCeFzRxxNHzoiq5de9tPnDgxrBi2LeBTAGMAZwjMqOjFNhQK1Z9tKzAF4YKE1AwIwbxer6e7u/29mZlv7wI/jMnwdJeeMkm4QeNdQB+h6HR5Qjj/Za9UDqEPYACx6R7bMfa7Bwf58JNPDvzSJZRKpca4GU6I4SSKzpqfds2OBAUDCFHEUPQhguWKJV3Fir25WUqz6kS5Qit4cRQJPpEleyH2Fd8FSDIQgUKpMhyrbG+3hqur3xkAJ+L+/t0IKDPjIAo5nF9AxweBYsTEPGhLmdjNhqVt4D+oOb0y9P0GJy225UkLYhNF8av8Dxtcpy6AHQk7NN12x0ME7iTBO5OT6VBaDe12Y2psTDNJoiV3fsUMX3HnMg1z+KnUt6LBgFTmwp4cexBuk9qwgM7S0jBfWrrmJNRqoT8Ud5ME92LuYxQmWUSS9ZHQyU+gstEglUkK0gmaXcplgbX0o1qj9Ml3vvPfdi9f3siAa/Go8pRHlPhftfX1uXRif67MGBYofiW6/zekvkHhLImGGcujgUifDSkn2CGwB3FT0sNhzO9JvjVIwpMJbXr77Wux1dofmPlmjP4pgBsQHkrqgBpVX/nTVpkpEudp/DUX3wJ4yd2WQyjPHRygAlzLJyfnO70e9kJIHlG6C/CmhAcSD/9Bl6lIpHcJHABqIqJ1+/aDzl/9VXWwsnI1JslUCCGMkzwh6CSgCXwho3ApGnKRwyS1QRI8lzqauzFnvXIt1TBU3FkuonfaF9LOWXhkk5Q4WUpTVQYDlIDh6BlLXVIeIzID8xeZ+H/eRrkaEhYkOw3YVJqGMgk/h6vD/ak7XVrSAkIT5EFRaOTwZzy/PwtdARskPnLnbUSt93r7O5ub2+0rVzoZMGX9PqfN7Lxkl0hccuEtGl4FMIefKrghAXJ3ZQB2aLyNRB+56VEIWRu4FjFiPzQa3nfkuzTcA3Rf8kcQtgAc8qePpDUaSwIbMDsh8K0Q8M9AvQ3oTKNRrWxuzpSuXXv7yJgeR/TC1dOpKUz0FafkOCfhVdDeBDAFsqqfXKRxQLmEHMJBEbbjkYhPCV8T9ajbzfYrFe8BT3lm+vTT8aG77ZjZLQkMQbk7AUd/pNI9DiB9lj98FkOw0F+sAWiQOiTZkxilPAPi3o0bq91Ll/bj6dNXep3Ov9vLMl9nCA1JVRLTKCLekVDDLxybZALahHYNOiRD95vfvJYB1wAAh4cx5NI4HYs0LAIcl5QcATXkZ0OQBXmEy1CIDV26BNw/rNGM5pFGgxXFpBdt4LPvM4ByGkmbmKhyfb3DpSVAyhWjqRjpCgEvLNBtrx5oAAAgAElEQVT9cUtrAmYJOynFuwW/90ne95ofHr7Vj/QWgH0zmyrSOWr8YsbqyfZTAFqEHgn6GMRaktjWqVPf67733mq4eBHh/v12fXy8uhChZaMuAnyFxBIKB/mTjv0EbQEtEPsAbhn5MRyfALaR56Xu8wvR+vowK00lh/3MlLgmzGyMQlnQEsBckgFISab4Ub/0bNEVJkGWXJiCoWnkI/f0fqm0sHf+/NwBcC3DEeBInGSr5XUpnLVoyzJ7C8RpFNvg8k/bLo5a81okmqLWKdyU6Sbd78WoR4G+Xaqrs79fen6sHpaXG/nOTtwjFST2Q7BDSZtmPC/gVQLLIMae0y38jO+GSZwF9GoIMgAdgFuzs5X+9na/+957q73h0Lvu+UYx3JkTBJcKOgITQQl+Ud5i0d97CGHToUML/iMrqpkHuDVAzUGaB9D4qdH3EUKEyZXQQiBhwBSu4ZrOxzdiadqGsY0MzqgXVa35CXBQoMeeK+/D4rmltgMFu8GMJiEp7vWLSwc8g0hjFdA0pUXSxvM8/5FITYp5YknLHduApkaCK7/gRaVI5e6KJA4JrHv0m6TfH2RoAsBv/mavPDY2VgOS6WHUucTwhoNvElrEUxWszzgyKYx6+SU9hnSb4G133HPGe2T6QPKtfl/95z+3tHQn39k51a1Ucs9i5R5iHLpsk2ZvyNikYQhwEsIkikFuf//qFXndMgmCWID4OkPaI/2WB7sFFOf2eeNInGSeq25mZ8z4dZFvGLDkwtgTIvZP+tyIVtICsGXg7Qj/QT7o/2dy+LjbHfTdO71z55BPTPx4P+cVPzj41t7kZNquVstbw2H1canEuzHaJo0BjhMFybyQNv3M7y5ELGYFNEDUSGy7kjWr+n60hi6spoOdWw96c3O2EWO5mSTjC+5+0cwGAMRiwNgv6MA4QFEx3qTsMCr+iJPs9RQqFdULeTHOsXh4wot3QyIcJiIo88RNZoxsYUxZth27zYm8pkYM1BfeZ1swSxHz6Fl9ppffuNHQpUsAkJCjEa7uCk/psy/aPP//2XuXWLvO9Dpwre/fe5/3fT/IyyuKklhVtlhVdoFG0s7EKjRiRI1CoXtwjbgdd7uNhoEAiZEMMi5p3rMexWkgRpD0oAh0A0YBlZk56MegLccohyq7xJIoirzk5X2f93783+rBPlciWSR1r8gSZSALOADBu88++/Hvb///9621PrXNsCRgCvh8o/Fo/50sa5RF4TUZm1oFuYwzFyUkOaKRBYBj0u/EmP9Nlo12iwJjAOh05hqpY650raXBXxXtV632KmjyKdSces/ASS4Swn2APzH5/0fnfQ+4PzeHfeC4mJ9/pD8wgPeqlZXXx8CHU+D1yWCQ3C9L/dSS9Fgup5hJcFItgE8MkgAMRENgKtd5gFPSGpCBzn0At892nU6HFxYkJfDmzbez+fluSnJZ8k0zuwzpIohl8mktEj4z/ZQjB2uyOOg/teA3G4wfz839H5/m/ra3v9fodP77xnCozB3RnfHggPHy5bQARmNgd+J+sawqH8xcrzdJuwTIIHQB9vDEKYRIsjlTBJSSXoH0RiZMTLx9FYdDXP5xDlwd3rmTTdvt3l6S2AMAO6Lm4JzHGd3NWZvJDmDYNXjfKivqK7IVAITpFM2iUFfiHKAeyKxe2n/ZjzcJKqXUgqFFV0aW3L22qs2tYTW/CzJRLjInMam9I5Q8+X7/UlD3JicqAlMY8rxSiTuIu1d2/dq19/nbv91N3Gs/SRpTvaw2CWTmri5qlUnXHW1pKwN2HbgeR6OqYsSI5L6EYxIT1TO3M/wES1ADAH1IO1HYLUvfW15u9Xu9T/mtcxXSzSheJnkR4DkQiwROmqc9ZefKIYwljkV+QvnPofizRDzsT3U0P/9vx7j5dob5bkuHf5AgeAAVBgPG6XSS376N/MMPr01u3KiD9b/4F3/4EY09FzJjfVwkFoAnml6fjP1A4xygDYGpgPsG+2h///fmxuOi3NxEQb44Vc6Lm0m+dzVZP7fa9UxzdDsv43lJGyJXALWfnac6qZJx4q67NP3EpRt5znssj/O//Etwc/Pt0G6H0GgsLbpjuSx9yV3TquKETMYPHuT9okB/c/N63ut9b9LvtyR1H9DsNqQPZiYYF2aa3Sc+IJJmDfbUIHkO4ptSdFLF4eHi/cVFTIH34uYm1O9/o6+65/OHFDdApc94Az4NpTuHAX7g4lAJCwi8hd10HqsNxLJHZB3UOdMG8eVotZ8AEsiM1pHUBZmZJba19b87sFXdWIU2jzmhNDTi2EFn3Z7hy5JNRgBTSFMQQzkni+sL0yUslf8b3vV3trZ4cKCMZMcMPQEtviTDaRImIAPRhLxTurp3+ujaXHe6ga1cA0Y2NIJ0CMOxwPyshRtJxSzIbht5J8APz50b5sCPPy2koEyWqsDLAH8NzouguqcbWxyJ2AH0gNLHpLZZhb1pMprs7aFcX38rDNZXu+7ZnHvVDbKmR7VIH6e9sPfq1Qv781fXitXVSfzud6/HP/7jfD+x9AOQFcAWwA0C5+ux83RT5pn71SKEjPANldpwD+cajU4fGB2j9sZ8IXhxQfLqt0J6VHSLKqwp8Q3SNkRsGLQ8W8o+Iwf0aaJ5AupuVPnX05i/X4Xx4MOfFDneegttvBKq42Gj5VpEsFeocJFEP23ZMSoeVaGB9ppNSEykH03m5pBPJr/3oKrSTyQs18J7dMBn+xpKoqQGxPOUA6LHiPtpWmYnhSIAvr+vgSV23ww/hxBm/MAzwaXSDAPQ9wkfpIkKAdjbm0tju9E2t64R7fqBYuOhwtNZf+q5IMEoNAh0DexKajIEe9jUuH/w+1MgjCDrk0pUj63noK6cHjN55BTgAMAwmMZd/HVB1mqMd4RAIjVDuzY8UfNLnOU+gpmaJEBqCda24N12ETrD4zlh/m/L2PpGhTIdB9Ohi30QD/ufngozGe8BiY+jeFe0w1u31ovXXntIRpqFRYFvuPRrpNYF60KfL4yQMKbhPoCfI+CWC9t/eeNP9956C760BEn/PEvjuCvTqoItl5XmGNgD7CgWgbFKx/lkqtXVrgBUS0vF/mAwngC9gxiTjRDwpoSKBKCnvx0INAmmJObltgHifCPYeh6NOFyc4KsYJPf2LE2SZInURUW+ioBVgG19bs+OujsgasfrPqhDlXbQ5PCofzgp3nrrejzEH80l+XS9smwdtIuQLjlwUcQIkUMLPEzID+KgYbv6QwGdAlgqq+qjCaADkncBrKA2GXjK0uXhijcTAD1RLse+HKukFu7e/d5oY2OjJP+kDMHHDu658DEUlgBdPKtKkGRJagTw0D0duU9LACyKTiPNki6AeQFt1n2jX8Iyu4YRBrDt0jLFFTN1ptPykbHjlowl3zXploBqVmDqfRnHJzEHdADpnhnuuWMArD6UH/3QzL7ZgnEBwArrZW76EniSJ7/IWtigpsQe0Jhrp7G6detbk7m5MmZWTSLQd6RDgwoQOouwy6USwKHEO5TfV6wGo9HE/1xvJZexmhaHi1kRqxUznSPtvKA51JZun/sjhCbuOqDhE0TtWVYNv/tdVNJW9uABsoODg4Wg7A0QX1PkeQa2AXQAHSbiAmNYWEk697maPwCwA6DY2Zn6uXMLBvAQwCGAYwhtUG08vQfSw1SzRYoXotsbjQCNsuIYwPPR8x7CCwuSWcZU4hKCXYLwKqjF03H6JCOnkg8oHMIxaJCj+wfI79xBfO016OBgMl+FcNnIb7rjIskLJDZoKAQUcvWNasm9sKNy2rfB4JNP7g83NlABnT6gnRCwJ+cYdT+PzzsmA9AiSBqWASwDYTnLFoZ7e9XwBz9ATJIwmcawR/fbkF8MZmd+cxEoY9QEsOMQNI6xXQJbzBZaGaAeHPMUW3jZPcEpA9ChsELzVQE9s+qRe2vGkapwH9QHpJnqAPlEHf2Lh3IBu4Q+jBF33b3/3nsfCgB+8APYzZvHtrLCNoElAGuzoPBSOxNKMhoataokzsfSJ5cuZce7uyOPWXcaYxwYMRJR1A6Yp983gWKmfLkTjPfRyAZXrtz27e1uFkKzmzbL7kzFsjyTujZwyk6NEnIDDlVpG4iH1ajKJdjhIVqhm/VU2oW6So7fYOArIjJCGcBDUOsmXGim9tOQZg5g5513rumtt96KSXJYzi0ujuh2BMPBrPjUONV5Ez2XNmnouzT0itunv1qfjxcWJENgWlVYBvgaqFcBLIFKPv8NSAHKAfYBHcLYj4jjr33tx59VetNsLrjeEPBfkbpI4zqE9VnJRwAG7swBPiiR7IbKff5KnEy2JyXbaT8l7ptlu4oYzRKPn3c6BqAtsAVgRe4rJi03kB2yUvXOO1vjW7cwbberfQ9CM033BE3OOpN0qBJtXBXxWIpjqayuY5ffsflGWcUeFOYFvbT82QkkBAIdmAzCapT3QkgT1E+VAKAsNQ7B7zvsA0pzNFx4kf4fzz5ATgnfddeHpO4A8fjq1dcdeI/vvAPcubNqMrQpLIFYA9Cc8fFeIkgADVA9JMlcajza26tCnqMiJ1NrNvoeNTTZFyCTs3DpqIpxe+R8YEMO58/9lrc27qXFcdlNmCwTvgxoGeBS/Z3T3azaR0EH5vFurKrDwuMU2GJVdVpJjAvm3AD8V83s74N6A59F3iPANghdlIOVh10AN959F/7uu9f9k0+2ctKHEg4J7qP2pTydU1PNnLlAqgS5HWP5QpupPXeFTwIlmFnMYDYHw6qZrZDsnHIGJJ+RyEmUBkTpUZYLKwVJDTg6IFuoHWaS2SclkVmda1oJztUsS7vNvd5zvAB4UlUzSQ0Y52V+vgrFWmxV3ffe+9CyLCuAdGgJ9wHvE5yQKAGdXh4lRCrmjUY1TFNMl5aOq7cAlKVncrYB71JsfHkFkKeBBJBKaArokbbsbhs7O7+7trv7/Z4ES9M4nk6rB4r+c1C33LEN6AGgPmoT1heNStII0D6oexJuS7ppFu8A6APXdPfu91o7O7+/0mxefEWONYBzqPOkX5qD0jNASBmFdjDrWGWNEBLb3ERsNFiE6OOE9Zg6ncmsRCKSKEHlJIeWhIOsVR0n5zgF3lW1W7Sa4FLwuGnAEutJwIw7fMq5KukAo4QyTazqdFonippg0RpmoUmyodoz8oQYnkhsybEAcM2ARSm2f/hDhId9WWv+MeruO2fx2SNaJBZoXJe0YFZ70L4oz9fnDpLXrsFu3HgzGQ7zZr2M4aqEh81vPx+Ck6xAVVHyX6QC0gBLATQpZo/nKWYXpA3YEpOwmjt7aTpNNjY20GpmJJPgbp/egzOBSA2YJ3U+TZPVENC5evV13ruHUsqHU5QHcAwEn8q9IhBxSkY1gSizPEkw6nanORAj8HU2GRNzbyVkW1CjJm+/TIiztqcNkF0AK5JtZlnrHNDuvffe1XDcm4w7nex+GcqbAm6Z4Q6IByD6qE1eXzSikUMKe3BsG/BxCLyZJPHu0lLjGIB6vV67k9pqK01fDeQagDmIDYjpS5JOPgQRQgpXW1XsuMeG2dCAXS/LoyLPq7E7pgTK0wwngoLkkEdKuVfVqBjlxxrlgxUMchJKUzRJLZthE8TSF9OESyKiZ6GcpozHmgjYZZ5XiVnISDZYW8M9cn3NkJipQ2CJ5HyaWmtraysAW58GsxiNpJk4C9qnDpNsilwUsQ7Dgnto3bjxZvLwvp8Hz73c3tq6atvb55MkCQ2T9QCugFhEPQs71UAkIEk1QRXSkwpT7m4hzPRwtaxspqRALUgQ2y6swLGeMNmtKrRv3x6ivWiNRpplsUQKnrgAnR5GJILmKJwD+CCE5C7Qsd/4jT85cWkZHx39DwMoTEgWkjLQnnHeD414ojJVeZ7fHx8cjIqbNxtxdfXQLlzopCZrxaiOERlBe7k6FhJAotpZqQtgJU1xQfLjRqM9vXp1bZ+8NsHM0u7g4J9cYJp8AuBVyZz0TGIL9UvqOWSLtdKjHi4oSNREfPgduW4PJ/1b/+bf/J+HJ64wh4fsJKY1R3IJwDrBOeHL87l8NkhRKcGWOztmnpklBlz3fv+tottNZZZORJYE/SE+8ZMpMZhV+cUSQE5yVFXh+Pz5a8OTbUJAk9SihAuSlgQ7c5AUIDN6lDtg6imdeVUGqypPzJiwTuY7askuZ18MmDlYSVoEvHd0VLbL8qjK89+MnQ6yJGGq6Gn9zMFqicZpLiUaIFLVlKF5mbcWF19PbtwArlx5foeg5wqSEmx39/XG3FzVljQHaMaNO1OjJdZEc/RIzpuhJT2e74rDRsNuueMvYXwV1AUQFwgltbaVmrV8eNUho6uZJGGu17PcXGteYRXS10mcO10x6ZFzTAC2zTgvYS5GNYHRybkJAMxCKXAsaIi6ubzh2dd21oQM0WnVZNQsNzcPq83N/9eBLTs+tsTdG0ZrQkj1UgjkT4akJslz7nqTZEWWk6Ojxo7qXtcCoMEg2fWo9xlMhC67eBm1m3QHtaP1Fw1UdWsAYkhxV9JNo9+E8LeQPsmyJL9yBfzzP3/Ler0BycZyBF8n+W0Cr6g2fP1KYEZxSSQ0SDVIS0YjWK8HXbqECuhjNFouK2dkXWx01AP9aWfg9YuDI0lDknmz6Y+kfarKM0tCF+ASiA6+gM0fgUwRPcpWUPk0dx1fu7aqt99OhlWlXQltGG+Rfs7ISmKLVLOmhJ30h8IqYN9isjRqZgtFo6PSI4KkXwf4GoAVEl0Ayamim0DMHKAkNC2wmy1k8xstjN/D1fGsT/gXxnPOJLfYLFqNKPbY5BzAluogZKdNBAOgC00j59yxAKhTVUx/+EPY1tanTX8GJG+ZMUgaOFWwznc0YWwRSOHsgrpowALInshlS1ACXKN8jeS6hHPgmaWDAVTLhQUQPScbwOIj51ZJpRnHEAa1oagy4Mn9U+rOgzrxkYwmVhsbtdUTAN28OeTaWjeEgIxgQ4YEp5yRfymo39rnatIr8xiTnaqynwFvT65fn8Tvfvd61e/7blXZjaBqDwgDBjrJoFp/nuKLB8koaUDgAUwfSfhJRfwVKv84qti7fv1GAWxhc3MYLl/uhtEISzHyNUrfFrGGWm31lcBMuBAgZvUkQUm3W5KEfvCD637lCsp/+A8vVSQjDI4TweVTQMIl5u4Y0ziKQuHefCQ4mDGlrCNqkUAHRHpWqb3EjFAPsOUkwZF7M9va+re+vf29kZR6q9U2Q3YO0gpJB7UAYEFAh1QLQgvAKshvQZjzynKCOdzhwGUArxFYmV2XU8anmoMtRyDVkNhDbM9lWfTlW9/Kn9f44jmD5C5DYzOzYB0p6UWohdoj8iwzH9KQSuiQnAOslyTofve732/fvFkW0o+LvT0bxTTerfKYB4bKECBXAqpNqA2gbcaWu9okF0nF2r0b9Ig1gasAuoAaPGNfmFlltwVyzl090RvAhI9uY1V05QYbAWoK8GfR5meFHYcwW5K8V50k5z8QwAGCgxnoDYnpy/GreRqYSVgh2CbRJ/HzELqrw2GofvVXV8YAql7v3x3dvPn2MEka93uL80niasCYgpzOzrkEEGZLMJtRjGZL8U8xc+uprxHJCGJs1B0JnwD6AI4bRPGThcXD+8Ak/s7vvF999NHfay4vtzqHh+qQuGCmSzBeBtAi0XrJ/hufggbAldCQEWoASsgGAeDdd+vC38EBIgyRkgsny8YnDwXV2sV6RSNMjCja7fhIkIxkGuhtiAsudGYu42c7bqIBYYHkeckOkiQ2AeBP/uRH0ytXkP+Df/Bfo9M5/7FZMudQIecKjMuE5uXozWaI7hFrJOcIVQAijCS4BmgNqIUZp79VJOoVqZFsuGI3TdgbFMpbrTj83K9/Dp4rSL733oCvvZYmSVADHpuCpQDtbBknsaa4MAXUlbTursshLBQLC8XejRtbe1eudIoBjgdAJhPMK4wFbqPuzpaRaLrUA9Gj0BWsBaANR89qK7TmTBsadMaWB6TqfJzUlNigW7K7O3pkBwGMLpWkZn2Cn8XFlAC6pApkxGOmEJcBDOA00CCG2jjjpUgRnwLZ7F613LEG4BtmNqiq1k0yv/2v/zVuX78O9XoPHDhf9Hq+nTQtcdchhA3JNlxaIzVHYI61dV4D9ez7s17qVD4r+EwB9AnvQzwUuU1gm+Adpz42S4bAAwd6kLbC3t50CWX2apqEV2PEN0lsSGpLyF6Wg9IToTo3a1KQEBhoGFeP3WeTGSLEikD8nBSWCFSACkiF6HH42OYpaRIzB1uzAHnmFYqkrhEb7l4C3i/LeO/WrbcaW1sP/MqV9+POTpiGgHskzcAd0bsiuxLbgrdn7JSOGTqCdyTOA5onOE9qbqaM+0KQRAEJnQ2LaLYtSebWpy+3cHP16lVMp0UoS2sgsAEh4Rfqu8IgwEh2CK4D/oZ7mMTY1OJidgT8r9Odm28Pe704jXF51Gw277nzp2RppJkZU8AXA5IFiecZ8HVB3xDRA9CRq0UyO5NLwAyzKmhKY8OkDFRYXX18G3kgSkq5iEqCnlabqJtAej2DdDnwizWZCjTSAoSEtaQOX5kZUH0CGeoeO6ugvi63YMZG0mrnv/3bb929det6dfVqbbh6cPB7dyeTyTGZ3g6hse7Eupmdo/y8keflvoQ6n9zFQ1V8iUPUdnV9Ufcg3BP9Hl07rrDjroMkGY56vRtD4P14/fpb1ut9aK+//uZSdPuGOa/CeNkdF0C0QdpLM7V4IoiZaCHMFF42YfnooEmi3E1GRPeT1NNThrAkkNGgglBBWZVo8tioURCZUWoBzPCFqGXsCtigoQWGu6nxZ/Pzq40kWS2uX19zoMi//W3dazTCURnGTTJNqgKpmVKjMqNnHrnhFV81w0XUdKx1CWsSMnyuQu8ZR2YAhMSCZWbelJAeHGTPfc+fK0jeuHHIzc3FIHlCIiU81KX7s+yFn1qM1TQeP8egryWm0gxVnheDg4PfO0iSu8X6+vUx6/7Pj0D6gfX7dxZS+UIp3xMsQOpJbJuxAWIeM2+ss/odzs4mQMpEJhRsb6/32Bm6ILhotYHAM/z/TqymJNTVfHt828tIOWasFRkmB1+O9+GTceLJWRe0ME/YZt1gjbnF2O921/euXNnq7+3lo5WVPxsvLf2HIYAB8NaDB6PLB21hB8B9d+xCvk9iCVKPhq78s4dW0tDMBhL6Jt11+l0F3muYDg4PHxxeuPCj8exYuI3vNX/jN1Y7o1h1qfR1Gb7h0rconINheRYQvlKo36FkdA8h0GJ0az9GgU5gEuECvC7ePH3wCvWomqWa3OGywaPbxEirdfXMUPuf2lkNnEk0JS2zLvxcjMKlEvP3uis6/k4v7c/P/9UIWB0B/2HwML+zvldXw507WTI/f3Ff1hgDKICkIWEJwDoEw7Nbunw+RJMrjVPLoiNh1nr5FKAXCUkZYWtyl2AJAGs0iKrC3V7v4u7Nm2/v/fCHP64eKujM8K7m5v5oOtge99VtWwjISueI8F1I32JNIGa9TPzib6ovEydJOsdz8hd+ucgkzM/e4V8DrEpDu0Xp41LNj/f2vn9nOFwqL10alcCbbpNPxlwxxNxLTTUS9KDORavhjmZ4dPqdQz6FY6oER0YelbR+nmN8eNiq6ofu7XR3t5u207BSoXq1AXuVxDfqD88BmNdTCmj/BV8MNWeXKSCSeMWI7zRDlXmpj5MkuTUcfuP+dJpPVlbemgCPtHvViYPWcLh5SMaPgWQUo6KoSFgu4jzB8/iKPaNfqSBJIoO0VtNt1DmZk6YpGoBrfn5y/PrrVx147xHuU+1udn7a20AJTCZ743RM+N0AHBBsSXiFVMcdVjsrf0WmZX/3kZKYk9SuE2xoQVoj8FfNJKmAzsHKSjkB4OS7hbQ1BpCjgT4a2YPBIKSkAhlsOh2FRvuzXlCSuzsjVHmMjWphIZY97FRoT+LCwvUIbNnuLtIY0TLL1ixJfpXQVQGvkbjgwgb5RZeU/wVPw8zRywBm7rpIWipoxaS/itFjozE/qb2zy1l+vsbDDlrS4hEwGR8fl/fc0mgIlYiSjgioB3DxZZ3fk/BcQfLKlUVNp0UsS6sAllGMPKNB6KMgQSSol6JdAGsAL9WdOK2Vpq/OX74cxqPRd4p+vyqyLFRSrCQvj48/GO/uHo7//b//8eSfvPN2NY9uP4w6TXe/beRtyBJSy6jdTk59RHWFVZHGgh4rgL6yMnxscmcEZYRCTYJ9uu81idnpzbhd8XGq1E1I64LXRm1nt+7/MsFQPzRsCFqGaAC6LpaxRGXWDP0+jkge7e7+48Hdu3meHSX5KlDgSlH0etceWxE8GbUJ8aIB3QRYbwH/c2M6jZ0s88UKWCD4OuTfhNmvQDoPcIFkB1+pHOSjmJlRiYHR4R6CfDx+dJsKTsrMCHPJnpXIqmmXMo9KAAXI7HEPphDkDqsoFABnTfK+OEg0XJqHoyB5iQj5dOptIBz1++tHg8H/OAbcpWaMsSySJI670+MJbv2sxC3kC9+9Prp/9PvbCaxBA42Yg+wCgXKWrz29XPJTyEmUlnlhQVVRjJ77+XnO6vZ7ePPN71RSlSNwSmep52vVGQGMSQwkjEg2AJ0n0SVxibSRoHHl1VjCeDqNI3eMQuBxkjTvrK8v3H3nHRwAkwh0dVxpwMS2EfXBiYkniYWztFlg3W2xhCsHLDdjtbv72DakCUpBNgQkeEaip+bHmYkKIA18Ap+0MomKACvwc7s9fiVAIFOtjU5I/YoZOhJflXSPTLezVno/TdP9Rhf7g+GwP94ZTdfXt6YzP8pn4s4dZL3esBmzrGNuy1Rcdrc1GjfMdd7ICzBcgLABnuizvzp53KeDDihKrEC6Wo/f50CzOiduBnsWy4GsQy6IjECGoEA2H9uekfLCYRNCHYBnd++ux2MlIQKckhqjtnNbA9AF7RukDwzsSxhLSQHEwizsVxXvDRqte1M1+riCIYBhi9PjHOknKUOEh01AR6i7J/yqgLsAACAASURBVJ7ovk/9rKruBF9F9wJBU7nKpaXiuVuKPGd1u6e9vWkMwXKT5QArUv5FByeJKGjsjiPWtvUNAOfM+EpNuLUGgXGUDwT0EbBP4kDCfXe38bjq/8f/iMOtresOIE6n/92g0ejck+wDAC0LXID46lmOSaBYm29M3b2oKsTV1eYjgzlCodZ4nyTEZU9/6ZP135FACnhcQ3wTwLocEZFUJafDnmd2/uVAYAYiYd3rvAvgFUAjkj936edwfBij3S7kwcuGWkqE9z4sADzzQZXAA2RpnKBDD0tyvyjxVUKvQXzDDK8TXJbQAtnkrCDxshuSfS4IyetCC+BRorcfF5hUTg8WrFaePNO4WjXvIAhIUdN7wmj0KKWolDyQBYWJhPLURiyPHra7WJEoCE0AjAXmBNYALMnZAm3kwBjgCMBI4ojU7UD8lLGpJiN7DSsBDOfmdvtAPtnbOz9M0+6vkHYEKJ89FmdKlZAU4VWUcvdyOpmgmkyOX+5MElhV3rAidY6aCQYeMeGn0/hfbN/6ZEgASgmliCNIH4L4UFBfYgIwIX3NxIuA1gH1ag2uluRcNOFY4qKEUZY1D3/rt74/PjgoJ0tLk3GjMV+QVZ/kDsA9gCOfrXVPC9YP8YRQPzEMKOV1Z4KHtqEnBjYB7wpsQAhPi2kzOk/NJSWsJlRfTaQTxQ2wJkRRBRhyGcozl+RfDuqqd73wCxCbErq1MxKDhE4abEWRG9ZL9hgwOG59c3hw8Gt5klRRQnxYFkGYMSocHVlCoYeAHoSFEHBO4HkJGwQuEDwHoEciSJ58xr36ir9UHHV30HqpmguqpLy2JphV7YdDhOgIII14piSxVoILGYm2xDbArNvNH+XzSiURxqKOrKbHlWdX3GBA4IHAB6B2CD0wqi/xosCLhE6oPCskliRMAUwkNUFRVIYsudlXFQHsk9fjD34A/2f/7PtDdxuEoGOJfVC9WaH1VJ60M8aIg8yZ2LBEMuj14mR3d+O5e908Z5C8pmy6lbda1aDwTj8wnXBGppZ4SmkiXdAUxIjSPUA3IP0Fifs0hRg9IcLXVffBOVc3w2LHgJaEDgxLBi24eISQ7FucGwPVLtAtq8oigFHS5L5HHFlt8X/WYTELkjiSMIAsBw4fDZLOlIEtAV2KzWdJH/WZRb4BDKQnOzvL2d7em+X7778ft7a6Oj5mjFGFJcrpmC25/y6BRM3/wyxXmQJacvASAoYAh06MyTCuZ+ghJ5WHh+4NhQyJZRQaM0eptoiOhN5MudE7KRrVL9KveFR8DCQFMQJeSJaTqoZDkwS+997VcPVqL8SIFDZTJdWKkqeSgCQapJlLk7ru3phMwiOrFHeVllRDwA4ELM3MMM565IcQ/pbC+yTuS9wB1QdwmdC+g6+ROC9pA7AuqLaAaubilRJcrPXbyRHqdZPefRf6p/906kliEwl9CUecyYFxKnZCbXpihuhCDmqA6bhfhDDd3//Zyw2StV70w3x7+7y3WuwzcAIwgrWBwylNLkRi6lIfwH0A7weL/9fOzv6tZrNraXpszeaFI1LnAX5Hjg6oDEBaT8YoSWsE9wHtZFnjMMakPDgoj6fTQdluz49EHAB+DHF61iUGDZWgsQvHFtgPAVOg88hQdSKl0CbZFfULVm5P2u3s2gSRSaPRTq9cueJXrqz5jRvA2loVkyTJFZXTWOmJicuvMsSZB6YBWELdhe/ExUZS3dVQZE5gLGgMcayHCwlEi66OasOQZm0EgYwAaCdOQppJGcW/E3Pth6Ca2FgRlrt7DljV6ZQOgMvLvbC3N5dmmSeqZ+EP9Yt/6kiwWTWfZmhLzKbTR92oksSKOtevA8GGquWhZz3wQwAf0PH/KOpeifJejA/6rdbGvjuGACqQTaNtCjN+cv3NHqgFghckjAC7+fBuy3LeWy1MFdkndUiqpdov4VSYsVac8hxRw6Iojg8PWyeihufCc1OArl17z998880qTX89J8MghLArYUUzTTVOk1eotYIz+RVLF4uvfe3H+cmyo9///RE8PRa0DzJAmAPrBuozcnaos4eIVYwxyxiLAtjcBA4OIgmZ2ayg7HVHxNPChcpq1/T7gHZjjCNg6n/xF1fTzc3lLM/TzOQ9yVogMtazyGdMVx/6cSrxCk33uc7t2xUvXvyWX7mS++HhpCR9ArMRwRxE/CqTJX8Rn57jQxf6odO2mkZCKSWZgmjC0fkskAIAstk9bkhIZ07iyaPB8O/Wq+NRSBRKSROSI/dYkJUDb9nc3IWsqrzlbi0zS+vK9rMH7eyvVjtjqUmi027H+d3d7/ePjsria1/7cR4jpkyxD9kdCOcEnFmzRzJKKmWYRnneSK3o9S4V+/uToYx7wcIDAANJ1WOze8oFNzohj6ieuP+TsF4/1qc+rKmEMal9AEfunBweflhduXIlAs//5LwAP0k48L4mk78/LQr03bVHYn+2Mmjgc4JkvSKDQ4iAx1mN6rO/ATo8DDmpPsDdWcU7E/Cptbtq650ooMzMc009Lq0Uvr29SLajpRVDGmiK8eyUEKF04pi07VLlA6ZhCOz6+fPnM7LXnZ/3Lmk9wJogEp1QNU5zaxwhSZhJ1l5ebldAngM/i0myWUo+cddYtAKwv2PL7c9BrVtOAJnqTpMNko9WGaQAIrBeSn/FJIUvAhSgEtCY5Mgs5O5dB1YtTT0LIWmTaApKT/NSn6mygmoFW4OGbmrJYlE0jpeWegMJxWiUTKqqPHDpjhlfpzA963tGAqQTd/LU+/0Cvd7PFMLG2L1xQGHXDAPXL0RBJ1lCykEWdXX8MUSaUwGfVrVPmUSRpiQO6dgRcGQWJ1euvF8B759YEj4XnnvgsV5au3soENkn8EDCLsAh+OzK5SNQbQfzi/8LxRhzgMdy7LjjwMURoOLkQyqXkLtjWrjnnqblzk5TIUzY5iRkWZXKy9TstOYb9VBAfWNzuY5dvB+R7k4rjoBVtdsrWaORdcnGMmC1l2btbXmyPPr8a2cM7mi6h25ZqnlwMEoAwN1Ld5uQNhSRQ/oKBcmTa3Ni9/bpJ57hMyP0MwBokGyjful99iE7AJvCzIC1/s5ZfuOkx7Q/dsxfFYhkQWIco4+SxPMYK79zByHPW1kI1pasJSE9XdqKxMzHlESDYhewxUajOZdl1rx2bcuKwqZTpAcVw50o7IsY45FrdAoQdR+AJCrLKvV6qa5dW1Weh4lUHSrEXYeOQU0AFKiX9CXAHMBEwjA6pqHu6PgpNjeBiGgEwqztrp2W0iFgAuFA0D26DkO0Cfm4Ku+L44UpbmJUCXGfwEcudUm0IH5utzxJhrrYMefAohR67tb6z/95K7tyBZG8Fttgv6j0kRkaAnZB3gfwQEBFqpQwMOInIfhHDTQelOaDwWCvWllZbxUKc2mVrANakdQ5JTnVUTc8mgrYo2nPEfdHedXvoD9953/5M/2rf/UHzWjJsqJflPsKa+ehM0FSCrKNwPkITKcKQ2BVVZXkSVIMyOwYsgnJ6qvzdFMkogQnUAqqavJvHZRq8v1L4HV+mrHTTFt+4lbEk6W6zfixX4k1ep3PV+6OQZr68WhUTdfXu3F3FyHtqlmUYc7qVhkZzq7dTx1aTGgXgMYwxphvbe0eACgGg2QQY0Mk90HsQdiX0LS6c+Mp5IBqAlo0YgPBikLqb21dOwS+PxmP547KMt4D7G8E9gRsA8hIZpD6ErZJbRv1fozaBU4q+W/Z7dtpc2GBXUCLVitu2qDCaWq/RvYl3JX0AU07Een4c790BrywIFkUKlst7FUVPjKzrqA14CmJh0dACmrWSwotQppzr9pJkjdqP0n4wUEchMCPwGoYrPEgRuwC2IcwdWJiZsce9TP34lbkeHfUR/Gf/lO3+kf/KEsQ4xwR1wGu1PSI08zy6AAmgB/DsS9xPwbtp8XR8crGRvnuu/B/+S9jy4kVEheBsFx3NTxzhiepE9Q+L/fBQpIlwL9Tlv1uDqQDyY8lTsgvQPr95UGQIoRSQA5oDGIisURN/4qzWcmXGyi9rhAIDKpNHBICLcLbcrZJJKzlS1+RZbsEIA+BfTIeh2CTW7d+5nOXLiRhiCYs9rxix2jZp/Po0+651j4vVO6bNBxJ5eENrNru9d3y8uXVUbttRQjZvlz7dbDkvDsCeSrNdNOMi3JdiDH2U9lOXaQ9Nz1qb8ds3GXi+BuKkeTHUepK3oXhCK7bIm5XrnvtzB7Uu3vL7mA1bS1njapi14hFgkuAWtDpuggIGIi6C/EDd9yvqurM7Z2fhRcWJIdDL0MnO7S0+tij5iG8AWlMftoQ7CkSI5FERipInIdhwVJbWl3tzff7oyGwVS0tFaM7dz4sO53OXlWt98l0CNgxyRGDj2KMA7i2h4Hbry5cO5bArS3YwcE/blnaWlTEBRBrILu1P+OTzuCR/y0B9AXuMHCbzt2WxaO1Cz/69A0VgrXptgLhVQArs/azZ4KEFIY2iIWQ8iDXJO0A2imPigWfH1ojOSZt7PCKsDNwT58H0gmlAp/NDiNOjG+hUuAUQE5iBOcI0JBS4VClWRuHYKfpb/4CjxqiC6zJ5ExQ99XuAuiS6Eps0JTVrUoxk1MqzAptJ5X4GX5Z11eaVWEFsBJ9wiQOAib9cZpPL10axGMoRPMWaHNmmM0kz3Y8BDNBiyQvyLmnkN29gsT43WsneurJ4eAP9+G8D2obkpNsAnpoDD/tN9mUa1nAK6TtJkGd+lr+SbxAlNI/j0dH449oGEO6A/i8yDkQxwnxcZLY7cV2OQR2Zy2jv54tDMsOsrAo+II7FuSaMzu5R0/FSYrHAR2SftdD/DBk4QHGo69mkNzf/+u4tPTrQ3c3md0zcRvE3VlQ6s4G7FMp1hJMUBvSJmDfRpJab6X38TYOi//72o/yN998MwIoms14FEL6CamRO4oQmSMUU0/jUXI0nFXEv9fs91vNEBprFF6R4TKAVyAs6PMKSTWlqCBxH+QNyd9HwP2yTItZbogArN9nT9Q5gm9IWEct8zrTNaMhlaOHwGUU2g3KMrSAy0uT4uioMVbVGoaQjiROAOWofQd/2UtGB+QgKoJHko7NeCSpr5qmNQB9RMMI4kRETmIKWmWfBtQTU/EvETaLckRwVyBU9zshGxKadaoFbdQO9XMg5ynMQ1gAsFArur6EApEQBUUIU0CTcsLR8TiME2OO+dc9DBuJErXduShijn7iYHWmH8mMWCLwqsv3A/FzYCeTUAKzXB1xAPpNgm2AbwLokpwHHuHyPmnfXRDnKVDSQVXp3mDwu/d6vWoqfZgDfx1H4eKw65lNPU5aDey5eys6JxL3i8LHBwdFubPzwAFwe3uy0mplr7DS6yReV30vQs2zfsZRCFNCQwBDSduA3atK7JSTpF8UeKHdOV9YkLx69b0KeH24s9PMGw0syMI2hG2RTRCknhVERIBGsElqw4BvklKRe+lH5Q6A/P33348A4m/+5uZht4txklQ7UuVS5UvdrLpzJ5abm60CeMsGg6WWpDmn1ky6CPJrJDdnOcmnXnzWuTSRzCXcl+OnzvBTl99fWTwsAPDEE6/X01yt9tAbBOZmfL4zgUJKsIuIJTPrSp7VS5fr5cLCm358fGUAYERqAjCfmSL8UpuCkfSZpX4OaB/EHRJ3XH5PwLZBu1HsJwjH7soTlRGOKFSCgtgwSS+hueMJCxNOY8ICYhVj0mAaqiomTH0+QHNgWKTbBqELEi+Q2KQhQ92oCr/0fkJEpJiDmkg2QloMNzdvDK9jzTfwIyf/IHiBjtVdDedRm4ecKSdJMpO0LCgFsCNp8f79buPcua1pvcW16KYDut90BZHeJXgR+Hxus8AOofOgzQHaFvBRnqdL02nVX119PQLXppOdt4fZfDdvpJ1DRg8JFUZkzPJJvrr6Yb6w8J5vbkI/+AGYplwm/etm/LaA12qH8pN+3E8/bxJTAIcEHwDaBrRNHtwfjZbKS5e+AP/zGXhhQbKuJF0rABT74/9pP0S/68LNWqPMIHF+lvN4iBg7++bsHwAaAtdIxOiskiTtd7ure//NW1tZOSqnC5fyCbBbAtfyx0jhlLbS3V202u3znarCujnXQrDLMF4keV7Q0qwZ1VMuPKWaEjGF9EDCnQh9KIsfx7GO0Fusbt58O11dtXa73eiQWAW0Bti6Zm0kzhq8VCflewBWY9Scu2ezKxKB9+ODB39vkmUYkeyLHKJW6CZnMeg4JSpQJcQKwNCFEaQ+DLcI3ooeb9PsTnTdsSw+SEv2e72sT/7JCx2Mv0Two8P/dn4+SeeypLFYTLVrTPaDdCRhBCEHsAKgQ6LtrkbtFq7kRS+93VWaYSTpWMSwYcmYfL8A3gcAjMdJUlXemRnbzgtonfUYJKUQuiQzEGukVtPUVgaDkQYDjAGMLdcgp2+nFkUPr5jZfda9oJokm3pKJ8W6Hw8SUD06XiHweha4j9B5MD0qGhNtHTWbKK5fx+R3fudP42fHBKK3NXv2t1r3h2j90R+HZmr2moRvSHgTwAaonj4VY/zCac+q8HRJfQjbgH8Ex20Zd1dX/2zw+BdeBH4pfpKTKo57wu0ApqKVABOwHoSzYPLEBDGpROIcANGsgqsCknaZJh/Hnm/v7+NuCDY6OvqDKfCn05PvSVu2u9tZarXiCpCcSwyXRLwK2uuSXgfYERCeaTVV8yz3AN0D9XMQP09TuzeJjSNbt/E17Ppvry52Q0g3AG4AfA3gioQG6q5uZ56BsCZKLxA4J8dCSOwRCVarxehuQ0C7lB6oftM3gbM3cHoWJExJHhE4hnQHwh2SdyDsSv4Asr0k+KEcR1ZyMB5r2usdfoVoSZ+PZJjmxnRgsJhSsSz9WMR9krckrpvxvEOvUNokbQnQHGpXoxcaJI0cy3VA8j7B4zyvHnnRFEWemtKewDWQS5DaOHNFkAQ1I95rAcArTNI33eduZQu2DWA8XBjlHLT6rUwh5vpYwvugAsDzqu3mnjLGZlQjgaQ2AHyHSdKLwu1paH1soXmn2+Lu1lbYBfBQlfmPkpsHo1Yve7OJMqxnIW7AbEPkrwTjrwB4BcC8nt1J0yEUpAoS9wT9DaD/JPObqpVAvxT8UoJk2bNRPsLt0tFvmWiuFQpvgDzJNTwxSEpMSPQktUA2SDQBWzXgb83w/7P3bj1ypdl14Fr7OycuGRF5vzGZZJEsVrGqWC25hu2BWhgbFATPuDEDY16yIcm2UJ6B+8mAPfAPKNaj3/wsGIOGIWkA8UUQNGh4XpqDETDQSLQuXWTdWCSLTDKZ14iMjPs5317zcCJZxe66sW6sJHsBCT4wMvLEie/bZ397r73WWzHzQRmOU/UkojCIOkQwizNZlpwKgWcFvGyBL0k4Pjakn0BBC/nUxSbBJe2CuCHhWqFaM3qwc7/dOn8e8Ue8HHd2fn8iSbAcAs9JeM6FOXyUHT/2ZpJUBjEpx5KAKYuPBkl3i6Q67rZNwxalqkuzjyu5/3kg1ZdjD8R9l95y+c+V+XUydMikkyTq1WqWAZ4B12KjcTV+GQWZJwitrl4eXr16IZ+ba/Tr9cl2qVS+PxqFCpA0ADbS1J6D7NdAZqDHYrJLja83RlICeha4A2ADRCspzM4+egVDEoWGAfMqbA2qePyaJAGEcWlmSsRqsPCSZM5oXQAbq3hlePW9jTybG8WpqfxDC5iUMwgGkjPAL6pRfuy9x/XCQmSEdQEnDf6uA7OeayLArT3CAT4WJNfXm8mxmaQak3QSppOK4VUZX4WwKuA4xGUQKT/Da5tAFDmUvAfwgYR3JP9LqbTn7vuPd4++OL6RIPlX6GY/aGJ/VEO/ktRvA3gf0CKE45AWSS6iCCxBeGTO2SSUUSjpFPPNUs3hAtAJRNMj0JnIMgAHh42U7e3tUpquLADhrKRXATsr4TSAORQivuNM73CtPdLJ7pHoS9qH8Saod7I8f5fkvRShff785Qz4cXL37lrJzGYz50kjX1IhuTYe1v/SUSslUBcBIyadcUK6kAJnHLjszWaIZH4A+CbFRRQdyy9Aq/p8kBhK6gvoEVwndBvSLQpvp8a39zoHN0qlfPTee53Rb/3WlShdDMCpZGfneKVcPl/qdr00HDKtVhFGo5CMaEY4wViwbQBg9KnOul8vSh/VQFPJgVyAyT3PJcQYs/zBA4xOn+4Me71WNj9/b3Dp0tXupUsAsNYEsnKnM9WP0YMKT7quAT2XnEQNVBV6fPbCJ0FAz6N2SNwnrZWmpSFwyBe8ELpdVCjWJcwY0PBC4OHxM8nD36HqAlYgG8DQC/Jd3fuf7uDG/xcv3KznuDDT3dnxzcKS2cbz36qz8NY5tOFNPum9WbBFKpImBTqkIMkyeI/e3ZDQAgodh1oNJfd0qiQsjXI+J/EsgJcBzgKYQaFK9EntPkchMuMCWpK2jNiU/N0QeNM9v9vt7g1XVjpfa7Pm4/hGguQaLjtWL2a3AcV2eYtIrgVYJullEi+j0Boro/Ce+cT6GqFEZK1YPLZsxlVL2MylHF12AGwBIHDRKpWZMllejBEvkjgPYF6FxWw61mv89MK30JKwIdk6TG8h6nqahvfdfK+z2x1OT19IWq2tWrWa1sx0jLTnQJ1jIfI6+ZVmOIhUwERBQ+FkMDT295frU1P9IXBxlOfNWCpNtOl4IIV5gCug8q8ju5HQI3i/qOvoAwnvS3rfzDbyHJtAa7CxcRAvXrzq0hvc2blblbxWLs82JJ/Jc86kqdVHI06ISbVET92RACEU7R8RIXw7QTJKGhuqRSka0lwR0Rh6TvXStNQtlbwJ1JozM0utZrPbv3TpQg/4g/zq1Zv50tIZlMvcnZiwd2PUPuBbEHeN7IhagbiMIqP7qhCFLsgtUndjVHMwGI2KNf56qdnslpOEDYcmUdQjCwrQZ63fz/uDwgQKv58E0fcN9qDFyQ/DhLr7P8i7q2iO8hxNoMy0YjkdiUgD2CssgHUMnxYnWAiZjHmZC6RZMJLkBpW8A1wIwFUHENO0UtYozEfhOUWcpGFFwOKYu1z+jDTDARYMCuk+ibfd9Y673pVG671ee7iyspGN/843gm8kSBZNnCs5gHx7+59tojY1crd7dPQAViEcL2a7meDTjt7F/9VpmgDYg6tJs4PE/QB1PShetUagE0Iol3PnEsgXBbxKKDm06dTnUPZFtiDdBnDdpbc82LXOtn+4u1uJFy785xx4vVwq2cRQw1m5HZN0GuBLFKeL+upXulMJC1/wqqCpXJj0Urm2jyG2UY1nF2p5u4220e47MSvp7Jiw/ZUhqQfgnqRrJK6HgOvu2293uxyurGxkc3NXs49e+38nsXKimgyr00OPi4mwaobjWcSCmU25fJpAhbCSXCUWPXh+o234X/g4h3N1gmWAhjCO3NAC0BLRhCd3Ja2PRjmlMtfXm6MTJ5ABVzPpag5czICF/b290i0rp5sGHQgcyZVb4Q3+udNjX+AyAaAjx5Zc6yL3SqXREFjjHrKSl8sTyvNGYDoJYApFkPxK95DgBKhlALM025Xjw9JEOm9wq3mekZf7P/vZxebqarU9PT3XTtMkEIGF7qoSCfPkJz8gJBQhkTKAi5JmCZYpe9dDVgdKCXAhl656v4lKTs1RfC4EO+HQMRT2LIH8rHq+nMQQQBfUhoC3FPK/CMzuk95cWfnz/tc1fvhp+MaNwDY3y8NqdbDPej6cLZc+kNkki7nMJUhLIudZkFireCRg8tDjAoAaIBcF9SLQ5gh729u/s7u1pWqazldJLjDoRPGFsv4oi2F86iAioCggQugAagNsE/62hHeLJ5PdqZR9b+H0T4Y/+9nFcOPGD0vT0/mMGU6RyWkmeBnAKoRJFN7F/MQDwheHfTQBxLrEefUqK4N2ZWc2Zby20R0sLZU7lcBt5baJwCZgXQBDFMpHj3XUJzWS2JXUpeGmot4j/VqW6WaaamNq6v9sTU0V2fmtWxcr8/MnJtNUk71eabpqWPBSXDTXIshFUUuBnHaoQaAxbsalAFIBpJNfWqL+sUEdSooQyN2RAcoQcQBjm0LbgXmCKyGELUA7ExPlnZ2d392T1L52LbbPn98eAJeHc3Pob2//i81yOdRckRKhQum7WmQ9qgGFAtUXvjpiPImEoQv7km8P42gzBN8fDNLR9nYzmZlZaCQhmYdxUcAk4WXgcyX3vgAUUJSwSnItQ3ghi9gHwi0LEzelHw4Ku5OfjjY3/2XbLL1PeomUAGU0jAgsAZyUOMmx6nlxBOdY8o8Axl5H0gyIFebhbKv1fBbyrJ/ZC/0UWiXtZBROu7BCe5hkjNfII2eyKKE/pr61AG4K2qTwjkzvWhyu7+/3Wu7d/tTUN0/I/caD5PXziK9heTDcfhDrLN9JGZ3iFmHPizhL4TSLzvfCYUftl7I/oQJizkHBcABiP6ByEAKmQ+AU6UvuOMVi1vUTIcEBjgANAd6TcBvEbUA3zXRTyu8AaHa71pPAdSykvt+rhETziZdekHhBjhdJrBTHi4d6hl8Lxp4ji2T5ZJJIpRIPzl8fdXeWSp3+/oHS6fomgT0QB8TY2qIooH/ha3DniMR2MNyT8C7IaySvpWm6CfRaBUfzx8nmZr9UKuXV4ZCnYuRpID4nhSVAS2aYFaxOqS6pWnDyUObDKRYWk1XjZ9PXdX8+Bw93GKEIoxOIAqYIDAuREJ4E1CFtn8QDBntAS9bjCLenp7Nbf//3J5ohrGXS5Wxnp92Jsb6OUtJjDhRKPCgDWCKxNGYYPM7FRQADEV2amgS2a7TNrXav3+3GbH5+PiU5LflxU1gRferrCZCHF1DUESXMG/mSm1XNOEH6oN2uNycn54fAxeHSUnXU6fS3JeWRSdfEfZFb7jhj5KmxZUYNxb34lNjBkqRjBM8DaRVJqRWofTlWFHBGxX5fGpcSfvm3i2GOjGAT4DaBdZc+oOF9KH6Y0tZzpC33bv/27S8y9vzV8Y0HyR/x8qEiy/D99394Z3YWwoNUtAAAIABJREFUm0mpcm3k9deotG/jXJlQAx+TP3sERXF4gVQDQB/QQZKg444lgIvu4RjJ54RP70aSiJCGALsk7sn49y7+VwZbH2Fwf37yjzaBQ7HgtVBrouQ+MWEoLThwDsBvkDgx7pSnX2eABAARNYKLND/pjs5ohAf80eX4xhvoXryI/oULvzsNVPYAHKBQPTEApcd5jJIasqjlvm+ma5KuDYd71+bn/6yLcUq8vt5MJidRdq/VSTwH4AKB7xlxzIkVkpMsRHWLdlMxVgrgsWQ6v3Y8JNt+zF2SGBtfSCI0dp7UUMA9COuKeJ9UMjFhzXo9dg8O4JcuIX/zzT/rvPEGuufPY/2f/JP/FaRXIE7IIIgNAHOPd3XKQQxYTIe0co12/q+f/fHWtWvQm2/C9/bWqlJ9StJxyVdQjOd+jVzYh2t1bvxgOylhKOOGJ5UP2yhhC9X8Bf7BsFDwwk6r9fomE2xl0deNtudRIDEHKJGQfMaXXZKwQuJ7Bs0IvhWcWxCW3fE8yTMApkBVPi0HJJFLaglah/Q2ob+hZ38TY7bVbq+P/tN/+n+Hb7757bErvlXf7b/5m5/mr7zyiubnV2OpVr/nuSok+5TuAbg9FsWoi6pTmBBRGdsh2Fi8oEzTgsteoFBiwJQ7ps04LWgGQhDVZ+G2NoI4YKEq3oe0D6Bphj133QL4fg6/m0ftlVxd1uBvvbVWevCgkm53Q6NUtlVGnABwjuJZQHMAJg7Vn7+YfNVjQKxTWhbYNtN2nscqAL75JvTmm4gbGxpUKnHHjLcBKwsPmwmft5kc1LDgl2ETwi3Jr0t8n7St+fnyEFjj7du10tZWN6lUGsfd42oIOOHOlyScA3HcoVnKavolS94nGBk/AZ/cSHvkeg3QjAAn6GbMCj3L5FZtOtz73y79j/f+xSXvnUU9Jy/Hfh97wyFuAsHgEYX3CqaKpuAX82Ah2ZF8Q9Q9JzeQh4Mf/ejhJme/n6TVqs2EgFUJqwCmUShEfQ0396P3MFMCsQLIBDwH4TVkpRDzeHfB59e3t//ZTuGX/dNsehqDnR22zJyWIHHISe5JWCAxA2gWRBXCBIq6eqlgphR20BKOk1aVazES+zRMAVxRoeVgEEcARpAPQfZRqG51pOJBAmhdwLqoDx3+YdbLWsvL6M/MrMZvM0AC33KQPBToBRb9wYPB5sREbZhl/iA1mycxT2pRxDJhywIWKM0AmCEwMe6GlwHOEypBWFZk2YjyWIm5BNLGM7FtEG2wONoEakfCpoQHMeYPJNuRsKuovXLS7e/udYYSuLMzLEu1WprlS7TkZdB+XdKLAE9ILOZ79dmudV8WJOoilk3MnLqVIJ843PAkFEJlIPmWuz4AvAKGMqmHJYrPgEMcSH4AcZPULcmvAbxFqgUg3kAnmT9Vq+S9MCH5aSD8A4nfM9OyhGVA8+M63NdKYn9CMID1cXmgLGrCQlgGtKJofzfcn+8n2tft6doAQBwM4j7Jm2R+IKFOcFnCMYIT4znvz91DEjoA7sPtHdLvk6GDceZerDuVGOKsw06SOgHYNPDFFHAeB+NJlpKEAPIkBJhpluDfu4xmjazVSjvT0z/2K1fey8+fX2inaTJyLw1i1K6ZvSeN9ydxjGJRJpPmSTZITUIsA6oLLAmYZeBAwtCpMqgpghVAkcBQjpEZ99zZBLBH8oHTNwVsUthODNtZNtqrVtScW0ZnbD/8rfNzv9UgOT5ZC7jiALYBbEuw1u3/ebJXSidLnFhIyzyDEM4AOAngGArS24wKHlVJ0OR4EL8gtAIA4RJGoEaCeiR2SO5A3IhRd0ncQfQ7ptGdg+F7d9577+royhX44ROpyArfCJXKzepwiGmz5JjElwn+hhHPS5ogOaGH9+vrz55cqhsBGYzCQgw2ceUKwsWLcAAqlUbDPA/bIeADkTUrAlf+aO70iSpLLqEHYE/0+3LcirH/9vz85fuHt29ra63qIasHptMR9rwZvg/iN12oEqzqC5kxHRkEoBBcMcO0xAVAzwuYEzhQzO6lfRtWPXMJQ+An+5cv4+Af/sOL96enTy8DeB7C6eKmqwx+2r356HuReCDwnoB33W2jNmEdAHjjjYKeFmMsJ+AMgVWRx6mHylnfxGcPJCRglcVEzwmCMFNrIkUzDjMApdHFi1f6ZOGNDWDnjTdw6/x58Ld/+58fy5k8l4b0pKSTRpwkORA0X+wkTY2beDUcEsM5rjVCLkKQBpB1ABy4awPAhoT7kt8E8psZR+ueeLvzoNN+4YWfDr+B+/BY+FaD5KdAvVI+qtfTjntCmhngPYAbgE8DmhZRK9J6VgEkkgIfBknKAPei2DsCOJBwAOAAUAuJ72qAPcV8Nxup3Wyfybe3rz58ijeba5P9fn3S/daMu52wBCeieCrQXgIx784qoJSGb5RoQCBxV5VkA7S5QFt56R/8zuq9g9KB1D/Y3AyjalW7JG9JNiXwJI1tAQZHWswZf+I7jwBtknwX5HWaNkJIhuMtbAC4v19ZiLAXQkjOSv49iCsqlNZLNNjR8tf54jgU5pVYFbSYkueCpYNqI3k3y/zmtWtrH1y/Xqjrd7vwqSnuhoD3JTQkPD+etqp98rszFvPwyEjtAFo3wwejkW/t5Xlfgu3hn9fXd0OjNqHjEBYkTRHFensc1sKXwVhEomzGhkvPA0nWy8ICA+7290brIfyrrXv3Bu2Vlff2gav5pUvAtWvQD/6HUa8yCttK3JmwLWlDUTfMWJfYIDHBsZaBxOSwCSscukMiFrYR3iPQJ9lyVytJrJll2k6SdEvEQTLYH5w92/9O6Kg+8SBJQj/7WWe0uno6Tk93s0pl0B9nTJUYrWzGsucqkXnqphJhCWkJ6IlAIacYEI3MQogjCZk7RwocBfdhjBjk1GCQ9wbHT2T9efx5fv48tLZW/HmgMpXnWJXSk4DOGXGOwCkAc2OOWKVwrNM3S/sjw9i/py5oLnpYKYXqSu6+ub2N4dLS9eH+/rndPPdhmoYZEOfk6JCouEDyU7/LjMTmeM71ugffyGv5oAHg6tULYW5uNzQaXAgpX5bjBwJPQFghWSUfqnk/pSALSouMwDzEc3DWYlQ1AQbz85U7a2uDCFzW5cuIJ0++vhOhGxJTgmXCPpU7SSDKMRxPc+0G03rMRx/4QF318h4aF0390KhUwxLcVgVfADhZcBIZ8E2vNykhQXcSwPMEpyzohBzvhsBpADdLpXBvc3Ouv7SE/NKlw0dlpwsgdru1dmbYCIZKBCqIseRRJZKpmUokSu5MkBgJEZILIZOUS8qCI4seMncNzXwIxEGMw76Z9bODbLC0upxfuvRn34nR1yceJAHgt37rSj4mnw9RdG9/EZTAK1dgZ8/+IJ2YmE77aSWte9VdmQ+HQ+902tlf/dVC9qMfXf7Ep48Eu3r1Qpia+mHaaMwn/f5BWqmkaanE41F63t1fDIHnIZwXcHLMQQwf6Qt+ww2KYvQrQcGAmjPj8ai4FcgsLU82yaudP/mTq+0zZ9A5e/b37pPlTRLbEkpFX1kfo6VoLJwLJ9F3YVPQDeTxRixrd/9GJ7uzfyGp1yuVSuXlSghcNtgLAC6QNulSHZ8tNPC0YMxTLXzBSQYLmoWs7+BdczY2NytYX78wWlu7mm9vd1tKyx8GGFMLxySdK8ZENVY8/yj7U6HdeOCuFoBNyTf+9m//+N72NrS2Br9x44el5eXSZKa4YvCTci6CaBSNFeCbXW8sZruFwCJrrQBaHkvHVQGlkpI0NUuS2eH+/u/tP3jQycvl2ezUqVIEmp1a7SftTyJxS+CNG2dLU1OraZIkwWLZOlayLCq2h70sW98d3bx51dfWvj4Pmm8a34kg+QUgALhyBd5ojPK5ub6q1Ri7MZN7VXne1u7uQbx27cojN72oNa4ZcNOazTMTr7xSaoRQbQyH2ezExPRsBOboPA5pNTEcl+M4DZP42IL/SmOHXw4GwyzhZxJDH1IvTbL74266AMT2sNRGrg8h/S3JnpxnAE7hYztLhx49jj2YduXaqcyke0Mc9NbP9uOv7b00ERMtJQxLEM8U/D/VIVXMGJ7A537CYCjoMYCgRaNOpmk8l+d68MILZ7bJq3u7KvUGe/leSKoVd+6OxYi7AkpjGcCHWTeJAwAfUrgJ6EaWhb0rV4oa+Noa0Dg7n+ggnw/C8yLPgVjiE3swieOpl4oLK3AC4BTJVbJyNgRsHT8+u5dlvtdqtdsh5AeNxtpBwf+8/EvB7uzZG+NEZSECFQ42u1Q25WF/Kr57c8qvXbuqH/3o2/+UXxZHJUg+bPpcunRVAGIxkniIKzp1Cvr+9x/9si5dAtfWEGZmjiWVSqkxGtmye34MsOdoOEXjKRhm5ZyTMFNoCWJiPNKIb6KL/fmgEZqFeAay6PKNLBtO/If/AB4eeUYHeScB7tJClYFGakrg6Y+9h1Bk5W0Bu3DsOuJO6/5ua2VlI7uIq7Fb/t1qptIxml6U83kVPswNkunTfcT+VAQaKhITUAsiT5J2Lk09uIchgL1ZvNPH7LG81TJLWNp2ZwtEh2AND21QH+IAwIeA/gbyG2nqu4ff36VL4L/7dwdpjI0FC3aWxpcILnnB0ngSMIkENEFgRYZpA4+jWDt7HrVO8JZZuO1e3khT2wB2BsBNAg+niQAU+7QInjcceI0AsLRUBXAZq6vQ+fPQj350NDLIQxyZIHmIjzrklz/3ta+//nqpXs9nKpXKdJ6ny6SOJ4kdd9cZEGcgPk+qJrA+nqH+hXL5E1mxBqHB4gw9pHEZXpr7t/92bWt9HaPV1cvDEIa9kJQ3GF0ym4xRqzS0C6GAws8aQB9AE9QWhL0S0V74mEdPs1+uMucihBcgPCdgfiy2+iwGSKAIFCUAJRQSZauAtUn23cM2AJBXMwCZ9ONWZz9r0rRr5J4AOFAeq5pnADKHdijcoeXvmHG922V7agqS1kr/5t80ymQ245YswXBCwCoL5Z0nQLF6uOI57kqXCEyDmAOwCGMHhYdTg0DNLEyNRmz0+8t16XjT/R+3gP/94Bfe8Qvv0aOAIxckvygksNvtTud59by7nSdxXOKsCj3G+bEIcKMILEq+K6To8TR4KmlCwAwcK+56nqwNqlXfvnHjhztnz9aGW1vDVqVCF5O7lvC2nCcKki+mAdZIdCBtw7BBoOW5Z8BhCQLY62QTCdJFimcErLjwtQvMHlkUD8wlkRlk20miG4++IHendUhsOfEAQoLi/glUE0DTyFsC7sRM90ajfG9pKfYA4OBgZrJcHs1nWXoyBB0HMDfWZCyPNQ2+E5AQIFTGA6ZLEgKJGUlnSO6GYE0yvgUMr415oDgqNcbHxVMZJN94A3blCuzChWRasldJ/veATpBWBVGVVEbhMVzGQyGN7wbGwsBjzxXM0HSMDGfgec8q8Kmp+j7wk97i4lpzc3O/k6bHF0LQHQC3QeRjPcCqhK4D25A2XNj3kh3q7fHKFdhrr9kEiEUBZwCssFCNfwLlhe8iWAW1ZGTZodseHxWg3dzMvFxLOhC34HhAYBJgBiCXY4/gXQG3yXjHTOu7u/u9+fl6LoH7+8OpGHmCxAsST4wztjpAU9EsfDIf+ZdhIMuCUollALMSToHoA+gB7LuzKqXNK1dwc8znBb6i4st3EU9lkBzXftTplAKJiSLD4kLhxsjPNAN78hh3HoEAaELiklHPK9ggBTqliWQTuDgALufLyxjt77++bWa33DEJKJOjjGK+vB0Cd2S27RGd3NNcgt2+/Xrp1VctzTI0kpKmCc4BaJBIn71mzadBJQgNQSmk2Yg4effuD6r7+/vx/PnrOTDwdq/WY8SeyG1JixK6ACKBdTO9DeBGCHwwMVHvTE39cQ6s2ZXbF8vfm03mkhTPUTwnYAX0ybHNLb5DARJ46EVF8BE+KHuguhB6ZKgDTC9efBgYn8oV9FQGyXHx2N2zUQiVfRe2QEyOl2D1I3my7zxSggsQohHRM+0ilu/uDY/32+2LI+nKsNOJ+2Z+U2ImBQCalDAFoCX3JqGWufWqGOZX8eOwMNOpjmK5PmGaolgjVRae2WbNJ4M0FF5MBFEzD41yeXVqZWW1D5zv375d08ICBnK2Ce052ATQQqFyfyNG/zt3fpDn+c7ERMev4kKyiv3Si3PHqiVo2Z0vCDhP6pj0aWT07yyGcrRI7LirKcU+nsCo4LeJoxIsHhsk5F4dubMtcMvFXYk9feuG0F8JqYAFAC+48+XoOKEc03FjNFEfTqa4BD54sLM/GrVvDYcHfxWjvyPhHskWjM3oag6GaOWmXoyMcxiF+bRSrZY1HdIwBbLmsvJ4TvipXQuPDSlALEGYoFgDQoNsTMU4MwHMJKdOdd37PmT0NlxNQE0TW5S24P6BlP1tmrbe7febO8Blv4DvhfxerWJd1d21DOAsqVcErKDI+o8MSAxANF3aANQ0sz5ZqGc96Wv7pvBUZpKHKJXCaDgctUKwdYBTEKZo8CN0rDQSZRbf0zyMz8n8fLJYScwr97C2Njx79nIGXHBgv3/Q/I27YPq2pADofZIbQtbOunFApvEUSrafZRVFNnJ6g8bKmDT/LYqIHwV85OMiqUxqIk3RAHy0t9fvzs7OZDHrDLOQdAK1jSTcgkkEWzC/VTLfqtXePWg0ro9HGodTtZnGiqKtAnie0rJkU+TDgYUjA0l9QDsgPpRzx539J31N3zSe6iAZ42AEcM/d7wKcNeOxIpM8UgHB9JE6+ymUbBCc5QhpexHbC1g7VEZxBX8A4OcCm2bcjpl2EpXb1Yb1t7fzCDQTs1opSThRFN2RHqUN+iRgVnR53b0eY9bt90fJ7Ow9ZcmpYTWonUduBmAg8kH02E0tfFirdXvA9Xi5YMDYP/ptzJfJl2D4NRHnAM6TSgQZv+EZ7a8bAvsAtwHdMsNW4Vz4dOOpPmI1hskodd9j9Duk7gNsSzxS9RNJJilxoSHgNIDvy/hrEleGQ5QuX76MYurhchyNOg9Go/7Ps6z7//T73Wtmw3tA72A02h+cOlWKe3sli9HKnoWa4qF48NHapN82JCaiKgqse2Alma6Hy5cX1O+PhgfDrJNncXPYz98bjbK/lOJf7+4O7gDlHgm/dq04gobIOZHnCPsBwRcBzakQJPlcD6bvGgj1SG2JuiXl20kSn/og+VRnkuuDg7xarbYtj0kSkk1RTSM6Krrbh7PS32F8XDAViYQ6AAE6EYK9UK/Xtn/rt37//sEBdoH/vNtqZaPZ2dBJUx8dHABZlijG3JOkk83MwAvOWzBnkpAIAk36eqRdn17I5EiomJaoEJDz2rXL+sfn/uUoVvIuyhh5teKeR08SZWaD4aVLlyWt1fr9yuxwGGYZcI6y5wQsC5gs+IdH6a4rEswl5QD2XdqJwP0c1iyNssGTvrpvGk91Jrm6up1JrfYIvc1cvuVQE+QBiT6o7PPf4bsDSQmKIv8MYCsiziHYhVAOL6JUnpPAs2fr+ezsaLC/n3fd867U77nf7xeexJcdmAEZCPhY3UdHaqs+ERQWY0YPIc9p7JX55pvw9ez6yCfybqxstaU7Hfftbqt1e7C6up29+SbU65Ubw2inEPDfSDyvwgpjnsATmqz5SoiChiS6AFoUtpFlG4NWq7W3t/fE9R6/aXzHM6mvBvJKjmKG9qDV+l+2BO65eGCF2fwR++wMACYATgBaMbIPKrikfDRqoowPxmIDn6rB12yOCEQjQ5BgUGGL8St8JmiAwZWkZgbmBIDvf/9qBlz9pQetBErA7kGcCgqnAL5G8MXCiOxxvXG+IxAiiQHAAzM089x3Fhb+8AGeUl7kL+KIBYovjxhjn0nYInlDYAZiBVLj83/zO4mKhAUCItghcNDq/X4Plu/tis05/lH7SV/gswjp9cpOL5+hczowvEzgHMGz7jhmhvoRYlU8CrIvaYvU/Rhxf6xw9MzgmQmSIaS9YP4gxvg+YElh6HQ00yiSZXfNC5iAWBgpRWTw9Cb2zAH8Kkg+Aezvj6pJmiwHs+fkfEXgOXe8SHKyUJd60lf45SCpb+QmoBuk3wPYxjOSRQLPUJDMssHAPdmS9IEZJ0kcw8NJAfEodXnHaj9lFGotQ9AHNDhhygM6d++u7ezvI54//0pOvukf/V5XQC03syGAAcABgIEKk/iAXxCOfYZxSKuKJAZyDI0+dFeu6qPTJYVgyMUAVMP+IEzLbTXP8AqIlw183kyrhTDyk/kgXx4PhZthZFfwLaM+AHAP0K8yyacRSZL0Q8B2jEpILRJ8XoXV6nhO+siO5TXkXIVoElQ2ojQ5HRoN7ezt3djFx7LKmRmMBoNR051pjGEyRlsws3kASwCmxj/PPCQNzLgPYB/gbSK/K+T34LGZZf5Io+LGjR+WpqfnZkPgHBBOw/A9wL5nwHMSZr/bOgGfBQpQRNG0OSDwIEbcBHwjTe1XQfJpRKt1e1AqHdsx0yBNSyeTxFqQjQSkYzmoIxokVSd5HIUXMtw15lbiRqVSG+CRo/d21u8vtGIMWSVJqoDNQ5ovnOwQQP5KLg1AoSGJHRL3AP9Qjrs+aN7vyXuri/YI5WV6+lgpBFsgdUb0l418FcSrBBfGc9lHNEiqELeWRgDagj+QRjfzPN+anq78Kkg+jTh16soIuLC/vl7qlkrnNiVsk9ohWQdQx5H1lGYFQKUQimWfRE6K7kSejwbt9u+PGg0NgLtD4EqcmbnYvXGjOpiamqmlqd9CoeQyIpC5RBIVFBayZRQB8zslJff1QgJYTCtJOckBoKGEDYC3QN0S8EGejO4N9PPd/f3JuLp6PS+O2K+Xm81SOYS44B5Pi3gZwisgzkJ8TgXV58hizIvsSugUXkrcGo0GDw4OBvsLC8if9PV9m3hmgiQAXb58xs+cuZmfPu37DHaXwHUJxwEcx6dagx4laErESYglM09krCja9N7e8H6nU7v/l3+J9sICcPFiP3Y6yy3muhmjhmbYjO73aLwD8RipYwKXxko4JTy1QZIOagRxRKIJaEPSBoi7oN8BeccV7wWPW5ub6/nBAXT5Mvjaaz9M6/NYLiWDY1HpczS+ZNBLIE+hECQ5og/cj1DwIrlF4p7E2yH4Tr+v0fp6P/7hH/70mWnaAM9QkCxUSi5HAHHn4JWWu9ZBvk0KlE2hqMsdcXBKrgqIeZBlI+tucbKSVhNU1V5bwwFwxQGoXt/aB14bdru+AaR3OdIdIhwXcX7sGV2HIFJB4pHf9J8EEi5xRKqnQk7vHZDXEtot93gvz0b3QlB3ama7f+EC8kuXwPPnwTjdLk3Y8pIjfZnEyxLPQXgRRYAsk0yOltjUJ2LowrbAD+D4MEbuJkk6LJxNny08M0Hy42DwA8LuubwC5yToKwRHH1MpP6qZ02HXewLSUA4jLB1F5PAkb2e/VwkhO+h09g+WlkZD4I869TrazebrQwujPnK1GIKLjAQHTs5ImAE1CbFSjNOpVNwnhaPTCdehvW4UECEOSPULoVy15GoB/FDAdQOuZ9S9LAy2Fyf/j20AunLlYlhYWEv/9b/OGyGUGwkwn7u/YoZXATtH4iSAYwAnAeDoBkiN7XrgEDqEHnjUDdI/lNhcXZ155gIk8IwGyTBSl+SGF57JxwieAdB7io6XBmDSHccBlAQlpnTahVX30i0vp7f2wGb79usj6SfD9fXucHUqaQ4sz0ZMnMSuk+9bMWt8TMKyAYsgliROAyiDKONoNbtyAUNAPRCbEjbl2CT1QOKGzB/QuMHUNkp53J+pzXQBCLiQvPzyiVK1OihrNHkKZqdBnQbtDIAzpFZdnGFhuXHEQRHKAIxAtAC/b4YbUn7HPW0BzSMlDvN14ZkMklNT9c72djPLsqRZr088L2nPjD0XQCJIR/2+iAAnSUxImDZiUvDjNBxzRzmFtdvbw2G9fiAAo9XVywPgYlbBVruzc3Z3NPIblUq9yrRyitJpRzhD+AsEAsASCAJMcYSCpITciIHENqG7gN5z4QMp3k5T3CLzvSzrD/dbm8PV1VEOXI2Fwn0jVKuDcoyom8VTIL8Ps18DsCRgWY7psZHcEV8zRfkBQkZqAGDfXRtS/gEwutPt3hsuLFz5VZB8dvAH+cLCmgP5qN31LXN8KPADAEvuWCKflEn81wUSY5UjMwQJTlpJDgA+DEhVS3iXobTdav3Odq/Hzs7Obv/Xf/16T7qeAegCF0JrcM48K8dA9iF1IOyZaVnCFIgpQDXJKqAqEMrAobkabDxr/m1l5MUREXIJGYkhyaGkIYCBhCGAfYf2jdx18UOQt83i3Rh9Y2enu3H79p92rlyBv/km9P77PyzNz79e63bzaqfDOXcumPmCFL5nxpcAnAIxBef02FnxqUCh8sMmhC0AtyU8kNC8detm78KF4qHxpK/xSeCZDJJFhnDZgTUo566MN0jUILwMqAbwqSFVj/18KsChJJoFSItpSO8IuiX5rVIpbqyszD74kz/BAEXAEXA1YnBif6Cgaoo28vCA1HsRnCU0R9ocgDlCcxDnAM2QmCI5Janwr/7WgqQEIIeQgTgQ0JLUgmPPTLskdyXfhftuDu0JbGqUN91ja2LC26dODfs/+UkxSfPGG2BlsV6LFpd6niwl4nMwnSbsFIAVd6yQmoNYKYRzj0hZ9othBGgT0Lsk3ia5kaahf+HC1YhnaAzxF/FMBkngo253s//6Tp7bB6lAkXWSq0/XcpABrAKoAKoTXATxMsA7cL0lYCJJLHEPg2YT2ygaHAIg6U/3p4E2cNFu3FgPlcqCDQar9UajslSp2aKcqwBPUjgJ8Dik6I4yCRZ6ld8WFYYOIQM0MKDljgcANijcVcQdg+7K4oNuN9vcwPu7UyuL8Sy2HLjqAEQWAVICL10CJ/JQsxKXaXZWjlcJfo/AKwDKMJTH7oY8aoK5nw+OCG2a8I6c77j0YDDQYHLy6Tb6+jw8ZV/y42Pj4F8tlIAFRF812j8i7b+DcB5AhURFOvr6dGRvAAAgAElEQVSct49hfCxFlLQD4baZbkn4ENCHgD4k1cpo7WrI90ejpL+zs9l/4YWfHnp242c/u1g+f35h2iyZNkvmybCYJFyQOAdg1h2zAGqSJkBWUUw0pRBSEAFCQiIZuzMWTAKSvzQ/LwmEF/8yQnIREWJOKgcsE5RDygQMDOyR6KFwLdwDtAdgW4rbGvq2cjZjab+5sPBnnY99lvDqq5PVSmWqGmNSVxqn4DaVu44H2UmQJw04ReiUhOdAhKKMwCNTi/0CcByWJIj7lP8Fib+Q/O0YbWtv78HWCy/89KnXjPwsPLOZ5CG8vd1NGw0NLcQAOyXpHol5ADPuSMiniSOoscEVA4EGjCckTAJYIfi8UVui30mIO4M8uRst30mS8g6AwyCpixcXss3NykGl0smyrNxNEm3HmNbMYtXdqu6qIqBmZjXJ65LVSNQI1SRUJFRR1C2L4AkmBZ0IgfwoMxMYAUWQ0YVsTNEaARgQ6Evog+rC1DFn16luQutI3jfzvjv7ZuoliXXzoN5o5IPNjfIQHx0befbsQmoWpvM8zJlpBZ6cRMRzJeOygEUAiwSmAUyTSADyqBkkfT4kFA+YlqQNEuvufifP432zvHv2bP2ZpP18HM98kDx+/M97AHr37v24F6qjdRjuEVwCEEjUAVU+evVR4QV+GvjRjHoxpz0JEpC6INoC2+52XeQUTBaU2uRkbfDWW6/0trcX/cqVK05ejgC645/dT/orW1trdTI2UE4bRGkmKJmWwnSMsWGmurtqpFUAlkmWACUkE/gjNcyixgjkFAYSBjD1JHYi0AHQRsKmOGgiqm02OGhMpwfj6/tUFCOFsKtXLxiAqtnEbAhajZEvkniVZq9KWgIwCWBSRRPqK9737xoeUbaMgLoAd8x4z4F1gHcWFv5w44ld3ncMz3yQPESvdzfWaoubMl53lxmYA2iMu5dHmWD++SiOv1UUB95VUDBwmtQmQmnz+PH/dmd1le3XXjvR/vf/XgdZpq5Zt9PppMPNzZt5odL9ERYWOlmrVe7nwwxJWonRY1/Svhkq7qiYqUwiJZkAntARAA+gPYxGFKLMI4AIIYM4kpSZcWCGQYzs58NRz2zY7ffVJ/PRf/yPf/pINVlaC7dvb6e12kICoC5ZrdVK6xImz5wJk07OImDRnUtmWBGwKvkcyQkJafH8+Ha+gm8fFAGXMCSxIeqaS9ei4no50VNv7vU4+FWQHGN9vR9nZ21LjG8bmbusEciTEmZJJPqYF/PTBoJBVLUIDDwhYQbCKRFNBjYJ7sqxoZhsSL6hxDcHXtnEZGxfWD3Tl67mH6eHXMZP87Xptd599Eeh2ev1+8l+mpYTIEvMFEgEMg+kGZAwc1rht/NRpp6m7qNhVKkkBxIfDt0l9zRN8na7H2dmqlmbnh+M9rLzx6sZ0I9vvvlog+EGOsnc1EI5L6GqrLyUMFnUOCAyYCWAi3LM0DgtaQqF0VrDXcVoocSn9CvHuFkVAQ1deOAe3xb974Z5fl9Z96n30n4cPJ0r4EtAAu/f/3G10RhUzcon3OM/BfBPAbzkwgTJ6tEnmT8WHFCPRFdQC+AtSLcgfeiOu0jiHSd2OUo6IQw7WVbJ5+czB6oCRg5sCthyoCFgQcDlwyCqL8u300d8GwJrBLYJHBA4Q6BmQJdAxXZ2UjMb0iusKU/qVN6gcNLMVk12EsbTKOx5lyHWANbwFIhSfHFIIAYG9AHsSvovkfG/dIaj/1oPsXvz5s3eL54OnmU8S5v+M0FCb73VzJtNDOfnQ7tU1R2CPy+MtbgqYRXP1P0SUWTQFRX1ueMQyyTmYTgNT/YMaCHgIPfyAZO8u9dOeoyjXggYxDg7CGFm4I5RmmXDOFwbjSrDrNOZzf76r38ex+TkL0QtKbieFw2ohu3telrq99JQrqSjdLkcwlIphKQcLa8Y6xUfxYkkiROmdCIfoAFDA0gmCczCMQvjrBwLJOcATkgqkXoK646fB+5KugfwNuAfBGm7HmK328Xo5s0zDlx90hf4ncGztjI+ExLsypWL9sKFk1MTSF424GUJr0L4dRK/DnD6SV/jtweJZJTkADMUlqJFAwUYAhwI6gLYp9QuRjttD8Aeqf3DnxjzrkXrxBG6iQ36291skCSbw83NUX7hwqPH9E+/kosJgOTGjX5pubFSyZ3VUJqshsTqHrwuCw3Jp6I4RWjGHLPumAMwRWISxCTIshwVAOWxZmYFQImEfYyO9IxAkvBzyX8O4ufweN0sXltf/9v18+fPx7Hr5lNbjX1c/CpIfgLu3l2rlifLx1PjcVryiiJ+k+JvopBTS4ufo97p/tL4+Obpk2pLOAC0K3DHgB1ATYBNh7fgOEiANl0dZ+iFsnruPpSUuSuTopfL4RM35HAYCZRoNkrNmJIqmSdVd064Qk3SZDQ0YJyCa8aM0wDm4Jg38v9v791+K7muNM/v2zsizpU8vCbzfhNlXSjLVtOoLj8MkHprAdWFfkljpmY80MyD/g2l/oQGBmjAwABGFwYYOB8GmC7AaGOAynF3lafaomRLVlqpvJFMJi9J8hyS5xqXvb95iMOUZEtWSknmNX5AAlJCihNxTsQXa6+91remvNQAMAriC1Mxn9vfDQAyUOmwauA3An5jAr7vpRXjeKfR+N+bj/sEn0Seo+Xjg7Nx8lZ2onN+F77GElUhzYyIIwSSoQP4xHOWn/waFEisDAvBLYnq8PvpkegZsQ+DgWQG3igWlfgUqWRSGGU0zCwCl2SUgfmTpbdI6w1A41UKvFdAMIAYDesrSyLKliwRrHj6qsAqqRoN6pLqICp4tpoBHhL1ILZA7UC4DeC2iwfLElpxap7rgvG/RPGgfwXzWMhQP7+7seF6aYAAljOB4bTPayctpLEiCAeGnSfV4biHmrwmQWTIpw1meUE4PCgHwhPGC5IxcN7TS/CecAQy5UOnvoAMwACEJWmooWEGYQBQlOWwNMvD7/8uAUQrIIB0//99ev0dD5weoE0AK/loCt2WmksTE/0EmC42ar6GQiS/gmFfdwIgabf/l60BuJwBowYwEEKC45BqQwfq4Dlbwn3xWvenTIbAfQcNAF+uL/yyRBGS9vulh/NlkNdDfhkzbGO0w06XP6tVvX9cfUUCbXgu+rNTfu5wgJzEDHkqZBHwn3rxtjd+Y3ryl8WM9m+gEMlvoF/v9EtxbcWn9AbGQSpTmgA56fMBYvXHfY5PKQRgSEC5vv7JxgkpaSiM99spH8NpPt2QSCX0APUILZP8hNT7UaC73mvncZ/f00Ahkt/ANNDf2HGrWcZmrZbBwEyJPCUxRN7XXYjkd4MAKOUh31d3thB45px2Hi3yyAB0CbYALEv642CQ/jYMs8H4OIqi8QegEMlvgLzsJPSvXEH82mv/07q1umHBBoGel86DrObO1HjW3GEOkS+lJ75BBAuN/A4Mu2ngBDRBLhlo0XtcsxZ37tz5rDk/f94Dl59rC7QHpRDJB0MXLsB1Ot2W99XrWYbEGNsjGZCYElgmUNZTNM6g4JnGA0oAxIZYF3VVHh86h5tJ4jf+039acPPzC9+58+l54zkqoP3ukHkr3VI92Gn68HrXB//sid+DWALQJjQQ9NxbShU8KcgTTAzZI7kuZ/44GJh/cs5+LPn1995DUSz+LSgiyW/BVcBdHNvob6KeBf3aik91lWA1N4XgcKyoguGyu4gqCx4hEnIPTk+wJWGF5LJz/g+Au50kcbNcdt3NTRSlPt+SQiS/BRdx2QMXs2nc8jvxi+tA8LGH2QPsGyQsiDGIT+O41YKnHopEJjHN85C45uE+hOVnoeHtSqXXnpo6Gk9PH/uLfpsFf04hkt+C/bk4ANydO9FGo3G0nWXprSCYNN7bIwTPgJAoiy915DxXdZQFj4wv1QR475HRYCBgG/KfefCf+2m8HDNp/8f/7f/u/qmVXMGDUTy83xHpnRBoldrtrOT96A+NsT8U9H3BnIF0FuCRoeO2HRooFBQcMPtLbDhAHYF3DLXsgGuQPnRJ+sFgEG8C6J88eXlQ5CG/G0Uk+Z35mQPm4+3tkaxWqyxXKvKQbYKaB1kGNCKxJKH8zccqKPj2EJRy5/YE4C6Nbgj6gHCfMrBLwajZ2sHR7go+dqeGAvkFT04UovlgFCL5LRnOsSby2dTZuXNI1/XT1V433QuQ3qOPqqSZoTAJYkSiITHsGPmTiYAFBd8aiaSQd1w65N00XRLrzvsbNnAfDDJ3vYr27ghauyO44mZxwUqvRkDDbm6WbLsd2HK5nEqdhLxSVGV8A4VIfguuX3+rtLJyvFat+loUYdDtZj3g77vtG1vZxCz66td3LKPrBipBpuU9zpM6B2AKQATk85of82UUPPUoE5AidxZfBPyShBuW+sOgq3X5tD2wQTwycsVvbPy0GoZ+nDw7LmUj1tp6Y0I1GNzd6tVXJGzgC7PHC/6cQiS/FROlMOyPScFUHKtdrWabALqzs79MFxbm/cmTzgVlczMz5a6V7hHoC6wSrEgCiABFbWrBQ+IBRyCWsEejmxAWaPGJF1el7tpg0GqfPYuMhNbWgqr3PGoMztCGR0hMA5oC9WGamOTG6uz27OxJJ10pisu/hkIkvwHpot3Y2C2naaNUbtipwOGEjD1hrbayJLLN5jsp0Erm5zdT4Fe9jY2frku9vVKp0jbG1EmOSz4AOAlhMnfFhhVki6V3wYOSjxHJ2w0F7pBoSlonzLXMuI9Jd9Vmg87MzHQb+L8y4IKV3or29jTmvTsF2FcIHJdwFDRH6P0ghGlNTb3earfV2d6+0AWuDB73dT6JFCL5DWxtjVSDoHaiXNYJOZ4yxpyiwSnnuG6tbjgXN7a2KptheHxzbAwtaZBubqIvuaYUXBuWadwjNes9XiQxqdyDsYZi6V3wgEhKJQxA9Eld9w43aXg9c9lnDLK73TTpmNH+YBTwwDvB7m6n7hxr1uo0rfkegB/IYxrgKIERGPMiFMZCvZqmfrF+pHb7H/8RmxcuwBdL7y9TiOQ3oE67Fo5WTxtvf+CBFyWelddZAsvOYwwwFdLf8N4OALSAy9n09EW3ipovbQ8+y4w2AwbrATAgVNXn5rEVFEvvggdE+ciFDoQded0g8S9Zkv4+DLUNlzRPjt5qA7lpxerq35TGx6frCtxUMuAZCC8TeIP5GIsQQCAgIU2ZNJMKfQne71648FYT6KNYen+ZQiS/AumivdGMao1SWDWOZ+j4IohXCcwCOCHwJARD43sUegD2vMcqsD/P+DIk9G+03nJuLNybKk1kPlOdNFUj9UUeF5ARqJIoSSoVS++CPyX3glQCMDHEPQnrANYEXk1TXYtj3lhfH8Rzc5sDciHbn3B4926+o2NSgBAFayVEwwFoJUARhRkQgaQKgT2TBa12ezodDPp7cfzjXek3RV3lkCKS+QpWV/ulcYXHbWZeD42Zh+WcDGZheAzUKCAjqASPMQnHAI5by/K778Ls16GRwMpK39mdNHH9uOV99hnp/0lW/xUGH5K4RmI1H6JVUPDnSBhA3Ib8sqRPvNf/55z7f5zLfi/Fq0GwPpibQwJc+dLyuNWqZDaJO71BspVkfo3EHRrcBrABqAMAAsqAxggeE/Ayrf8rB/vjoFx9IRo/O5rnNAt9AIpI8ivJstFSqcbjCMz3PfycMZyFMCuoMWw3NCRKAsYAHPPSOL2vXLgAA9zP5+jNN69kENwfPnm1VTl+fDATVJe9H1v13rQ94A2ZASohLxEqKPgSpAYAtkjckfAH0n0gJR9EUdQbGUl7wK8G+X/35Yhvbu5yurAw35mcHOmHY2dXfeZWaM2iIY3EEqAJAmUIkYQqSUkYFTBJY2B8uLm4iN2zZy9kxdK7EMn7SDCLi/9udHS0PCLZ4wZ4id6/AnDWC8chNEiGklKSPUGbJO4AXLQB15I+upub0KVL+eHuH5jQa7iaSFezK1fQff31/z6yNqwaS1LqeqmHPF85AmAEYH3oxm2KJfjzggTkBeISYmPQltDx0qoBbku6DeDTMMTtWu36+n7u8evEK//7hQxA1mz+tGmtve2pijxjGDmKUR5JokKqAnCSlIEkZWgFNO1G43R5e7u//dlnP26+++5v4vfew34B+3NH8RAOkd4J2+3BOcmecw4vGmteFTUH4RSBUYCjoDICbUkdAlcF/B7S751L75TLbrla/T/XgK9u99pfhrdaF0er1epUHHNa4hljeM4D50mcgXBWwknkL6/C6fy5QSLpJHkSTQjLkpYB3QZwC9CtINA6YO7Vaj+/h7z4+4EE63br7bF6ls0osDMBzRw8fmCMeT2vleQUgAagPskeoG0In0n6DOCnxrhPgeTayMhnu8CCe153vYtI8j6JzTIzY4lXA8vXBc1CmAUwiXwYlYHQF9ABuOXhbwdGHwK9Xzca8eCTT0rxa699/Y3L+72zl/eAC907dyorI9NTG9bxHq1Zt2DfgFUCR4YT/op80HMDBcADzCS1vbQE6HcGuibx5thY7wYwHgPHvrVQnR37+R4w311ZiZZt9aXEGIYS6wA8oSqIMYAVCSXk0WVAwwnnNeqlOPb9u7srUffkyQv609zn88JzL5Kt1ttjpBvf3uaRIOAcgZfl+QKoGZA15i4CsaSExBqBm97rFsmPvfd3ms3N9rVrbTc/v/BAPn25WF7JAGQ7O3+3k1qzaqCUCgJBqSGbBKYkTAEa/8JoiPCQv4qCR4uXFJOIJXRBbIHYlnQH4KeB0afe+5VSiZsA+uTPvpMPZC6qCx5Aur5+7l6lUvksT+eoLSFDPuqhBrCWV1pgTBIN0QdNsxKMDjAystjvpxvSxQ3gcoZvEck+Czz3IsmKJhkHs2GJs/Kc89JLoE6TqJOIJDhSXUBtgEui/4iBPsi87sRZsra4iOzKlQX/ox99+5um1Yj6YdtvVYKkRzDxsdnKxNvWYtZ7vUjyDKBxkfdnWxc8GxDwAvoSdgltyPE6jL8OryVD3CX9ahhqp9sNO5XKwQzsKpWiZhzHN6wNdqzlACS8hzWGR4Z2fvXhRo4BdEpCApmKvJ9sD+wf1ta29lqt+d4wIChE8nlAAvf2zBQMvwdxXsAsiRcAzOz7SgHoeq8uiW1IS5D/aDBo/5eZmcEuUM9OvHnlOzs9n+PPBwAGALbv3Lm41WhkN72Pxpwr/5WlkYQyCAupjq99cxebO08+fz4wV4An0IXUhHAH9L+Tc/9N6i5ywrYbQIe8fKAu4uPjP98BsAPg5vb22zCByjSmRooARgGMMm9yqAAsQayQmJFhJaTZnZmZvhFF3QR4vpbez6VItlr/bowsTW7vRVMB/Q/gzSsgzhliKvd/pJcQkxgAugfyhuBv0OCqgb8zM1MdAC0H/PLA3qa7u3ClUhBXKlHbGLtoBOPAJqATAE4KmCEwDmIcYgVUIBXR5VNC3nOdL29bAJqAtgmsQliV93dkeMM5bUaR7XVW++n48X841EjNBdkWEFwj5CTTBpFCGgAYIVmXEJCoApow5Gkv/SDOIl8dPb/caiWr778/v3br1oK/ePHZHyr2XIokMDYG6AULvgTxFQmvQDgvoEayAsCT6EnaI7FC+j+A2ftwfjF1/h7gBsM36YHdHHNzr2YLC2s6dmzVR9HYIsmdKAqXJJ0SzSkIZ2F0HsILgDgU8wBFhcLTgJOQ5C9d3PXCLWN4C17LtFwWtW7od4xp7TSb3f6+g88hno9CH2wByIxxTREJRUNDeI/jw+6cioQa8jTPWUMjAKMQP3ayPHbs2Fa5/GqWF3kUIvlMkHcPzNuVlShwxh8JjZmlzL/KPR9xDsCJ/V1GCQMSuyA2QC1S+qN8/EGjsbK+sJBkk5MLBz5xjnzPI484UgA9AGvS2+W9vWw9jc16GJoWvBzJikCRrHsvT+6XC+3XVRbGvo+PL8+cAeBAOOa/Z49ER9IiiU8y5z4J6JdIszQ+/h+3H/WZ7i+933//b+6dP38komUFDhENDIE6oBLJSEJlmK8sAzxCGljLVhTVl0ZGzvUXF4/0n3X3oOdGJFutiyOZrR2pNXRE3sx5z1eR5yCnAdQAStLAGPQBNAlcg3AN4jXneTuO0VlZ2XW3bl19hLmYyA0GcbtSCdZIeu8x8F7rJI5BOELwCIQJGI5DGs8Fk1Z6fn7XJ4v8JUvASeqQaHqvHRCbJO8JuueBOySXg8iuKAm3B4O9+HGecblcyZzL7hnDPxImgdjPhZ09AA2SDVABwZoEQTjvgY61UTgyMr5ENpb1/vwqbp33uPj1Be5PM8/Nw1QuV+r9BGcJ84qheRnUy8M6yDLJsgQZk+82glgV8Ecn9y8MdL0Xd5rLt9c6//k/X82GnQePhEuXfuYuXXp7t9XqDkql0q6E9SCI/pgk7jgMzxqDM97rLMUzICpeKOVJ+CKQfEyIRAYhA7gjaRnCkqRFIVuU0sUo4m6aas8gag/STjw9vflYo7C5uctZq3VxQy7q+SBsBYIDaEWBeW6+BjASVQdQAnGOQgDaaQnvuzhLNsJ0q13/MJvNV0HPnEg+00+TdNGurvZL1epU5AxeNDLzhP8RwBcAniV5FtDQzJQxpDUAqwBuAPiNMf6fRka6S8CtDFg47DzRN1wLCFw0wCe22XzjSBiG55zjeQCzNJwV9CLBuogaxSqgEECY5y2LNseD5X4boQfkAaQSMmM4kNQ3ZE/CCqDr3uOG5G9K8a1e77/c2t0ddXNzV7MnsXtlaenvxkcnSq/D4wck5wB+j8D3vMeYMfsbhdwD1IK0I/n/Kvl/Mib5rbVJu14P2uTl/uO+joPmWY8kK/X61DFjdIziS/KaozWzEI7mPdIAwBhQX9Ie6D+T9EcDfCrhehy73c8+u5XdurXgf/KTx/uGJCHpsgC4iYnvdeK4vuZ9kGYZd7zXCqhPBUxRmAYwJWmSNBOAGhKivNPimf+9Hw15uJ56KSPRg9DM2wn9FoQtL2wBukdyjeS65De9V2tjYyWbn8eBbvgdJEGwF2eDibUwtBZSLDIZZriPCxwHNAEpQu4xYGnsC5IZOJmKEN3q99Nb0qsbwJz7S73lTxvP9EOz0SlXa8aczLx/zRjzMqxeJvCigHzpkBMD2DPUBohrMvoXC31ijHbGxm7uTE0tZN+lUPww2I8+pDvdUunVdG+v28yyaCUMbdU51AB7WkanJZym4TkAjmQAQcjHRTzmK3hGECAoIzEgsSPhjjyWBLNojFsyxi+RbGVZ3LXWdrwfxJ3OZvyjHyH7/AhPHsePV2Kgv9rplHecCffovDwYgRBES3AMVETQSKgAeIEGZcJOyrEUG+7tbZxszswAwLNjiPHMiaR00W5uouJ9uWodTjvoRYFz8pwFeFrANCADIJPQI3VPwl0Y3nYe15zMjbS3tdRqVbLLl3/zSHOQDwq5kAILKYCuhB1g3gIjdm/vZNv7aI/ALuQ7omnLqykwLxQWqiAiApGEiEYBwTDf+Rf3j/44r+3J4P5yGiRS75WRSEkkAhJIMYA2YdoENkG/JGgJwJKULUtueWcn6548uZk+TSNbh8XrHQCd9fZPUQrDEQolOjpBkFAhUFeem6wKOoK8XKhqrNnNUrbC8Fiyva2du3d/uvPuu3/ffxbcg565B+LOnYuV0dHaSe/9SdLMiub7JF4bDkGaADAhIcH9sgx9DOIPgrsKx9s9H99urX20MTf3dCwZhu5CBgDb7f9hbDAojRvjx43BpLXBhIcmDTjhoUnCTJCYyJfibAAaFdRgXm9pcrEsRBJ5rnFfKNuA9kC04dFEXgjeBLQNYBuG23JqIuB2SDXjOG2l6WZrZWU7mZ9/ep1zpIv1vbh2zEjHXMqXJPN9iN8ndRTgFHIP1B6ovsQ9QZ8K+hTEp96567F31/vN5ubKSt+9mXelPdHP0V/imYska7XxiPRHjcGrguYs+ZKkl7zuJ58NySRv8OeOPG56uoVqSb/N2O/4HXRee+1qAlx93JfyQAxF3AHA++9/tjszc75bLo+sW9sO4xhRFIXVzAQzBuEMiePO+TPW8rSk4/ltyypIA4BP8X184JD0ALz3vpe3pGLDGCzDa1nSisi1wSBdDwLbLJVsUq93EmA8rdW6GfCr7OjRp1Mcv0B/tNRdAXBvNy73aEgQJXl4EkOjaJUghIDKBD3JUUmTlpbVSJtRo74DALn/weO9mIfhmRBJCabZ/B/r5XKpnqbxMQ/zEsBXkecfTwgYo0EkIRPQEbROaBkGy/L+qpjdbjY/3Wi1+tnc3NWnZnn0p/zoR/eX4fvw+vW3orGxyT5t0pYJ9kDsOccmiTUA04SmAdUkVgRUCEQAIlL5kpwc7pLDDouKn3ILN4mgA+QFZgBSQGm+jEYydOWJSfQFDGiwDWBTwqYnVo3hKsR1yG9FUbL17//95falS8+eK85w6d0H0N/a+p/XgsDf9LRhHmBABEoSKyAqzC3WJiQF+ewSbMvb3SiqR9Wq3bxy5cLm01xw/kyIJPCOtTaeTlOdAfiCxNcgvEzylIQxACGkTEAXQMcAt73wEYCPYMySyczG2hrSW7fm/Nzc1WfpZteHH9azN9+MOmna96WS6dMHLQT+jmRGoWxUwqihbYB+jOA4hAaAhoSGyFFQoxDrEkrDAsynXCQpUBmkhLkItAHsQdoDuENol2QLwg6NWl5ok36PBm067tFwL0jRrgS9LsY7g/feg3/vvcd9TYcL6dpkeUmZ7xurWHkRZQDiCIAjAMcBlJjnvo8CeHloGD1WGan+4Y03ap3hi+epfLaeCZFcWWkF1erIEWv1EmC/b6mXPPFSHiXRSLISYwBdAS1Ri9aaDwOjX1ervgds9YdR2OO+lAPnJz+57CR0Ll9Gb3r6wvaFC9MG2DTAdLC3hyhOEAWV8pQhj3rYowY8CugohaPwmgHpQBrKE0DwtKexmY9IyAwxkNQGuAmPTUOuk1iDwZqENSlbz6xdi1xnkKZIut2V5OTJMQ/c2/dn1NOab/y2TGcr4zcAABSpSURBVEz8Hx1gvg+MrPR2z8QpjYVMBZIHWQM1AbCcWwsqUt4mO+WIUSrrpKm9dfky9qSn0wzjqRZJ6Z1wY6MfjYyEDe/9Med4HtQLAo5CGBFgh2a5XVIbgG5LWrTAxxSX2+1sd3V1K/vww/pTu8R+ED7PW165/3cSeP36fDw5uW2rel3ONpyNfN9AuwQ3rbiSRwjD6JKoyaNG+DJoQuZL8BBSSIMA2q/DVEDCDs03rCBL0IiyvL859G36zPc3ULS/S+pJeAnDJgC4/T/Mnb0dgAxEJiAlkSKfWZ3ms6sZk+rllQ1oA9rxxI7AFuS3s1hNa7ldKtnt/t7d5sRMIwUuZxMTz4cgfhVfNO7t9d7ZRJLeBGlI9QE55UVRNZFVgB5AV9IWiU3vTMc5m33yCfSTn/z5sX+hi/ZVwDYAW0YcDFZKoTGBGRkJJYVybs+Nj/dTYC0dnsMjF9qnWiQ3EZTsiEYSYRowJ2BwDsK54dCuCEAGqJePXMCyxI8s9UGWcdkYc3dmppLMzNT97OzBmJo+TeTF6QtDoXmt3QaztJ+1AxPes5mrOGcr3vuKsSh7mYqU1eBRA00N8nVP1g2ZPxhiVfBVEhVCFQAl71Um8xnPMnmec1jMHgAISJg8yn+Q0FQi4UQ4CJnADFQKMIFXQjKWEIN+AGBAsi+xb4ievO9J6gGmTapDskOi6716AdRLZWLjObDG9b3L+qVa2HMu7vf7O/2Vle1kZuZXT/XO7EEzGLR2TRLeYhDtikpojGgIEUchHVUerG8SukHoRmDNPTMTxO+999UvmTdudIKJCZTSqFwOsnql0TBlkylSSk8lPqqFcbcbdGu1Shc4n+T/18H6bH4TT7VIltudUhxHo6xwygsnSJ0jeRaSkWQA9iX0YbADrzsgPkqSwa+dC3dnZioJ+bMDd/N5mvh8ufgPPeQlUV+J9K7Z2vqwJpVqZGU0iqIJ5zRJy3FCY4DGDM2o974BcBRSzZI1ATUBVQgVGJTzZD+AfCTGt1i3D1sAPRypBFQ8HKnRJ9mTRw9UFzIdA7TlfZsGeyR2SO04h50g0HaaqimxZW3cbTTSLnk5eagv8DlkYuLyLoBdCbd3d/9XGcvAOZVBGJCjAEKCm5K7mXnclHFbU8DXfs8jI1PBbpZVqpY1IBp1TqOSr8gik7XOi73EI2ivZ57c1dZWA8Cj7Vp6pCL57rswFy5cMCdPVmy5XK8ZU66XSrZqDEJjFEUM7k8HlHwWe5NY6+J2lvadVbe98rvu1atX3b7R52BQj6vV3m6SIAoCc90LE6R6IsbkNZ7/M29C/iYsrmaZlsNg0NvZ2c1mZurPXfT43XlPU1Nvp61Wtx9FBs7Jk2ZA+h3vWZVUM8ZVjDEVShUalrLMl0mWDBWJjABFEoPcLJhB3gF0f/lNk2+LfkE4h54zwyjSS95aZvkGHDMSKcBEzifGmJhCTGogYWAN+jLoG4Oe965njO/FsenEcdrx3vXCcDf58MOk+P0fAhLa2Um3geA64BxlNgDeIU0o6WNBN+iwXg7M3iefwEkXLYaVEzs7tXGSEwAmADZC2QaEUYkVWpbz+8V4ZPLe2zgAO2Gt3oEf2Tt1Sru722/vpop3SqVBs15fbh32MvyRZuH/UReC0sp0OF2NwoYLZxC4mZB2yhhTc1Ld5vVXMLltWSyi7Rzastqy4r319e3Nl14qxQAcednt5yTr9ayepqVXSLwsmhcpnBFwhlAHwPueWvBwt23k1sfKrXXglymes2FGD8vwJrdAP9jZmYqCgGEcu8jaLDDGhGnKsGQiS7ogy1wQRYHNnA8cYQPQOMrmEyANSRoHZ5zzBqQJYAg4A5gv3o8eMF6SB4yslQc0/HevPCdpvURnrcmAzAXeZlLqJJcptJn3SqPIp9771LksTZI47XT20u3ttpuff7yGJc8CzebFBlBuZJmbKJWioySOAowkLJFcBLKtXk+DmZnz/cXF/zeanDxWd65UB/w5Mpj1wIvMhXIc0BiAAETAvCMOACUoIxiTiCE0Ja1RWvPAohTfyrK1W7u7K+ns7I2MxKEsww9dJCXw8mWY6Wnwtdf+tlIuNypdV6qVrDsNzzMSThrDBqAxAhUMkxoCeqJaMKZJYJVGy46DOzZVt9cL+r/+9d8PPvkEeu896P3354MX5n543Kf+RGBwxju9QvEVUh3v9Wty8Osk2diYnp5OiiXWk8W778L82387bycnt20QHLt/P+7u7rrNzav+zTfv3/iFoD2h/OIXF+1b/x0mFJQmjFVkvG1u9/vNU6cu9999F2ZuDvzX//rvRsfGMJVlZhrWvkbYNwzxBsBJ5GObx7/m8MMokY7QZm4955cI/EHMfp9l3Y+sjbutVrd/7tzh1GIeukjeuXOxMjaGunPhiDGloySOe2+Pe7hpCUcITJCogtwvZM73yqREZJdgF0BT3m9K2AwC3pV4N03Tu0FQ67Va/f5vf9tN/82/qYwN5MdLYTjpY52Q4XEjxd5nnyZJ91q7Pdgdtkg90zvZTxv7L9GLF0Fg/gv34/NVZvM0I4FbW39bR3e0bsIssJnpNE7XO8BnajZPVJ1LqlFUPeHJFwnOQjhHmjMAzpKoS6gDqH3t0XOR9BDaymcDbQFaBHCT1E0Si865pUbj6gpw3h90O/Gh5yTr9VopjjFZKrkZ5/QKaV4V9CphaoDq+UwZ5bueeUfHEDrm3RAZhJ4xpg2gLeCP3vuPFdAN0Gn6xsBfvHg5Bt7qpM2J1JhsT3SbyUA3vIdLU7XIoP3hh7/MLl4sHrgnjXyXff93WfjiS7tIhzwlkND77x8dzM+3so2Nspk4PkiBnzng7UjyI0E1mnAZXrDEvwL4IxDT8mqQGJUYkgj/fJ7klz9BgiVVhWBAjMhzhMS0HM8J/rfOK9nYmLzXbney2dmDNf89lEgy37m8YIGK3d2dOp6b3NoXSL4O4AcAXxcVQAzxAEJNIM3rHRlL+hjA+558P3W4E8gv37790fqtW+f9xaF9/H50AgDPwzS3goInkaYuNtCtnIE3Zyj+gMCPAfPXpOqft7h+567ujrzaJPYAXfFeVwD3z0HA7sjIZof85YGNxTikSPJiuLc3WncuqYdhcM57vkbidQ+chThDIiRohqUg34jybH+Ql4/wKIE5A9VCy4/hZE6d+l5y7pzpA+/0gZ+lX4xOCoEsKHi0/OIXsOfPzxu0yg3SnIfhGwRfpuExeUT5Bt5DG6qENKjkrbI8QcuXQNNzjndW22N3kPvEHgiHIpIbG+WwVHKj1tppOZwX9DrAHxtizEs1gSHyL+kB57HICAhAWglHBdRAnjaSEW3b2mDLe+2srq4ODQsKcSwoeBzkq8h5A5wPNlq+ESI4Z8B5D7xgPMZz4xR+wb/0O39SAKAqoCzopMCOtfAentWw1AKwdRDXAxySWUGlEpWMwTSAFzzMi4A5B/C0xCMg6sC3DbXJYcN8YAzqxmCG5DkA5w10PjTh2YoNpuq+Uj6M6ykoKHhQLppm8+XK5matUaKdInGchmcIHAfR0NC7dPhMP4RQ0gKMAJYJM2mNOS3Pl0V7XJmtv/suHrCb65s5FJEMQ18zJjgl8YekXhZ1RFCgh3575G8qCQZSAHAKBi8K+qGz9nQ4Wf+aHbKCgoJHwY0bnaBSwWgUZceNsScITMKjRiICYKGH14CvoA5phsAZwh+R0pG3374QARfsQQjlYYgkez3VMp+dAvm6gJcITA/zEAeAmI9fkBX8NITv0fCHRv60c7Z+MJ9RUFDwXZidPWX7/aDhvTnunE4amgkAVYjhl6tXDhLVJMwQOkOPI9ZE9Xr9fLi4eDYA3n1okTywnKQE3rjxVtRonAvDsN/wub37URKTw6FBBzQaYP8YAsmahCMkMu8xjTgZ0R9ejfCUjF4oKHjW2NrKbLXKapbZCUmTyIfu5VEkgMMpqMnbXL2HEzACYQTVpN6wcW8Ba/tuUd+ZA4wkL9ipqZmKtc1x5HNVGgBGhgIZPnyi9isgSiBGBUzCYEzA6E7tr6pYQYTLF59yc9iCgqcPa9vGe1UMfCPXAA0DpMMjz24SuQWAKVlqhK7ayKJaZRLJQ0evB3byN25UbBaZasZo3IETIBok6iTLJA+n1EgsARgFMOk9x43FSCno1naytITztwqRLCh4xBgTGu9NBWBDucP9oYukJCp3/rKCLzunUShtRDaoVOAeWiQPTLzK5boJU1My5aDmHeqAKcsrwKGF2fmrY3jcgFQp87aGcqWWtIMMjSP9A/7AgoKCb4CsEE4GFlZQsO8ZeriDwO6n4AjAGEvjvbWIaUx78OTkJMOwbLIsKwVAPXf1cSXmgfBBfcRfQBQQGeOrsfP1oKE+JupFJFlQ8Ljwuf3do+4DNgC8E+k8YQ5mn+jAhGTGDFg2PjJCTU41itHB7Wh/EySIUGTVllALgqC0uXlYO2kFBQVPKt6D8GIAgIl7suokNwEAToA8DHxuBXdQR/9mDCnvIUB+ICs/XS52tgsKHjHeOy+vWEAbQhtATOiQA0rtmzN7UDGpTj/ttTM7GExPP7zH5IFuqCQwCqy8vLxoHqmLi7wUGLostV5pKgyKQLKg4FHjferBaOC82sagDWDwKFbd3B/xAcT0akeOu93U9oGHF8kDiyS9LysM4SSfAcoAuX2F//zPQfL5cSUJBk5iVrZBWipVnHOtIpIsKHjEOJd4Y0zfWu4A2FE+29wdng4AuQjLAUoB9R18h1Xskc0nSyRnZqwLgqgHsAXDFoU+Dv0NQuUjLOkkDLx37Yx+N46Tfq/nHulEtYKCAmB6upaRftf7dFXSXQM1AfQJZDg0PWAP5JaEuwC2SLWXlraS3//eOeDyQ4vygS23P/mk66fOlPs2CXdMiF1D9A87zB4u5z2ADGTfBmZ3ZKSzkyTxYHa2X4hkQcEjZzEz5vTuAAEigzGJTYIDURnyAXAHvpkrqC+vbVJ3QWxlses0m7+K33orn9H+sMc/sBOem4MLEz/oItkD010AbQA9EjHAwxKsTMIAQIdAm0R7dbXf3dgoxZcuXSlcyAsKHjGXLl3x29umG7pky0sbAO8B2CK4A2i4ujyApXe+SeNAZKB2jcVdGtykwXqpFLTffBPZQY3+OEBVv6y9ibuJs3EP8LseflvQmvPaBtAdzk4+UCR1AK0bo9vyfnPgsm6rdSubm4O7dKno2y4oeNRcugRtb3/ser0kVeJ3h7NoPpBwFcAGyYOZMSV4eSSSegLXvMe1zOlDn2optr59IJ8x5MCW2yS8dCVZuDXvGmdf3Q1LdlPSGsEqCUqqH0JheYfUuheWYPy9ErLO3NzVFLhamO4WFDwG8qkACxmw4DY6P91RxkVrVTIyzhAleR0nGT6sbSKJDEBMsi/5Ne90zWX6IM6yZpCmT6ZIArlQAgt+e/v1Tua0QaMbBEIAFmBj6Cln9FCWSXIAnCRHYssLS5Q+I7EehOVuIY4FBY+X4TOoe/cGvdKoXUtSklQIacQYjgsah1AFUMF9A+6vW9V+aUnuAGQCUgG7NGgKaEK4YS1uBUF7eTAI4unpzQMdLXsoxhP9vuuVR3CHYkQaD5kIwBEJNUDR0GX8u5IB6IPsC7prgGvO62PSraRpr3tAl1BQUPCQ7O520qOV+o68kZEPQQReigGcBngC1AkJpTx4YvRNx5OQ0GCP4J6kO4Juy7tFQdfo3d0k6Q7abZtNTx/sfsShiOSJE6a72cVyMnDtcmiNIaYpzAIIlLcqfuMX8nVITEH1COwCXJHSa+Vy+lGauu69e51CJAsKnhBmZ3+ZAO/s1JG0+33G2SAbwNotCXMkMgGNPOp8YE1ICO0I2jDQpwJ/R/jfAa4Jg9Z/+A+/6l+6dPCjiA9ppOxFC/RLu7ujJWPCVwH714D5a0DHJE0pN+SNSEaSvvDlfNEr5PMwm2Si/A0UC9qEsC5ondS/+Cz7b4PBpx+1Wv1sbu7qge1oFRQUHBybm387EoaNKWZ+CmEw6z1focHLAEcBjkKok7AArO4vvSlATlLGfIm9Q2JdxIaozwhdDdD742AQDzY2SvFrr11ODuPcDyWSvHTpsi5deidtt1saGQnXAf8RgC6gFwCcH/4ZkzBOMgSAr0nk7r8VegS3AWwTuA3qpqdugrxtTLi+tob01q05Pzd3tchHFhQ8gezspEm5PNitVm1mvM28MU0DXQcwbsAxEGMAShLKpEKP3IdBUmLJjve+C2BHMk1YNOV1L5G5Fw/KvXa7k83NlQ6tLvrQfczu3v2baqNxdKTXy0bD0Lxm4N8A+EMRJwx5XOARYF8kvxxJ5lEhReCeF5YJLEn+4zD0vyPbv09T2xsd3eyRVw40UVtQUHDwSBjO234r2Nysh91uGtRq9amSCSdhOCFhxBhfl1CWoQPkvVfPittIkia92bVR1q5O9drAXgogA664w96sPRzH8C9w/HgnAUw7y5IEKC3JMQIRE5zx0AyJCRIhgdD7z8+HRCbPBFQiYBvEKmHWSN6SdKfdvtGamellwI2DqbsqKCg4VD5Phf3SAUgAoNm8qFBh7OQ6xtpKIlVpFAHWS/DWcmCydC9x3AsU93aW+oPq1D/0H2UVy6GLJHDFLyy008nJEV+vn1wrl22MDGsZMAZhLMvUMMZUSVaHJUIwhpKQGOM7nuh67/cg7Bi6HdI3gay5svJRMjMDj0fv61lQUPDwCAC2tzuDiYlIURINECBEkA5LBiXAKsvSLEqSGP0o3ttEuhGtZScecZnfo7AN/7PPfPdd8J13/qYshZUKS9WoEjYEjHmZamApgPLe91OZlvdpa89We2Y8ic/i53FRB1lQ8MzzRV167M/74xBJAIA0HwLHwuVllWq1yaqEmrVhBAChjLxLk6CWdQZVdfcQJmexmJFXiqV1QUHBI+URLLe/jgW3sDCPRuOIq1T6aRT1eqY7aoH81aGMru1tslWN0zkk7hKuPPY3SkFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQUFBQcGTzf8PYrKp23D/5ucAAAAASUVORK5CYII=
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAUkAAAFJCAYAAAAWit+oAAAACXBIWXMAAAsSAAALEgHS3X78AAAgAElEQVR4nOzd2Y9cV34n+O/3nHtv7Lknk7uSqyRSKtlWlcpbD1hotBtGe/yWRg/a5a7xABoMBpj+EyS+z3sDBYzRsAfdgPgyaHhQ8MBA0fA03NMu2uWSqCpJFPctmXtmRMZy7znfeYgkRVJUaiMzgszfp6QCxYyIvJEZ8Y2z/g5gjDHGGGOMMcYYY4wxxhhjjDHGGGOMMcYYY4wxxhhjjDHGGGOMMcYYY4wxxhhjjDHGGGOMMcYYY4wxxhhjjDHGGGOMMcYYY4wxxhhjjDHGGGOMMcYYY4wxxhhjjDHGGGOMMcYYY4wxxhhjjDHGGGOMMcYYY4wxxhhjjDHGGGOMMcYYY4wxxuwEDvoCzO4iwQFw8/i9UrGxt1xOUE7oS6FAmZSHvJADhQ/dPISuT2udjd5G5x/v9DoXz50rzp6FAGjQz8PsHn7QF2B2DwkE3kyA2RTNw/Us8+M+ZtOIbp+DO+jo9ilij0vcFOXrqXflUDCtI1Gl2c337NkTZmev4m/+xkLS7BxrSZpnToK7gDf9YRwtcdGPkBxhVp5I4Sbh0kkhjkfFcYklIApwEcAaItYErQhYcNEtSPlq03ebl0dvbyxgWn+EcxG0wDTPloWkeeZu3fqD6qar1GppeSp1ybEs9UcF7AEwAXJcQhVABUACQAAlqUOi7RyaEpcALUXgegzFpTaan6Qj5e4vcaP7A54vBvvszIsuGfQFmBdfrM+UR+RHEsSD8Ph1Cb8pYh/EcYijoAjQQdr60BYIRIJRET1AK1FaceQvAM96TO/6DfJMo1IAsJA0z5SFpHkm+hM0b/rbt/elSdQhMj8h7192wGk5N0toUkQdQu1Bh4aPdmy2+tEFgBId61Ho0rMlX0Xh4tXl9sTVT/T7CzfRDtaiNM+KTdyYZ+Ldd99OLl0arQCVRqXi30hc8juOfItwRwDtBVGDmOErvAZJUhEpHTJJowD2EYwi1xttbjSWnBqNj4NN6JhnwcYkzTNxS39QzTbrY0F+Momlf+Xo/xXB1wWVCGYA3Dd42FxCl1QH1P8dhZ/4NP+Z62m10WivkufC034exnyTF6oxX0iCk+Crq1N7MlTfKKHyewnd6xCnBWQEPaBv+OEsRyqVUFbES5S+G7vpb/Xkji4vN2vvvQffX2ZkzNNjY5LmKTvjgIp3WTodFH+NwA9E7HPEFIB0azH5N+UAJCQc4A4BgogqkfZCmLlx6tRcBzhni83NU2UhaZ4a6UyysXFyrNMJY6UKjlF8GY6vQqiBqEr3X2/ftLFHAvCAHKRJQQmJCOGWL+H6vqNZsrj4h2vAf954Ws/JGAtJ8xQdKkWPw0nFnQzErwE8TKEBIpWe8iQhWaI4AmAvEU96l60rpnVXL38CwELSPDUWkuapWV/PSiIOE+57BE4DOiSg0e/8ik95nrAEIkN/t+MrIUYfAaeCKwCuPc1vZHY3C0nzrS0vvz3KShjr5jycAK/A6QSAA5BGAW6NQT7NgCQfPCBRpjgNInhi1cV4b3X1365679bv3r27fuLET7pP8RubXchC0nxrPdeeKIfsaCK9CupViMcAzAisPuupZgKpgEmQZUIbEVwSk43IcH1yst4DYCFpvhULSfONSOB5nPHTuOeSdjYdA0+C7nUSxyUcBDGyE2txJKQgRgGMAmgKWIXQRoBUzlakMy3gfCQRd+ByzAvIQtJ8I1ev/qj0aiWMuMrBEedxHJGnQL0KcIYO6SAW4QgcI3EcZBKBEDpu/UZrb6xM/emG9GdNWsUg8w3YYnLzjYyM5FmS+Ik0ZocYcJzQqwRegTADKRvENbHfojxOh+868FSS8XDdZ1NqxRrwji0yN9+ItSTN1yKdSYCK73TSiV7PHYnEqyJfduABgePof/AOJJAklECWJJRBHIkRrzufRraVLXcvbUpzHeBUQZ61rrf5yiwkzVcmgfPzh0rVmUoll/aTeo3kb5M4LHECgPvmWw6fKg/wgCfejHTlrCwoVJbW1kZWR0eXN2GTOeZrsJA0X9k5zLl/WclKm2v5SNn7/XI4DfGfAaoASjEkBVNIOAEHIExSqkVpmYiXQsjzhYXFHBaS5muwkDRfqr/f+h0HLFc3k/aRSkxOSPg1Eof6VX2QgHAShyIk1S/em4AoOXAS5Cuia5LxIyQjH3/wwanrp0+fDuS5CNvnbb6E1ZM0X+rdd8/42yhlvXZrFEy/I+G34fgGIl4CMYn+h637XNXcgeJWtXO4rW2RY1EsFONyqzK6sH6niYmJS9FqUJovM0QvajOsFvSHDddujAp+vyvSf076fw7gBKARAKPDFY6f0wWwDmAd5N8K8a/zovdfK6631mg01sgf54O+QDPcrLttvpAEd/48XFirT6dJeiw6/zLBl4E4A7AhsPQcLD30ACoSHBkPA/hO6pMQXfrJMlqfALCQNNuykDRP1C9ee8adOXPTr7eTqRiSV1HgeySOCZwB2HjaFSueDXkAFZIliIcc1Q1CooheqVW5iX4r05gvZCFpnugSfj8baY2NuXh0zIvH6XjCUccANwOqim9dG3Kn3K9BCU9oTOIh51xgxL2e4nyr9ad+cxMb09N/ZuXVzBNZSJonmlw5VM4y7cupoyBfJXlcwmFINfTPqHnuCKwBmkGEE7Do6Nd70aVJHVdhNSjNF9hVIdnvQs5tbcVcIHDyoWbQCi9dajJJZh783ezsDl/gU3T16md/brVacWFhIZ4/fz6ePYvtjzcQ+A7A5mJRq5MHPHk6RryqiGMgDwx9w3F7VYBVQVWSqzGqA8XonVrSmZvA+fBV9nf3l0T1j6kAZobiJ3L1oT8XmBcuAd1uXadPj289n5UInJMV+vj6huIX/MwI/CnO+IOo+CnMVGI7r6tI64qsKqrmXVImkZLKSKSRLiOQkvIhwJN8aG/7UM/gPoEkIQCKgpYUdVO9eHNjo9U+enR880mzuhK4sjI3ItVHQuaOZHJvCfhNALMgDgKcGcATeepIdCBcF+INgB844u8Zw8+cc6u12to6ea79pPtdufKj8tgYyr2eJn0pfYkOL5Eu2yooPOjXR3QOQVCU1FOBXIo959AJEZ000xqcX2FvbW1kZLwDrHTtdMmv5oVuSQrg1auzychInsFhLHHlPb0QZpLETwmadg6jgaxttS5qFGoAahJTR6YkPCAq4rMir8+PSLIHIBd4yTn+N6VFPjY2ujQ/3y7w5FldqlwfAXQgFY5LOgW57wCYAFEd/onsr0hIBE33J3MQIK1LXAVwY319JAfwuZCUwNVVlFHujXpWZr3H7yLinwmqb01gDaJYjD77g4IicgAFiabzbEmuCYe1JMFaCLqlHFdjb+R6s5mv3b3bDAAsJL+CFykk+d57cNPT4Guv/WElhNHK3bu+OjKS1pKKr/U6cU9K7E282wdiynlOR2GcUg1kDXA1EDX0gzIFkPXPZSFBPYchyQLQKoRVAqtyoQYXCSdi4tFbbs1ke6CeeXFG8idj1Gnn3FEBBwhUXpiABKD+jHc9CmUAbQcug2xFglkWmtKpJvBhIB8NkfX1Hktd71xFGeVG6bCXwJ6t1011IE9liyMLATmEAkJTQktCk+KqItacc1NwanjnGz3FhT2H9t+7s/E/ru2tF5vAX7StG/7FXpiQlOYcgGxlBZlUPZhW/AHC7Y3AlMRJn/oJ9OsNjgusgag5oCIg62+tUwYhA5kS8FtHn3JICjZ8fUQO8S6oT+H4AeCuZNC9aiVpXbzYfKwVOZeurKCi8mjDU0cg/YZP+Boi9gNKnrvPh6/GOcJHaUzkUQBJHhCKwNU8f2N9c/PNtvRZeJDQjRt5p1vG6ohPb0v4GMKkiOMQZomBhOQD/XWgSkC4rdMpU5BVCCOAOoqY2tpGesqRN4seb6YuuXF7kTeudX7r+nvv/V1vbg7Ram5+3gsTkgD82lpajjGvutQfjoV7g44vgzgguQOkRiRVBFYAEQ9C8P5gErn19/zsVfKcBiQARRUk7wbhQ+bxIhN3pVrbmAfOxddee/yNMJ6EsF7znd5ETLJjIN9E4GkBJYIv6tZV1/8g5JgiUxB7Aa0p4npE+Xa1GgSc6QLnH7SwDh0813kH6P4vzR/eKSX4CIVPIQnkKID9A3wuAOQeOtM8BaitPoIcnSTkAHIQbQCX4NynHrhYKivua5bmR06dCsCHdmb5EzyXIdnvHoLAXDLfLI+56EfX25xwKaa9K01T7hjIYwIOSZxy1KSACsCMYPrFj/x4Jj6XGbkBYt0RdyV85Jw+jImuCJ3lxwfqpTkPXPSrq709TGvHAtwJB73ihD2gagQdoCHbk/00fPZ8CCRwqEBISLxEn7yBIMToPwVmP5XebAEXAokIQmcB/a/qbPqev5PTJSRqFMZA1QnWJTV2cIkUn/jHBzUZ+n+nfuylAAKgEsQDBBykxEWXNcaONOrjR24sLLx1+733/sPCxYvQ2bPW/b7vuQxJAATe9Fev5tWxsZEDSHgkFpyFcATEbCQmQIwDGCVUVv+QqES7oxL7uiKuC7jkvT4U4q+y6G7Uamo+fKN33oG7erWWxni6NDbt9hHuDUe+ReEIHcfwoKX1wnMQUgAewuFIRXrVixj8/HxYXlw8Wpw+/WYX+PGD0JjGeHe9E+4xuE0moSZwXECDwgGAJfaPuh0yIkBPEKAmAZZFjMC5SQfOOuofkHX//nvfm12dm5st3n33vKzr3fdctRC2WpC4ffsPKo3GRKXbxaRLk9fB5HVCr4J8GcRJ9sPfY3eEIrbaChFglPQrEL9AiL+IiP/QceEfD478+dLn73Em2dg4PBqjRuBLb4nuXwL4AYQ6gAaA0k4/i8HTBogNCVeF+FeI4f+Jvc51Kazv2XOu+aR7LG/8T69JeEvid73jK4JeJTiFBzPew9sKJ9QBuQrFNYDnpfBXCfP/0umstaemSpu2RKjvuWlJSnBXcSYrlitZvTx5qFAy68ucpXgM1FEIB0VNElsz0rsIiVzCpqBNElckfSDo53C6mWyq8/Bttz5o3PXr+xu1MXfUkced+AaBwyDqAsoknHZhG0JAiogaqEkKxyP8Miu1WpGHTwE8MSSjz1dckX0Cot/wIusEIaEGqL7DT+FrEej7s/KkgFnS/XqhTEkydWURuAzbhQTgOQrJCxfe9EePTpdCLFV9lswS/D7ENwDsAzkjaQRgaaugwdas9O7ISgGFgCaJJUhXvdf7I43kHxYWVjozM+g8eus5B8An9VKdzh8V8JsReAWKLxEcAbhbutmfQyAF4SFMge5Y6hAgIsm4ikc3tTxQrGu1Xi8+yXNsKElqkGYiUO2P57KG4X4RevL+WD1eEpBLKDPzqLTiXVhIAngOQvI9wR/Fm27fxslROLcvhd8XI74D4DUArwIYgzRK3h8sv/+aHObX5tMgAQzoLyJeA3VNUVei8JEYrpP/x+KT79eottvFSIXxMOSPgXyFwizAied1T/bTQw/Aw7GKqH1BIokmqfmlzX99z1dc8yby1ms817t/j5mZv+gAczmQFOub/tNYcAqEAxUFNLYmCh2Gc+jn/gdiCmgKQKADYhHutHx+eWnp37SXJ5a7J/iTXX3cxXCHpMDv4UcpVlfLlSTZG0PpDRG/RvIYyCOQxiVUHLkLu4eUgB6BDsi7gC6GGH6WeP9R6MTlL7rX6ionCvhZ79wrBI4DOAByAkTZhun7CCQixkh6Qmsh54pjo6tWuHYgz64B6D10860JnaQdIq4hkQPQlZhQ3CegSiDDcIbkZ4gKhGmJwTkcTmP6UlIrdWY2/BJ2+ZlAQx2SArC8nGexXK7mud+XOL5B4l+QmFLECMkqef9Mkxe95fh5hHogmoi6G4WLyNt/02r2lvJ8pfVF98mBCe/dMQivgTgm4SCJBnbpz/BJJCUARyGMCsgd0XZegaB6pbgIYPX+bfsDkeeChHbo/OG1SmViMcDnUW6fpNfJrdbpkL/XtsYmKxRSkIdBvNTNtV6Eak/C8m6e6R7KX1y/CzCXXL6MyshkdsxFdyzx/rQUXyY5ocg6qQy4X4BiV725A6kgsQvymqKuSHpfobiysdFeK5Vie3YWxcN3uHLlR+VKJYyw7BqJdy9LeE3AKxT20jHrL6zfVT/DL8EH21AJNgJ0OAZGgC2H8kpTPwptuNYU/qz5UHhoairvLS/PM7jp+SThRTo2IB0B+RKBPQD8VgAP4Q+7/5wFZQBmAL3iHNqVLG68+y6uYxcvMh/SLsDbfnGxURrbN9pw3p9w9L9L4nedcycgjJIqY/ceYhZjRA5hU1HXAPy3SP29S9PLR47Ejf37mz3g/CNLN8bHe5Us8zMp/UkCrzriNTq8AmDP1hpB8wVE1R1xkMRpUC9HF4+215IDbGcj58+fefAaJKFz535SXLlyr82iNw8VH4QYfhoi3o9R8zGiF6WAhzd0DSGSCcE9El9l4AkoTr777juDvqyBGsqW5CKKclLnhBP2wbmTUfx1Kb4CsAKwiqEN92dPUg/EmqAFCZ8SeD9N44fsYRX4y87DhQokuAsX3vTtdjbqqzjkyVMAX6ZwjMRBazx+BWIZUAngCIE7ilhwHh0XO+HMmfqKhAhAJPRHf4QAXAjS0ZWlpXjZOb8Cr5qAvRKmHdnA8K/f9QAmHOjpNA9xHPgwkZDv1i73UIZkshonnXOvBuk1eLzq4KYFlkmku3X88T6SqwA+JfAxiI/yEO+0l9N1AJ2RkYdKZwluHj+sHHg5qWZK9junkxJ/A8QsgKFevzdc+q839gt9HHDkb1CxFEOKdnt6qVL509WLFze6wLmHJnPGC+dWmqEUo0flGor4ofNIIR6RVCa32xo7cA79axQixwLCyNpaWhsd/VFbauW7cYH5UIYkyYlId4rE7yDisIhpsH/i3aCvbfC0CuESGH+mgh+h6Nzev//mKnD+sQouc6xuVCod9cbg4gGJLxN4E9Ko+od4ma9M98/J2U/FcZA1Oix1Y/Jxs5XnU1PliEdmvH9c/PX4XPMofrl5tPf6Nca0TtGBKBHcL6A2oCfyFYggyoJSQWNOrBdFUr18uRXbbUTswhqUQxOS0plkdXW2Hkt5XfCzDDwq4CiIia1lFM/JwVPPRA6hCWIDwKd08SMp/qrw4c7UWHeDPP9goqbfxX7br6ygWjAccklyBOBrAI4AnAZRoo1Dfg33J1kEAFWQZVAHILwM4m4Skk80kl+RsLl1a92f8QYQbiyeXq6kvBIRE+c4QmEcRAdAA2BjUM/qiz10cBpRicK4Ej8zNlZ3taNFgUeXP+0KQxOSwKFSSMI+5tlhObwqaZbkDMAyh+o6B6Ir6C6A61Hxlyj0SQ/dqzWXb1y8+PiLdi45cuRGmZWZcV+4ExDfYn/R/WFRFYrDPiY2xESADuIIoJclOTLWQs+1L3yI+cuXEdFfN/mgRV/W6no7H7tZTpLgwJrAsoA2yZcgDGFIPoyZc3GMSvYjUVFZdy0AX7i87EU1NOGzvp6VvNNeQKcgvSy4lwDuGfR1Dc795fEUpI6AO0740AsXY+I/3t/4j9eedK/5+XLqXK0au5r03p0A+X2SxyDV0S9asSub4t/eg2U7BNQgcULiPtD3fMqrhw+f+dXoaCWXfvLIBMf09H/eALAh/en6ygYrIJL+Rh7WARzq32oozsj5PKkEcAyMByi30UvcwqAvaRAGHpL3TzBst2Otkyf7Qb1C8jDAkUFf2xBoCmpSuEnolwH4OYv4qZSvftEdSqVsigmPRfAVUicoTAKqgEh3366kZ4WODln/TCQdQsE3mbwUG5PF9ZWVuevSufXPzwTHPAD3XHAf+wQVCePqH7VYJVmVhq/qkkAPqiyhIcWK8y9sAeZtDUG3a84BzaQoVKPXXkeehHCY0JB3RZ49gS0C83K4EqFfhdD7eZ4Vl7rd5ZUvug8zP0m4UyS+D/GEwEkJVdk45NPkFFGWUI/iYXj8hk+S/y51pZNt+REA7p13Hn9vtfLN2LnH2P0oj/GjqHCV1G1JazE+8VC2wSM8gTKEhiPKrlsMvFE1CAMPyfn5cvnevbGxApgmuFfCQfXr8Q30zJABiiRyEl1SC4AuK+JX9Li0ubZ+/d//73+xeODAX24+fIef/vRMIv2wtr7+J5MO8RCcTiLyFIkD6E8QZP3iDUPYpXs+OfR7YSUHTFE87sg3vOPxepLtu337fxh/++0/KD98B/JcODz6H9eXlv5u3hf5NUZ9gqgPAdwktY7+6ZXhs2GWoeAopKQrx+iyR49Y3j0G/snQaKSjBfyBKH9UETMiquif0bErfyGkCokdAG1J10j+o2P4hXq8mSRp90ll9b/znQPV5eXkIDwPkniNwlEQMxLrGILf8YssQhVHTggMgo4J2b1y3TkU5VsS2o91u+Px45eKxcXvLvqE70OxBedbgKsCqPUPpGOGIRk33tqX6Sh550GEOBTXtdMG+gaSwOWmxjzc4QgdIzHD/hqy+we+D/LyBiKKgUAb4BqIq1Lxc+W9n6+vt5p///fpE5dfhJBWS6XkkIRfA3BaxBFSM/3akPK78ee4UwiWIaUQSo44poh1xyT3Jd8G5m5vLQXq37YfmEEaWQBazcXNcCWN1RqoWUD7IW6VLRsWogAPKomE90x25Qtp4K2MJPqRCBxyxEuAJkC3VX/vmf0+Hv5kLwC0AXUE9Cj1SDfY8SHFDQGLABei4i9jN9wCeqtF0c3n5v6vR1qR/cX1Z9ztdshckZQJlCnkJBfQX+oDWkDuAAJUV8IGEjoRlcBeGUAmzfWAc48t9P9xAcy1pqq13loLlyH8o/rd7QlAEwQH/r4EAAH3QFxXxDwc1kLo7bo1ksCAQ/JdgP8bOOqog/3y8Rwn4HdqUGbrhbkGYInAGpxbj1uLggeGWIbDTSrecpGXK7Vkvlq93J2evhAenzG9eHEuCVPldF9FGSg65wKEpSgUJO4O6insTgquv2W0g0gXxPTiRVRGR4GDB+d6j7copXPx/HkUr7/5o+vO+//qybuKOBCjDmhoDhLTMiKue4frKLjk0ser3O8OAwnJz46EPZUsO4wKPADxIIBRPfPqPgLACCASaEG6F4HroBYcsCRp/dl+/+05YKHIw7VIXZNP1sercY288MTWba1WczFrJWTFOcQC1KbkCgL3hmv8f3eIEPr/xJwApqbKiXMdf+HCZYfHtvNtfeAVS0v5bSVJM8rfQgyzUpwlOBzLgah1l7h5ws1nCZc2Nyu7svjuQELy4sW5dP9+VEolX/PARATGSTW2juPks31/U5CaAjYA3QDwPqn3QbeiyJZ3aD/L7/6lV+ewkRVaJlurnXa3c+FXt75wr+zs7NUCmMV8M6x66lrqXTsMSVdtNyti2HBZnPfdtfbUVJ6fP380AheeeNv1ibTn1jZb9axE56TMJ2sxDEcBjKjQSYX1osBG7nrrrVZnV3a3BzJgdffuD2vpSGncxTgpJn/ghP8ewBvYkaKkCiDuIOougA8j4v+bluLf5iFplmJRSGGgh7LH2Cm6XfTu3bvYW1jYE8+cOf+5bvZ9n7XI5xKgW2o2S2WgbIOQA1avhxxY7wKV7ufHIx91v5zdzEyW1GoHsyRJUjIZipUdEkNRtIter1zMzHRy4FRBnh3o+2MQBtLqKJV8GgIaIWjaOY1FssYH5zw/6/d4f5sf++cN36N4u5Fl18kfD3Ys8ok+3ParW28+bZXp6sFOt3vu9Ot/Xojoj48PtBdjnmwgn1jdbsgQw4jrl0Br7HR1bAI5gU3SbTrPHrBiA3jGmCcaSEsyGWFajkkjSNMCG9rBtWHsb2nIAbUhtAXkN2/u1Hc3xjxvBtKSrKLsI2MF0Ei/+IIS4P742jPubxMkWBe4V+SBCMxUJisTH9ybq/9Mbw/FgLkxZngMpCXZ6+UJkFTg0ABQFul3arZhq7r5KIAoYgORV3wsTc/UyjHMtwUMabEBY8xADCQkSfkIlUk0ts6ucTt3xJAooAYhhdCiNBsLHC+5otqrYaXV+tO1nboSY14MyUNnK/XUQldSoqqKuI5U9VjEPG8Wzan1fAkb4U1cCA8fWDfsBhKSOeETxJLEOsgStXO7bACAgBeREZgE+boDK0Fc90g2u5G7cleBMd+YopxzMUaJLikypT2CvQB1G07diLTtS9WlkebkUt1xdbH6xgbwZ8/NSowBtSRT399VoCqEkrjTZ2jTE3ICpijURJ0AUECIxPPzCWfMcKCiEOhQAK4HqBWhlqAWgA0QqzHisgpcVhFvbm4WktB8Xo6oHUhIZogsiBRwJZAJdvSYWG5NDhEEPIgygHGrA2HMNyZHBABBUg9gm8QmwE1CLQHr3ruRCE7ChX0jTG6ttP7k5kq7WGMX66OjP28Bp8OwHlc7mO52TqeEnkRKwIrBGvOc60+IEgQyAaSQEqhGaQzCFKBJ53BUcPcEdwsRNxnTT6PHpdXVt26OjbW6ErrDOFY5mO52Fumi9wJSQj4KjpaTxjyn7vfO4LRVsf1+P5qPVT0ksErwpoCbIBo+qp2HfGVlZVzj43M94NzOX/6XsGIIxpgdo37l9XH0B/83RWS+nO5VjJcXNxuf3r37w7WZmUqP/PHQLMUbWEhGiAQZra9tzK5BIJM0RrLiiFTgHkR/CNTfJWAz1FDMz7eBIVqvPKCQTOGcIIn9rBzMVRhjdlxCMgFQi0KFwJSIMQDrRYFlL+c4orsSOgA0DGOU1t02xgwEoQREmcIEwFc9vYfzkyiKf1pe/v2Nzc16LqE36FlvC0ljzIDQQyoL8A54VcR+ItYhbISYXq7X882LF9OAx6q67zQLSWPMoNxfNgQRIxRKAA/CuSNJefKEV3Jn377Nu+jXSh0YC0ljzEARYL+mrJzASVBHoGS552KiMjcADPTcKQtJY8xAqV+y0QFMQU1AnBXQ88C686VrEjjILYwWksaY4SFWCO0hWcSIK3nExMLC3F0JPeBcPoiwHIoDh4wxBgBIVSTMKOo4yAOMmKhMl6sLQIYBHQbnwM0AAB4ASURBVFxoIWmMGRoSUhB1kJMAJxU41dlIx0OzXjl//sxA8sq628aYIUKScCSSKDR86qZBzaRQPn1meiAFsS0kjTFDRJTgJVDSCGKcEbXXkWunUbOWpDFmt3tQyoHOoQxxLCJMxIjqbWQWksYYc5+EsqAxiOOerKQLKwMJSZu4McYMJQIlSCMARulQ5nRjILPb1pI0xgwhUUJKujKgSgxIHbq2BMgYYx4gE0pliRUSKVdqFpLGGPMZuf4RLzENgCd7FpLGGHOfAMKRAh2hgZXmtpA0xgwlAoBAOsAP8DosJI0xQ0kAAREgwwCPU7WQNMaYbVhIGmPMNiwkjTFmGxaSxhizDQtJY4zZhoWkMcZsw0LSGGO2YSFpjDHbsJA0xphtWEgaY8w2LCSNMWYbFpLGGLMNC0ljjNmGhaQxxmzDQtIYY7ZhIWmMMduwkDTGmG1YSBpjzDYsJI0xZhsWksYYsw0LSWOM2YaFpDHGbCMZ9AUY8/RJD/1HBFCAKCAGQAFAACCCcTDXZ74cBWiB4JKC1kl2pJa+/H5Pn4WkeUFRAKKEDqg1RawB2nDEhqSWhJ6juoALg75S8yQSiDXFuEbqJqXbzfZ4PogrsZA0LygJQCTRFrhI6JageUn3BCx6pybJFqRccANpoZjtSBI6Ub4jYM0F3Nm/HxaSxnxLEVAQmBNYBLBI6q6kW/S4CXARUcuIccVBm94lm4IrBvLOM9sSJMEXCZEXRa9Dp41z51oDGR6xkDQvDFIFhC4RWwI/hvB+BC8r6F4oMA+GVhFCu+JdO0+Zu1jkLcBakUNI6qqqIgpFBLJibGy5Ozf3EwtJY76+zyZpBBSAOgTWhPhxhP622+l92CiFpUbjPy2TsIka87VZSJoXQQQoSYsUPwX1CYLeR1HcSmJY7XSKTqNhLUbzzVhImucchX6XOVBYAPEByf8PjlcrleRmterWgDsFaSFpvhkLSfO8iwDagDpwuAPhkwC9r7yzvLzWW6nVznWedKef/vRMcvBgxZfL9QcbKpwb545dtdlWjCs6eLAmYF7AvQhciCQGslzLQtI81wQVJFcUuAjghhTvxLyz4H1vc37+cvGk+7z33px/4w3UYqzUvXcpmWyFo7eQHBqjWllxIcbpUCrt7dXrpzalv2gPYlzZQtI81yjkAFZIXSd0PTDcnpr6P+8B0He/++Q31NGjl10zvFGrV9xkCK6SIpKMBAoLyaERBcScTPJ2O25KhRqNuQ5wbsevxELSPOdYAFgjcTsICyx88/FumQQC4ELrR3tSYK8DZwBORnEy8SgLjgIJ0EJyaHhFxlYiNb3nIln7FKhsADvf5baQNM83qpCwDuKOAxZdVZsPf1kCz58/4w8evOnH9/Al55K3BH4HwCiJUQmlrQd68H9mKIhyy5FagnAFVHth4e4NAN2dvhALSfOcY+Ec1gM1z4DlIvLxiRqeOVPxi4unMjoeDOJbdDgDqQ6xBiAdxFWbLyURdwHchWNJwJU0rQ0krywkzXNNkBRROIdOkOtJj3bHLl6cS0YPoeaTtFGVG4vQCMSawIyQs8aj+TJWT9I85yg65LFAN8bQK8f2IyE5ehq+mo5WE2Tjchgj0QBUI5DBXv/mK7CWpHmuEZCE6DKfM7JoKnlk0Xg6X3Z+FGlSSsqSK2+NQWYP7m3Ml7BPUvNimwG6XecIOkU4WTKar8lC0rzQZoD+9HURCYj2gjdfl3W3zQttYaFDlDIm8CSEKJFPdzlk3KpEFCS0BbWdY1tCF0BXUk6wt7Wec4s8gRRkKqkMoAyqQrAKsArI929n6zaHgYWkMd/OVkCyR2DFOS5KWqG0BmCNVJNAU0Cnf2NKUSVHV0VUjY7jERqnOAlyD4ASQAfIAnJIWEga8/XF/r+KEjvOcZPEhqDbEbot6B7EJUFLktY8w3qMfjMBBVHesawYR+DUADFNuGlSeyW0SUSJdQklUlk/MHH/XzMAFpLGfG0KEjZBtQjdVuQNkDcozROYF7nifGiFyFaI6MD5jpzr5QAyUYXLUx9QDkAZBevOqw5hXOReSHshHSRwSMB+SFWSVVhIDoyFpDFfGwtQTYJLoj6W8I+I4QOfcKHktFgUcTMGFzDiAxaL2Ov04sxM56FiG20CFbeyMu69D94heJ+klV4vn0LiJ0X3WlD8roPLQEwIyGg7gwbGQtKYr0QC2IPUA7BE4AqAywJ+CcWLueLHnZCu37yysv7aa+d6X//R307z3DVjvrkUWWbivBdiDnIWxCzECRKZpMwmdHaWhaQxXwkFYBMOqxCuSvqZYvwZnG4GuHslaXmssdL9Lx9+0yo1Pw7r63PtWg0hcdkVR9+N5HwEf0NSfyJHGAGYwtZ67igLSWO21T9ojGSMUosRixG4ghh/trp0/a/+/M//euPs2W9fCLZfTPZcG0BbOtMC6rcWN+ufJEWV8H6SUF1CQrD+2cy3tSh3goWkMduiAClKhSNuReAXhP4pj+HWSrmcnz27/dk5H3wwl+3ZgyzL0hQAyAqLolOsr9/qHTly/n7Zr8ce43wE5orN3LVHPG4I+LnA4IhTiholWUJ/IsdCcgfYjJkxX4oRQi7hNhB/LsV/yJjcfHN/s4cvObd7zx5kQK3e6ZTGez032WM+1aEbw9hs+b334N555/NB1z+07FwRV26383a8qUI/R9A/IeIWyY6gArDjcXeKtSSN2QaBXFKbwrqk27mKS61u73KdRQs4/1gF9DkPwAONUqvVrhZFUpXKowU0ljlXA52LgC87bZYKrv7gB3+y+oMf9Jp//MdrzePH77XPnbsQ/+iPEACIhKTzvdXVHy0oui48KqKOUVgFQFFVgvb+3QH2QzZmGxI2BdwVcIvkjZKwRBat6Wn0Hj6mVoJbXs5qMZbqaer2BV89SueOOmokAeqEKgJJ0dGjQ4cmWdqIofTx6FT542Zz7625uVOb77zzF+2Hxjg1NobO6moPAVx08ncEXAdZENgDoDyYn8ruYiFpzHaoFoU7AD6O0q0e3Mq/nz63efaxbvb582fc986kVfSSyV5PJwj+DonfFtgQUEF/uyEcAQF5v9scN+n5U4ekaEffWt9I9e67c52zZ/uHXfVbk/+hOzaGfH39j5ci/B0A1yRlIBoAx3f+B7L7WEgasx2hQ2qB0DXv3IKYt88+dKypBHfhwtv+6FFUO+t4yfvwCsXXQb4i4TCACskMDy0GJ1AIyCF2Rbzi5DboYoIi//jChfYmgDa2QnirtRoWF13bZ1yCdIPkOMR9Nm2zM2zixpjtkB2AS1G6lYditRTcYwvF3/b1+t1yp9Mccz6eoNzvwLvvAzgCokoiBfT4+8w5IqFjyYMvOYfvO/J3Up8emTlRKb/3HtzWCY8P5CXfE7TCxN0EuCTi8bN8zDNiLUljtiN1I7hKl9xGt7eWM+SP3mAlOXCgVM6ZjFI4JvAtCCcBJoSSL1jL6CQ4QEkEDlPYI6Eu4Fq1qP9sbu73W0C9AM49mBgq1dNe1sIqPW7lwhKAzvbz6uZpsZA0ZnuBjJ0Q1SqS0EXHPbajZjwLoTtC7ychNOiUAfD6ir00gh5ERqAGaSoHDt1e3osschXAxv3bFQsrIc+qm0nMVhzRlJjbUvKdYd1tY7YhMEjo5EVs+rTSyfPOI+sT55vtktJkhHCTpGtALAH0X6Oyr4eQSaoDmEoyHqx5TMfYrj58o1arVjBhq9vrrBSFWoDyL3g885RZSBqzDRJBTr2KL9q9sJF3Os1HQrLh0sQHVCWOSKoISCX4fnf6y4KSRP89mIDIQNUJjsujkTRqj1T9abVasRRavbJDK0vQIb/pHnHzdVlIGrMtiQEhhLyoRYZut/7ISGCH8oE+cx5lkelX7WY/AQG4GJEGeM9O95HHOX16XFIqKcbQ309uI5I7xELSmG1IknOuCCHkITB0OpcfCSfXlXdUVgRVCKX8hscusP8/T8+EISZd+s+9N6VMMZYiAmURuXMsJI3ZFp2isjT15U4nZqOjex55z4RSzEPUJhDXQbYFBvRbeV+vtUcECZuKWkHm1keyrPvwly9duuGShKnUq5LKQDv4cafY7LYx26IXVVJSqY6Npd0Yi0fCqRR8r3Bxnc4tMagFsvhGrbyoQHLDRS7Ewq0WCo+E5PHjdbfc7pXSaqmm6MqQkqd86qP5AhaSxmyDTh5COUY08tBupwfLj4RkXk97rpNvqMByFNcpbYroOtCrv05ym0eXAAZAQUALimsRvcXNbm89m0ofCcmFBXhAlZDEkTR1FciKW+wU+0Ebsw0JGegaEZjsJNrMkC0//PX2beR+pGhmTJdI3YL4KYFUwATACXx5zcdVgkuCLoG8lSpdPjQVmkDnkSU+7SxNR9JKPcQwDWAURPaUn6r5AjauYcz2UkiN1Gsyja7e3th4ZGnO/v0f925+tNJstteXYhFvA7gM4AaANXzpmCQFaDUS1wRconRrYyNfOX/+1iZw7pGQnPClpOjFERfcniiMArSQ3CHWkjRmGxTKJCdj5CEKy6U8LaHfOtwKwPNhY+NM74gbbRYh3kqc+xD9zdptQEFERWKJQEJSBCQoB9GV0AHwsRA+hscvHdxtHWhv/uDg+eLx6+j6kCXKxiQddOQkpIqd3rAzLCSN2YbIKqC9gjsOhrsxddWf/hT+/HnEs2cRSeidd87Hgwd/v1udnLrppZxKVuS4QGABwpSDJkDWAURJEdQGxCUAi464pOg+ZdT1Imh+/peXPxeQABA2WGZJ0ySPUpgBWbFVQDvDQtKYbRCqQNhLRAH8OI1FdXr6lHv33Q919mz/NmfPIp49+5OuhJsAbi8u/utbSCoLzvMe6A9LONxv/SGACALuQfEaiGshhKuF71758MJ/WrofvE+6jpi4EsEp5zArYQZA9Um3M0+fhaQx2yEzQCMACwL7C5+9NHXw+xvr67+1Kh1cJc/Gz24KvfMO4r/7d6EVfLhDZJGOS0S8LqkBuCgwklqX42IswlIhLmzcWW3/4Ae4v77yAQnu1safjGeK447uJD0OQpwEUAeR2oLynWEhacx2hAxgw0Fe0gFKs8671XaI+OTCX27g0QO5dPYsNDeH9v797fkic+uhhxuJdyVPpkCA4ORD0StSdkqu2VGn21lbu9fBEyZ5Llx42588qckihGNI3MsqdJiOk4JqlL13d4r9oI3ZXgIgEZiS3OeI41RsJS6GvXsPr1250mjNzk7n5Ge1H1977VwPQA/9Ge6vTZrzV68upGm6UOvFsYPeu1eA+Aro9gsYIZh++aOYp8VC0pivxkVpH4A3AFcBWapMjMc6J++urKwt4xsG4pMsL2e18fFDk8Glex39aQm/LuAkyT2EnB23vbMsJI35SuToOKOoMUeMEQguqlXE3IVSo4unGJLlMmshJPvocDwonqZzb1B4SVAJtrZ5x1lIGvNVSWXSlQDsFXQyyOWURn2B0aWN/3nMFUVrc3Oz5f1Se3FxNN/qdn/JQ85li4uNUrmscpGoFou0ViAcjvTHIZ0geALCDMDGN60wZL4dC0ljvhYRRA3AEQJ1eDdDaH+UDrnM36ym9VvRucX9WW9DQv7w2dyfeySBa2tprV6Po93oppAn+0nuk5JZIR4jOYuIaQH1/jp0MwgWksZ8JQ9tbxFqAGoCZkHsh9x+UvvzPP4KipmY+Jzyv5j/veKnV3qhXVR0+KFivaVSk0kyw9u3M1er5eN5zhnQH3LenYzSSQlHAHcEwgHQRiAHzULSmG8jqgZqRlGeDnWKB4hkMXHZ2kvV6tqhCrpS7EmuAACfAMRoqohSlErR+THAjUVokjHOEJyRNE3SFosPCQtJY74NogpwD4lREvsl1xbUBrgJcJNQiy5tQuoCIPrd5jI86k6oi6xIsUKwIqgMoAyyRKIkWyw+FCwkjflWmAHIAAK63zVmISCX0APZlGKLRAcAKVFihURdRL2/KJwJQM+HOtYWkMPDQtKYp885yovMINVJZAILAJBIIqYSMwApQAcbdhxqFpLGPHWi+pXDE/RbmZ9NTRPoL3XU1nGyevgLZghZSJrnW3/21zHEBJSvo3gkbaanEZaXY7dwaCXed0g8sRTZU74o4kHqfVH4WSg+LywkzfNNYBQ8FdIgJXnvc0exhjTttH3M1iOxCbjCAsp8HRaS5vlG0YkJyFIpVepT91hILsRu92g3hHwjKanpPJqAWiAdIQ8r7z2sRCCHUEAxiIyD+kVZSJrnGkUPoiphIs85GsXSo7c4H6emKr3FxRRJuudWjHifRBnUKIFRQSXoQdfYAnN4iNQ9kItBWpPQiTF/YkHiZ81C0jzXBHhBNdBNgBoplD8SkiSi9JN8agrFysoP7wTvP/DyUeBB53hAQh0O3NoXbSE5NKQYuQRoyZGrjLGdx9JAFkZZSJrnnBKIIwT2OvImIqvaahne3zdN9gvjLrS0xIKfysWeg78nYR5kzel+QNr+6OEhCfr/27uX3jiy+wrg59yqanbzIYoSKWUojz2KOeNgsgr8BbTNB5B3AQwHyNeI52tkFSQOsuAum1l4w6UBA04yk/HI8ujhGZKi2BLJfj+q7j1ZkBwpsSIJwVjVTZ4f0OCmSPy7G3V4b91XNwR0BOyjwNH6au8dDLr9MYekzTUJRQi4Kul9hrCbkF0BPi6AG0naif9jg4lht8+wsodG3k8p24XiFYaskXD6uMu77MwOIUkpTESOywq9pQaeAu3yzb/53XNI2lwjmSdxTQJTTI8T0pWnT/Pi5s3DEqdHK3wbkhsb/9aT0Af+fn97+7fc2GhzZeUjAtnpBT+u5z3YH+vhvgDgDjYEbAuAXrej0p+SQ9LmXUaoBUIQNjOEH2WLf/W808HB6uqPD4B/Hrx88emN9slLN9vOOy7X5o1D0uZdANQCUIC4RfIvoGyMTF887acegMGb/oDZ6zgkbd4FgA0CDUE3lPChkIFM0wVmR53O3Wo0ak52d1vThw+P092726mubpvNJ4ekXRgUlwBtAsiAECEuRC4/zJrpyQ9+MNy/fbsx+OKLu2PgzccqmJ1zSNrFQSwJaFC4hqQWyPWA4j0wfj6NnAKB6+sh4vS4V7O34pC0iyQnmINqiOE9UllKajALjUYzWwmZnjXzcNwZ/LQn5Gk6VSqK4K73TIpKyqpCKKtqPCaz7i9/Oej95Ccvzjd/VxySdgGRkJYBMBBNiNeQ6yOBJ2WlDlh0JZQhV6mEGAIdlDMnE8FBDOojbz7LqQd37/7ZCIBD0uw7EEguA1gWcBMAIEJSD2SHYJfQGAgjEFVKzsjZIxF4LuEIwKMIDNvtg28ATN51JQ5JuzyIAsKSoAChBFSCIXrF9kwSgIxSEHicklobGyu1fFMOSbs0CBQgKWgBYCL5zrtu9tYkkKQUgEMwNI+P+b/3Cn0nHJJ2iTADcHrglluPs06ARgCGIhYFNciylm+tlmQ2M5sXDkkzs9dwSJqZvYZD0szsNWoKyRIpJQAQKEGep2Zms6mWkBSCACUAkUCCd2UxsxlVT0tyCgghCYgAE+BlYWY2m+oJyUIpSBXEqYQI97fNbEbV1N1OSYFTKY0ZND1tTZqZzZ56QlJFklAGcqSE8wObzMxmTi0hWShWimksqSdgrBq2PzIzexs1tSQZ81zDENAhMALkkDSzmVRLSMZGrFIKoyR1SY1IVnXUYWb2JrWEZFNFFUMagepIHEFuSZrZbKolJHtpFBtZPswYOiBHkJ9JmtlsqqclGWMZovoV4hGVeiDGACoAyXMmzWyW1BKS02lZluW4l1VlG9SJhJGg0gM4ZjZragnJjQ1Me73Yi7FqA6HDgCHB8myZoluSZjYzagnJnZ12yvPuJM/jIBBHkg6I9CSAXXhiuZnNkFpC8s6dnbi52Zr85jftYYw6pvhE4IGgHj2x3MxmSC0HgZEQsB0lpKPehydK6UmWcU/gioj3vHGamRHQ2eM3ZaLq6mLWflpig+jELHwNaI3EDXk6kJnNkFqPbyChLFMnKH6DwMdJOvYIt5nNktrPuJm2ikFqxMME7ZF4AuBQUgfApO7azKw+AgQhIimqxgHd2rvbxxiNwrg8WkQ4yEK+D2APQAbgGoCFeqszs7oQTIKigIiYRDVqGa2oPSRv8x/HAMbtwc9akPaU+AcSC6AWIFx9cSVZW5Fm9u5JiQwloJIZo1I9I7q1h+S5RsXxNFS7JP89ME8AmiTXAWQSMgAOSbNLgwI1AVM3ACekRtO1WEuXe2ZCst9/Os6Xrn/DhJjnWkAImxK2BDUIBGek2eUiYRKAbhI6JMdq92ppStY+cHNuc7M/bYjPs2b5CDkfJumxoF0ARyAmpxtfnL/M7KJjwCiBJwKOQsKwLNdqaUnOTEgCO+nL/mByMp72YhX3ifhbSr+G8BjCwGu6zS4XCaOU0pGAZzHEwXQ6vdzdbRJJ2h4DGB8f/80eQ2MxESkEFVLYBHHttMst97vNLj5BGGbAs7KK7SqEwWAwuNwhCZwvVwROTpZ7IcS9mFIQeJ1BaxAqgWskr54N5JjZxVMJqiBOQB1Lqd3M0SZj/8t22yF5bnX18XB3d/lwZWV5GiPXGMLyWXf7hwCuAA5JswsqEhwhoC/hWEK71x89z7J8tLOz45A8R346ATD5L93tf2+4fFVCk1AAuCBpA2SLUC69XL/nUZrNP01BdgA8I3gYoWf37//ryc4O0ief1LPqZiZD8txfAvFojHbe0r2YQgSQBCUKmwBuArx2eqWfU5pdBAK7FB4IuJeSHmoaumcBWdvA7UyHJLmdHj36aXuV3W5RLPfHCYlkJLMRTpcsXj0LSIek2YWgrsAHIH9VFMVXwzDu1NWCPDfTIQlAt2+fLlv8pvO3WQtxKSgoSFEkSJUCViWtkljA6ZQmuuttNj9IVBKGBIYCvg7CA6bqviq2s2l/VHd9sx6SL3S7o9a1lb3JBCPlGBHpJIkHJD9kCFuArhEoJBR1l2pmb09ACegwCXskvwTTw3Ja7mVZGBweYlp3fXMTku+/vz0CMAKw3x787IhVfhCgJyIShHWIyyICIYek2TwRSgmHAH+niHsEHq2v/9Ne3WWdm5uQfFm2mA/COB3GMguZqpYQRoDeB7B+9roq4SrJxReDOu6Cm82AlwZgdAzgCNA+yc+S8HnIwn3l8Vlt1b3CXIbkPo5HN/srz9SqRrFM46wodlNK36d4O5AfAPgARA6g5VU6ZrOJwFGSvqJwL6Xqs1SlzxImT4Bhr+7aXjbX4SEhtNt3F6V8iY1iM2OxxcAfMoSPlPQjQrdENgg2ABQgcggFTudcEjO1dt3swtFLPyOgBGAKYAJyQugLJX2OoM9jTPdYTb+8fv1fuvWV+2pz2ZJ8iTqdfrm6ujwIsTgMTSUCR4L2APwO4E0I6wzpekq8ztPdztckNEPAguSQNPtTI5gkDQUMSLYl7QHYlfRI1ANF/CEUxcHaleWZPLJlrluSACDhbJ7k32X7+yiazUHeamUrVRVWgLAeld1O0J+D/IDUBwS+D3CFxIrEZt31m11g5y3JClQb0jMCXwn8Twj/EYUnIY6fVtX4qNPpl1tbn07P92+YJXMfkq8i3W0AaAyH2ZUKzVsJjVtK6VZA2BS1mRJWIKyQaAEoCBQicwKZgPx0h18FADwLYXjgx+z/crbH62nAJUGRYEVqkhInJIYCj5DSEYivCd2LyO6lMD0pO43urVv/MKy3/teb9+72K21vI378MaY3bsQuGQBUXRTYZYblKmmlyENLKS5KYeksLJchLEpqkWFBSAXJHEAAzyeoX8x/KGbfAQlMZ2FZ8nS2yVjiiZSOiHCsFAdk6OeIJ0D2PMP4+cqSxli6X/s8yDe5lDf+73//1wvxatG4vnhlOUsL14l0vaq4mgWsIHCZCI2ktEB8G5SkW5JmryRIkBKAKGECogeqH8GDRhztTqf7h51Oq9za+rQk611i+P9xIVuSb7K7NYp3sDU9xmS4MKwYYz4F4kmEmhm4EGMqyHAakBAhUXRImr2SpCwPqaqSsgxlCBgnYZJnsTPsl71+f7fc3f1e3NqaveeNb+NS3vgvBnvuhN3djaLZnOR5fi3LspSRixlZccRxABrffj5kdSk/K7M3kXIBwCJySSlJMaUU4nSq8uTkyfQXv/i0/PnPoVkclDEzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzMzOzufDfseIv7B/pTBoAAAAASUVORK5CYII=
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAUkAAAFJCAYAAAAWit+oAAAACXBIWXMAAAsSAAALEgHS3X78AAAgAElEQVR4nOzdW49cV5rm9/+z9o5TRp4PTDKZJFMUJVGkpFKVuqqnxjOerLmYQcHdhm+oG08PCh6g7uyvIOkbGPBd+6aBtmeMImADRg/KGBgWpz1wY6ZHraqSKKlEiqJ4SDKZyTxGZsZh7/X4IpISWV0HJpk8av0AAV3oyB07ghFvrMO73heSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJEmSJHnC9KRvIEn2g40AffDBW9lbb72eLS1t5Xk+lmVZmUlZkELYUTtIVUEh2AZyN1zGGCntIna7nd7kZK8LP+8BlvATflnJUyAFyeS5YM/ni4tHagMDqsfo4Y4rw3nmZhYYiDE0Qq5ajNSFM0QGQElpu5BCS6HcQtmqu9vLRdFaWVvrdU+c+Hk3Bcokf9I3kCT74fLluXxiItZjLEbKUDuYKRzMgsdjyTiE0VgyhBm2VJGpCNtSV7hrWBZhWS6vFiHPYmy2R0e3OHv2TAFnyyf92pInK40kk2eOPZ/DkVqrlQ90yCarjhMlmhSaiHgCNCKFERwHQYOCAUt12w0FMiDDIFMYCpuWxGaMcQWxaFhUCLdC7ltlYHGnvb54ZOTsKqRR5bdRGkkmz6CpyvK2h6PKqZrzk6XCqygcsz0rNAVUhKsOyrHyiHPhIJHJErg/OJAsHBEFuAghdJF3BC3wpdj1lwr6qN4d+sXPfsb6mTPENP3+9kkjyeSpZxNgPsDhga2tykDHlYlM8aBjNmt8SoFTwFGsGWDirj/d4+fb/fEl9IS/jPJl8C9t/227E89nRbkyPX11RTpX7NuLS556aSSZPNXsd8Lly19VR0a2alSbRzNxVI5zMYY5FI9BmJaZNh5FNB5+nGeBMsOkrBxCBXt0IOMItezvlpeHP7TZIu1+f2ukIJk85W5kQN0eHArRL0T5u8BpBV7B4QWgaqiAwsOHLN0ZeeagSWASPCnpqLPsKGgHDl6AMx04VcB7KUh+C6QgmTyVrl//k4GhmZmBxVZ5cGgifxH0osWcFOZkH8aakKgAwbYe1cqRUU14RIEZHF/PquXG8vrQhW74/DKw/EieNHmqpCCZPJWGhoYG1IpTNfQy6B9Z/BAYsT2KGUBUMRUe8bq6cBU0gh2AN0KeVWTq1by2TgqS3wopSCZPDXs+X12dapZl1uz16nOqeY4YXpP8BtZJpJpwFSm79y8fZZxUP2UIgThCdG77dtkNF+w/Wzh/vt177bWz3Ud4A8kTloJk8tRYWpqqNxojM1lWHo3S6Rj1mvCLdphF1NUPVk8kI0MisxmzVJE4Eu2Zm2u9a4cPN9dsemkT5/mVgmTyxNmE85zKtZ0Ndwsfk8MboO8Fhe8RmMFUgcoTvse8P+1mBJgNUYcHQvNAUagANkiJ5s+tFCSTJ25z86fjMyoPyj5OCG9i3gSOIkawK0B4ulJ6NUwIx0rFRWW04cwNOHvff/zOO/0X8957xEd3j8l+CU/6BpKkQzER0EmUfd/ijy39EOkEeBSU87R9Tu1hzDGVnFAvTnzwwdh935+N/vRPyebnCbuVi5KnXBpJJk/E++/P59/97sxQrGZDKnjF6DvAG5gXgjxhk9EfPu5Hek8El4YSUwqVgBBVcPWbh93neqcYkD1NCDNWHJmeXs1tit9cl7R/WllYoBKGe80shpFqHodXNqnPnYiNPAtea4VieT12qvJ6pxM2sizfWlhY3UkbQU+XFCSTJ2J+fqrSag0cVE9zMfCmzVuSXlE/zWd3er0/y3wSMUa6ktqWO9id3XJpw6DdtU7vIRKrQdAEZjoEDQ8MtCoffPBWYX/wG4Eyr42Obgz1evUZMk7gcFxoLIRsrP8gtfOgjZ7jJfL4RZ61F2ZmWARSkHyKpCCZPFb9c9g/zVqtnaFu1FHZ35H1huAUcKz/qDvx6oFGkFGiZ9MDF0I9m05AW9gtYAd5B6gJHTQE46r6wTL7A9fuvwaoC8aMpqLDcLV6sPbWW9Pds2ePx7tLq21vt4d3dvLDoaKXMW/i8JrwlKUpCWR2olnNlE2FPBvoRWq9UBRffjnfmZujSGfEnw4pSCaP1dLSmYHBwThq149m0hsWP0TMgYb36Sl6thclbhpuIS/K3BZsxsimoWfUE3EswknhVwQHLQ4KDdzPEwhymwZ4MMjNInNzla3u8TOXSqC00Tnms86mXsjqlT/GelXyMewjlpoygxiMG4hGNMIcEJ6uUB+sTB5r3LrVXbZZktLmzpOWgmTyWMVGfWCrGw/mCieQ3pD0DyIeFq7sxw62TU+waPtToU+NP+uVvhIV1xsKa/aOHauOuQ/jfNnRPYUsCkaB+wqS4BwUgGZZMogrzV6rvv3W4D9swwcCwuzFaxkHXprD+sfAa7ZGgGFhIe1u9MjCIxYTWCeBUSMHZ71sII9wZnkPu+bJI5KCZPJYvP/+fD43R66eDua5ThP0XewXjEaEag942SjRtekirwLLmBvA547+PMpfEcLV+mhY3CTbHtGfb9/5w1utn9Tz6BuE8JXxoYB6978CKgEZIpeolqFbz6XKNW4GG86dm9fcHLJcx4xIjBg1BTX/vaVPAVT7/5dmAuFV4x3KvHXtGpffeYdOShV6slKQTB65fqrLVGVjY7gBzETCdxz1AwXP4PtbB/ydl7bboE0iX2D/Kih+UlpXq1m80u12N1otb8XlhZ3Ll7lnfa8bYy9TXIPshsjWjR5g/c8y5LEdatWBkM9S12/+//ujRgXuY5hsPGb8CqJAvjo42Ku9++5bBXyQciqfoBQkk0fu3Ln57PTp5kieM0nG8RB4BfOyTUMPlAPp0tDDtIGbQdyw9Ksg/mNB+VERKsvjzday9Lv70wwUOwXVZitXWI5RLcPee9lYCiJUqyHvdop8aXMjTE3B1NRUaDTqmWLIycjBWZDkPzBUlTSIdRi7E5QfybLB6c3N08v/4l8caL333s87e76/ZF+kIJk8cidOTFVCLTtq+3URXo/2IaAhyHeL3O7pejZtBa2geAs4H4nnZV2Mhb+s5nFpvNnZgrO/d+RlV01HZS+nF4JKbO/5WLgAxwDO6vVcnRGAM2FsbCcviqJeUbUWFKpAxXb2h16nTW6oS4wGNGdq33XpiwcOzFwCUpB8QlKQTB652dmhfL3lI5HwA6FThoOCxoNeT1JbsAT6Ijr+ba/o/L/ubN0oy15rZuavdu6n2EQ5PhK12Ssqcrc/itSekzL7YVWSFLrdELQ5JCYvqdGYqsRIXaKGqdE/d34fI2Zn6jcpG7N8vCzDOsRSZXYLWNnr/SX7IwXJ5JGxf1xbWBgdWl3tHXRefSFIxzGHJA3wQP1naBlvBfMl6JeCj2IZPwsFt7plr/X5563u4cP3l4Gery5l0KzFPGsGueqvd5zvn4SxbTtWqzF2hjYNr2fV6mbD1khBNiBc8X2uSd458WNcEzoYcl4VYdF0L9g/uQWXU+7kE5CCZPLIrK1NN4aH8ym7nCulOcGcxQHJv2WX9w+RjTeFbho+ReXfFHHnP8W8tnZxs7N+7W8a3TNn/uq+NzdCqISioB7MUAn1IO+9iIYBQgSX7XZhbcBiXMvrI/lA7IUxcBPdGUXe/7JCCFRspmXqhi/L0hMbG9sDGxtTO0AKko9ZCpLJI1PWYlORWbvyCnDEZgox9Ic2MH5DlCiRu5gbLvnM0R/F2Pvk/X/3by6cP48fZOe3kw9Uc+JYkA67nyO5h1Jsu10V5dKRwi67lWrs7YyMxQZUvF2OBOkQMGJUZY9VjGzlkocNA5jZLISjZVFfrFS4Bezs8aUmDykFyeSRsNFKKxuJ6EXhN7BmLFe094Tx0mbHpgX+PIi/jpnPq6sbb7/94GkxtYIBQjhi6TuYw8AecjVlIGIVktsEtqqx1lm/3I3Dk2WtVGMK+UWbKfUble2RdafAh+xpo9NZpbpTrfAxcGvPl0seytNVgip5LrzzDuHcOTKsEazjiDcQh4L28qNs72ZYFuqftV4TfF5q5z+s3/7ig4mJnZv0J7wPUgVD7eimFY6A3kAcFqrv8d6iHYsyxk4otNXrFZ25uWrZzfJaJB6I5kXDlO+pMnTft6d+2whVTJg24bSjXgvowN6vlTysNJJM9pWNVlfPDNmDw0TNKvggaAK7yZ42R2T6yeKrho9lfySVH+902bh9e7Ocmzv3QCWCbt78swPVajZNNbxB9AtI48CA77O4BYChI2ghloNY66i9FXa2yoWFWKkPTw1JOmBxDDP+TZWhByN5CIVZ7DXLXyxv/8vDm52NrbnRtVbaxHk8UpBM9ptcHxnK8aHY02HEQcSERH4/uYK/IQKrSL8sxb8j+tpa2V37oz/6oOAB66hVKvWprMLpMvIm0hxiXJB5Dyd/ZDrgNcGyHde8c7vV7m3GbrdZzeoerlaYFsz1jyPyACPJbxgNY1ctdjDH6FUO1xm9BZUOaRPnsUhBMtlX587Nh+98n/GyDMcddCzABGZgr0W4bVoS6zJfRvtCp7f564FQ3zw9tdRmDwGyfyTyx9VWa3A4xtpI4fJ06ey7wGnwDFZjz/cmtgWLJi6Q5WvLyyO9kZGRwaGh5kSWhcPYBwlhwv11zoc5dkm/KLAqRB8gMJdl4ZTkbH29sk7axHksUpBM9tX8/Mu63YqTWeBl8AtYIw9S3Ed4SXAx4o9L++pm3F7bHl/v/o/vnrvvzZrdtdFw8uTgcK059EpQ5ZUQeB3i60LHbMYf5N4C2oxwPViXY1munT69FG+tHxvLVTkR7ZMKOmgYEM52z20/JAvRxLwg2MlD6FTy4SvA6sNfO/lDUpBM9tVlPs+Gy5cmLb2EPAcevv8p9m5qDSD5luRPMvnjSiW7enLk/9y833uw0bugn1yerw4PN6qu1ieDddKU/8jWK0IvWUzsLUB+c2+2N4FrpbKvJNbPn58KB4/kE0IvhcArfH2iaD9a2NxJMGdA1lFDI5orvdj+cHeJIKZ2to9WCpLJvnj//fn81VeP1LLtxrCyOGUzE8SErcYeQkVEdDE9w81YxAuWv3C7WLvfC9hnsstrzaH/oZYPerw4ZGWHM/FC6fCa4CRo2ri+91QkGdyveB68hP1lL8YrlUA5NlM/GEI4bjgdpJejmdjjxf/ws+PcMIwUYvTRIJ1YXP+zTnWkvQJn1/f7+ZJvpCCZ7Iv5+UbWauUD3XZvTNXKFPiQ0aT2lPajKOhYbMu6Ifj1zvbWFzHubO3hVrIRV4djrzwoZa8F6TuyTgZxGDNruaYH6uFtA90gth1ZssvLWbe4EqkOD1br02WpFxX8ms3JIGr73whRucSQYCDLNBvL7EQtY9Or9RJIQfIRSkEy2RfLHKpixiu1yuFoTyINak8J2mDoOXoV6abxArmXWq0PN06cuPg7d3Htn1aAytZWHIqxO7KymU8QyllFZhX0MgqvuN87ZxR5WHsu9XOHCuRlmwXjBYWs1cu71WrFR2xOyH4F6SAw5D01FbtvAQiGCvigg0+GQIuaNmyuA06tHh6NFCSTfVFvud7LK1NlUb6QBY1H7z0/UNBB3ED+rIzxelGWrQ8/vFicOPHbv/w2YXV1dcCuDqlSPyZqL2FeDIHZaB9BmjSMqx+4frMi7l51HbmO/UtCuAKRWhg4FMrweoQfSj6OPcoDHCnaK6Mp4FRZhu08hGtwpgpjhf3nTuuT+y8FyWRfdLOsFgpPhX4S9cTulPY+A8bXp7nb4JuK/jSP4XotY+vtt/9+Mdz335/P5+fn8rU16llWmyqKOBXQqyh+L0ivYWZCCDP99BkHkB48drncHUVugq5Hxc+EVgihGRVnQ/Rrgu9LGjFu3nfv7ofgyDhSJYSwVkR/vLU1MtxsFttwZvvubo3J/khBMtkXWQi1Ek/2U2s0HqBy/3HpzllodiRu9sr4ebQW85HYvvtR9pkMyLa2muPr29UZV3WYGI+owtEoH8U6ipmRNAzk/YD1kAOr/pnxJZvrUlzMg3ZijAcU9VpuzRqfFBqOUA8oPI5hnKSqzaDtA5l8nMyvbXayq0M1rpJyJ/ddCpLJvih7vZrIJzFHhccIyveU8g3RYifGuEjW/bWl1ZWLK79ZjTtbWqKaN8pJyngqZHo9wssKvGxrXKKBqANZfwT58FNfSy3hK+CLpVl0oXYIHBP6B8gnRRgUDAKZH6DK+gOqhECGmYxwvFeGJUyxttNMVYIegRQkk4fys5+dyU6dInPMm5LHkKYEg9j5/QYMo47wlmAZdLuuzsrWVn37xInB4sKFH9cGBw8ONxpxeGUzO1BpMkUMcw68DHrRxFk5HBIM7LZ63T3h8jDB6u5ibsoMAwGNSwoxMh7MnNFRxES/qO6dUetjCZAAwSaAhgSzjtrE8Xab7uULF3688+GHPy9+2zJF8mBSkEweypkzrXx1dbAeHYelbAwzCdSR7/8sNOwYlokskrEy2KQ1OHi1B+fi5ORPGj3CbOHshQAnsU4iHxaaiI7jQWHA9gBfB6r90i+wIahhpqx+29uQAWZY+rp4RXjoKf0DshkAZvsncnw5r1THJk/U1r974sc78PMUJPdJCpLJQ1lZGa8BQ1gjNiMKDLObrnK/1zBsYy856IZKrb377tnOu+9iQLGmoUrBMeTv2rxB1BuGKYmqCJX+mO8RjuBEDRgTHrJpIDX61Yysb4LyYxtB3ntromYzaajI4Wge42xvY2BrMo4ukRqH7ZsUJJOHUtYqAxWYVGQy9nd3M/YYNQJuRWkBcw3FjX6AfCtfWjpeq1bjgRiyU0L/UNJB8Ii+HsE9Sv31ReHcom4T+60Y9metc384SFQxTcQxS29Vsnro9soI3PcppeT3S0EyeSjVTAOUnopiCmjuBpE9sWgpsoDiNXZPjywsHKoMDw82elEHkE6B/ovda+85CD84y1bO3/uePDWpiAFUkdy0OSZnPZfuZMpuAF886Zt7XqTK5MlDyYqshivDSEP99qnSN//dH0e2hRZVxBudomxJeHBwut52OQaMywwCtf4aoMJer79397yG8Pf/e9TPf7/u3J8yxKiCjiBmKxnj16//ycDuaaSn4D6fbWkkmTyUQqplZEPYQ9aDtCoAYKugXGwX5Q1qbAL0Kr1GlWysLDUmqD81Y7enkIQcGQFXhGZK4sTw8FQTdrZtynQK5+GkkWTyUGLpeq8sRmOMI7b3cFbb7p9moQjSVoCV4Rq3Dw/tbAPkoV4vrXGhMcMe+s98+9iWpDpoFBjHGslzNzc2qjU4k0aSDymNJJOHEmNohMA48hh7aqYlA4VND7wTI9tDIzvbH3xwqQCIvbKRKR/DjEXcSJPGP6g/9bYqQgM7O9WhsqQDS+mde0gpSCYPJQuuA2PAqOTaHpbAbLuQ1BHsVKraks5+fVokxrJBYNxoPGgvwffbyqL/5ldCRqOgHMwb2jh/firNFh9SCpLJw1HMUajJ1IzyvRTYldgGr9luYXr3XLZSqRBpBmgKKmlR7ff55l03RJfuZTHvVB2K06fH0lv3kNKvTPJQlGWZRA2p1u/pcp9/J0rEdjSrUaFlx3tqRobSVZUMyjTth+s4+C0TS+hlmdoxFgV8noLkQ0ojyeShKMY8RtWR67vVs+9LNJbpBLFheyeS3RMkSwhBzpFym5AW1n6rArmD6WA2kTYFn5dFvLnZ3trq9eg2m1MpSD6kFCSTByWAGKkg6kg17aV3tRxBXRR3JDrR9xbWzSAiFbZLSani9m9h3JVZBZYtXcC+KPNpJcTPQk2rnU6lC/86vXcPKQXJ5EHoZz87E44fvxSkUJWoG2oEZ/fducCyoYfDNrhrl/d8mW1KOfak0MWU6J7KPN/CgeU33RqBEohB2jDcxP4qyP8p2v+R6Cu9QitTU//rfXeXTH6/FCSTPbN/mm9slENb8ZUh8ISgCVR3y4rd5zXsIDo2WxDbtu6pWlMRy12Vn8o0IUwKndj9y29hgAShwrCzWzHppsQNRy8gXY32VcuX81gsoN7G5ORq90nf7/MkBclkzxYWqDTHNdL0wLRLjUcYNOxxuq1o3IlyS5F2/I0gCeWyeuWnMQ/NTLwCxLvSXL51Yj/xvmWzavsTSb+M8oU8lFfqdK8PDOQ7oDYsFHAulUnbRylIPqB+0dO3Mjier6xUK5VKVsmyWO12a1WpyHshy4OcQT8rRmRCUXdv03Zd2gQbR1tlJRZFrFaK0kVRRPdqvUp3Z2eht7raKE6fPls8qW54/bYJ57OFhe8MN5v14bKMB8qOjobcR0x8GWt0t3VsuP+2Nsg4d6RqO68r3vOHGxtLW2F4alGlrwX5GuKapCHJQ8//brctqQRHmxbyptDy7sjxOtZnDvqUqCutsrs0O/y/3H7Sd/w8S0Hygf24srIyXotRTQhDnaihXNVhMkYU8oFKVEOoBmRRzqAMYHXiN+tpIWSlcJRCtyxjO2ZhR0WxrejtitiMeXe9Wj2w0WyubJ89e2r7nXc+Kd577/EGSpuwsLBTGxw8XW82m8fIOJFl4QTiuM1x0CGJUfrpZPefSQ5BqB6k4ZCFRs++57M4M9PqXrvWcHVwaMmBL4U/sTmGVUPPe5CUo13s5o7ewFyy/IXkC0FcIC9vO4Tbo82dDaimdg2P2Ldy6nK/3O8wr/Pnz+QjI2S1GtlmTlbNhrNQxOZQRQO2RoBxMsajNRlhMkjDRIYsBmTyfnl/AjjormQW26X7i/AdWS1BC2sDeQNYMcVylmfLRVlu7HS7GyPVaifGVlmWlGNjlDAWoVbCRyWci/R7L+9Lyod9Jrt4sZWPj4/XaFRHVIaRTLxh9D2s12xeRDrON5+hvX2WxLbsr6L9VQj8PznF/9Vs/sUn9JPMv34Nt2//t7Oh2viB5B9A+K7N94CJ3Ys8B5/fezakSuHCVhe5BWwB54FfReLHvV7307/+v//y0zNn7n2PkkcrjSR/B/tMtrREo17P69NHGxOBbEIwPhY8momRUtlQYQYNzSyo4ciApGYuN6PVkFwFVQkE4YAVANl3f7EVhWMQvWh3ER0FtWOkg9gW2VZRasvOdhp5Y7trthVGt0TcWttkM6/EjTK21tydWwnhzMbGBjtw9qFGFu+/P5/Pzl7LtraaYxOHGgdcZocodNTmaCkdlXTEcEhi5GGeRzg3jPcXJ32sE7PD20s/WYKtFpxt3XlclnmLwFcxhqrEJHASGNsNkM9BkIT+1JqIWTVaio6LWFdj9NWQ6arMtZB5IVSz5fPn8dtvP+k7/nZJQfJ3yxqNiYF2uzuWVbPjoBcl5qJ9tHSYlTyswBCmZghIwTj0FxkdkGQIfNNeoF/p+t6vtUEYW/1upNHGu3mBEYgBohV69BOHN2SvIG6jcKOMvmmHK7Yu24PXIWDTftBRRn/k3MiWl09Vu914IITKK5ZOQXhD4nXEkE1D/enuQ352lIPH++1ffTTPw4wC1yrUI/B1kBwZ6W0tbG59VSVrhVh/RdK2RAnOnpMYCTgaFcIrwMUs8ElZFr+qZb1fdDrFZp7Xt0eHacPlx77ckqQgCdxZd/uTerM5XHOtOkJZGV1vebykmMrqmsI+LJhBHApo2nAANLDbiOmu97D/pf29nU9+a/j6XV92AbZwRJSYUZsxlE3KniSGGcV4mApzsQy3hkZZWd/6Vyvr62yGoM1ut2xtb7e21tfPt5aWDsT5+XO/rbagrl49Uw8hby4u1ocrjeyAakxLOmrzguG4xPGIDwtV0d761/wuu93+AqaCdbDEpxy11YtVbJa+uc9TxczQV63NzeieuAJ8JiTjKWD8Ye/j8fpmam3oCLYV2MRaEl4CvrLjl1H+IuS6ONS8dW1o6HYXPijS9PrJSUESgJ9mIyNxqNMpJ7TDcWc+AZoDDiEdkmjaagr6gVE0dtuXPqaz7xKQ9Z+XDNw0jGOOEMK27G1lYdP2GnjVgWtRXMmy7NrA6OD1ZvP09ZERuvBOhPe+/rK98w5hfp5QqRRDtcGhQ5l8JFqnDacxBxUYlzVmuKuvzP73ljZMIb2uQGFYob8Ot+s9w5ne0BDbt7cqVzB/V4IDeo1nLkjeIWPvWNwi+jriY8X4sayFjHKpWsmXe73uBnQ78EEqmvuEPS/zlT3pB4f58PLLL1ebzaxmd4dj9AwZMyicUtBrkk6AD2IOPQsbBJK7tjaADeBStL9Q9BdGl0rHS/TKFgNsTjVpLy+HspzsxXKzaNBzI3NjploLLzjyshS+h/Q9wSj9YreVR3/3XrNZBX8s9L+7WPs/xsYOtuF/6t1Je7LfCbdb11/BfiXAD6TwTyR93/ZdLRWeWhEoEQXRHUlt40XgqyAulmX8IKP8242NrdvtdmvrpZd+njodPkW+dSNJGy0s/El9cHC6XpblTFR5jExHZc0KzVo6KDENTGINPkVNn34vmwy5gSXhY4IhBc0an84JS6pkN13GxdWNeDvUsnWvaSdzdbZSDYeJnrV9WOgwYgY8BKr2G289htjTryA0gnUQ+XiPgdfW11s32u0/W4S/3Oo/6D3HnZ+s5gPxkmM+JfRqP4dQNUydp/sHv2fTEqwjrkTFK5irAV8tS64p8zXFuALsnDgxWPzBqyWP1bcuSJ49eyb8838+XN9xHM1yHc8cfkDkOwo6AjoqUcNfT6WfpVJyAasB1BFDQRyx6QXoGndsf6HMX0RnV0RcqNaylVjwZrTvvPZJgkb7r/3rjoSPJ/CYGlBFPmg4Xqtlp6LQQNA6/TQYJHzhwuLqqA5tVRrZgWhuSd7cPaVY5Sn+t9qtvr4RzU3sXwn+1opfxCK/vrW1urS4eKl4660PiuHhZ+QX+VvmWxMkr14906iO5cNlOx8v4Fg1C8dkvcAGyEEAACAASURBVGTpFZvjMhPIw1i/sWv6NA9Q7vZNSoytO8cDq/SnzIXErKMqIXgCdKzolVtBmpM0J5iIMCQz8IRe++6IVQMQD8cYXgdvbha+8s47rL73Hgb84Yc/L86ceSuubb2+bGcXsA5JegFxHD8tn2WXSB3sLmgFsYLjLaTrIfq68YVIeSEU5WJZsnrkyMOlbCWP3rMSAR7axsa/nIgxO0bGccjejNZ3JR3CHgdG+lO+3XSe54ZNf70gAjugnf6uqjuGAhgUDO5OWSs8+R/NluC68XWJn2f2vx0cvHgBzsVv1ibR6uqfHSHP35DyN2V+aPEPd5tgPQXcBW3uHiX8zPavwZcwX1Wz8mqvF9fDiNeGqO/A513pXJpeP+We9JfikbN/Ul9bW6sXgcM4nAzitRj5bgh6Ezy6W9Q1h2dl9XEvvh5dBmAIGNpNUrr31/GpeeGuIiaAarSPUnpma+vQSqv1Z607a5MSXl3NNnLlXxZ2FqXDmNPIdaGcx/qZ/vpHyEC/+C3eAG5Z3DJ8RORjF/FSm+1rv/jgf7sxP8/XAT95NjzXQdJ+J6yu3jjgfGo2i341ou/F6NeMDtlu0l97e45Gjs+8LJoBoUxwtFR4o+ehWKuVl9hdmwQYHaXdarWXKCt5qGRXDNd2j36OAIOP73ZlyYVRCdwS3IhwNeCLyF+48A1lLLjSuV3fWd+YnydV53kGPddBEv59KMPxAyHqVBnCHynwxyJ7TV+X3LL6g4BvzarD0y4IGuAGcCxkvJ7bHUsbwFd3HiT9Rdums7b233Qjk1cdWeif3KGOHl+QlHA0UdDDXjL82vBREctf7Ky1flGp1Duffnq186MfpSn1s+y5DJJffvmT+sBUZ+Rmqz5RDeF1oT8SftVoknuaVe1nbt2d0xQyUBqXmLI/tZLB8a7K0nf+5s4OeibIdkdDuwH8qc77e0S+ec3G4zIvxsiGg64sLf3XQ5OTve677/689957/QIP168f6NaacSEEfiEhcA00wjdJ7/v87/v1v18LecNmBXuBEBdAV6K44qK86lBem51d2obNcnr6gzR6fMY9l1PN0VHq1V7jYN3h5YBeR/q+0augR3xCQ/1NErlH/wz1lne/UIh1+07SdP8/ow2jlq0dQxcoIfVzARAaBb9o+SXDITVHh1c5Up9/d/7rz+zq6mpBKBawf+kyXth9b/vFIh4J98/Xw6Yj140+Br/f65RnizL+26zo/XXRLn7l9s7Cu++eS8cJnxPP1Uiyfx54PtxYy0YqmY8FhzckvSw4gjS5+7AHHl3sLrjH3WKoXfo5iF1QV9A1dPsnX2hLbEu0HV2CCvonLiJ3HeCVYwWUC1WjaYDq/eIRqgpXbCpIObhK/+RLxVDZ3aB4BKOlp8oAUkXokOCIi8pcWO/dOLE51aW/M8/p05SLrXJloFal1/GM4CawZtOUNMD+rKP0kLuy2pZb2K1gX0V8aemCxK8a1fKjwcFy69y5e6fW7723D8+ePHHPVZC8ePHHlfFxapXYnQpZ9WWJtyQfAdX34/q2bSiwusK3o70CrAivGK2iuAnaUHQrKm4psh1CKIDCJuo3ptuSshIyyRXH2JCyuu0hAkM2Q7aHAnEIaWS3+vcwMII8KMjtx3Fk8IkJu7mPw4gXQG86C9ngbHMF2M0tPBvLwT9pbWyqHMiq14m6gjwraXr3FM4+zJTcBlbsuGT4EnM5KFyJLq+VsVzIYnlrY3u1NTh4ozc/n6bWz6PnKkiOjAxWYqw1s2p9CumExJuYQXigY2t3B7TdEaB62G3kbds3BVeCdNX29ehyIQSWrHyZSnt9+3a7NTv74da5cxfLH/2I37Vwr3feQWfOnMobjZnG4OBUPeb1iZo0HvMwIcVJo0mjQzKHLKZDfxRlW/Xdewy7xwf1TZOs52J0GYAgPGxrTg5tm9Vyu3MBWIP+xgn81Tawvbr1r25E6QpRRxA19asE7a4/3+/78fUgfzetR9GmJbMYzZfCfxdD/LsyxqtZsXlzcvzs+n6+4N0iz0+1b+PywXMVJLPBwTG1dUyB3eIUGjTU9ZBnkAVLuwUJFhVYNCxiLUssFWW5aljLq1oryt4WgValW+6E2Z0OXCzn53/v+pjfew/m5z+Jc3M/6IQQosqoUKVNKNYdwy3HcjDLwrCzMAwesRkNeNRiwtETiDHQGP1KPU3wY0yBefRsNRCH3A8hl9zNp1dWzmzfvt1q31MIIrCi6E/AVawK4jD9kzx3jljej2joCdqgBeCG4aqsr4jxSlC4kuOrUm91cKz5UEUo7DPZtWtUm02qnc5gNc9VWVkJT+0egd21G/W42IoxNOP2JJd24LeW3nvuPFdBUjEbU8Zx8AlbByWG9M0O8gOLsAQ+L/RptC/EEL8QsTWQ91qlup2yrBS97VbR7cZydaZRLLEU5+86JfIH+Ec/orD/ooQzPRhrQ3dtkTKrrm7lWTac7dDOh9TINnuxXsnKRiw9nIXsCPgoaA6HFxBHjA70A+XTPyK5b/2e3oeCNBjNJ1msTKP6yujoUAS+DlRxu72aZeFTqPWcecboTfVPEt1Jpr8fZUBt2+uSf238YSY+L1xcVsyuh0pnZ3NzZedOY7aHeVkXL7byAwcGG0Ux2Kw0K03H2LTy++42+bjZWaTXjY7uqR1Xru10ir/5G2w//60knq8gaY+GoGMRjgUxZqg8wCy7C3QkbWGvRmtV8AmB81a8oNj9KrSXr2xs7HQn5s519/H0hGBJQO1mi0Z07qKgfenSL7YvXToe3377L8t+18JWvr4+NpBR2+hEVrNcyyGwCFyN0QcFByOMSow4MiipCtT26R6fhEzQQGTIs6EWTxbOOqEeLgKbdx40Pt7cWV6+udzTSL0eqlckLgMFaILfmmB+95FNr4uwDqyZuGprqYz+yMEfxaL3VSPvLQyN/5vbD1fxfT67dm2qUhtrjiiGkeA4VsJ4XgujjuWAqnkjxvjUBklMLGPuLNBTYGVo7NTtf/ZfnVxdbxer1za0oc2VnZmZv9p5HgPmcxEkbfTuuwh7NEpHQUciGn6g4ZS1A6wKXwV9nMkfR/t6kBYcWN5aKzZXV79qnz59et+mGu+8Q4BT+eJitUK9cqBarR6wKbMhL73wwoGVt95qdWwinI1wphgZmdjeYPvmwE7c3CnjQgjxs6IXxkLGVBmZlvQSkZNBYdYwxrMdJIE7mQsctvVHuSoRx3Xg2jeP+PNycvKn7eXtYj2LXDF8ZKvcPY//W4JkP58V0QNdjeYC1mWJqzH6ujLdLGNvsch76+vrxdbDVeiZz2CqXq/XhurWy2UWXollOCY8U8YwhaiojPnTvZZsZ0E2lMKbJmwSw5cx5p/Vor9QbfwmnOnA2edu8+qZD5I2OnduPjtz5lYgaMT4MNYh7MH7/8x5d0QhW2yAF0r4DMX/j27nr6VsY3iouiX9z71v/uaTfbj3Mxn9zYVqi/pAfYSmi8oxCs85ZD2KxkCZ1yvL2+2tbODM1hh04XwJZ4thWNUAK3ddq7q01Rwve56oVPKl/i6Og0yGtNu065lMGbpzvxn4oCHE6JZi/Pw//+e3Kv1R9tndpP0/j0tL/91mWfO1aM5nctPoEGLqrutEoLTpSbTB2zIXZf3niD/J8Re93sWrU6NTXTjbe5gfwrtH/nZ1RFWmemSvyfoB8IoVjgkOPuT785jcOfVPROxgtw3nJTUrVZHn1d7Fi0vL8PwdvXzmg+S5c/PZa68NN8pyrGEzgjUMDISg3Pf98VYJbIG3AnyK44cK/oigCw7l5shIu3P27Na+JSjfGfkubTWn6FUOZpV4kKjDQToEnlJg0saOYTXDqyEOLntLt1col0LvB7di/O6y1N20z27eNd0vtbOylbmGKo3PgyvReANUGg6o3zjrzomeZ5AlwoCCJzAz0dmxl157fe7wK1qz51fvVNNptWKvWWUxWJ9EmAohvAgclFSxqYJXo1mWuGnrepCuYV8qQnlJnXhju2ivLC3d6k5NTT3QTKE/tT4TgGytPXwouHnIWT5DZDaI2YCOAXMKHNjtkfSMsejn7xKsQxG/6RhrvaBi8ODgDfvHG/Dz3j4uQz1xz3yQnJ+fCq1WvRFjNlKSjSCGBc3d6dl9kShtWraWUfzMxP/gzs4vQ6hvjo72NuFsfPvt/VtrOXuW8Kd/SnA3HqhkflUOpyROg04ZGo401K+e0BO0Ddcw1wPhQqiET4MqFytqAPNbu/22kc6W9jtb5/j3Oy9tHu1VXNzKYtbKKtmUzBuGmp79DoMDmDrmsNBc0dHxSs9fXV6e22Q3wfxv/3ar96MfdW5G1zZDffgIsCRpy6YJVEGrCv4iRj6xi1/1usVHpYr1RlldX9ugPTd3o5ie/qR4iJmCLl5s5SMjg5W8XsyWqrwhdCriV4VOGDUcPSCpstsnaX/emcdKOSaL9ozQCA5jinEhxIFfXrpE9/jxtyJ8kILk06MZut28GkLRFK4rqOKv8+PujyM95EXE58YXVOrq1na5PDt7uSed25fpw5f+SX2cbGB7rRzOlU8EGJf0koJewj5h8YLxEUG+e8pG/eobLoyqgiEUmtEeBc3sRF9rb754bX39xcWy3FgaGzu7Ib0Xgfjxx2c2a7Vqb+xA9VosuRIyX8JMGU31C0g8iyQgp9+Wd8yKxyGs5NXYG8s7i7snoNxft53fAXrr7ZGrsdSnjs4QFUEF8SUxfKEYvzD5xdbq5leLi3R/+MN/3Rkbe/DRj/3f11ZXO/WdHUbGDpQHg5gO6KSlk5jjQTqGOAQE6U7l92cyQH5d3FmiLpFbTNk6FKwjzYlBL3G8hA96f+BCz4xnPkguLFRDs9mrlkEDetAy/qIDXMPxQ5uLrnlldvRsl308A1zdrA7uFBzKa9nRYL8a4NX+epSnEeP0N5oq/cZWXyeFAwqyR/rHFT1iOCa0EhSuCq6WLj8q88bfwVvbP/vZB/Httyn76Slv7WxsvLoas/pl0EcBveJ+TclnNEh+wzAsdAIUyx4rlLULFy/+ePvDDweLt98+W77zzrl4+jS9f/rjEzdU+kPkRYmeCYVivBndvZkTlyuhu378+KXt48ePP3SNx2vXtpvDw+VEtxteyEP+ZrTfdNABzLRhTP3qRHvJ2XwGSLZzTMPiQFD+Yghlt9oa3OSu3unPumc+SGbZjqQsC1JFcuZIQHvbnBCUhk1ZN7OKV7bLVlt68AXoOykf0MjgUBWK6tpaeSRWfFwxnBThe4jv2Qz3k79Vvedu7v0fAWnQMIiZ6l/fHczR0ixIGZTxxuXLR259//tD7d0E3wgfxJs3T23UB8urZQznAxq0dERoCPand/aTYmg6ckQiC9LnvVBOTk/Xt7///aUtoHzvvX7A29jYWipi7VNnXOn14rayynbc6W5sTi+vv6S7OxJ+8ND3NDDQHihUncpCdhz4XlD4J7YHFGjw946PPjdxMuwOiKuYsZB5xs4Xu5mf+WyKuz3zQbIsV22PFTFmHWUqghT3unhou4qYVqaTRbfcFpXl999n9dw54p0v3F5cu3amPjo7OOhOPhaLeKSItSNZ7iPBOuoQZoHDmJH+8TmF+99g+loGHg2SkI/lWZgbnhxZrjK0ZNO5s+GQZZWdoh2u53kM5NkBzEvAsETNfnbTgoRzYED900ZHFCqvduKo6vXRq3Cufedx29v5TggsDda1FrPQi7HXG5qmPc3+dyQs80qjTpgo4YDxmKCpQGUva+PPLisEQllSsWIe2t3n6jU/80FyZmYyLqyoqISyk+MiBnnPv9OBCmba5lWClkPJxdnZE9m77170g1RyGZxt1ryp8RjKYxC+J/wW5ijSjPCYUI7IbIL7aTl7fAZniBH60+djyHO5ws1YqgvvLMN7BpicvLSzzPC17lZtNZRDL4WQrQgOxkgm6ZkNkkAuKcNE5CN5np2kDDuVUa8CS3ceND39l9tAG84Ap3Z/it7zo0h4zrO8UUYmwQdkjSKa/R+/B/n3fbbsnjnPJCqZnFnV5+oFP/NB8vz5rTgxMdgmi5tUvSW8Q/+4Wr57bvcPkpUbj4GOBcKqQqM9efC/HFtp/ePFaxvlYr7t9vR0uy19kyi7+8EIi4v/rN5sTjfLkmaWVZsxi824nU/HzIcxR8uol0LgRWASGMNq3vsNfZDPk0R/fSsTTFjZS5G44Yq34D9dsen2A8G5cpK32outiVgZGFoQ/DpCQ0FH6O/2PqsiuLQpsEs72sJ55973cjcYlnD2gZ/IPpNdpllpUGbTtCM0DdUS/ry8ex1TPQVlyiLOdU9bkOcqXvxWux2TFIIojUL9+Tp088wHydOnKaG102pBZGAz4m1QRwL7/na5Df9/e/f2W9eZpgf+eb611j5vnkSK4lHUwSpbstvlkieZughaQdAXBjp3UWUyqUIqCVJA0MDkT5D9N8xdgEYa6AECWDeDRgGF9JVyMYOZKrM6LkvyQbREUTyfuTf3ca31PbnYpCR3Ve+SSUoiqfcHuAyUyb3W3hIfrrW+93vfEEI/ibzoQPheiRMUfpdP/O984DdnZ4spniuUvXPnRjA1hbBUOtvTTDUCH4zIYVhJcM4RE16YIjnqgB6IZVA56Oiv3gQMwONtwMUSFr5ejzJLd2+kUqf5wK1b0+no6PX2v/hX48uCvnRkQUKJwNhRn8urw04/T6pOoe6IGl3aTMP0yAuZZ2eL0ZkzvtgOmVv1YZL3PimXt1rAjeZ++ZU53U58SAK3/b17N9v9/Q1fKPdU6dy2gKokAi8cSgHIooCipIBwPYL6IIQMQ0UK1/qGtL6z8/M6EEjZQGkcZ10SZshkUOI4Ao5LHKPjKMhxAhMAh55eSHz/hwAvhigJHCNQc0zHhsPCmeEfum3geg2YjjvPVKf9v/yX11cR4isIZQBjAi7t1ekd82Foz9qXdcbhsilgl8S2F9YIPpbDcurdTlpH+wiOtrfoNpGtVDJZKemXgsGwHRSFYLvexDbQXymXz8WAza55E5z4kCSBTz9FevHiki6Vh3fksQTqnDoT98rf//WYhdRPiXDMSG5SgSrwrqogaHrJK4anohxCn5OCEsgeQL0UegT0AOqRUHglGwCFiFBRwCDlzssVr7XT6PHW1sUnwPTTfodVplvZFA8Dpz6n4DKINQhlOpROwOJC57ZZWAW14IA5L83S+8dywXwStxcCH6wDtUOVnXQ+h4+i2e1svid0Y0GgMfjM+RS4QKAUMfpdJo8v0jRN19aWm3iuC5E5vU58SALQT35yOwWQblU/2Aa4SGkEUO/BtikrBzJLohfgJAntPeNrSYgBJpQSEgWJBe4VfgPOdaohRIjkAdaPDigCEBEYlDQF4loUhEkmKK4DeBqSE71/uSlha7v285L37l0HronkXnH5ce9wvtdYAasgvlSKz5PU/12rVr0fRTut4eG/bQKHb9k1PX09OH8+ykQtV2IhnEoc33cB3iPwnsgeQRHgVxT6aoTikTbcNcfXaQjJpxRrHYH/EnQFAf0EJp9NJHzRxNzfUcDn/h9SUNCZfsgUlAeZ2Ste39/q91wB+PP/ftn23peQc05jEH/oParNZjr32WfXN65fn366wEBC29usuJAPKPwGwLudWk0cyXiLw3s2kVDCLh2qADYBLMNj2UuziNNHHpz1TotJslYfH0dy0JrW/ZlIVUz2+mbQyyAa8okfC3Mc88KFAJiCNCHiTOf3n0LAMUKIxC4i3xinKiSjqL0ax7yHMMqT7hI6e59D6dlWqgNye1vaQkDau7o8VgXZdMhCbhzwRTi3kGbCz3OTF7P37l1sA7efPqtzrlmJ0+wD0QWOQdkBbwn7XYKODYGqAFgE8EDQ55K+CEO30Yz9pg9chbWk/ld/daf98ccH7/E4PX09GBkpRdmszka5cNKn6dsE3xP0DslegD0AigAKBCsCOhsKbbnmjXKqQrJUalar1XyaUmdAPAI068UBR/Qfsnj6O+MfDlD8/dJJiEj1SSyCnMzBTZ7NFteyE8EG8KylWr0eNtJMupgLADB8S526wjyg3Hd3/rxSCYiYQlOd7WxVSHN0nKX0tZf/vFWv3k0DNM4OofF8Kdb3rWO9e/dm5uxZZGq13uL5K77PyfcTwcVUugDxbdBdA/CWIzrTKkG3d6lePT6/Es2rdKpCEliLd3aG6oW+0krg/X2BPSTekcc1nOzi6T+qU/LEkJ2itXOSf8+5sB0DX+K5kJyfv9++cOHt7XY9dtlS9ETko87iD8+i8/jglZPUAlgFsAr4GYkzAfXEp5pniMUcudJ3DrtAfwL850Ndx01c6ymx5QaTxE0ExBW64C1JwwTPgjgr+bMkMxL3R/Ye0bs0J9WpCsm9noJJpfKvVmPk7sNTzrmsiCkCpec7mOx/y2s61SO3f/uvzhjWERHvUWg7pBvoBCUA4MMPp2NgOn6kn7ezdT6h+C2gkoACob5nr/iy1ua/O5Fwb4WrJmhDwiyA35D+/0WExb5se4n869oRHJR7xf/c2Un6FWYmBb0HuB8D+MeOLKlTGhV9d9v/qfnrYQ7hVIXkvnI5bDSbwVIcix4YkFAGeQnCORBnXvf5vWwkypIbd/Kbcu7BUvXmUFBCYwjPblWnkEnXY66Ekf9CYp7AAMBRAHx5RZ0AwARUG0JdwpqkVRALkJ8H+Vg+fZjILaax31l9sn6oOkTpo+z29nA+m017Nuq5YaUYDgKdl8eUo6ZIXoBQEpHFISdqmtPrVIYk0GyurzeXe3vzlVTZEqlIQNsRkXD6Q1KdJhZBZw4JxhEXzrKebqKwEWNv19Dt21v+n/2z3mUXkZ7ohfgWoBQvu50XkUBsevlNEF8BuCePGdLNxKmWFGDXV4La1lYluXbtV4fqSbi1Vcq1XdoftzITIXUN5LuEO09qEuAgOp3BC9DhJ2qa0+tUhuTe1VJDutler4azARRBe+XhoNQZeN9DKrO34+T4Tqk7gE5pkpyAs444n8lE7ziE325ioIa9AuibN2/7zc1/XQkLWd/cdU8cuSBxhVAZnSL8o/hM/F5ZTwKoBrAGaQPAmnPBgnz6tYe+kvxci825/+dv/+vWzZvwLB90bMKNYHGxlOntHezxPupJoOHIcwQRJgm8Lbm3AZ0DOIzvDAezK0jzDzuVIfnMbd/Uv1/LKE2yYdJUGjQ8/aZz7hKIyxB7AeVftBHGSdF5PskQUI8HLlHcRco0rUVLACpAp2by7t1282za9mGuvAwEj4hOUw6QeRxJSHYCUlIDxAKpOQiPQD8D7x+HoV+Vc6suTirN7aT2k5/AAwcr6Zmevh5OTg5l+/vzva3UXWHAK0hxng7jFEYADBJ+EEKJREYWjOYFneqQ7OzA+MtNAJvLyz+rRhFrctwi1ZSUd3SJwF5BxWedW8gTOlXweQ6d2s6y7+zCCUksZcPgi72mH56E3n33dhtAu1L5D6up/EMGblAeWUDDAKPv9zl8d0EGnWrCFqk6gW04zMDrPqG7qdp3k+aT2b6h1TZ5/1D7rTvv52oATBS2tnI99TgYCZx7z3v9rwAukpgAMAjQdVrMkcewgsscY6c6JJ/nXLPuXLDkXJAmQJMOi16aIDDmyHOSzgA4AyILMYNT8NmQiBzYJ0De+4m06SefVP+3ek5pBbj9dJ+zc9qBcw984iOAPRImQTiSGXyvLYt7s6yBiqQKiUVIj70w5zzmvNIn2cAtBArW+4dW28D9g+6U2Z9ImNnayg2lLhyEc2NBxPGQftILFyldBDgIoNgJSHvmaA7mxAfBixoaulqfmfn1Ul/fyIZzzUUBXzDMXQD5NsArJC+BCOXRy05D3FPw2TAi0QepALpxOUzkVNyS6imem0FSLCY7u+AD1NEEwgkK70HICwoIvmBIUgC8oJTANqkFQncT6TdhoN/BYTvIue1tBM1RfNsm7x945fr27Zvu5s3dsFIp5RUEo2HAK/K4BuFdD3cJQJnOlQBlJIaATtXjFPNqnYIgeObRo5/n0IdcoR1mwzKiApMwSVgrldZqwC/jy5enYwDtmZmP2n190Q7aQeKiTDtwfltwSwQeAzrjPftJlYC9CXudrY0hCIf9p/yUx7MNagQUQK6EzqLHsfhcO0PFGAEMCI2EcO+kmbSRCcKmhFVg/5FELV6fXav29IytBhHnU7iHjnR7PSe77usW0CDUELBLYJvAlqQnAJ8A/pso8PeQ1GZ3dxvN0dFfNnoP3oSCy8s/K6gYFgKvvs1qeVDkMKGLEi+BvETwIohRCJGk6NmjgpP85MS8bsfih/monDnji61WOJjJpX1qBz1Nx4KTFjc28ovSWGVwEE1yOpZ+FQPX/fa2W/WZ/kaa+kUouA8f9Aj+LIlhCIOQK4soC8g7p5yEDAEHiPKIAcQAQEdCzBKYFJHDsboKVWeYGHDOQ++7IGg1Eax8dufGgxs3/tR3Rj3c9r/5DeIf//hmvdiTWyR0X2KGAXogDHR7dUK7e23X5gV9K+khxYXE+QXXcmthNt4o9ezWenoa6UG79Ox3gW802FcTR6LAXVCKdyS+5ZwbkjAMoR9Q797WSru1NkfmGP0wH4wEN4sbmRJ6omQ3GgkynEyoc6AGIFcG1OsyhUyK/FqtNlCRLu4CxQSYTfr6/u8KiW0A+PRTBBcvwk1dvXk2UG7EJ27Yw/VD7AddEUIBdLm9yXchyb0rSQUSMiBKgAbk4b/nsMaXaP9EBAiD7Ix72Hap7k9N9ZXm5++3bt1Ca69LUPrkCRoMsagE9+nQC3EcwCg6vxgcQHW+VqmENsG2wHlIc478RqnuOoX3vdfqUE92heX/88Ctcm7dgvv44xtufn4ompuLcoVCLh9kORUKF33grjniAxDXJBTZmSYZ2hWjeRlOfEgCP8uXqtE4fTruybed4w8InINYoEMGwgXngmtK/XI7xVK827fkgfWkfnmdHKp99tnD1ocfTsc3b8J//DH0f1zYrab5DMVgNwhc3qc+74iM92nWETnJlyCWSbNKLQAAHB1JREFU4NgPuAE6lCGcgTAIsN85BMexAQYcsxB7BQwHTpP9/f0XM5lg9ac//Wjtk08641VXVh4m+fy1VR9ECIChgLgsYgxUnmJeUCKxDXJL0JygOQiz8P6xiHknLqdpuuJcsgt8c6hRCv/x45/lV2tJKerPns346LyXnwI4BmKcwpg6jwJKIDMnoGmwOcFOfEgu74aFvMN5uPADCB8A+EBww4AcBMCxAqgSBG4e0gwDPkiS5NugEPsEOQ0PX0yB6XjvVlDAr3Zv3LhRHxoactlruwzR4BSGCDRYrZYLYGkATM+kwBXSlyAUBJ4lMQ6hfGwXfIQcgIykYZCTHu5Sy9Nfvjy4hb0C8w8/nI6l8gqAjUr98ojE9ynsQKSAvMBkb9DaKqDfUfw10uRRo9GarVR2N7PZSjw1dScGoOeHZB1EoZrPx4zPKAkvI9A/Cpz7UMDw3lTLIokQQAjp9/p/GnOUjucP9At48OCj7JkzEznQj3i5K4C/TvIihLMA9rqSS53QYh5ASDCjVH2RC8eE4HJAbEd9ud3Nyn+oB84ngksgee0tyHC314Gpq8CFqe+JHF0+FXoJ10diHOCYgHMUzkro6czRPo5XNU8bezgQfQTeCkJXl0+TWi1ZkvC0s/d+k5Dt7YurcO4rEAVBA3Tsh9e2I1fl9SSA+1LCV41WsLq2Fqy///7fHLgRhXTL3bt3PywWi4X+fp1J6AbbqR+D41gQ4ILAtyFcINEDopevr6WbeQOd2JAcHBzOMxcP0EcTaYq3Sf4IQA/B/PN3u3ur005CIKLkHMekzpQ9AHVHNAA1vHcNUg0BMeBT7x0Cx9D7MCKYI5X3Yt7tjW0QUCRQYCdE8gRzAIJj315L7BF0RZ0r4LV6mr27NntjZ2pqKAae9WnMZjPrbZ/c9QkbcBqg0O/pF5NEs3TpQgJuZB03nNtt/MmfoHmYU7p3736YzWZyxWIwKMdrDu6aC3Hee06BGAbQL7EPUIanbHeUOf5ObEhGEXLNts5QGnUBxgFMAaS+E1IkOu8xJJEF0KvONSLU+d82hBbAloi6OsEZky52jhAQOSISVYBYAJADlNkrsu4s1arzes8c44AEQCovYMQBBcGdj5CeKwwNVYFGBUB9/+taLe4457+NiUro2JvK91F80kjrj9pby2uzs0j+6T89+LRA6WawspLL5YczWe2wV1IfwEmQPyL5I0ETdJgA2MPOFbB16TGvxYkNyTgIskh8L+H7BZfnAVp8SQhIZgQ5CiHpch5+73ZbIBgIcPt1d53nYDyGt9PfB9kZaaEcgJGEwVX5vpT1/kd4LiR7exuNxWprIx+GjdAxlyY+jyTZyWFn55vZO8mdOwd75njrFtw//+fXg60tFKKiG09qbhwOkxTOA5wgOCafjgPopXM5CNb81rxWJzYkk1i5KAh7vdDHzuiBg7yMk5TpFFwj37m6dH9obXqvqkfE3jXoySUCCEhk6TgMBW8j1G4jxiaApf2vIv+qKaGF/a7m2b1vPuREwo8/Bmdny0GaDYpBEk554AMHvAfyPQDjIEJHhhLcs0UZY16fExuSkveCS0jGEAXiAE0pnn79i05S/H4vfyw9rZ103qsEYggJBgKX/N54i2cr/ocjgbOzN7K9vUPZarU40jMUTAVwU6IuB+AlQhMCBkHmITjhIH+WxrwcJzYkvZgKvg3v2nJMT/g98KtHElKB4BnB96WpXuJY2Vvs73+Ql/I9KfC28/gnot4HeQbUAMCipOL+bqaXdx7GfH8nNiTDTNpCElUAbDtil0Abe+3OdCzLcF4nCWBKKgHQlFCHWAXwRPBLAjZTz0OtUHdz585/d9euTWXDEGUIo47uHQEfgMhBzAlwfOXzyo15MSc2JIOWq5HJspybh4INgTVAWXamIlpI/j2diYSoAVgG9EjQI1BzcHzs5OcQueWXdewbN4BGwwftNjNimBORF5inENqijDnuTmxI9vV9UVtZORPnyiN9SIN1OFQlQFBkP3T7GyOf9pcViQaBbZGPIf+Z9+lncunj1tbW47GxX9b/wZc6AtO4wktMwyATZr2UU6oCifzeOb7MQxtzaCc2JG/fvuhv3kS8VmEl49y3kP81yYsSLuE1zY8+PpgISAjtCtggsE5qDnBzlB6nHrNy4eMcw80zo6OHGrYl3cysr7eyrWxfps+5qOXC0LWS3b6+2d293TvGnGgnNiR/8pPbqQTv3c92QP/Qe98juYDkCIG+P/4Kp9de49umpE2S30j+G4j30zC+H7caK6UwX2s0dhtLO7vx5cu/OlSQra+XsyiUy9k0KMX0RSQ+12K6DEw1AVhImhPvxIYk0ClRWVvbaaS5/kVKoWNmeG++dg+gDN6IPb5S57ZaCTrF4HUCGyTWQM6DeCDPB85hxjWjmZGB/7JziCMRgFtc/PNsEPSXcjkUU/phB3dW9AXvKZFxNozqa2vVtSN7i8a8Ric6JAFgcDDbWlnxa86l7SgbXiawALJXHv3gm3DbTXUaebAJaonAgrweAPgm9ZhzAdaEZK1dw/bOzsqhVrCnp6+HIyMjkdQ74DLBBTGYco4XleIiABCYD+jmvNdKGPbbHmtzKpz4kCRvx59+io2LF7F16cq/ewzxCRzOwCGC1PP8V76+szxq2ptGSAGIIcYENuX5GMSXCNxvfav9W5/uzi0voL03FfEQR7vl7uC/u/6toUImDYpkMBqG4TsgfijwqiPf8VCT4GceqDsXFBmkFpLmVDjxIQlAN2925jVX6sFS6vU5hRBiFp2u2qcQUwA7AHYELUNaEDjvAjyGx5xj8iTMBhvFItpDQzhU89sH+ii7Xv/6zPv+0gCCdBJRNAnpPIhJiZMAzgnKg4frBGTMcXUaQvLp9rmNupYQ8HN6ZEROUPtb6k7dLo4U0DaIeRJfwOnvQuprOK0jm6w31xqtmbmHrQ8/nE5wiG2Ft27BDWwi64P8OZfBJbjwh176EeAueKBEqggyAyFDaquz1/q0fdTmTXcqQnIfm67KfLoAj7OEWwS5AqEIsoAT+14lAS0CLRBVSNsANyQ9cXBzQvqNc/iy6dO5oXxtl7xdwwGD8Zbg/iN+li8gn29W0r5smPYDwVl4XPAJLsDxB/C6Aurc/hRJaD8VySPY5m3MsXNCg+MP6+/faqyj5V17YBmOTyjMERwGER2vCYbfBz2lOqBtAI8AfOWIBwrcokO6iCDYaMR+KylmqtPIxDh4UvEfz3wURWPhQEvJcBi4t7yP3oZ0UcQQHQcBDAAc2JvF7SwUzZvghAbHH0bebgNobzf+7So8Hkv4hhAk9AHM7m2BO8b3g0/LeQQglRCTbIJY9sKKg+464tcBki/gsVYs1tbI2wd+5rhf0jM7eyNKesYyfblsKUk4Gbloit5/AOJ/IfkDCEUABQDuu5/eMf4ojTkipyok9zWTZDdA8G0A5fZGjY4QyKPzfo/7qmsMsCVpC8AShEVQc85pzieaS5DOIq6uA0mtWPybA1/KSeDKys8KKoaF/KAbdh7jLsW4kzsPn06CmIQ4LqhAMpLtsTZvqFMZksOlZnWz4WecsrvyPAfyXXkNOAdKxz4k2yBqgFuC/Begvyuvb1O2ZnJBa7NU2qkDf/t0cNchjkMpLITiADs9HX/k9hvfOozJswQiQzCSpaN5g53KkJyefphcuPB2pdasumJPecF7zJHIy2PwOBWYk0oBeAlNEDsQKqQ6t9bE41T+W5/6hxmnRZRbyyU8rAPT6UHGtXZmU99w29tTJVJnNjbcYC7nRkSOQLxIx7cAXBRxxgEDoPaeO+7fYFtOmjfTqQzJ69enEwCNhw8vslB2S6SfgVwBnTZqx2ZftwQPIga0A/ERiEcSHjjgm3a7vRRE3FAUbSUF1PuROXBAAsA0fhGMAFEp3x5iGl4LHa96cArAeZJDkPpA9kDKCQzRmRl0hO/WmJPpVIZk5zZ0OpbKtUqltAy6b7xDGcIAgHOAHL5zlfQq7C/KwAtKICYkKvKqklwg8JWkr0l8mbbSr4YGauvAWnzQTjqdRZkbAXAls7MTZP3WbrklV/ZRcMmLP3LkB+wUhJ8HUQTpADh+5yOxq0djTmVIPvOn3mceryDx9zxcgdIIyXEQOYK5V/t8ci8ghSaJTXSKrx86YIbwcy7gouCXFHON3K1MTz9Mrl+fPtBVo3TLAffDajXsSVx7RIxGEWbHM8Q4yAknTBIYF9hHh0yn1tEWZoz5Q051SJKf+AX9YnW3Wt0dcIWSc+5tAlUI1P78v1fm6X7rJshV7/0cof8/TpP/r11LHhaLtd2+vu1d5P/Uk58cKByf+WWwsnImyuVGej2CS4HDuwSvCXyX0rDEvIgcIO4Vg1s6GvMPONUhCQBL09MxRkbqZ0qFNdJ/S8cRD14gkX/5BeZKJdRJ1AVuEFhzDksemCMxJ+9nMjn/BHF7u6/vSYucToA7BzkQP/30avRnf/aPCt7HpZ2dzNlMXud8GEw4ucsQL4MYJzAEoIzOn3to2WjMH3fqQ/L69enkNuAndv7NRuiiBw4sg8hIGAP2Rwi8NCnICqg1B30j8UvCz/gEi3J+AWFUGcglFeTWWsD0QYvCKYFra9cypM7k84XhduKvku5dpbhEh2EQ5yQUBBTYWZSxGUDGvKBTH5J7tYRppZLdafv2YxeEOXqMAtglmRUUAjyCZ5P7t9NIATYE1QFsO2heHgse+ArQvQTpw2yAtVLpv6wftM6xsyjzi3BxcTEql8uFlZWwHOSyA5ImWjEmRHcNwLt0nOw0IEYvYNeNxhzEqQ/JfdXqYj2TObsQZETveIXEqqSMgBKPZBcOBaIFqQVonsBDRzz00JxP+STK+OVW4tYSYKtZimrlQxWC33SVSlouFvt70zScjArBRRDnJTcKcFTAMIGzEHpIZGWVPMYc2BsTknsTAevb2/97w6swHwDrEPpIZgDkjuAQgtQGuQtgTt7/OvGcjshHfb3bs3v7yo/EvXsIxi6h7OPCuZD+mrx+DPJdAMMkhvnc7bQFpDGH88aE5L52uy/OFtvzEn5LMpFwFZ3FjH0vcFf6nUYUOwCWAawIfoXCCsCHEGYyTnM1hNtlHK7xrXQjBKbCet0NxHE64p0bYeLGiXRCwBTIi/A8Q6eX/YzVmDfOGxeSQ0NBvL3tFzzdb12Ave7lnPj+r9Tp1ANg00tfQfjCgQ/jNHnkQqypnewkalWHh9A+bKeexcVSRvL5XJkTLgh/SOeuSZxy5BSAXkcUBeUhRFbvaMzReuNCEvgiTdPJdYXBA4dgmHQ/gDAuIgchhy4JQ6rtPRog6gB2SFQkPAwcPndM76bikyxqT3rKuzWUfxUfdAuhBM7P/zjX2ztV3NkJy8WiGwA44F1wBdD78roKYRTEKMDo+LeAM+bkeuNC8mPc8X9x5uaOamECFh97r8cERiEOsVMa9A+Wx3jPJqhFAfMEvpXXQxFzbZ8sQsGSd+1KY3Ot/t/+253k5s2DLcx8+imCe/euBsMXzvcjzU0xdFOp5xTozkMaAzki4SyBUmdV/tSNpjDmWHnjQvITwn+C27sAdrdrv3gi6RGIEUGBhH6Cbj94OleC7DTA7bQm2xQwC6/7cJhO1fytK2lpCO3mYRdm9rv0rKxksklSzKGeHYkjd5UK3qfDOyDeAdnXmSfz/J+bZaQxL9MbF5LP82ysS8HnDs6TQVNCgUQfyIIkSqxCqIJaELBA6gnl5jzwxFNzKbm1i/n2AIYOtTCzsPDnha3G6KATBvPldEQpRlJpknBTIM4LGKZQRKem01LRmFfojQ7J/vzW+nqt7/MwE26DQV7EuCQHMAJBSlsilgBNg/zMp/jWs7nZRrwZFZLmMK42gb9OD9v8FigX0EwnRPxADtfI4KpzGhXQR6AsKAswg6dXuZaTxrwqb3RIAr9srqxcTYaH/4Rh1n1BFxS9OAphEAS9uMzOCIW79OndRr2xMDqa1MjbjYMeUbrlFhenc0mxJ5tRpjeI0Rdmw1HC/UDUDyRdJnAJwhkSWQAZficULSCNeZXe6JAkIel+srJyfUfN9hcIw3VHDiBwffTeuYAbAbnRTtKNTF9rvd2X3b2DpQP1d9w3M/PrqG90ojfnNeCkywpwBcIFBJqgOMFOU+A+kBlAx33UhDGn3hsdkgDUuVX+6xqAGQAzC/rzQrhaLrtS4Nbqld23h/6meqgDCPz4Y/CnP/0o6u0tRcVif7nRSCcUcNw7/NCRH9DhkoQhAIOwprfGHCtvekj+nlGMxmtnt2rbm9su2MZhV6wJ/Dz7n/5TLRuGxRHvovF26ieCLCdBTkoYlzBOYEBC3pZkjDl+LCR/z39OhoB0aADAwGGHvNx029vINVQq54PgIj0+FPEuxSmC5wFlQWQEhI5wts3amOPHQvLv2VupPmgLswC4GlQq10rKlPp26hxQEJwrZjTsxbcAvE26KQHDAAY7q9V733tE52+MOVoWkkdEAmdnb0S9vUNZRYURFweX4XAZwmXIXaQwCKG/U9KDgpXyGHMyWEgeHYbhUMG5XK/3PA/H9yC8zwBXvHCFQHZvSOveo0cLSGNOAgvJI/OLoLe3OehdOAXvrhG4JvAHEAaPpqmvMeZ1sJA8Mu0gRnaQqb9C8qqH3iVwZe+5o82UMeaEsh/eIzI/XyOhgEEQkcyws40wg84vIgfY6FZjTiILSWOM6cJC0hhjurCQNMaYLiwkjTGmCwtJY4zpwkLSGGO6sJA0xpguLCSNMaYLC0ljjOnCQtIYY7qwkDTGmC4sJI0xpgsLSWOM6cJC0hhjurCQNMaYLiwkjTGmCwtJY4zpwkLSGGO6sJA0xpguLCSNMaYLC0ljjOnCQtIYY7qwkDTGmC4sJI0xpgsLSWOM6cJC0hhjurCQNMaYLiwkjTGmCwtJY4zpwkLSGGO6sJA0xpguLCSNMaYLC0ljjOnCQtIYY7qwkDTGmC4sJI0xpgsLSWOM6cJC0hhjurCQNMaYLiwkjTGmCwtJY4zpwkLSGGO6sJA0xpguLCSNMaYLC0ljjOnCQtIYY7qwkDTGmC4sJI0xpgsLSWOM6cJC0hhjurCQNMaYLiwkjTGmCwtJY4zpwkLSGGO6sJA0xpguLCSNMaYLC0ljjOnCQtIYY7qwkDTGmC4sJI0xpgsLySMyPl4U4ATIe0gE9brPyZhXghKJ1Kc+dWIqBafq776F5JFKBcGT8P5U/TUxpgsB8N7LIQHSVIhP1d9+C8kjMjsLeAWJl1reIyaRvu5zMuYlEwCB9HKIA6rhHNtC6l/3iR0lC8kjUqvVPJyv+ERLBNYANV/3ORnziqQEd1PP9cT7SjYN2q/7hI6SheQRWVtb8wjCChwXBawDaLzuczLmFfGSai7wa5lsuJMkil/3CR0lC8kjcuPGHV9rV+phVutefhHiI3k9ArABIMH+rYkxJ5ue+6cKao7QV3R4RGCxlba26/X1U3UlGb7uEzgtSHgprq0hjkOV5xD7bwAMELggsAQgeN3naMwR24E4I/Cuj5MHPm4vtNvbO6Oj+dbrPrGjZCF5hMjbbQDt1Z1/v5xx+opgTkAMKRJZYOfzdhDY+Q7xdZ7vEduWsCuoIaQx1Hx21TwN4BKgbCqfAsRB3rZEsO2lmAe4MlfnrokgM4QyAL//L6295Yg22793C6bQJ/BoEaiBbgfS5vd+/eOM+yVtEsgYQAJhBsAXUPq7AHo0MNjaIH95qq4iAQvJlyILbKbAlwFV9cIiwYcU+gCVBeQABKAcwFMUkloTOUNgkS7ciZu55Nl/m4Z0VXEcKgwi7/1BfjtQHtgCsAqiCqAt4IWefRFyADIAMoTOAu4sgNL3OboAgJRECYHU574T0C709TTNrDn5WQAZEckfep2TywuiB5RC2vbitqPmPPGtPB4zSZaB01nRYSH5EvT0/OUWcHNnDZhltfwIDO/Dp8Ohc0OE7wUYAgqIA11SHU/Cjnd+gfJLTFylOVh9GhLXr5e12QiF2MkfuDhEIrgJ4CGhVZK7kl5scYwKIVcEVZSYEupB5xHIkQlT1cF0TfQZepcQ2DnK13/dBHgviETLQwuQ5uXccoxkdWHmd9vXr0+nJE5V6c8+C8mXgISA26l0o1lFuCEfpAqjHbW1kjgWAsp5IDhNV5J0qMdpuh0w3Eobzcp4T/9zV1JDaqdoFum2E/oq4FroXHWw88ih2+eg/Su2FNAyqM9T4QmpuhdfqMyKQCCvgnPKQwwAjoDo7/ynP7Z4+fT4XlAjSdOdUEGtjcZ3rhRX2pnGANN1RFESI61QXH6RczspgkDeCwoCxhHdJuL2ZrPOStLe3f3ww+lTtZr991lIvlR30pWVj6p9fVGrWcluZjJh5Fw+8EyIAkBkTk1IZn2SNOjjoLXRHh6O2x9//Kunt14ff3xbf/EXNxvMnyGZVCG1AHrsPyf8oygAKYhFeP8/wORBnKAZZqIXWiBotRSUgjibxMgxypwF+Cfo3EG/4OdPCUodUQ+jYCsoprvVmfXvhOTWw+n6xesj8fb24E4apktRmM282GufDCnaYgik8r6euHamp9Gq9OzGf4fSKXus8PssJF+izhXlr1oATtVq3/f1ySfQzZv32oOD4wqzYzsuDNcBrBMo7t32dgurmEBN0rak+djp0fLu0mw8v9F+0SuYW7fgfvrTj6Le3kYUhZfmBC2RHJFUIlns9r3s/NnVAK14r81m2qgsLlaa1y9/Nxz2ziUGUH+RczInh9VJmldB167dT4aHN9oucOsEZ0jcB7D6x7dvsiboMYjfgppVElfi4Y329evTL7xI8Mkn8Jcvl5KhoWrLuXCF5NcAvyG58ce/mzuSvnXk53B8okC166O7beD2qXz+Zn6fhaR5JUh4cjr2CDbg/Qyk+4BWvJR2nvv94X8E1SDMCvo70c0WHCsfcjr+vosE5O2UnI5FrdLhKyL9mtR6t2PvHX9H1IyH/x085kfLSY28k3TuEsybwG63zSuVc34rde5reKUC6gQq8jojsgdCjqQHIBAVQhUHzIn6wiH4IlH7Sb1+uD3xGcZrzSS4HwZIUq86wG0v9ALoIRCR9OyU71QkVen4wHl+IaRfOmkJ6D/1z+DMd1lImldqaWlhe3Bw+GtS6965HYAbYDAJYQJALzqr2B4eCyLmHfWQjl8zrc8MlMp1lNYOFZL5vNbiimqxTzYDBNsC1wBOEBwHUNg7fgviPIAFCjNy/muXBo/rjUajp+evLSTfMKdmddWcLE+e3MznctlJF4WTzgWjAscA9jgyFeQFv+SFRQTpgpDMDxX/r6WjPP6G/nUPd3OT8OmkYzCaimMk853j+7aXX2TAxUTpQuxb82M9/3X9KI9vTg67kjSvxfj4WlypDK15H7ZCYkny36R0WSER4JSmfjdDVdv1ZFdqVY/6+ANoN6vyy165urwWoiy+TFNEQiKJqXOoMk5284GvDpWT2lEf3xhjjDHGGGOMMcYYY4wxxhhjjDHGGGOMMcYYY4wxxhhjjDHGGGOMMcYYY4wxxhhjjDHGGGOMMcYYY4wxxhhjjDHGGGOMMcYYY4wxxhhjjDHGGGOMMcYYY4wxxhhjjDHGGGOMMcYYY4wxxhhjjDHGGGOMMcYYY4wxxhhjjDHGGGOMMcYYY4wxxhhjjDHGmKPwPwEPjXqV0JS5WAAAAABJRU5ErkJggg==
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAgAAAAIACAYAAAD0eNT6AAAACXBIWXMAAA7DAAAOwwHHb6hkAAAgAElEQVR4nOzdeZxkd1nv8c9zlqree2ayQhIIIWEPohBQiGBYBGRxRZDtAl6UC3IF3EAFWQQRAY0IevWKbIrLFWVfguyLsqkBErYkhJBlss1M79116jz3j6qe6enp7VTV2aq+79erX5l0VZ3zVNep3/P8fud3fgdERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERERE9srKDkBEiuXuEfBs4Me7v/oo8H/MbLm8qERERCQ37j7h7v/ecveNP+7+JXcfLzs+ERERyYG7v3Y96a91fzYUAa8pOz4RERHJgbvfsDH5bywC3P26suMTkeJoDoDICHH3VgKRb/FYAB5Cw8ySwgMTkcIFZQcgIoVa3Cr5A3inQzBZZDAiUh4VACKjZX6Xx6cLiUJESqcCQGS0zO3y+OmFRCEipVMBIDJart1l4s+diglDRMqmAkBktHxjl8fvUkgUIlI6FQAio+Wb2z3QnRx4v6ICEZFyqQAQGS1f3+XxC929UUgkIlIqFQAio+U/Iljd7sEEJoD7FxiPiJREBYDICOne8Ofzu0wE/IVCghGRUqkAEBk9H9vuge48gJ9397GighGRcqgAEBk979rpwQT2oVEAERGR4ePuX958Q6CNP+7+bXcPy45TRPKjEQCR0fS2neYBJHAu8PiighEREZECuPvJ7r6wyyjA991d9wYQGVIaARAZQWZ2M/CXu4wCnAG8tJiIREREpBDufrq7L+00CtB2b7v7w8qOVURERAbI3f+ktUMB0D0VcL27n1Z2rCIiIjIg7j7j7tfuVAC0OkXAf7j7VNnxioiIyIC4+5N3GwXoFgGX6D4BIiIiQ8Ldzd0/uMci4N3uPl52zCIiIjIA7n6Ku1+7xyLgU+6+v+yYRUREZADc/YHu3tqpANhQBFzt7j9SdswiIiIyAO7+nN1GATZcHbDq7i9097jsuEVERKRP7v7yvRYB3dGAr7v7RWXHLSIiIn1y9zfttQjYUAh8zN0fUnbsIiIi0qPulQEvzVIEbBoReKm7n132+xCR7e20FLiIjDh3f34bXpdmbCsMCCAN4KvAx4DPAJcDV5jZWg6hikhGKgBEZEfu/ijgrQmc5D28fmMjE0EC3ADMAwvAkQGEuJ15YBH4FvBN4MtmdkWO+xOpFRUAIrIrdz8LeGcCD+ilCCjDVo1bBFcDHwHeAXzazOrydkQGTgWAiOyJu0fAc4GXJTBd18y53uhFcCXweuCvzWylxJBESqECQEQycfczgNe14ecdatuF3lAI3AD8NvAWjQjIKFEBICI9cfcfBH4nhZ9OIahz5jQg6kxUfLqZfafseESKoAJARPri7ncDng08IYGTAOpYDHSLgDngmWb2j2XHI5I3FQAiMhDdWwX/BPAE4KIETj36WGlRZdctBF5iZq8oOxaRPKkAEJGBc3cD7gE8GDgfuAtw5wROLjyWHl7TLQL+1Mx+ddDxiFSFCgARKYy7TwOzwBSw/u+8TAFnA3cHfiyBc2HvBUG3CHiFmb0kn/BEREQkd+5+N3d/jbsfznizo2eUHbuIiIj0yd1n3f3V7r62x9seL7n7+WXHLSIiIgPg7vd098t3Gw3ojgJ8zd3jsmMWERGRAXD3KXf/8B6LgN8qO14REREZEHdvuPv7dysC3H3B3U8rO14REREZEHefdPev7GEU4NVlxyoiIiID5O7nuvvcLqMAc+4+U3asIoMQlB2AiEgVdO8B8NKdFkdJOmsXPK6gkERERKQI7h67+xW7nAb4RNlxioiIyIC5+7N2mhCYuifunucKhiKF0CkAEZHj/V0ES9s92IYQeFCB8YjkQgWAiMgGZjYHXLLL036kiFhE8qQCQETkRB/b5U5pdykmDJH8qAAQETnRf2/3QPdugncqKhCRvKgAEBE50Xd2efykQqIQyZEKABGREx3e5fHpQqIQyZEKABGRE63u8nijkChEcqQCQETkRLv18OcLiUIkRyoAREROpAJAhp4KABGRE52+y+MqAKT2VACIiJzozts90F0f4JqiAhHJiwoAEZETbVsAdH2zkChEcqQCQETkRD/sOz/+jWLCEMmPCgARkQ3cfQy4/y5Pu6yIWETypAJAROR4D0hgfLsHI1gGvlBgPCK5UAEgInK8J273QHcC4OfMbKWoYETyogJARKTL3ceBn93l/P/HCglGJGcqAEREjnliArO7POdfColERERE8ufuobt/a83dt/txd537l6GhEQARkY4nJXDedg92z/+/vahgREREJGfuPuPu1+3S+59395PKjlVkUDQCICICL0/gNts92O39/4WZ3VJUQCIiIpIjd78odU926f0vu/tty45VREREBsDdb+PuN+yU/FudAuC1ZccqIiIiA+DuE+7+2dYOyb/b+7/e3Xe7NFBERESqzt1jd//Absm/2/t/fNnxioiISJ/cfdzd37PH5P/esuMVERGRPrn7AXf/zB6T//d02Z+IiEjNuft93P2K3ZJ/97x/y90vLDtmERER6ZG7N9z9d9x9bbfEv6H3/6yy4xYREZEeuftD3P3yvfT6NyT/l5Ydt4iIiPTA3R/q7p/Ya+LfkPzfWHbsIiIikoG739bdf9Xdv5Il8W9I/he7u5X9PkSKooNdRGrH3RvAHYG7Aj8KPLgN5zuYZ9iOAQGkATzfzP40j1hFqkoFgIjkxt0j4A7AnYG7dP89A0wC0xk3N9t9zRRwegLR0f30EJsBEdwEPNXMPtTDJkRqTQWAiAyUu/8g8ODuz48m2yT6XpL2oHST/6eAJ5rZtSWGIlIaFQAi0jd3vx3wFOApSae33/l9eSFtqZv454CXAH9mZu2SQxIpjQoAEemZu18A/E4Kj0khqFrCX2edHw/h74FfM7Pry45JpGwqAEQks27i//0Efhyq19Nft2GS3z8DrzSz/y47JpGqUAEgInvm7vuBV6XwS1Xt8a83ahHcTKfH/yYzu7zEkEQqSQWAiOyJu/8s8OcJnFKlxL+xEYvgIPAx4B+AD5rZWjlRiVSfCgAR2ZG7N4HXJvAr/ST+QTc23R7+N4BvApfSSfxfN8u0FIDIyFIBICLbcvfbAu9J4N5Zs+qGofgW8F/AZXSS9TXAIjCfcZNHuq9ZAI6YWdbXi8gGKgBEZEvufifgwwmcnXV1ve5Q/N8DHwY+bWYLecQoIiIiA+TuP+TuB3u4mc4l7v7o7gqAIiIiUhfufld3vznjLXQ/6O73LTt2ERER6YG7n+Hu391L8u8m/mvd/allxy0iIiI9cvcpd/9ahuT/9+4+U3bcIiIi0gd3f9tekn/3P88qO14RERHpk7s/Y4/Jf9Hdf6LseEVERKRP7n57d1/YQ/Kfd/f7lx2viIiIDIC7/8tuvf/ufx5edqwiIiIyAO7+qN2Sf3fC35PLjlVEREQGwN0Dd79spwKgm/z/ouxYRUREZEDc/ef2MPT/VXcfKztWERERGRB3/9JOBUDinrr7g8qOU0RERAbE3R+yh6H/N5cdp4iIiAyQu791pwKg+5/blR2niIiIDIi7T7r7/C69/78sO04REREZIHd/0h7O/d+57DhFJF9B2QGISOF+fKcHQ/i8mX2zqGBEpBwqAERGz0W+zQPW+c/bC4tEREpjZQcgsht3PwDcDbgrcAfgdsAZwMbr01eAm4GDwA3AlcDXzOzSYqOtNnc/L4Fv7VQARHCmmV1bZFxV5O4BcI/uzznA6cBpwMmceOxdC3wPuAq4HLjMzG4tNGCRjKKyAxABcPcI+FHgwcC9gTuvwumLC+n4wUNJz4Xq9UdWmRpvJFMxS8CtwNXA14D/AD5hZtcMIPw6uc9OD0bwzVFK/u5+Fp1j7gLgfDrF5YFDq0zcMLcWWbv3QdJb5ts+ORUsN+F64FvAl4GPAp81s6T/6EX6oxEAKVy3Z/UI4GeBB6zCWYfm1ib6aWx71RyL0n3jHAGuAL4IfBD4sJmtFR5MAdz9pQn83lYjAN3e/1+a2S8XHVfe3L0BPBx4JJ1kf8fDy8yuriSFH3QepuyfaSw14RrgM8C7gA+ZWVp0LDLaVABI7tz9VOCJwKOAe966kJ7SaqWVPfY8TDl9pjEHXAr8M/BmM5srOayBcPd3JvCEHQqA/21mbyg6rkFz9xngF4GfSeEHbpxbmy6jwNyrOA78wFRwI51j7gPAO8zs5pLDkiFX2UZY6qvbw/9Z4H8AP3LwUHIg6zbaOY2Qhp79rFe3ILgF+DTwcjP7z4EHVhB3/2Jrm9MA3QLg4Wb2kYLDGgh3vzfwYuDCG+bWTuol4VfpuDttf3Qr8HngLWb2/wYelIw8FQAyEO5+HvBc4JGHlzkny9BqXo1uFnttoLvFwM3A683sD/KNavDc/TstuONWj3ULgPPM7DsFh9UXd/9t4AVZkn6djjk4eqrqSjqnqN5gZt/OLTAZGSoApGfufk/gRcCP77WXX4WGd692a6BP2x/dAjzKzP6jmIj65+43tuCUrR7rFgCnmtlNBYfVE3f/YeD9ux17w3TMreuODnwE+ANd6SK9UgEgmbj7/YAXAhfdMLc2u1uPq06N7262apyn90erE3BPM/tWCSFl5u5LLRjf6rFuATBuZisFh5WZu99pvs1Xl+aSxubHhv2Y26g7InUE+Bjwh3UqRqV8KgBkV91LpX4f+KmDh5KZ3Z4/TA3wVtYbZYudlfllbnebma+b2T1KDmtPWu6+0xoAsVkt2gR3/9r3rjl49+bUScDwH3Owt9GB0/ZHc8C/AL8zSpdzSm9q8WWX4nWvy/8l4FduXGjd1VvbHyqj0PhuFgQBq/NLrC0fIggC7njO7Z9qZpVfQW8YCgB3f/wVV17992maEsdNmlMn4eF272p47eEU1feBtwCvrMOojhSv8l92KZa7/yBw8ZEV7r+ynITbPW8Uk/66IAhoHTrMSmvx6O/OPOcOR8YDDlT9Wu617fM/AI2KFwDuHiy1OXTtVVcdHYmK4yaN2cwXmgyVnYqBsfGoPTvGZ4Hn1fkKFhm8Sn/ZpTju/mTgZQcPJeds95xRTvrrgiBg+cg8yercCb+/4zm3f7OZ/WJJoW2pe1e/nwXuCZyUwoPb29wDJIQ06JxLhs6qiZcC7zKzy4uJdnfu/tYrrrz6qWl6fJ0VRTFj06eM5EjAZjsVA6ftjw7SuYLlNcVFJFWlAmCEufsEcPEqPPHwoWRiu+cp8Xdsl/zXhc1pP+esk+9ahTvpufspwMXtzqI/ljUt2rH/egj/APyqmd042Cizcfe7fPfa6y5rLa9u2W5FUUxz38lFh1VZOxUC+/ZHS014B/B8M1sqLiqpEhUAI6ib+N9wxHnKyuEk3uo5SvrH22rYfyvnnXuHK8zs3ILC2pK7nwt8JIE7DKI/3L064Go6iwSVVty4+1Xf/s5VZ+/0nFGeE7CT7YqBeDpKDkT8P+CZZrZQbFRStuqujSkD5+4T7v6WhRZHDh5KnrFV8m9bouS/yXrPf7fkD3DFlVff0d1fUUBYW+ougfveQSV/AAcSuD3wHnefHdBms8Xg/vIrrrz67N2e12qtsjJfi2UMCrXd97o1n0QHDyVPWGhxyN3f0u0cyIjQCMCIcPfnrsFrDh1KxrZ6XEl/a9sN+6dpu/v4ifMko7GZ9A5nnnSumV1VSJAbuPurEnhRHv3f7kjAa8zst3LY/Lbc/fbXXnfzFUtL8yf8sbf7HDQnYGfbjQhMz0RrEyEv1hyB0aACYMh1e4SfOXgoOX+rx5X4t7db8j/2vBOLgDJOBbh7E7gxgZkcC4BFOqsFFnbe2N2v+PZ3rjphcupun4PmBOzNVsXAafuj/wYu1GmB4aYCYIi5+z0dPnfjoWRy82P9Jv7QI4IAgqB7CEUQEpJGYAE0WtDecIIh2HSktenMTGsDnoKlELSgbSmeejfGFG9ZKUXKduf8NyedY88PN/1/wB3Puf3rzOzXcwtyE3d/WAIfybPP2y0CHmNm78txN0e5++uvuPLq52+e9b/Xz6HMSwRDj7DYwSNCUiwwQg/wkKPfk22vswXC1rF/J2Hn+7EaQdDqfEfaBKTewtrBQL7Pm528P1oM4b5mdllfG5fKyn6LKqkFd3/gYsJHF+aPP8+fpaFYT/JhFBAEAUEDYjoNVwDseMX4Ti3bds9twvHTUjoPuEck3ayWdE9IJ0mnEWx5eyAN4EZZk/9W0jTle989+AJ3f4+ZfWpgwe2sqBGH84rYibtf+J2rb3yep3tfWiFN28cVAa3WKn745oGPBIQe4WFKbCEWGFEUQASRdQrbMNj8/cjyhTjxJQ2AGMYAGhu/I52VkFc9Agdbg5ZDO2mTpk6a7u07v/6cjYXAzYeSyfHp6L/c/cfM7HPZ34BUnQqAIeTudznifHQlQ/Jf762EYcCYhXgD4qAas0TNIO42pjF0GsbmemRhp5EjIk1gtd2m3U5Jkr0n641Cj1g7dGvm5L858QCsJks2v8QH3P30goZS9xewD4CT8t6Bu0/Mr/EBby2eUGZm/SySpAWHb+5rTkBsEUHDaIYhRJ3jMKjCl6OraXSGZ8bWS4L14hnWPKLdhrVWC0/Z8bvRtuS4ImB5PoltJvq4u9+rSutByGCoABgy7j7h8IXNM/w3J//1hB9ZSDQW0AggrOkJoWC9UGlAk5CUkLQds9iG9uLer2oIPWJtLnvy3/i8zUXADdddNTl97h0+Cdx7TxvpT00/wS197obvXTW9+Ze9fhZJ0mJ14ZZMlwgGQcBY3GC8CVSkGM7KrFscBDARd5qEtsespdBa6xTLm0+zbS4CluaSxvT+6N/d/TQtKTxcVAAMn0/eeCg5oeGEToKLIiNuhDTjavVgBikAghBmQ/A4YmUtYml1jc3nkTfqN/nv5Iorr/4hd3+nmf1C3xsbAe7+d1dcefUP9LudLU8HzN+060hAEARMNBuMNXY5zVVTocF4COPjnWI5cWitRKy1W9vOuTl4KJk5bX/0ceBHio9Y8jKkKWA0ufvTb5hbu8/m3wcBTE6OMbsvYmY6ZLw5vMl/MzMYb8L+qQbNcMs1jwaa/Ld6TZqmXHHl1U9w99/PvMER4+4vvuLKq39hq2JtEJ9HkrRYmb8Ja2+d2ceswf6ZTq9/GJP/ZgHQMJgch/1TMftmI6bGx7ZsHw4eSn7Y3Z9eeJCSmxFJA6OhDX9q7c5H6mFK3AiYnY7YNxsxEdd3iH8QggCmpkNmx45fBiGPnv92RcDVV17/23k3oHlf9Z7n9t39GVdfef3LBpX8t3vt+umAzUXA5OQYk7PBSDeKQdApmGdnI6amI+LG8X+NFC4uKTTJwSgf60PF3X/z5kPJlIcp4xMRB6YbTE8GhDrJc1QANMZgarpTBOQ57L/VNtbSFbvymmv+2t2f1/cOhoy7//rVV17/f9fSlcyT/vZi8zZardXjioDZqTEmYjWI6wxoRDA9GTC9PyKe6jQkNx1Kpt3918qNTgZFx/vweMH4TMRJIzR82avxEGYmxlhduGVPy/v2aqvE1V5N7Iorr/5jd3+/ll09ujz1h6648uo/yiv5b6fVWmVt7hCTk2M0VChvKwamY9i/L2J8JgL4zZJDkgFRmqi57trsL2nBC8qOpW4W55ybbvzuCb8fdNLZaqVAgImZU1tnnDr5deD6Ae3q3FuPpLlfo39gNrgC+NYANnXb629YutvCwsEtJ2cU8TmccurZTM6oGcwiBZrwOuAVZnak7Hikdzrya8rdDXg68OoWnFJ2PHV16OA8R+ZvPu53efQ6tysCZGtFfAaz0yez/7QtL5iRPYjhRuCFZvY3ZccivdEpgBpy9zOADyTw10r+/Zk9ZZrYmsf9Lo9knedQ9rApIvlHUczMqUr+/WjBqQm82d0/4O63LTseyU4FQM24+4OALyXwCN3nrH9BACfdppi2S0XA7or6G5186pkjfVXMoHRX5n4k8F/u/rCy45Fs9BWoEXd/lsOftUE3OR0gd7jp+zeztDp/3O+LSEZ5nhoYZPx5xVnG33iiOc0pZ56sibID1L1JVAI8x8z+sux4ZG8097Um3P33EnipEv/gmcG+25zM0nfnd3/ygNVlVKAuce7FgdOU/AfNgVbnXkj/p3vvi5eXHZPsTqcAakDJP39xCDOzZx73O03cq7+tJv5tsyCkDED3lMDL3P3FZcciu1MBUHHu/lwl//yZwcyBmPWVFGX4WDtg6pRp9f5z1i0CXu7uzyk7FtmZvgoV5u6PcHhf0tPNxKUXh48kHL7pmuN+N0zD36Nkc+9//0m3Z3a/CryixJ05AY82sw+XHYtsTd+GinL3M4G3t5X8CzU7ExFFx48R61RA/Wx12d/0rJq7IiWdOWbvdPfblR2LbE3fiApy9wD42wRO1tB/sczgwMln7v5EqZUDJ585MnfArIruqYD9wNu6bZpUjD6UavrlBB6o5F+O8UkYiyeP+51GAepj82c1Fk8yPrnNkyVX3SLgQcAzy45FTqQ5ABXj7qcC32zBvrJjGWVrCVz33atO+L3mA1TbVoXabc65A011dUoVw2HgzmZ2Y9mxyDH6WlTPSxMl/9I1Ith3ylkn/F4jAdW11Wez75SzlPwroNumvaTsOOR4GgGoEHe/M/DVVucOnFIyd7j+usOsLR864TGNBFTLVsm/OXkSp5w+Q6RWrhK6VwXc08wuLzsW6VBtXC1/mCj5V4YZnHbbfcRx84THNBJQHVt9Fo1wnFOV/Cule1XA75cdhxyjr0dFuPuPJvApTfyrnrUEDl51DW1LTnhMIwHl2ir5R1HMabc7k1jdm8rp3jPgAWb2ubJjEY0AVMkryg5AttaI4DbnnHXCbYOhk4A0GlC87f7usTU59Uwl/4pTW1cRGgGoAHd/cAL/pt5/tSVtOPj962i1Vrd8XKMBxdiu4BqLJznprFOV/CuuOwrwY2b2ybJjGXUqACrA3T+p6/7rwR1uuXWVlUNXk+wwXUPFwGDtNsoyOXs6J500rsV+aqBbAHzczB5cdiyjTgVAydz9IQl8VMm/PtxhZQ1uuf77JElrz69TUbB3ez2tEkUxJ93mTMYa6CY/NdItAi4ys0+UHcso01emZO7+6QQuVAFQP4nD6rxz68HvbzlBUPITBAH7TzqLyelAvf4a6hYAnzSzHys7llGmAqBE7n5hAp9W8q+3NIX5IynzR67LNCIg2cVxk6mZ05meVeKvu24RcH8z+3zZsYwqFQAlcvd3J/BYFQDDwR1WUlg53GZ57ibW2stlhzQUGuE4Y/tOZnIyohFrqH9YdAuAfzaznys7llGlr1JJ3P3OKVzW1qWYQ8m7Vd1yAr7stLxNmoKtLdNK18oNrqIsmiCM4k7PPooYj6HRnWeppD+cQkgDuIuZfbvsWEZRVHYAI+zXUiX/obWesCZiIO72dQCYPlocyPGU5EdPCkEAzweeXXYso0hfuRJ07/j33RaMlx2LiEiZYlgGbm9mN5Udy6hRD7Qc/ytR8hcRodsW/lLZcYwijQAUzN0jOr3/M8qOZVDcOz/rV7l7ChaAG4R0q0zTwSYiW4vhGuAcM11PWyTNASjeTyU1Tv6tFFptaK+lJKlhaWdy207XwYfeOcyiyEjDlCiMiRrQMA1Biexmr3NG6jyHIoGzIngU8O6yYxklNT5k6snd/y2BB9dlHlgKrLQ6CX+tnZCm6cC2HQQBsYWEUUijidZwF9mg18midSwEutNkP2xmjyg7llFSw0Olvtz9vDZ8M6343z0FVtvQWmp3L18bXNLfTugRUWREYyFjsUYGZHRtTvwb/3+hDVfcBEEL7ngmTGxoSTYn/roVAgF42Lkk8FtlxzIq1M4W6zle8eS/3Ia5IwkL8yustluFJH/onEJYbbdYXFzh8KGEueU27boMk4gMyMZk7w5rDi9/L4w9Bcam4OQG3O8MuOBsOBDB2Ckw/ovw2ks6p+Y2v75Oum3jM8uOY5RUOhkNE3dvAte14EDZsWy2Psy/utoiSapzw5rQI6KxiOmx+vVmRLLanLxf/G74o1+lMz1uL+4Mr3oDvOAhx39f6vTdieFm4Awz02pZBajRoVFv7v64BP6xakV50ob55Wol/s2CIKAx3mAq1gErw2lj8l9yOOmZkL65x409HW79K5jcML5blyKgOxfgp83sX8uOZRToFEBxnlp2ABulwNx8m7m5pNLJHyBNU1YWVzhyJKHioYpktjH5H1qB/Rf0kfwB/gYOPAQWN5y9q9npgEq1lcOsJnVhvXVX/vt+C+KyY4HOpXxzK6uka/VqFaBzWiCeipiuxF9SpD8bE3PiMPkzDO5CuF+AlXcc6/3XZRQghjU6pwFuLjuWYacRgGI8KalI8l9ehfkjSS2TP3QmC64srjA330Y33pVh4Q6P+zMGexX8O+E5bz1WZNRlFCCBBvCEsuMYBTWpCevN3f+zBfcqM4YUWFxMWWkNz9yaKAqZmYwJdRRLTa0n5Rvn4KzTgZUB72AKrrsBTpro/G+NRgG+YGb3KzuOYacRgJy5+z2TkpM/wMJ8e6iSP0CStDk8v0ZBVyqKDNTGnvmj3sjgkz/AAjz5/9ZyFOC+7n7XsuMYdioA8vf4MneeAofmndV2MQPmsUVEYZPYIkLyLzjSNOXQwhotFQFSY5e+Lb9tf6yfCYXlKrXtHAU1GRCqL3e/vAV3KWffcHjBSdqrue4naBjTQRMbO36igwNrKawutnMvQIIg4MBkAwm9AjQAACAASURBVAtz3Y3IwKz3xi/9Xmdhnzx952Y4q7sCSY1OA3zNzM4vO45hphGAHLn7+UlJyT8F5hfauSf/sbjBgYkmjbETZzka0AxgZjpkanos1zjSNOXIQqLTAVILG4fkP/bN/Pf3iW/nv49BS+AeOg2QLxUA+frZsna8uJjm3utuNseYngz2NIw0HsLMTL5FQMsTjiy1anOeUwTg0u/nv4/LrqnfPICu0trQUaACIF8/V8Z3bbkNrbV8u8LNMGZ6PONrApho5lsEJEmbhaUUDQRIXdy6nP8+Ds7nv49B67adKgBypAIgJ+5+pwTuXvR+2w7LcwltS3LdT3My7GkCyUS++R+AldYaK1okQGrirqfmv497npn/PvKQwL3c/dyy4xhWKgDy87iid5gCc4ut3JM/dHrzvTDrjB7kbWUhwbVssFTUxtX57nH7/Pd359PrtyLgBhoFyIkKgPw8tujh/9VVClnXv98E3mzmP1W/bQmHl5x6ne6UUfRT9ybflngMHnq3HLefo+739yfLjWJ4qQDIgbufnMJ9itxn22F5Kf+eP0AY9ZfA04Iu1Uvaq7TyWFxFZIAmDHhkjjt4PEQ1bum9syjQSWXHMYxqfFhU2iPSgv+2iwvtQob+B8EK/MvMr63VbdazjKDXPy+/bf/Vs/PbdhHaEAIPKzuOYaQCIB951vMnaCcUttJf3aRpyuJwrYAsQ2LjOflnPxi4MIedPAaecp9an/9fV2ibOipUAAyYuwfAQ4vsdC4t6qK3nawtJRoFkMr7yJsZbIs8Bv/+Z7VO+sDReQCP7LatMkD6gw7efRMo4MKejqQNLS1/t6O2JSxpLoBU0Mae+QPvCK/60OC2/br3w702XP5X50IggVOAHyo7jmGjAmDwCh2qWl5Ja3Puv0yttUSLA0mlmcELHgK/8a4+NxTBqz4Cz/mxeif9Leg0wICpABi8RxQ12uye/4p/w6LlCanmAkgFbUzSZvCKn4R/vBQ4u4eN3R0+clmnkNi83TpbPw1QbhTDRwXAALn7rMO9i9rfSop6/xksrWplIKmmzcn6sXeHhW/DM94K3HEPGzgPnvf3sHhp51TCMCX/DS5w95mygxgmw3NoVIC7PzqB9xY1AjA3n/9tdrcy0RxjMuN9ADZacZg/UvxJ+dAj9s1GBCp7paI2T1Zd//8vfg9e9WH4yuVw8LrO7257O/iRO8ELHw7nn9X53eZkP0TJHwMieKSZDXCmxGiLyg5gyDyoqB2lKSSJq4TLoG0JrSSi2Sg7EhkGe7myJGsCXn/++rbX//++t4d/eebe99Fv4t/pvZVcVDwIUAEwIOoLDdaDiur9r3o5w/+hD6ZmHNR2slrVaQDpk/veb6mb5bkbmW3dm9/qZ7fX7dV6rLvFu9fnDVp3d4V1skaBRgAGxN2ngB8san/JSv0n/4UeFV7EJEnn/gAaOJGstkp4a7d8h/Sqd+M3f4Xg0PfgpDtgJ/8QY2f/D9ID+094ba8jAtvtv5dtbrbVdi81eBvwNeAbdOYjng/8HMf3cnp9X324j7tPmtliYXscYmoHB8TdH5HAB4sqim9ZWiVdK64E39hjb45Ffc8BWDp8LPEXXQTMzo7R0JEvGRyXJFuw/P6HEl3yb7S+1flVuuHxwCAah/BcSB7xFMYe/DY2DnhV6bz8xve1Cvykwcd3fxVnY3wWOHnD64t4X915AA8zs4/mv7fhV6FDsd7c/VUJvKiIlOwOhw4nfSXOuBHSbMZE1lloO4t+hhmht+HDxDqvWUkgWVkj7WPxo6npMcYLuiGR1N/GY3XxE79B8Devxa87PulvJzAYOwuSX/kLGj/0y0d/X4UiYOP7eonBH574jC1edXzgjwX+qcAioFsA/L6ZvTjfPY2GChyGw8HdP9uC+xexr9UU5uZ6m0XfDGMmp0LCGn/yKbDYgpXF3v4G/V7FIKNjY5Jcevud4G3fPiHxt7aoReNNs6saE5A87jzGn/ytSqzLv/F9XWjwxWOPZNjKsTdwawqTBb2vGD5tZg/Mdy+jocZpoDrcfQw40oJC5pevrsFcD2vbDlviW27D8vwc7Yx/9mYYMzOtIQDZ2cYkuXCxEbzvWK9/q6S/nfViIDDgiWcw8fTvH32sjCJg4/s6yWDh2CM9bO3YG1gEogLmBMSdsxWzZraa315Gg64CGIwfTApK/gCtHr6nzTAequQPMB7C2GT2dUHaVv8JlJKvjUly+V8f2nPy3/j81IG/u5bVf3v+lvsp2lMNFo4m/V4DOfa6c/qOaG8SaAL3LGh3Q00FwGBcUOTOPMmewKYmh7PHOxFDFDYzvcZbpvsCyJ4k13+N5l/9W8/Jf93GIiB4w5+QHpkfTIAZrRcc3zb4B6DTg++3Cum8/iDwzk3rGOSo0DZ3WKkAGIxiC4C9zD7aIG6EQ7363dhE9vFG0+2BZRvHzYx/+/ksdQeae03+69Zfv7oAq39/en8b69M9jv5rUF+EznaeNqCt7YEKgAEY4rRQqAuqnE+azbjsEHLV0FEsObCD1xF/Jqdtf3CJ9VW8izoNsL6fm3Oed3BJzqMA3c2qABgANZ19cvfZFM4rO46dBEM+1bOXCUc6BSC7aX3pBSTL3X8P6IA5eipgEda++LLBbDSjVx7916AzdGd7vzHgrW4lhbu6+3QBuxpqKgD6d++04L9j1klsjSoPTwxAAAQZz3HoFIDsZvXSf9jTtf69SB3a//nSfDa+izflvP3Lc94+QLfNLWzl1WGlAqB/xQ9FZVxHf3XIP2WHzAsD+ZCPikhvNg5bN76//fMGIbg53+2PAJ0G6NOQp4ZCFH4QhhkHsNvF33m3UO0e7u9ThZXYpNqSw/luv3n9sX+XeTlgjakA6JMKgP7du+jvbhpmKwBaa8lQn/NeXcv+Gh34squ8b5U23HNzc9Vtc+9dbhT1p3awD+4+1YbbF73f2LK1HC1PSIZ0FKDtsLSa7c0N8yWRMjjRvny3v3rasX8P14hUMV2iFM5x98lCdjak1BT25x5ewnLKvSSwIysrFHjzwEK4w9xC9jcVDPtlEdKzjYl45ax89+Wn7d/9STnIf0mwYr5f3YmAdylkZ0NKBUB/7l7GToMehw7n59dYHZJzAWkKhxecpJ19OXBTASB7EN/nV3O7hDYwaNzvT/LZ+C7+IOftX5Tz9jcppQ0eFioA+lPKwRcZhBmvBIDOTPm5uRUW5xxv1/NaeHdYXoXDc3M9JX+AKNJhL7sL7/+HBN0B5s139+vV+nbGZiE6/6mD2WhGzwI63/5BVzed7b12wFvdhQqAPuQ9zWXY3b2MUfV+zxcupasszXeKCIvCzFcVxBMh432MI7ZSWF7MPnW/bSlJsv663u+91OsIioyWuNFk7VH74R8ODXS7gUH7cQ8kLvi2wGadArrpcFcLcrte/x4F3BEQjs40UAHQBxUA/SnnFAAQBwHtPquPtiXQTkj2+Pz1UYdwDejjzoJtgyTxYzEUKPRoYL05GU7riRJg4gnXkH5wiuW5Tu+9nxUB14+78EyIf+aT/Qfah085nGIwmJsBrW8HvjyALWWkAqAPagp75O6zCZxRWgATxX90g07WRSd/gChKK3HQu3eSyWqfP60UWoo/NzY9Seu3X8tYd9So1+Jx/XXNJoS/9a6jlwAWPft/fX8zwJuP/bbfrQLOkyiu97+uDbfXksC902yoHrn7AxL4TFkT61dTWDySlJJEJ5pjTPYxArDiMH+knOsSx8fHmMp29+CBajssLrSPjoBA74XQxnkgUWRMToWEOX+j6x5/FhsX51n+14fib/y345YG3stowMaCYSyG9q8/j+ZD/vjo78q4/G/j+3qGwd8ee6SHrXXewG2A7254eWGnNYAI7mdmXyhmj8OlCp2huip16KkRgMVDdl1fzkKP+pq70K81h8PzaySJ07bk6E+vNm4jSZy5xRYZV0TOpO7xZ7UxiY3/1EeJf+93mdhw1XkcbD8isPmxxgy0Xvaa0pP/5v2+2eHFxx4hW5+w89wLKCf5b6DTAD1SAdC7Uq8/NaCppcQysdgJS5r1kgKLiy3SNM1l1KaTRNvMzeez6mPd4+/VxmQWX/gK/OIvMHa/4++wuZ7sN/6sCwzsxyF805WM3/c3ttxuGTbu/3cdPnL0/5xjhcBWQW58rM2bOX4YtKT3dddS9joEVAD07o5lBxBP9HY54KiKmuUVTKtt8Fb+rWOadvY1aHWPvx8bk1p49gVEr3Qaf/wO+GkIT+sk+c0/jduCP36a8T+/hMnfdMLT77Dl9rJyP/6nHxvjeJDDqsNfnJD0ja0KghcBqx7ypPKTP8A5pe255ip0xq1e3P3SFpxfdhxz821W28VOo6rjHIDQI2ZmIqKSTgHML6astHq4aUEPxuIG05ODre3rHv8gbJdwk0PXE93yJZKFG/DZ84hm744dOGXL52ZNklmTfK9JeKv9fM3g88BVwFnAvejc+GTzBbhlj2bE8BUz030BeqDuY+/usPtT8hdMhDBf5XnU1RAHQWnJH8DzurF8Qfuqe/yDsJ7oNifLaP9tYP9jdmxM8078m1+XdX9bvbd7ONxjj68rWemjsXWlAqAH7n5aAlNlxwEwEUJiES0v/mqAugg9Yny63B6lpcW1lHnsq+7xD9LGpLdToh5UbzxYg+j918K7/wMu/w5ccwjiBE4/Be51LvzkfVl7xJnHndB1723/e3lvFUn6RyUw6+4HzOzWsmOpGxUAvalE7x863/nGRERrUQXAdiwKS+39y/AadDLcmHTDeQhf+EH487cAW+S2a4AvXgJ/9ec0OBl+7Um0XvFofOzYtvqJr2qJfhd3YMs/kuykeifa6qFSk04mYgh0j9ttTU/UqyWT0bQx+Tf+6fuEs0+CP389x/La5gl5Gyfm3Qyvu5h44sk0PnDDltsccpVqk+tCWaM3lTvYJiZ7Xxs/q6TP3rQV2CiNxY1K9P49KPAceg77qnv8VXdc8n/px+DxTwNu7P5mt+vzNz5+EB79bBqvO7YuzogUAZVrk+tABUBvKnMKYF0zhKBRTBFg7f6u0ypqjlfoEZPj1TjEwwKrkDz2Vff4q+y45P+mr8HL/4Cdr8Xfzvrz5+E3Xkbjr7+x5T6GVOXa5DqoRutYP+dU7fsUALPNoJh1AfqcbpAWczUZY1MRVTkz0mgWs2ZD6BHNHOrAusdfB41P3QK/8tvd/+vntJUBa/DMFxF/eW4AkVVbty3WCEAPKtI81k4lq80ohPGJ/Bvp1XZ/S7auFbBuQRQ2j97ApQriAOJGvgVa6BFxI5/LHesef1Ud1zN/yquBZQazPIsBC9iTXr/1voaPCoAeqADIyN2Nzr0vKqnZhGaYf+ZbXO6tAlhLIEnyXeotCAJmpqxyB/fkZEAUWS5JNPSoc0OdHBfQqXv8VdZ4x+VwzX8NfsPf+iyN9103+O1WT3l3Zq0xXQaY3cnJiYthVUYATE+FpHOe69oArdYCq+kMzQztdQrML+U7/h96xORUVKm7yq0LgJnpkKUUkkU77o56/YgiI54Ic7/RUd3jr5rjeuQXv7/7j0EeuJ3b9PKG98Cjn3V0nzW7vG9PEhhz931mdrjsWOpkCA+FfLn7+QlcWvXRtFYK8znfLjgIAqanGzT2cBSlwEIByxaPT48xNWKJROrp6Kp9KxBPPJbBDf8ftxfgAK21f2B94GYYC4DubYHvambf2PXJctRojrf15/SyA9iLOIDJ2SjXc7ZpmrJwZI6l1s53El9N4fChJP/kP67kL/UTf2GOTvLPy61E/z38kwGp8KnZqtIpgOxqc5A1A2A2YmEhJc3pRuttGiwurrAcBMRxg7gBoUPbOrP920m3159zr6PZHGOime8+RHLx3e/lvgu75la490zu+ylZbdrmqlABkF0tRgDWNQPw6QZLh/M9HZCmKaurK6yu5raLbU00x5gY1/ksqanrCzhtff3NwNn576dctWqbq0CnALKr3UE2ZnRuhTtk11eFHjE+3rk1sZK/1NaB6fz3cXLtmq1ejMSbHCQVANnV8iCLQpgej4ltOAZ9giBgfCZiSsP+UndnFzByfbsCiozy6RRARioAsrtN1a8A2E4UwsxsVMg6AXlqhjHT042Ru2xMhlNyn1PJ98ricVo/MJvj9svXbZNVAGSkAiC7Wo4ArFu/lnt2bKyYZYMHKPSIZjNmZjrc06WHInWQ7gfudEF+O7jgwqO3CB5ytW6by6ACILuhOMgaY7CvOxpQh0IgikLGZyJm1O2XIXHc9fi/9LDuPwY5vtjd1jMesfU+h89QtM1FGu7DYcDcPWrDWjpkf7e1BJYWE9KUXK8U6EUQBDTGG0zGxVSr7tBqQ6vVuYQxTf24+x54mBJbpwgJGiFx3FlzQZV0sVI6i10lq50rUNpJSttSrH3skwgCCAIjjLqfU1i9BHh0NcAUGs1nQfsKBte8OOy/F2u3/NHR31Tt/Q9SCGkAsZnlc83zEBriw2Hw3P1AArfUdQ7ATlJgtQ0ry63c1+rfi9AjmmMR4+PFJNflNiQLKa00zVQErY+eBE2n2Yw7t2XOK8gRlwJJAivLbZLEMxeroUd4M2CiGTAWVqfxWy8CGv/v2/DzzwXa9B+dd34++HbWHt45NT7MyR+Orga4z8yOlB1LXQz5ITFY7n5OAlcMYwGwLgVWUlheSbHVbMlwEKIoZCyOGWsU02AttWB1dTBFz/oNbeKJsFIJpu4cWGnD6kIysPtbxNYpMJvN8gu2jfcEaDz3X+GNb+z+X69HUHeDv/US1v7gR4/+dkQKgLPN7OqyY6mL6p/8rZZ9ZQeQtwCYCGBiIqA9HrCURLSX8js9EHpEEEAYBYyNB8QFtcarKSwtDXa0o20J7TYkc04rShmb2tt9EmR7SRvml5ykPdgVplqe0FpOWF2JmJiMaJTYEpodKwJW/vSnGLtmAd7zVjqJPOsB1N3Q//ifI5X8Nxjuyx0GbHQOiwFw94sS+NgwjwBsp+2dyQ+ttTbp2rHz4r0Mw0LnDnDRWEgUQWTF9sIWl2F1Jd+VEaHzXhsTEZNNfdF6sbwKS6truS1jvS70iGjMmBoPSx0NOG4k4OWfhJdeDMxveMZ2R9HGFmkfvO63WHv+fY69akQOvu4IwIPM7FNlx1IXI3JoDIa7/3QC7xrFAmAzd2in0AJstbP2fxuwNMVTx4LOoZXGAVEbggbEQGCdyVllxXx4YfC9yZ2EHhE0ndmJWF+2PXJgvoA7R27WDGOmpssrAnxTwxJ/dQ173pvg45cAu91GuwEXPQz/8/9F607HVscaleQPRwuAx5rZe8uOpS5G6PDon7s/LYG/UQFQP2kKRwY85J9FFDbZP62v217MlZD81zXDmMmpkLDEj+qEQuBbq9jf/Qe8+zPw7eth6ftAA2bPhnP3w89dRPvx96N99vGvG6XkD0cLgKea2dvLjqUuRuwQ6Y+7Py+BP1YBUC/uML9QXlJZV3YPsw7mj6Ss+G693XxFUci+ybjUBLq5CMhq1JI/HC0Anmtmf1Z2LHWhtigbTTCpoSokf4DVdouFPG/7XnPzi+Unf4AkaTO/0B7okjxZmfWWxHt93RAZ+onag6QCIBsVADWzuEwlkv+6ZCVhufxlFipnuQ2tteqs37LabrFQgcNmPaHvlNT38pwRojY6AxUA2ai6rJE178z2r5K2JSwtrvU9xDtM0rRzjX/VVqFsLSS0qlOTHJfolfS3pQIgAxUA2cyUHYDsjQOLC9lXiytCmqbMr2gYYN3cSmtgC/wMUtsSFhZVqdWMCoAMVABkM67moB7aa+AVWNJ4O8mKs6aDiTSFdLW63VhP2qxVrzaRLXS/TqNx38MBUQGQTXP3p0jZUmB+tZq9/3VtS1hdqtD4ckkWl4tfbjqLtiWsLLfRJ1UbaqMzUAGQjQ6uGmin1e79r1trJyOdWNyrNfFvO0nitKsfpnSojc5ABUA2jbIDkN2trVbvtsZbSdOUlQrMNC/LclKPz6ltCUvVD1M6VABkoAIgGx1cFZcCrRqdtG2P8GmAOr33dG2EK7V6USctAxUA2agAqDh3yPneMQO1ZqN5GsCBVo0+KG8ZbU3arAO10RmoAMhG1WXFreV02+K8WDsYyfPL7epP0ThO2xJqMF1BVABkogIgGx1cFZeWv5JsJm1LGMXB5Rb1KtSgfsfWiFIbnYEKgGx0cFVc3veOz4ONYAVgxd2ReWDa1GzYYjSpjc5ABUA2OrgqztP6naitYc3StyQsO4LsLK3ugkVylE7TZqACIBsdXBXXruEhbSPYsQxqOOqxpvxfB+qkZVC/1rJEbRUAlRfVcATAa9gb7lcd33OsywAqz1UAZKICYI/cPXRQH6Dikmb9DulwBPNKGpUdQXYW6OtfdW0I3V0f1B7Vr7Uszwg20/XTrNfEcgB8BPssUQ1bniCoYdAjxsDNTG31HumI3iMzG8GpWvWTjpcdQTahRzRGsLmqY2c6rmHMo8bUUctEBUAGOriqL7ZOUq0Tq1e4AxFTr88p9AjTDKDKCxjJhTV7pgIgAx1c1RcH4GF9PqYospH8EgZB573XhYcp4Sh+UPVTny9/BeiQzsB0cFVeAMRWnynmYVSfWAetTu89tlCNZT2ojc5Ax3Q2OrhqIJ6oR2IJPaI5wsPKjWZ9TgM0J+txTIna6CxUAGSjg6sGmmE9EksUGTXqBA9cXJPTAEEQ0Kh+mNKhNjoDFQDZaBJgDQRAc6zaBUDokXqVwEQzrHyxNhk1MBUAdaE2OgMVANmouqyJ8fFqjwIEATT07SNoVHsUIIpCmjW7tHTEqY3OQE1QNjq4aiIAGjPVLABCjxifjrSsJJ3PaWKiuqMAY+Oxev/1ojY6AxUA2ejgqpHJEKKwesvsxY2AGq5YnJso7PxNqqYZxozrLE3dqI3OoHrfumrTwVUjBuybMuIKrbQTRSGTk/rabTY1EdAM47LDOCqKQianlP1rSG10BmqJshnBG7fWmxlMTkeVGGKOopCZyVhfui2YweRUWIliLfSIiYmYUEP/daQCIAO1RdmslB2AZBcHMD4TlXozlyAImB5XUtlJ2C3WyvycQo+Ymo50iqa+lssOoE50mGezWHYA0pvxEKYnGqWMBARBwMxUI7dr/q2knzzEAeyfapQyEhB6xORsRKP8QQjp3VLZAdSJDvVsdHDVWCOCqX0Ri4tOkhRzNicKm8xMWS49/wjaBv8C/A3wXxTX+5kA7gU83eGnEhhoaRMEMD0TsbiQstouZkQ3tojZ6QhTl6ju1EZnoAIgG40A1FzDIJ6MmV8JSFactiW57CcIAsbiBpM5XUMedxL+z5vZt/PZw44OAdcC73f382L4pxb8wCB3EBpMTTcIVmF1dY00zacQCD0ibgRMTga6LHM4qADIQPVuNjq4hoAZzIyHTM9GRGFzoKcFQo9ohjGzk/kkfwNi+BBwYUnJ//h4OjE8IIaPDDqBBsBUE2amGgSNwZ6+6XxOAZOzEdOTgRrC4aE2OgONAGSjg2uIxAHMThutNGJtPqCVpj2PCKz3JMfGA+Ics0kE1wFPNrPKjEaZ2aK7PyGC/27BWYPefhzASRMBSTNgeSWgtdbf5xRFRmMqpGHqAQ2TbgFame9FHagAyGbJ0GLTwyQAmgE0ZwPaHpC0IpZSSNfWsHYnPWxONus9UYudyEKisYCxgNxXjOtu/n+a2S357ik7Mzvk7r9s8IG8vh9RCNOTAT4RsJJGpItOy9usnx3Y6XMKPSCeCAv5nKRUugogAxUA2WgEYIiFBmEDmgBjDVoAKaREhAm0QrAAGt5JIkUmEgMieLeZfbC4vWZjZh909/cm8Jg8i2SzzlUdzHT+Ku6QOLQtwlOI29COOsVdGKiXP2I0ApCBCoBsdHCNkBiOZY/Ghi9LCT3IqLMGxa8Xv+fMfi2Ch7VgrKgdmkFs3c8r7PyoYRtZGgHIQMVxNhoBkMJ1643fNbPvlBvJ7rqTAn9Po+xSEnXSMlABkI0KAClUd+j/s8CflB1LBq+L4PMqAqQEGgHIQAVANioApFAR3Epn1n9t7kPRjfXxEdxcdiwycjQCkIEKgGx0cElhos7Np55gZt8tO5aszOwa4Cmhbs4ixVInLQMVANmoAJBCdNfb/1Uzu6TsWHplZh8K4Pk6FSAFUhudgQqAbA6VHYAMv+55/9eY2RvLjqVfZvanEbxWRYAU5NayA6gTFQDZ6Jym5Kqb/P8CeGHZsQzQb0bwpyoCpAA3lR1AnagAyKZyK7DJ8Ogm/9cBzzazoVlwsvtenhfBn6gIkJypjc5A38cM3H0qgfmhaZlrZquDdVg+ixDSAH7NzOp0uV9m7v7rKfxhe0g6H8N8TNZNAB7CpJnpUsA9GoovYVHMbEGXNhUvhvkY/iyCH4tgX2xmEZwSwcNjeEsM+dzTtwDdu/sdCeBnhj35A5jZawP4uRjm6tz7iCGJ4S0R/HgEJ3ePyX0RXBTDG2NYKDvGURPCjUr+2dT5O1gKd/9CCy4oO45R0B0S/xDwi2Z23XbPc/fzgb9M4Ifr1Pvqvr+vAD9vZleUHU+R3P084J8S+IEafmb/DjzTzL623fPc/QzgrxN4eJ3eX53F8O9m9iNlx1EnGgHI7ruqmvLXbWjfCTx6p+QPYGZfBS6M4EUxrFb98+n2+pMIXgncf9SSPxxdMviHI3h1DElNPrPVqDM588Kdkj+AmV0LPDqCd1b9vQ2D7t/4u6UGUUMqALK7rOwAhl03+X8OeNpeV8Azs7aZvRr4oQg+0r2OvnI29CDvZ2a/a2arZcdUFjNbMbMX0SkEvlDVz6v7mX0YuJeZ/WGGYzIBnhbB56r43obQ5WUHUDcqALLbsfKX/kVwA/A4M1vL+lozu8zMHh7BYyK4rAqFwHoMMVwVwRPp9Pq/UnJYlWFmX6ZTBDwlhqur9JlF8PUIHmVmjzCzb2TeTucYflz3mJZ8fbXsAOpGBUB2OshyFEOLzjnxHYf9d2Nm7wPOj+BnIvhiGUllksI62gAACTpJREFUQxL5RgRPA+5sZu8cpkv8BsXM3MzeAZwXwTMi+GbJn9kXIvhp4J5m9oG+ttk5lh9f58mqNXFp2QHUTdmFdu24ewgcasF02bEMm27D+zwzu3jQ23b3+wNPBx6fdD+7PLLw+hcqglXgX4G/BD6upJ+NuxvwEOCXgMcm0ITcP7M54B+BN5vZ5we9H3d/fgKv14EweDEcAQ6Yme49kYEKgB64+0da8LCy4xgm65P+zOyJee7H3SeBRwI/AfxEAqcdfayH7W38AnXv3Pdx4F3A+8xsrp9YpcPdZ4FH0+mRX5TAgaOP9bC9TZ/ZDcAHuj8fMrNc15J393cm8AQVAYMVdz67R5YdR92oAOiBu/9eAi/Vl3gwusn/m8C9826AN3L3ALgLncs6LwDOB852OKMN4Xavs86CIweBK+kMO14KfBb4mnog+ep+ZucDDwDu2f33OW04zXdoz0JoG1xLZ6b4V4EvAF8EvlHk6Iy7TwFfacF5Re1z2HXbjxeb2e+XHUvdqADogbs/JIGPqgAYjO55/weY2RfLjgXA3WPgNnSGnWeAiM7522U6w8QHzaxVXoSyWfczOw2YBcY49pnN0Tkdc31VPjN3vwD4bAvismMZBt0C4MFm9vGyY6kbFQA9cPcmcHMLpsqOpe66X97fNbNXlh2LSFHc/cUJvFydiP51V108eZQvqe2VrgLoQfdA+7iqp/50k/9ngVeXHYtIwV4ZwSfVhvSn+/e7RMm/NyoAevf+sgOou6hTue95sR+RYdGdK/L07pUH0h+1xT1SAdC794SgxNWjbuX+XDP7TrmRiJTDzK4CnqdRgN5FnXke7ys7jrpSAdAjM7vedBqgJ92h/w+a2VvKjkWkTGb2NxF8WO1Idt2/2UfN7GC5kdSXCoD+/G3ZAdRRBIvAc8qOQ6QifjmC+bKDqCm1wX1QAdCff4503+9MulX7C7vDnyIjz8yuBn5HowDZdIumfy07jjpTAdAHM5sH3qYv7t50h/4/D7yp7FhEKuaNEXxGbcnedP9ObzEzdcD6oOOtT+5+lzZclupvuasY1oAf6OWuaiLDzt3vBvxnCxplx1J1IaQB3NXMvlV2LHWmEYA+mdk3Qk3i2VX37/M6JX+RrZnZZcDr1ZbszICgs/a/kn+fdKwNgLs/IIHPaFWv7cXwPeBuRa71L1I37j4BfL0FZ5cdS1V1TyU+0Mw+XXYsdacRgAEws89G8CFVU1vr/l3+t5K/yM7MbAl4gdqSrXWT/weU/AdDx9mAuPt92vAFzQU4XvcL+z4ze0zZsYjUhbu/N4FHa1TxeEHnTpwXmNmXy45lGGgEYEDM7EshvF3Z/3jdyyR1zb9INr+iS4yPZ0AIb1fyHxwVAIP1gghuKjuIqugWQy8xs++VG4lIvXTXBvg9dSiOieAW4NfLjmOYqAAYIDO7BfgNfWmPDv3/N/CGsmMRqamLI/iK2pOjnYnnm5k6WAOkYysH7n5JAg8d5fN3EbQN7qfhOpHeuft9HP49gbDsWMrS7Ux8AniwmY1yszpwGgHIx7MjWCo7iLJY5+ePlPxF+mNmXzJ47Sj31Lpt6f9U8h+8UT6ucuXuT0zgb0ftiO1W618CHmBma2XHI1J37h4Bn07gh0e0PXmamb217FiGkUYAcmJmfxfBG0atworgCPAEJX+RwTCzBHhK97s1MrrJ/2Il//yMWn4qlLvHwCUJPGgUKvfu+tw/aWbvKzsWkWHj7g93eP8ozAfoJv/PARepM5EfjQDkyMxawBMiuG7YK63u+ty/o+Qvkg8z+7DBi0ehLYngWuBnlPzzpQIgZ2Z2A/DwCG4Z1i9u9wv7ejN7ddmxyP9v7/5d5aiiOIB/D84DtQmBhNhYmKSwEAVRg2mCBo2K+AcoorEJoqAhGjCFgk0QDaQQxEYRSWNrFRBjY6FICBIwSGIEGyWPPLVQwZFrsWt4hjSPl7ezPz4fGBZmlzunmHPumdm9O8yzqjraJUfnvJb8muTxqvpl6HjmnQZgAqrqbJLHuuS3eUvcccIeq6pDQ8cCi6CqjnRz+NTAVZP/Q1V1Zuh4FoEGYEKq6uskD3bJpXlJ3HHCHq8q/84FE1RVh7rkrTmrJZeT7Kuqb4aOZ1FoACaoqk4n2dMlF2Y9cccJ+3ZVHRw6FlhQr3XJsTmpJeeS3D++UGJCNAATVlXfJdnVJZ/PYuJWkqWk75Lnq+rw0PHAoqqqVlWvdMmLS0k/q/WkSz5Jcl9VfT90PItmFs+ZudBauyHJkSSv90k3C8sEx8n6c5Inq+rU0PEAI621vUlO9Mm2Gaolfyc5XFXHh45nUWkABtZa25Xk/T65a5oTd5ywJ5M849e5MH1aa7ck+ahPHp6BWnImyQG3/IflK4CBVdVXSe7pkoNLyfK0dWTjW/6Xu2R/kkdN/jCdxkuOH+mS55aSlSmtJctd8lKSe03+w5u2c2ShtdY2JXk5yQt9sjVJhurkV92iey/Jm+NHHQMzoLW2JckbSQ70ydKQdSRJuuRSknczWjX0+0DhcBUNwBRqrd2U5Kkk+/tk95X9G3zcVcn6Z5IPk7xTVRc3+LDABmmtbU/yapJn++TGSTQCqyeVLvkyo1pyoqr+msDhWQMNwJRrre1Isi/J3iQP9Mnm/72/zvGvStazST5I8nFVLa9zaGBKtNa2Jnk6o4uKO67sX+e4V08gXbKS5FSSz5KcrKof1nkINpAGYIaMVw7cneTOJDuT7Phv65NNax2vS5YzeuDGF0k+rarz1y9aYBq11nYmeSLJniS7+2TLWscYP5nwwng7P379NsnpqvrnOobLBtIAzInW2uYkt63arpXUf2S0jO9iknNV9dPkIgSmUWvt1iS3J9meZFuSm6/xsUtJfsyodlysqpWJBQgAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAATNC/n5wv8Sqnq5IAAAAASUVORK5CYII=
📡 API Calls Detected
- HEAD
- POST
- _arstorage
- about:blank
- GET
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Code Obfuscation
JavaScript code obfuscated using 97 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
General public
Attack Method
obfuscated JavaScript
Exfiltration Channel
Unknown
Risk Assessment
CRITICAL - Automated credential harvesting with Unknown
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 97 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Generic Phishing
Official Website
N/A
Fake Service
Banking/payment service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 97 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
www.jaiclub23.com
Registered
2026-03-13 14:28:09+00:00
Registrar
Dynadot Inc
Status
Recently registered (25 days old)
Hosting Information
Provider
Dynadot Inc
ASN
🤖 AI-Extracted Threat Intelligence

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.