Phishing Analysis
Detailed analysis of captured phishing page
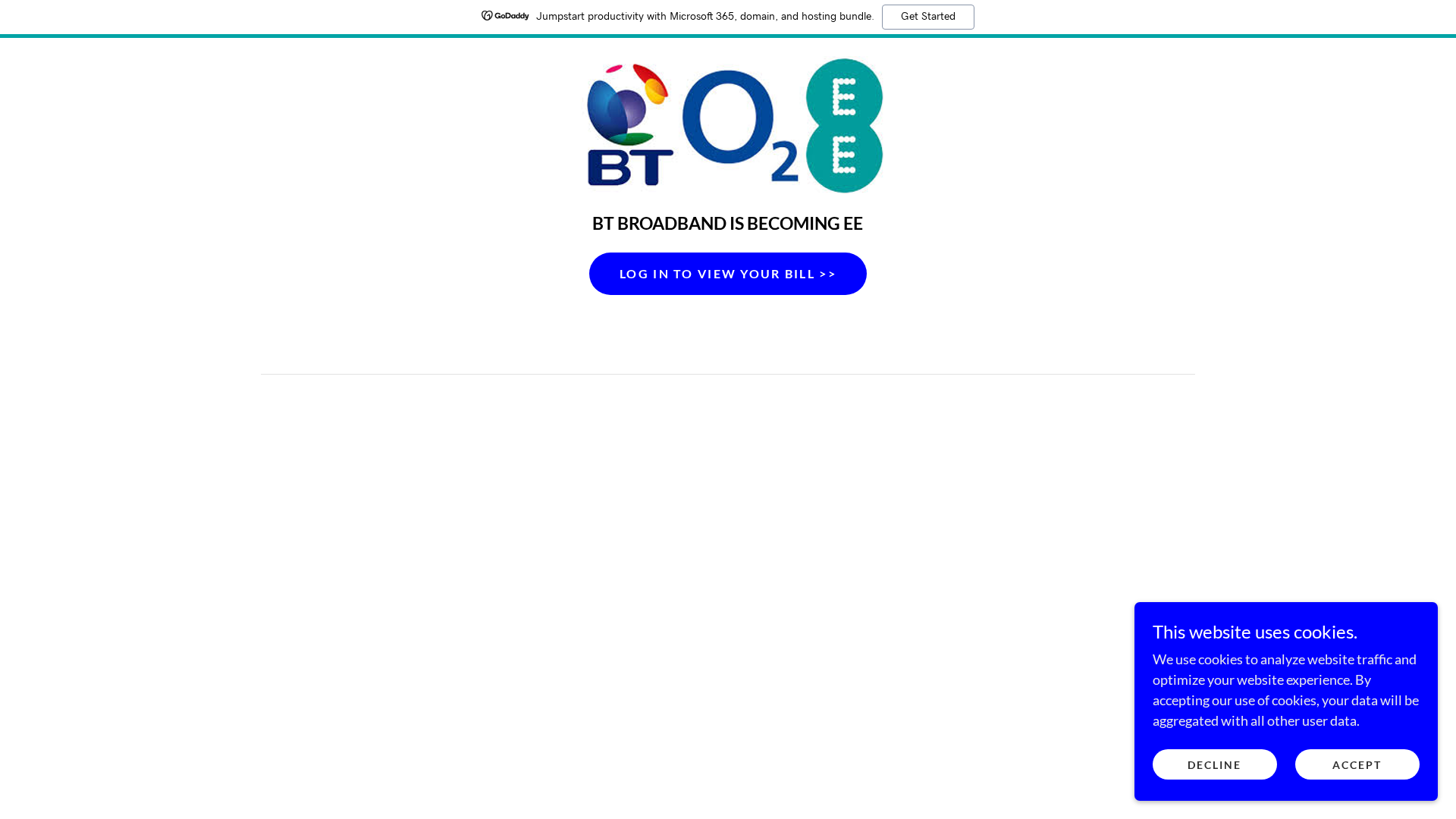
Visual Capture
Detection Info
http://site-1enk6s1fm.godaddysites.com
Detected Brand
BT/EE
Country
UK
Confidence
100%
HTTP Status
200
Report ID
9eb55ba0-15e…
Analyzed
2026-02-01 13:20
Final URL (after redirects)
https://site-1enk6s1fm.godaddysites.com/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1A852424622082966C2B3489C94506684B387DB4FC961877086BC5E7F1FD2EA2A795F3F |
|
CONTENT
ssdeep
|
192:cQO0YOryHjbI1jaFhdtPCZw7yBNQ6VyNU4JQMdBCWvoacsLjwpcBlb5h1oQ46X8D:2Oryddiy3Bg6BR+FhoQ |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
d2a5528dad52a75a |
|
VISUAL
aHash
|
e7e7e7fffffcfcfc |
|
VISUAL
dHash
|
0d4d4d0c00080808 |
|
VISUAL
wHash
|
00e7e7810f0c0c0c |
|
VISUAL
colorHash
|
07000000580 |
|
VISUAL
cropResistant
|
0d4d4d0c00080808,451144f4b4064145,c9c8b0b09088aa8e |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Phishing
• Target: BT/EE customers
• Method: Impersonation through free hosting
• Exfil: Potentially login credentials.
• Indicators: Free hosting with BT/EE logo
• Risk: High
🔒 Obfuscation Detected
- fromCharCode
- unicode_escape
🎯 Kit Endpoints
- //img1.wsimg.com/isteam/ip/7a17d71d-8d60-4865-9278-d2e9a6eb3bfb/BT%20%26%20EE%20NEW%20LOGO.jpeg/:/rs=h:182,cg:true,m/qt=q:100/ll
- //img1.wsimg.com/isteam/ip/7a17d71d-8d60-4865-9278-d2e9a6eb3bfb/BT%20%26%20EE%20NEW%20LOGO.jpeg/:/rs=w:72,h:72,m
- //img1.wsimg.com/isteam/ip/7a17d71d-8d60-4865-9278-d2e9a6eb3bfb/BT%20%26%20EE%20NEW%20LOGO.jpeg/:/rs=w:114,h:114,m
- //img1.wsimg.com/isteam/ip/7a17d71d-8d60-4865-9278-d2e9a6eb3bfb/BT%20%26%20EE%20NEW%20LOGO.jpeg/:/rs=w:57,h:57,m
- //img1.wsimg.com/isteam/ip/7a17d71d-8d60-4865-9278-d2e9a6eb3bfb/BT%20%26%20EE%20NEW%20LOGO.jpeg/:/rs=w:60,h:60,m
- //img1.wsimg.com/isteam/ip/7a17d71d-8d60-4865-9278-d2e9a6eb3bfb/BT%20%26%20EE%20NEW%20LOGO.jpeg/:/rs=w:144,h:144,m
- //img1.wsimg.com/isteam/ip/7a17d71d-8d60-4865-9278-d2e9a6eb3bfb/BT%20%26%20EE%20NEW%20LOGO.jpeg/:/rs=w:120,h:120,m
- //img1.wsimg.com/isteam/ip/7a17d71d-8d60-4865-9278-d2e9a6eb3bfb/BT%20%26%20EE%20NEW%20LOGO.jpeg/:/rs=w:152,h:152,m
- //img1.wsimg.com/isteam/ip/7a17d71d-8d60-4865-9278-d2e9a6eb3bfb/BT%20%26%20EE%20NEW%20LOGO.jpeg/:/rs=w:180,h:180,m
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Free Hosting
The domain is hosted on godaddysites.com, a free hosting platform often abused by phishers.
Brand Impersonation
The site uses the BT/EE brand logo to deceive users.
Obfuscation
JavaScript obfuscation detected via fromCharCode and unicode_escape, making analysis more difficult.
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
BT/EE users (UK)
Attack Method
Brand impersonation + obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 12 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
BT/EE
Official Website
https://www.bt.com/
Fake Service
BT/EE Bill Viewing / Login
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker likely aims to steal user credentials by mimicking the BT/EE login page. The 'Log In to View Your Bill' button will lead to a credential harvesting form.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
site-1enk6s1fm.godaddysites.com
Registered
None
Registrar
None
Status
None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for site-1enk6s1fm.godaddysites.com
Found 7 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.