
Phishing Analysis
Detailed analysis of captured phishing page
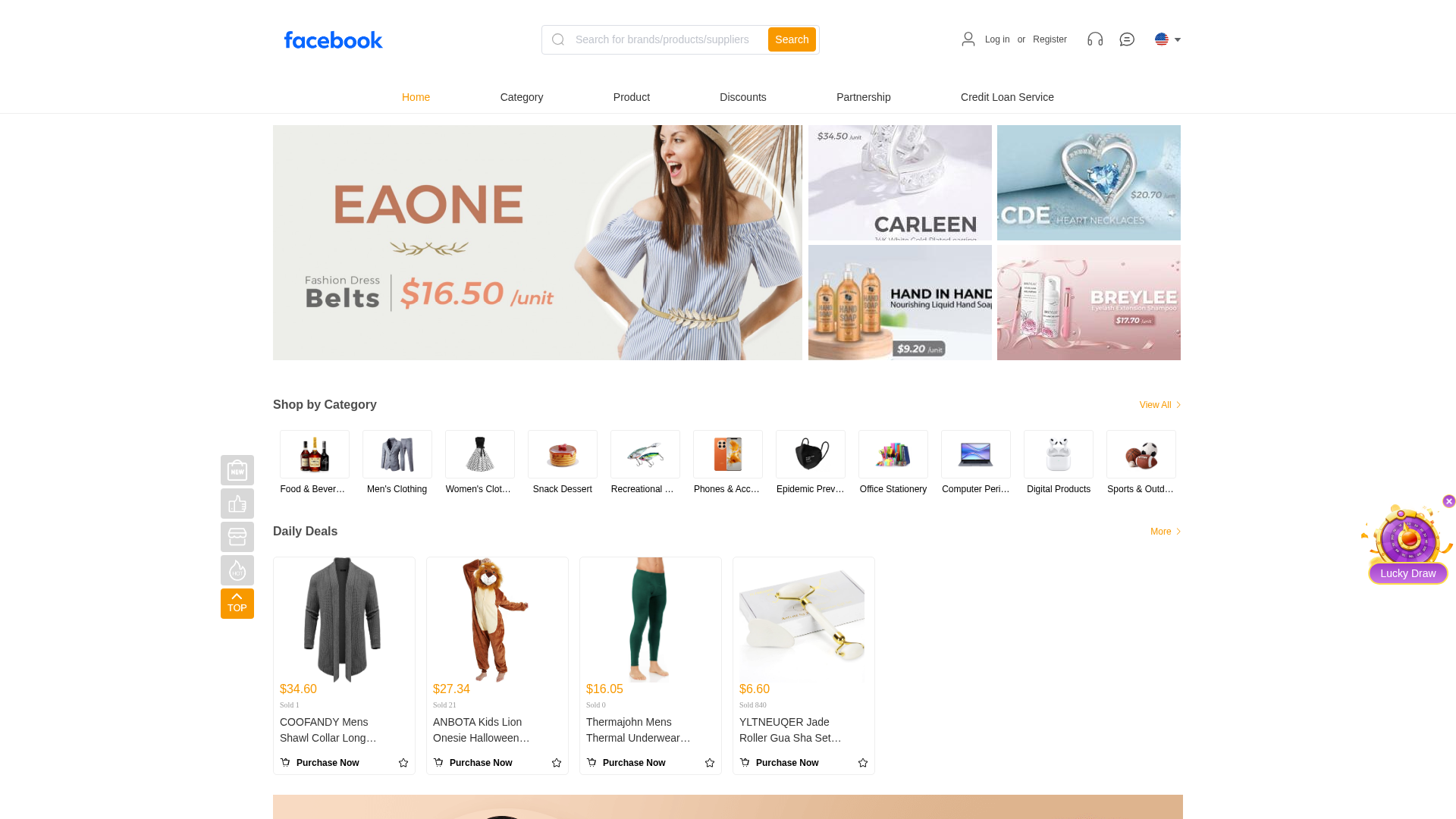
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1646320B1C695213B02278EE4B4706B4F72E3C31DDE67891157FC878E6FEAC94EA05489 |
|
CONTENT
ssdeep
|
1536:v4DAoy9ObtmohIgAHJUBpNxmkaGntpoyxiGaUAWj:v4EgzEa |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
bf63809cc89e75a2 |
|
VISUAL
aHash
|
ffc181e1ff8e8fe3 |
|
VISUAL
dHash
|
650b0b0b262e2c0b |
|
VISUAL
wHash
|
ffc181e1838e8f83 |
|
VISUAL
colorHash
|
07e00008000 |
|
VISUAL
cropResistant
|
650b0b0b262e2c0b |
Code Analysis
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- document.write
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAF8AAAAVCAMAAAAXUcLNAAACc1BMVEVHcEz///////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////8bb2ogAAAA0HRSTlMAv1iIcM9goBCAAUAKUGgMBgQDCwgPTfNuBRwHSQ7f1yyjh4JnGBT2MJACY1QqEhZaIDw5LxrxUbsbN8koa1Pk6ZlcdIpEZSudTNu6xo6+f9gVvX4n9at4jJH6r9R6eYa8F7VGCcyVy/5CuCGxzeCUhJjh/WI+M3yeSkPRcoEuQX3EpvskRSWn08hHV92waUtIwzatrI0m92Hlx5ZZIyI7deelXU41mj9tuWyLwmZv+fSS1R2pUvKq0E+yd5y3Ww3BPY8e3MUycfw4anZW5rZ7RFkjWwAAA2RJREFUOMud0lVXY0sQhuE3AbJDJq4kAYK7u7u7y7i7u7v7zHF3d3d3r590LjY5EAgDc+qua3U/a1X1x4WWnnciCV8Zu6vTo2c29A9l5rGo8naO52i9wJq3R2U+36pdKiF+jmyOXRT/zWk3lByPA1xvzuvDhlD/4YoHKhfDt/f6AHwpJeBcdg9/a6iP0boY3jJhuRBjuvqLO/80oNzDXzbLD5YzJWz7I736Tea7vxlj/nD8fE23gK/M4x8ZC9ct7Qj6KQb/+O8O+/D/9H1dmnBruRQV9MsL8Z3nh4IpP2vbi221bpe64oQCXfZbdalB31rjrn20ygbgyB9ZlwHoAhIwmUy54Kpqasve79YDbOmT+CaT6QDozZYIB1i+LlX9Fa+ueqU4QgYqAUOMp7Fmfev1+nbVz4zp3XLw2efW+gBttUgEoNsjUTqdLoG8J5ZGpLqebAhUAqZMiTfrdK2gN3PyxIhPV4Tq7zxkBP9qecMGafGeQjB8IXtUv77FCoby9B2pQFGDRADEiLqfokceywf7YTEDLJHgfpovfndzrPH4kpPNgCJdceqj14yQ9mBiFpAj1UZAkeVrAJzbpd8Gjm5ZARA95bc/vhIgSVYBHAn61tirBxIscSWtsZ2AIi8DUCeb9IBjPcBn6l1FGtW/K5BAKtgS1SwEfUNcFkCyOpU26M/OyEpCxgPSEoP+VH4SyvZVTWct6Kv19OoF/MhZfvGu3v5ZfuFeaQrvP7PxhHI/vqX2/RsZwcO0Hy+6ML7z9eXKU0Teh1+64WOTnTn++Xipm+vn9r2bA9P+pwv7yfKVl7l+sSe9Zqa/yQYwKZ8bZ/p7B+fyhk+m/KMSpcf/t+yeMasiG9VbzbLWDvyXnygnYPhJktX8tKhvGkrn+sYdkgRAtgTy8Y/JpBrpY3mAIneMAP5jnpcA65CMAwzLzkHA3i0TBjCclS8Brsm5XMAWwtuzz0nPNsBVIb/+CUVlf43AqbMez8EsE4rIsB/idtW/ABhOlcmZD4DYzZLitZZ7b48OZGC/1b3vyqCljZJROeyi0x3im7drNH1KLHcnKzSaG/84uFVx/c6lm3n7L3d9X0xyeUFS5nsdz0fneoGUDzWaoY51YDt0uWxrf4KB20M/fpuoTYse6Em6CNoz6Vcmjjpn8v8C3kcAS+1rQYkAAAAASUVORK5CYII=
📡 API Calls Detected
- https://epaycash.hk/
- /api/credit!apply.action
- /api/notification!message.pagelist
- https://play.google.com/store/apps/details?id=com.commerce.app
- /api/credit!beforereapply.action
- /api/credit!pay.action
- https://www.hsbc.com.hk
- https://www.huobi.com/en-us/
- https://www.goldmansachs.com/
- api/syspara!getSyspara.action
- /api/credit!config.action
- https://www.graceloanadvance.com/
- https://10bestpersonalloans.com/go/pmax-usa-eng-d-g.html#o6
- https://www.bdo.com/
- /api/localuser!get.action
- https://www.bitfinex.com
- /api/localuser!registerNoVerifcode.action
- https://www.hangseng.com
- https://www.binance.com
- https://www.bankofamerica.com/
- https://www.kraken.com
- https://play.google.com/store/apps/details?id=com.in.ceapp.go
- https://www.nectar.com
- /api/category!tree.action
- https://crypto.com/
- /api/credit!bill.action
- https://www.mastercard.com/global/en.html
- https://www.credit-suisse.com
- https://www.about.sainsburys.co.uk/news/media-enquiries
- /api/category!sellerTree.action
- https://metamask.io/
- /api/localuser!registerWithVerifcode.action
- /public/userOnlineChatController!unread.action
- https://www.coinbase.com
- https://www.sc.com/en/
- https://www.cimb.com.my
- https://www.citi.com/
- https://www.zellepay.com/
- /api/credit!check.action
- https://www.loanstreet.sg/
- https://www.dbs.com.sg
- https://tuclothing.sainsburys.co.uk/
- https://www.kucoin.com
- https://www.ubs.com
- https://www.rhbgroup.com
- post
- /api/credit!histroy.action
- https://www.sainsburys.co.uk
- https://www.okx.com
- https://www.barclays.co.uk/
- https://hk.lendela.com
- https://www.jpmorganchase.com/
- https://www.about.sainsburys.co.uk/sustainability/plan-for-better/our-stories/2017/standing-up-to-modern-slavery
- GET
- https://www.cimbclicks.com.my
- api/user!logout.action
- /api/credit!beforepay.action
- api/newOnlinechat!unread.action
- /api/activity/lottery!getCurrentActivity.action
- https://sainsburys.jobs/
- https://www.about.sainsburys.co.uk/brands-that-deliver/argos
- /api/jscode!execute.action
- https://apps.apple.com/my/app/shop2u/id6448880380
- https://www.wellsfargo.com/
- https://www.hsbc.com
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 24 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 24 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
