Phishing Analysis
Detailed analysis of captured phishing page
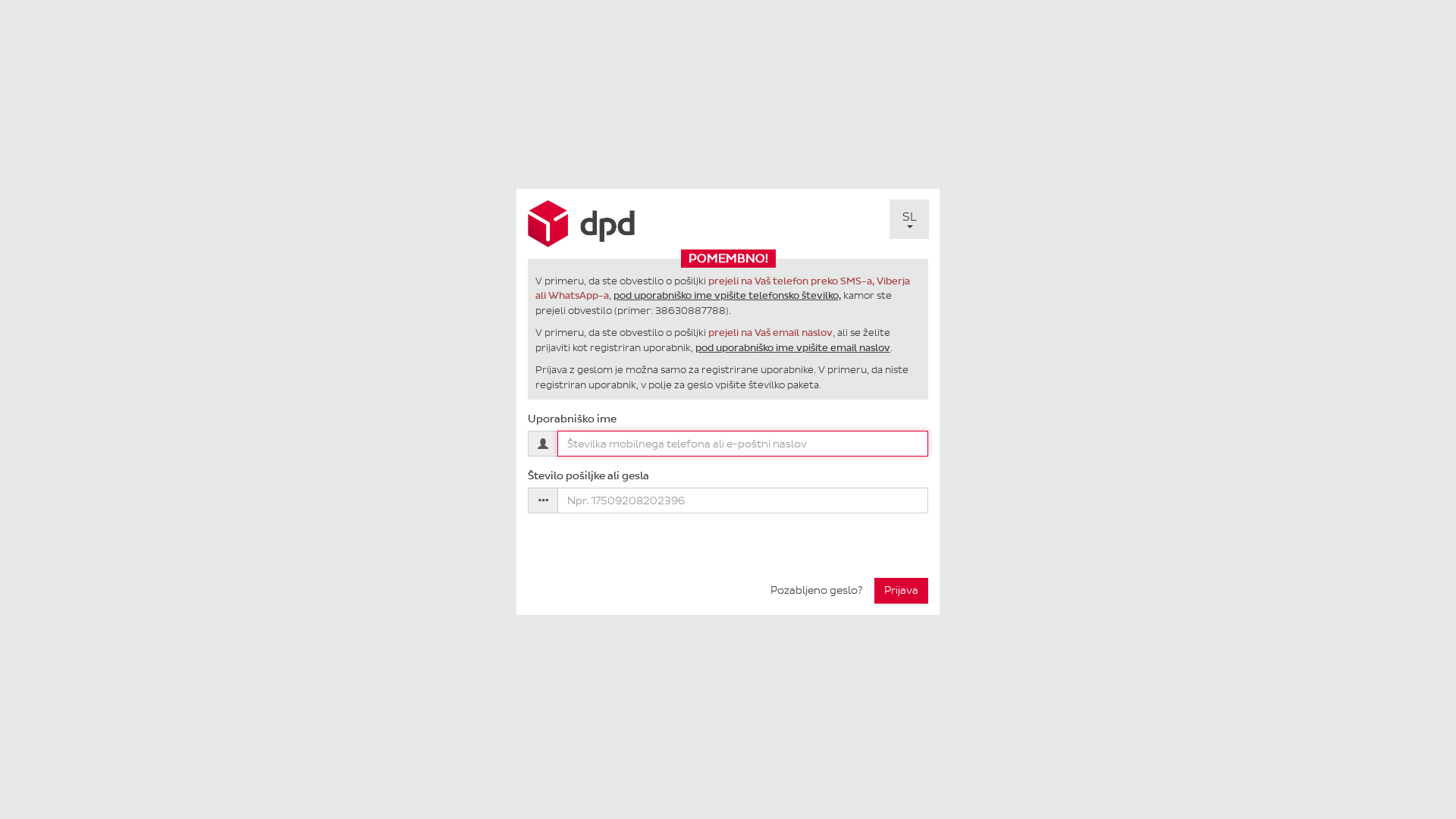
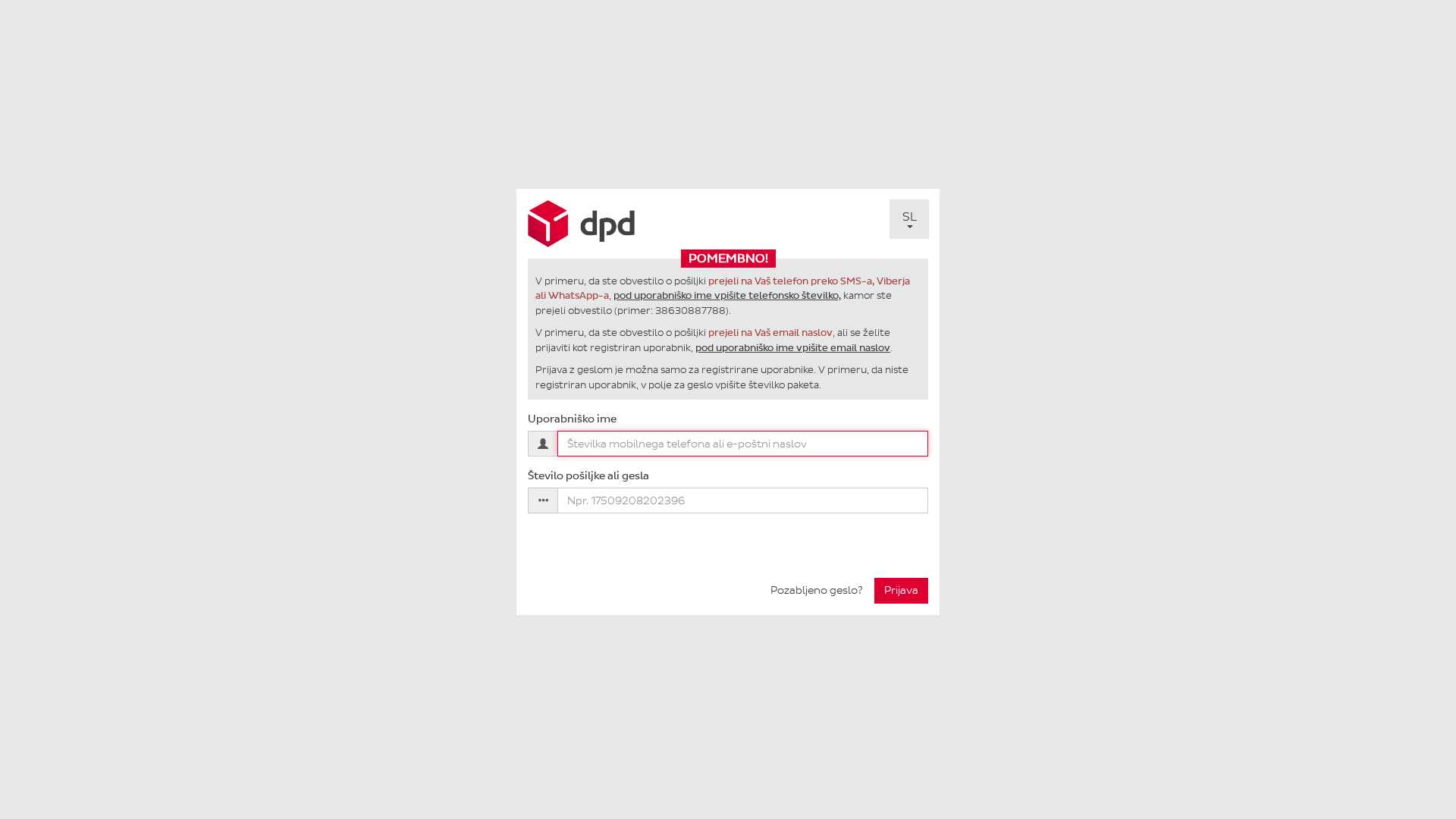
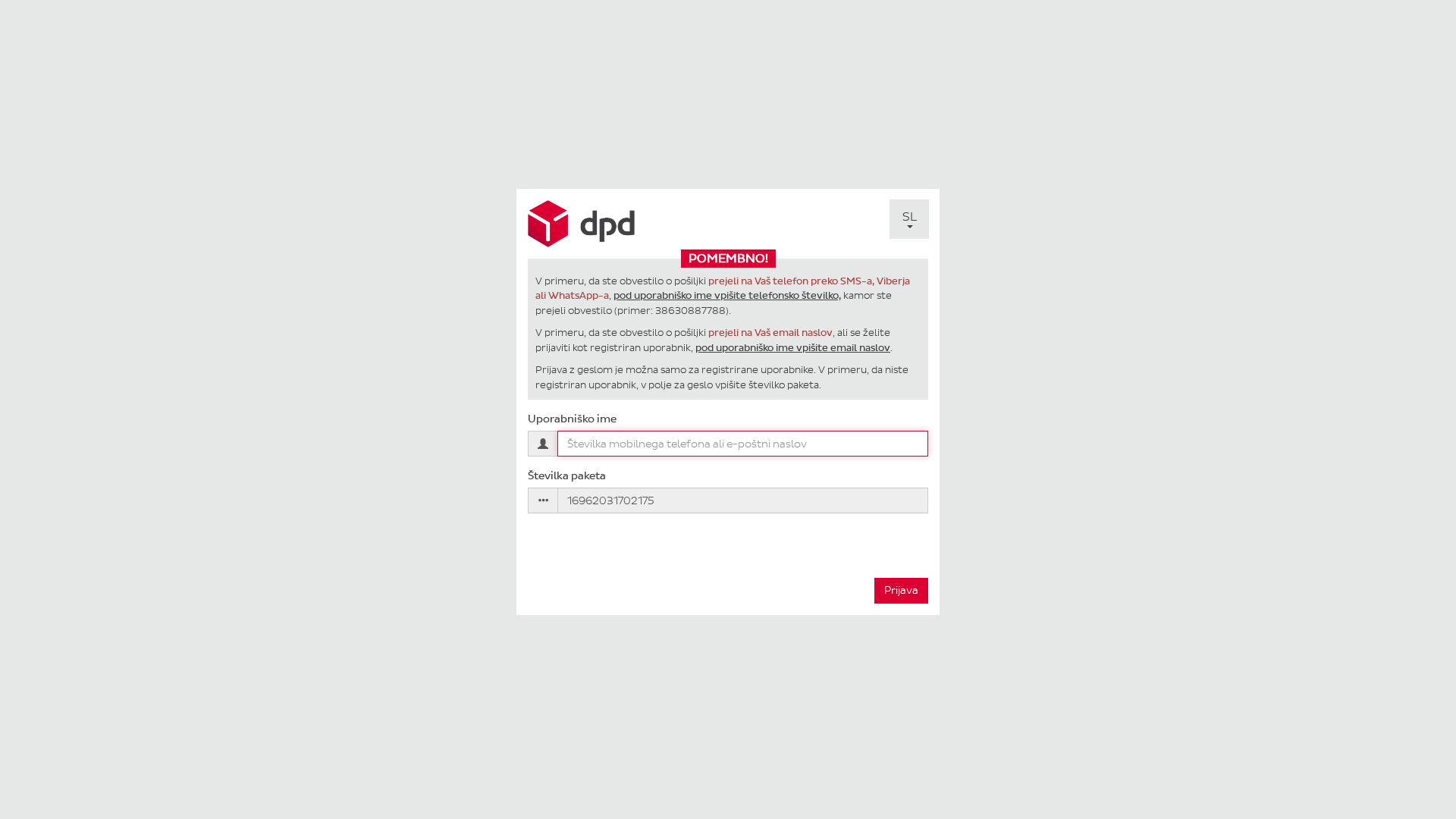
Visual Capture
Detection Info
https://pay.mojdpd.si/SL/Login/Login?scid=16962031702175
Detected Brand
DPD
Country
International
Confidence
100%
HTTP Status
200
Report ID
98b81144-0f1…
Analyzed
2026-02-17 16:08
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1C2A1A57190048C3B569784EDBAB09B0A36C5C248CE4B8E46EBFC93EC8FD2C57EE25551 |
|
CONTENT
ssdeep
|
48:vd/cpZ8NzktQg5ZW0wX60TMlllq8CGC9SrFy853TS5QcHs6Z01h6mbzSJmREDLh:1/8Z8RktQAa6SUpCuFaskstSJmeh |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
993364cc3366ce99 |
|
VISUAL
aHash
|
201844243c3a1000 |
|
VISUAL
dHash
|
2c10184c30322408 |
|
VISUAL
wHash
|
303c0424fcf8fcfc |
|
VISUAL
colorHash
|
07200000006 |
|
VISUAL
cropResistant
|
2c10184c30322408 |
Code Analysis
Risk Score
76/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Phishing
• Target: DPD users
• Method: Impersonation via fake login page
• Exfil: Phone number/email, package number
• Indicators: Domain mismatch, form submission, request for sensitive info
• Risk: High
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- fromCharCode
- unicode_escape
🎯 Kit Endpoints
- /IT/Login/Login?scid=16962031702175
- /HR/Login/Login?scid=16962031702175
- /DE/Login/Login?scid=16962031702175
- /SL/Login/PasswordForgotten
- /EN/Login/Login?scid=16962031702175
- /SL/Login/Login?scid=16962031702175
📤 Form Action Targets
- /SL/Login/PasswordForgotten
- /SL/Login/Login?scid=16962031702175
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Domain Mismatch
The domain does not match the official DPD domain.
Requests for sensitive data
The form requests a phone number/email and package number.
JavaScript Obfuscation
Obfuscated JavaScript code present.
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
DPD users (International)
Attack Method
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
HTTP POST to backend
Risk Assessment
HIGH - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 16 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
DPD
Official Website
dpd.com
Fake Service
Login
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker is trying to collect phone number/email and package information from unsuspecting victims by impersonating DPD.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
pay.mojdpd.si
Registered
2014-01-29
Registrar
Unknown
Status
Active
🔬 JavaScript Deep Analysis
Total Code Size
191.8 KB
🔗 API Endpoints Detected
Other
10
🔐 Obfuscation Detected
- : None
- : None
- : Light
- : None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for pay.mojdpd.si
Found 10 other scans for this domain
-
https://pay.mojdpd.si/secure-account
https://pay.mojdpd.si/SL/Login/Login
https://www.pay.mojdpd.si/SL/Login/Login
https://www.pay.mojdpd.si
https://pay.mojdpd.si/
https://pay.mojdpd.si/SL/Login/Login?scid=16962036...
https://pay.mojdpd.si/SL/Login/Login?scid=16962036...
https://pay.mojdpd.si/SL/Login/Login?scid=16962035...
http://www.pay.mojdpd.si
https://pay.mojdpd.si/Payment/DPD2001

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.