Phishing Analysis
Detailed analysis of captured phishing page
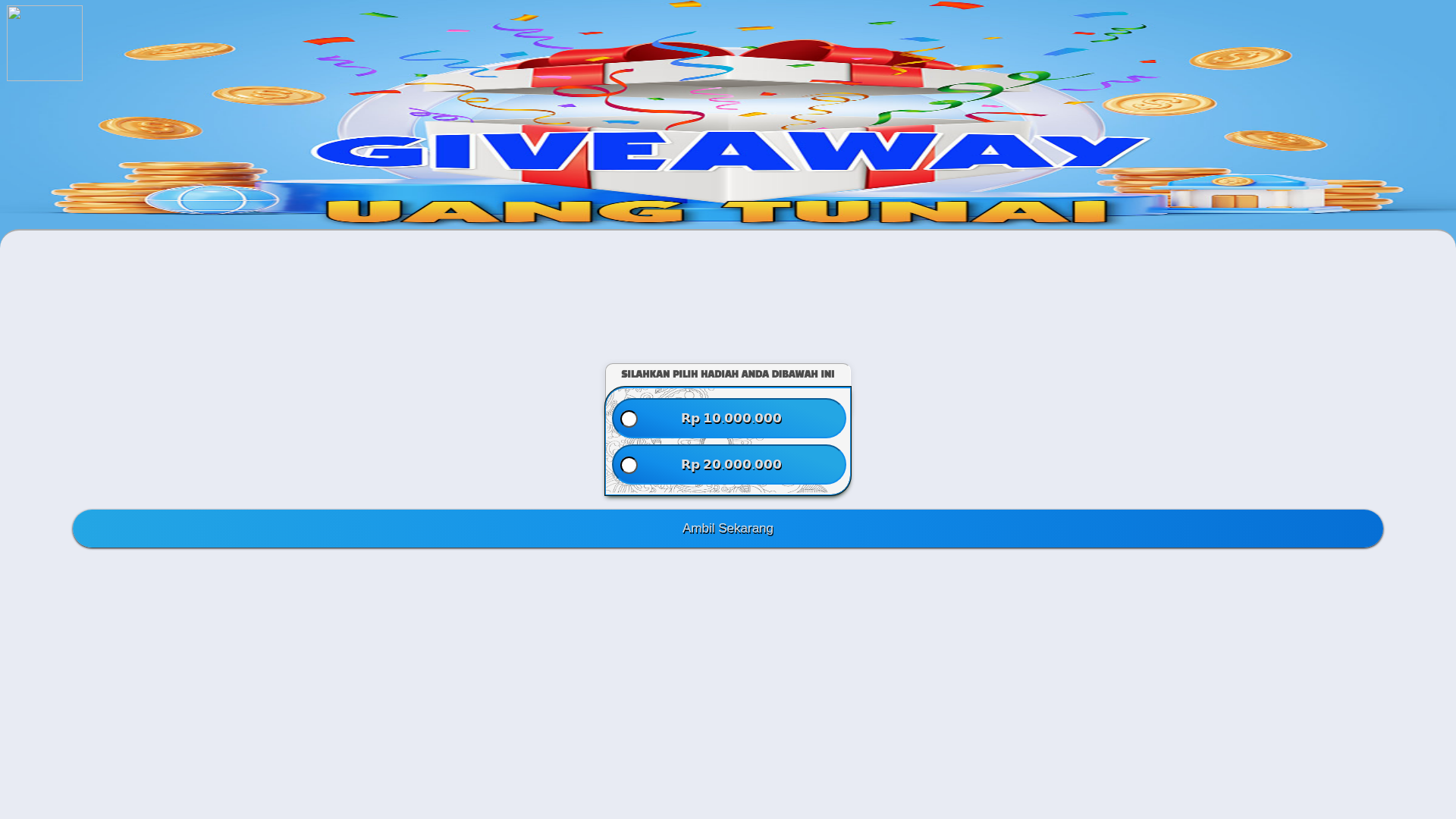
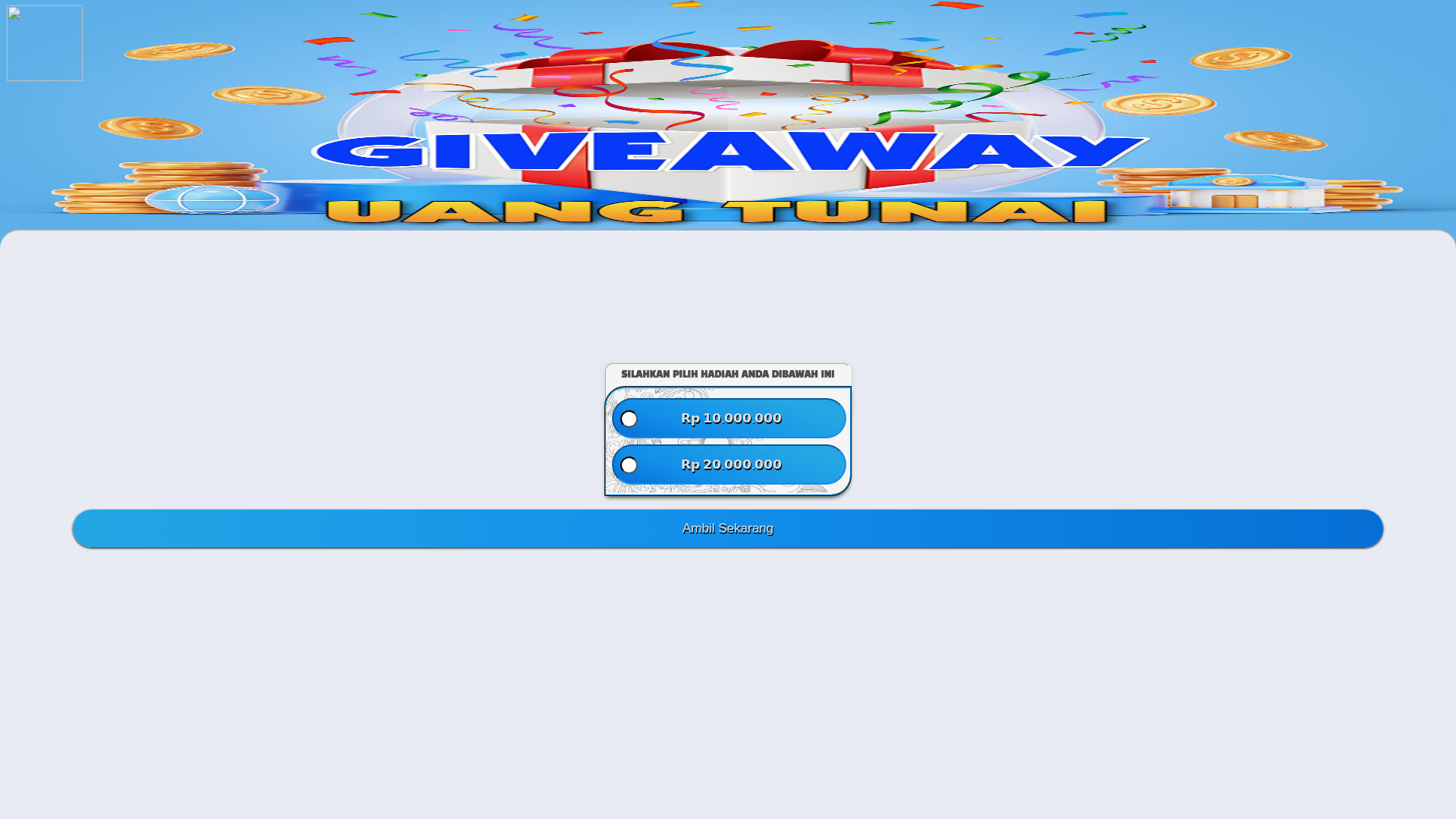
Visual Capture
No screenshot available
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T17EF1E8A2A15C48083226C681BEA1FE486337CA46CB5D193AB1B62457B3DE5F4C1373A1 |
|
CONTENT
ssdeep
|
96:Crhvf25BPf2iSiSz5TdvVXZXh9h1kD5OEpdjKlVZsquTn1P/y8tj7PadPOQie:MU/SiSphFZvkDZ1Kl/squpP/y8tvSdPz |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
f3151d62e68c4a37 |
|
VISUAL
aHash
|
0000dfffe780ffff |
|
VISUAL
dHash
|
d49632cc4d118401 |
|
VISUAL
wHash
|
000081ffe700ffff |
|
VISUAL
colorHash
|
07006000080 |
|
VISUAL
cropResistant
|
d49632cc4d118401,0000202000000000 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Indonesian-speaking users
• Method: Deception through fake giveaway.
• Exfil: The forms likely collect personal information. (Forms detected = 4)
• Indicators: Unrelated domain, obfuscated JavaScript, and suspicious offers.
• Risk: High
🔒 Obfuscation Detected
- fromCharCode
- unescape
📡 API Calls Detected
- POST
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
- 4 obfuscation techniques
🏢 Brand Impersonation Analysis
Fraudulent Claims
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attackers will likely attempt to harvest login credentials or personal information from users interacting with the page. Forms are present on the website.
Secondary Method: Malware distribution
If the attacker is successful, they could use this to distribute malware to anyone who gives them the info they asked for
🌐 Infrastructure Indicators of Compromise
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for qwip.qzz.io
Found 2 other scans for this domain