
Phishing Analysis
Detailed analysis of captured phishing page
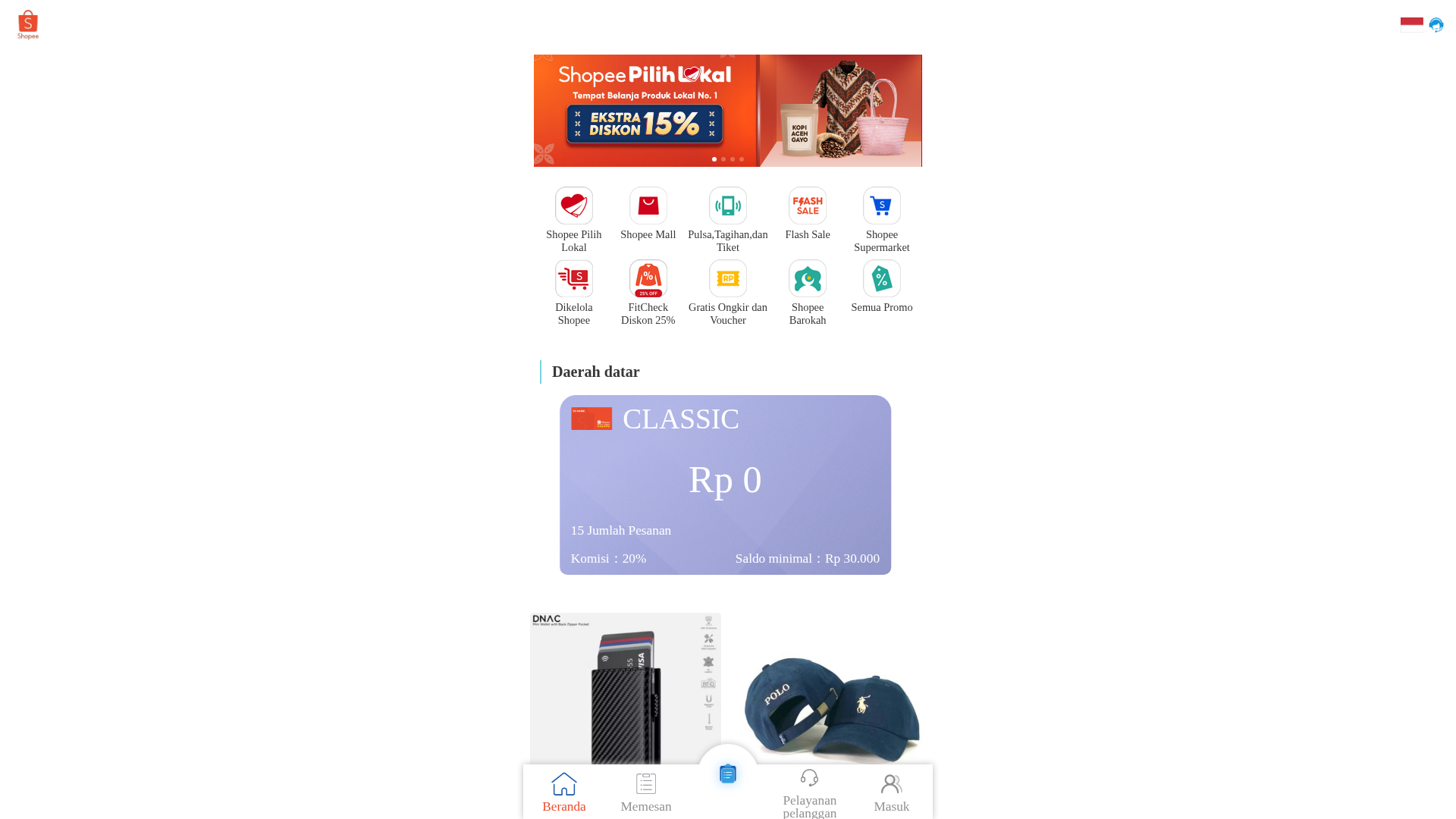
Visual Capture
Detection Info
http://mayonetteofficialjob.com/
Detected Brand
Shopee
Country
International
Confidence
100%
HTTP Status
200
Report ID
a72759a2-042…
Analyzed
2026-01-01 01:01
Final URL (after redirects)
http://mayonetteofficialjob.com/m/index
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T161A2BD72C04120AF1936EC93FB35BB5AD1C3E32EC931D41096648F5EAED6EE0536649B |
|
CONTENT
ssdeep
|
192:IfUut0MRJ4jSL7chyte4JirHTVOMwYdUKmmMJh7tb2ZStIvqKxf+LVdCrGRVt2z0:QkKfVu+qNGlK5ArQCOz7LD91k |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b3333166cc99cccc |
|
VISUAL
aHash
|
e7c3ffe7e7e7e7e7 |
|
VISUAL
dHash
|
cc4d100c4d4d4d0c |
|
VISUAL
wHash
|
42c3c3c3e7c3c3c3 |
|
VISUAL
colorHash
|
07000000006 |
|
VISUAL
cropResistant
|
cc4d100c4d4d4d0c,9d6dc98c8ada58e3 |
Code Analysis
Risk Score
95/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Brand impersonation phishing
• Target: Shopee users
• Method: Using a fake domain to impersonate Shopee
• Exfil: Unknown - data exfiltration target could not be confirmed from the screenshot
• Indicators: Domain mismatch, recent domain registration, JavaScript obfuscation, JavaScript form submission
• Risk: HIGH - Brand impersonation aimed at data theft or fraud.
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- document.write
- unicode_escape
- base64_strings
📡 API Calls Detected
- GET
- POST
- left
- right
- post
Scan History for mayonetteofficialjob.com
Found 4 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.