
Phishing Analysis
Detailed analysis of captured phishing page
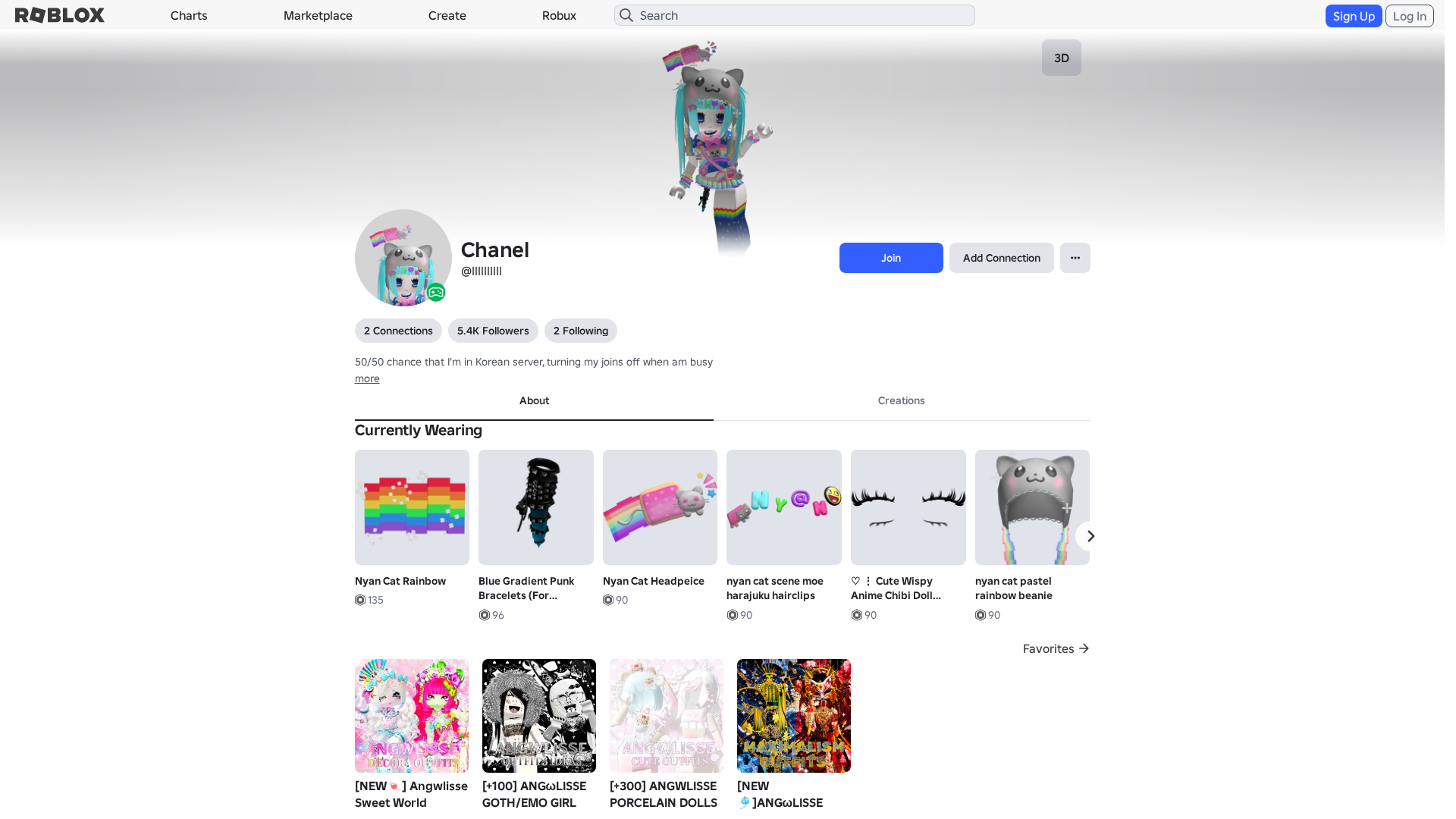
Visual Capture
Detection Info
https://www.robiox.com.py/users/322180173372/profile
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
9742f803-249…
Analyzed
2026-04-08 10:23
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1D6731E7292142837627B69CAF064672ED2D7C70FCA4346E1A2F8D39A0FD6CD1E96340D |
|
CONTENT
ssdeep
|
1536:WdkXWn4rtT2YIDsggUgLsgm2gdwgoigVegJ4gqpg4RgrLgDmgx+grmgy+g+Gg3EW:wkXWgTGuhc1W55IZk0JbqOvQYvjEiB5v |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b04f324999d4ed3c |
|
VISUAL
aHash
|
0000d7ffc3cbc7c7 |
|
VISUAL
dHash
|
c8c8263012128d0d |
|
VISUAL
wHash
|
0000d7ffc3c3c7c7 |
|
VISUAL
colorHash
|
07001048040 |
|
VISUAL
cropResistant
|
c8c8263012128d0d |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/106042195157268/nyan-cat-pastel-rainbow-beanie
- https://api.injuries.lu/catalog/127377929465548/Nails
- https://api.injuries.lu/catalog/18538150608/adidas-Sports-Idle
- https://api.injuries.lu/catalog/105966052025495/Blue-Gradient-Punk-Bracelets-For-Korblox
- https://api.injuries.lu/catalog/86499698/Woman-Right-Arm
- https://api.injuries.lu/catalog/97516976423549/Nyan-Rainbow-Cat-Kawaii-Bag-3-0
- https://api.injuries.lu/catalog/18639918194/nyan-cat
- https://api.injuries.lu/catalog/94610886790653/Cute-Wispy-Anime-Chibi-Doll-Lashes
- https://api.injuries.lu/catalog/106025973091367/Baseball-Hit
- https://api.injuries.lu/catalog/75736751501442/Modern-Woman-2-Left-Leg
- https://api.injuries.lu/catalog/117011755848398/Amazon-Unboxed-Animation-Pack-Climb
- https://api.injuries.lu/catalog/109623821557417/OG-cute-bouncy-kawaii-dance
- https://api.injuries.lu/catalog/77568709550148/bow-bow-bounce-Dance-OG
- https://api.injuries.lu/catalog/106722085020010/Woman-Revamped-V2-Torso
- https://api.injuries.lu/catalog/92504533520053/Hello-Kitty-Dance-OG
- https://api.injuries.lu/catalog/125108870423182/Amazon-Unboxed-Animation-Pack-Fall
- https://api.injuries.lu/catalog/105421944471466/Nyan-Cat-Rainbow
- https://api.injuries.lu/catalog/75816928331300/Nyan-Cat-Headpeice
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/86225180587392/Nyan-Rainbow-Cat-Kawaii-Shirt
- https://api.injuries.lu/catalog/129213624162138/OG-needy-kawaii-bubbly-anime-dance-trend
- https://api.injuries.lu/catalog/75927368362630/blue-chrome-silver-spiked-studded-choker
- /info/blog?locale=en_us
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F322180173372%2Fprofile
- https://api.injuries.lu/catalog/133685484220846/KATSEYE-GNARLY
- https://api.injuries.lu/catalog/136169361994449/ponponpon-kawaii-dance
- https://api.injuries.lu/catalog/14618207727/Default-Mood
- https://api.injuries.lu/catalog/71162009076220/animated-blue-super-kawaii-moe-c-Dynamic-Head
- https://api.injuries.lu/catalog/100924695943215/harajuku-decora-kei-rainbow-bracelets-w-bow
- https://api.injuries.lu/catalog/79024402886472/Blue-Vkei-Scene-Emo-Goth-Pigtails
- https://api.injuries.lu/catalog/86499716/Woman-Left-Arm
- https://api.injuries.lu/catalog/110418911914024/Amazon-Unboxed-Animation-Pack-Jump
- https://api.injuries.lu/catalog/81315493219208/nyan-cat-scene-moe-harajuku-hairclips
- https://api.injuries.lu/catalog/114630462397189/Agnes-Tachyons-Low-Cortisol-Dance-In-Tempo-V2
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F322180173372%2Fprofile
- https://api.injuries.lu/catalog/128339543796138/Amazon-Unboxed-Animation-Pack-Walk
- /login?returnUrl=
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/2510238627/Rthro-Run
- https://api.injuries.lu/catalog/139607718/Korblox-Deathspeaker-Right-Leg
- https://api.injuries.lu/catalog/137392271797713/Amazon-Unboxed-Animation-Pack-Swim
- https://api.injuries.lu/catalog/120446841623811/nyan-cat-pastel-rainbow-skirt
📡 API Calls Detected
- get
- https://help.roblox.com/hc/articles/30428367965460
- https://ro.blox.com/Ebh5?
- GET
- https://apis.
- POST
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 212 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Roblox users
Attack Method
credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
HTTP POST to backend
Risk Assessment
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 212 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 212 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
www.robiox.com.py
Registered
Unknown
Registrar
None
Status
Age unknown
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for www.robiox.com.py
Found 10 other scans for this domain
-
https://www.robiox.com.py/users/262683709646/profi...
https://www.robiox.com.py/users/387072077925/profi...
https://www.robiox.com.py/users/217025834840/profi...
https://www.robiox.com.py/users/335157511751/profi...
https://www.robiox.com.py/users/239884675658/profi...
https://www.robiox.com.py/users/377777277866/profi...
https://www.robiox.com.py/users/255445160301/profi...
https://www.robiox.com.py/users/378472335145/profi...
https://www.robiox.com.py/users/411240076850/profi...
https://www.robiox.com.py/games/90118298734859/EMO...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.