
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
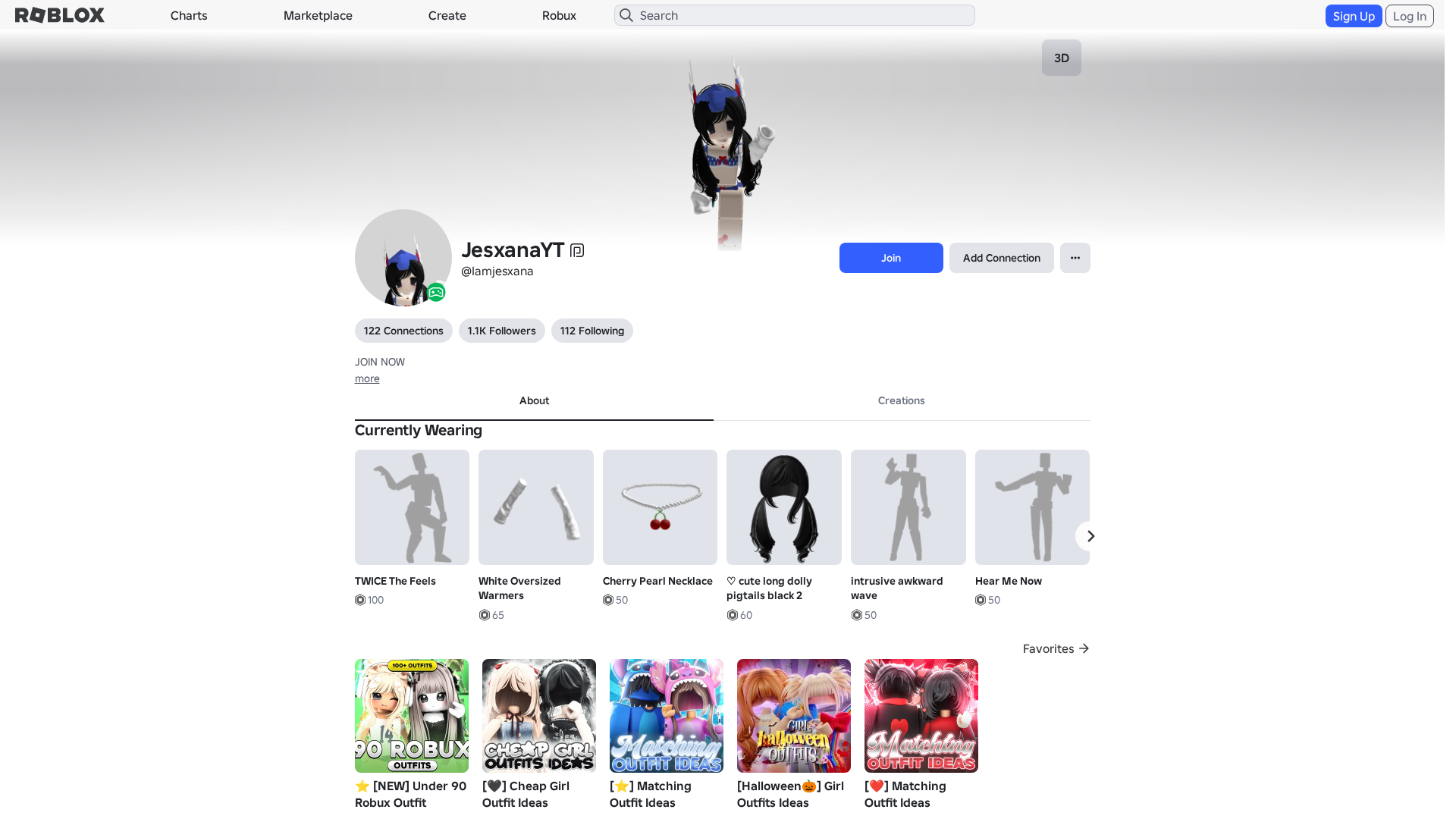
Detection Info
https://www.robiox.com.py/users/377059899225/profile
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
95921c7c-435…
Analyzed
2026-04-07 22:39
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T10883107292542837617B79DAF064672AE2D7C70FCA8346E1A2F8D39A0FD6CD1E85340D |
|
CONTENT
ssdeep
|
1536:j3ogSkXWn4r/gieXlsgn4glMgkcg6tg/2gX2gk2gu+gfKgDqggqg3ngxHdgjDg4B:jYgSkXWegJL6Qcv8mvPkris5QQF8bTVU |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b44b77439999cc64 |
|
VISUAL
aHash
|
0000d7ffc7f7c3c3 |
|
VISUAL
dHash
|
e8c8b6302e2e9606 |
|
VISUAL
wHash
|
0000d7ffd3d3c3c3 |
|
VISUAL
colorHash
|
07200040040 |
|
VISUAL
cropResistant
|
e8c8b6302e2e9606 |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/2510242378/Rthro-Walk
- https://api.injuries.lu/catalog/2510236649/Rthro-Jump
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/133307355099075/Hear-Me-Now
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F377059899225%2Fprofile
- https://api.injuries.lu/catalog/86499666/Woman-Torso
- https://api.injuries.lu/catalog/14618207727/Default-Mood
- https://api.injuries.lu/catalog/11600321661/Realistic-Idle
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/2510240941/Rthro-Swim
- /login?returnUrl=
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/553970961/Green-Queen-of-the-Night
- https://api.injuries.lu/catalog/113598419875472/Helsworn-Valkyrie
- https://api.injuries.lu/catalog/85665834724929/intrusive-awkward-wave
- https://api.injuries.lu/catalog/72150908678645/Dont-Start-Now-Dua-Lipa
- https://api.injuries.lu/catalog/11524641707/valk
- https://api.injuries.lu/catalog/2510238627/Rthro-Run
- https://api.injuries.lu/catalog/129730987657361/animated-cute-surprised-2000s-mo-Dynamic-Head
- https://api.injuries.lu/catalog/77170959609138/Cherry-Pearl-Necklace
- https://api.injuries.lu/catalog/80963950541052/hip-sway
- https://api.injuries.lu/catalog/128217885/Fall-Fairy
- https://api.injuries.lu/catalog/86499698/Woman-Right-Arm
- https://api.injuries.lu/catalog/84634421588465/cute-long-dolly-pigtails-black-2
- https://api.injuries.lu/catalog/77684969500159/Sabrina-Carpenter-s-Manchild-Emote
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F377059899225%2Fprofile
- https://api.injuries.lu/catalog/10789933479/White-Oversized-Warmers
- https://api.injuries.lu/catalog/1080949/Bunny-Ears
- https://api.injuries.lu/catalog/553970606/Blue-Queen-of-the-Night
- https://api.injuries.lu/catalog/12874468267/TWICE-The-Feels
- https://api.injuries.lu/catalog/122829513155529/Hype-Boy-NewJeans
- https://api.injuries.lu/catalog/2510233257/Rthro-Fall
- https://api.injuries.lu/catalog/1365767/Valkyrie-Helm
- https://api.injuries.lu/catalog/139607718/Korblox-Deathspeaker-Right-Leg
- https://api.injuries.lu/catalog/2510230574/Rthro-Climb
- https://api.injuries.lu/catalog/11524638268/valk
- https://api.injuries.lu/catalog/86499716/Woman-Left-Arm
📡 API Calls Detected
- https://ro.blox.com/Ebh5?
- https://apis.
- get
- https://help.roblox.com/hc/articles/30428367965460
- GET
- POST
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 212 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Roblox users
Attack Method
credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
HTTP POST to backend
Risk Assessment
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 212 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 212 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
www.robiox.com.py
Registered
Unknown
Registrar
None
Status
Age unknown
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for www.robiox.com.py
Found 10 other scans for this domain
-
https://www.robiox.com.py/users/262683709646/profi...
https://www.robiox.com.py/users/387072077925/profi...
https://www.robiox.com.py/users/217025834840/profi...
https://www.robiox.com.py/users/335157511751/profi...
https://www.robiox.com.py/users/239884675658/profi...
https://www.robiox.com.py/users/377777277866/profi...
https://www.robiox.com.py/users/255445160301/profi...
https://www.robiox.com.py/users/378472335145/profi...
https://www.robiox.com.py/users/411240076850/profi...
https://www.robiox.com.py/games/90118298734859/EMO...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.