
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
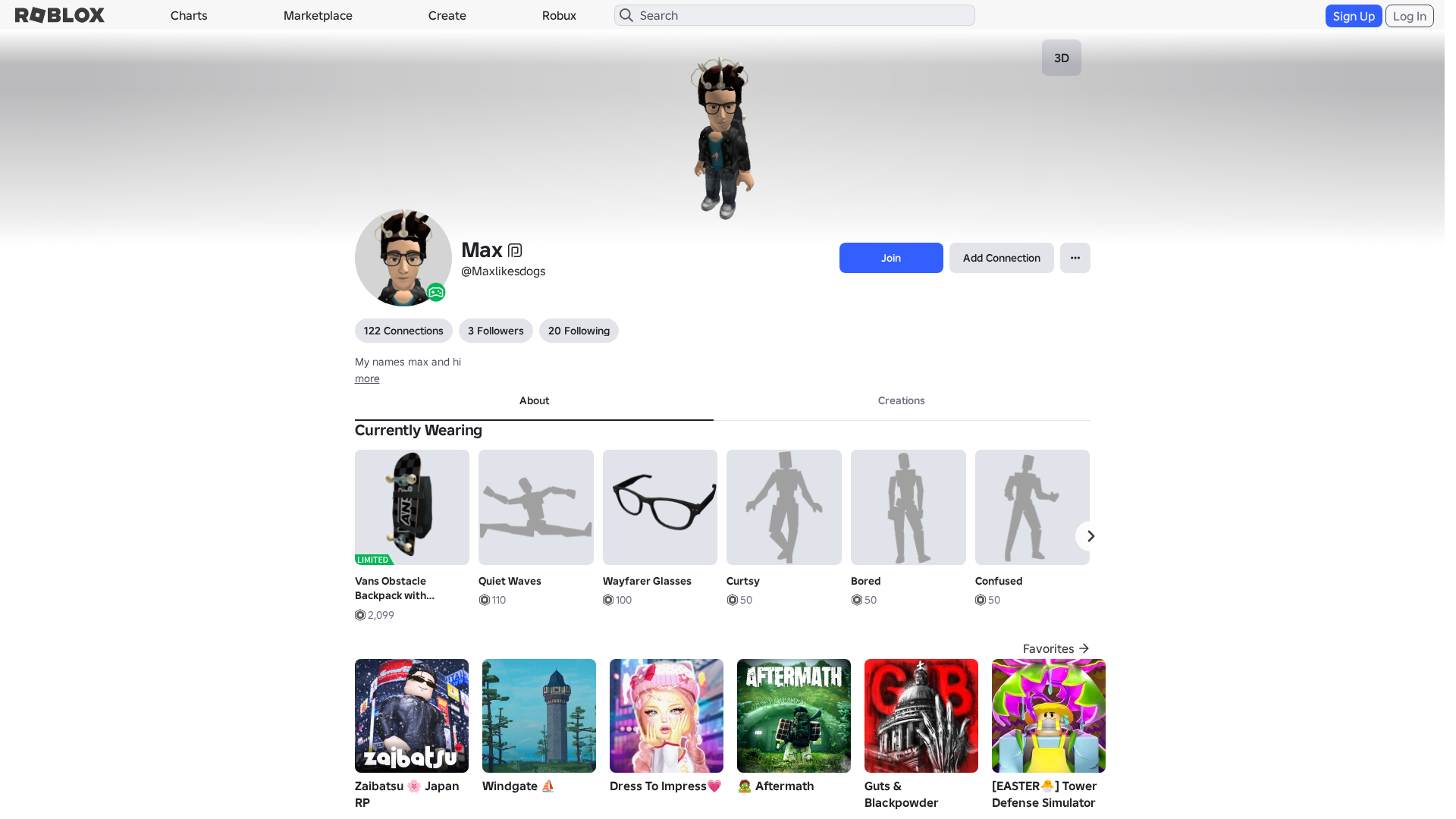
Detection Info
https://www.robiox.com.py/users/317364274826/profile
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
9ff6d41a-8ea…
Analyzed
2026-04-07 23:05
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T15873417292142837617B79DAF164672AD2D3D70FCA8346E1A2F8939A0FD6CE1EC5340D |
|
CONTENT
ssdeep
|
1536:K3XdNXWnUr/LA+aetJsgJugT1ghkgFWgSmgm+gmQgK+gxHdgmdgXDgBtgDbgmbgn:yXdNXWSLA+tTqHaO2Y1RoUU7RgdwPbyV |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
bc936553d1cc9c2c |
|
VISUAL
aHash
|
0000dfffc7dfc3c3 |
|
VISUAL
dHash
|
e8e8b630b63e3616 |
|
VISUAL
wHash
|
0000dfffc3c7c3c3 |
|
VISUAL
colorHash
|
07001000000 |
|
VISUAL
cropResistant
|
e8e8b630b63e3616,e1e9b936b29263e6,156465ccc5d8c929 |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/301823492/XBOX-F-Left-Leg
- https://api.injuries.lu/catalog/301822804/XBOX-F-Left-Arm
- /login?returnUrl=
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F317364274826%2Fprofile
- https://api.injuries.lu/catalog/3576686446/Hello
- https://api.injuries.lu/catalog/20642008/Bandit
- https://api.injuries.lu/catalog/301819845/Johns-Hair
- https://www.roblox.com/games/3540051865/Windgate
- https://api.injuries.lu/catalog/7466046574/Quiet-Waves
- https://api.injuries.lu/catalog/5030224026/Wayfarer-Glasses
- https://api.injuries.lu/catalog/301823806/XBOX-F-Right-Leg
- https://api.injuries.lu/catalog/7592037079/Vans-Obstacle-Backpack-with-Skateboard
- https://api.injuries.lu/catalog/11573370910/Anime-Mood
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/4940592718/Confused
- https://api.injuries.lu/catalog/86499666/Woman-Torso
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/12778883791/Oliver-Head
- https://api.injuries.lu/catalog/6685865126/Elevens-Headgear-Stranger-Things
- https://api.injuries.lu/catalog/3576823880/Point2
- https://api.injuries.lu/catalog/12778888565/Oliver-Brows
- https://api.injuries.lu/catalog/4646306583/Curtsy
- https://www.roblox.com/catalog
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F317364274826%2Fprofile
- https://api.injuries.lu/catalog/9801091948/jeans
- https://api.injuries.lu/catalog/3576968026/Shrug
- https://api.injuries.lu/catalog/382538295/Guitar-Tee-with-Black-Jacket
- https://api.injuries.lu/catalog/5230661597/Bored
- https://api.injuries.lu/catalog/301822975/XBOX-F-Right-Arm
- https://api.injuries.lu/catalog/4689362868/Sleep
📡 API Calls Detected
- https://ro.blox.com/Ebh5?
- GET
- https://apis.
- get
- POST
- https://help.roblox.com/hc/articles/30428367965460
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 212 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Roblox users
Attack Method
credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
HTTP POST to backend
Risk Assessment
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 212 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 212 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
www.robiox.com.py
Registered
Unknown
Registrar
None
Status
Age unknown
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for www.robiox.com.py
Found 10 other scans for this domain
-
https://www.robiox.com.py/users/262683709646/profi...
https://www.robiox.com.py/users/387072077925/profi...
https://www.robiox.com.py/users/217025834840/profi...
https://www.robiox.com.py/users/335157511751/profi...
https://www.robiox.com.py/users/239884675658/profi...
https://www.robiox.com.py/users/377777277866/profi...
https://www.robiox.com.py/users/255445160301/profi...
https://www.robiox.com.py/users/378472335145/profi...
https://www.robiox.com.py/users/411240076850/profi...
https://www.robiox.com.py/games/90118298734859/EMO...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.