Phishing Analysis
Detailed analysis of captured phishing page
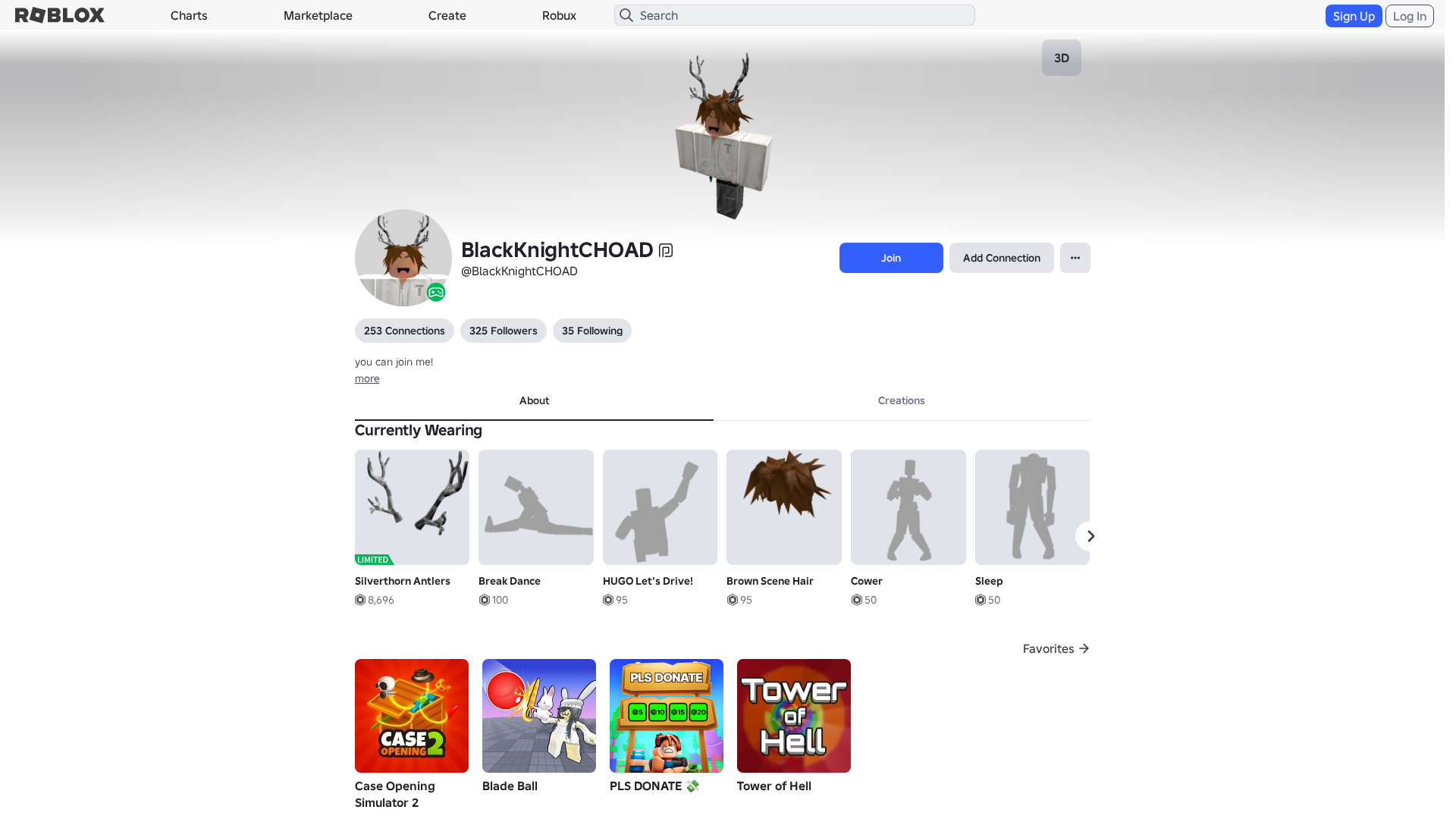
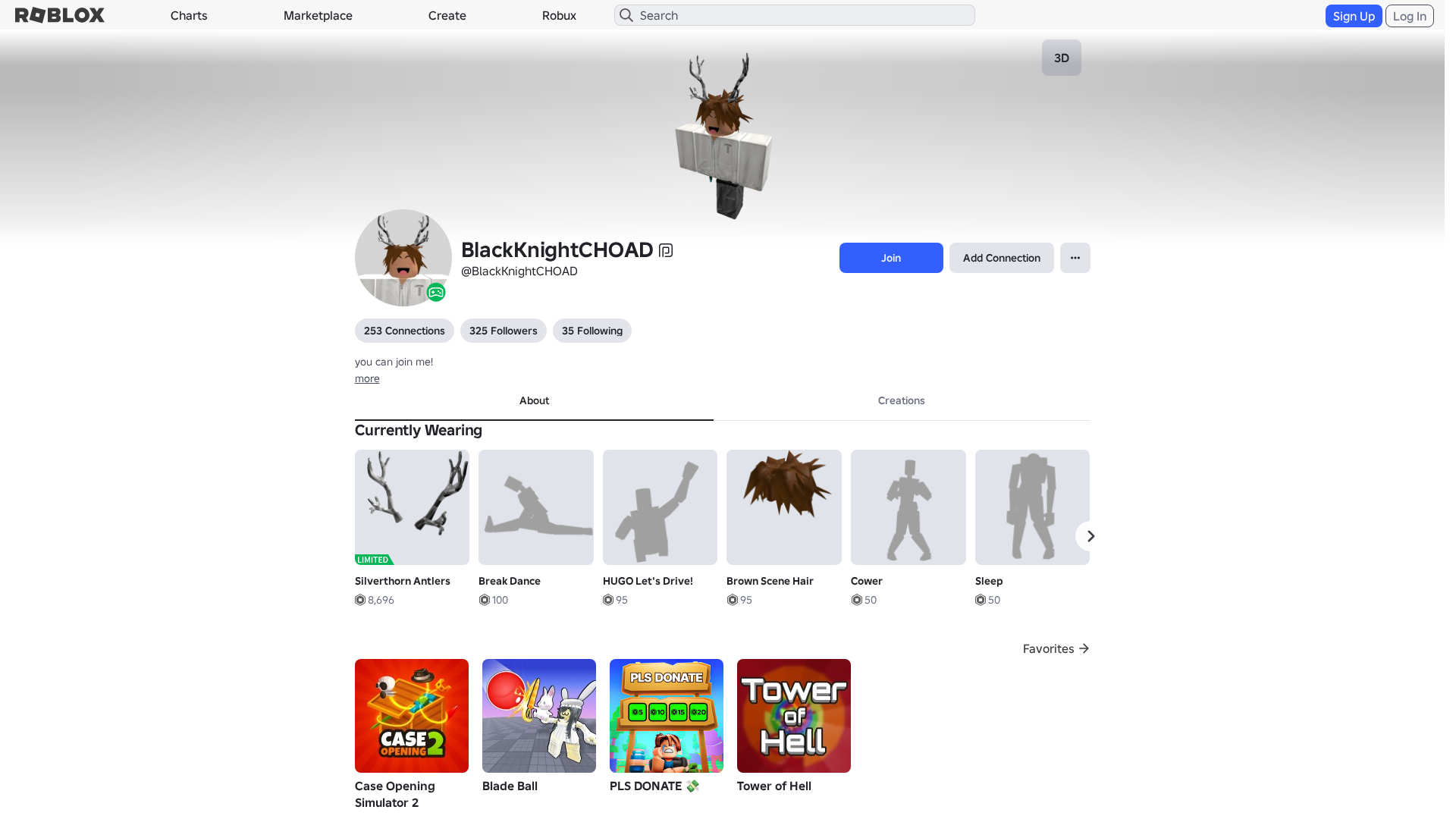
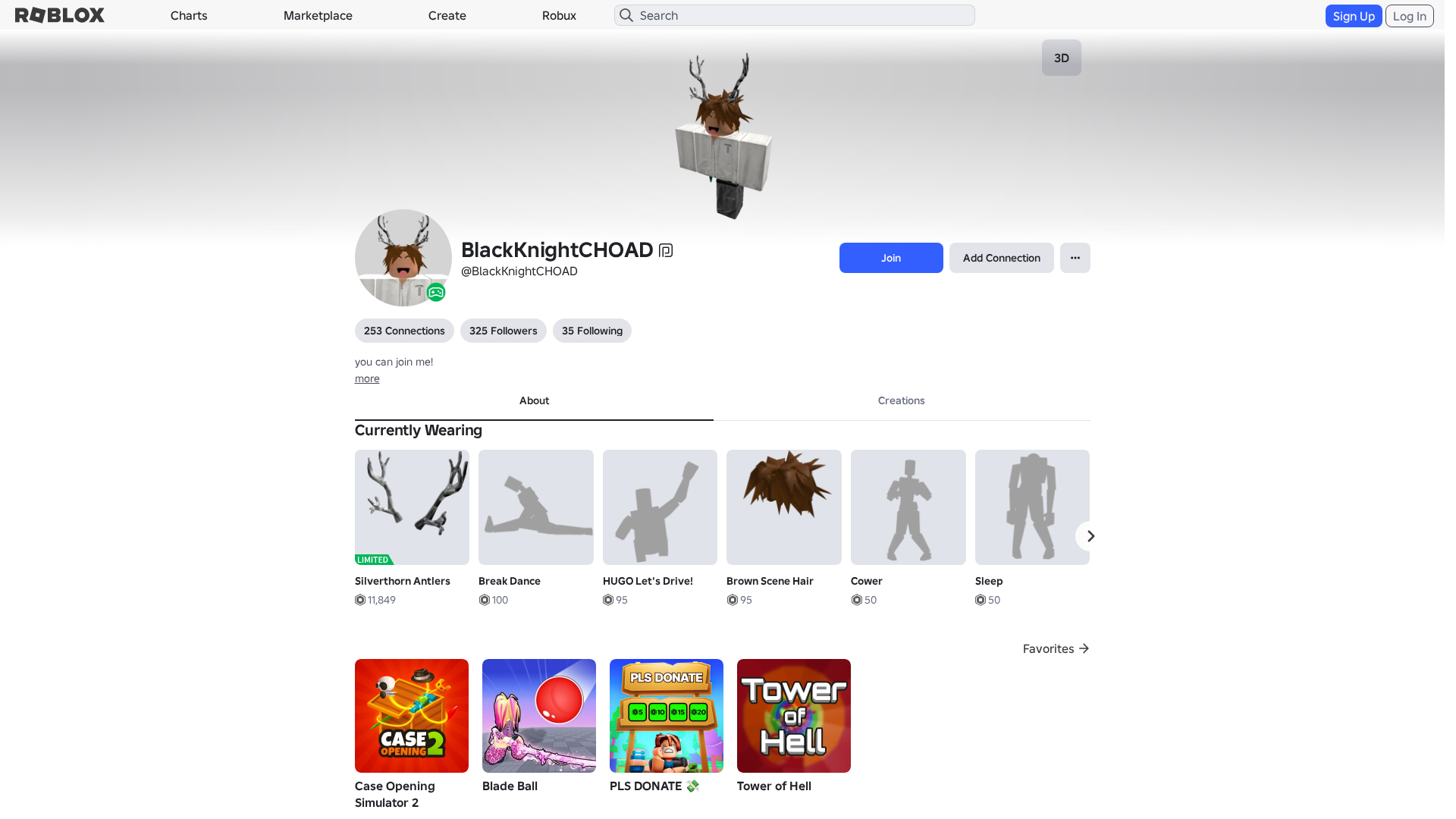
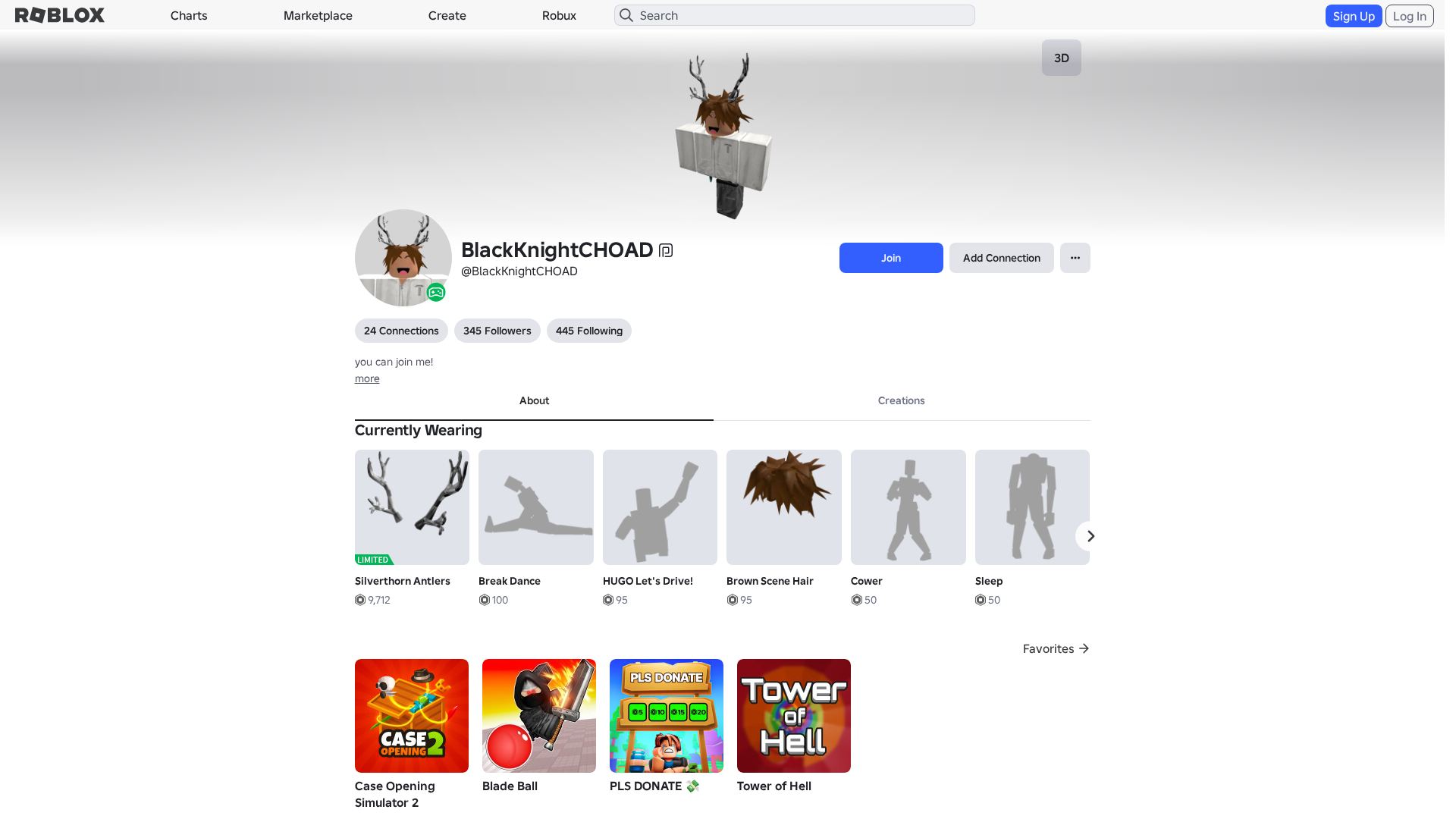
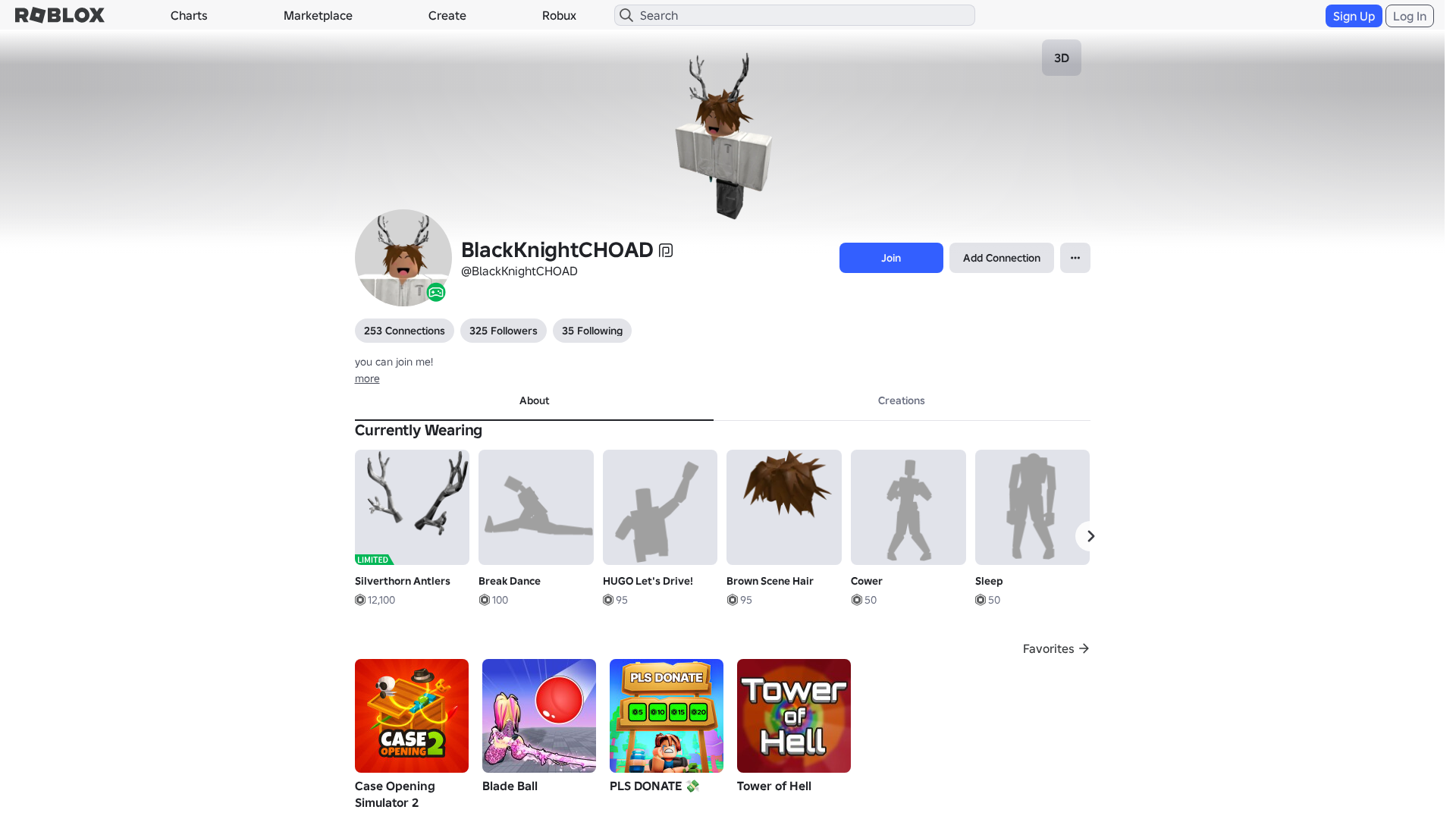
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T13E83327292142837617B79DAF164671AA2D3D70FCA8347E1A2F8D39A0FDAC91EC5340D |
|
CONTENT
ssdeep
|
1536:pvHXWnerYUCebZsgLHyrgEcg4ngn1gYOgmQgVogFWgiKggWgWOgdrgFngahgvHgL:tHXWhUZHyZOcLGrLK0+9sTMjqi70Cj3a |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b44f32479d98cd34 |
|
VISUAL
aHash
|
0000d7ffc3fbc7c7 |
|
VISUAL
dHash
|
e8e8b6302e062d2d |
|
VISUAL
wHash
|
0000d7ffc3c3c7c7 |
|
VISUAL
colorHash
|
07000018040 |
|
VISUAL
cropResistant
|
e8e8b6302e062d2d,c4ccc8e09cf0f4a8 |
Code Analysis
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/4849502101/Sad
- /login?returnUrl=
- https://api.injuries.lu/catalog/619536621/Zombie-Run
- https://api.injuries.lu/catalog/323476364/Brown-Scene-Hair
- https://api.injuries.lu/catalog/9255011/Silverthorn-Antlers
- https://api.injuries.lu/catalog/15001674422/chrome-heart-white-zip-up
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/4689362868/Sleep
- https://api.injuries.lu/catalog/17800970314/Shop-TopShelf
- https://api.injuries.lu/catalog/14618207727/Default-Mood
- https://api.injuries.lu/catalog/5319927054/Oldschool-Swim
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F323529055501%2Fprofile
- https://api.injuries.lu/catalog/135470357521276/Super-Happy-Face-Dynamic-Head
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F323529055501%2Fprofile
- https://api.injuries.lu/catalog/5915773992/Break-Dance
- https://api.injuries.lu/catalog/2510235063/Rthro-Idle
- https://api.injuries.lu/catalog/17360720445/HUGO-Lets-Drive
- https://api.injuries.lu/catalog/754639239/Mage-Climb
- https://api.injuries.lu/catalog/2510242378/Rthro-Walk
- https://api.injuries.lu/catalog/5319917561/Oldschool-Jump
- https://api.injuries.lu/catalog/754636589/Mage-Fall
- https://api.injuries.lu/catalog/4646306583/Curtsy
- https://api.injuries.lu/catalog/5915779043/Applaud
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/139607718/Korblox-Deathspeaker-Right-Leg
- https://api.injuries.lu/catalog/4940597758/Cower
- https://api.injuries.lu/catalog/5915776835/High-Wave
📡 API Calls Detected
- https://apis.
- https://ro.blox.com/Ebh5?
- POST
- get
- GET
- https://help.roblox.com/hc/articles/30428367965460
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 207 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 207 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for urlyte.com
Found 4 other scans for this domain