
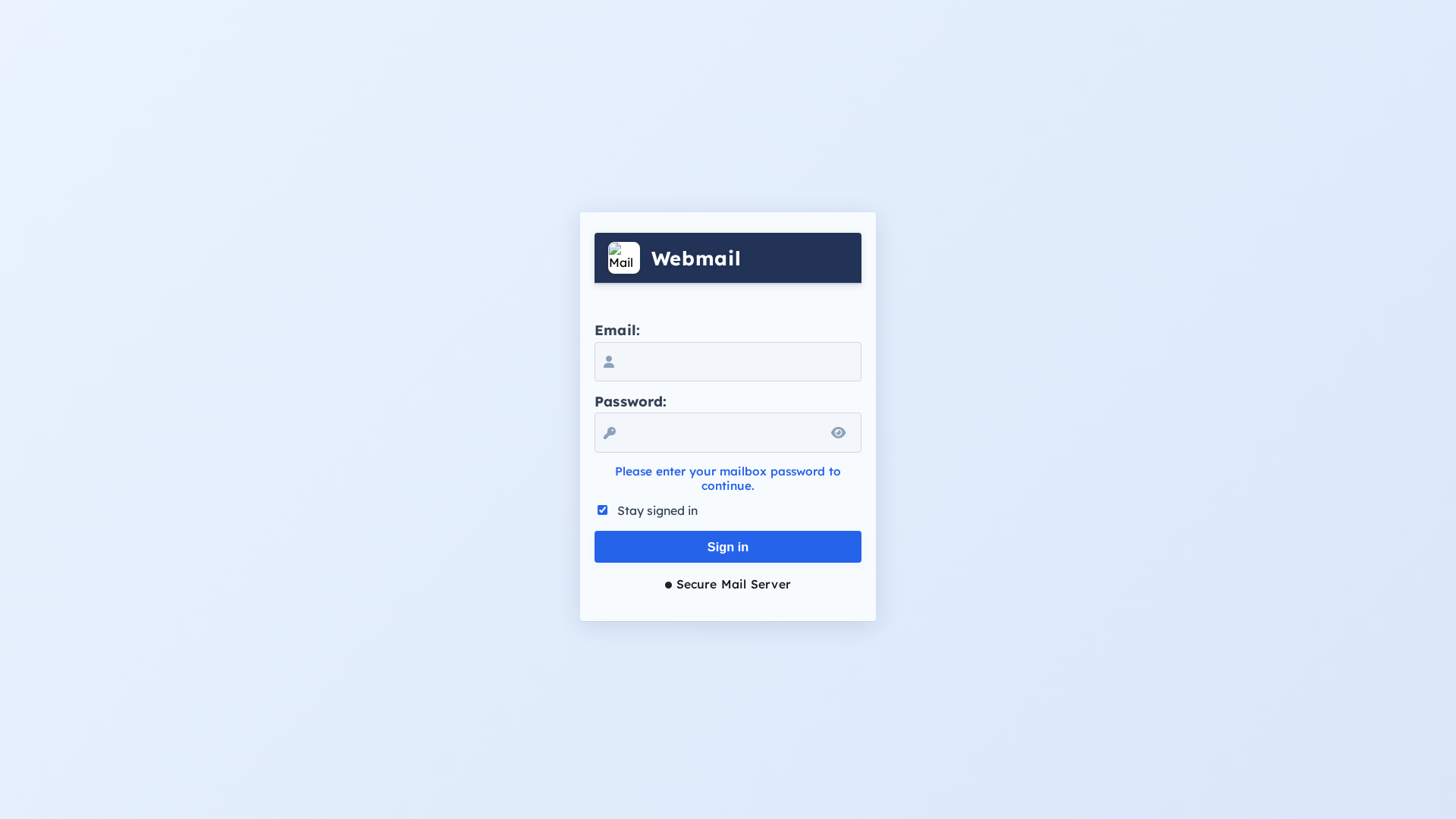
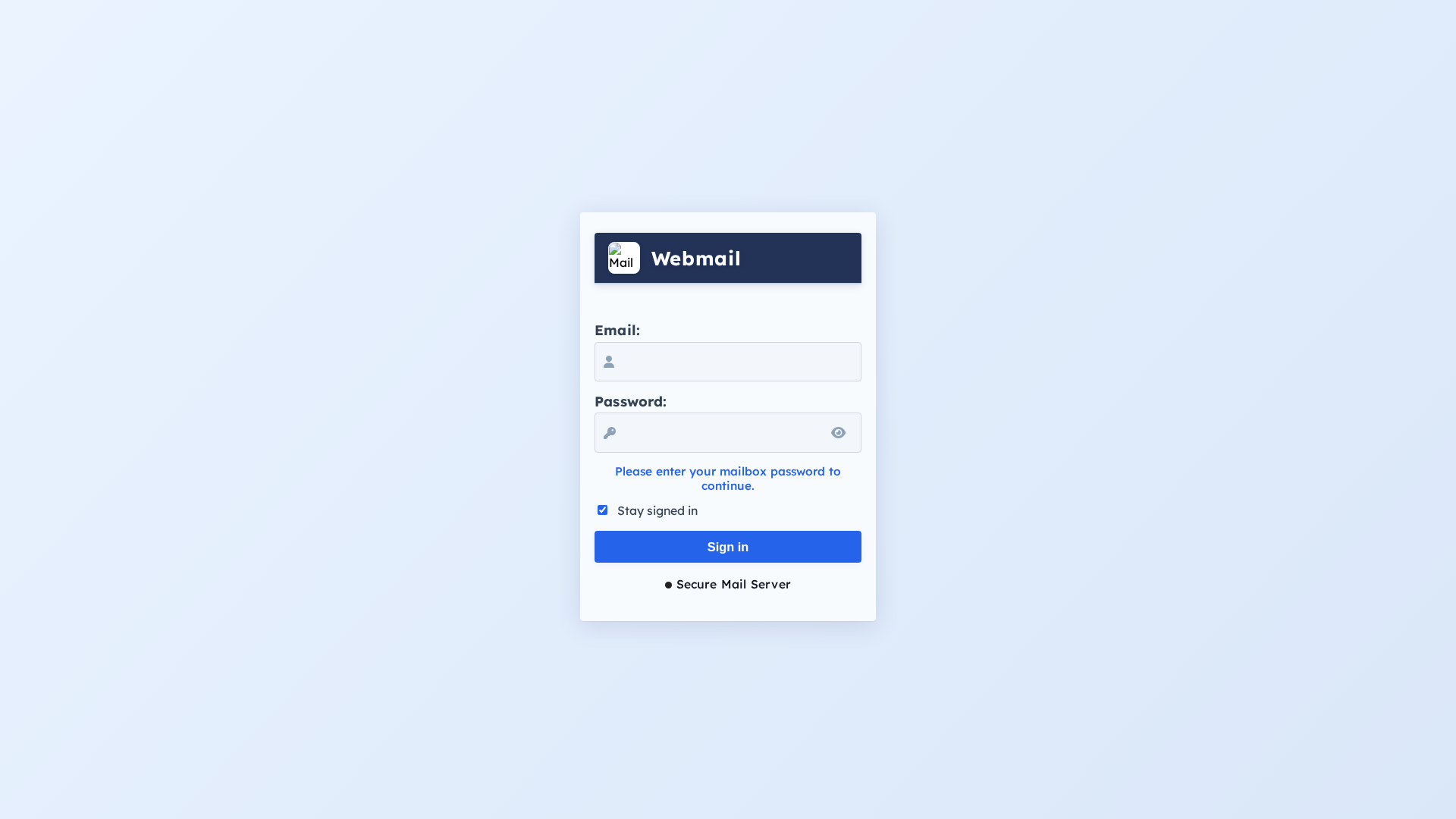
Phishing Analysis
Detailed analysis of captured phishing page
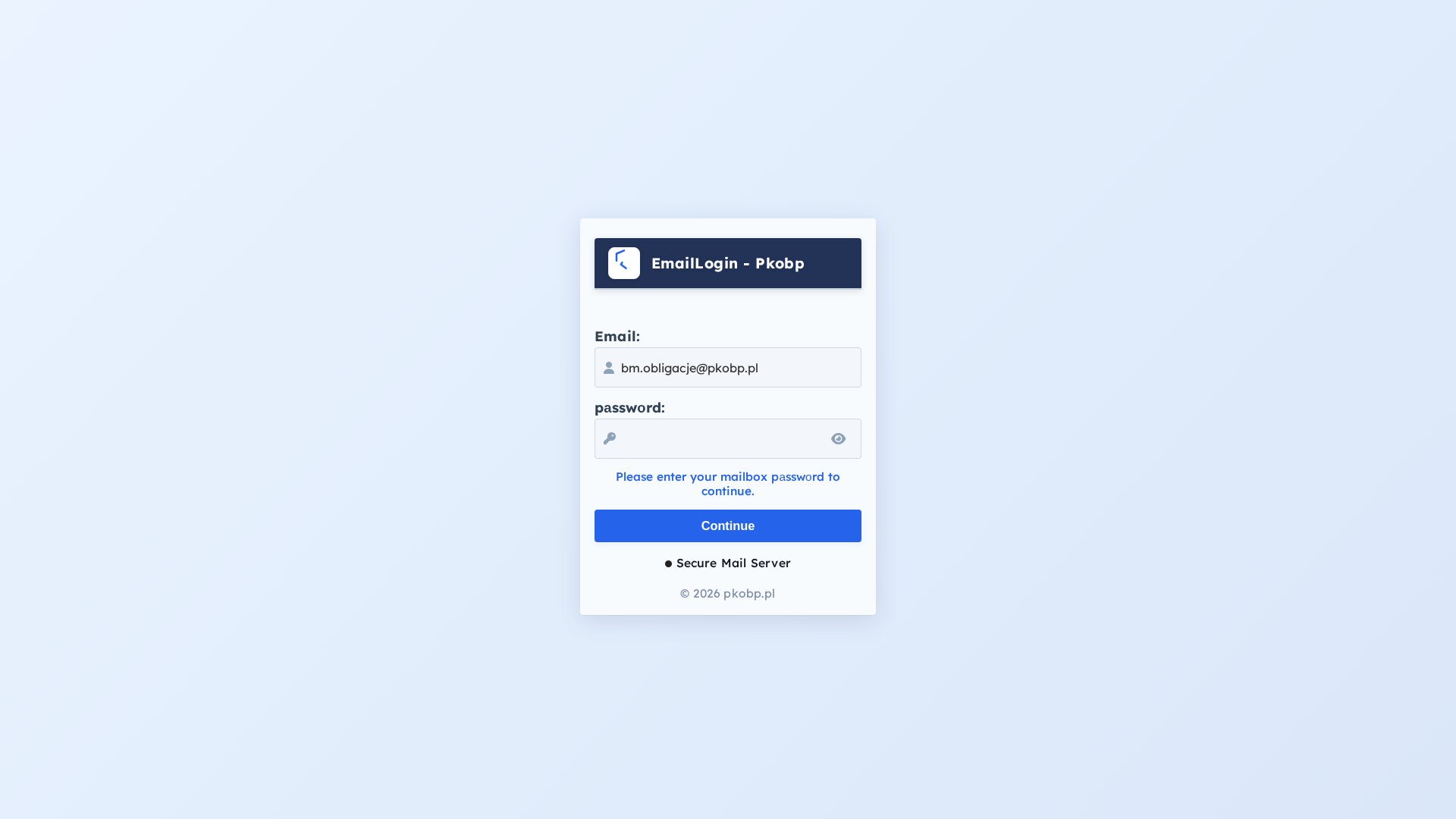
Visual Capture
Detection Info
https://bafkreigpc2vwbbztkll32zobc4asja44hmms2qxkhvypcw4moxtlgz6mnq.ipfs.dweb.link/#?8JX2KQ5NP=ZPQJ7T8W4KYm0ub2JsaWdhY2plQHBrb2JwLnBsJX8V4N2QPK&mode=retrievalVK9J2L8PQX
Detected Brand
Pkobp
Country
Unknown
Confidence
95%
HTTP Status
200
Report ID
98dcbad1-948…
Analyzed
2026-02-24 10:40
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T115414431A01968731292CBD877E17F0B36D6C306CB222A0063FD539D9BFAD0EDD68494 |
|
CONTENT
ssdeep
|
48:nCKWhcqGgC9bK5aOWJGFPvaIU/G82DAnHk:nChrGPGaOyGFPvaIU/72DAnHk |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
f6a6cc9999886666 |
|
VISUAL
aHash
|
ffffe6fee4e4f8f0 |
|
VISUAL
dHash
|
00104c100c4c3000 |
|
VISUAL
wHash
|
fcf8e0f8f8e0e0c0 |
|
VISUAL
colorHash
|
070060000c0 |
|
VISUAL
cropResistant
|
00104c100c4c3000,c0242b2c24242ad0 |
Code Analysis
Risk Score
53/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🔒 Obfuscation Detected
- atob
📡 API Calls Detected
- POST
📊 Risk Score Breakdown
Total Risk Score
70/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 3 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Credential Harvesting Kit
Target
Pkobp users
Attack Method
credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
MEDIUM - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
- 3 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Pkobp
Official Website
N/A
Fake Service
Credential harvesting service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 3 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
bafkreigpc2vwbbztkll32zobc4asja44hmms2qxkhvypcw4moxtlgz6mnq.ipfs.dweb.link
Registered
2017-02-24 01:05:26.675000+00:00
Registrar
CSC Corporate Domains, Inc.
Status
Active (older domain)
Hosting Information
Provider
CSC Corporate Domains, Inc.
ASN
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
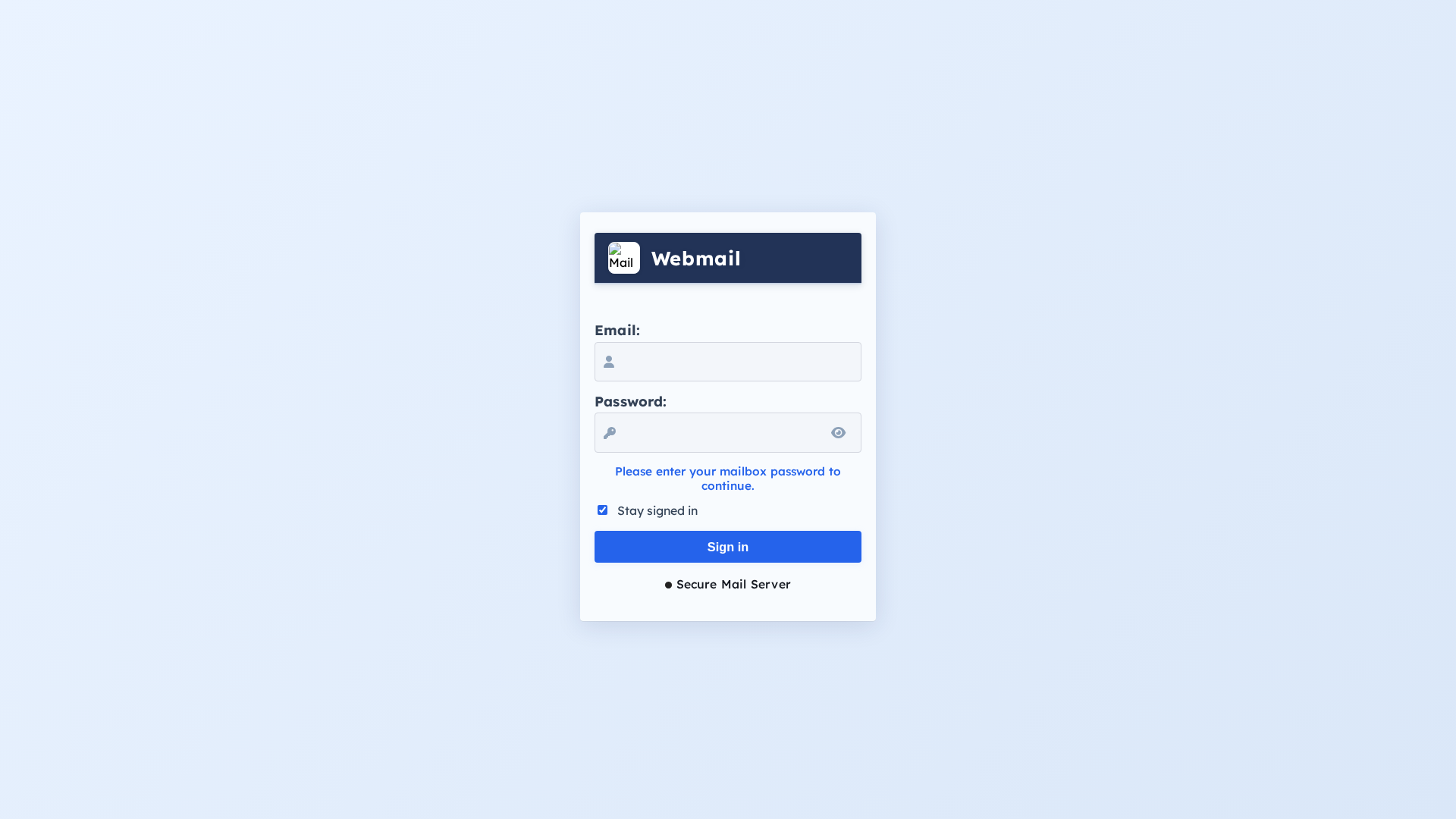
Unknown
https://bafkreiegwxj3pfnc2yw57fzl7tfjmdhqqa3qczjjcretig7quyw...
Mar 19, 2026
Unknown
https://bafkreial2cuys7iusfolkwwkfnlitggozipsvdyq7lg4wo4z7tw...
Mar 16, 2026
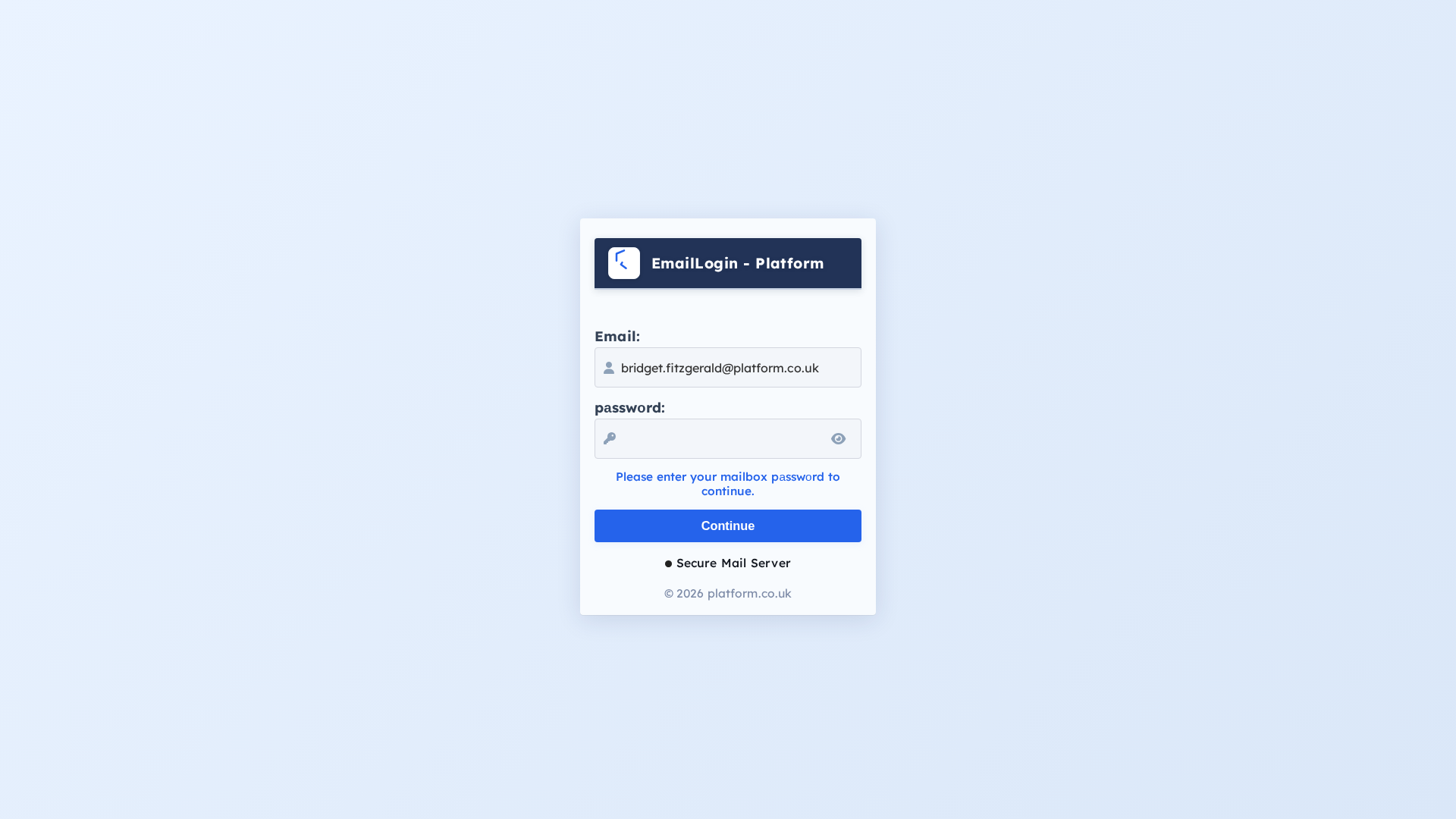
Platform.co.uk
https://bafkreietmq2owe4mmr4olp44ogax3zu5zxvomkq5cawnxu5viva...
Feb 27, 2026
Unknown
https://bafkreia5ihvxa3nwohacg5auov7n6ah5rmawhnhm5vo3cddhnmq...
Feb 22, 2026
Unknown
https://bafkreibrbyrcuoxifhtpqgkshrysa5uq2u332vhtmzvui7gtius...
Feb 05, 2026

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.