
Phishing Analysis
Detailed analysis of captured phishing page
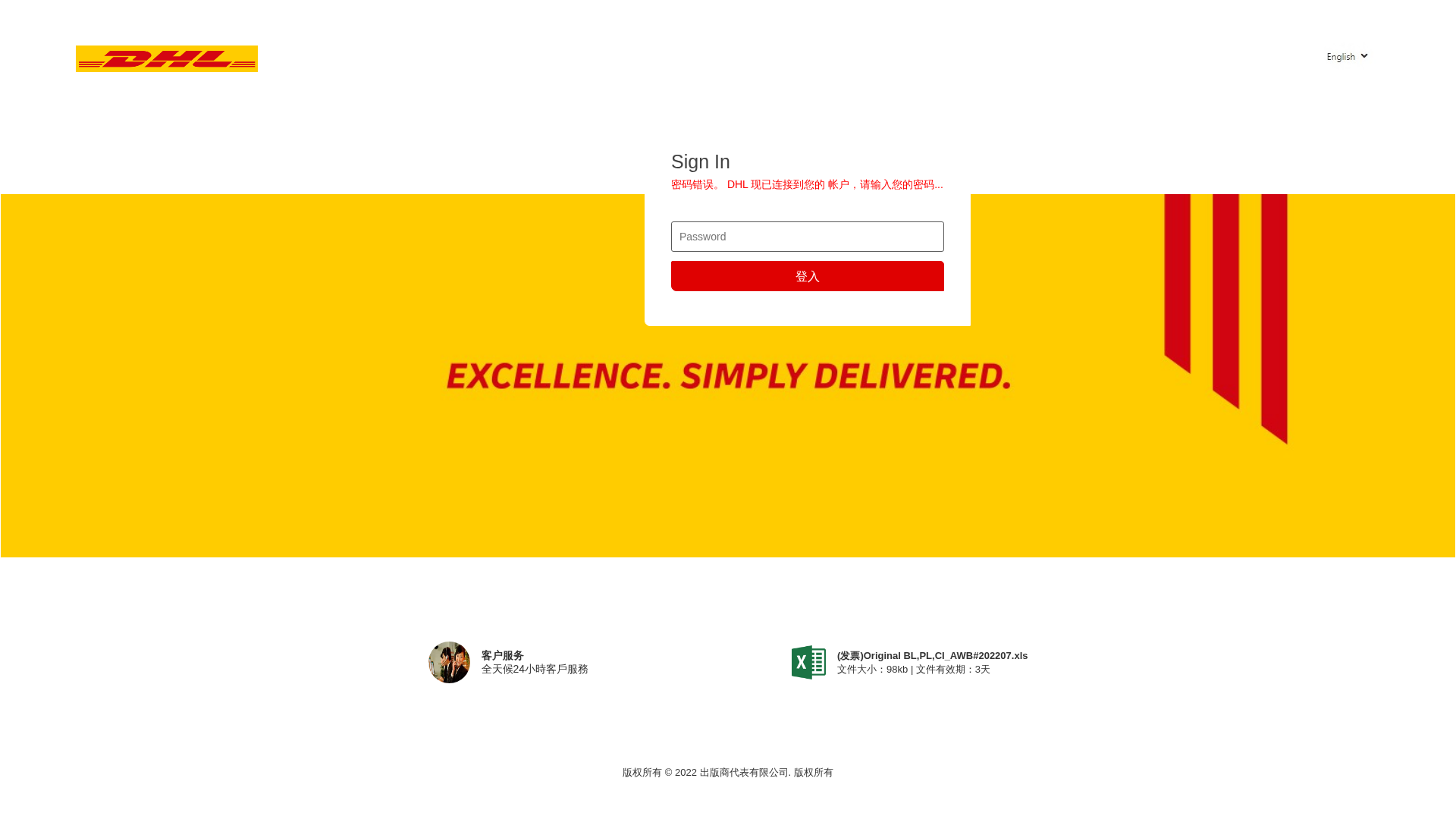
Visual Capture
Detection Info
https://www.maison-orbey.de/wp-content/plugins/xleet/b/g/index2.php
Detected Brand
DHL
Country
International
Confidence
95%
HTTP Status
N/A
Report ID
9ec8ea7f-0de…
Analyzed
2026-01-26 04:37
Code Analysis
Risk Score
80/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🔬 Threat Analysis Report
• Threat: Credential harvesting phishing kit
• Target: DHL users internationally
• Method: Fake login form stealing passwords
• Exfil: Unknown, likely sent to attacker's server
• Indicators: Unrelated domain, mimics DHL branding, login form present
• Risk: HIGH - Immediate credential theft
📊 Risk Score Breakdown
Total Risk Score
80/100
Contributing Factors
Brand Impersonation
Impersonates DHL, a global logistics brand, to deceive victims into entering credentials.
Credential Harvesting
Contains a password form field, indicating an attempt to harvest user credentials.
Compromised Domain
Uses a legitimate but compromised domain (maison-orbey.de) to host phishing content, increasing trustworthiness.
🔬 Comprehensive Threat Analysis
Threat Type
Unknown Threat
Target
DHL users (International)
Attack Method
Brand impersonation
Exfiltration Channel
Unknown
Risk Assessment
LOW - Automated credential harvesting with Unknown
🏢 Brand Impersonation Analysis
Impersonated Brand
DHL
Official Website
https://www.dhl.com
Fake Service
DHL account login portal
⚔️ Attack Methodology
Primary Method: Account Takeover
The phishing page impersonates DHL and presents a login form to harvest victim credentials. Once submitted, the credentials are likely exfiltrated to an attacker-controlled server for unauthorized access to DHL accounts.
Secondary Method: Credential Theft
The harvested credentials can be used for further attacks, such as accessing linked services, stealing personal data, or conducting fraudulent transactions.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
www.maison-orbey.de
Registered
Unknown
Registrar
Unknown
Status
Age unknown
📊 Attack Flow Diagram
┌──────────────────────────────────────────────────────────┐
│ 1. VICTIM RECEIVES PHISHING EMAIL │
│ - Email mimics DHL branding │
│ - Contains link to fake login page │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 2. FAKE LOGIN PAGE DISPLAYED │
│ - Victim enters Banking credentials │
│ - Form appears legitimate (DHL branding) │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 3. CREDENTIAL CAPTURE │
│ - Input data collected by attacker │
│ - Victim redirected to error page │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 4. DATA EXFILTRATION │
│ - Stolen credentials sent via HTTP POST │
│ - Standard form submission to attacker server │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 5. ACCOUNT TAKEOVER │
│ - Attacker uses credentials to access victim's bank │
│ - Unauthorized transactions initiated │
└──────────────────────────────────────────────────────────┘
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
┌──────────────────────────────────────────────────────────┐
│ 1. VICTIM RECEIVES PHISHING EMAIL │
│ - Email mimics DHL branding │
│ - Contains link to fake login page │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 2. FAKE LOGIN PAGE DISPLAYED │
│ - Victim enters Banking credentials │
│ - Form appears legitimate (DHL branding) │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 3. CREDENTIAL CAPTURE │
│ - Input data collected by attacker │
│ - Victim redirected to error page │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 4. DATA EXFILTRATION │
│ - Stolen credentials sent via HTTP POST │
│ - Standard form submission to attacker server │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 5. ACCOUNT TAKEOVER │
│ - Attacker uses credentials to access victim's bank │
│ - Unauthorized transactions initiated │
└──────────────────────────────────────────────────────────┘
Scan History for www.maison-orbey.de
Found 10 other scans for this domain
-
http://www.maison-orbey.de/g/o/
https://www.maison-orbey.de/wp-content/plugins/xle...
https://www.maison-orbey.de/g/o/[email protected]
https://www.maison-orbey.de/wp-content/plugins/xle...
https://www.maison-orbey.de/g/o/[email protected]
https://www.maison-orbey.de/
http://www.maison-orbey.de/wp-content/plugins/xlee...
https://www.maison-orbey.de/wp-content/plugins/xle...
https://www.maison-orbey.de/g/o/
https://www.maison-orbey.de/wp-content/plugins/xle...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.