
Phishing Analysis
Detailed analysis of captured phishing page
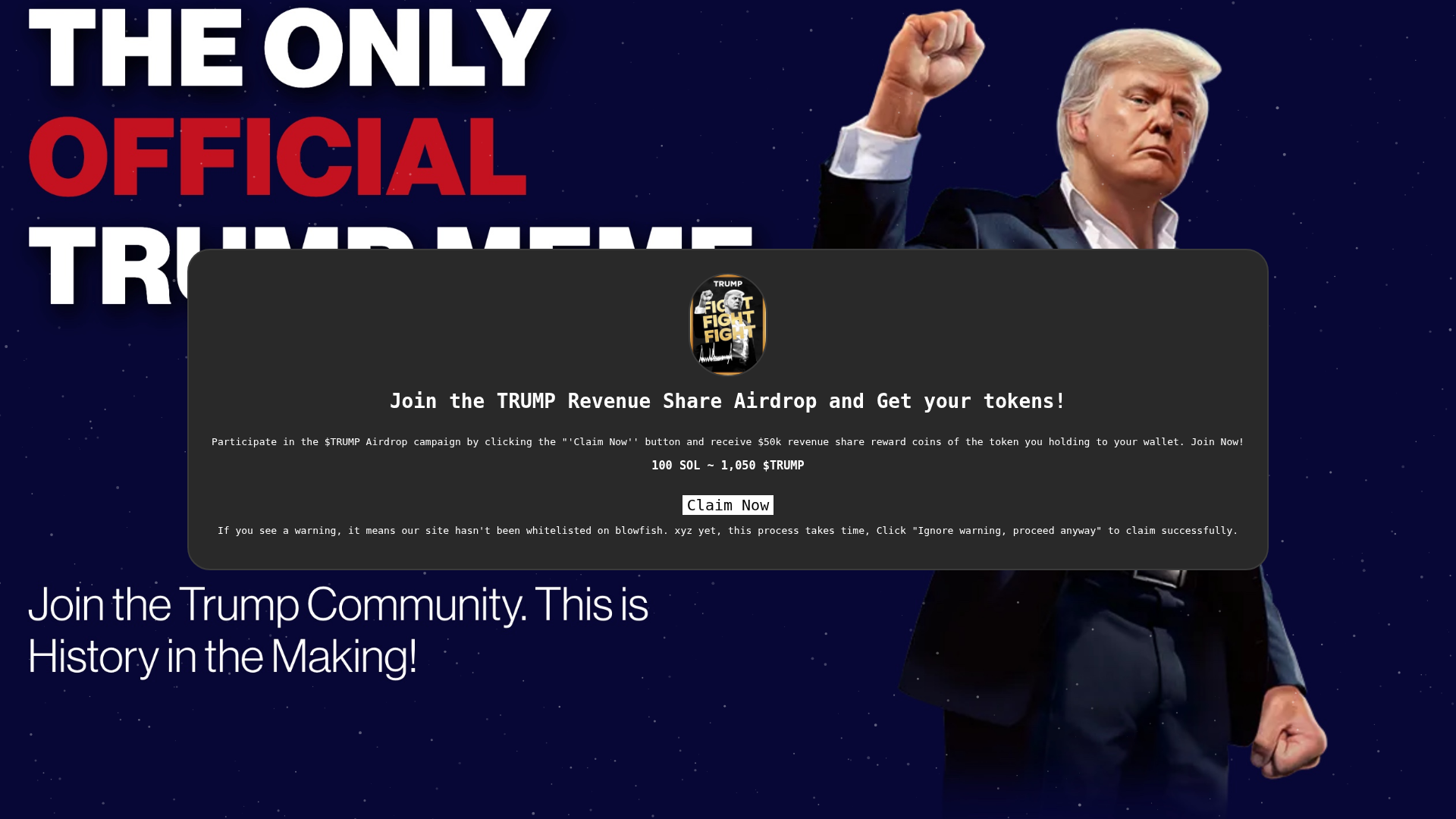
Visual Capture
Detection Info
https://gettrumpmemeairdrop.pages.dev/
Detected Brand
Donald Trump (Trump Meme Coin)
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
a9e7cf24-a93…
Analyzed
2026-04-08 12:34
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1C7311036C9C0053F93E2C36C9F52A3642B46C94DC3996D4849F4A6DC8BD8E118DE61EA |
|
CONTENT
ssdeep
|
24:n9CECOTgtntvHg5mcIoAy4bo+TgEupeIyhmUjpOSBJEYUb0F9:n0tnNHg5m8tDryhjn8YM8 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
d5f273c381e0e8e8 |
|
VISUAL
aHash
|
e66ef67c7e700000 |
|
VISUAL
dHash
|
cccc24f0f0d48672 |
|
VISUAL
wHash
|
e66efe7e7e700000 |
|
VISUAL
colorHash
|
32601000002 |
|
VISUAL
cropResistant
|
8a8aa8b2b2acaaaa,ac945470784a8aaa,e0b673c6a9f2c230,591d959599949494,cccc24f0f0d48672 |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔒 Obfuscation Detected
- fromCharCode
- unescape
- hex_escape
- js_packer
- base64_strings
🎯 Kit Endpoints
- data:image/jpeg;base64,/9j/4AAQSkZJRgABAQAASABIAAD/4QBARXhpZgAATU0AKgAAAAgAAYdpAAQAAAABAAAAGgAAAAAAAqACAAQAAAABAAADmqADAAQAAAABAAAEyAAAAAD/7QA4UGhvdG9zaG9wIDMuMAA4QklNBAQAAAAAAAA4QklNBCUAAAAAABDUHYzZjwCyBOmACZjs+EJ+/+INLElDQ19QUk9GSUxFAAEBAAANHGFwcGwCEAAAbW50clJHQiBYWVogB+kAAQANAAMAAAASYWNzcEFQUEwAAAAAQVBQTAAAAAAAAAAAAAAAAAAAAAAAAPbWAAEAAAAA0y1hcHBsAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAARZGVzYwAAAVAAAABiZHNjbQAAAbQAAAH2Y3BydAAAA6wAAAAjd3RwdAAAA9AAAAAUclhZWgAAA+QAAAAUZ1hZWgAAA/gAAAAUYlhZWgAABAwAAAAUclRSQwAABCAAAAgMYWFyZwAADCwAAAAgdmNndAAADEwAAAAwbmRpbgAADHwAAAA+bW1vZAAADLwAAAAodmNncAAADOQAAAA4YlRSQwAABCAAAAgMZ1RSQwAABCAAAAgMYWFiZwAADCwAAAAgYWFnZwAADCwAAAAgZGVzYwAAAAAAAAAIRGlzcGxheQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAG1sdWMAAAAAAAAAJwAAAAxockhSAAAAEgAAAeRrb0tSAAAAEgAAAeRuYk5PAAAAEgAAAeRpZAAAAAAAEgAAAeRodUhVAAAAEgAAAeRjc0NaAAAAEgAAAeRzbFNJAAAAEgAAAeRkYURLAAAAEgAAAeRubE5MAAAAEgAAAeRmaUZJAAAAEgAAAeRpdElUAAAAEgAAAeRlc0VTAAAAEgAAAeRyb1JPAAAAEgAAAeRmckNBAAAAEgAAAeRhcgAAAAAAEgAAAeR1a1VBAAAAEgAAAeRoZUlMAAAAEgAAAeR6aFRXAAAAEgAAAeR2aVZOAAAAEgAAAeRza1NLAAAAEgAAAeR6aENOAAAAEgAAAeRydVJVAAAAEgAAAeRlbkdCAAAAEgAAAeRmckZSAAAAEgAAAeRtcwAAAAAAEgAAAeRoaUlOAAAAEgAAAeR0aFRIAAAAEgAAAeRjYUVTAAAAEgAAAeRlbkFVAAAAEgAAAeRlc1hMAAAAEgAAAeRkZURFAAAAEgAAAeRlblVTAAAAEgAAAeRwdEJSAAAAEgAAAeRwbFBMAAAAEgAAAeRlbEdSAAAAEgAAAeRzdlNFAAAAEgAAAeR0clRSAAAAEgAAAeRwdFBUAAAAEgAAAeRqYUpQAAAAEgAAAeQAQwBvAGwAbwByACAATABDAEQAAHRleHQAAAAAQ29weXJpZ2h0IEFwcGxlIEluYy4sIDIwMjUAAFhZWiAAAAAAAADzFgABAAAAARbKWFlaIAAAAAAAAG8KAAA4sAAAA5RYWVogAAAAAAAAY9gAALmXAAAZR1hZWiAAAAAAAAAj9QAADboAALZSY3VydgAAAAAAAAQAAAAABQAKAA8AFAAZAB4AIwAoAC0AMgA2ADsAQABFAEoATwBUAFkAXgBjAGgAbQByAHcAfACBAIYAiwCQAJUAmgCfAKMAqACtALIAtwC8AMEAxgDLANAA1QDbAOAA5QDrAPAA9gD7AQEBBwENARMBGQEfASUBKwEyATgBPgFFAUwBUgFZAWABZwFuAXUBfAGDAYsBkgGaAaEBqQGxAbkBwQHJAdEB2QHhAekB8gH6AgMCDAIUAh0CJgIvAjgCQQJLAlQCXQJnAnECegKEAo4CmAKiAqwCtgLBAssC1QLgAusC9QMAAwsDFgMhAy0DOANDA08DWgNmA3IDfgOKA5YDogOuA7oDxwPTA+AD7AP5BAYEEwQgBC0EOwRIBFUEYwRxBH4EjASaBKgEtgTEBNME4QTwBP4FDQUcBSsFOgVJBVgFZwV3BYYFlgWmBbUFxQXVBeUF9gYGBhYGJwY3BkgGWQZqBnsGjAadBq8GwAbRBuMG9QcHBxkHKwc9B08HYQd0B4YHmQesB78H0gflB/gICwgfCDIIRghaCG4IggiWCKoIvgjSCOcI+wkQCSUJOglPCWQJeQmPCaQJugnPCeUJ+woRCicKPQpUCmoKgQqYCq4KxQrcCvMLCwsiCzkLUQtpC4ALmAuwC8gL4Qv5DBIMKgxDDFwMdQyODKcMwAzZDPMNDQ0mDUANWg10DY4NqQ3DDd4N+A4TDi4OSQ5kDn8Omw62DtIO7g8JDyUPQQ9eD3oPlg+zD88P7BAJECYQQxBhEH4QmxC5ENcQ9RETETERTxFtEYwRqhHJEegSBxImEkUSZBKEEqMSwxLjEwMTIxNDE2MTgxOkE8UT5RQGFCcUSRRqFIsUrRTOFPAVEhU0FVYVeBWbFb0V4BYDFiYWSRZsFo8WshbWFvoXHRdBF2UXiReuF9IX9xgbGEAYZRiKGK8Y1Rj6GSAZRRlrGZEZtxndGgQaKhpRGncanhrFGuwbFBs7G2MbihuyG9ocAhwqHFIcexyjHMwc9R0eHUcdcB2ZHcMd7B4WHkAeah6UHr4e6R8THz4faR+UH78f6iAVIEEgbCCYIMQg8CEcIUghdSGhIc4h+yInIlUigiKvIt0jCiM4I2YjlCPCI/AkHyRNJHwkqyTaJQklOCVoJZclxyX3JicmVyaHJrcm6CcYJ0kneierJ9woDSg/KHEooijUKQYpOClrKZ0p0CoCKjUqaCqbKs8rAis2K2krnSvRLAUsOSxuLKIs1y0MLUEtdi2rLeEuFi5MLoIuty7uLyQvWi+RL8cv/jA1MGwwpDDbMRIxSjGCMbox8jIqMmMymzLUMw0zRjN/M7gz8TQrNGU0njTYNRM1TTWHNcI1/TY3NnI2rjbpNyQ3YDecN9c4FDhQOIw4yDkFOUI5fzm8Ofk6Njp0OrI67zstO2s7qjvoPCc8ZTykPOM9Ij1hPaE94D4gPmA+oD7gPyE/YT+iP+JAI0BkQKZA50EpQWpBrEHuQjBCckK1QvdDOkN9Q8BEA0RHRIpEzkUSRVVFmkXeRiJGZ0arRvBHNUd7R8BIBUhLSJFI10kdSWNJqUnwSjdKfUrESwxLU0uaS+JMKkxyTLpNAk1KTZNN3E4lTm5Ot08AT0lPk0/dUCdQcVC7UQZRUFGbUeZSMVJ8UsdTE1NfU6pT9lRCVI9U21UoVXVVwlYPVlxWqVb3V0RXklfgWC9YfVjLWRpZaVm4WgdaVlqmWvVbRVuVW+VcNVyGXNZdJ114XcleGl5sXr1fD19hX7NgBWBXYKpg/GFPYaJh9WJJYpxi8GNDY5dj62RAZJRk6WU9ZZJl52Y9ZpJm6Gc9Z5Nn6Wg/aJZo7GlDaZpp8WpIap9q92tPa6dr/2xXbK9tCG1gbbluEm5rbsRvHm94b9FwK3CGcOBxOnGVcfByS3KmcwFzXXO4dBR0cHTMdSh1hXXhdj52m3b4d1Z3s3gReG54zHkqeYl553pGeqV7BHtje8J8IXyBfOF9QX2hfgF+Yn7CfyN/hH/lgEeAqIEKgWuBzYIwgpKC9INXg7qEHYSAhOOFR4Wrhg6GcobXhzuHn4gEiGmIzokziZmJ/opkisqLMIuWi/yMY4zKjTGNmI3/jmaOzo82j56QBpBukNaRP5GokhGSepLjk02TtpQglIqU9JVflcmWNJaflwqXdZfgmEyYuJkkmZCZ/JpomtWbQpuvnByciZz3nWSd0p5Anq6fHZ+Ln/qgaaDYoUehtqImopajBqN2o+akVqTHpTilqaYapoum/adup+CoUqjEqTepqaocqo+rAqt1q+msXKzQrUStuK4trqGvFq+LsACwdbDqsWCx1rJLssKzOLOutCW0nLUTtYq2AbZ5tvC3aLfguFm40blKucK6O7q1uy67p7whvJu9Fb2Pvgq+hL7/v3q/9cBwwOzBZ8Hjwl/C28NYw9TEUcTOxUvFyMZGxsPHQce/yD3IvMk6ybnKOMq3yzbLtsw1zLXNNc21zjbOts83z7jQOdC60TzRvtI/0sHTRNPG1EnUy9VO1dHWVdbY11zX4Nhk2OjZbNnx2nba+9uA3AXcit0Q3ZbeHN6i3ynfr+A24L3hROHM4lPi2+Nj4+vkc+T85YTmDeaW5x/nqegy6LzpRunQ6lvq5etw6/vshu0R7ZzuKO6070DvzPBY8OXxcvH/8ozzGfOn9DT0wvVQ9d72bfb794r4Gfio+Tj5x/pX+uf7d/wH/Jj9Kf26/kv+3P9t//9wYXJhAAAAAAADAAAAAmZmAADypwAADVkAABPQAAAKW3ZjZ3QAAAAAAAAAAQABAAAAAAAAAAEAAAABAAAAAAAAAAEAAAABAAAAAAAAAAEAAG5kaW4AAAAAAAAANgAAo8AAAFSAAABMwAAAmYAAACZAAAAOAAAAUAAAAFRAAAIzMwACMzMAAjMzAAAAAAAAAABtbW9kAAAAAAAABhAAAKA5AAAAANU0CR8AAAAAAAAAAAAAAAAAAAAAdmNncAAAAAAAAwAAAAJmZgADAAAAAmZmAAMAAAACZmYAAAACMzM0AAAAAAIzMzQAAAAAAjMzNAD/wAARCATIA5oDASIAAhEBAxEB/8QAHwAAAQUBAQEBAQEAAAAAAAAAAAECAwQFBgcICQoL/8QAtRAAAgEDAwIEAwUFBAQAAAF9AQIDAAQRBRIhMUEGE1FhByJxFDKBkaEII0KxwRVS0fAkM2JyggkKFhcYGRolJicoKSo0NTY3ODk6Q0RFRkdISUpTVFVWV1hZWmNkZWZnaGlqc3R1dnd4eXqDhIWGh4iJipKTlJWWl5iZmqKjpKWmp6ipqrKztLW2t7i5usLDxMXGx8jJytLT1NXW19jZ2uHi4+Tl5ufo6erx8vP09fb3+Pn6/8QAHwEAAwEBAQEBAQEBAQAAAAAAAAECAwQFBgcICQoL/8QAtREAAgECBAQDBAcFBAQAAQJ3AAECAxEEBSExBhJBUQdhcRMiMoEIFEKRobHBCSMzUvAVYnLRChYkNOEl8RcYGRomJygpKjU2Nzg5OkNERUZHSElKU1RVVldYWVpjZGVmZ2hpanN0dXZ3eHl6goOEhYaHiImKkpOUlZaXmJmaoqOkpaanqKmqsrO0tba3uLm6wsPExcbHyMnK0tPU1dbX2Nna4uPk5ebn6Onq8vP09fb3+Pn6/9sAQwABAQEBAQECAQECAwICAgMEAwMDAwQFBAQEBAQFBgUFBQUFBQYGBgYGBgYGBwcHBwcHCAgICAgJCQkJCQkJCQkJ/9sAQwEBAQECAgIEAgIECQYFBgkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJCQkJ/90ABAA6/9oADAMBAAIRAxEAPwD8yodNaP5NvI4retNPugeEzmv0D/Zb/YK8IftSeFbzxJrnj+z8K3VpLt+zXLKC6/3huZeK+rLb/gkH8MLPDN8ZdKJH/TVP/jlf5T8UV1Kq489j/STLs6wdFuFW7fo3+R+O1ro95KMmI5+ldPZaLdlgvksD9K/X+D/glb8MLb/msel8f9NU/wDjlX7b/gl18OfMHlfGHSTz3lUf+z1+aYlVG2lP8T6OnxVgIrZ/+As/KS00Gc4+U8V1Nl4d8Dx6XqeofE7WZ9As7aAPYTw9ZbznZE2M4U9TX6y2/wDwTC+GoXd/wtXS37cTL/8AF1fu/wDgl/8ACXWNLk0bW/iPo97aS8vFLKpXdjAbh8gjtXNlqqxxKVWenXVf5kVuL8Dytxbv/hZ85/s9ftzfsfXPwl06z+N2uW9p4j00/Y5QqMwlWMhY5MqMfMuCa9oP7bv/AATnQbh4kRsf9M2x+eK8kv8A/ghf+yZqM813J4801QoeaTy7oZCLy5xv6DB+lfBEH7B37HHizVb7/hTWqnxFollP9nF9vcI8qjLhCfvAevQ1+hYrKcpVF1vaTst2kmvzPDy/PZYuq6dFv56H6qH9uX/gnamAniKLn/pm3+FMb9uf/gnsGwPEUXH+ww/pX5nw/wDBNr4FSEGaA7f+ujD9a1IP+CaX7PRO5o2H/bUmvnFSyJ6KrU+6P+Z7apYrvH5H6Rj9uv8A4J8IP+Rii/75P+FOP7ev/BPwHC+II8f7pr87of8Agmj+z2f4GP8A21aro/4Jo/s8Y/1Tf9/GrGWHya/8Sr/5Kaexxnc/Qkft6fsAMMJ4jiH1Q/4Uh/b2/YMQ8eIos+yH/Cvz/T/gml+zqvWJ/wDv4akH/BNP9nNj/qWH/bU1z1aWTRdnOr90Q9livtH39/w39+wYo58RR/in/wBarUf/AAUA/YOHTxFEM/7B/wAK/Pn/AIdm/s5nhom/7+tUy/8ABND9m1f+WTf9/WrLlyX+er90SXTxKe8fmfoA/wDwUE/YKQ4k8RxZ/wBz/wCtUJ/4KDfsD5/5GSL/AL5P+FfBB/4Jpfs3HpAT/wBtGNPH/BND9mvHNuf++2raMsmt8VX7olrD1mviiffKf8FBP2CAcf8ACSRf98n/AAqT/h4R+wajceJIx77D/hXwIf8Agmh+zXj/AFJ/77akX/gmj+zWvAt+v/TRhVc+Td6v3R/zD6tW/niffjf8FDP2DV6+Joz/AMAP+FIP+CiH7Bg/5mdB/wAAb/Cvgc/8E0v2bv4YD/38NPT/AIJo/s24+aA/9/DT58m71f8AyX/Mr6pW/nife3/DxD9gvv4mQ/8AAG/wqdf+Civ7B20f8VOv/fB/wr4GH/BND9mzH+oP/fw/4VIP+Ca37NuMeT/5ENZVXk8tnV/8l/zJlhKvWSfofe3/AA8W/YNPH/CTp/37/wDrUD/gop+wbn/kZ0P0Q/4V8HD/AIJofs0MceR/5ENSp/wTN/Znz/x75+shrPkyj+at/wCS/wCYfVp9/wAv8j7tP/BRT9g8dPEyf98N/hSH/go1+wgnB8TIP+AN/hXw0v8AwTN/ZlB+a2B/7aN/iKm/4dk/sxN/y6j/AL+v/jScco/mq/8Akv8AmS8PPufbh/4KN/sJE8eKE/79t/hSH/go3+wdgj/hJ0/79t/hXxUv/BMP9mI8Gz/8iN/jT/8Ah2F+zITj7L/4+1H/AAjfzVf/ACX/ADF9Xn3Ps1P+Cjn7CKn/AJGlB/wFv8KnH/BR/wDYSP8AzNaf98N/hXxzD/wS5/ZhLgm3/wDIr/41qxf8EsP2YH/5YAD/AK6tWPNknSVb7okfUZn1qv8AwUd/YQPXxWn/AHw3+FP/AOHkn7CEZx/wlS/9+3P9K+U0/wCCU/7MLcLEP+/xqVf+CUf7LxPzQkn2mahSyb+ar/5KJ4Scdbn1Q3/BSn9hMLx4rX/v0/8AhUY/4KV/sKDn/hKl/wC/bf4V80w/8Enf2XD96E/9/mrQT/gk5+ys4+aD/wAimnz5P3q/+SiVCT6n0dH/AMFMP2E1OG8UIf8Atm3+FS/8PM/2ElOR4mT/AL9v/hXzqn/BJH9lRulsfwnNSD/gkd+yoD81s3/f/wD+vR/wjv7VX/yUiVCa2kfRv/DzX9hb+HxQo/7Zv/hSj/gpx+w0BgeKV/79v/hXz4n/AASQ/ZSGB9lb/v8An/Gra/8ABI/9k4LzbN/3/P8AjUtZP/NV+6IKlV/mPcj/AMFOP2Gc/wDI0j/v23+FSD/gp1+w1kY8VD/v23+FeCn/AIJG/spE5Fq3/f8AP+NOH/BI39lDPFm3/f8AP/xVTfJv5qv/AJKZewrdz30f8FOv2HM8+Kh/37b/AApH/wCCnn7DY6eKFP1jb/CvB/8Ah0b+yiPvWhH1nP8AQ1JH/wAEjv2UOcWp/Cd/8aL5P/NV/wDJSnhqj05j3Vf+Cn37DeOfFC/9+3/wp3/Dz/8AYa/6Ghf+/b/4V4S3/BIz9lFjn7K3/f8Af/Gk/wCHRX7KP/Pq3/f9/wDGr58m71f/ACUX1Kp3R7j/AMPPf2HT/wAzOv8A37f/AApjf8FPP2G+n/CUj/v03+FeJf8ADor9lHtat/3/AH/xqvJ/wSL/AGVRn/RWH/bw1LnybvV/8lBYKp5M9z/4ed/sN9/FCn/tm3+FIf8Agp3+w5/D4oUf9s3/AMK8JH/BIv8AZUPW2b/v+3/1qd/w6L/ZU/59m/7/ALU1PJe9X/yUf1Kp2R7uv/BTz9h/HHilf+/bf4VL/wAPOv2Isf8AI1D/AL9t/hXz+3/BJD9lVDgWrf8Af5zR/wAOk/2Ven2Vv+/z1PtMj/mqf+SmLozTteP9fI99b/gpx+w83XxSv/ftv8Kgb/gpn+w+Tx4oX8Y2/wAK8J/4dJ/spnj7Kf8Av+/+NOH/AASM/ZSI3C0c/wDbd/8AGhzyL+ep/wCSiVKfSUf6+R7kP+CmX7D38fidD9I2/wAKlH/BTL9hbv4nUf8AbJv8K8JH/BIr9lU9LST/AMCH/wAaY/8AwSL/AGWFOBaSf9/3pc+Rfz1P/JSlh63WR72P+Cmf7Cn/AEM6/wDftv8A4mj/AIebfsJ9P+EoT/v23+FeBf8ADpL9lVeGtJM/9dmqL/h0j+yluyLN/wDv8/8AjQ/7Ee06vy5QlRrLqfQZ/wCCmX7CZGP+EoX/AL9P/hSD/gpj+wh28Tp/37b/AAr58P8AwSQ/ZWx8to+f+u7/AONIf+CR/wCyvj5rVvxnY/zpcmTfzVfuiXSw9eXVH0Kf+CmX7CeOPFCj/tm3+FV3/wCCmf7Ch4/4Shfxjb/CvAf+HSP7KoHy2bHP/TZv8RUbf8Ej/wBlfGfsj/8Af5v8au2TbXq/dA3eDl9qR79/w8w/YU/6GdP+/TVIf+CmX7CJ+X/hJ1/79n/Cvnc/8Ek/2VwcfZH/AO/zf41IP+CSn7LGRmzb/v8AN/jRbJl1q/dAHg/7x9B/8PLP2EycDxOuf9xv/iaD/wAFK/2FRyfE6/8AfDf/ABNeBL/wSR/ZZB4tDn/rsf8AGkb/AIJJfst97Nv+/wB/9ei+T/zVfuiT/Z8v5vwZ78P+ClX7Cjc/8JMv/fDf4Un/AA8v/YSU7W8Trx/sN/hXga/8Ekv2W+1m3/f7/wCvTG/4JJfsqlvntDn/AK7GnGWTdXV/8lKjgpL7X4P9T6A/4eY/sJ/9DOP++G/wqUf8FM/2Ej/zMw/74b/Cvnr/AIdK/spf8+h/7/t/jTf+HTP7KvX7Gf8Av+3+NU55L0dX/wAlB4WXSZ9E/wDDzH9hT+HxMv4xn/CkP/BTD9hg/wDMzxj/ALZkf0r51b/gk1+yxji1Yf8AbZj/AFpn/Dpj9lk9bVj9ZGqHVyVP4qv/AJKT9XqLqmfRDf8ABS79hgn/AJGhfwU/4VEf+Cln7DH/AENCfih/wr56P/BJj9lkdLX85WFMP/BJj9ln/n0H/f5v8aFLJX9qr/5KHsKnZfefQf8Aw8m/YZPP/CUL/wB+2/wo/wCHk37DP/Q0L/37b/Cvnv8A4dOfss/8+x/7/PS/8OnP2WT/AMux/wC/z0/aZL3q/dEX1efZH0Kv/BSX9hnP/I0L/wB+2/wqZf8AgpF+wwfveKE/74P+FfOn/Dpr9lvtbEf9tno/4dLfssvy1ueP+mzU1LJnpzVf/JQeGq9kfRv/AA8h/YW/6Ghf++D/AIUv/DyD9hb/AKGlP++D/hXzh/w6T/ZX/wCfc/8Af5qP+HSf7K+f+Pc/9/molHJuk6v/AJIT9Wr9kfRz/wDBSH9hdULf8JQv/fB/wqr/AMPKP2Fev/CUL/3w3+FfPTf8ElP2WFBb7OeP+mzVB/w6a/ZY/wCfc/8Af5qE8nWnNV+6BrDCz+00j6MP/BSf9hUj/kaB/wB8NQv/AAUm/YU6/wDCUL/37b/CvnL/AIdNfss9fs5/7+saYf8Agk3+y0Dxbn/v61NVMn71fugWsPJaKR9Kp/wUo/YRC4PimP8AGNv8KnH/AAUn/YO7+KI/++H/AMK+YD/wSd/ZaHBhI/7atTf+HT/7K3TyD/3+P+NZt5G+tX7okOhLufTj/wDBST9g8jnxSv8A37b/AAqE/wDBSP8AYL7+KVP1R/8A4mvmr/h05+ywOfJb/v8AH/GlH/BJ79ln/niT/wBtm/xFVz5GtnV+6Iewl3PpQf8ABST9gsnC+KFH/AH/AMKVv+CkH7B54/4SlMf7jf4V80t/wSd/ZXJGYD/3+b/E1J/w6e/ZUH/Lvn/ts/8AjTdfJOsqv3REsNLufSB/4KRfsGoB/wAVWg/4A3+FRN/wUf8A2DzyPFSf98N/hXzfJ/wSe/ZYxxB/5GakX/gk/wDsu7h+4/8AIzf40vbZI9nVfyiUqMo7M+kj/wAFHv2CwuW8ULn/AHG/wqM/8FHv2CiOfFC/98N/hXzpL/wSg/Zg24S2z9Jm/wAaqn/gk7+zI3/LoR/22P8AjT58l/6e/wDko37T+Y+lP+Hjn7BLf8zOp/4A3+FO/wCHjn7BQ4/4SZf++G/wr5jb/gk9+y//AM+zf9/W/wATUTf8En/2ZAcLavj/AK6H/GqWJyZaJ1f/ACX/ADI+r1Ja8yPps/8ABRv9grJ/4qhf++D/AIUjf8FGf2CmUqPFKDP+wf8ACvmM/wDBKL9mT/n0P/fw/wCNRf8ADp/9mbORakfWT/69V9byS29X/wAl/wAwWHqfzI+mv+HiX7Bw6+KUP/bM/wCFL/w8S/YJ/i8UR/8Afs/4V8wS/wDBKT9mlBxbj8ZDWbJ/wSt/Zrj6wLz/ANNTUqtkfer/AOSmjoT7o+sB/wAFDP2BCefFEf8A37P+FSL/AMFCP2Bd2R4mQ/8AbM4/lXx3L/wS0/ZpH/LFQf8Arq1Z03/BLX9nIfMsKY/66tV+0yR/aq/+S/5kewq/ZkvmfaUv/BQP9gZh8viVP++G/wAKpf8ADfH7Bjt83iePH/XM/wCFfE3/AA67/Z03fdT/AL+NTZv+CYn7OcQyoXPtK1P2mRrepUXry/5mlOjXX8vyPt0/t2/sAMNz+Joz9EP+FQv+3V/wT3PXxLGf+2bf/E18E3f/AATQ/Z7GV2Ngf3ZWFcxc/wDBNb9nhW+SOUn/AK7tW9N5A1d1qn/kpo6OJekbH6Lj9t//AIJ6P+8fxKg9hGf/AImj/ht//gnVn5vEsY/7Zt/8TX5q3H/BN/4AwqXcSKP+u7UeGP8AgmZ8BPGniux8KW9wtot5IUe6uLkxQxADOWZsA5PAAOc124WlkVSSjGtU/wDJf8zml7eCcqk46ep+j9x+2p/wTpk/1nidAO/7tz/Ja+Iv2q/2oP2YPjJ438M/DT4ZeLE0fwbGTLq2oxRv5rykj5f73AHGOOa9x/4h/fgcYCR450eMMMg/bgAAenO7+VWfD3/BC34Q+DtRTUtP8f6HJJGeA94sgH4FhX0dLKspoLmhVk30T5f82eHHiuh7VJ1br0l/kfntrmiMl/Mmk+ZNYhj9kmYHMkGf3bkHnLDk1w1zo16rEFCfcg1+3En/AATJupY0t0+LGkhUUKuJozgDoB83QViH/gk74mv1LxfE+wZT0KlSD/48a+C9jjJzclJWvpqfQx4sy9L3pX9E/wDJH4Z6npUjDa6t+ArzLWtLuIpGJibaePumv3/uv+COni24YFPidYj8v/iq5zUv+CLHjW9Yxn4o2Q4GBx07/wAVfW5XGtGSdWSt6nDjOKcunBqEmn6H88N7avGrh1OSD2xX9QHwO1S4h+Cvg+JZQAuiaeB+FtHX5M/tp/sBRfseeHLTVvFPxMsdU1TUVZbPSIsNPOM/M2N2Qq+uOa/UH4KWUzfBrwkwU86LYH/yXj9q/r3wxSnQqXXb9T8J45xqq1KcoPTX9D//0Nj9ji0/0rVRJGrj7KSMjI+8K+07bQobh1jSxtyzHABUYP1OK+eP2HdAj1K+1UY5W3x/49X6G2vgl5v9GhIVmPB7Z7c1/iFxri3PMOVs/wBRMJFQpubV2fF978YP2dtI1u58Pax4k0uK+s3KTRQ2k9x5bLwVLIuMg112g/G79l6MebL4osuP+oZcf/E15j+zB+3v+w1+yT4V8RfBD9pzwJdXfiyw1y/lu7hrOOZpg8pKHzGIbG3oM1+1f7MHxC/Yi/a8+Fs/xg+D3g+wTQ7G4eG7e8sY0ZDEiyN69FNfo1Xw2o0sLTxErvm7PqfiOYeJuLp4mdONPRH5z2P7Sv7KVq6pdeKtPCHg/wDEuuE/HlCOtfSvh6HwJ4v0CLxZ4T+xanpd2D5FzbqGRio5B4yD7Hmvjj4of8Fif+CZdj4S8WaP8N/BjXGu2VvPBp8/9nw+TJdbWRCCu4KNwyCwwcV61/wTCs/E2p/sc2PjLxtaSWt/4g1G61BUkTy/3cjEJhNoAXHIGOleHxPwDPL8D9flpd2t1Pa4T4xxGOqONeNke66h4F0C48L67NHYwqf7LvFzsHQwv0r8Kv8AgnB4b03S/wBkrxF4mNsCNAmu7uWMMcTurNgE8kAgYr+kzWdPt08Ga6QBxpt5nj/pk9fz9/8ABPjSxe/sP/E7ywOIbk8e/mVtwhUvldeh0coX/E+qxWOax0VB9D5L0L/grLeeI7i6g8K/B+W6gs5DEzrcMwLL6HZ+Ndzb/wDBTrxZxu+Dk8Z9DI3/AMRXy3+xx4faX4f6osQBK6xPg4yTwtfWup694J8L6ibHxFqUFpOf4Hxn9a+6zfDZdDEzwtLCXs+8uyPo6UZxpqtVqaF2D/gp54qAH/Fn7j8JSP5pWn/w868UY/5I9c/9/f8A7XWFb/EL4Uh8NrMHr1WtH/hY3wq/6C0B99yf4150eHMNLX6l+Mif7Tof8/EaQ/4KdeKeP+LQ3OP+uv8A9rpB/wAFOvFpbK/CGfH/AF1z/wCyCqw+Inwr/wCgpb/mn+NPX4j/AAtHXUoMe5X/ABofC9B7YP8AGRUcfh5b1EaCf8FN/F+Pl+ENwT/10A/9kNH/AA8x8YP/AM0huF+kmf8A2SoU+JPwsx/yErf8Cv8AiauR/Ez4WIP+QlAufVk/+tS/1Wo/9An4yL/tHDx09qhYv+CmPjEDH/Co7nH++P8A4mrP/DzHxn2+ENx/32P/AImmx/Ez4XNz/acB+jL/APXqST4k/CzvqcOf95axlwxQ/wCgP8ZD/tnDr/l8hB/wUt8Y5/5JDcf99j/4mmv/AMFMPGIPz/CG5x/vj/4ipE+JXwrI51KE/Vv/AK9RyfEf4VE4/tC3/wC+/wD7KhcMYf8A6A/xl/mH9tYf/n8IP+CmHi8nMXwguse7/wD2FJ/w8v8AGv8AF8ILk/8AAv8A7Coz8R/hSBg6jb4/3/8A7Kmn4kfCbvqNv/33/wDZUv8AVmh/0B/jIn+18P8A8/kWR/wUx8YAYb4Q3Q/H/wCxFJ/w808YZ/5JBc/99f8A2FQD4jfCk8rqVv8A9/B/VqP+FifCn/oJQf8AfQ/+Kp/6tUP+gT8ZCebYZ71UXU/4KZeLANx+EF1x/tgf+y09f+Cm3izOP+FQXP8A38/+11RHxL+FecnU4R9GX/GkPxQ+GH8Oow4+q/4ij/Vim/hwf4yMpZnhulVGqv8AwU18WHr8Ibn/AL7B/mgqdf8Agp54qjOT8Ibkf8CH/wATWGPij8NO2pQj/gS//FUH4nfDNs51OH/vpf8AGofDMFp9T/GRSzPC2/io6Uf8FSPFI4/4VHcj/gY/+Jqb/h6Z4uxj/hUVz/38H/xNcj/wsz4YD/mIwf8AfS/41L/wsn4X9TfwfmP8aS4Zp/8AQH+MgeZ4T/n6jsU/4Km+LVH/ACR+4+vmf/a6sj/gqn4rVefg7cfjLj/2nXEH4nfC4LhNQgH/AAKmD4l/DJuG1GAj3bH9aP8AVWP/AEB/jIqnmdD/AJ+I9AH/AAVb8UouW+Dkx/7bH/43Ukf/AAVq8XRjavwamOP+mhP/ALTrz7/hZ/wuHC39tj/ez/U1DL8T/hd31G1H/AlH8yKFwpB/8wf4yOevmNBq3tEelH/grn40BwPg3L/38P8A8SKT/h7n42PH/Cm5P++z/wDE15iPid8L8f8AIQg/Bl/xqYfEz4YHj+0YfzWq/wBU4f8AQH+Mjl+uUH/y8R6cv/BXDxmFyfg1If8AtoR/7LS/8PcvGR+58F5P+/p/ohrzZfiZ8L1ORqUJ/wCBL/8AFU4/E/4XHrqEB/4Ev/xVC4Vil/uf4yH9cw/Wqekj/grr41HJ+DDj/tsR/wC06D/wV98Yqdp+DD5/67H/AON15sPif8Le2oQf99J/jR/wsr4WN8x1GDP+8v8AjVf6qx/6A/xkH1zD/wDP09NH/BX7xrjH/CmZP+/v/wBjUy/8FdvG0g4+DUv4Tf8A2FeVv8SPhQOf7Qg/77WnQ/Ez4U/9BCDH+9SfC1P/AKA/xkTGvR/5+o9di/4Kz+OZOP8AhTcw/wC23/2ArTi/4KseOJBn/hUFyP8Adl/+xrySL4p/ClOTqUP/AH2P6mtq0+KvwkO4/wBpQ8Y/iX/GuCtwtHb6p+Mjr+tUVr7Q9OH/AAVP8bt0+EN3n/rr/wDY04f8FTPHeP8AkkF1/wB/v/sDXCQ/F34RLwdThH/Al/xq5/wtz4Q451SL/vpf/r/zrn/1Sh/0Cv75Ff2nho6uR2P/AA9J8eDn/hUN1/39H/xNRv8A8FS/HRGT8ILoe/m//YVx4+L3wjJx/akP/fS1G/xd+EYPGpx/nR/qlD/oF/GRMszws3pI7Ff+CpnjrPHwiuj/ANtf/sKd/wAPTPHn/RIbr/v7/wDY1xX/AAt34SHrqUf50f8AC3fhIOmpR/nR/qlD/oFf3yLjjMN3O4X/AIKk+OiMn4Q3X/f3/wCxpD/wVK8b/wDRIbv/AL+j/wCJrjE+MPwjHynU4h+NOPxe+EhJP9pxfnWq4WVtMN+Mivr2E/nOyP8AwVI8cAZ/4VDdf9/f/saaf+CpvjlRn/hUN3+Ev/2NcUfi/wDCFvlGqRfnSp8WvhKG/wCQnEfxH9aHwsumG/GQpY/CJXUztF/4Kn+OG/5pFef9/f8A7GpP+Hp3jsfd+EV1+Mv/ANga4w/Fr4Sd9RjP4j+lMPxd+Eg4/tGL8TUvhdpaYb8ZGazTD/zHcD/gqf4+/wCiQXJ/7bf/AGun/wDD1nx2OP8AhTs//f4//G64T/hb3wmxkX8Z+ho/4W98I886lB/38H+NC4Xv8WG/FkPGYaf2juv+HrHj1uF+Ds+f+ux/+N01v+CqXxDI+X4OTE/9dj/8briF+L3wkzldTgB9nB/qal/4W98Jjw+pwke7KP8ACj/VaH/QP+LKjXwy6nYj/gql8Q1+98HJv+/p/wDiKjk/4Ko/EVjx8G5iP+up/wDjdcgfi78I/wCHU4B/wMf/AF6aPi98JD/zE7c/8DX/ABFXHhaH/QP+LG8Th7/Edd/w9Q+I3/RG5v8Av6f/AI3Tm/4KofEXHPwbm/7+H/4iuQ/4W78JBydSt/8Av4v+NJ/wt74TH/mJw/8Afa058LwX/MP+IPFYf+Y6n/h6d8QzwPgzL/39P/xFH/D0r4iHr8GZP+/rf/EVyLfF34Rg8alB/wB/F/xqNvi98I+N2pwD/tov+NZvhmH/AED/APkzLeMw3834nZf8PSviEvX4NSf9/W/+N1G3/BUv4kZ+X4NyY/66t/8AEVyw+Lvwfx/yE4PwcH/Gl/4Wz8IG5/tKE/8AAxS/1Vg/+Yf8WCxeG/mOp/4ek/EXHPwZl/7/ADf/ABFRf8PSPiEeB8G5f+/rf/G65v8A4W58HOh1OLP++Kd/wtv4O/8AQTj/AO+hR/qpH/oG/GRSxuGXU6Nf+CovxFY4/wCFOyj/ALat/wDEVKP+CofxB/i+D0v/AH+Yf+yVzA+LnwfH3NSjJ9yDS/8AC2vhE3/MRiH4gVpHhKL3w/5ieOwvVnTf8PRPiH/B8H5Mf9dmP/slOH/BUP4i4/5I/L/39b/4iuUb4tfCMH/kJRfnTf8Ahbfwf76nD/31in/qjD/oHYvr2E7nXn/gqN8Ru3wdl/7+t/8AG6Z/w9G+JHf4OyD/ALak/wDslcv/AMLc+EBH/IRi/wC+6jPxZ+D45Oowj/gYo/1Qj/0Df+TMxeNwv8x1Z/4KkfEft8H5P+/h/wDiKhf/AIKkfEZuvwek/wC/rD/2nXNp8Wfg6xx/acX4Mv8AjUo+LPwcHI1OL8XUVM+Eo9MN+LKjmGGv8RtH/gqP8RBx/wAKek/7+t/8RSj/AIKjfEQ8j4Oyf9/W/wDiKwz8Wvg3nnU4PxkX/EU9Pi58Gzx/adv/AN/F/wDiqyXCNv8AmF/Fmv8AaeF/mNc/8FRviOG/5I8//f1v/jdO/wCHo3xHH/NHn/7+v/8AG6xn+LvweyP+Jpbf9/F/xo/4W98IP+grB/32tUuE0t8N/wCTMHmGGf2jYb/gqJ8Rm+98HmP/AG1f/wCN0D/gqJ8Rh0+DzD/tq/8A8brH/wCFu/B89dWg/wC+1pp+Lnwg7apCfo4p/wCqkf8AoG/8mYfXMN3Nr/h6N8Reh+Dcp9xI3/xFJ/w9E+IfX/hTMuf+uh/+JrHHxa+EZGRqUP8A38X/ABpf+FtfCT/oJQf9/F/xqf8AVOH/AEC/jIPr2G/mNn/h6J8SP+iMSD/tqf8A4ij/AIeh/EnovwZk/GU//EVjf8Lc+D7cf2nB/wB/F/xpP+Fs/CEcrqkI+jqf60lwnD/oF/GQfXsN/N+Jtf8AD0H4lHr8GX/7+t/8bpw/4KhfEcff+DcoP/XQ/wDxIrF/4W58IR11SH8XUf1pD8Xfg/8A9BSD/v4v+Naw4Ujf/dvxYvr+G/mNs/8ABUT4iH/mjUp/7aH/AOIp3/D0P4igf8kal/7+H/4muePxc+EOeNUg/wC/i/41ZPxa+Ef/AEE4P+/g/wDiqt8KxW+G/Fj+vYZ/aNlf+CpPxIU/8kak/wC/h/8AjdSD/gqX8Rv4vgzJ/wB/D/8AG6wf+FsfCI8f2lb/APfY/wDiqT/ha/wh/wCglb/99r/8VQ+GIf8AQN/5MxPF4Z/aOhP/AAVL+In/AERiT8JD/wDG6T/h6V8RT/zRmb/v5n/2nWB/wtr4Qrx/acA+jj/E00/Fv4R541OD/vtaxlwvC9/q34yBYvDLqb//AA9G+If/AERmb/vv/wC101v+ConxIIx/wpaX/v5/9hWF/wALa+EP/QTg/wC/i/8AxVB+LHwkx/yEof8AvsUv9Vqf/QMvvkP65hv5jX/4ee/EVj83wWl/7+4/nHUT/wDBTfx+2P8Aiysv4Tf/AGusn/hbXwjHJ1OH/vof0o/4W58Iv+gnB/33T/1Xh/0DL75D+vYf+Yuv/wAFMfHjdfgpL/3+/wDsKqyf8FKPHbn5fgs/PrN/9rqJvi38ICedTg/77p0fxe+EYOBqNuR/vUnwtD/oGX3yKjmOHi7uREf+Cj3xGfhfgsw9/MP/AMRVGf8A4KJ/EJ/+aMSZP92Q5/8ARdbX/C5fhSvTUbcf8DWmH4z/AAkcYbVLcj/fWhcLQX/MN+MjVZnhn9o4+4/4KCfEVsufgzOP+2h/+IrnL3/goH8QFQyN8Grg49JP/sK9Dvvi38Ijb5XU4icj7rrn+YrgI/HHgrxXO1h4d1FZZAM7Q+SOT6E1f9iUKSvUwui85GsMVRn/AA5q54h4p/4Kkz6HqVnovjP4Uz6Wt/II0leUAe/8Azx6V+mfxC8E2dho2pWIjWSIaPDqCBx8uJ0D8f7pOBX4V/tw2KnWfCMZ+XF1vIznOCK/pj+KXh9X0m52ADd4PsSRjknLbf5CvK8QMJg6GX4bF4KHs2+a+5hhqsvrEqUmeLJp+jT6VYn7HaKiQREfulIAKj296p+I9S8F+B9Pi1jxtNouiWVwxSGa+iUeYw7KuCxI6ZHFex+HvCTf2ZZqB962hIH/AABa+Zv2ibv4H/Bv9p34f/FH9qvSTq/w5+x3Nm6SRNLbw3GM5Kj5SwJBIPavzbgihLN8dHBVJtc34HHxVjngMJPEU1do39M+LX7NshQ3Hizwwc+tuR/7LXq2nfF/9leCIK/i/wAN4X+6jDH4bf616v8ABP8AaV/4IpfH74oWPwk+GvhnRZNc1SVbewhksCBO7A7Qp6YwOc16z+1N4w/4JMfsYa/pfhz48+CtHtNT1aIzQW9taGRjEG2lzzgAMOtfsMfCVfWlhJVGm9tLH4biPF3Gxg2qN2eS+AvEnwT+I9w9t8PdZ0fWJoT80duAW+m04J/CvSdQ8H6SlpKRZQl2TBIjA79h2r8yvhp+0B8Cv2if+CrOhWX7H+iwab8P9A0aY3E9rbfZo5ZTG5LSevzMo98Zr9pF0uzaeZShCfwj2r4rjnhGWTY5YNz5tEz9Q4Z4kljsIq04crtqfzBf8FhvCthaftcfDO4WBI3k0p87VxnDOB+gr9Vfg1LPF8IPCkSYCro9iBwOgt0r4D/4Ld2kVr+1t8KBGpG7S5v/AEN6/Qn4QxL/AMKm8L/9giy7f9ME96/uLwfrSeWRu/sx/wDbj8k41adWLXn+h//R+yP+Cduki6vdaPpAf/Qq/TIeHVTDRjJzXwp/wTe02PGvT44SLb+JNfqNDZwsMY5r/DDjuDeOum1qz/TPD5jaDi/I8S8Y/CX4V+KfDfiLxD4x8I6Rq99Fotw32m8tY5JX2IfkLsCxHueR2rl/+CdGn6NpP/BM/Wo/D1jDp6btaYrboEDEhsHGTztAXJ9K+j/EsCR+A/EqcZOj3n/otq+ef2ACYf8AgmvrOOgOsf8AoJr7rhHF1XSUXK+qPwvjuEHifdW7Pzt/4JB/Cn4N+Iv2Qr7UPGPg/SdYurbxJebbi7tkdyXfcDuILfLnjOfYV+wxuopI0t4Y1ghiAVIol2oqjgBRgcD6Cvym/wCCOszj9jrWIyOf+EiuCf8Ax2v0+DkAsv1r5vxFzyf1+pCrJ2ufo/COVwjSU7alzXLjb4L8QEdBpt1/6LavxI/4Jg6at9+wT8T5m7pd/wDtSv2T1+7Y+DNfUdP7Mus/9+2/wr8n/wDglFpT3P8AwTo+JV6ACDHd/oJDX0/h7+8y6u13h+pnns/YYqMn1aR+cv7Efh23m8FalHjLf2tN/wCy1+Y3/BWewuNJ+INneWsjR5uRGSpI4J9q/XX9gy08zw1qitjC6pN/7LX5Y/8ABZC1WDxVayA4xfLj86/b/CdRq8SxclfV/kaeI+IlRyabpuzsfjbcXOq72xfS/Kdo5asyS+1RQW+3TZ/3mFblwV3ssfXeD/OsqVZkDGbq3civ9FKuUYRRjFUlsfwa87xf/PxmU+r6wg2i/n/77ao11XWgwJ1C54/2z/8AFVO8bdixB79qqtG7EDb1zWcMowvSmhf23jF/y8ZaGra121C6H0Y/409dU1s/8xC7P/Aj/jVePapIBwQMke1PcZ+UsP5Vf9kYb/n2iHnGLf8Ay8ZJ/bOrq+Df3f8A32f/AIqphrWtPx9vvMf9dD/8VWZ5Tkn7wx+FLEqt8wGffNZPI8M9eRFLOsWtPaM1k1PXMf8AIRuv+/jU7+09aHzf2hd4/wB5v8RVdIkUZK/rVpVQrhVYH/ez/Oj+wsN/z7Q/7bxf/PxjRq+sdtQux/wI/wDxVTR6rrR+b+0Lsj/eP/xVVmby9xYOpBxg/wBKUOXXKgke5P8ASh5FhVvTQLN8V/z8ZrR6lq+f+P685/2z/wDFVb/tXVh/y/3f/fZ/xrDRlLAFxk9OasGUqMZyRwcUv7Ewn/PpB/a+K/5+MvHVNQxxqF5/32f/AIqq76nq3WO+u/8Av4f8TUPnq3AUnNRSbR22nOM0f2JhP+fSJlm+L6VGT/2trCfev7vn0kb/ABFNbVNVfkX14vuZG/xNU/MzkK2cdccUzcrffLn8a0jk+EX/AC7RP9r4v/n4y9/aGq/9BC7P/bRqsQ63qq8LqF3/AN/GNZLNAi7t+PY9aekoXGzPJx1qv7Jwn/PpB/a+L/5+M1X1bVmYMdRuv++j/wDFVImp6qTj+0rzj/aP/wAVWYk8rE5IAXqT0rQt5TOTs+YZ6jitHlGDt/CRVPN8Xt7Rl3+1NXjHOoXP/fR/+Ko/tbWeov7g/wDAz/8AFU9o8H5weemTmo3jA5IxWf8AY+Ee9JErNsXza1H99xf7W1rtfXH/AH2f/iqjOo613vrj/vs/40FFHTn6CkcRseBR/YuD/wCfaNP7XxX/AD8f32Jo9S1cDnULgfRz/wDFVFLqOsn7uoXP4uf/AIqmbE9P1o2oO360/wCxcF/z7Qf2vi/53/4EQHUNbAOdQuR9GP8A8VUH9oa2f+Yjdf8AfZ/xq8yKwJxUUaIxyKX9i4P/AJ9oxea4q/8AEl/4EVv7U10fL9vuv+/h/wDiqge+8Q9f7Rux7+YT/WtYrjjjPpjmqwVQwpf2PhP+faKWbYv/AJ+Mw5b/AMS5yur3Sf8AAj/jUial4nC8a1df99n/AOKq9cQgthVqhIqLlW/Sn/YmC/59I0ecYvpUf32Hw6t4mXg65dj/AIG3+NTHXPEYOP7eu/8AvtqyR5a1CWUkjGaHkmD6UkQ80xj+Ko//AAI3/wC3PEfX+37r/vpv8a0LfXfEJAA1+5P4tXLiIEZAq/bGQLuA6e3/ANanHJcGt6MRLMsV0m//AAI6GbU/Eb426/c5+rVB9v8AFHbXrr82FUY5nJyDn/P0qTznHGf8/lVf2Pgf+fMSv7SxX/PyX/gRcGoeJcfNrt2f+BtUw1DxKemu3X/fbVAvmbeSKVGkBPI/Ks3kuBf/AC5Rm8xxX/P2X/gRchvPEuf+Q7d/99tWjFfeJI+Trl23tvb/AOtWfFI45yPyq2rTHkkY+lH9i4D/AJ8oP7RxP/P2X/gRabUvEZ/5jN1/30f/AIqk/tXXRwdWuj/wM/8AxVRb39f0pD83Lc03k+Ce1JB/aOJ/5+y/8CJDqniInK6pdY/32/xqI3/iX/oKz/8AfZpaaOe1J5Dgn/y7RUc2xcdqkn/28L9v8T/9Bef/AL7aj7f4m76vcfg7f4UwkDqKAQegpf6v4H/n2i/7dxn88v8AwInj1DxIM/8AE3uD/wADannUvEvQavcj6O1VwfUYpA2TnFZLh/Bc38NGsM8xdtaj/MtfbfE3/QXuf++2qYXniLr/AGtcf9/G/wABVfeuQPWnhhmnV4ewXSminnmK/wCfjLa3+t9X1K5P/Az/APFVKNT1deuoXP8A30f8ap+Z/n/IpruuKw/1awS19mjH+18V/wA/pF1tU1UnJ1C4/wC+z/8AFVGdW1cHjULn/vs/41QMgFM89fSrhkODTv7JAs4xX/P1midW1cddQuf++z/jVSTVdXJ/d6ldD/gZ/wAapu5bpTK0/sTB/wDPpD/tjFf8/GWH1XXgMrq1yp9d7GoX1fxFj/kNXX/fbVWlYgYAqvnP3gKznkGDbv7NEyzrGLab++w6bVfEmf8AkNXX/fbVSOreJhz/AG5c/wDfbU+YvzsHAHpWZKH7sB+FL+wMJ/z7RP8AbeM/nl/4EWZNX8THn+2bo/8AAj/8VWZNqvicg/8AE6uv++z/APFU5jgYNZz/ADtgVSyPCr/l0jT+2MV/z8ZIdU8Sjj+27r/vs/41VuNS8UMBjWro/Vz/APFUzauc1E4RvlHWtY5Lg1/y6Qf2ziv+fjIv7T8VLwNauR/wM/41HJqnis9dauf++z/8VTHRRn2qu5Q9Kv8AsjB/8+kH9s4r/n4yz/anivvrVyP+Bn+jUw6t4oXn+3Ln/vtz/Miq1MKDFP8AsnCf8+kH9s4r/n4y3/bPib+LXLr8z/8AFU0614m7a5dfm3/xVUWVc7fSm7Fo/snCf8+kH9s4r/n4y8dV8Rn5m125/Ev/APFU06r4hx/yHbn83/xqntAxxTuRxx+X/wBen/ZWE/59IP7YxX/Pxk/9q6//ANB66/N//iqBq/iD+HXrr83/APiqgJI7j8qTcfVaFlWF6U0H9s4r/n4yZtV8RP1166/8f/8Aiqb/AGp4hH/Mfufzf/GomDNjkU2Pcw4wf6VX9l4b/n2g/tnFf8/GT/2r4h/6D91+b/40p1fX8Y/t+7/8f/8AiqjwO+KayzZ2Z/UUf2Thn/y7Qf2ziv8An4wOra/jnXrv8N//AMVSLrOvA5/t+8/8f/8Aiqr5OMljg0KrP9wsaP7Iw38iEs4xX/Pxlxda1/tr94Pxf/Gj+2te7+ILz83/APiqoMSMgt9316/hTSGHVsfyprK8Mv8Al2h/2ziv+fjNH+29f/6GC8/N/wD4qlGta7/0MN4Pxf8A+KqksbsMpuYeoxioQWBHzHPXHFH9mYf/AJ9oP7ZxX/Pxmt/bevH/AJmK9P1L/wDxVNOta+P+ZhvD+L//ABVUd77SwycUxjI3qPyo/szDf8+0H9s4r/n4zQ/t7xCvA8Q3n5v/APFVG2seIGOT4hu8/R/8az95zgSCnh+OWJI647Uv7Kw3/PtB/bOK/wCfjLP9reIuv9v3X/j/AP8AFUi6r4gP3PEN1n6v/wDFVXIOSN9IDtfClST7U1lGH6QQf2ziv+fjNG31fxRJOkJ166IfI4Ljsf8Aar9hv+CPEuoanr/iFryd7hm8tN0hJOMt6k1+N9sXa7t1OOpx+ANftJ/wRStxN4h14NzmSP8A9mr8s8bMvo0uHKrjFJs/UPB/NcTPOoRnUbR9z/tuWyL4n8Jq/Vrgj/x5a/q++JnhyG50pyw6eD7H+T1/LJ+29ZL/AMJj4OQ97of+hKK/sG+Ifh0DQPPYcf8ACJ2Kn8nr/NnjjLnPKKLWqvI/rLMcw9jmtNdH/wAA8V0Tw1Cml2T7ThbeJe3QIvrxW3qvw68D+P8AR38L/ErRrXXtIkYE215GsiA4+8Aehz6V6fp+iRR2FshAwkSD8gP8K6C30+BcBVH41+G5Fga+HxHtIOzR7Oc46OIp+zlsfm74T+AvwL+HX/BUfwJD4G8E6VokEWg3M6Gzh8rNwAcSnB5KcgHrXkX/AAUD8F+C/iD/AMFtPgxoPxF0mDXdLn0WRZLS4AeI8ykOyuQDtI/WvsPUJVf/AIKeeBlAPy6BeLjt0kr5d/bWOf8AguD8FuxGizj/ANG1/T/CuZ15UJVJzfN7N6n89PBU3mLgtj798L/Cr4L/AAuub+1+D3g3TfC0d5IRO9nEqSy4PAJHQd8dK7gHZuwSxx1PUnPt/Sq9/Mq30oJ/5aN/M1TluiIJHXqMH8M1/O+ZZ/VxOLvWd5H71lWWRw+H5aa6H89v/BbjEn7XXwlXv/Zkv/ox6/RX4QMqfCbwujdRpFkP/ICV+cn/AAWdJvP2w/hLGen9mzZ/77ev0e+FlpGPhj4cGT/yC7P/ANEpX+iHg/VX9nRu/sx/OR+PcW03+7TXf9D/0v05/wCCc0Kx6b4ikH+yP1r9IGmWEDHevzw/4J72V5FoWvTrG21mRSwUkZPOK+/LiK7HJgk9/lb/AAr/AA+40XNjG07bn+kEOVNpyRB4tuGk8E+IYIfmeTSrtFAPUmNvWvkj9g/4r/CjSf8AgnRr2g694m06xv4BrHn209xGksWQ4XchbPzY49a+r4xepN5qRPggghkJBDdeMV+fPj7/AIJY/sjfE7xhqXjbWNL1u3n1eUzXdvaXLRWzsev7vaSAfr3r2+BszwVKUljpPpax8VxNw5LFyjKlK1jyf/gjrPFc/searLasGjl164KOOjAADI+tfpySyrtzXHfDj4PeE/gv8PrL4XfCfRn0nQNPz5UJBLMxOWdm5JJPc13selaiUyIH/I/4V8NxvTWKx86tBNxb00PvMipww+HUJS1Of14CPwR4iY8kaXd/+imP9a/Pf/gkVYRy/wDBMT4lXHomo/oj1+jOuaFq0/gvxGiQPltNulXII5MJr4A/4I9ROf8Aglh8UPOXaVXUxz6hWGMV+1+D2TOeBxC63j+B+a+JGZWlTnB/aX5n5ifsDFj4Z1RvXVZz+q1+WH/BZwE+JbXHe+T/ANCr9Wf2B4mj8H6jkctqcx/Va/LX/gsnAT4pgXHC3yfzFfqXhG0uJbr+ZnqeJFVyyJyfY/GQxN5khb+96etQXNsSvAwP7zdK6I2u4yueDvqo9uzMRgHk9elf6SSknsfwYmcncW+QDu5A/h6flUX2NXbZsYlsck4FdW2nqewPryKhXToy2Yo9xQ5wW4NSUc4LXpCjAFsjHXp71AId4aSMAY4OeQTXSNb/ADqyxRr5mSBnBFV44N2f3QGTjyxn880AZP2Qk+WQzEenTPpSJbuXKkfd+92wK6KSIPl3jMWOoVuaqG0QD5mYHPcdRQBnNa723qr7R3BB/PmmRQxyEhycDOQa1Wtozlgigg4yOD/h+lRyxI7BGwhHTGTn6nFAFJbaFI180gDGN5Oc+1VmiClssNyjIXPUetbCwRoQyDfjqD0B9quKqtsG8bV9FyTn1NAHPxmaMGNuMnAAGevU1ZCSyx5fPmHPIHUjrWpFb5l2I+AMjJ/iBOR/hWgsZOFjG0EkDJHGTyelAGEpJ5csTjHzDBqvcBo/3UnDdB3GO35V0+AWMZlG9eu5c/lWfdxDzAoUFZOp7/lQBx5lcyFYzuZsjAHHHfNRpLI+RuAIGcMDWnKqpM2QIwoOAves+VC77SdwXGO3bvQBB9qBcMWwE4zjv7Cnx3DFl8w4LHP4fWqc0RkO9xkj19vSq8m4Dd99c5x6UAdPDIGYqWVgeAPrV+KYu8cRChtpAUcLx7+tcjGzRzGRIlHI2ktg5960YLkNGIhujzkuMZ5z/CfSgDrre5RXV8BkPHByVPoatedFJwRjPQE81yP2pGQ/JjPGQevp0qGO6+bfzn3OcUAdssTJyBgdzTti1madPLKMsd2OwrVPSgBuxaNi1GZgODTfNk7AYoAkZeCvaqKsY0wvvVsvvXFROCFwKAK+Cec9e/epEVSMAcdfxpvze1KpZT2oAWWPncKovZiQkt3rXRd33jn6VaW3jC7uaAOTbT+eATTBp7A5xXYLEG7U7yB6UAcitgwGAOasR2hUY5YjrXQtC4OBTvLwOmDQBifZkzkcew6U0WyliTxzW2YQeSKrmDk0AZ+1kGAc1JECRuHTv61OyYOD0Heq7OYjuTr2NAF2BVbgnFXFP8I6CsFbkBiR3rUhmBGSaALtFRebnpSZB5agCag+3FQ/L70fL70AKxB5zSKcGm4XsTSjqKALSpkZp2wZpU+7UijPWgCBk2g0wrICAKuHGwYpQgUcc/WgCoDIc57U3JI5q0I/UUSRqRmgCoehqA4AzVp0wOKpSrgUALvFMaRccGoMY+8TTSrDnFADiC5z2prLtozng05kUL9aAKMp3HdkgDrWQ43d61J1CjDnbnvWW4aMFsce9AFWXgdc1ULlTvHappDnJqvQBHs3c+tNcKvy+tLICBuU1WZpNpc4wPWgCsvysR+lQOzp/hUr9j3qOdTQAw8DNIDlc1HvJ49afgBcUAQk5Ymk5zUgQE5NKV7CgBhJBGO1NLZPHNO2gcFgPrSJGQxAYcetABTdqyEqwHHPFS+Vu+XcKYEUrw3Gcc0AKPmUA5UE8Y60rMp3L1H8XuaZsjAZWc9sYGTSoQoIUHn160ACkOOeAc5/Co8EcqMYPc1J/Dt+v61GASVGTgDB+tAEirG4Kqy7gc4PPFMCIz4KjLDjnABpCqnsSR6Yp6xqh3Kp/nigBoijU8quQO3PIpAUdQ3GT+VPXKgbGBwc8g00DnaAKAIysbcsM47dqWTywFZSOMnpycdjUoK7z93j/PpTWjViV+7gkg/WgCntDnecgY3cf3T3phPQMMjPBPPBq15Y3DLk9sdiPSlNuWDAEr049MUAQF2UlA35ClJJGHduCO3BNSeSHYAMwU8npkfpQ8IDH5mOOe3+FADGLoN24gjp9D1FNDZO4E4HOPWpWijcNlzwc/n+FCwK67TI35VrAAsmDXlv7Fj+YNftz/wRBi8zxFrz/wDTWP8Ak1fiTGnkXcCR89eo9jX7gf8ABDVS+t68CMnzo/5NX5N46Stw5U/rqj9V8G2lnMbn6Hftx2uPGvgkjvdA/k61/Z38SbBV+Hb3ZXgeFrH9A3+Nfx2ftv2R/wCEx8EbuP8AS+foWSv7QfidYzS/B6ZrZDJI3hizVVVSSTg4AAHJPoK/hOplf1nh3mtdxkz+h+PMf7LMsM79H+h4wkgVEQdAF/lSi8RJh9QOPrWU66uoANlMuAByhPTisq4i1ZicW8oz6qR+tfzbXy6rRm5PRH2WFxlKotZHypf6xpNh/wAFQvAsmt3cNjDJol2qyTvsVmO8BQTxk54Gea+a/wBtnU9Ivv8Agt18GJ9IvILrGkTq3kuH28THnbkDjn6V9PftP/se/DL9rjTdPsfib/bOl3ulPut9Q0nEc6DIOzcytlcj0z7149+zr/wTX+AH7Lnj7/havhN/EPiPxMsTQ297rbCZoQwwxTaqYyPX8BX69w3nWW4fK5+1qXqcvKl6nwlPhyUczliU/dZ9uanva+m38De386oySN5Eqg/w9fxq+um6lIN0scjMc5Ow/wCeKSXSNS+zyOsDncAB8pr+equW1frPtFsfslDG0o0uVyP5+v8Agr+vnftkfCdSeRp03/oT1+mXwvjK/DTw6vpplp/6JSvzY/4K5WNyn7aHwn89ShOmzsAeONzeo9TX6h/DG3UfDbw8MH/kGWn/AKJSv9FfCenKGAin/LH85H4txnVjGUJd7/of/9PU8SaV+2Jea5/xjb8Sz4J0t0Xz7Vd26SVf4jhTx6VsWfw0/wCCpeojef2h5U9sSf8AxuvcPCsBa4dT82DmvdLK/wBM0TRdQ8Ta4wisNJtZbu4kPQRwqXIyeOcY/Gv8a8fxhjadaOFw1OD6axTbfzP9LKfDeFxCdSd0/U+SdM/Zx/4Kp62oeL9pCSD0P7wf+yV2lh+xp/wVdvjx+0xkkcbhJ/8AE17R+xT+2D8P/wBtLQda1TwVpjaPdeHJkSe1kYFnhkJCTLj1xz6V+k/hdsx/Idy5Bz/SssfxXmeFrfV8VSgprdckf8jyMRkmH5G4N6eZ+S8H7CX/AAVlmG0/tOxxk9AUkP8AJK2Yf+CfP/BW6YYT9qGLJ/6ZS/8AxFexft+f8FMPE37AXxD8MfDPwt4OPi668SWn2hGWQhwwYptChWz0zXyNbf8ABf79opCFh+Cl9keqvj/0Cv1bIcHicRTjWrUKfK1e/LDU/NMwwOKnJvDybR7K/wDwTi/4K039hPp93+1DCI7hHjk/dSHKuNrD7nccdq/QH9k39kW8/Yh/4JzeOPgjr2uweJNWt9P1C4u7u3R0DNNGzAEP/Mda/LuH/g4B/apmKQ2vwcvI8n/nm7f+yCpfEn/BbD9q/wCIvhHVPBN18IrryNYtZbRiUZNolUpk5XnGfWvtKObLDQcVCMU97WX6nzNXh3N8RUgqkHZNfmfMP7BdqT4QvmK4zqE3/oVfld/wWVhf/hL4Fzx9vT+Yr9zv2QPhjq3gHwdDp3iSMJe3chuZEUfcaQhtp+ma/D7/AILPwyQ+NIB2+3J/MV854O4pT4iUo9ZH6T4nU5RyaUX0X+R+OLwyB5QuMb/61Va1csc46nvV58hpcqSdxpG3M2Ng4x3r/TGEdH8j+EFGzMwW+PlCLk8U77NlkVgOFJ46ZHvV/au3aqfdbk/WgRptIIJz2H1plGS9sjqEmCqGGSQM4IqF7SzcFvm+YYAXIII79e9bhC8rH65polcSAZ8znkDigDDOn7kRhEcHJyG5qutlGvzEyL8vGefwrdMbFo1jj4YeuMUNG2dhGF7jPSgDHGlxKu3BYHnk4qaO0KfMWKqvbr0+tXlh3NuePLBjk56U4QuQXXt/DQBkizjEpmZWBY5HHWpBZxhjJFlW9j+nNaexyQFJx1GT+lRMrM2AAS/XPSgCoEliVEYAcFccHntz9KYXTBLAHcMNwe3p71K4jRupZR1HoabGVBweDyce/fFADskt5W4KF6Ej/JrOuHkkbz96AdG45A9quEr16j/a6/hVW8QbDs64zQBz10GScxs6nkEMB0Rvr9KzpFm3sAm85+boBjtWlcoPNwBuG0Ice9ZzxQnIZiST1Gc8dqAMu4RoxtYEenBJ/wAKzbiQndMQwUYG7GMH6e9b0/nFSxY4UDp1/KsqSRvtEodic4685DfzxQBlzGRHKhN4DAMx9T3prztECvmMNh444IPUVbkDmNgBv29cHGR2P4UxQ8h2MQUwefSgCAvKIyLcFdxBAP61ehaUDIwN/IOciq6oHmVkJc7cZxWjb6YyYfOPbFAHVaVKWjXJJ4OcD0roVDiPLHmsbTysUaoW6HHSuo0u3n1bWrfw/pg8y/vmEVtG2MSyscKF9ySBQBkyIxG7jP5VGCTxx+ea/TS1/wCCOf8AwVDngW8i+G9xtlCuhWPcNpGeoyPepT/wRv8A+Cox6/Di6/78n/4mgR+ZqxHHFObCKN3av0ub/gjf/wAFRs/8k5ux9IT/AICs29/4I2/8FRyMJ8N7wn/rkaAufnCPLb7nFSqi7ulfoJF/wRt/4Knxnj4bXmP+uDf41qRf8Edv+CpQIX/hW12f+2J/+vQFz870CKew/CrzRqyAqQfXFfopF/wRz/4KlyEJ/wAK1uwT0/cn+oHb3r4z+Jvw18X/AAI8b3fwn+NtudF8Uaa4W8sZUIaMtyv1yOaC1BnmAAHSlVl3YNff3g3/AIJQ/wDBR74jeELH4geAvAFxfaJqsYntLhI8iSJvut17iukH/BGz/gqWPu/Di6P/AGwP+NBXs30Pzg3qxGajYYcV+kR/4I1/8FSyMf8ACt7r/vwf8ajb/gjd/wAFTVwP+FbXZHr5J/xoF7OR+cLAkYFQMrLzX3z4p/4JP/8ABTrwlZG9ufhdqNwF6rFbu5/8dzXxV8Qvhn8efg5MLX40eCNV8PfMVMlxbyIo9fvKKCWrbnISGNzjvVW5hHI6YFMtryz1CM3FkwkUHGQMYx6jtVxwSBuoEc9LAqYIPBqFr42vIr6K+Af7Kv7Rv7XeuX/hP9l7w+/iO/0eLz76KNSzQoW2g4JHX619Hy/8EXv+CrEpIb4ZXuc94CB/OgD85BrxX2/CpU8QvjCru98Yr708T/8ABHv/AIKh+C/Dl94v8R/Dq6tdN0yFri7lMYXZCgy7fN6Dnivzz2f6SYUk8xoztkA/hYdR+FAHRwahNdHcw25rQDNkAmsu3G0sH4IrotO0ufWNRtfD+nlW1DUZEt7OMA/PK5AVfxJAoArxck57VYHUV+h8P/BGr/gqZLbLcWnw3u2RwNpCFgcgHj5e45p0X/BGb/gqwz4/4Vre9D/yyx2/2sCgD8+wDkgdBUyc/LXVfFX4c/EL4E/EK++Dvxi059H8UaXtF1ZyYyoKhgcj1Bpfhb8PfiL8dPiDYfBz4L6cdZ8U6orNa2UYy7BRk/kKAOXMZ3Be1GT6frX3/wD8OdP+CsJ5b4aXQPp5ZP8AJTQn/BHL/gq+XAPw1usE/wDPMj+a0AfABzjim7XI55rt/il8K/ip+z58Qp/g98etIl0DxNbgO1rOmzcrDIZDyGFcO7mIlc4oAgy2/aelUZjnCryT+lW5H3nIOeKyrmeO2ZPO5aZgkSr953bgCgCQiNX2yHNS4RuVFfcfhT/gkr/wUx8d+GLPxr4X+G19JpmoostuzRNlomAZT68gg10o/wCCNf8AwVTZCo+G15n/AK5P/gP50AfnNM0QbaeDRuKqeelfTP7QX7Cf7Yv7Ivh608a/tO+E5tA0i/kMNvPMu0tIBkrj2HNfL889nbWwnupdtuduZdueGzigCpK4ZNwOecVUZsDr9a+6/hr/AMEt/wDgop8bfB1p8SfhN4EuNT8N6ku+yu0j3CVOx4PFdZef8EYf+CrSLlfhld/Ty2/wNAH5sylCmQetVsqOW6V+iz/8EZ/+CsHb4YXpHtAf8Kef+CNP/BV0REt8Lb7/AL8MaAPzmbaVOD1rLnyV2D1r7Y8a/wDBMP8A4KZ/D2zk1DxF8KNW8mLlmis5mGP+AqRXxR4hs/FPg/WP+Ef+Imi3mgXittZLlGXJ78MqkYoAi+8wB5xioJgFYsOtTqySf6ohl7FehHrUEu4HcOg4oAiABO4dB/n1ped2096eAAaaT8woAdTSwHBoZ/8AP+RQMNyaAFBBGcUvVSx69KZjGSKfn5do/DPr3oARpVA++v8A3zSeZvXd8vsMY/GmmUkYpTkqA3PNADl3svHXvioGEgfGCfr3qdlPymNQTz+VMAUNujBUdiaAIyk+SqAEDnPr7UCJweQSpIOcirLH5dyHkVC0aKuxT17Ht70ARiRlIA75oC7eMnP1P+NBDJ1xxQSkgxnmgA8wIw3Gm5jSTczD8j3ppAXC43Z4xTgJB8gORQA/dIrYV+DyPpTQ4jO6Q9e9N4LhG79KGBLLkds0ASCVyv3xx2x1prAtEAOMnp9KkVVmXc30qNnKZY9GIxQAgILYcnPfH/6qlBO75TkCm5+Yn3/oaaq/uyynhguTQA/cDvz8o4pwaTYRu+nuKY425Q/MT0WlQqy/vONtXGVikhgBa7hIJ4zn61+7n/BCCy+1eJdbj9Z4x+jV+FFrzdoR0zX9Af8AwQAtlufGOvJtyfPjx/49X5H47T/4xuq/63R+oeD7tnKP1I/bt8MLB4r8FyFTn7Tj82Sv63f2gfCvxg8Yfs2T+Gf2ftR/sXxle6FZR6feFlTYe+CwIHGecV/Nr+3V4QuGbw/4zlt2ax0W4jmu2QZKxAjcQvc8dq/USf8A4Li/sMaRpVjbTyX9w0NtHCzi0cN+7XGBlhkV/F/h3nFFYGpQrNX5r2fU/dvEbKMXisTSnhYOVk/xt/kfIL/sd/8ABdiBSX+McS9/mlgb/wBoVh3P7KH/AAXGiBaf4zQDHq0I/lDX1dff8F8P2DLYZuBqoXv/AKIen/fdec6z/wAHBH/BOhd8k39rDaOos2/+Kr6DH0J1daFCD/7dR8nhcrzCDtWps+Zb79mv/gtlatmb4y25H+/Gf/aNcpqfwb/4LQ6ShkHxft2PU4aMf+0a+0fgT/wWF/Yp/a8+Mtl8BfhI2pnW9SYrC727RxcKXO5i3HANfXXi20uIrie1YEmNyuQT296/GuL+IM1yuso1sPCN9vcR+l8PZbQrrlm3c/DbUtC/4LJ6WSbj4uW5wOm6Ln/yDXAXHjH/AILB6S5aX4n20uD3MX/xmvvL9rv9oT4f/su/Dv8A4WT8RYJrmOacW1tbQkCWZ26hCx/hHJOK8wGu6d8RfAml/ELwhIslhrVtHdQ4OdokGWjJ/vpnDfQ14f8Arnm8sNHFzo0/ZN2vyLc+0wnDOEbtG7Z+avjPwb+1n8a/jVoPxX/ai8VWeryeGraS2to4I0Q7GJY8oqg89zmv3P8AhneXDfDfw+yjg6baEf8Afla/OHxHZyl25O3B/lX6MfDIMvw38PKM8abaf+iUr+m/CTN6mLo1ZVLacq0Vv5j868R8DDDujCH979D/1Oz+L37SXw4/Zja3vviHb308d6GMbWsHmoOed5yAPbmvmP8AaE/4KEfDz43fAbVvgn8FNO1SPWPEssNrLcXVu0UMVtuy5L5OC2APfFfqd4TvFsXkgvbS3v7W5zFNBcRrIjKx/wBoEg+4r4tnvPgZ4D/ayl+G/wAMoXuLJ4hdeIbS/Zfs2m878xyc46gYPfiv8iMJi8BGo26DnVguZO/u76dP1P8ATqhGbla9kfL3wX+KN7/wTz/aN0b4q+PrWT/hFtf0SLTtVi05PNLXEEQUSrGu3O5xuB7gmv1f+Fn/AAWH/ZY8YeLdP8EeGNP12d7+QKsgsJABubALpv8A4e/tXkX7ZPxm+EOoeEbXXvhbcw38SMkWs31hCkktjathS6Rt3xwCMAetfoP+x34B+Cvwr+F2n+MfgqiarD4jh+1S67eqrX1wSSCDx8oUjG0HA/Kssbm2FzDD/W8xotVNrp6aXtfQ8bNaE46U+p+Y/wDwWTuWi/bT+C9yhZfMtSwZWKtzISP59O1cjHfLoVk2qanfyW9pAoYs0hxj/wDXWv8A8Flrlp/2zvg0zHLfZN5Yj1m55ryT412kV38Ir+0kHyzIqt9DmvbxOH9rDBUIdY/qysggqeDdWS1TaNq1/aL+F5uzDHrbOcggrITxXreg/tMfCiGZTc6nK6gdDIf8K/jy8R6ba2njDV7GOedPIvCi7JXX5QTx+VZotpGX/j/vR7ee3+Nf0ngfoz0sTRhVjW3V/hPwvHfSBhRlOmqTvF2P7gdD/au+AtjPFLe3gG1hksd2PyIr+f7/AIK/+NPDPjvxFaa34XnE9tNeRlNpB7ivyEiinWMg6hfbj389sY/Oo3jncbJ7u4ulHQTOZAD2IzX3HBv0f/7Jx0MTGrez7HwXE/jFLM8NKh7Nq5dkdHdtp6scVGSzLsOMD86T7qozdc0xZMA7upNf0ootN3Pw+W5PtOVlXkEYIqPgqV3ZIbmmh024OQKDLG/Bw2OMeoqiSVsMwMmA3PToRUUiQ7QxUjPQjvQstuo2pkY5Of6U1XRWKsW2n7pxkYoAU26HAOSQeOaZJHCy5wRu68+lSCaJV2gksGB59KVnixmNgQO/agBqxIyeYN2O/v708W6q25c/TNJ5qqdnO08dc00yIwwpIYHv3oAFiCnbhiPrTHSENgKx9qn2heoLfQ4FIfMLhgSFxj1AoAxZEjDnbuHr71C5EWW6BeF+hrQljK7jJzzjBqlIGUEYHXpQA2IIwO7kjjjrVeRAcAEjbxz2NMmDsdxGMce2Kecueu5wMZPSgDKubaQuHj4JXnHTI/xzXM3UojbMjbNx44JK/lXW3DBJGDdAB0OeRmuYuXDyMN23ec8fligDHmKkASliM8FT1+tU2LNLuYhTt2rz0x3/ABFabxMpKkKynuMg1VCTD5FCKynB9W96AK42KrLFgMAcd93Ge1KNqnJyqg5JC/3qn23CnozE8DGO/FTokjnaA24kADqcigC1bwSFTJJkFOenY+uK1WRgyqcevHNXBBJsLSZWQgD6Y9aHh2vhQAzc7h29fzoAckgUZGMf4V13wyk2/tB/D6SMkOurwEfXzVIri5I2ZenA/l3rY+HM4tPjX4L8Q6g4hsNP1KCW5mPSONZFLMfYDmgD/a2+HOD4C0Ytkk2Vuc+uYxXa4H93/P5V+Pvg3/gtn/wS90Twjpej3nxb0gTW9rCjKPMONqAYPye1dIf+C5H/AAS2HX4t6T/3zL/8RQNM/V/ap6jH4f8A1qQhRxivmX9mH9tL9mj9sfRdQ8Qfs4eKLbxRZ6XKsN1LbK4WN3XcoO9V6j0r6kAVwGHegdyAQqRnaPyFL5C91H5CvHfj7+0R8H/2X/hvefFv446zHoXh7Tyi3F5KGKJvYKMhQT1NfAdr/wAFzP8AglfeWyXdv8XdJMcg3KSJRkfQoDQFz9WbmJVhYqAD0HAPJ6V/kl/8F9NQdf8Agr78Q55udt5ADx1+Ra/0X5P+C3//AAS5ljKR/FzSAccZ8wDPb+Cv803/AILWfFLwF8bP+ClXjT4tfCTU4tc8M6rfW/2W/gz5ch2KGALAdCOaBJvc/wBPL/gklPcal/wTn+E93ct5jHQ4BuYDkLke1fo15JHYflX5x/8ABIJNn/BN34TDOc6JEfzJr9JqCudlXyT6D8qUQ+o/QV8MftWf8FLf2NP2JvEOn+F/2l/F8Xhq71SPzbcSxSOGXJHWNW9K+UR/wcF/8ElC5Rfi1ZEjP/LCcdPqgoFzs/ZRoFI6Z/AV5R8SvgL8H/jDpE+h/E/w1puuW1xG0TreW0UuVcYIyy5HHcEGvl39nf8A4Kl/sGftU68PC3wR+I2matqbfctSxhlf/cWQLu+g5r7/APMUjigTZ/B9/wAFnf8Ag2v0n4f+GtT/AGo/+CftvLa/YFe51Tw6PnRovvM9vkE8c5X06V/GHpt9HcSGNozC8MhiuIGBDROOCCDyMHj271/t3XdpFeRPbzqHjkUqyt0YMMEEdwRX+Vn/AMHBv7GeifsVf8FKL678BW32Twz8QFN/FCq4RJZiTMABwF8wnpzjHGeKBH6K/wDBnVdTv+1t8UUBAR9FIIUDkrcx+tf6Igj9Rn8BX+dj/wAGdh8r9sD4nwn/AKA7n/yZjr/RUoA+Of8AgoG3kfsR/FWeP5WTwxqRGAOvkNX+L/4bH7zU7kdTdMT+XNf7P/8AwUJ/5Me+K3/Ysaj/AOiGr/F/8Mn/AJCfp9pb+VAHYu26d3Pdj/Ou2+GdxcR/Hr4avCfmHiKywf8Atsh/pXFSjbKw9z/Ouz+E/wA3x1+HLP8Aw+IrP/0aKAP9q7wGTJ4P0wyAEm1hOcDn5BnsK6m4iUwMGGRg9hXK/D7LeDtLcdBbRD8kFdjN/qm+lAH+Sn/wXovZLv8A4LF/FUyHiOWGNR6YtovSk/4IDXUlv/wWn+F0kTHlLlcdsG2krH/4L1MV/wCCyXxXXOB9pjP520VTf8EBGC/8Fovhb3K/aB/5LSUAf620CI8KttHT0FStChUjAH4Ci1yYQT6VOeRigD+UT/g5v/4JZL+1L+z4n7WfwhsAPHPw+iaW48pf3l3YLhmBC/eaPqPav87ix11db09b91McqjbMp6hwTn8PSv8Abq1nStP1vS7nRdXiWe1u42hmjcZVkcYYEehBr/KY/wCC+/8AwTfu/wDgmz+2fdeJfBts6/Dnx+7XtgyKfLt55CfMtx2BVsn6flQB+QyTLIyIDnPp1AwST+Qr9q/+CBP/AATdv/8Agop+2TbfEPxnZOPh58PZEuLnzAQlzMpBSIZGCGYnd7Yr8Q/BfgXx38X/AIgeH/gv8MYGvda8UXCWtvHGCzbZGA3DHPA6+1f67H/BKb9gzwh/wT4/Y+8NfBHQIEXUvJW61a4A5mu5RuYk9cLnAHoBQB+iuk6dY6Xp0Om6dAltBAipHFEoVEVRgADHAA4Fa+xf4hx+FEUYAweoqR/u0Afxof8AB4+7j9knwLbxjCtq0xPAGT5QAr+ALXCf+ELiHby4j/T+tf6AX/B4wu/9lHwGP+orN/6LWv4A9cVf+EMi/wCuUP8AMUAf6wP/AAQBle4/4JZfDYyv5jLbyqMgDAEhwOlfs3tUcMoz9B/hX4v/APBvzg/8EtPhxj/njN/6Nav2oJVRkigCExKOAi/lTxEmOUH5V+f/AO3B/wAFMP2V/wDgn1ZaReftJazNpS607La+TA027Zjdnb0xmvgaL/g5c/4JPvdpbt47nVXx8/2KcqM+vGf0oA/fK5tILiIxTRqynqCAQR6YIr4A/a+/4Jj/ALGf7a3gm78G/G7wXYXJuFbbe28McN3G5HDJKgVgR75zXqP7MH7dX7Kv7ZWgSa9+zr4xsfEiwf62GBts8f8AvRNhx164xX1azrIvyHt/OgD/ACgv+Cx//BEf4tf8ErPFLfEPwo83iX4V6rM6W96BmWzZuUjmA6HHfoa/C6P97Es8bB45BuUjpiv9q39sb9mrwN+1r+zf4q+AnxBtUu7DXrKWEBhkpLtOyRc9GU4IIr/GO+MPwt1j9nn42+NPgD4lyLvwnqs9rgjBxE+DwccYxQBxA+YfLSBecnrWN9uViQx5oS+J4HOKANnGFCkc0D6YqBLmOT1zU4IIyKABj0x+Jpd+VPHIOKT/AGfU0kgKLz+lADflOcDnvT/3agAnmkEeWIHXuOlJmQcMBQA12DDbk/hUq7QMHI46GmfxBmIIHpTgW7k49qAG5yRv4xRhicMMntUmPMXYAXI9aaCSm49aAGOEGAR9c8/lQI1PQ4H6/hTyMrz1NLz0P6UAMKqvHUdj/jSeUin5ic+tSKzFd2SB+tG5toHr60AMAjBL7fkbgeoPrTTyAM9eR9PSpQxXDbtoU84qOTzSBsXGCevoaDRwRCGEeVBxn1phyQpLAEdMg4/lVsRuRllz9CKZ5cpx8mfQDGaDMYV5+bgHH0/CmqpUYIUrnjJNOk+UAEEEHoaaHViODyP1oAXPzk9COtOiUOrk9qMkNu46c01NgzkHJB+lAE1mGN6sa/Xiv37/AOCAWo6bovjXX7nV51t40uY8ljgdGr+fthuJEYCtxz7d677wV8RviN8Obaay8C69c6fDdENMsR2liD6gg/SvjOO+Gaub5dPA03ufXcEZ/DLsaq8z/SM8TeNvhtfQfZ9RvLa4iIw8cm11YehBrwnXNP8AgFIheKx0gg8n/Rof0+Sv4EJv2ifj20nl/wDCXXv4yuf6mmx/tA/tBE7f+EtvCP8Arq1fym/ou4tS541Umf0Lh/GvCQekWf3BeILT4EFNkem6DISOn2ODv/wGvnLxd4O+H1yJX03w3orqehWyh/XA4r+P++/aD/aBitnuJfFd4yJtBHmNzX9Lf7Bd7qmufs+WF9rUrXFxKnnPJIxZmZh3J7V8P4geEOL4dw0MVOvfmelmz9F4P8RMPm9aVGlrY9O/YH8MaDY/8FavDCaZptnZFNNkP+ixCIFvLZQxC9+a/Yv4/f8ABV39iv4R/FrWPhb41n1v+0tKuZI7nyrDeu4HB2sW3EcdRX5B/sRnP/BXHwmXHWydQD0JKkc1/Rr+2L+zF8FPjroWrXHxDtLXSrnTXkmTXIYkS4tljBYuSB8+AOQxr4viinhMT9WePTl7q2fe/e/YzmnTzKpS5tP+GP5yP2mv2lvBv/BQH9pDw6vwUsri78JeEdPaYR38BgWa9beOVbPGSg59Celcp+zP+2p8L/2bPhXqX7MP7QMd7H4j8P6pctA9nC1zHLDIwPyshPGc4I45r7X/AGLPHXwI09Nc1TxdqFonh3TbyTT7TXLtRAb6RDwTGoYjAPXPPtXE/EEfAvxh+0tb/DLxnqbeFfDt6/m6d9hhH/E3lkbhFnUHarY6dj9a8KvmuFlfKXh26PZPWLWvZ/PQ/QsHhVyc0ZanD/Dz9pL4X/tBaxd6R8PLfUjLbRmV2urV4kA/3mPHtnr2r9fPhxazr8PNBUr0061H/kFa+OfFJ0i00ePwf4N0u20LRLHcIbW3QeYzcgvLJgM7nqc5x2r7g+HK7Ph7oKemnWo/8hLX7X4PYjDzjiJ4VWj7vW/83kj8m8T4tSo3d/i/Q//V+3tDnhiEjyE5QMQMfxYOz9eK+PfgB+wLrdx4y8R/Gv8Aa4vWiHiO9F4dJtpP9IulU/uo5ipwIyAPl/WvrvTGS3kDDqDuB9D6j3rv9FllmkZ1fO1Sxdj0VeTnPQKOa/xKzLPsXg6lSjhv+Xis389vmf6fYOkpUlJnCfGz9kz4U/tI+GrnS/DyDwZri2f2SxNmNlnNFwVjnRcbuB3PB5r0/wDYU+GXxV+A37PH/CjvjakaXmj3sr6XIjiQSWspVjgg8ANn8/bmr8NviL8Ofirok2r/AA31KLVbK3mMMzxfNtljPKsO3qDjtX0To9w0qo9zMZnUAJuJJVeOBntxXif23j40v7Prp6O7T3TOathoyknE/Gz/AILKN5f7ZvwZiB5NkP8A0ca4j4tqG+FNyxPZR+WTWv8A8Fiblz+2x8G9xz/oQ/8ARxrnvisxPwkuG9SP61/Q9CKUsC1/K/wZ5WEThgqkfOX5H8sfjKRz8QfEKqSu2+Pf1zWOzsku8H8K2PGf/I/eIf8Ar+rFm61/p7w+v9hpO/Rfkf55Z1dYqq/P9S2Jiw5NR5+cbWwPTrVQPgYFJ5h6EV2uTta55nmah4DHrnpUByMA85pqO5GO1SlVY7FOGHc+lJOyshtkcjOrgLyDxUi/MRgfXHBoClXDMw4qtKzZYZG00CLSsDgHOc8A81X81UDeYSGz26VEoVWJUgEDr6/SmLJhdhGaALQlRPnj+YtxzSBiScEAr044qt5iZyRyOwpgnj6jjr+tAGhhlXDc7TyafjDYckk/dqkn3c7uQPzp2W2Aj5tv50AaKybRtU5PQ545pXKbcMcsR90dj9az1ZfJBI3Lnr3zUnmRgeZg7j1xQBZMayLubqo5rLmhxgg5z0PtVxZN64Bx9abLuJUswAHFAGWYkPzMCKb5cQUd9oJ6VelVyzYOQDjFV5Iyfl/u9/WgDElDAM0YAYLuxjtWNe2zMomyFBGenU1088GIyM9Rjj0FZssYMgdxkcH2oA56SJUCqTlsc1mkQ+aRJhxuzwDn862rqJvNPlj7x4pY4ZAcsQecdPagCs9qUGwDG4ZGTzWlb2qAiQdG9eMH60+OBWQRuSoU5yea0o7RhGUkGAeR/jQAzewUrJ8oHcjP+FKIt6Eg89sCrflBdrSndgcCpjFIu3IwaAM6SFhGcVXMeITGOAwww/meK3mhHl7d2Me1Vhb/ADZJ60AZceiWMqZZpMsBkb2xkZ6c+hpW0HTUtZpfnJCHHzn+v+Fapyg4HSo5H/0G4J/55t/KgD+7f/gzgtvs/wCzZ8UGjkdgdYtNocg4/dP6AZ61/Z0owoFfxj/8Gbrbv2ZPiYf+oxa/+i3r+zkdBQB/P1/wc0qR/wAEhfifcK7K0UVoylTjn7VH/Sv8t/wxplqfDGltmQGS33sd/Vixr/Uh/wCDmo/8af8A4qD/AKd7M/8Ak3FX+XV4YH/FK6SFA/49FPT/AGjQBotpdqBkPJx1G8jI79MVgeLP3Gi2cMRPl/b4yFPODnn8xiukeQgFSa5LxjMBplmv/T9F/MUAf7B//BIhQn/BOD4TIvbQoP1Gf61+kVfm/wD8Eiv+Ucfwn/7AcA/IYr9HmJAyKAP87T/g8pXd+0D8LPMJEclo6OQSMjzAT0I5wcV/HodE0ySZvNVwN52gPngDAzn1r+/j/g55/wCCZn7Z37cvxh+Huufs0eF5NetNKtpUldSqIkrMDhyzDAwK/mf/AOIfD/gsijNJ/wAK6jLkHH+k2/8A8XQB+S3hvxT4w+EOr2fxK+GuqXmnatpNxHPE8Um0qykYIIwf1r/YY/4JY/tD+Mf2pP2CPhr8bviDhta1rR4XvJFG0Syp8jSAf7WM1/BB+yB/waw/8FC/jB8UNJb9qq2t/B/hKGVJrxzcRSyMiEEoqRsSWYevAr/SL+CHwh8GfAP4TaD8Gvh3bC00Tw5ZxWNnEAABHEoXPHqeT7mgD1nzOen+fyr+B3/g8hsrS1+J/wAG9TjUee0Fyu49SPOQ9sepr+9tnAyrHAAHb1zx+lf5o/8AwdCftO6F+0R/wUU0f4JeGbpLqy+Hdv8AZ7iRWyBNJ+9kU44+Q4X8KAPdf+DPUO/7ZfxOIGB/Y7/+lCH+lf6KoYHpX+dR/wAGdjt/w2H8T/8AsDOR/wCBMY/rX+ijDyCaAPj/AP4KFcfsPfFb38Mal+kDmv8AGA8MgbdUP/Ty9f7P3/BQv/kx74q/9ixqX/ohq/xgvDBAj1QH/n6b+VAHaysEZieuTXUfCuUf8L3+HYHGPENkf/IorjZmzM2OmTXSfCxx/wAL7+HY9fEFl/6OFAH+2B8O2/4orSx620R/NAa7Kb/VN9DXHfD1QPBumAdrWH/0WtdjL/q2+lAH+RV/wXvuM/8ABZ74qw9P38X/AKTxj+laP/BARw//AAWh+GDDt9o/9J5K57/gvqwX/gtJ8U8/894v/RCVs/8ABv2wb/gs78MsdjOP/IDj+tAH+uTbcQL9BUpZQM1BbsBbq3sK4j4keJNQ8KeAta8SaLCLq6sLKe4hjPR3jjZlU/UjFAHal97Yxwa/Kr/gsN/wTu8J/wDBR39jPxH8Hb+GNfENvC97od2UzJDewqWQKRz8+NpHvmuu/wCCaH/BRTwL/wAFDPhJqXjPw/GlhrXh+/l03VbAHJhliOAwzztbtxxiv0qVFcgsOlAH8Nn/AAbAf8Ec/E/wk8a+I/2tv2o9Gkh1/Rp5NK0G3u0IMZibbNOFcfgpx71/ciNgUKvGKPs6RLiIY+ledfFH4keFfg98PdZ+J3jq6Wy0fQbOW8u5nIAWKFdzHPqQMCgD0qMinv8Adr8yv+CaH7f8H/BQ74Y678YtA0sadodtqclnp75LGaGMf6wn1zjIFfpkXGOaAP42v+DxUgfso+BSe2qTH8o0Nf5+Gu3DL4Nj7/u4R/n8q/0Bf+Dx6TZ+yh4DA76tKPzjWv8APx1xWPg2D0McP8qAP9Yz/g3umM3/AASu+HMhGMRzj8pWFftjIMrX4lf8G9S7f+CVfw7/ANy4/wDRzV+279KAP4VP+D0KO3T4Z/C24Pyyf2ldAEcZXy0yD+IzX8HUmm6SkskEcKkEKFIJ3DK84JyPxxX+gf8A8HgPwI+MXxo+HPwxj+Fnh6/15rTUbppUsYJJyFaNQMiNWIyRX8QUf7Gv7b+oXix2Xwn8QFpVVCTpl0BwMf3OOKAPWv8Agl1+1J8Tv2RP24/APjX4d6tcx2dzqcMF7aq7FZoJHCSI68ZyDx16V/sx6LfJquk22qoCBdRJKAeoDAHmv83v/gh5/wAG8/7TvxF/aF8P/tQftZ6TN4X8J+GriO8trS9TZPdyRkFEER+ZUz95jX+khaxLBCsUY2KqqFUdAAMAfpQBNIgaI7s4wcj9a/yDf+C9/hzTPDn/AAV8+Kkelosa3d880ijjmSFCT+ZzX+u3r+tWHh7RbvW9WlWC0tIpJZnfgKqLuJz6YBzX+MJ/wVD+Oum/tLf8FHfi18ZNEn87TbzWrpbN0O7MMbeUuPYhcigD4Tbl/M/SpYm2nrios45pwKfeoA1rYqxxW0hVAFznNYUTDaCoxir/AJh4xQBp5G4H0prSfNuPT61RE7elP8xsZxQBaDtIBkBiOAT1xTiRny8AHrxVRZCVwoIP0q0rJ95s56cDNAC4VRgDr1oMnI29B1oKncCwOO1AGW3DtwaAFfB4PX2NJvDAbOccmmE4f92M1IqhRgd6AHYAznnnFNYAjC8GjcVcLIpIbnjtS4PcN+VAADzjOCelJ868NyT/ADp2Pl5B/KgH5SRnOcgHrQBGVUZ74OKRYw3QdPU05UwmGPXnNAf5cNxu/SgrnYZ7bRgd8Up2MMKOvYHFDZjbpximg4bzWHXt6UEkUu5WBUkAcAZ/+tQWCEM3POKnVP4drMPansgPXjvg0AVSVxuxz6f5FKTwOOtTbV37+o6cc1G4ZSBnp/KqS0uBDsdjuH1NTxiPbyMGmMSc44zTee5pwqStaIPsSH5W3jP0pSwcbgME00nK/SkYlVBHpQpCUbbFTWcro8ynruX+df1n/wDBP6KM/s8WK4xstYv1XNfyWa07PpkhP99P5iv64P8AgnxD5nwCtAva1h/9Ar+afpKW+oUU9uZ/gf0N9H58uMqTW9juf2NozB/wVq8FMD9+MD/x1j/Sv6J/+CiFj8UPFH7PXiz4c/BfTn1LxD4pvTpkaJj93DJ80rkkjaAq43Z4zX8737JSmH/grF4Gk/2Bn8mFf1deLNWkt9Y1KK3O0zTuCTz/AD4/wr+JeLM1lh6GErU9+Vfmz92zHCSqZrNx7f5H4v8A7K3/AATu0H4H+GtIvPj/ACQ67rNnG62+kqN1lb+aSztIpBEk3zfePQ9OBXyn+1d/wT18Xajqlh8QP2Tr2W/u9C1VdVXS7yQfaLSRTkiAnaDETztxxgHNftf448X+G/Cdhc+IvGWowabaI2Hu7yURx5Y9C7HHJ7da+e/El8ks41rQbgxiSMTQXNsfvxOu5SGHVWXofSvy3D8X5jhsX/aKvytteWp+h5XD3OVbny94hl/tGWC+njMN5NbRveIR9y5KDzV9vnzX254CmEfgbRY9udthbDOfSJa+NNejLSPK/JIYk+pPWvsDwO5/4QrR/wDryt//AEWtf1d4IVW6FeT68r+/mPyjxLpp1aSl5/of/9b65n8VeCvDk2PG2sWejrJ/q2u5kiDEf3dx5968U/al/aQ+HngL9mbxLceBvFGnXviLVY/7LsobOdJZj5xw7KqkkfuzwfU16D8RP2fvgp+0GqaF8YrNnFuT9lu4yVkt3bowxgOCeoIIr4dH7DHgb4dfHzRvAPxGFhfNqpWXQ73TAscy7W+/cKhBXCjqRX+PdLLsqVZYzESk5xd+VK6dtj/TvLVek0cv/wAE4vE+j/sxftJSfDDxZenSfD3jLRoLpH1CRUSO8WIPICXwMltwH0Ffux4c+KPwlvdZXSdI8X6NeXDsVSFLuLexz0HzYr85P25v2UPgjoOl+H76+sF1K+vZltLKN5CY2nkACmV8japPU5Fdt+z3/wAExfhV8MWtviL8c7e11rxK+HtdLsm8uytgv3S7owLle2Tt9M9ajiHF5bml8xrOUKjTTVlZtbEexdOaSPm3/gr/ACNcftrfB5j1FoFP/f0/561j/FHd/wAKbus9cir3/BWBfO/bR+ENuRjbaLtA7Lv4H0AFR/FyDZ8ILsejD+tfb4OSccDyv7HX/EefL/c63zP5X/Gn/I+eID/0+1hyEk4NbvjPA8f+IR/0+1zrf605r/UbIrfVKa8v0P8AOrPF/tda3f8AUDtXmnJIOoH+fypjFcc0zK7Tiuo8wupMc46e1OkcdSMGqySBVxTvlb5s0ATuU8ocVVMgI2jkUO+MKKrzSYHB2j9aAJCExwpyOlRDv6+v8NV/PwDhic9sdaQSxqBglT3A6UAWgcHIpMAnNVvPA7k/WlQknIYc0ATGVQDg1LDLjj9B3qqHH901bjcEYYkD1H/6qANHfGOqkEjkelQyREHjOD60Ky5yuSR+BpHBEm3nj1OaAG7dqE9gakkWNv8AVfUj6daMgjNM8wtmPPI/h7Y9aAHPIcDZ3qC4dQAq/dHT3qbdhQANxPc9qpyKx+9QAwEAHd3qo8RBLP8AdxVnbhTUcyuUwtAGO0AZvvYPUfSryQDzFIcBcZI96WCJt3zD9KvJFnhsn6UARtBGVDZx7VLHHgYb7vrU7RZJx0xVhIuAzcccZ9PWgCNIVJBYBT0/CriwqV24JHY0kcWT8mOOc1oRM0fXnNAFN7ciLy2X6GqnkE9VFb7ldtQD7xPagDAli4wKy7tdtnOPWNq3rofMce9Yt7/x5T/9czQB/dx/wZvAL+zL8TQP+gxa/wDotq/s5HQV/GT/AMGcJB/Zm+JuP+gxaf8Aot6/s2HQUAfz8/8ABzYcf8EgPip/1ws//SuKv8u7w5keFNLK9RbAfqa/1Ev+Dmkj/h0D8VD/ANO9n/6VxV/l3eGufCelf9e4/maB2ZccMozJXHeLlZtKsiT/AMvsf867qRAXFcl4vVU0yyf0vI/5mgR/sI/8EjV2/wDBOX4Tj/qBw/1r9HsA9a/OP/gkec/8E5/hQf8AqCQ/1r9HKAKhjQnJGf8A61LsX0FfhL/wVg/4Lh/Cn/glZ428O+DPH/hu711vEETTCS2YAR4bBHIOSP0qh/wS2/4L4fsy/wDBTn4gan8KfC1nN4Y8R2UZmgtL6RSbpFGX8ojA3KOcDJxmgD953VdvSq0kiQ/OxCjvkcYHvkAVME8zgc4rwb9pz4Paj8dPgX4m+FGk6xeaBd61ZSQQX1jK0U0MpHysGUg4zgMM8igD8Tf+Cz3/AAXI+Dv7C/w21L4VfCLUYde+J+qRvbwQWzeZHYsy4MkxBxuAPC596/zaNY1fxB4w8X6n8S/GV095r+uTyXV5PIdzM8zFiMnJzzXr37UHwQ+Kv7MP7T3jD4AftGrM3inTbp3hu7pmcXcLNlJEZvvb1wVIJzXikoP54FAH9RP/AAZ6mOL9sT4lwnhjor4/8CUr/ROg6Gv8w/8A4Ni/jVZfCD/gqG3gydxHB4usJrEZIG5mxKOvqVAr/TwhdCGC9MmgD5F/b7srjUv2K/inZWwLSP4Z1IKo6k+Q3Ff4wWjWU9nPrVtMCDHdMMehxz+tf7ivi3w/pnizw9feGdYiE1pqMEttKp6FJVKsPxBxX+Sz/wAFgP8AgmR8cv8AgnF+1N4jv9U0S61D4eeJ7mS50rU7WJmiCOxIjYgYDID8yMfegD8sHOXY+5rpfhFDPqH7R3w50uxBaY69ZMFAzn98oxXmMni/RQDsiunY8hfJPc8YFf0Wf8G+f/BJ/wCMX7YX7WegftO/EXRLjSfhz4MnS6Wa6jMRvJ4m3RLEGA3Yblj2xQB/p0eAFKeDtLBBB+yw5B6ghACD9CK66biM84qpZwxWqLDH8qoAAO2AMD9BVDxLqcWl6Fdag7qBDGznJGMAE8+gHWgD/Ip/4L6zxXf/AAWd+KxgYEx3UStj2gSum/4N+VUf8FnfhgAOv2j/ANJ5K+Qf+CjHxXtP2gP+CjXxf+MVk/mW+oa1MsLA5G2PEIwRwRhK+v8A/g36YN/wWe+GD4xn7T/6TyUFR6n+uHboTbp7gVxfxGjK+BNVDc5tZv8A0Bq7eDP2dfoK474i/P4G1Qnj/RZv/QDQSf5T/wDwSk/4Ka+Jf+Cc3/BTXxFrOs3LN4G8Ua/c6drdsSSio9y4WVewZSQc46Cv9Wvwf4q0Txp4Y0/xb4bukvbDUreO4t54jlJEcAhgRxg1/iFfFW0/tD4qePrYcMdbu2U9wwnkxj0Nf3g/8Gq//BWC6+KPgmT/AIJ/fHDUA2veHFZtAmmYb57ZTua3yxySnUY7ZoA/takkwpYenbrX8L3/AAdbf8Fb18NeGZ/+Ce3wIv8AfqN/GJfE9xbknyoCuVtyQccghmPocV/S9/wVl/4KJeAv+Cb37JOt/GLX7qI65cxva6JaMfnmu3GAQOu2POSfpX+Q/wDGT4m+N/jj4p8WfHD4k3j3uueJp5Z5ZJCcjzX3Hr29B2HFAH+mh/waw/J/wS18PREDi9uWJHfLgZ/EV/SmFUnGK/my/wCDWlR/w6+0IJyBdzgfmK/pNOaAP4x/+Dyglf2T/ABXjOqzf+i1r+ADWQW8G2//AFzi/kK/v+/4PKhn9k3wBn/oKTf+i1r/AD89cmKeDrcdhHF/KgD/AFmf+De4Y/4JX/Dkf9M7j/0c1ftg33fxr8SP+DelzL/wSr+Hbdf3dx/6Oav23b7v40AZs0FpcsBcRo+DxuGcfnQNPsFcbYYxj0Uf4V+dX7f/APwU6/Zt/wCCcGkaNrn7Qk9xDDrryJbm2QSH93jOfmGMZ9K/NZf+Dpf/AIJbIu6TXb0ZAODApP6NQB/SK0MSqAqgAccelMO1BuPTqa/lC+Kv/B3r/wAE6/BUEqeC9O1rX5wMIscSRIx9yzZx+dfz6ft0/wDB2F+1h+0foGoeA/2Y9OT4f6Tchonu4yHvWiYYwshBCHHdRn3oA/eD/g5E/wCC2vw4/Zt+Cesfsf8AwH1Yaj8QfEsRtb6W1dSthbNxIGYHiRgcbR0HNf5qdmZYRJdXLl552LyMerZ9fzrqvEWteIfGmu3HinxlezanqV45lmuJ3aR3djklmbn86xTb4JyaAEUlxkGk3FRmnCJ0OAcg0MnGKALcF3sHzHir41C02daxGAVNvU1RMcgJPUUAdUNUswnLc0n9p22NwckemK5fylIBwRTxGVOxRkHmgDqor1Nm+NWOKuwXI+8QRn1rkkVQMcD6HmryyjhQufc0AdSkwb7tTtu+4hw2Oc9651JTtDcDPTB9KmE7KuXY4PXHegDZYOpBQlT7inHzYxyhzWG1y5AHnHPpTXnc/MSWXpy33fw9KANfzI14dWUmpRLbt8wLZXg571jeZtX5Www/Oq5u5ApCudxNAHQhk37xllPXHUe9PGQQ+CW7Y7ism2uW2jzst2q+soQ/MykfTNAErYZSi9M0/gyMWpmVK57HlQvGDT3HOO4GR9DQBGfmcBm3Y6Yp7Fu3ej5dvGQaad27Kj/69ADgpbhScilpiopJIO36U4xjZg4+goAZ1bb2pH+9n2pwLfwik2mUcnr0oAiLbcY70Nu2kk075+VXjFKVJQhjRcBuMfPQTu5NIGKDApc55prcChrQB0iYrxhlr+wP/gnRpwk/Z5tpl5P2KA/jtr+PzWv+QNcY/up/6FX9k3/BMqE3H7OFmGPBsYf/AEGv5j+k67ZdRf8Aekf0V4ARvjKiLn7PNsNM/wCCqnw/uFGN4K4AyTy4H5V/TT458UeHE1q/s31KzExkcFPtUIdSD/EpfI/Gv5uPhxbf2d/wU/8AhxdD7pmRc9vmMmD9K+2P2z/+CZnh34ueLtV+Lfwf1u4i8WXF200+lXshW0usMSUVhgrnrnOBgV/EOawwmKp0IYmfKuX9Wf0bjKDhjnJdj5f/AOCtPjzQviz8QvB37LGjXovdItIG1vWTYTK53bWIiLKSuVVAcdctXov7CPxi0/x7+yjpuleJtStYdZ8Ly3GlzWss6RzrBCwWAMH+Y7UOOPSvN/2L/wBjz4a+IPFviBpowniOyZrfUbXzzLBbOCcJFMCQwOM4zmvHviZ+wbbeLfj5qvw++FhW88QLMbrVr24k8m3s7eXo6ruzKfoCR6CrxVXLcVg/7IbagtU7dev6H0eBwUofvEz9BNQlstUkkh026hnwCzeVIsmOO+08V9feCkVfBukrnpZQD/yGtfnf8Pv2Xfgr+zXCYvA8tzrfiCSF47rU7hyIslfmWCPoBng55NfpB4Hmb/hCtH3YB+xW+eR/zzWv2rwajSVOuqErx939T8s8RHL2tNy8/wBD/9f7i0u5iGoFioYLuY/8BGa/LD4E/DD9oD9o79pjx58ZPCyNpNlf3Ys47+5JEFlZphZHj3AKWKjGFOc1+oNoAtx0yQwPPI9CCPQjrXbXutXuraRH4euzb2+k2ozBYadGIoTk8mUDBY55Oa/xQx/GP9nTq0oRu5q1+2p/ptgaM5wTi9j43/aa/ZR8Xat8LtTT4C67ceMNHS1ZLy1uHZ7qO5jwfPhDYwGYfw/hXtn/AAT88ceKPGX7LGl+HPGq3Fvrfhi6lsZ/PyrvGx3xk7/mPUjPtXuMOsSeD7C88fyXJ0uPSLf7RcTxKfkgjUsQyL99QBnGPevkG+/4K2/sMavrf2+XxAiXK4SWS3tJEEhU5BYAc9T2rXJaWOzLLZYbD4dzUWndK9rnVVqqnVjeVvI8M/4KeW41P9uX4SFiSsdgP/Qjiun+N2lRW/wYvG2/Nlf614/8b/j58Kf2yf2v/Anij4JzyajYaHZeXdzNE8YR1PI+YDNfUn7RWk/Z/gjdyAY+4efqa/TcH7WOIwuHqq0oxV1/282eXOMY4Oq2fxt+OJT/AMLC8RKB/wAvuP51hL8wyau+NZZB8R/EbdjfsR+BNZSSHbmv9ROHZp4Oi12X5H+dGcq2Lrer/Mcw+ak2moS5zmjzG/z/APqr2Typbk4wOvNG89qgLMRmkWVcc0AWHlPHFVZTuUt3qGeXcRt4qPzMnb60AIpbODQ/UUH5SWppIYA9KABzk5FTw8jPtVY4C8c1YgztAoAnqWNwRx1FRZxzTEdVbcTk+lAGrDjaZerelNEhUgD5vU1Aku6PA7UR7vMyOwzQBZY4jH15qL7r+YfXB+nalMmVG/8AGofNJTZQBMGZWKDnPemNx3pDtKhl61CWIbmgCSkJA603zF/z/wDqppdc8jigB4jXcWLYq0IwuCxLcHpVJJCxKhckDNXQ0u3PFAD0BTBY5zVqJCke1+oHH0qthiBs6nrVqIuSfM6YoAniXkOv5Va+6Mms8NKjZXoelXU3NgsaAEchhtXrSkN91O4pVK78+lIUABYdeooArvErKQetZd5a4tZuOsbCrLTSAkNSsrzW8qDupoA/uj/4M5k2fs0/E4f9Ri0/9FvX9mQ6Cv4zv+DPiWDTf2Y/iZNduFB1q2HP+zExJ/UV/YoPEuibR/pMf/fQ/wAaAPwV/wCDmcbv+CQHxUUd4LT/ANKo6/y+/C8G7wfpB7fZlH86/wBPz/g5Vv7LUP8AgkX8T7a1lV3eC1IAOeBdRc8dq/zGfDEDQeEdKikGGEAzQauSsSfZfUVyfjC1H9kWf/X9F/M16CMZ+UZNcp40ilbR7NVUnF9D0Ge57UGR/r2/8EmR5X/BOz4Up0/4kkP9a/RgElSTX5v/APBKjULKy/4J5/CmK4kAb+w4CRnpkdDmv0IfX9KQHMynPoR/jQB/n3/8Hidlbv8AHT4WTyDJ8ibj1/eiv5Yfgx8XfiJ+y78c9D/aN+Dl42m6poF4lyVhJG+NTyrDgMCOor+qf/g8DliuPjv8KChyssMwXjv5gNfyRtC5uywXcvQqehGMY/GgD/X3/wCCaX7d3w6/4KDfstaB8d/Bc8YvJ4Vh1SzVgXtrtABIrAcgFgSvtX3+WSTBXBH6V/lQf8EMf+Cl+q/8E3P2u7fwp4tuyfhr44lS2v42PyW8sjAJKoz1Q4z7Zr/U30rxd4d1bS7fV9Nu4p7a6QSxSxsGR1f5gVI9c5oA/mp/4OQf+CRdj+2z8Cm/aS+EFoI/iV4EgadHhGJL2zT5miYjBLIAWX8q/wA5Cy1SS7V7e8iMN5A5huYWBVllU4IweRz27V/tl3WqeH7+CS0u5Y3ikUo6NyGB6g+xHFf5vn/Bxx/wSlX9kP4zS/to/s/2u7wB4vusapaxj93Z3sp+cgDokjBmGSApoA/ny+D/AMX/ABf+zp8e/Cf7RfgKZ4L7w7fxTFl6hEcMc465HFf6/H7Ef7WPw2/bO/Zz8NfHj4a30V5b6vaRtcRo4ZoLkL+9icdQysD1HNf44hnt5YisfzQTLkqeQQa/U/8A4JVf8FbvjV/wSf8AiZJJpUcviP4baxIDqejs3EYyB5kR6K6jvxxwaAP9aElZOc8CvOfiJ8KPh58YfDs/hP4naLZ65ptwMPbXsSyofcbgcEewr4H/AGJ/+CvH7Df7dvhq21b4QeMrKLU5VXzNKvZVgvEYjkbHxuwcjIJzX6c291bzxebbsJFIzuU7hz7igD83NM/4I+f8E29H15fE1j8JNBW9Rw6v5AIDA5ztY4PPYiv0I8L+EfDngrRYfDvhOxg06wtwFjt7eNYo1AGBtVMAV0XmRj7zAZ6ZqtfX1pp9q93eyLFEg+ZmIAH50ASEEDNfiD/wXx/4KBeHP2E/2DPE+pWeoxQ+LvE0DaXolqGHnPLMCryheu2Nckn1wKj/AOCiv/Be/wDYd/YK8O3mnT+ILfxb4tVGW20jSpBcFphxtlkjJCYP3hnd7V/mu/t3ft4ftBf8FIvjvc/Hb4+3bxW6Mf7L0peILOLOVVE6AgDk9T3oA+LtIgmEcuqak3mXuoO9xOT1LyMWyfwIr9ef+Dfsq3/BZ34YkdAbnH/gPJX5LNvkJbGM9PwFfrJ/wb/mK3/4LM/C97mRY0AuSWY4H+ocfzNAH+uTasDbx/7orjPiOR/wg2q+9rN/6LNbMWv6NHGg89Bgetcf8Qta0q58FapbQ3Ee9rWYD5h18tqAP8Tz4htt+M3joj/oN3Z/KZ/8av8AwZ+LPj39nn4xaB8dvhdfPp+vaDcpdRyxNt3CNt204xkEDafY1m/E+GWx+NHj2Gb7ya5eKfr57g/lj9a89Jdyp3YUdcdaAP1B/wCCsH/BVT4n/wDBWL4o+HfF3i+1fRdA8OWawwacGLL9o482XqBmQ/kK/LrxLKp8MXSxjhUwB7DFWCxbgKF9h0rJ8Qkr4cu4+5X+ZoA/1F/+DV5wf+CX2hf9fc/8xX9J/Un3r+aD/g1quINO/wCCXHhye6kC+dcXLgE84VgD/Kv6RP8AhIdHXkzqPrxQB/HD/wAHlAz+yb4B9tVlP/jiV/nz+JCR4NiUddkX8hX+gp/weMXlpffsleApbZxIP7UnX5eefKU/0r/Py8Rxj/hFEUckLFx7DHNAH+sh/wAG7xP/AA6n+HO7+5cf+jWr9uzwgFfiD/wb63VlpP8AwSq+Gq3syoXhnbBPT963Xng1+0Z8SaGcL9pj/wC+hQB/DD/wenMq/Df4WbVz/p90pJJHWNTiv4KpNA0yJlLQrtZFOcnqRX96X/B6ITefDD4X3tqyyQLqU6EKc4YxLzX8Jky7gjdQEUfpQByh0XTlbMUKqPxJrRjg2qEUhfpWk0akVA8ZVgV6UASwR8c1KbdTn3qRF6N2qXIPAoArNCu0/L/n86zJECnNbLMvT1qlKgJ4oAy9uGO6nbVNWJAuc0g2/nQBVZWAIDAfWlWMKAFOTV5E3kqW4HtT5Lf7qqeF5H40AZ6R7ZMkdat427sDkCrARgoYjNWo4AVy4NAGeF24RenX/wCtV8khS5HykdPSkWJG27eoyavxxSPH8iBhQBjx7X/dIMk/xUSFwrgjHNX/AC2EZ3ALjoRUDxtkBh9aAM3ZJuZpDjIB/GhWA+bPT1qdgGCupB5IIFO8uJwDgnnkd6AFid+V754rUgfgYHfGR1rKRNoIQ4zwc1ciBiCxjnBzQBsLKW2sBkHjJqTsRnlf1FZCTtEAjH7pPNXDdITnOTQBdYqG2j8aD8vPeoI3Dxjd1qVXjPHpQA7jGRQORkdqOM5HWkLMpwR96gBn8W7NCjYAAegPPvTtu0en14puODtA6dQaAFC7WOe4wfx5pp5TPfNPZvmyOoA/TikIO3ae3NAEI6UtIOKWmgMvVmYaTOWH8KV/ab/wSr05r/8AZ4sIVH/LjBn/AL5r+LXV/wDkEy/7qV/cB/wSRtkf9nrTyOpsoB/47X8wfSidssov+8z+ivAB2xtV+Q/S9Kk07/goz8OZW7TxD8i1fqP+3H8X7j4J/s/+NviBpOV1lnk0vSyuNwnugMkZ6YQMc+1fnl4kit9M/b6+H2oTOkQjn3MWZVAVMknJIFfqL4j8Q/DHxRrktrq9xoWvSx3z3Fra3VzDIqTMAqt5GSXkAHyjHGTX+eWJxc08PVlByjDf5Nn9YYvCyq1eaPY/H/8AYu/Zt+LeufDawuPHN9c+DfB18ZLzUb2RzHe6ley5wI1PzBFIALMMEc85wPCP2qPBv7Rf7O/xR8IfFLxJ5monQ9QjT+1bLJg1DTQylBKykncoXBD8nNfujrms6lrV613rUwmeAlI0C7IkTHQRnjpXGW+q3GmWNxpflwahp1wAZdOvoxNbE92UHJU5+orzYeIfLmEsXCmnFtqzOing6ija549rV7b6rKmsWYAgvIVuEXH3VmTzMfhmvqjweY18JaWrdRZwD/yGtfLepBJQzRqI0CFVRfuIAOFUdgBwK+p/CNsX8KaY4PW0gPT/AKZr71/UngVOMsNXlDZ8vy+I/IfEH+JTV+/6H//Q+4NAsv7S1lNPicI0x27z91c9z9D19q4vV/Gfxu8Kapc/CtV0Oe0adGXxnuAtbWBuqSDkeYDwFJrvvDagXE8o+8sTEfiCK+GEuJ5P2D/idBI5Zf8AhJIepz/dP86/xNxWVUq2N5aiuf6c4KE1TXKfeHxa00aT8GfHGlW+prriy+HpX+3RgLHPvibLLtJwMdq/BP8AY2+G3he8+D+n3U+k2088l1chpJIUdsZH8Tc4Fft7Yn/jEa5UjgeDnAH0hwK/NH9hjRo7j4LWKvGDi4uCM/UV73D9eeHyzE0aOl5xWnozZQti4uetkfbnww8G+FNGiV0htrOVh0jRFP44xXW/tP2VgfgReiznjlbglFIyMZPSv59f+Ch/xx+Nfwy+Ktva/DzWptPt2TaVUjaCBxwQa+CT+27+1VLA2nXfidrpHG10kVGXB9sAV+/+HvgjmGNp0s0pvmXq9vuPyrjnxMw2GqSwT0PCPGWG+IHiA/8AT6/P0JrETlcVDPeXGo6pc6heYM13IZZSOhY9ce1V2nkjXrX+g+S4ZUsJCk946H8UZrWVXEzqx2bLTDBxSVWE5Yc0jSN/Ca9CUbaHmFpmIWq2D60PIwHrUHmk8HipAV2JbbS7cLmmH+9TN7HgmgCUYzzQyYOSetR89+3enb5WUYagBcY5zmrSSlOCB1/SqoLEfMc0FpSegPbrQBaaQ7Se3r2qFDk7gKiaQjC5+X0qs0rFi33QP1oA0UlVFO4kfhUpniCLIMsAeT0rJa4cZCjHpQ1zcugK8kdfpQBda5YERqp5PFP81ySpGCP51QWQu2cYJ6VPGWEmGPA/Q+tAFtbgIcHkmniZWOTUCupYjHWkYKozigCz5seRSCdc7VJFVkHXPSpAxVgBQBaVmB3DrjFO2J1zUYJIyaeNmc54oAngO05FaKMeN3Ss0fL0q4CNh3UAWDNgAt26CrAlVCcZwRVNJEyGYZzVolVXJ5HagB/m/u/m7VALhmG1jjNRSliu09TVZvm+tAGkYt/cfWmMfLG1D9arpIY096nDCQcjpQB1Phf4jfFvwHayWHwz8X6p4aglbfJDp9zJAkjDoWCEA4966Rvj5+1ax3P8Utfyev8Ap8//AMVXl4OFyOuanJO3IP19vpQB2Wu/Fn9oLxfpMnh3xt8QNa1jTJ+JbO5vJZYZFBzhkZiCMjNcY0SLGI4xhUGFHYD0phl2ttXPTrTGkfHXNACFWUhvQ0KIZX2TLuAIZfZh0NRiQqfTPFMZsMQtAHpun/HH9pTQbNNM8PfEvX7CyhAWK2ivZ1jRRwAqqwAHsKtL+0T+1cp3L8WPEYP/AF+z/wDxVeSEq3BxUBPzDaOKAOk8U+OPib8RJorv4r+KNR8VT2xJt5NRnknaHJydm8nAPtXJSKeRnr0qzKSOP51SmZiODzQBVuLO3uoDBcoDzlCeqn1B7H3r1Oy/aA/ag0y0h0vR/if4jtLS3XZDDFfzhI1HQABsDHSvMQ5k4ftTSis2Mc0Aewp+0T+1bjLfFbxPk/8AT/cf/F1l+IPjV8ffF+iv4W+IHj/XNd0eY5lsr27lmgkIOQWjckZBx2rgIFwArCnyqAdueDQBk7IYRsh4HAH0Haqc0rgGJDgN27flVmdxHwpzWJPIzEhTQBTgRtE1OPW/Dt1NpmpQNvSe2YoysOhBXGPwr7t+Gf8AwVf/AOCmfwZtIdL8B/F/XHsoF2pDc3TzKPbDkjFfBsjBQeuaqO2VyKAP1su/+C93/BWm6smsU+JEse4YJCxBvz28V8pfFP8A4KN/8FCvjdG9t8S/ixrtzbyZDwR3bpGQeo2qQK+PZAFXAqFRggjpQBNHAr3cmo37NdXUpy00xLuSTk5YnJ5q+8gYcjr1+vrWexLdTS7mwBnIFAGrhQgx2q3o2ta94X1ePxP4QvpdJ1W3z5N7bMY5o89drrgistHYgjNNc9qAPXz+1D+1p0/4Wj4jP/cQuP8A4uq15+0z+1pPC1u3xP8AETK4KkG/n6Ef71eR+W3b/P60bHwRk0AYEjXOXad3nnmcyTTSHczs3LFmPJJPNNgRzkNWtJGSeajRQrHdQBW8oj5s4qGVY5kMUo3Kexq3MQWG3jiqb53H5qAPSPDnxz/aA+H2jR+Hfhz471nR9Oj5S0tbuaKFCeuFRgK6CL9qb9q6Rtk3xM8Qc8f8f0//AMVXiMhIHBpVzkDNAHr3iL4yfGj4hQQWHxS8Y6p4ls7Y7orW/uZJ4lbGMqrkgHHHFck1zHNGY2QMvGARkDGa5YSuh3g89Oasi7ccMMfTvQB7Pov7QH7RfhfTI9A8I/EPXNJ02DIis7a8mjhjBOflRWAFWpv2ov2r0OR8UvEP/gfP/wDFV4yk4I3ZwKq3BJHXNAGz8SPix8ZvitDBa/FHxfqfiS2tTuiiv7mSdUbuyhycHFecqxK49OK0bmB/ujJ+lVRAUGGFAENL7gU9FBHNJI/lrtHegCvvYcUkkwTATqetV3kA6VTdjnf3oAsyzEOQvOKhM4xuJ5qvk9aoMSWOaANMyK2aUMPWsxSR0qVXIHNAGmkqhwc81qI6hfm71z8b7myK2bT5utAF9QNtW0YiPjvVZBkY9qtxnahHegBkIkLEkAgUjEY4DDt8oyKmQYGR3pnlxltrjhu/pQBVYjAXDAD1qNnDNycD1q08KbTkEYqBY2GUc5HagCELtJIdQP8AdqQjYykSDceTgHFXBEhQKM9MHFLsRVCksAOmaAKCIcFC28E54GKlaEBgRGR9atokGcsT+VWHjiKhlz6ck8H2/CgDLcKFZUGxs96bnDYJJ9xV50AbfGeD0z6U0Io+UDIoAdH9ynKuCT60YCrgUKGKj170ATIefegMzHrTY1fJpylVHvQAu3LEg5A9eaT5ugwPwpTuY+1KVBGDQAnBznrin/eGT3oJHJb0xTVbPA6CgCLBPSjDVMAB0paAMvVo/wDiUTH0VK/uc/4I9WMt7+z1pxTo1jB1GBnHTNfw13SG5spIWBwV6DqcdO1fpx8IP+Csv7QnwA+H9p4G8C6LBbW1hbJD5xd2LhONxHSvxPxx4IxnEGBhh8HG7XyR+w+E3EuHy/FTlXdkz+wD9or4AeBfivbLa+LLYTJGSQ6HY3PYMOcV+TniD9nz4ffBr9sH4VN4FtpLUXF8rTh5GfcY2wpG4+9ex/8ABND9q34n/tb/AA81Dxf8TrhZJWmRIlRQqRqqnIGAK2vjxah/2w/hQGPK3g/VhX+c8Mux2TY6rl9adrKaa3Xws/tzLsZRxeGjVpu6Z+uPjQXt1rmpDS7GXUrry0kjtbcgSSZXJCluAcDPJr53/wCF0/C3W4rTwv4Xt9YvPFt5cG2fw8IFW7hZM7mYthNgAznd0r6L8Ta3f+F7/wAT+INIk8q6tLHfDIACVdYiQQDkda/NTxJ8XfHek/AvwP8AHzQ7lbTxx4i1eW0v9XjhiWeWJmKhG+TaBgY4Ar8hy/JYV5Oct3K33/8ADHRVnOL5Uz601a1lt2mtriJoJYgVkifG9H7q2PlJHcg4r6m8Gxr/AMIhpX/XnB/6LX3r5b1e4kvM3lyS00ibnc9WJHJP1NfU/g3/AJFDSv8Arzg/9FrX9i+A1Pkw1eP+H/24/HfEBP2lO/n+h//R+69DjKT3Kg/8sW/9BNfCEXH7CnxN/wCxki/ktffukIPOnJ/54n+Rr4FiGf2GPiZ/2MsX8lr/ABdv/tzf9bn+ouCVqVz7F0/n9k24U9/CEn/oqvhX9g+xRvgvp+3+KW4H6ivuy2Cp+yfKx7eEm/8ARQr40/YDiT/hSWlM3eWfH/fYq8mnehW/xx/UvFxtPm8j8V/+CrMZtfi3ZoP9r+VflQ7EOSvGa/Vb/grjIo+MVps6Zb+Vfk/5hJOOea/0/wDAqcqfD8eXqfwb4uwTzeUpf1oWYnAPHWkkdCcN0qMSHHeoSgxu7mv19xsuVH5bCdyQyrnaDwaMq3zKfu8GqZCq+ajcs2VIzQttTM0C+WXkj8aVQGX169ap7uAoHGKQZAJJ49KYFzeOlRM6K20VXB2jPSnqA3zNQBL5kecZOTS+ZHuMeTmqpO1s9hRuV5N7UAW/NXoc0nmIT0BqH936ZpCCOYzigCd5I8gE8VFI+/5cgimEKW2rwR1FGcc/zoAXcy89QKTcrcrSH5Pun6+lIxB5PBFADhIQdqDmpUlk3EHqevvTUG9Bv4FORFBJz8w6H2oAsAsPu81Om5h84qtuYjpU6ttHFADn4ximc/fqVcdaasZIz0oAb5jPwp/Kk3MPk9OaGGDheD60pdsYoAuxMzIWz0q6GIXms2ByVwa0Q2F4oAkQ7/kFTli37sdqhjUK2asZ7mgCPJwcHJHrQFydtNILHBokYIwCmgAYnOQOlKrSLy3Q0qvn7w4pxCMPlGKAGl/l3fpU4uQQNwBIqmBikwefegCxIxJDetMd8nA4oj+UAnrU6kK4DUAKFBU7hVP5t521qMxLg4z2qKSDY4Ocg0AUfLZzk8H2qBhiQAdKuvmMEiqskjYwetAEcgc8Yqq+FG09amup5BFvB5rKa43D5utAA7bMkVZtCH+Zv1rCupePxqotw6H5TQB2mcPvzxUdxLEBnPNchLdTn7rVny3Nw33mxQBsXjEMdpxWU7Pu461X80/3h/n8ahLsW+9QBKdxB31WzhiD0qXeQOTmo8YQ0AQ7i2c0icginFAeTU4jGB/n+tAEESE5BP51Osag5/pUhVV54pQQy7R1oAkMLgAjvTGBHWrXDALTWTuaAKxJzSZNWfLyM8YpfKPp+lAFTaGqpKgBzWqYu2KrzRYfmgDKlhbbuznFZVdIYxisqSPbwaAM0lz2zQJKleOReScA1RWQhtq0APeR2YAc81YVn6GqJYs2KtxhlGaALcbMep71PIXYbRVVGkK7gce1W1IKbnHPegCERybRn1qtLGavtLggjtTHw/zA5JoAxCjKSewqhOJX+Y8VvvHvJU8VQlhUKdooA59o2J5zVY5Bwe1bMsdUJYgB8y0AUHJB+TkVVb71aTIMEVXaMYoArx96Zk1IFCMc01+TkUAKr+WM1qQ3RjANYyfezUqSEGgDo0veK0oHLrurl4pDitq1YtEB70AbZ9BTfMAG00iP021Gy7myaAHzspTdk81VyhBZTg0p4OKZ5f1oAVZGY7c/rVuFuMd6p+WKAoHIoAvxuC+1jzVkMJAD1weKzUIA5p7SYXC0AXFWMnmjK+lRQdBUiKTIT2NADo9sg7DnqakOAxAGPf1pjjPydqeAFA96ADOKTApeD0wT6HpTD1wvIPrQA/txUZL46U/HGBTCDjB6mgCXA2/jUZwvA70FcnmlCgHIoAbuK8GpByM0yQbsYp5O3k0AIRmqsolW2mMRIPkt04q3nAzTWYtbzDn/AFbfyrojFNNy/DQUU+ZWP6n/APghTaxt8BZXZSzNKc/n3r7B/aBjA/a++FztwftmB/31XyT/AMEJP+SDzf8AXST+dfXv7Q4J/bB+Fx/6e/8A2Za/yr8V1/xkmJfnP/0ln+jfh5L/AITKUOyR+nnxJVltfGCx/wDQPY/+QjX5R+OpJF/Y4+Fi9M+IXz/32a/WH4hEbPGH/YPP/oo1+TXjUEfsffCmQ9D4hbB/4Ga/B+GVd2f81/zPsMTT98/Qu8jDWkWRz5ZH4YFfVHg5VHhHSh6WcH/ota+aJ/8Aj3QekJ/lX1B4O/5FHSv+vOD/ANFrX9WeBsr0K7/w/wDtx+K+I1VqrTXr+h//0vvvSxmadf8Apmf0U18Bwn/jBn4mr/1MsQ/Ra/QDS0InmPrE38iK+BY0H/DDPxOb08TR/oF/xr/FqEr44/1Hy/3qWp9i265/ZNmY9P8AhE2/9FV8ffsJRiH4LaQn92SY/wDj3/1q+y7OMD9kybJ/5lRh/wCQK+O/2HFP/CnNLx/fm/8AQjU5PNqlWS/nX5MrFayt5H4cf8FcEZfi/ZE9yx/nX5TKhGckda/WH/grngfFixJ/2v5mvyXEhYk1/qR4GR5uHabfWx/CPjIr5rJdv8i1kBSuaY2F6mo9hJ+tRSlVbmv2B7n5BCbRGXVjx2qEM5JzRwmSe9NDgEkc0jQeJMc1IHz83r1qrS5/unp19qALG/PDdPSmYYcZ4qHzE+939acJd444oAl570p45qDzCvJ5pTKuKAHh8nAqQyFRVdWBHFKD680ASEsMAn8acCwOahZs0BiDQBJznnpSfOfrSB8kZprSbWwBnNAEvmyY8pjkelTxkj5R2qozZxxUiBvXGfWgDQRnVm3DFWAHHLVQfYkQmkfGOcngfnWVc+LvDlp/rboOegWP52J+i5oA6hWC9afvHU8D1rim8e+FVl8lppA39zyzvP0GeufcV9Ofs5/sn/tc/teeKYfDH7OvgDVNZEzhDdmFkhTP8RdgF2juc0AeNGCR8snPtn/GqpkhWXyGkUPjO3Ir+tb9mj/g0b+LXjGO28Ufti/Ee28PRDDvpulA3Eyj+67NtUH6A1+mGu/8Gk/7BvirwFdaV4D8Xa5Br3l4h1BzGwWTHBKDGRnqKAP4AoQc4/Gr6sDxX6O/8FJ/+CTX7TX/AASz8XQxfFJP+Ei8F6jKUsPENopMfBwEnHJR8H7tfnMUj2LLCd6uMhgeMf4n/wDXQBYGByaXflcHrUalXqXYT1NAEeW3A+lK4VXGOeMc0Hg4qhdzEfMOKAHySkAhelCXOByaxricqN1Ys9xIT8poA7gXER6GkLhmwDXAxz3AbCmtuzF0x3OTg0AdWjgDjmrUQGeayog2BVyBskB+BQBeYMrY7VMMlcsOlO3KygL0FSK2R83IFAFOdTgEAVkzMDknrWzIwK7zwKwL2ZSx2jigDCv5peVXgYrFMjgfMea17lvMUMxrKmCkGgCk0rZ5aoml5x1psir0x+tRFQPu8UASPIwGBUW8cb+4J/KmlGIxmq7K/wB33/SgAaWNj8jCglgM5qOWPLZAA/CmIzj5H49qAJiMkBqmQsPlc5FV5HCcelKJwccUAWmYEbegFPBGKrbWb5l6UuGAznpQBZBHfil3Acg1TDFjzzT9oxvJwo5J/wD10AX4pOTmp5DuAC5zXP2uo/21qkWgeD7efVr2U7RHbRsxz6DuT+Ffp7+z7/wSV/b6/aE8i58FeA9TEMpX95LC0YXd03FwMfyoA/OmFSTl/lHqeP51PNf6NaL5V3cxrJ12g5P6Zr+ub9nT/g01/aC+IU8GpftC+IbPw3Y8M8cf7+457YBCg/8AAjX7j/BX/g1Z/wCCbXw5ggufH1tf+LbyLBLXMghQnudsfb2yaAP80lLq3uh5lhFcTg9DHCzD+WK2NJ8L+MPE0v2XwzoV5eztwFjiJP6Cv9cDwV/wRo/4Jv8AgURLoXwx0kmIAAzJ5vT1Dk19d+Ev2T/2avh1CIPBfgXQ7Db0MNjCp/MLQB/jzeB/2Mf22viVCZ/Anwr1/Uot/liSKymkXd6ZVSK9Lvf+CVX/AAVDt7VdRuvg/rltA4yrTWMqDH1ZQK/2LNJ0bwtoEYtNIsYLQKdxSGNUXP4CtSSSwvz5M8KtnoGXP86AP8Y6f/gm5/wUFQMLv4f3EbJ1RlUN+RI5rzDxL+xn+114QtHvvFHw61eCOM4Z1tnwPToD1r/aL1r4X/DzXHD65otpKwOcmJcn8cVxOt/s/wDwU8RXH2rUdCtnYoE2lBtIB6EdDQB/ijRfD/4jRh1uPDWpAIcMfIk4I7H5eK5i9upNKna11W1mtHTAIlUg8+xGa/2QviZ/wTE/Ze+IYluNM0ePQ5pjmV7SNAX+oI618qeP/wDgh3+zb4u0Z9BbSdPvI5Ex9ou7ZPOB9Sy5oA/yboryxkXd5nHqQR/MCtJZI0iDIwYH05H51/fd8V/+DWzwbqGuS3OjWttJYysSptXMTKDnotfnD+0F/wAGofxf03RbjX/2fPEDR38I3fYL9MI2OyyL39sGgD+SSWeOVCYjVJJ5VHPNfcfxx/4Jd/8ABQj9ni5uz47+H99eWloxDXNonmoQO/GD+lfCepDUdBvDpviOyn026UkGK5Qxtkem7HHucUAaSSb+opSoIOe9VIp33hJBjjPr+oyP1qyjl13YxQBVlixxVKZBIMCtlj2PFUZgO3agDFlQK5Jqm33q0rgBsnNZr/eoAozMXfIGKMZTiiRcGkBwlAFYFwdo7VYBXHI5p2GHC/nUBVu5oAuxONhFbelt5gK+lc3EGJwDW5YSCJufSgDp1TGCKawwabFKrYGetW/K55/lQBnEMWIxUp6GrrqAOKQxL/kf/XoAokEJio9rGtQwqcfNimbApxuz+FAGfsanjcBjFXmUD7pzUZOBmgCOOVV5arEbqRxVBid/Snwck54xQBohvlLD6VESAPekTIBGaXL8HPHegB/AOO/rQzKpwKNkgbAGBjNGCwAxyaAF6ilJwoA5xQ+T06ikDZOXHNACE5B4pU+5ilbB6DFMI9DigB33evekZT/DwfzpUyB83NLQA1CDEQ3UUwMPs869xGxP5VIoxxTXGIrrb08pufwrovZWNVBcyP6qv+CEpx8CJQe8kn8zX2F+0GpP7YHwuA73f8mWvjz/AIIT/wDJCX/35P5mvsb9oH/k8L4W/wDX03/oS1/lX4rv/jIsT6z/APSWf6J+Hf8AyL6foj9NfiBzH4xb008n84TX5SeOFP8Awxp8Jl9PELf+hmv1g+IMRWDxj3zp2f8AyEa/KPxx/wAmb/Cf/sYW/wDQzX4NwtK8vn/mfaYp2nY/ROZT5AbsYs/+O19QeDv+RR0r/rzg/wDRa18yyp/oiD/ph/Q19N+D+PCWlj/p0g/9FrX9WeBa/cV/+3fykfhviRJutTv5/of/0/0I0kFppf8Ari3/AKCa/P2Zin7D3xLUfxeJoz+YX/Cv0P0iPE8uB/yxb/0Gvzzuoz/wxH8SVH/QzRfyFf4sU9Mcf6j5b/CPstMr+yfOB/0KpH/kHFfIX7C3z/BfSSe7z/oxr7GSLP7Jtz7eFW/9E18dfsJ4PwW0sjoHm/8AQjU5R8Fb/HH9S8X19D8N/wDgrt8/xXsCe5cfzr8jYJMHJr9Zv+CwF0tr8UNNkPdnz+tfkXHcIRuHev8AUzwM04dpn8G+LrbzaV/60L4nd3J96YZBg1VE0Y53YqhJdxgkA4r9ee5+TWRpFyoywpyMrrn+VZ63WSOc5FNWRVJZjgUhl6YqoyKqCbIznFRyTx7ck8VU+1W+cE7RQBe81felEoAqg11bD5Q1AuYgchqAL/njuKTzB2zUBmQqDnNSALjJ4oAkEwHvQJiT0qBgAeKcnWgC7T1HzcEfjxVC8vLawhaa6bCjj61+3P8AwS+/4IPftIf8FMdOHxQ8Q3Y8CfDyJuNSukPmXIDciFDjIH97OKAPxMbULAkx/aIww6jcM02XUbGC3aaSePaoyTuHSv76rb/g04/4J42/hyLSZ/HOoS6rP8guxL8jv04UD17ZrkfD3/BpJ+xN4T8Zwjxv8Rbm/itm3z6eijzZF6gY5IB9cGgD+CSLxZpl9J5WjLLfOeAsMbE59On9K+6P2YP+Cff7dv7YFwlh8B/hxfTW8sgDahcxukaA+pYKOv6V/orfCz/gl9/wTU/ZyS1svhv8MrSW4QDF7fQK3zqOGZjk8+2K+2/CeojQ9PXQPC11Z6RZk4ZdPjEYTtgEAHA6UAfyBfs3f8GkHj/xBBba1+2p8Rl0uNypfT9MKiUZ6qWYFfyr+gf9nD/ggH/wSX/ZuWJW8Hx+KNSgAZbvVnMrswxyACF5PtX6m23g+w1eIXV1q5a4b5Q785z3561Yk+Dfiuzj87T9QS/c427jt47DFAHxpff8Epv+CUOpeI/+Ex1n4P6G18JN4fy2AyvT5QwUflX6I/Cyz+EngfTo/Cnw+0az0a1gVViitYUjUIowOAK+N/iXceNPCUjWesW8sEYGfNC5Td2G6vO/g78TPGD+M30i/t/Nmcbo9pyNg9aAP0D+Jfwqv9Wgl1/wbcOl0BveJzlZB1wM55rzr4PtrCF7y73RvvIZW7EcFSK978A+KpdatRY3hET8nDdcjtXMWEdp/bmrafZMDKlzvkx/CGQf1oAx/wBoz9nf4W/tefA7XPgn8XtOh1LTNatXgIkUMYpCuElQnkOjYII549OK/wApP/goN/wT1+Pv/BMT416h4L+LGi3DeBLy5f8AsTWwhMDRFjtVnHAYDGQQDX+uZYT2unaVLqOoSLBDbqXldzhVVed2a+Jv2m/gl+zt/wAFI/gZrvwG+IlqmpaJqaPDFeYG+KdQQJYieQQcYI60Af5HZZVCTBt8cih0ZehUnjH4USMD8yHivvX/AIKQf8Euf2if+CVHxXj8D/Ek/wBseAtYndNB1qPJQr1WOQkDa6jt3Ffnnd3hg+SPmgC9LcCJQetY15I0hC9MVVOqseGAqpLeO5wOooAbcSknHbvUCKjE0Mwfr3oX5elAFq1hRrlQa7VI0EYVBXIWDAzgkZNdkh5GKACNO2RU5QRgbqlR1BIbjFKWSU4B4oAfCyHpmpHZkUkDIrNlnWP5AauRXKyxBFIyOuaAKMzuy8dKxLhGOWPSuhuYmSPzB09q5m6k3xstAGZPIhXaBwKzyqt8yn86sN901VX724dRQBCyc/NTAExz1q53zVSRS4460AQMqsc/5/nVeQBTgCrK8DBqBkJbJzQBCTzyMn2qt5ZOGKnJ9asmM4xmo9uwBj+XpQBFIqt1606NVAzijbk896WbNtEZDz6UADMQ3FLuyOPxqpLc/v4LGCJ7i6uWCxwwjc5/+v6V+iX7Kf8AwTZ/aT/ai8a2HhLwxokwkvHQsqIzFEbuxxtGO+TxQB+da3kTXcdhbxtdXExxHFHyzHtwOetf0f8A/BMz/g2e/ab/AG3V034uftE3sngnwJckSJGyEXlxFjI2IwwufVhX9U3/AATw/wCDc79kj9lubS/if8YNPj8SeLYkSXyJf3ltBKAD90j5mU/hX9GZS1tLaKw02JbeGEALHGAqKBwBgcfhQB+Xf7GP/BFv/gnv+w7p1sfhl4KtLzWYFCnVtQUXF3IV/i3MNqnJP3RX6lWNto+kRi20q1S3VeiooUfX5QKpCYCUKfvGtq2jjwWlP40ANxNKQZDnnPNLhmj2fd96Y97HF9zmqktzNN8sfQ/xenvQBopNFbjJ5I9Kq3F7IxLQjINZv2q0iP8ApE6AnhQGzk1HPqNhBGXZsbRyKAJJdQKD98nH9apxa67zfIpbHT0rlL7xpoNsQeXPT2pza9JfwAWcYB6n/wCtQB6D/abNHvuAAPX09qetxGSC7D5uQB6e9eL6je+KAhNvYSlB/ESMH9a5BfGVwku3UA8HYmQbVQ9vm6c0AfVUUjAgLhlPep5LiDd5ZxXzNpXj+9sLnyHuoODgq0gzjs30NdpaePtOvMPc3EMTE4wXGT7jmgD2hCBwGAHYADj9KV4reYbCAffGf51x8d4FiW5z5iHnKkHj8K2tO1OyucLE4H160Acf4v8AhP4G8a6fcabrVjDKlypV8oCemO9fhP8Atnf8G9/7OP7VVtctfRxo8ytiQKElibsyOoBB9untX9D5mQNxzUwVJRlaAP8AME/bY/4NVf2zf2dLibxR+zjqC+NNCGT9mYkXMW3+FgOGzxgjBr8FvHv7K37U3wv1S90f4geCLrRrzTlJminRo2kA7xhvvfgTn2r/AG3mgVwY3GVIwQeQR718X/tdfsKfAT9sDwsNB+KGlIbmFSLe9gXbPGSMYDAcj2NAH+LZFe/at1tIjQ3MRxJDJ8rrjr8p5qqVLFlYkEc1/X9/wU1/4N7PiJ4I8YXOr6FbG70mQMbLWLKLPlnP3bhV54HfFfyr/G79n74tfs1+KW8L/FbS5YY3OLa9VSIZlP3cNgjkc880AeNzMQTVTljV0KJSWU5A79j9KiRFwTQBQdSrEGo2BPAq3KuTkCqhQnqKAGtkDJNIAuOTzTyjEYxwKQxs54GKAGqCOUP51pW5xjdjnis8xu3WrluuFG7rmgDft5QQDWykmVwDk/rXO2pULljjHSta3nxIADjFAF9nQjcuWT+8O1PwT9D0+lIZE37Im56nI4p5k2Zf+729BQA3adw9BTcI3TIqUYcbhyR/WmoVK4c49Pf3oAVSuwgCqZGJParZY7celVywxhsUAREDl+4qTaAcikwNhxTqAFBxR8x+51HQ0xjgZo8xVAY0AT53HrzSrkqMnmoY8jOB15zUu1/vZ4FAEh27e+ajHal2qefWlI447UAKSACTTWyFDHvSg55H5UYGPWgAXpTSX9P8/nUmCV4GKj3HcF9aAHHpTJNwt7nHTyXP9KFdim/FJKS0Nzn/AJ93ranrFtmkHeSP6qP+CFTEfAqTH/PRx+ZNfZXx8+f9sP4XZ/5+j/6GK+Mf+CFJP/CjJR/01avs/wCPH/J4vwv/AOvlv/QhX+Vfiz/yUWJ9Z/8ApLP9F/Dhf7BT9EfqL8Qo8Wvi8jvpmf8AyEa/Jjxuuf2OPhOP+phf/wBDNfrh49w1l4sz/wBArP8A5CNfkn40Gf2O/hOP+phf/wBDNfg3Cm69f8z7THL94j9GZUP2ZM/88P6V9P8Ag6JD4R0o/wDTnB/6LWvmi44t0x/z7/0NfTng7/kUdK/684P/AEWtf1V4HP8AcV/+3f8A24/B/EhP21O3n+h//9T9HdM6y46+S3/oJr891YN+xJ8Tc9vE8X9K/RHSIiXlwP8Ali3/AKCa/OrBH7EvxNHceJY/5iv8VI/72/66n+oGX/wkfbcAz+yVc5/6FZ//AETXxh+wiMfBTTM8fPL/AOjGr7WgiY/sh3Djgjwq2P8AvzXw/wDsKFx8F9Myf4pf/RjUZO/cn/18j+p6FdaP0Pwb/wCCzJ2/FPTf95v5mvx1jvcBga/Yb/gsyf8Ai6mmlvU/zNfi/uBLYr/U/wAFf+RBS/rqfwL4u/8AI5n/AF0RbuLw/wAL/lVL7Y4+Y/zqs7AHmoJyHOV4Ar9cPyk17fWWiPzVdfXUYlT0rkGKn5ScVChZXz1FAHTzXqzHg4qkZJRwzYFY5cjnOOamNz26j1oAv75GOc9KcskjLljisr7QM9f8/lUy3DE8jigDorHUfJIRua6lZlYA5HzV5zvVhyv5etdRo7rLGSevvQB0OABxQx+UbeppqgKcA5zUy7WYK5ym7nsfzoA+2f8Agmf+yDZ/t5/t3eCf2cNela20l7pLnUnX5ibePDuM8YymAPev9VXUfAV94J8F6V8FPgR4d/s/w7okCWcMSL5cG2NQADn7w4GT3I96/iS/4NBf2dNZ8fftS+Of2pNUtR/ZGk2rWMEjKCfPcjgE88IvOBX98Pxdi8QPKkvhTW30u8OFxIoe3fPZwOgHqKAPA/DsN14Z1hNO8Xw/ZNXZRthADQnb0MZ/wryL9qr4r6Z8PLOw+J2moItQtJVhnn2j5424ZT9PevPP2kv2jdU8PWbfDrx9ZxWfiO0AksblMlbnHeF8d/Qmvkb4w+OovjL+zZrVurONYvLV4liLA+XOnQkdRn1oA++dT8VeEfEPgZtZ0qYv50SzPHuAOXGcivC7PxMNHv42STdZjAw52bnxxg9zjrX4o/ss/tky+JPAseh+ILlorvS2k0y/RmO6KWDhdo9GABzX1lqXxz0nVvD0+mX08cFtGd2x+WLY++D2H8qAP0L1H9pfS9DdFiLXckJBMatsVAP7zn5a+tP2ef2u/DHxJ15fDyuLiQYxKuSsZ/uEjg49a/nJ1bxFe/E9Qvh+Vb3TdOXlEfyxIc9WORvAx0Ga95+D/wART8O762aec2lvO6sUgQuDIeiEDoP94igD+ojxZomgfELQbrwpq6iaO7iYE8fK3YjHIIr8yfhr4Mv/AAvq+peHASl3ZXTD7TnMjRZIAPp06V9Ufs8/FGf4ipDJFABLabY5RI3zMrA8jH06da+XfCl9D/w094u0G6wsP2yXy33/AMeFbZ198/jQB9teBbCFrqAW4lJQB3mkI+YDg/zrzj4KfEWPxj8SPH9jGA8en6r9ljkXq+xBkH869q8HCOSK4mnmPmWkLFxkbQMZzx1/Cvzt/YK1uO98f/E6WKTe83iedg5PykbFwVzQB9h/tn+KR4A/ZC8f+LS+37FpM8hY8YwvT8K/LX9gL453PjH4QaH4ihuNouyzbE+6F3Y3H0Nfo1/wUbilv/8Agn/8VmjZQyeHb2TPXISMt/Sv5ov+CW/j3Wda/Zo0qbTJhEll5i3KNhi6rJxsAOe/Qc0AfUX/AAdQeCW+KH/BL208cad5c7eGtUiuS6/NhSvlkgjOOor/ADldL1Majo1neFssYlDfUDB/Wv8AX21j4I/Dj9tb9jnxD+z18QoEXTPE1hJasUHzRs4wkgzyGVsH1Ff5VX7bv7GnxR/4J1/tL61+zP8AGaB4hBM8mk6iw/c3VszEoyv0O4DkZ4PXrQB8umUZ5prOxYbRQZlQlZV+Ydalj8tlO00APjlA61KQNhaqG0BwwNWkZXUqOc0AXIXeICVa0odUkDBD3rEyYwBn8KcHDe1AHWzapEFHPOKz/t2ec1hBi3B7VLlnGKAOgim87Dn1rcgjGCAeuK5qxBiT95zWrHqKJlSKANd5GMRiArmZsqxQDOTWk1+ZFxGKrpC7tljQBi/ZyTuTvTvsTjkYro0s1C76iktwx+U49qAOXaJo2yaqtGCcsK6CeL5M4696y7iMcAHBxQBhyR7AWHeoK0HQN8pPSoxBxntQBUwT0pjg496uIgA5pGiyeKAKSKwbzMbtvO31Paruh6Tqvi7WofDeiovmyNh5ZD+7jB/mR2HvTtOstR1jWLbw74fgkvNQvf8AUwRDLv16Dr1H4d6/ta/4IXf8EK/DPjDwxbftJftV2n+hWkgltdLc53suDmTPB5B6Z6UAeSf8EiP+CD+o/EfQ7b4pfEO0MFrOyzNqd/Gc7MkkW6HBz6Gv7WvgJ+zv8JP2bPDFp4f+GWkwWceNsl9MA1xOV67ccjNegmJo7W38OeEbRLexsUWOAIAsMUajAwBgHjjmprDxV4c0/WYtD04/2rqkyszSE5jiVPvZPYD24oA9UiS8lYzE+QmM/NyxHqT0xSShdhaNsr1LGsDTfE0GqO811MvlwttZFPyqR1JPYfWvNvGPxg8LWYeSGYNbWxIMSZ3zN6KMZwKAPWIpIxKJ5+54H061qLfQOoe3AdH4Bzx618d618Vdb1K3Gu64p02wKqI4i6xll7MxzkD1HU1ww+MvhxtU+zpqK6o7AhBA5hsrYEYxu4Ln1oA+3tW1qw0wJGXjMkp+RAC7E+vHAFePaz49ubjVB4dtkmkncZ8iLlyPcDgD3rhrbV/Emq+G31i6u4dNtIuFuEGBIh/udS35Ae9czYf2rBpI8ZabLNY2OdhlkG27u29ELYKKemTigD0mHV72GX7HYWyXt+p2mBX3PF6FvT3pmrarqFlD5HizVLKxm+8YUlyw/wCA9a+a5fjHNDqD6HotsumzysRLHbktIf8AbmlHT164rnL/AMQ/DTR7pIfE9wNY1qNTKJoXEcSjOdrStyzdsflQB7L5t9qhknsb6OS3ViXkOIwi+pLkY+ora0H4j+GLecaFaa29xeyHMcywM0KEDoWzyPU18R3XjrSfiJrjaL4Z0+6W7Y79kLPIj47O7YAUe1d7bzeJvDtkYNX16GS4lXYukWSIz+oEr/w5HuDQB6d4717xJf6y8d54xlL7ADDp6MI0Tud+4rkVwFx4iuFC3CaxJfWownk3syv5hHU4GCM9q4yLwz4k8Rx/btT0l9JjDeXHYxXJVZR3aTGGX6HFV7nwx4j0m5Gn6ZoMV2sGB5j5jjXd6SdSR64oAXxF46s7m7fRbwCyhIDHU0VmkVe0Xkgg4H972qrqD+OruGGPSNS0rWbWVcxzNIba4hQ9SVOSSKj1DTPGdrrME2grFpU4YN9tunW43n+4oYYAHTIr1vUtB8ceMpjDf+HNPvhLCEnvrlRGCR/dx+hGcUAcX4X1v4weB9bimsrvU9SigG9ASptHHdXIHGem48V9Cab8XJzqtnq99q8ehS3QOdPlIuYy/TIeJQV9s8V4tpfwy8R6VqsMcPimSCNDtNjbXDlVz0DKxKle3IFQal4g+JOiX4tb7W9E8MFXMaR20ayXFxEOd3y8bifUUAfo34e+IT29nFDr8sSPKxCMkqMsgx1UdR9DXpOk+IdOmuTFbyNIcZIwAP061+XuhfHdvBdrLDexW7XMkhLXssZJII4KxKvX6fjXrui/th/D2wKaZ4s8TeXcuA0Yt7bbIcc4YDdxjpmgD9G0YOoZehp2U5Rz9a+SrD9oG0uLPTdR0vTtS1aDUsmGZFCjbnBLqcEfkK9d8MeNtJuoZDcRvYmR9oW4dWcnsAATigDu9V0XStVt5NNvolnt5kKyRSKHjcHjBBr8hP2vP+CS/wCzb+0D4SvvCnifw7HeaLqO/wA+FFxPauxyJLZ+o25yF59K/YCC+zGGdCFHGSDV7fFInyj8waAP8jL/AIKsf8EP/wBpD/gmx4om8c+G7S48XfC+7dmttWt4y/2dTyFuVX7jAcbsYJ9K/FW3ktr6I3Ngxde4xyD3BFf7n3jT4beDPiN4Pv8AwJ400q31TR9SiaKe0uY1eJ0fOQVYe9f52H/BdX/g3E8S/svz6r+1d+xJaS6h4SAa51PQ41LyWiZyzxY5ZB12gHaKAP5D3VTnd24NVCqA4Bq7b3ialaGeFGDIcSKwwwb3FRBlz2B+maAIfKB6A5pNmOtWycY3d6TB5O3NAFVxz83SmDH8ANWnUkHfwRTQBs+XmgBVYKcnp3+la1rMdvIUkdTg5rIKjnd2FWBIolJTOD2FAG7Dc/Pl2YDt0q2r5ORyu459cVhwyEncBnb2q9CXxgNjIyP89qANFXkxg4OP4h6UgZgMMdw/h+lMAYLluFHH0NIGz14PpQA5pe1Mwp54/OhzhMY/GqJ8xSV9KALe5UOM0/II61RyT8x6irCOuWUjrigCUfNyaGIHBoAbblRkClQg/MCAT1z7UAPiOTmpgU3jdVYOSMryPypd3rQBOofPz9O1KyjdyearhVBxgE9e9LQBNsU+n5//AF6XAXiolIU/NSORxIp6UAPOS+QeKfxnce2Khc5wAKRsL8+71wPpQBLkqMdaJGzBc/8AXu4qFjJ0Ip2P9Fu/+uLfyrak/dY4v30f1Sf8EKv+SGTf9dT/ADFfaPx2z/w2P8MP+vo/+hCvjL/ghQrf8KKmOP8Alqf519ofHIH/AIbH+Fv/AF9t/wChV/lb4rq/EeJ9Z/8ApLP9GfD/AP5FlP0R+qHj0f6B4r/7BP8A7RNfkb4w/wCTPfhH/wBjA/8A6E1frv49/wCQf4r/AOwSf/RRr8ifGP8AyZ98JP8AsYZP/Qmr8I4U+16/5n1uL/io/SmcZiQf9O39DX0r4Q/5FLS/+vSD/wBFrXzbKMRp/wBe39DX0n4R/wCRU0z/AK9If/Ra1/VXgmv3Nf1j/wC3H4X4k/xqfz/Q/9X9RtDs91zPH6Qt/wCgmvzTugqfsVfE1R/0M0Y/UV+pHh+32Xtyx/54N+gNfltqTbP2MvibGOf+Koj/AFxX+KcXfGNH+nmWyTpJo+9Ybbb+xxcP6+FGP5w18CfsJ/8AJG9NU9N83/oxq/RdLcJ+x1cDrjwoR/5BxX50/sJkH4NaYD3eU/8Aj7U8oX7ub/6eR/U9KvUVn6H4Kf8ABaN1j+KGmt7t/M1+Loxziv2W/wCC17MnxO0wf7TD9TX4zrwuPSv9UPBZWyCi/L9T+BfFyaeczX9bFK5eRCcjiq7FgufWtRsOMPyKqmPDYP8AEK/Wz8rKOMpnvTMEdakZSCWFR5YjJoAY/wB2qskmBirT/dqjKDnJ6UAIJW9KtJIcVTAbjnirSDC0AaMDlWBPIrq9NPlxEnp2rk7ZgTzXXWq+bBsRgpoA2rd2cAYycU65hv7vydG0WF7nUNUP2a1hQFneRyF+UDk9QKoNPFbxESMAqKXY/d6ds989AK/qn/4Njf8Aglbf/tO/Go/t1/HbTceDPCD7NFtriM+Vc3i/8tMH5SsZ6+9AH9N//Bvl+wN4l/4JwfsG21l8TmMfizxrKNXvbUYxa+YoEafgmN3vxX6G/F/4h3seqArMPLXgqf4hnPPvXtPjrXRf3MsNm37qNAoCn5VCgY449Pzr81viR4oc3t44m3tDzlug596AMn9p/wAN+B/2nPhTL4N169+wajbhpNN1BT++t5RyoJHOM9R0r+T/AOKX7Uvxs/Zn8RX/AMHfitcs6pIYrXXIGLRSjnAcjgE4FfvH421jVtDuL/WTPMirCWkYZ8pgQcBR3/AV/P5+0F4Lv/GPhzULrxLC9zZyuyNBnfuLcq4IyUNAHwtH8db34YfGw+NriYLovjFfKvRk7Y7leVlGP7wxzX0FdfHb4j/HTxz4c+BfwzZvt3ia7RWaNj8tpC3zyH0DHnNflx8X/h9qnw1026n1C4m1fQGRInkGd1nKzfLkN1x6jtX3d/wQ+1Cz8T/tNeLb3WrkXV5pllHa2Fy3LRQ7igZMZx0GaAP6RPGXhnQ/A2k6J4b8Ns9vaaNAluzxNtaWXAyz8c8k9e9fSXwe0DXYL1HWGC9uZ9pbA8xdjjhuoG5e4xkVwWr/AAu1S21qJ9khX5nVZcsJ2BySp5A617B8FbS80y4itUjilt5nIBGR5MhbBEueij260AfrD+zJo0ujXWkwO2+UzOxmjOFYhTyRjHfHU9K+OPDfjXUIf2x/HWm38YBS5d3iGCIycDzVOe67c193fAiPUNNjuda1e6TytJtpmNvFkJ+7XKyf3SCfzr8i/gmPE+s/F/xD4rdRc3+sXjZ7N5Snec9upx9AKAP3L0DXp/DfgvXptT4hjsZHWcsPmPlscYGemK/O/wD4J32jy+E7jxexVH1a5eR44z/EXILfXHWug/bM+P198F/2Mtf8Z2iRQaxcw/Z7S3bBMrS4hO33G4nPtXhP7GHja1+Gnw1srC4kWO6tYLdJ9xBDSXAEhdcZ7kg+mKAPv7/gpxrknhn/AIJw/GG/hUKU8MagAW94WU1/Hj/wSU8WeJ7j9mewl0iSNEd5S7s2Cp8w8j3r+m//AIKy/HPwboP/AASl+KWveLL+K5tdU0yfTbeaJwQZrlcRr167iARX8V3/AAT9+JeheD/gbotu0N1PdBXJhiyFy7sQSMjPGCMUAf3i/sZeMNP0vSoUjuWmklAWQuRgt3IHTnPqKxP+Cq//AASr+Bn/AAVI+A9z4L8c26WXiiwiL6LrUYAltZ/4QTxuRujAnp0r8nP2Tf2ooNK1G1s9QlC27bSyhTmM+5OOa/pl+HHxK0vXvCNprG8FJ03LgD5lA6kigD/G3/am/ZG+PP7Cvxx1D9nr9o3T5LHULVz9jvGUiG8hyQjxueCrAfh3rw6CGRGO8jt+tf6mn/BdT/gnD8N/+CjX7G2ta/pFisnjTwfbz32kXsC4ldol3vb7upDjgf7XOK/y0NPWcQyafqOY76zla3mjYHcHQ85/AGgB7x/Lx/n9aiAKHK9K0hAxOM4o+zM3FAGZJISR1pV3A9zV82mGyfSi3iG8g0ARKjBdx71ahU5Gae9tIH3DpV2G3fAcjFADmD/LtqfYF+Zu9X4Lcs2OvFSmJW+WgDKyQcjir0Mi7eaakPXcelVZHAcAHj1oA1FuVWIITVU3e4kjjHrVEyKfvfnUJlQ5wOKALE03m5A6DpVOcNxGuPrVfzTvznj0psk5WPYOSaAGNF3HI9qhK/MB2q6qkx8HHGaquGRgWoAqiORxgYFVLq6t7Kya9n5CEhR/eYdFArTVWdwE4+lfcX/BPj9lvVP2r/2jPDXhY6ZPcaBHexJIQjFbiXzOYxx3AyeelAH77/8ABvR/wRp8TeP9Li/bi/aKtW060vmH9k20qfMbVesqqQMbugr+ye5+I3wv8B6LL4suJo9J8K6GDDYWcRCi4lTAZ2AxkAjvXC/FOZfg98M9F+Cngu4h0zy7dLO3VB5cUUMSgPtA6kc/jX48ftM/EJvFSWnhS10zUZ0sh9m06zQMqu2cLNIDgFCQck9cc0Afpe37d3hnxNNc6bG7WWm4zHGOJZ+wHB4B/rxmujb40aVp+jJpPGn6hqi+fPEOWtLOPojHIw0hOeuTX5HfDnQdD+GV4niDxdrFrq+vW6/abmVSJIrbHEcEK4CeYCRnnjHQ1B4g+OvgKOa9vJb57q9VvO1N4pBLcXLOcKnynau0D7uaAP1ovvjnNJYma5mWG2zst4Y2y1w2Bg8dgOp9eOa4a5+NfgjwdqD3V0y6h4oMRa2sxykQOMlh2Ydsj271+Yv/AAlnjPxM5/4Q7TZdA0dISY9RvyF8rC8DcxCqGPXGTz1r2f4K/s02GsWVx49vvEQk3k/btanZkgSNcFkgLnLlv9nPQ0AWPjJ+0V4s1XVotM1UzaheSv8A6NDbqzb2HJDKPlXHAxk4rW+HGl/EXVLy21zWNPL31x8yaTCTsRB3cgDk9xjj1r1Ea78JvDNlBH8OdKn1h4yVtpzgzS5PzGMsRtU+pPpXV+HfiTpOqWc2m2l/a6Jbo4W7hilWW8XnJEkq8KP+BUAfR+j+OY/hnEfE/wAXdTj1rUWjEdho8GDBbDHG8fdyOleY3fxL+IPxD8QPqmqamIYHGBCeFt1HQqg4rxPxn4w/Zx8PXjXNz4ptprmUYCWzG4kJ9+qgmvJm+InwjiAe2ubx4ZP4nI3tjorckY/GgD6X1NfEFxNL4d0qBba2LD7TcSHE1wOxLDPy/SqOi/DPwh9nmtbqG41e43iQw24IRR23OecDr0rG8FfGfwbretwRyafeazcjCwRx8hQB0booGO5r6Z/4SfUrq3NlaeRoOnwACWKzAkunz1UyLxk9OtAHAW48eabZSafplrFpGnwAm3SMgzTHHOTw231yK8v0/wAaXevajJ4FfR20LVH/AHst8FDRSKOScjBBA68/4D2S7vtF0XUo/E0FpKhKskRud0rqp65QZ6+prI1LS9d1UwnSf7MtoJXDv9oBaWTcBuUFc43DtQBu2d58ONN8ODxRNrjahqqD7PIUZtreuVYtzV1/GF/osH+iR289s0O+2jiceY7N/f3YwPrVfTfCHgDToZ7e307cwPmSWgPlh3/vIefl9iRWU/hzRNYlkvLhoYroY2JLMgQKPuqy8sNtAHTaHFpN3Paav4kuYvNkXDWkZDDcTnAbPBHcV63b/Fn4QeDn/s3W3kuZFBPlqHCA9gTu7f7teJr8OtCW13atd26cbh9lKsdx645Xp61y3iDQfhxDYCDRdV8+SI753ljbbgD7vysST16E0AdJ4y/aQtL+/ubfRfDxByBC6pgSRsO+ADu9DXm1/wDGGXUHju/DHhhJNSiAjWS5Qs6HPJGcY/Gk0bVbi1046ppNjqN9bhsIA6x/cxgxo5LkfhWprHjHxNcRxT+KtFi0mH70b3ciFuOrMB0wOc/pQBo+H7fw7rOszya9NIfFEMXmM2V+yRr+OFBXuK8/sPG1sst1r7S6TcXunNlGwim5V/k27sds8469K5qb4v8Aha8dtMtbae/0iIH7ReQKqW+7qRJI4X5T7E18o+OP2pPg7fa9Lofg3TdHk1q0BEdrYnz5MFSpMjL8i4BJOenWgD7VtfH7a3qUsPjDxvDpmlgrKdOsMCbyjn5ARyACOea+oPCXxo+GWmqlh4N01bvVFKOkk3z+YnYqScb8dc4+tfgFfeIYbmVdY8PXOi6DFIixyao7yTvHKxw6uqkjHuK+mPhV4T1T+0ks9K8QXvidXCSC4toXjtwO/lNxmgD95x8X/iXc39pHALcWrKGkRWBlxnHATPPt1r6F0fx3cTxssSPNHGu4vjJQ9wa+FPgz4ds9MsLaxs7P7PeSjEl5dPumweyKPu/zr720DTJtHsvsmnxZ3LlgxALlup5/lQB0dl4ogutO/tCVDES20bjjj1q1qVno/iXTJvD2pwrcW91EVlicbkdH4IIPavPNZ0ySVWm8RXP2oQOHht7YEAkchSB1BqbRL+4i1aPcGMu1ndeSqZ5A/CgD/My/4OWf+CYlh+wp+0/H8dfg1p/2HwN45dpWhiXEcF2cmRBjgZ6gdq/m9ESgjyfmiPKt7Gv74f8Ag8K/a9+FY+Dfhf8AY5sjFfeK7u+j1KTyyGNtEAQpbGSN4PT0Ga/gptrWSz06G0PO1QtAEXlI4wB0qHySXCt0rTgiYruI46fjTmgZRtPWgDNaHcu0kcHj6VDsG0qFNaTxBXBI59KaF2qT6npQBmBQHI7MP5VWZSGwvGDzWrsC5YDr+HPaqyht5Dcnv9aAJ4tysOMjHDelXLfai8YJj5b3HrVVchDs+Ujv1qQEHk/xHK455PTOO2KANAEiMBucru+p9PrTyrY3K/8AwH1+mab5kWWWNgh4OeuD7U7zNwLggjPAxyPXj3oAUsmQGG2Nh8zA5NQeSeN5J9z6dv0qdS68IoAYcfSmEsqgMPw64oAaIQeB0XkUbUXKZ68U9iSvyUbVLFm4C8fjQA07z94gY6U8j5dw+8fyxSNtIxjd9KczKABnb9aAAdCOh6j6U1GYr0/OlwN3XtQMY4oAX5t+7FNk3AfL1oYvg0o+ZeaAGYy2Qc+/apFHzYPSkChfu8D0pQSD0oAkCiP94e1OkQHJ+h/xpAVYFD/FTmPAUc4oAZ/Dk0jgi1uye8TfypxXKbag3MbacEfeib+Vaw2Gl76P6sf+CFP/ACQef2kY/wA6+zPjj/yeR8LB63J/9C/+vXxj/wAELPl+A03vI4/nX2V8cHz+2R8Kz6XTD9c1/lf4qf8AJR4n1n/6Sz/Rrw/X/CZT9Efqt49/5B/iv/sFN/6KavyJ8ZMB+x98JP8AsYZP/Qmr9ePHnNj4sHppRH/kJq/ITxlz+x/8JB/1MMn/AKG1fg/CunMv73+Z9Zi/4iZ+mUwPlIf+nX+hr6R8I/8AIqaZ/wBekP8A6LWvm6RswoP+nb+Qr6V8IpnwnpZ/6dIP/Ra+9f1T4JO9Gv8A9u/+3H4b4kRvWh8/0P/W/XzRLY/b7r/ri38iK/JzWRj9jr4lqO/ieL+lfsFodsftNyT18lv5Gvx+1w7f2QPiT/2NEX9K/wAUYP8A25/M/wBN8qf7o/Sd4Cv7HNyf+pWYf+QhX5mfsI/N8HdNH915f/Q2r9Smhz+xhcyHv4VOP+/Ir8uP2EF2/BvTT6tL/wChmrybWjL/ABx/U7quz9D8Df8AgtfhviZph7gt/M1+MaHJwfSv2b/4LWDPxN0wDuzfzNfjOy+W2PUCv9UfBj/kn6Pp+p/BPi1/yOp/10G4wCtMY7hwOcYFTAetJsXsBX60fmBmldvy+tQMp+6ORWnJDuHNZ8iBThDQBCUPpTDb55q3DGGb5jVqWBB0A56UAZBt+O1M2kCrxidM5ANQmM0APiAXkVsR3gSMqvXtXPyhlOM8VG06wQvLIcBRnn2oA+i/2b/g14t/ah/aE8Ifs6+ELZp7zxJqMFs/lDcQjuAzN6Koyc9sV/sRfBP4I+AP2Mf2avDPwG+H9qltYaDYJE4Ubd8gUb3bHUu2Sa/iv/4NDP2GNK1jxJ4o/bx+IdorjRo2sNJ83BUO65lkAPcLgA+pr+v79oL4rzlbiK2n+Qk/u8fNlegFAHO/EP4iWWnaX9pnkEMc3AjU/NKfY9h2r4N8SaxPfXjakYxOy7vMRGB8lT/E5PFYviTxkuu25uJ50iijbbPExJaFh0ZQeCG6enpXmt/4x+2K2m+GrCK2gT5ZwxZy8g43DPHPcUAZvjC3u/F+h3MPh2SaVJMoL5V3YcD/AFSr2z0BNfht8R7L4j+D08SWL2X2adwwvLe5Uid4M8mPHyhvpX9Dvg/xF4guIn01kFnHeDE7JGBtVeFcKB175rN/ba/ZKl8f/DG1+MHh6NJdS0e3xebU2SXFvt5lwO4AAI9KAP4fv2r/ABJeaR4dGiwaXqMR1G3SCwgnCSR3EjHHzbeQec81+4//AASX/wCCW2n/AAp+BMXxJvbK51bxfflLq4azk8oIjDiMZA3ooPOP4q/Oz9strHwH4l8BWWiyR3l7PqaXgdxlPLXaGUg/3TnNf0Ifs/ftf6J4W+D+m2ml3JtLiyiBKAAEx5ySM8kntjjFAH2Jp1hqui2sGg+JEZpLhj5cUQZmhbj+NuvHXFeyeDdE0GPWorjXH+wWUJCMgTeZZQeroPmwT7V+Tut/t3eJL7WEg8GafNfajezGG3tlQy3DSdmTHI/Cv0v+BcvxE0iSPxr8bbjTfCenwRJJeXuoshION8o2uSA6jjJwPQUAfqX4i1GL4X/AfxP408QLE+mWGmO4hgG3fvQ4XJ579DzkivyH+AOqab4stJdYgDR2ck+wvcA+YoLYCoE9T09q/Nf/AIKOf8Fj9J+Omqx/sr/sp3LN4LtZ/wDia6wxIkvZEztCkf8ALJSCcDO7AwRjl3gj/goJ8JP2UfhTp3jH4nFtSk0hDJpumJjzL67A+V5B/cBHGAMDtkkkA9m/4OCvjZp3w78OfCb9mzR7yL+0rnUlkaFH2nyUQuXccnYx/Wvz5+EH7Vc1nZebJqgsLkyu0t1fS/6FaJHwG+b5mCr8wAHPavxm/ai/a2+KH7Rfx6v/ANoz4jWrXXirXlaHS7KQfuNPtCMAqp6HbwuTjnPcV8WfFjxj4z8RCDQLy/lN5eqoETMQI4QNqoVxxnB/CgD9LP8AgrL/AMFZ4f2pfhxo/wCxH+z3LK3gLQJEudS1GZcSapqAJeRkQfdjDn5A3bFeIfsheOviF4LutNuNP8A61qfkxpFHNCqkAAAAohBHbvXzD+yv8J9D8V+L5LdIY7jUYZGYW8h2jZjrg8kcV/Sv+zZ4C+Mvhu2X/hFNJ0SR9u0Es4KDjr2Uj2xQB3vwL8XeIPFuqxT3PgHxlqEpYNJBNJHZxbx1VmUZ2/jX9IX7MPibXvDWgRS/ETTrLwnY3key1sxdvfXB9BIeQtfjha/DX9qHxRA0fi7XotMtjtSOPTj5RYnu0n3jx7mv0w/Zf+Gx8A6NFomoTSX7SShvPuCXcyAfd3Nk4JoA+6/jb8bofgf+yp8RfjTq6wJYaDpdzPbwsMCSRImILZ/vEAfjX+QyPEk3jrXda+IdxGI59cv7i7dEGFVncsQB2ABOK/0JP+Dm79qGy/Z5/wCCe9l+zzpF4I/EvxAuFXyI3HmmBTmXK/3SflGa/wA+fStHk0ixgsZR88aDjtk9fyoAlSIMm7aT7daGQjqCPrWkEYU14y/XmgDJZMnio0hQNitVoQDUbQjGV60ARpGWXb2qxChACtRH05qwuAxzQBNF0Ibr6+1PwAwxUJlGMD9KczjAPpQBEfn3ZrHlUFWHpV6WXPK8Y61kzyOzZUcGgCi9wwO0VXEz4IHFWmi3SBgPmzyKYY3EYJHegBkYduSKtQ24d8txUkSOh3N8qt0q6ieZ909OaAKpXBaL9aqtGWcY5rTCguQe9J5QHPT0oAx7yCQW/kxHa9yRGp9yef0r+/8A/wCDcH9mnR/h/wDBNvjD4i0/ZFo0O6CS443Xco5ZM91Xofev4fP2cPhHq/x+/aN8E/BfRrd5ptY1CJWVPmwpYBs/gK/1kYvhX8P/ANmT9l/Sfh7pNulvZafaw+YoABnmCDLPgcnI70AfLvxVuNc8feJdT1eyhKPCvlwrIRsigP33z2cnGPWvz2k8P+PvG3i37J8PnGp6nbM8N49w2IoYFPQE/exls4r7/wDj1reqaT8Bre+05/sWpa5KLq5YDkWyEMAfQHGPeud+DekaZY/DcfEu4iSPU9XEkMMQGDEvHmSORzlieKAPzr+Lvwk8OX2iDwlpkUsml2twLxt7C2gmuVb51RP9ZIAePQ14H/wrDwt4cuL3UrTT9N0W7s333LXbm4k86QDbHBAnylyMEZORX65/E34feH/CmmP8YvF0EX2yKzknht23NFHbInzMAejscYPvX5U+IoJ/h54XsvGGur9u1Jo5tStYcbhJqGovtgQk9fKjGaAJdMvNRsIri28I30/jHWdOQzalqOt4i0rSxjcVS3HLlFwOlfnjrf7WXxR8Y+M9X8SeJPEMmp+HfD7FTJAphtWZRgJDFgAZJ4yORmvqz4yeJLP4PfApvhT4VmLan4g3Ta3dyscxySgs6u3UAcgV8t+DfhG8/wAL7BPse/S2mX+z43XBvpznM0gHVQeOfUetAEVv+0bqOuIbmG21LVJZyojBkaCBUIyUEajJPIGc1v22qfEv4gXX2J45bS2DBX0qwDIhHrNJklmHua+l/hl+zlHfWkcM433EIMs7gfLkH7iKOgHT8K+6vhp+z9cW5gfT7Q2sVwVbah+b6k+9AHxP8O/hvH8PEFhf20cktxh7iGVfPmRe20ghVY9gc4r6i8C/Crxbr9/58gjsNMn+WCGRfNldW6ZVQFQ46+lfoV4I/Zb0vS3Ov65F5lxI2VTAIXP8Rr6L8MfCGw+0ZhjDk4GCB26flQB8jfDX4P2lldf2bp+9owAJ5CeWz2AHQV9jaD8ONHs7FY7nd5VvwkMfCt3yx6mvdNB+H1tp8JFrAvmt1OBXRzeBL25tgpPlsfTjigDwoXel+HYnuI4xHKVO9osbCvTkt1ry608VeALyee20jTkjaYkS8sI3IHLYPP1xjNfTuofCMarZvbz52NwfeuBl+EWnx3QjgiAaMbdwAz/KgD5x0678NSax5lvEzwQ5RJYz5UIY9N6MS5H0rckbwSoa38Rvp0zxtyyKTLGT/CZOmD+de4X/AMIdNntl/cbZFA2spwSe+a8L8d/BO0giby4ZlMp3SNGvDEdC3rQBz+p2nheZRcRf2ZDKCfKnnfzkjA6EqPmB/SvM9d+JugW6iOfxZokU0LbC724AJ/2NrDH414Z4r8GW1hfpJINStTvYErna/pkdxXkniv4K+E/Easl4J1uJDuKpGowfWgD2fxf8dfDdnrH2tdZsr7UFXZG9vGUkA9nZ9in3Bx7V8x+Kv2htIv7qa6/0F9QiHM2oTGZyn0BC4B96Lb4DfC7RZRHq1teaqZAxHn4UI6jOOO1eX33hj4SaLrSyW/g83UknLG5ywGByFyelAHy38bvjb8LfF2mt4f8AG2pav4wDEk6fpsn2HT1J/gIX5mx6187+GfCvijxmIfC3wc8GXmi6XAd7T2wFnAwJyfPuLg75MdyBg1+geteI9X0wSN4F8H2OliPJWRIUkl/DIyPwr5d8SwfFvx/4hXR76WfzLtuRGWwqjlsrnA+UGgD9W/2E/g38FdNiHhbxJqdrrN3dkx3NkqeZbRuw5+c8Mfda/eLwT+ztoXgfToNC0pf7OtIT/oRgCtFHnnGOoB96/ks+DfifUPh94vt7jQJDbsqgKmSRlOrYz1OK/rt/ZO+MNt8YfhbZX8vMqQKr5OSXXgk56ZoA9CsvDVvotyLXUjB9pb7skafMT6n616LbW5mhVbht8v3Sx56fSqviFfKmimXgoM/hXnnxP+M3wz+Bngy98f8AxW1aHR9LsIzLJLI4Hyj+VAHqiz/ZSVwqHvxlvwr8zP8Agpz/AMFIfgd/wTM/Z51j4oeMLuKbxHdQumj6UWBuLq6ZflAUchFP3ia/DP8Abu/4Ouvgh8LdDvvDn7LGnr4g1xt0cF1IMxq2CA5wRxnnHP1r+Ff9qT9qf45/to/FGf4w/tD+ILrWtQuHZ4oZW/dwqTnCJgBQOAOPxNAHG/HH46/FH9qf4069+0R8Z72W+1zxBcvOzyEnylYnEaZ4CqMAAcAV5s+JCCexyKsBY9gQLhccUzHynIGKAIAqqSfXpSNGWGKe2NgI96YGK8k9aBXInjOcVXERLYzirrKzPuzTPLcjgZOe9AyqYsnFVDHg1olH7VWkWUNxQBAVBGDQy7/vemD2py788jNSfMeMdf8APrQA6IBPnHJ6VaLMRkDn3qrDG7ZANXDkrQO2lxgPUt94c/h6U07sFgcbhjHfNOIP3gOR3qMBVOCd0mciglO447DhOgp55OaibymG4njttqZdxXBHTvQMQ5wQnBPTHepEZ1yWJHtTBlPy4qIgNGoZtuOh7fQ0AKApJYCnoAOCMAjIo2Ptw3yt1/8A1UhOSvOaAF3Er0pAOOOKcRg4ppPc0AL7npS5OMGozkSbOuRz9KVwzDI4x39aAHYxSuSvzCmHIXPrzSjlQp6mgBY5Hbg0kp220uP+eJoPAJFMl/485j/0zb+VdEI6D5veTP6sf+CFQL/AWU/9NX/ma+xPjaxb9sv4WKP+ftv5mvjj/ghEzH4By5P/AC2f+Zr7C+NBP/DaHwuH/T238zX+Vnior8R4n1n/AOks/wBGPDud8tpryR+sfjz/AI8PFp/6hhH/AJCavyF8Z8fsgfCT/sYZP/Q2r9ePHvFh4t/7Bh/9FNX5E+M/+TP/AISf9jFJ/wChtX4Pwvq3/i/Rn2GLjaoj9Ljyij/p2/pX0r4Scjwppg9LSH/0WtfNjdUH/Tp/7LX0h4S/5FTTP+vSH/0Wtf1T4H29hXv/AHPyZ+G+I38aHz/Q/9f9t/DyYmu8/wDPu/8AI1+L+v8AH7H3xLH/AFNUP9K/afQY28+7/wCuEn/oJr8W/ESn/hkL4mL/ANTTD/Sv8T4P/b38z/TXKX+6P1Qlhx+xLcE9/Cjf+iK/Kv8AYTbd8F9Obt5k3P8A20av1guxt/YiuM/w+FGz+EH/ANavyc/YOIb4H6WB3eb9GIrfJ9KEn/fj+TPRaupH4H/8FrF3/FLTCP7x/nX40SjDkV+zX/BaZT/ws/Sh6M38zX42mLJya/1S8F4/8IFJf1uz+B/Fl/8AC1P+uhUwaUAggmrgjGOlOaLbnd26V+rn5iVH5wAe9UhCcncc81ab71G04zQBEi7Rig7c8in1GSATQBXmkJ/dgcUxlXcpzVgqpxSoE3euKAMydQJM9RiqWsFItIZk6thcnoCTwTWtPBuO4cVl6xEiWMaNyzyoB/WgD/Us/wCCA3w3HwJ/4I5eEjqC+VeeIzJeMehCT/MufcAcV6/8SPF/9szzzylQ8jDZgZKlAcMfrS/sAC98Mf8ABJ74Rw36b5302B1i+7uTyen414hql0t7dX2xmQSsFMXJbn+EehoAqTan4TvYJW062aDV1ZvtNy5xDKmWGB833vTjrTbKC5kaNtYZVgjGbaFeHL56sOoFWW0aM/vWgjktYEwY8kHdkEu3bnngVwwtNQXxCus3UTx3M25kgT5uCc/NnPTA5znB6UAfUnhHw7pt/d2890u8ScuOcNt6Dj1r9APA9j4X1fw8/hrV4xNC0bQtGpJBiPBXn1HFfHXw70Ce+0gapNJGkCJGHKtkpI3QH/61fT/h+xksbOEK5aQIWdl60Afy9f8ABen/AIJb23wy8O6N8fvgcZLrSk1FUKoCTYiYkspxn5C3Q+9fnh4K+APxT1DwBBqltclLFdlvbO+TI8jYAwvp6t0r+8jUvCvhP4oeGbvwL8RbRNQ0TUYDb3VswySGHDg9ivBHvXz38Mf+CcPwu8NtqrazezavZ3dq1hZuQqG0hKlBIR08wKQNw7D1oA/jr8W/tH2//BPfULay+HltH44+MesRBHjTa0GmQsOQXXIVyOCB2FfB3xvl/bt/a+vrvVfjd42/srw/bxfa7qwgkaO3iiHzFSchWc9DzzX2F/wU4/Yu1/8A4J5fHOXTfAdnN4r8HeIZDONYt2P25pGBYwM/IABPUdR1r4R0/wCGvxo+KOoW2s/Gq5NhoNgEa18N2W7zJVJ+Rrhh97rlgetAHR/s4fAHSvihrthYfC/xD/Zv2ptkdzeqRHHL90KwzuYEjIYV9SeLv+CSn7c/9tX2radd2vie/tyRE3UEYyBEX4xz271+lf7AP/BPLxj8TviHpvjTxSF0TTRCBHNNF5YkTkBYoBgjA+6W7+tf1jeC/wBlD4K6Dptlpkcd/dyaeFCzTXLq+4AfMNhUde2MUAf5p6/8E4v+CgcXix9L8f8Aga7s7aVhI8yn5tqnDbSMc45x3Ary7xV/wTw/an8MT3/xCs9Hl162LbVQI6z7V4O1GGCwHoc1/rUTfDzw5q2npFImzZgZCqcgDAzuB5I75rzPx/8As96Fq9gj+GIbKGeHJ8q4t1eGTpgNgAg/7Q5oA/zIvgf+zB8NfiLpUFtYxz6XrNoVSS4GY7mA5+dZAOdoOeor9tvhH+y543+Euh2ra34qbWbYjKLbuTIyHBwcqOfxr9rP2zP+CV1n4ktX/aK+A+hQaB8QtIy1/Y2nNrq8KjLlV/hkI5H0x3r57+D/AIL0j4h+EoxZxSwXyMyT27ceVMuAUc9QeuPpQBofCP4c+IddtF1DRmaxQAKIpGLOwAxniv03+DHhrQ/BGlTax40mAs9Dtn1K7llPyxxwDJYk9D9a82+Fnw5uvBttDC1rIrhfnz029+P61+af/Bfz9tTT/wBjn9gG8+F/hu6aLxb8Vm+x2rAlZIrNRmViBzgqdg92oA/ja/4Krftu+Jf+Civ7dHij4w3czf8ACOaBcNpmiQE5QQwHCOvu2Nx96+C1R5WMsp5rA0Sx/snT47AZLcu7dy7/ADHP0PFdDEWIxQA5YhnIq7DDG/DUxUAXipYdwUlSfwoAkayh25wazpIFjcleorV2u65Jx64qq6L0Bz70AZrgydaiki9KvMihtp61QuGkUYWgCk0fzcGnl3UAE0wMCMnqKcu1hk9TQA1mJGTVRf8AWDdyKvYQ/KOtVdh3nHrj8KAG+RGf3gByaURqDxkH3q7Eihv93p9KsNF5hIA6elAGKiFeX5FT5wQyflVt7RkXBzUYgxxQA+LIzu9KsJEZtqP2NQpBt6mmzJJtZIFZi33SPWgD+kT/AINcP2Vp/jH+3Bqn7RuuQ/8AEk8HwP8AZmcHHnMDtx7gDNf3H/tW65FqmjeHfD96S/8AaGoIwCehYlVI+gr8Uf8Ag2V8C6F4E/Y/v/FNgkTuIybhlxuMzEkhj3wOK/Q743/ERNd8U6bfwo0k+mSSultGNzTHBA2jsVJwKBpE3xvtbz4qeKG8N2+/7Bpe0+WnInihB/djHVc5z6Vx0Piq3fxjpnw28OwhVeIT3G04SOKIf6tfVuK9W0rxHaeFvAWq+Mi6SXtyscVqAAPs6ScsspP8XXP1r85/DfjzSPG3xN1zxJo11d6BZ6UUBKDej3Z/hG75lUkjIFBp7NHr/wC358ajfeD9N8HaXEfN1qeGyjGf3jfOvAHXJI/HpXxr45Fr4t+M/hX4exyLLpGiyie4JYZWaziyVYf7bfdHoDV34u65qfi/9pXwpd+MLZxqtjE95BYoQId8XEc0meAG+9T9G8JxaL+0Npy+I44/PurcSSGI5aV7pNzyH2T7o+tBMo2Pzu+L/hy8+I/i0+GbrO3VLw6hqezOY4C5aKIgchm64Nfq3oXwK1AReGILGxdWktlWzt8Z8i3Ucu3bcxxg9a8w/ZY+DVh8W/jn4m/tZmGm6DfyX9/Ii4Z5EJKx+m3aNoFftr+z1o1z4l8TXni/XtOUwzERWSDrHEnCDHQDHX3oIPMPhB+zJqRs4hd2wt4A+8qcBmHqfUk19xaL8KdB8M2xkeNZZG6H0r3Cy0i2tIF8kCM45XFZWsHYuxuSaAOCXw5aTMLm7AOeNq9Me9dDa2EFlF5EKDFQ20wlfYtaA8zIoA6e2eJAUCDdiug0+2E8Wyfqe/0ri7PfFOXPINdFf6/b28At0wCRwR1oA2ZIIpIzIpG3pXC6xoUUrbozhhyAO/15ryXx98YNO8ExS31zcRyRxjLorgMn/AeteM+Gv22fg7q2rf2PLqJE78NcEjYuei455oA+gpLm+hvza/Zw2z72fQdK0Wm029h/egAjplf8a1tC8aeHdStUvIHTysZSUsCHHbH1q/f6RputZuLRxE5+YN0GD39qAPF/FHgvTryKYXtvHcQuM5IAYfTFfLPjD4N6bBpc2paeoXCnZt659K+mvEHivSNIvpdElvFle2Y+Zg5615B8Q/FltZ+Ab3XLZx5ag+WduRv/AKUAfMvhj4UahcWkjaoFjYZeNR9/cOuR9K1dR+DWg+I7OK78oedE2VCr87N6e9a1h8RLO30rT9cIYajMoWYN9wrnBOB0r2DUtd0/wV8Y/Cej6Uge38SMqvGf4SELMR9aAPiPXfglYWmoifUyAly23BGMMO31rtPDn7Lvh6aQxaeFEjEG7dio2RHkhc85I4x719Y/EtNF1jUtTjgiCxWbsIww5DAj5q/K74tftE698Gdbj1KzmNxeSuFlg3Y3RE4Bx2oA0v2mv2MPDfhKx/4TDwcjKkf+rYKQQF5JI9/WvpH/AIJafFXy9W1L4Y63Js+2Zmhc8ZbA+X9Oa8X+HP7XOnfEs3HgfxgCpdneF+sSlh/q/c81znhzRL74d+M4fiD4UcRTpOhWNcjC7vmz6ZFAH9G/xIkuLPwBqksDKl0ls6wyEgASbTt56gZ71/kr/wDBTz9v/wDbe+Lvxq8Zfs1fG/XLnT9I0nUZM2S5XeiNhMHqylQCORkV/q9XFtB8avglJY+btbVrHbuT+GQjhh3yG9K/zIf+C1H7Nvj+z+NmqjxdpzP418KbtsqJzqenDJDn++6jJPcqfagdj+fqHR7O1UeXHl+u9+WNWOEOQN3tVuK7TUIUvB8u/t6e1NaHf8y9BVKNw5WALyj5hge1KM/xcVLsEC7pDjPrVZ7+wUbnmT/voUW6WDTqKY2JYg9aYIn2YzVaTV9MjyfOXHsc1F/blmF3Q5k+gNJ6bmsEn0LvlsvJ4/mfrUqQ70LZwQam07SvGXiCQReHdEu74k4xFE7n9BXvXgz9kX9sDx+oXwf8L/EV55nQx2E7D89lcUsbTV7yWhTw0uiPATbkfKx+9x+FVnhLvnHJr9TvBH/BFD/gqN8RFjvPD3wvvoVYhf8ASkEJ574dgcV9aeDP+DZj/gqP41vbfT/EOl6f4dE+477i6jBAU4bIXca4KnEWDgruoi6eDqS2R/PuRt4fp2qF7i3j/wBY6r9TxX9b3gn/AIM9v2l9Tja7+I3xO0bTrdBk7UmlwO+SAoxX2d8If+DQj4FRj7R8Ufis+rQ79p/sy2C/MOSu95HHTnpXmVuOcvpyalI7KGVOUbs/hLuNU0mAgPfRknsmWx+GBVWLWLWQNKqu+D0QNzX+j94D/wCDZv8A4JT+GJ4ri9bxJrgVgFkeaNElYcEKqw5I9cV9w6T/AMEZ/wDglL8H9Jh1O3+F6asGkWMfbnklIZjj7q7cAdelfO4zxXy6N3T1NoZBXk9Nj/Kshm1C7j81dNvPIzzMUO1Occk8AZIqQlI3MZGCPfr+XFf6dv8AwU8/Yq/Zj8If8EzPjB/wqD4b6V4av7DRJpIZoIUMhCbWDI+MjGPrX+YB4dic+H4iR86zyR59gFPP519NwxxVSzOjKrSWxzYzLpUpcsjURgGjk+6SeAPmBz6+lS+YFHA69COp+tSNCqAonQEHPcVG6hgFPzqpOMcYr6tfDc8xkIuFOcDp1pwlXcMj/JqAMAwOQR+X4U2RThl+6pOSvcY//XSETNKgcpsJPQj0pROsalQcbemaqszdTx0IPtTXlyNxA5NAFv7SrAgDJqZZVGeOorL3yEcNyKlRyU3MfpQBdSQNhV4IFS/N35qmjADP607zSCMHjv8ASgCyN27IPFC8thqUgDp0pKACoJSPskv/AFxapgQRntTJ1X7JKR/cP8q3hPQl7o/qt/4IQf8AJApv+ur/AMzX2L8ZQR+2f8Lyf+fxv518ef8ABCH/AJIJP/10k/nX2R8ZRu/bR+F6/wDT0f51/lb4r6cRYn1n/wCkn+ivh07ZdD0R+rXxDI/s/wAWj/qGn/0U1fkN43+b9j74SbeceI2/9Cav2K+I1qP7J8Vsv/QMP/opq/Hbxb8/7HvwmVf+hlf/ANDIr8F4XdpP/E/1PucWv3iP05kjk3KcHm0OPyr6N8IxS/8ACKaZ8p/49If/AEWvtXhc0JEUTf8ATp/Svojwlx4U0wf9OkP/AKLWv6n8D5Xo1/8Atz8pH4R4iO9aHz/Q/9D90fD8R866/wCuEn/oJr8TfEgP/DI3xMH/AFNMP88V+42hxD7Tdf8AXvJ/6Ca/EXxMmf2SPiaPTxVD/PP9a/xNTtjvvP8ATHKqi9mfqdfqf+GIrvHU+FH/APRJr8k/2DSf+FI6V2+eb/0Mmv12uY8/sTXBP/QqN+sBr8jv2EPl+C2lgf8APSYf+PV0ZQ/9nk/76/JnfCpfmt2PwR/4LTBv+Fp6WPdv5mvxyyw7Zr9lv+C0wz8VNLx6t/Ovx38obypr/VXwXf8Awg0/66s/gvxXf/CzP+uhV6J9aHU43Z6VYaLt2qKX5QQK/VT8zM53AOcUwSKQcUjoXUn09KrR7h70AWGYKhqsrbhmnsSRtPekRAFPtQAJywqQ4QkjmmKNpz2ppyTk0APL5U7sDFbvhPwrN43+JHhbwNCjFtW1CGEY6tvdVAH1zWFH97png/yr9Hv+COvwfX48/wDBUT4ZeDrmL7Rb2V/FdvGRldttiQ56+goA/wBM3xp4f074Nfso/D74Ww2oxo2h29vHF93E6Rqgz365r4a8OZj1y706SZI4ziS7lcgh3PRYzyePavs/9vr4lR6b4o03wbCqopSKLzCwxGG65Hqa/IvxPr89kXsLdy39nN520sQWXrge/wBevagD6l8aavaeHdJWC7vTP5WbhIRj5M8AjOMkjt2rwDSfiTbatcSXFv5xRyXMnKkopHyjH3c9MjqBivlLxv8AGbXpNQSPVJAIrlN9s/YBflZSDjoc9cZAznnFdR8LvH0HiLxAbYvHb287ec7ggh5ASBGgACgYB7+lAH7CfAHWtU1URpd2UcNtMoaCMHcwHQM4PUivufSNLW305LeGUztvJM2NpIP8JHtXw98BZLaK3F7byiJCfkzkkOf4Tx0/GvunQr7zYmjuE2GMkMOxPqMetAHceH4JYblRGNuDgDAOc881v+N7sW/g+9hIKiaEqwBxj0xipvh3Bd6h9qlv4fKELDyyf4hir3jTTlurL7N/CQSM+ueKAP5j/wDgpXp2tfHz4xfDr9n7w/AGgs2aWSQ4Plq2Ac8YyMfd5r9Gv2Qv+CevwX+D/hKYeJLRNe1qWbz3ubhFIJz8ilTkYWtH45+Avh74a/aa0LUlsfJv3iLXU5PDBsbFUdjkHJHXpX254P1q0sWWOEjZLhmHYAjFAGvpHw00XTmfWktYoNRRSgMPA29jjpmvYPCccqwhZm+cjmuP0u8tr1isbYAO0HqSBXfaa0NrFtBGc96APSLG7XyPJbtWgjq4O78K5GxuopV2KQW71uxzJHwxyR1B4x+PSgCxN5m9Tb4jUHknkYPbn8x718IeP/gh4Z8H/FN/EWhW62tr4jIacKcRi5GcNx03DP419u3eqQxNgH5R1Pb8q8k+JeoadrOkyaHeY2FdwcHDIy8qw9KAMPw94YdofK1AokMK5d+6omeQfev80r/g4C/bBtv2y/8AgoPquneGJC/hrwIDpVoq8xsYSN7jsNzDt6V/dr/wVM/bZ0P9iH9gTxR8aIrg23iLVbGTTtEjkPzSXEqmJXAJHQZY1/lcxXmoazd3XijW3aS81SV7mYuSWLSMW5oAkEZBBJzj1q8nHFQ+Z/dHFSjjmgC3HnoamgYfdNV42GQW71PGyLIVXn60AW1YqSrdKjIiQHBz6VRnmkEm1ulUppyPuGgCxKHL7hzVVm5569KakhxnPXtSNk896AKbKoY0DAfg8VZMIL8jrUgsiwGOPWgCvEPnOaJIieVq2sODk/SnhADQBUWILkjrirAkIPA7U7Yvf/P605lTHynmgBxDj75zTo0U/KOtR5cqCacmQwajlb2NIxVh3lg9f5Ve8PaPe+JfF+j+CNNj8651m7S2gX/adgv6E1WLAnmvo79izw9N4u/bj+Evhaxj+0yz65asYu5HnL+n9KCGf6Ff7IXwQ0n/AIJ4f8E+dL8JxOTrWowfbroZ5YnaSf5159oOrXGo/E7QJ7i6eAvdtdJNg/8AHsieZIp92Y8Cvtb9t+0k8O+BbjX7hg8Gk6YttFAgzmUgYFfmH+znJrvjDTbDxXq8+Ta3NzHqRP3UiePd8pPooxn1oCO59F/FrxzpifA60+yIYbjxJrU16EU7nATITK9ht6+hINfDPwe17VvGnx81GxuCAbpWN0sXyxjyF2iRscFmI6+1ex/Hz4k6J8PPh3psN/bpA2pvI4hVgZvsrnA8nIOHchQAOtZX7MVjHb2Or6hr1o1uDDLNbw8LNEr5CiZyM5746UG5xdzpFhrmu+K79oZLlrTT7oB5GK3CgMT8rHkAAfLXtPw+n03W/Efw68VX0EcMmu2b2scDqDcRCBCgmLHnDHHBr548c6yYbbxHr0Uo06HXr21sEvZDiNbdV3znPGeMjjrmjwf8TdX8feD9E8UeHmSxvfDfiu1sredhzLpc3CjHUBiMnp1oM6h+wXwN+FcHw4GrG1CWa308zXTYG4q7Hap7nKnOTX6I/DjwpHZWq6hasBHIo2heMLxjj3r8+/B0d7fftm33w00W6lu7F4lvr+M4KQPIm4Ju9lwMe9fqvLJa6Lal4VCxxfKAB2HAoMyRrZY8HJJ5ya4vW5o3JHoDVS38QSOTK7fK5JH51zmu3zOwii/i5oAj0KbzppPUE10UtxFEOCGNeb2kl4itHaKWk9q8H+MXxv8A+FaWci31nOZRbvKXA3RptBxvPAGT0oA9Q8a/Hnw94AtpLvUyuxWxwecdzjrX56fHT/goBYRaXN/wq2JdoJUXcnADjgkZ64Pavxa8TftfeO/j/wDtAz+AroNYWyT7g5YotxGDgpGMnmv0o+Fv7PvgTxlqiWviENqd7EW8nTbUZjjYHgM/Q+pJoA/NT41/tv8AxYv4p4rzTpNfnQnzwpaMSoegTac1+Z3xV/aPt/h5exeOdFsrrRNYuomkWG2unkiZugSaOQ8EYwcYr+sT4g/sS+EUijjGoaXYO4KyRmWMyRg8gcEYPY1/PZ/wUY/4Js2segXHiW1jVtpJWW1mU7uvz4GelAHxJ4f/AODgv9oX4eSrbPE8zWsJiFkGIjU9A6tjO4fWvW/An/ByX8ePEV4dF1FBYR3O0PI7HaxH16fnX8zvxP8AhvrvgXUrlLqaSeKKQp5/J7kYNeKSGaJlCM21hnBPcUAf3Y/A7/gpTrvxd8UWuuar4it9NlkfylKsGRj2yCe/qa+8PjP+1ydC+Cuo3WoaxDI4Hy20DZS4ZyAMDse/Ff50vgn4k+LfBdxu0+4kZMZ25OF5GSDmv1b/AGLfil4z+O3xk0RvGmqyjwjocqzTwuS3mMnbvmgD+8r9nDw9FJ+zh4F8VfF69Frruu3hubeEkZS2LZVMdfmA7+teoeOvinYH9r3wF4R0gQyvbyTTSpwzwr5J2g+nUV+LvxV/boXTvEFp4muoD/Z2jQW62Kg7VjWM7UITufWvxK8N/wDBWnx34H/afuP2hvGkryzaXqEqvFuwXhmG1FC57DkUAf3yXeibtX1MTQshnkk3TyjEY6E4z1x7V8AfF79kN/iBeyyTWsOoO68SklWzyQB3+XrX87Ov/wDBwl4h1TxS+vxmS7sVl329uWCJsbHJ55Oe1e6/CH/gtPqvjHxtb+KvHFwn2N+UsoXEe0Hgl+u7igD3HxR+yf8AFn4R+MraLVlv/siOsunxRKyh7hm+YkgfMFr+gz4PfDHwz8R/hxb+JtJji/tG4sfI1uyGGfci48xM8hyw7V85fBz/AIKC/Aj45RadpVzPZhB/qpLhwZY2bGQoOetfWek6DYaH4lt/EvwXzZ3sj7iJGP2W63cspJPyk9qAO+/Y98daVrXw1utItjMh0G9eAi5BWXaueo47188/8FLP+Cdvh39snwha+P8AwbDFbeNtBUy2NwyqDNEfvQv6qQTjNfXGj+Gn8Oa3qfja0shp1xrcSme2yGXzV4JT6+tfRXhjWf7R0aElsTINr44wRTRUXY/y/fHn/BtJ/wAFNLn42eJ/Cnw70HSodHab7VbXFxcpHD5cx3KkbYOSo4bHAPGa9Z8Df8GmX/BRrV5Io/HXiPRNISU8iC484j6YUD9a/wBI3xxZ6je2ttNpbbQkuJAX8vCnjJPOccHFcFaSyxajPYAtI0KK6yscBgQQcdelflvEvGGJwdVqK0PewWAVWNz+IfwF/wAGaeo3kS3HxS+MUiTEZeGG13AZ7BjJ1/CvsL4cf8Giv7CHh+dIviP4s1bXnUKWVJBbr1IPI3Hr71/V9pt5PCbua5KmHojnq3HANOFvpZElsicuBvfPHPavzfMPFPENXvY9SGTrax+CPhD/AINov+CR/wAPQl9P4XvtWeIAnz76SRDjg/KABX2h8O/+CWP/AATX8BQnS/CHwi0O6ht08wzXdqtxgDtmXdk/SvuW3GnadqNy8rvGLr9yqyH5dwrPeS0sIm053aMQEtiM8uD0HvzXwWYeI2Km/dmz2cNkMNNDx7w58Hf2ePAl8kHgDwDoGiJ/E1lp0ELsMgDlEB6dea97sNebSEuI7OxVICNtsIolyGxjJIFU9Hsri41Xy5kVUnQbwfvRen5j9awYL28n+06fpdypgGAzjOY+R/McV8rPi7Fwk5ubsesstpNuKR09t4i1LQ4HtryV7u7dS7zuAqq2OIxjsBXA2fiB9c8S22qM8lxK0JWI5YRx/wB9mwRyTXJajf6zIlzcadbObWIFoZHYjfMTtChTzjvTreCTTb60sbubZaLETcSHgNIwyUGPfivlcbxpWjKyPdweS0VG6Wp7VP4xEOiv9tU3LZKOIQWU+gPJrlNIkis7abRFtrSwsJn3RwwnEiyHncQORzyT/Sua3z2dlvVVs3uTiC3d8M6g9R3zjkYrhZdTt7PWxcT3ANtID5hCg/MoKGNiG6mvNxnGdeTs2bU8iptXR32iTwxxxfZrjzxpTmBL9MCNYyCWH1HTP4Vn3njK81YyW2jPcKbY+aLqQYjYeo3cE15zoFxq2n6mIfDwEWgQIwuYJCCv7zJ5dupzj6Cpzt8Q6lLe6hqbRWETRRW1tEp8vfj+9/EP0rwVnVaU172520Mpir3R41+0NYyfEr9jj4laNJFJLZajo06LeSsfMuG/5aYQ/dVccDvX+SxCkFnNf6ZlgkOpTjAH0A/lX+w/4wV9T8I674Zv/wDl60yeGS2QDyo0VGw6kDqxr/IJ8c6Y2g/Fnxh4fdj/AKJq1zxjAwZGAOK/tfwCxfNhqtJn5bxvSdOSkjJbLupZtxA/i/kapzjB8xjnb8u70Ppj+tWSpYkvjLc/nTHVdzZ5UcfhX9CL4D4GKuZuAu9EHHRgfX2NMBzhpDnbge5rRAdByoLAYUH+H2pWiUt8gHP8qRBmFAgHOQOKQxc7Zf4ugFaIjGMjjPC//Xqv5QOQhK7u3uOtAFTyWjkUnp296QEINjc4H9aupBt6kgds1BLEuTnNAAhJ4HIp+0MeRiogoRcx5zTk8zq1ADwiH7wz+dNCxFgu3vjqaXfgEEgHsKaAckj+KgCRCdpqxOCtnJ7xn+VVkYbTxTpZT9kmA5+Rv5VtSV4tkvdH9Wn/AAQiOPgJN7yyD9TX2j8XF3/tq/C9SP8Al6P86+NP+CDqBvgLLn/nrJ/Wvtf4rKP+G4fhbF2Ny/6Zr/K7xa/5KHFes/8A0k/0U8O/+RdT9Efrh8Q4c6L4s56aa3/opq/F/wAT7R+yH8KEzyPErf8AoZr9tfHts50Pxa3Y6e4/8hNX4m+IlB/ZL+FKkdfEsv6Ma/BeG9H/ANvP9T7vF/xEfrDcQZtYT0zafyFe7eE+PC2mD/p1h/8AQBXj13blbGFh0FpXtXhOFf8AhFtM6/8AHpD/AOgCv6k8DP4Nf/tz8pH4N4hP99D5/of/0f340aLE90QP+WEn/oNfht4sBT9lD4nRrwD4rhr97dL07Z9pf1hf+Rr8FPGLiP8AZc+KEZ/6GyCv8T3/AL7fyZ/pNk9ROkfrPeWuP2K7tccDwmx/8gGvx1/YPZv+FLaWz8/PN/6GRX7S6ogj/YlvHA/5lJv/AEQa/Fj9g87vgtpg/wBuf/0M11ZUv3Mv8cfykdWDqX5z8Iv+C0jf8XW0wDpk/wA6/Ho/64/Wv2E/4LSj/i6+mY9T/Ovx7P8ArT9a/wBUfBb/AJENP+urP4Z8V/8AkbyY9CSTmqsihm3Dp6VMDhjz378fypMDpX6qfmpl4yCoGKq+W/UCtd48HIqHjaSBigChJECMgYqvsYcZq67MKhXkE0AQbWxjNJ5bf5//AF1NjnFOKYGaAGQgq/Pfiv6Wv+DTDwVpniX/AIKSaz4w1OAzPomlyyQvgFUZzs5Hv0FfzTqcZc/whm/IE/0r+2//AINDPhtpvgr4Q/FP9pzU7bddX0gsYXbA4iBbAY9MlhnFAH6+/tS69onjX4x3UbXgub6S8ldkkJRYYlY8rnjjGBx16V8q/EXS3zbW6vKsYZvnQgtLx8uc88flXtvx70HX/Hc95N43lbTbRSvlxIP3kjMQfllXLd/WvzT+Mvhr9qXwZpU8nw2I1PTowRbSXmEu4Ex8y46OvoDzQB5l8Yda1iHT/Nu7QrFI7I1xcFdjkMf3cn8JAbnuBgYGcV5X8Pvi7YeDtXi+234+wQ7FtrXd8/nnA3njlSM/PnHIGOtfKnjv4gftF6xMuhX9lPtgj8yMmNn3kfKdynhcDOO2AO1ZHw40w6trMWqa8bj+zIhicfdkmmJZvKj5Gc9D6ZzQB/Xv+yL8VdA1nSY0eMSyyKA5JBUswzuBzjgegr9ZfCLWR05L+Vm3MMFDhgV7EGv5bP2Lvif4e8D30NzGjiQlVltC2fIX+EANnGB978DX78fCv4m2GuIItPuMxygkbm+bB7ADjjtQB98+H/FOmRyrpp+aTBbIyAF7Z7VN4x1S1udKgFiyyPJLGn3gMZODg9/WvkD4g+L9W8J+FW1DQvnVmKMx+9g9c+wrx/4c/G/S7pjDPc+cLdmjRs8F+74PpQB5V+2vraaf+2Dp9uibvK0+IgEALkBiDnpnPNeoaJ8W1j0S2MuPNlaK3+QDdI7HooOeg6kDFfBX/BTz44+HdR+MvhfSvDYF9NM/k3LRMUk27QvzFedozXH/AA48X6pqHi2JrKUTSWsa2dhFkeTEwXDyljyQhGc4zQB+6Hh7xFbiBdQssvDHuRsHHzKcYHrjvXosXiKOWctNIqoiB2fOQF9/Svzm8D/Fa5vo/t8VyB4e05Baxvwz3dyxzLNGvUqp4/GutufiSvj/AFA+A/DSbLOFwZJNxDN33y9gOuB7UAfcEfxHt7udU0YF4ydof1I6n6V1tp8RIoIJEkkjeXIBXOdvuc5/SvgnxR8ZtB8KXQ8M6BcrcXrIqGUdFQcHbjv70ml+MWa2F1a25kuZB+5B6Sp/Fg5657mgD6o1z4libVb1Ld2aFI1KgdN2OeR7187eN/j58O/A9lffET4oapDpPhrSIjLqV9PIFj2xjc0UZzyxHUj8K8X+IHxn8O+CPBmsfE3x1qcOgeDNKgL319MfLaR1BzDb+uTxu6ntmv4Ef+CnX/BTbx1+3t4/m8CeAZ5tB+E+lSslrYRuV+1hD/rJcfeJ6jPAzxnsAdv/AMFi/wDgqb4k/wCCoP7Qsv8AwjIez+FnhJ2tdHtBlROy/L5rjqWbHrx271+T4m8xyW9eKbBa2WnWa2emoI4owFVR2A6HPfrUAUqaANGrFVgvyg/5/nVmgCZPuilaVVOR171AWIFV/MyxBoAmndpBvJ6VmjDNmrjIdvPeoVjGOKdgIX46VJFIxkAY5FQtncRSx8uBSA2E8svuPbmrSGNAdx3VnhdoB654q4iKCenOKAGgYJPY01yg+Y1bJULtx1qpJECNh7U0rgR+ZF2/z+lS7k2ZyKoyREgNnjrzwDWLeeJNHsEYS3CmRRwi/NmolJLcqMG2dIJVHBprSqTkVT8L6b478fID4F8NapqrdCLe2dxn6rmvfdD/AGPP22PFVut3oXwt11kbubSbp68KamWNoQjepOx0OjPoeCSHfJy2M1+sP/BCXwZH49/4KoeF7poBcnRbbzolIzmVFAX6ctXzTpP/AATA/wCCkniWyXUdO+F2oCAvs3SxshX6qQD+lf0J/wDBtj/wTa/a5+Dn7dOsfGX9oTwbP4f0nTtPmgimuI2AefgJ5Z74xnNY08ww1R2p1Lmbovqf1hftz+GNW8UfDS78PaKu2/J8wDHBOOn1FfEcvw/0L4Wfs2aZp2tEWF1r8DTzSY4gt4W3yO+T14YZPXpX6hfFjT59S16HT9YYeVPcqXK5z14UKfXvX46f8FB/HWpfETxjffCVIf7G0uxiisLhyVEMUIO/zbiQkBYRnlRy3SuoxPzn1nxXP8UvHy/ESOJrjV9Rk8jwvp7pmCysYCVF/OpGB3Khhx19K+x/h34z0u80O7+GtqWvbKNd+veI5MiN2AJ2ROcAqD3FeaaR43+HQt7jQfhHFFcjTY1g1bxPKD5V5GMApb7h8sZ+6qivnD4x/tjeAvAUk3wd0zS7jxhNqBMY0HT1/wBU3qzIOvsTwMUDuza/ad+IOifE7UNO+DPwo086h4f0pAsr5bZCij74lOSznvzXPfsn+CvEPxF+NulfC74Zm61xNMuEur1oVJtkSIBhHIxHLqVABB9a7v4K/sP/ALX/AO1R4aktfEVrH8MfCDAv5TbhLKnUiaQfvSSvQDjtX7Kfs1fBLT/gL4Ts/g18ALUaH4ZsnU634uvE8q61Kfd81vZxtiTbn+PpzxmgLn21+yb8DpPhjaaj4q8WlbjxRr00lzfzLyVDsSseR02jj8K+kPGWo4WO0QYDYB+ldLpNtBa2UWxCmRj5hzjPGepyevPWuF8UOLjVfs8fVRg0COXnuIY3W2Q4AHFUp7iIkbjkjisOWRxdNu7HAohUmXLcigBNZ1OXw9ZS6tYoWdRnABNfjr+3H+1Pb6r8PtR8KJp17FLIxSWVYz85PRM+hP0xX7Z2KpKPJTkN1r5++ImmeEG1+PS/E/he01S0bBcvGvzHPXnigD+Rv4I+GvC2kfES4+Nvxm1KPQrXw/aSSwpcOEMUbch2znLtg7R619J/swfEn4y/tET6p8bLDxTb/Bf4LadI0I1y/kVb3Uo1YhmhVzuO/tgda/bfx5/wR1/Yd/aHu7rxN4vsr1Z9Qj/eWqzlIV4+TCcA7TyMGvgL4rf8G6eoeI7q18U2nxMvPEyeGlY6L4dul+z6YqrkxRukbEEhsEsRknrQBg6v8TP+CSdjpslp8Qvjxq894snz3TzbHZx1PC5Ir4v+P3wQ/Y+/ab8O39z+xF+0HdalqGnpvuLa7uCygEZwASmc+4Nfh1+2J/wbl/8ABRzwV4jm8W3GjDWb7UbmWa5uYJgbcGQkhQRgqAMYOK8Y/wCCe/8AwSL/AGhdb+OV/aftAaTrPhnQ9HglZ5IBIrXM6D5UjdeGGcEGgD57+PXgL4lfCrxRe+FPiWgu7MuwW5RTtkYE5bI7+vaviXxHo1qq/arf5AudqDnOf4ucnHtX6UeNPBn7d3wQ8T6pH8SPCV74r8G/bXtIlvlEkqReZiMA/fX5cDvX0lrH/BIn9oL4z/BzS/jT8EPDF3b3moO0q6TertlWNRlyvfav60AflN+zd8Drn41eJv7BSUxwghZAqliwP93HvX9oH/BIf/ginobOfiJ41aS0FoA0EEoYQyhs8sM8nj9a5j/gh3/wQx+KPw1tJ/jl+0/bmytbtt1np7DDEhslyO30r+yD4X+ELHwvoKeGNJCRrGDgKAOB2/KgD8gv2k/+CXnwv8a/Dy90vTmitrgghZORtc8AJg9Pav8AOX/4KdeAF+Cf7U+p/Dy35SyWKLP3cvGAAxA6nr1z71/rWfEvTrowm2Qb9yupHYFsdq/zQf8Ag4n+Cd14X/aksfiTpCErqqtDcEABfPiPGB9NtAH4LjXZZAiNvk2clR0HuMd67Lwz8UvFmiXavZQuzjIWVy33cfdx0r2P4N6X8OPs5m8WsmF4PyZb9K+ltM0T9ma/SJrrUXt1kYrGzwny847tQBxXwZ/aq+KXhjxRp+pWtytskUgKxliCG6hj3wK/rV/Y4/4Kga5460rSdIOpXGs32nugvZE5giUnHAXByK/lrm+AOgqy63oKxXkRAaG6gfzAw54Ixkcc49q9l/ZtsfEnwx+J9rq3hK/e101HE15HHyHQHLJtHHvQB/qMfBDxvoXx3+HEGp6XdrczWqI6Mhww9Qf8K9q0SJdK1e4NxwZ1Hfgt6V+V/wDwSUOpeMvhsvxP0/XYp9Eki8tbGOLbIjsQQXb2r9QLzU45/EJhUDMHJx0zSu000B3GrIk+gz4UfdDbcdh/+qvI4I7eezXUr2U27PlAMnCgdMnNetorXVtLCDt86IgH6ivN5dG8u2jt5JFlhXIuC/AYg5GPevxDxRwkuaM46q36n0eTzd7EGoaDZXVhI1xOVIXIOSAvoQe+ffNeNTf2vFqyyxCSKO2z5RJytxuGPmHbBH617ddBLzT2s7uTzIZv9WV6ADoDXDJLYQ3qQAr5uMYHIAHf6mv5wzepBNK9rH3OVK92xLuyhvZUubpS87RDerEeXFx7fxDt+tYNrYzvcy3lshMMcRSN3wdzf3vXg/hWzdacZ0Fvpkv3pC0wPQqeSM0z7Rp8kgZW2pbgxeWvZT6eua+YxTXxo9ak3sjjbXULmwvF1KNzPK4ED4JO5hy2B1J7elaoa3s/E1vpdtPbW8IAEsCn98SRxuOScD+dU72RLVGv4o44XhA8tMgFcnlz6Nj681HDp+jaxYLNeuJyjCWK6+584OcNjH0PY159Ko5e7KRviKTs2hfF99Y6P4gin1N3muynl28ABEaJ2kfoMk/jXFaEXvGOo30bXDW+9Le12keY+cmTB6qP6V6FrwWVv7U1cw3E1rgsiDkcfKoH8XJBrEs5bCW+tJ7eX7TfhDDCVGViL8sHx0I5ry8ThJyrWi0zfC1XCnZnNjSNX1C6TUmtVku7ZvMAfIZe21fasC6V7a5kiezW7SaRAtpGAGjcc+ZKT155Oa+kbiwgMX22KN5biy67DtLsR07AjPrXkTaBqGt6hPdalE2nWUkoeaR3CzMg6BdmcjPHPaunEcJVptOPU2w2cwirTPNr+31OC+aeXbeyIn+kW0C4gKf8syw4Bx7c1l+IkjE9r4f1O+8pRAXeWEbVtw38JAH5Zya7jX20aLTzFqOv6ZpsnnCVDJJtXYn3fNB6+/Nee618cf2UPD2nyD4n+P8Aw/b3c3N1HHfRhJCOjKGPoOnSuzL/AA7xs3zbm1TiChDVs7mPXGsimhxshtP7LuNjSKd11tQbSD045yDya/yfP24tBh8JftwfFbR1txapFqLkRL/DvfcMfn+Ff6Tvj7/grR/wTi+D94NZ8bfFGwcWwaJLWzlW4QLjaCBGpOQOfY1/nOf8FLvih8Lvjj/wUH+IPxg+BmoDU/C2vzLNbXARkDFkGVwwBzkHqK/rXwNySvg5zVZaNH5lxtjaVaKcHex8XSqInaNee4xSEmMNxuzgj6mmoQVEi+lTdRsHAHfvX9Bf4j4BPQjVWVR5Z+bdk01Qi4x3J/Q07JDPkd9wPQYNGVbBGPXipARg+5hjOcEH6daWcRySbgOGA/SlbKjIOSvBHsaCFHyrwE7HvQA7EYXOOd2P0qu65OD3qRyANvrzSkbh0Ye9AFeOM46ZpjI2CFHPrVgKFBKnntQAEA2EkH+dAEPAIJXkUnH93/P51Pk/do2nGc0AViqlSEXAqGeLZay4H/LNv5VdU/KT60XCollKw6+W38q0jsL7SP6q/wDgg+zR/AiUHp5sv82r7e+Jimb9ur4Vhf8An6evhz/ghE+fgTMD2lk/rX3N42Uy/t6/C1D/AM93r/K/xYf/ABkWK9Z/kf6H+H7/AOE2n6I/arx/aRr4c8UjHXT3/wDRZr8H9eV3/ZR+Ewz18Tyj8Nxr9+viJbkeGvFLjnOnSf8Aopq/BDxAP+MVfhIo7+KZP/Q6/BeH3abX97/M+xnUcmmfsjqVisekxjv9jNd1oUtxBolnDGcKkEagcdAoFZms2X/EohP/AE6GtPTomGnwDH/LNf5Cv6h8EG/Z4hf4PyZ+G+IkrVofP9D/0v6R7W1dFuwR/wAsZP5Gv55vHA/4xm+J6NwP+Esgr+lAacPJup8fL5Un6g1/Nz4+jCfs2/FFO6+LLf8AXNf4tYrDtYtP1P8ARbhiupxlE/ZPUrYN+xHet2/4RFj+VsTX4k/sIof+FI6Yw7ST/wDoZr91tQsyf2Er6X/qTnP52ua/B/8AYLud/wADtPA7yT4/77NdeDw8lh72+3H8pHXk1dSnVXa5+Ev/AAWb+f4paWR6t/6FX5DFPnbdX65f8Fld6/E3TGP94/qc1+RpcMSa/wBRPBNr+waf9dWfxf4rNLNJJlZoY3+UDJp7ouAcdDUhHIZaTep49f8APpX6uz8uDarA7eaqGEnoKs7GBpy7lGG/SkBmyRYHNVtjDgCtZo9wqNIdxK9MUAZrRFRlhj8KQxjHOK1mhYpjd0qBol27pDigDmtamNro8jRDdLORDGPUt/8AWzX+oB/wRx/Zxg/Zs/4Jg+CvAjxRw3Xie1XWLzPDBpwGPPqF28fhX+cd+yt8GtX/AGh/2tvht8DvD0X2i41XV7cyx4JxGr5Ynjsma/1kfiz4M/4Vr8NdL8D+H4Alvp1jHBGFyNuQAR8o4GOtAH82v7bv7VfxN8FeJr7w18EtHufEFhbTNG8agtLFKSQHUgbnAPPHA6V+Rvj7/gpb8W9NsJdK8cxXNndDFt9qngI8rB5JGNpIHFf0lfGHxP4W8HQx3ps7KbVN5RYolw+0A5ZiRzjqfb1r8ufjHqvwq+I9s3hTxNZ2klhqEjLPiNQoccg8kHB9RigD8rNT/bl1TxRZz2MXks7qIo54gdy9vN27yeB26V4Ra/GnV72+N1dowtgSYp0GBvPDSAdQcD061798Wf8Agn/8N/Ed29z8C9Tk0S4J2rErl41Bz1BIOOOa+RfE3wI/aq/ZylW48S6OPEWmRICbvTm3Kqk5yyEAn3GKAP0X+APx3trW6haxaaWe7by4S+S8zHjccc8V+yXwX/aFl8NahaSXl40kkJClxlVPqoHTIPFfzK/CX9pHwg+rrdatC+m3cpCpvgZNpzjggYA9cV+mHhPxfYeLdGkbRtQikjhAPlRNnaxP3lxznuc0Af1SRfGS2+Ifwy1CW2uYvPaJhGrHHzbSPmPavyW+Ivxum+Emky67r2px2Jt5HeVC37okDAAf1Pb1r4e8OfHf4ieA3Tw8Vkurfcvmy8mPy25DOR/CK/P3/goV8Yb7xTbWUcFzE9lI7bo0bYXmbOXKA5KADC/5NAHpvxE/bRb4nfFkfF2ZysVrH9ktYVJ+cL8pds9C3Bz7V9N/A79rOxN4P7evXsre3DRx2QJElw8wwPn7DJ6g1/NivivxBZz7Ul2qUxlMAYzkAg+ldDpXjnVYJYnublkMeGVmkOc9gv8AkUAf2VWv7Q+papFbLoE0djY6dAYpLpGHk2in7yhScOxx255rptW/bVjtdIj8JeCgI45tpa4iBEt2QBlnJOVGBjFfyp/C3xr8Qda1uzigubg2FsoIiaXCFyPvOmTuyc9j07V+zPwC+GMWqCG78TXcwkvGD3MsZ3SYIG1IFHPPTgfpQB+ifhz4kXdwsviDRN8ouAq3E8g3Jbqx5C4U5JHAGSc19u6p8W/h3+z58CLn4wftEa1HoPga2RpbaKcj7deOo/1EKZDZkbkgdR6CviP4x/F39n39hX4RR/FL9qK7i06O1hL6D4St2Q32pTgfLJcbTlVPBJOMDj2r+Nj9uD9vL47f8FDfif8A8Jz8V7o2Ph6w+TRdBgLLa2dupwgCYwWP8TdT3oi77Dt1Pon/AIKcf8FVvi9/wUm8evoK+Z4W+G2kSGPTNHtSVWRY8hZJyOGcgAk++Mev5sW8VpaW0dvaKFjAAAB6YrMiTcvlrkBBgKAQKnXGA6HgDv8AzockviY4xubIkjA5p6mOU4B6VmqBLGJJWWNM43OwVQe+STism58Q+HbD5pNQhbHXY27+QrRw0umXKl2Oqf7tNikLjB6D8f6VyP8AwnGhSkR2pmnPby4nbP0wK0tO1HXNVk8jQfD2o3hbp5cLj8eK5quIpwXvOwo0mzogCe1Q7wjc81674Q/Zl/bH+Iaj/hX/AMLdb1JTjlLeRuvvtr6S0f8A4JLf8FPdY8N3njDVPhHqum6Xp9tLd3E1xGqBYYVLu3zMDwornWZUG7KaK+rvsfChlVj6UtZ9u8bgqhwYyUYEEEMOoOa0UBddw4+tehzNGTVtBmwU5UXNB44oqGxEgkEaFTUaTBmypzVKb7wBOPr/APWqpdX1tpc0VuVe4urg7ILeLmR34H3eoAz3/DNackkuYai90dLFIkm4Z+6CT7AV1Hwt+Hnxe+O3jKHwD8CfDV34m1Wc7VitYXkBzgZyoPA7npX7/wD/AAS9/wCDc/43/tdWun/G/wDa+mm8E+CWkWWCxKMl7eJ1BVSP3YYdGbB9K/t3/Zn/AGT/AIAfsi+F18Hfs3+DLHw1ZW6iKW98tTeTtn70kuNxPfljX53xL4h0MDLlpu7PYweVOr0P4xP2SP8Ag1k/aq+Lgh1r9rLxJb+B9MmxILKIie4dDj5TGuFU49TxX9K/7MH/AAb6/wDBM79m27g8QP4Xk8W6lDF5bPrD+fDI46uIcBQT+WPev1jtriWHXXjaWSZQPMWZzuznkjJ7da1l1K7lsYhpewSykxmT7wjU98cYFfkOa+KleqnKDPoIZIlY8z8GfBn4FeAblm+GHgjQNGs4GCSSWtpGjEnsAo4x6mvTZdY1aO7uNO07y7cIB5QSFQCP9okY/Ks/THiDXmn2uLW3tyks0+AfPY9cDtmuvhn0sPLqUsTxxRANI0vRgem0ZPTtXws+I8RiZPnqHdHDxirNGDFdePtTuFa3mj06JDlh5SlpR6gEdK9fspL2HTzJfTLIe2QEyfbbivJYJoLvVpPEJ3qlsp+Z8/OpzjaM4GMela3iDxvpvgn4Y33xC19DeQ6cDOq46N2AHcV+peGeMqVcRySlc8TOqcYRuj4t/bP/AGgvCfwO1JdKsZX1Hx5r0Jj0bS4lMnkMxCefIBzncQBX572/7LUnjuzj039s7xOlukr/AGifRLGRZNT1N2JbF2V5VQCAoPQda47xD8Z9D8N/EvWfjhq9tJrHxGmgN1bNdN+7srVywjW2i++0hQcY5UHnHSvnTTtQ8N/EnxC/xI8ZeEb3S7p2N3fX0uoixR0AyFZZGMpDHgkr3r+hj5M/QzStc/ZV8JaJB4W0XSLKHSI2KLpChr66Kwkk8RnCHjOGyRXz3c/8FAP2C/2c9Sk+I1h8J7bRoruYwx6leQ/6bNMTk+VBtMxyT16Hp2rLt/2NLn462sS+FrnU/DunX7rfrZeHYikKlf42vpCrOCT1HBOcdK+vvhj/AMEmf2avAepQ+OvjF5Wr6qsWc3rtf3Tkc7svk5XoAFOD0oAyfA/7c3xa+N2t2lz8MPAV9fpOEfTYr/ZbqobgyG2RQRFjnMnJxX2hpHgvX/h5qen/ABR/aU1z+3/Et9cJbaPo9uAlnbTSdkjXAdkHJY5AFdKnin4Kfsm/DuTxbf2y+GtPmO22inIbUb44wgxksozjavBUdhXk/hiTxV8VfEP/AA0D44ga0vZ4zY+G9OlJ2xiXmS5C4yH28FvSgD9HLLxDFq1jNPbsG8hdrMOhkHUD2HSvJjPeXN3c6hcMAOma6PT7fT/D3hCLS7ZycRgMByd/VmP1NcbeudN0oFvmMuTigDmJEW3uyFkLljnntmt2G2EgDhsetce08wUXMy7d3AqSPVQXA8zG084oA9H0+3lEoa36GtjUPC9hq8e7UYRuHQ46e9W/CMsF1bo55NetrZI0WGwc0AeSWlgLGBhbjAUYFci3ifUbaYxZZGU9q99ubC2jt32p82OK8J8VWd2kxa2iwx46d6APM/HWnt4phFtrHiibTlldWKDYQceu4dPpXA+JZ/hVD4PbQPEnjyxtTbZLXKRR/aAO6jjBOOM4rz34u/Db4h+LLC5t9CuWtLmcFElbJCA9wPWvyL+If/BHX4o/GzxAb/X/AIlX+nlxtYQSMo+uMigD6F/aV/aS/Y68R+ItJ+FvgAjxB4qjkSK1tkRD9qnUZUyJgkkkZ6V+s/7NfwQ8V+CfD8Pi/wCIE8cvijUUUtGFHkWNvgYgiUYGf7x6mvir/gnd/wAEiP2b/wBjDxU3xUeefxZ44mUgalf4byWb7xjzk5Jz83Wv2n8t2O+QAuG+Yevof/r0AY0mmObS4e4mLgLjaQAo/wB0CuG025i0+UszBIt3Dd816LrGoWsGjXEkkiqDxkn3r59u9QaKMsgMgycenBz/AFoA6jxpZrrthJcWjBJI+46465Nfwz/8HF3wx0PVV/4mfmxW2m/6fM0Cb5grDBKD3J5r+2S21iOKCSW3Ys0ikSIe2R2r+Z7/AIKzeC9d8Yx2vxF8NWS3v9iXOJ9yho5bdvllikXuPTigD+Fn4aar4G8OaM/xPh0maPRtPl8lZ7z5/PkXnaUxj2r6h8B/8FRPhz4bng8Na18O9Pn0btE6RHYp99pb368V/TB8JP2ev2Y/G/gWTwzrPguz1vw1rCb7zSokC3Nm8o5lgYDBwRn1r8c/2yP+CDXgbw5f3vj39mnxjFLozs0o07Ug0VzCW58rhTnHTrigDyBdQ+APx2v7bx1+xxrS+E/FcLebdaJdkCzmLH7qhiRg9OPWvaP2XvEWj+OPE3iHw1rOkDw/4u0Le19YNzFMuCGZB/dbII+tfmBr/wCyX8dfhv4dsfD/AIb8P276tZzPdnVLaYtL5b4CwsBwD3H0r3T4Z/Hj4q2H7Qnh7XvH2kNY+M7SwFnqKzptW8iiUqjPjqSgH5UAf3Nf8EdPjNJYeHPEvgLT1jtLZbM3OwnYscpYqPm+7zz3r9wPh5qi+JbaOSEo1/JFvmP3lwDnOQcZ96/lD/Yp0jxB8Bf2VPFnxnllkj03Wpo4YhcvlZZmIYpDx0GTjmv6BP2MPiRqtz4Li1HWZY7dZYENnKw4O5fuNnGcDqOlKS0A/QvSvE1pJfa5p8JO7S4l3FgcKSvRfUe9ebTayP7J3X00htGcsTjLFsZK9Olfmt/wVZ/4KKXP/BMn9irVv2n/AA1aQa3rmt6rBYWNvOSEZXJDPgYJUBT39Pw/i68b/wDB2L/wUY8W5j8IWOk6JE33VjthIeRjOXJr854z4axePaVB2Vj28uxlOn8Z/olaZqGseIoUurBm+zSPwhGxQvQnDc5qU+G5NGj86EgrF8zoGBkYdwAPWv8ALk+IX/BwJ/wVZ+Ikb2N549msLYggJaxRxYz0wyrkY9q8X+Cf/BSr9t7VP2o/A/inxt8S9eu1/tW1DrJfz+WV85N4Kb9pG09CMV+QYrwUxjpTqzmtNT6WjxBSi7R6n+rtfeIYPLt4olYpM/8AqIxiQ5HBb2HetB9PubcJqSxrvVtvzfwJ3OO5oupNE1bT9K8bxiQHUbKKRZ4sc7lXGTxySfSqeoahqF3cXOn6QWieGPbL5q7tzN/c9T69K/nzPsPOhJ06r2PrsFVc4px6nH6y1jda/wDaZQJIiuRFnAbH3SfbNb3hc3WpLd22o7biVk3LCg2xqgYcD1NUEs7ObTZY7wGPyD5TzMuWfPZe4rS0G+TQoLm4vmIg2nbCg/fDjGcnHHTrXykPcqXloe7Wl+4stzkte0qaSSCz1eRkne5DRi3JfaCQBvPtwK/lH/4Kpf8ABfj9pH9gz9qnxH+y38C/C1hb2+lsu27vYmmlnMqBvNxuXGc8V/WndTSwWyNpcqIrXSFpf4pU+XKD368+or/PH/4OivDf9kf8FQb7WN2Fv9NsJA2eoWHHUf7tfu3g9w/hsXj5PFRurHxvE+PqRpqEDxbxj/wcdf8ABWT4gtJa2niLTtJhLFl8qwiRsnsSxbI/CvjH4kf8FRf+ClHxQvPtviL4panagf8ALPT5jaIP+Aw7f1r4dSNk7kH3OamZWHy+tf2DR4WyyFvZUUfnbzGrJ7npOt/tEftSeL1dvFvxN8QXJf7wkvJ3U59cvXj+pW2qazP9p17Wr7UHPUySNn8yxrSCfNtalCopxXt08voU17sEjnq4ucupzy+HNCQ+Y0UrN/tyEg/pWvawQ26iG3URR5ztGcZ9ec1ZlX5eBUCMfukHj8qt26HN7WXUeGBIAG3PIHpTpCrfKxOPbqT60joThkIyKazlgccYpEuLF3kAF8MfQdMUz7/7voM59/wpA275x94nB/CnqAct2HU0Eilm3Mrjjrn2oEj8A9xn8KaVGAwJIb1OT70o8wEEYwpOfpjigAVBjd0FNGVOM8GnYU/w/rQF55/CgAXMYxj3FPXar8dKTn0yaTJ5yMd6AGMRkr0PrSsDs2D6/jQAGO496cSO1AEZCdM80XAIsZv9w/yqRlX72elJdD/QZR/sGtI7C+0j+p7/AIISjb8CLhW6iV/5194+Ljn9v/4UL6zv/Wvg7/ghUw/4Uddf9dmH6ivvDxYpf/goR8Jl/wCm0h/U1/ll4p68RYn1n/6Sf6FcBVf+E2Hoj93PiFAR4V8T5/6Bkn/op6/n11Ub/wBlz4Qen/CVS4/77r+h74jRf8Up4nI76bL/AOinr+eHUGDfsxfB5B0/4Sqb/wBDNfg2RRtP/t5/qfUUJ3R+7mpQB9Ft17G2plqQttGvooH6Vq6hFnRLcjvb1mQQsYUPH3R/L6V/T/gmv3eI/wC3PyZ+L+IDvWh8/wBD/9P+rQWX+g3W4f8ALJ/0U1/MB8RXY/s/fFJVHH/CXWv9a/qrktX/ALPuyR0hkH6Gv5WviAP+Mffikv8A1Ntr/Wv8guIcIqeJjFeZ/e3BWKvKafRH7tajabv+Cf2oSDj/AIoxj/5KV/PL+wNLj4Iadx/y2nH/AI9X9Hl7bf8AGvLU2PbwW5/K0r+bL9g242fBSxCHpNN/6Gf8K0jRtg4yXWUf1OzhHE89XEX6Nn4g/wDBZn/kpWmf7x/pX5Dj+Kv10/4LKvv+JemD3J/lX5IpGpGT3r/SDwX0yGl/XVn8j+LTvm0mMHQVCvzEFauCNabgEZAxX6yfmi2IN2VNKA2OtNI52infN/DyKBgwCjIoHG6kZlIxRyBk96ADLY6VGfldQQDk96mDDpQctIpUZ2nP5c0Af0cf8GqP7OEPxk/4KRal8ZdRj86HwBp7zwhxlQ837tfxAJr/AEAv2qPFFppNtcSYUNgjB6EAEA9a/lz/AODOv4dxaF8APid8bZrXE2pX62ST4+8sALEA+mW559K/fX9sHWxd+HZpptrTMpCYPOcD71AH4a/tJaRf+I9SvNR8MXKQxAMZW3ZkVmGCF9m/Svyi8SazoukXxtvG4nMAGyVk4dAowoHHOfX9K+4fHnifTptfuIbiXEls+Jkwdqns3PXFeA6/NoOvXCWviu2S7kdikEaqGHTO98YIPp6UAfMC65e6bd2moaJK0V91jMh5MQznePoa9Q0b4s+INq6FcXJaKJgZwy7zJxwrZP3SeMUzUfgLomoFtS0a+eWVzteINl/dF44rrNM8E6f4QtikFh9pIdTHDjez5H8ZwT8vegD2z4bfD/4GfGu8hOv6HFoGtWzjYUjHlye5yAPmrp/iR+wv4fgkuPEnwxmfQrkDMyQcBs8EsmOPwr274Ef8K91eZNM1RTdEFd1spxJG+AcYAyAO1fXfxEs9NtruO8W5a2RAuWGQXPRY3BOCueTxkUAfjAvhD4zeELR9D8QwRXFpGgUvGpBmhY4AdeT17j8q+Af24vg5v8NRfEiSz/s69sNsK2kQyvlfdTIOCGxkn6Yr+hPxETp9+moy2/n+WwkhjBTJlb+HG4ZxnIGa42y+BfgT4qX48KeK5UvVlZZLt52WSIzuc+VGcENgk9OKaQ1G5/GzD4I1jW2GpoY2THzRKcNk9OM4PuM1PY+AJINVT+1p42BI2hRjYy9A2a/0ivAv/BCz9j7xj4FTXrvT1sJtUhWQpDGixpngsoIyGPXrWtpX/BCb9iTwxp/9nXCI9w/AnkiQyOCedoJ5P0rjxeOpUFzVXZGsMPKWx/E5+xz8GPFXxf8AF9po/gzQrrU73cI4nhXKliQM428j/PAr90P2otR8c/8ABKH4Tab/AGL4Eu/HPxZ8S2ZnsTHA81lpqk4BO1W3OD/AMc98Yr+pf4G/s1fs/wD7LmgW+gfBHw5b2LjKPeSoDN7sGPIyRnAr3l9RmvFWWSGG+dfl3uqsWwc9xx/Lmvgcy8S8FRm40mpWPSo5RJq8z/Jg8b/sa/8ABX/9uf4nv8VPHXgjXPEGq3xEsZuomVI06hURjhFHbp/OvoDwR/wb4/8ABYTxlKBeeCBpMcjZ8ydoECg+vzcCv9RrU9R1VtGeTwulvBdQsvm+dGQAOnygdwPqKxbzxj9ssXs2unllum2W8cQwTgctx/CT/FXh1/FuLhaKVzrjkh/np+Bv+DT/AP4KFeLRG/ivxVpWiE43b5c4z1GEB6V8Y/8ABVH/AII3fED/AIJJ+B/DXjfxp4pi8Vz+JpHtjGodVgdQCx568HjpX+o1Y3d427z7mXLoFIGTtYDGN3XnvX8pv/B3T4PXWP2D/CXjZyXl07Xo488/dlhkz7fwDnrXp8N8eLF1o0px3OTH4GVNXR/Jp/wSn/Zp+Cv7Y37e+kfswfHy5uI/DuqD/R/szCNjO0QdFLENw3Sv7sfBv/BuH/wSg8AQmbWfCDat5eATdzSEE+6oR19q/hE/4I3eLZ/CP/BTf4O+JhgNe3+nB89CHCwt/n1r/V98YiDSNV/tC3ia6u5wkccZb5UPQtj+eavj3OKuGkuR2ReXYVVVZn5/+BP+CRn/AATC+FZjm8LfCvRopFPyF4mlyf8AtqzV9aeG/gR+zd4N8q38J+C9HslyQGS0iBA7H7o6138Uzy27ya8Yt4J+ZOAPbnvVSfY7G2tv3m9tzDrtHpkV+H5rxviJwcZM+po5LTjaxlfZ9P0XULiaw0yysrGL5Y/IiAkkYduBjA+hrG+Kmoarq/we8UeH2VJTqOjXkaIg+75kDqAw/HpxWjrl5q9jdJbaeA8Ug+UvgBGxzzVbw3YahqkVzZXrRkXELrIcEnJHb1rw8j4lqTxMHd7nTWy2EI3sf47urabcaL448U+H75Skllqc0RU9QQ2D+RqSOQBVU+leu/tY6KnhX9sr4q+HEjMfk+Ib3YCMcCdxyPyrxfJEnsOn07V/aGBrqVCDXY/OsWrVGXG6mmswVSxG7AJwO9IGPU9Kp6heLZWb3QBfnYgXq7noAK6ZO0W2Ypa2LAe+udRtPD+g2kmp6zqkot7C0iUs7yudqkgZP3iOBnNf3Lf8EUv+CA/gz9nuw039qn9uKyi1z4gasq3Ol6HMu+KxTgh5Ffgyc9CML6k9OP8A+Dd//gj5ZfC/w5Zft+ftUaQs/ibVoxN4csbtA/2SFuVnKMOHYZ28cdeuK/rZvNSkuVa7itle4I278DcFPb6cdK/C/EbxBlTX1XDs+lyfJ+d88xNR1dfEdtHaaYFht7KRUkQDCsFGAiYx0PT+VWLG+gaOS11ABAScg8N9TWPYWg0liySh1lG4QIPuN/ez1yK6eG2iLqPJR0ZPmkPUk1/PmNzKVaTZ9hRwap6HFanMbmdNPsi0cYIBZeRtzyCe+a6e00l7LS/sFmu13y0wbksPRfSof7MaMvBHgq54TOGA78VqTSOo+0zPsBBy5/g3ED+deRHmb1OytT2sVZ00Cx04wyqRDO2wFRkqFGTzz0pba6ubec6XfSnUjeZaAheFjC5Xf261TtrfW9UjWI2wihh3BQxBDg98jgZrpdKsL5r2a5kZY4TbriD+Nce3tXv4DL6jko20PLrVIxepg2Yu9YuYr28kENnGGinhIwSwzyPxOMfrWf8AH658VaX8GLzSPBNhHPdzxbN85URW0XeWTPGAOv51t+INY07w2LQXET3N/fSn7PEqkrNtAHLAYXA55o+Nfht/Gfwp1C0WSRLV4me9ihOHkjC4eIFh0xxX794a5VKhW52fNZ1VU1oz+TfxnqGt6L4yi8RaffXf9gaZcmW615FLTX94PlFrZq3WHnHFek/Di78FfbJfFnjrQ73VPE17cpPqFtfyiOK3sHO/aTnbuYYIB6Y6Ve+Mfxcu/hT8ZLTRPCumQ6nJHEyiymUmx0S2JAMm7OwXBIJwTuJHSvdPgj+wbofxdnvvFl74tt/Eltr10l48RkMdxJzkmYOdyqB8qhhtx0r9zPlT9DvAP7S37PuueD7fQfh5qs16Iv3dtZ6eGDGJR86nuQufmYsAPWsD4vft4/Bz4F6IdL0K9spfFnlD7LpSOZZ3dxlEaUklSTwScjrXqvhb9j/w94Q8H3Xh3w2uieCkuoJLfzrNEN1FbNkFklBGHYHO7nBPFfP3w3/Ys/Yq/ZA1bWfijpek33jjxTZr9rW91OOW63SckC3BUh3z3GT059ADkf2Yv2Zvir+0H41i/aw/bvvGSFCJ9E0GRgkMMa/MrMvAEa+/3sZJr76g+L3w+8eaxfXPge4ivvsEq2FvcRFfIjQrlxERwTxgkDivxM+Iulf8FMv2+/ivB4avHk+HPw/unKSwROILySx+84b+MZUYA4/DFfe/7M3wotfhjqC+ErAEaUtwY7NS5bAiGwMxzySck0AfpJonmXFuEyJNgxz3qHX0luYxHJgbemBV23hXTI0jiXkd/WodS1G3jXzWGSKAPL/EOowWbJGxwcAgYri7rVtMlXN24STORjj86s+N9d0u7++CkqcAAda8YvJHJLFPML8j2oA+n/CfxEttMQRysCB3r33QfizoV6wtJHAJ96/NOa51C0s28vlz0X0rhIPiFew3vzuyFemO5oA/Zu71yyuUU2xBDehrj9aR5PmXDfhXyn8Gfikuot/ZeotubHyn0r6mS9juR5iHIoA4rUdCmuFWV+56VSh8Mxw5PG416K8fmgMe1UZfOU/IaAKGiwG2kW3QtuHpxXkH7Yn7TngX9mT4a/8ACSeKdRSwu7jCxNI38WO4x3r1jXPGGk+B/D9z4k1kbY7dSzMa/kT/AGoNZ+IH/BV79s/Rv2dvD+q48PC9M0nlsS0MEJwxcA9+1AH7jfAL9oPxp+0b4fhj01Xl3yi4uZRwixsflwe+Qc47V+l3g7RraaERz4ZVGD6cdc1+Z37Vfx4/Zr/4I2fscxwWQie7sLdYLeEsonunxyxPXFfkb4B/4OJfhd44+DkXjjw5HIbtJAt7Ah+a2J7sM/dJ6GgD+lX4qQ2WiQyXtgAgfKIE43Z4P4gV8jeJPhP4PvdVu/DPjraNC8U2RtGZwNsU7A+W+49Mmv5qvjB/wXwvfEmuWf2KXbp9q5cuGz14I79K7rxz/wAFzvAvxI+FOm/D2KRfMuryCMzLncICwMrZ6ghc8igDwfxVN4t/Z3+MPiT4eaLftDc6RcSCymhGVlRSeBzjBH1rtPh1+3Bp3iq3PhP4s6VbSKAUN7MoVnY5wCQB3ryT446v4I174oqvw/vPtmjahB51ncyMfM3EZOSeTycc1geAv2etN+J1lPqmozm3vYD5cMJ4D4PXOce+aAO/1fR/hXc+JrvVNFZbaG5ZftMG7cuc/IQSema6/wDa+/YS0D4tfs/2Hxy8G6dHH4v0B0e9kteTJYHqRjqQMZrM0z9laNNTi03UNQMXlrmZWkBUseAR9Aa/df8AY/8A2aNQ+Hnw41G01nUf7dtbiyZUjB3JsborZz1B6UAfAXxh8PCH/gnJ8DvCFoDDb3d8plCHO6QI2A3qcg/lX3r408SeL/h14B8KfDPw80Y1xdNbULeNersU2hGHfjtXgP7TXhXVvC/wE+GWlaFpcrxRa3JttNpYRBmPzjA6AZ9MZr6x8PeBpPiX+2do1+/72LSdJtxDGpGFwB5m7noOfSgD8BP+Duf4sTaD+zj8D/gJOwjvb5XvruFCMBo0VSSOvLE4r+IGaPEaRqAFUAfpX73f8HLP7TD/ALS//BTfV/CumzedpHgKBNLRQQQsqAeYQBx948/SvwblDEnPegCtEik5cnj0q7pWoLo/jLQ9byR9kvI5M+m1lIP6VWaHb9KytVBht0n6bZFwffOfr2rOvC9OS8jSjpNM/wBlD4EeLoPFP7Kfww8XSz7oNT0GyJAGcs8aYP4NXr0099e2LrBMHvbdgijoRkgb29Rj/wDXX55f8EtvFs/jP/gmR8INTnkZ0i061t5D0wEyqklvpX2BZLc6NIkVwzXNzehyJwcL5YPyqTxjmv8AO7xH/dY2rp1Z+0cPU+ejFLoeg/2obEXETyLPLCQH39C2B8wA9K4u9u7azn/toTyXELxt9ocfdGBuxg/Stie2iuJsKhR1QtK6nIDY6e/SuFs1n13zNVS0ay0y2YrIsx2rKQD82CeAa/LK2K53GUuh9THCqKu2dN4T1qczSRSxIiw27yCI5/1YPDIOPmLV/Df/AMHZXg+XRv2pPAfxDnhKnWNHjjZj0PlHZ/Js1/cFLpuvzm2khSJ3tSz2U3IE5IyIWOenU1/IX/wd0+GNRuPAXwf8ZXCZZLe5hncchZGKvtB9uQK/orwUx/8At8V0Z8RxRQ93mifxkyuWlz2bmoRcuvU5rJ/tTzFBwBx2pktxuYYr+46SjbQ/Jop3dzeMzlhzjNWk2sMsa5xbklhzmtOGdXGDxS59NTI0yykbT9BVVgVc88Yziog7A4xwe/pUjOCpjJzgYz+tZgKSMkbv0o6MXHIHBHv6UCRSKiJG0OjYwcH+hoNXNEuFADKfcD1x1+lOO1gVx1560qFMHICFhnHsf61ETtJfqOmKDIkOWC7vxNJvUKxzTsqchfofrTWZOhHSgBgDcHP6U89KUdOKaSd2KAE256k0oUDOM8jHNKTgUKc8npQA0fLhewpdvccUpGRilUqfl9KAEIXB4/z+VFx81hK3ohphL46UtycWMijoUP8AKtox91hbVM/qd/4IUj/ixd03rO38xX334mGP+ChHwnHrJIf1NfAn/BCc5+Bl2vpO/wClffniz5P+ChfwlUdC8n8zX+WPij/yUWJ9Z/8ApJ/oDwI7ZdF+SP3t+Iw/4pXxNj/oGy/+inr+di8Gf2ZPg/7eK5R/4/X9F3xEUf8ACJeJm7/2bL/6Kev51bwY/Zj+D7evi2X/ANDNfhWTq1T/ALef5s+pwfwn7834B0G3/wCvf+lZFv8A8e8f+6P5Vs6ioGh24H/PHH5CsGFiIUH+yP5V/Tvgt/Dr/wDbn5M/HePo2qw+f6H/1P7BXgxp94PSJ/5Gv5OviGNv7P3xRK8f8Vba/wDoTV/W3cx7NOu29YX/AJGv5IfiUf8AiwXxTGf+Zttf/Q3r/Kfj7DqOKhJef6H9o8CV3z1PM/oT1KEL/wAE6dXYdR4Jk/8ASM1/L7+wPOX+CliT/wA9ps/99tX9T2qIB/wTe1lhg/8AFFT/APpIa/k+/YHk/wCLGWQJx/pVx/6FWuJwajldKXdr9T0+Aq/NiMUvNn49f8FjSH+JumD/AD2r8k9xHA9a/WT/AILAgn4kaYfevyhJWv778E43yGj6I/mrxdh/wrSt/WhDkd2pC38R5xSkHNNr9ZZ+YIjQhyTSKQmRUhX5famCPPIpAN5Q05STlqXym/yP/r0bXHGaAI4yx/eMOM1S1eV4dKubiPkqhxj1PH9a0MAd6t+H/C+o+PvG+heANEUyTavf21qFUEkmWQJwB7mgD/TT/wCDfL4IP8Cf+CSPhFFjMd54qMmrOzcE+e2Bk/7qj869J/a78UJaQvZyRFW+5vByM+wr9FPhF8L7f4D/ALM/gr4URIIYfDeh2lqo6AtHCuc++c1+Pv7Vfj60u728hu0D4ZlVuy+5oA/Ifx1Bptxql3DfoJCc55Cuc5yQe+OuK4Cx8J6Fq+mSy6LcPZ3W4/aJJBvMagDY0YUjII6j1rQ8dmy/t2TT59yxTbmaUMRhj93/AICTxXitxrunxardzxzskdn5fncFQCo429zk9aAPXdd0vVNMs1l8OJEZztHn4wJFycsVOSCOnODXGaR4t/sjV2sb8NDPEzKgiy4cN947u3Q1o2viT7TDNdWD/vb6IOtwpwAvowHQGuEvLpdQnNj5QtrlkaViowyqpww3HqH7YoA/WH9njxH4T1pYINa07dcuRHDfWSgyEddsv949s19F/GK2g8Pa7YyykyC+i8uNCu35iVBEhPXgn8+elfAv7I/xKtvDmvS+GrWHyU2K5myR5ZxkEluQT7ED2r7h+OUog8OWU7XhuG8syyPPg4UkEMMdEX1GCfWgDyjRfDB16/l0CO/isxHMyCSQYWGQjaPNA48s4xuBrW8I/DTxl4V+Itlpni2DT7bTrKZZU/s6TzReyMeGR+w747Vm+HJludCh1PTLrbbXcq5kc7wWZcphuu09WU8e9fR37M+i+IfFfxHtJ9YiDTSzeVFEoUoFT5GcL0JGOtXCkpavoVF2P6DPAOq3Om/Cmxu9ShEUkcCKsQO7gDAB98c1wb2Wp6rfnxLeu/2grtjKZZIlPBIU45ArpvGOqQeHrCx0O0KiKIKkgCjOcY9araXa6qVRrfIjdiSJD/AR0FfzN4kcTzqVnRovY+yyrAuMOZmfHb2c14unB5ZJwFkaQgbCF4HHbIronaCOJl3ZI6YwuD9KF0iz0HTZTFJ5SYLMerA+lcZLe6Jqkomsyzyg/ffjoK/JpVZwjzSikz6PDqMtDTndNV23s00haAkBQR83HRguMj0Hen2cNklkl/LaiBgjKsa8zbeBwegGO1ZS2Ul7AIrObyHEm5QADuI610Vpa2YUiSf/AF4Kx5Ybiw6kHoPSvLlUqSd1Y0q0oR6laeBLmwTT7l2jAJKPA+1zgdGz3r8AP+DmXwK3iP8A4JPalNFHKRpGp21wPMIZiFV13Z/4FX762fg/SJ1cW3nlI3LMpYn5h14Pb+vNfmL/AMFx/hfb+Iv+CWHxL0myeQfZbB7oguckKwPQ1+lcBUan1uFWfQ8DNZQnDlR/mU/sf/EAfDP9ov4P+O4X8t7K9tGJz08m7Ar/AGK4vsGqSweJ0j3Nd28TCUt8uGQMMD8a/wAVn4eXaxX/AIW1BgSun37w5PUHzg/8jX+yp8GdSu/GvwT8HeJbeZWt9S0iznjAxkM0KnOa/VPFum+SEo9jzsnslc9IlutK3NYMu90+ZkPIGarW3mW1wYmVUjPO5e+elUNQ0J4j/bU5dBCOZQfmZB94Eelaek3n2w+TJGQIxuRv749frX8x4mnUlJux9nRrRsV73ToL25CytuZeVXkL75qHRfIfVoY7AR2yQ53ler+o7cVW1ltbWVINKztlHzs/8IB54rPhsNRhuoZLZFiRXXamNp54LEevNGWLkqpruh1/fps/yy/+CtfhT/hBv+Cm3xR0pVVBNqFxcYHcSOGFfBCIrqrjjgV+zP8AwcM+Co/Cn/BVjxUIIvLXUbO0uRj+LfENxHryOa/GaFux+n5V/cuQNTwcH5H5XmCtVaJtoC461+1H/BCT/gnvb/t3ftfw+JfHtm0ngHwAE1DUNy5S5lBzDCCeCSw+Yeg96/Eq7S9v5YdF0xS1xeuIYgvJJJr/AE6P+CQ/7FOn/sVfsC+EvB19bvH4h8Sj+3dXOP3hkmAKwnvtRcceprxuPc/+o4FpPVnfluB55XZ+p8t/p7RLpWjxNbx2qCOGEKEjjjTgIo7AAAcUlraw6hbkMTEI+rRtzn1JPb2pkNvHqkJR3wpw4QHkeoPpV67vdM8qKwM3kZIXYud5I9xX8TZrjZ16rbZ+l0MPGnCKSMe3a90aQ25IuYmJLSpwwHfOeMfSujsre4urCSIEtAjBlRMhmOM9ewqvI6Q3CRxxIbfGSx+Z9w9c9Kt6fLZRQSx+cTlPNnZTkhQeKWVwlUbuViJLlvYyLWG4nuwm2UKTmSZiAEzwBmvNPi38W/hl8FfDVx4t+LviO08J6HbAMb/UJlUzKPvLFGSGY/QH1x2r5a/4Kc/8FOfgt/wTM+Bv/Cd+ORFqPifU42GhaIpG+WQZ/eSAdEDYLHH+yOtf5sn7X/7cf7Tv7f3xHuvih+0Lr800UrH7HpkLFLW2iycLHGMKO2c8mv3/AIS8OHWhHEVFdM+OxmfpNwiz+0n9pP8A4Omf2MPg3dT+F/2ddB1L4i30J8t7hm+yW7MvGVLAsw6chK/I/wAWf8HaP7V13qV3P8MPhfpekzXBOHu5JLhgfTPyjj0wK/l6s7C2ssi0jVB37k/jWnHEXy7V+zYLg3B0Y2lDU+fq46cnds/oC1D/AIOmv+CmOnqJru38PpFJMu9DY7mUPxkHzBwMEYr++r9l34y+Ofjx+xt4I+MPjyxitdY8SaRDcXVvH8sRWeMncozgZAzjtX+Pd4ht3+yDzOVE0X8zX+ut+yFLA3/BOL4cXNod8aeGdOB2ffP+iruCZ6HOa9fC5dQofw0ceIrOSsfzi/tX+FdP+GHxHEejkXXg/W9UEuvWd0PLlEqsWQwyDO8ZOSPSv0r/AGbP2ZbL4teLZvFn/CaXkGny2axalbwukcrW5A8pYwpHlhVwCTzmvlP9v/4YP48/Zg0fxN4bDx6nHrKxX0rtnyEjcjt91sHJI+9X07oum+Ff2PfEvg6FYRc+H/GemW9qbtp2aaeZ9pdt3QhW5GOg47V6Zyn7T+FvhXoukWkOgLbvcafZRRQW0V7L5zFEHDHjLE9cmt74tT6Rofgm4l16U2cFtEXFxCPnjCjjYP7w7DvTtF1mawn08YSSG5RVik3fN8ifdyfUivnf9oDWPiN4j8PSxaa1vZWU5CXM8oZzGmfnAQdSBg596APj/wDYw8ZWfxN+Ofi3VodTnl063tZLSJrqUvO8jkHew5VcDouRwTX3P4V8K/2TrcGi6kkRIhaRZYQdnXsT0b167q/m1039r3wd/wAEmf2zk0bxXeSa18O/iGXS6uJMNLa3Rbb5h9FUnp2XrX9PPg/xT4e8c6PZ694WnS5sLi3jkt5ImDI8TDcrI4zxigDuL+NI4ljj+6q4z6mvM9b1AW8e08nrXpoO6Fl9q8k8R207S/ZiQAaAPK73yZpybiHczHg/WufstKWa8ZbkbAGxXeywtCuJlJxwDT4YYZiFC9fWgDzHxH4Cm1CUzafdGNSMEgdq8h1n4WvpQM8UxkZwQqt1B7frX12NOkRDgjaegFZT+HBqUw1CJ5C0IwAelAHzj8OdO1XwzqiC5yZHbr7V+hvhaSeeyVpO/NfONl4euNQ1EXNwpBRvTsK+nPDMlvb2ID4BHHNAHZiAiEGs65uLCyha6vm2RhSWJ9vSuZ8Q+NbbTIjEXCNzyT1r8ov24f25rf4VfDzUIoDmXYyRqvVnbIxn19qAPjX/AILBf8FD9P8AAnh67+Hfw11ANdXX7hbdMmRmb2XmvgH/AIJU/tCfDX9kTwl42+O3xhAi8XQ220KwAZUkBZT83OT0r9Av+CYP/BMq4+I3ii5/bu/a/sf7S1LUXa40PSrtd0aIw4keNsZyOQKtf8Fhf+CLWs/tUeEZPiP+xYY9B8agAXVkHKW1zGBwCp43j37cUAfwvf8ABUv/AIKNfEf9tL4s6zquuX8kmmiRhawux2JHnAwM18A/s1/ELVPBOvXulx3DR2Oswm1uAOVORwfbHr2r+lj4K/8ABpj+398X/iEp/aC1aw8M6QyBpriHEkgJ6qqEAcevrXD/APBQv/g2b+Jf7FXgi5+IHgPxLdeI7K1GdohVWYqAeSnT6d6AP57Li8uNC1K6AmeVLaRkVmY7WBHy/L65PNX9C+LP/CDCG/sJje65G5IeTb9mjQryFXu3rmsH4rfCX45/DfQtO8SfEzQbrStN1NGNncuhWKXZwec/eHvzXhugWkt5OtuFM0kjiNEPeRjx+VAH9dnwaTR/HX7OnhjXEz/wkDRK8h/gCk9BX0H4J1rUtJ1JIkSZrvhP7qtnjrXwN+wx4qk8OeALb4T+KP3l2QpEu48DOcCv0c8R6VfWOmGRzvWJME52upxkEd/xoA9p1/xFNcaY0s6RJFAAqyFsOHPPI6kc4r9Zv+CdnxZurjw9e+FNY1LzJvszvE/UZHIVgegFfgHD4yh1gQxTlo0iyswmALKQQAzHvX1d8H/iZJ8NdeKrIpkvYDEXhO5HST5Qy44B9fSgD9pvia15qnwa8IXf2zybmfWiGfblSvmf6tf96vQbPWI/gN8UPi18XDbJb6boXhc3hmkI/wBaIWcKnbqDXJfDKwstf8B/CXwddoZ4dRvZZWZwcqE+bOe5r4a/4OMfj5P+xR+w3r/he2kM2ofEa4eyhnUlW2soyhHokZx+JoA/zi/if8RtV+Lfxk8XfFzWpDLceINTuLt2zk5mkZxkn6iuRE4YZ71g6WCLLegwGYsfxq8CNmKALxlzzmsHXpozpkgkBY5UqOnIPrWin3aq3cSS6dP5vQISPrSk9CoztJH+n5/wQU8UWXxQ/wCCRHhO58bTzPDol61qotATIBARsVgOoy3J9K/ZiTS12NYWqySPGm1YQ2UkjXkZz901/OB/waqfElvEH/BOLxB4GFybOTTdZmm83uEZUJxn1xiv6NLOXVdJk1Rb8iJcqYXjciTYRz5n16iv4J8XIU6eYVI27/mfrfDVWXsy9DFpDqmkWe6N0QExO3+rY9i38WDxXEDS4NTmmfVI5HeCQkRyuI4nHTCqCQaadQilu4xEovIPvRB+HdvVyASQD0yOax7KHXZdQaTUrBmuirCOS5OMdz5ag4JA749q/B6s4ym3HY+8oy01On1DVLKQQPcJcxW8bYdVAKRgjAIxzkV/Mf8A8HTXhg6l/wAE7/BviOSUXD6VrfkGRRwQ6Pjrz0xX9M1nryxWBkjjP2uyI8xcfNIzHG36Yr8O/wDg448Jz63/AMEu/EEcqK7aZ4hs7pVHPlAjlT9M1+0+EeM5Mxpep4XE9JexbP8ANTsrhzbRnJA29KvpIO9YFkuy0ikLkL8wP51tDB5j6V/oRB8q5T8MrTtInjuTFMM8+lb1vI0hyRiucUAsM11FsI1i3GpOdotlmEe8Y/GoVldhk7eaWZomAI54qspDDaOlAi0k28lcdKZ5oRQcZPTI6cVASF4Jpqghi3rQBbilDA7+O+etWk8rAIOSfbFZynBzVxJMDce1AFlVwMdvWlKLnI5qJGyc1NQAUmBnNICN/wCFIAVOKADdhqC4PXvT6Q9DQBEzsT8oP9KQkn71NfoKeYgTQA/eDxj/AD+VJPuNpLuH8B/lUYZQc0Tyf6NL/uN/L6VvGXusSjeUY+Z/VB/wQm/5Idef9d5K+/8Axb/ykO+En++/8zXwJ/wQpfHwHuf+urfyr7/8WMG/4KI/CTH/AD0k/ma/yw8Un/xkeJ9Z/wDpJ/oJwRC2Ww9Efvj8Q/8AkUPE3/YNl/8ART1/Olen/jGP4PD/AKmyX/0M1/Rf8R/+RR8SY/6Bs3/ot6/nX1Bf+MZPhAf+prl/9Dr8JyeV5vyk/wA2fVYKF43P34vudCtc/wDPEfrXLxk+Wv0FdTeA/wBg2px/yxH8q5FA+wYz0r+n/BeNoYhf4fyZ+OeIH8aHz/Q//9X+yK/U/wBm3X/XJ/5Gv5GviapHwD+KhP8A0NtmfzZ6/ryv1H9nXIx1hf8Aka/kW+KG3/hn/wCKn/Y12R/8eev8vvEGlfEQ+Z/ZHAdRc9T0P6J9TYL/AME29ax/0JVx/wCkhr+S39gmQn4H2eP4rm4/nX9aOrDH/BNrWz6eCbj/ANIzX8lP7A3PwPsD/wBPFz/OnmEP+Eig33X5M9Pw7t9axXq/0PyH/wCCvjE/EXTSf71fk2ww209q/WH/AIK9nHxD00f7X+FflFLGfMb61/c/gi7ZFSXkj+dvF5f8K0v66EG5/wDP/wCunDrSN8pwe9OUH73pX609z8tH/MDgDilyE4xgUxm3javWkY549KQEu4YzTSUPJqMHH0pcbjxQA8bPvDtX6l/8EOf2f2/aU/4Kg/Dvwxcw+dp2lXw1G6yuQqW487J/4EAK/LKUbUJHQKST0r+yn/gzz/Z3XUPiH8RP2mdQi80aZbDTrdz0EkxLsBkddgFAH9pHxr8TWOmeHdUvb0lYrdDGijjJUdB/Kv5bv2jvGFprGpXd/CzR28jPleS3tkde1f0K/tceMLbwz4UuvtbDdcE4U5+XPJJ/HFfy5fG3WWvvEV9fyI6WaKSXxkFjn7uaAPm7U9Xjv9RUXjGeRANmB8oGOM+uOtcV4ruo4Y47lIIwMEb0x8wPXeP61bSzu5tVml8yKMCMGNYycgsOSexrA8SGSysHZbZp7VfleRuCTjLADjr2wKAKvw0Z/FbXOk3E7WJhlLSPLwjwjnEePau412O3kvZmv0FvEMJYkEb1ToS2OfcZryz4U6rYXdvP4gDB4o/3ccC9FycASg9M1t69dRQ6h9seSTyTldj/AOslP+wD2H8qAPqr4VCyt7+SS2YS7kQGUH74QY28cc+x+tfZ3xb8Y3M3gjQ4IUEkrwswUn/lnkfKD0/hOQefSvzx+Gmr2ME9lLNH9ljLDbCvIUg5yfc969P1T4q+J9Z1JdC0O3Edgkg/0tjkowJwqrnvQB9UeJviRH4d8I2CeCHin/toNcXLEcW6phdijoDnNfrf/wAE2fAsF+r/ABV1XDqoDRAZxntjP61/NRqnxktlb/hHI38q3MqiRU+9lTl2yejHn5enev6AvAn7fv7Iv7Bn7NOh+Lv2j/Ea6Fp+uw40+Fo3kldVXh9kYJ7d64sxrThRkqe7N8PFOSufrjqbzXmoXmp3Ug8vOVU9fwqxpWpaxLp3mxS/aGfBQODkL7Y/rX81/j//AIOhf+CZ/hdm/wCEdg1TxM652mCNl3DtxJt/lXx98Qf+Dv74QQg2/wAMPhlrL7RhPNeJVwPUAE4r+Z8x4DzDE4iVWMd2foNHNaMaaif2YaUVuLq5dy1wAAjxjJ+Y+g9qh1jRJ77bBDas8oGYXwAF/wB7oB+PNfwN+Mv+Duv9qq9mK/DH4Y6dbxHJzfNIzZIxn92U/rXx/wDEH/g5e/4KlePIZY9Gi0bw8jjlreOTePoXkP8AKvSXhPj6nxM555xBPmgf6SWhf2xbSTG9tlhmjUgtI+1dx4yCM9qr2s2mW13IuvatYQoUwm+cfIR1+9jr1r/Kh8c/8Fff+Cq3j6EtqfxivrKKYYMdowQAA55wpzXyx4s/as/bK+IDFPGvxX16/R/vK1xJtx7AMK9nBeDE4q85I8yvntz/AF5fFvx8/Z/+Hqi98VeNtNsRHkf6+IDnjJG7Nfld/wAFCv8Agox/wTk8Vfsp/EP4MXXxV0yfVNf0u4gigV2dmkZPlVSqkcn3r/MH1m41rxAwfxJ4j1W/kJz+8nc/zY/zrA/4R/RftPmoLhmUZVpJ2Pzdjjp/OvsMq8PKWEkpcx5NXN3PRsl0ozaVYTOwKLBqpmTI5MfAz+O3Ir/XY/4JueNLjxX/AME9Pg94pndWDaBZrJnJY7V2dvcV/kbeI5ZbnR7p5GLMQCD3wBjnt+QFf6n3/BCLxDH4z/4Jd/DfUpGM0umQyWQwc8ROwwQfSsvEyk1hoSOvLKnu6H68PfWsv+jooJlwAnUY7ite4tohInlIqBRz0GPauUmt7fy1k86OC48wlcHkk+1N3Xl9aPPeyBJiSAqHIBFfztDN4Qk4yhc+mpxlJJovTPG0rRKBnpmuY1MvNGps5XiEb7fMTBZSCMjnsatxLeWun+ddEu6nOAO3vWNetfXEoiBWCBz5m1PvNznBzXzdHEr6w5WseraTg0z+An/g6U8Ev4b/AG7/AA/4rePC6vokBSUcbzCWRvf0FfzfNnzNzeuePc9K/re/4O5vD3l/EX4O+KIYyobTryJj6sk0ZAz9GNfyLGV5GUqcITuP1H/16/tDg2qp4KL6n5lmcLVj9Lf+CPX7Ndn+1d/wUZ8EeANXt/tOl6ZeLeXuASqJbgyHf7EgCv8AT81S/ebURPpgMUFmfskMQHVI8KSRzgZ6YPQV/Fj/AMGkvwwg1Tx38Sv2hb+38yW2t/sMLY5BbMhI98Lj8a/tJ0bS8h7kzHzm+fBx/wAtOT175r8L8Y86lOu6MOh9rw9h0o3Zqy6jcXU0mnpH5QOMNxkjqelSz2VrdxwzadD80XAduoPrVrT7ALd+a5J7MeOfyHSrd9pMxUx2+ViQbl2nAz9K/AlQqtNtH1kpxuomNqEB0u3i+zhp5j99icY9evFeUfGv43+Ff2f/AIQ+Ivjp8QJBB4e8J2b3rSH5TNKoOyD33MRgeteoTtdXoSwsnOGUmV1+bBPAAz3r+Xz/AIOpf2mb74X/ALNPgv8AZJ8JXJSbxfctqGotnDtBb8IrDpguf0r9H4AyaWKxMYNHhZvjFThY/j1/bX/bB+Jn/BQH9o/W/wBoD4q3ks8Ety0el2bk+VbW6cRxqnQYHfv3r5vdhIRu4GMYHaq1vDFaWsdrCBtjUDj881KpDdK/s3LqCo0o049D81xFZSk3YfhFB296sQkbcVUyM4qhc6zYafMIbmQKx7Hg/rivQqctuabOfnk3ZE2up/oDNjOHU/lzX+p9/wAEwPiRP8Sv+CVXw78ZeGZIpZNN0+CCTfkL/owETg/Tmv8ALKlhuNcsZodKjNxKFIVUBJJI4wO9f6G//Bub4m8Vz/8ABKHVvBvjLS7qwOiSXTRvco0aSJMfMyhbGcE846Vxe1ouXKpajtP7SPpP40fDq68VeD/ib8PLWTddalYJrVlbgsCJYMrLs5GcjBIrlvgfe2H7b/7AqeFdPBHiX4dl1tnwTKs1sS/fkBozgD1Fd/4u8TSeH/iR4c8WyXi2sZaSCT7T8y3FvIRGYdy4wTkEZH1rzT4EyaN+wF+2Tfrq0n/FvviZIYo3k4Sy1F2LiFsHA3lsKT13AVsQfffwM8d6/wCO/wBl3SdZslK63o7rFslPzM0bqCCTxkg5IJz1r6qicXXh6LxFrsAdrmNRd2vG1m43kZ6HJx9DXzz4E0/TbfxPrTaaltpOk6hIrizjfEqXABWVgvQhjyDXtur6He6z4WvNIaXyLWZCI2iz5inGCQT1JPNAH5pf8FJP+Cdv7JXxU+CGo+L/AB6Y7fTAPO89lz5EgztkjYKWBU4AH5187f8ABHj44eMdN/Z6h+GHjGV7waNcywaZcyHl9PVyIWPf7vqPSvvH4p+C/EPiD9nrxL8DLe8F9b39rMkS3Tf6QrMAfm54G4fLivyc/Zpg1H4I3y+H9bja1uoCbWZWOQSPu9OAfcdqAP6L9P8AE0c0XnNICG6VkajdJev5uQeetfHngT4p/wBoJ5MrjAB716v4d8WnUbk2jnHPHqTQB6y8abPnXINZdxqFtYEy7RlRwParEF0typ2c7c8CuV1JWe43yjKkYoA7Kzv4LnDx4Utzg9K6KQMkO63KqqHGf7xrymKSRT9njyA3cdq04Ly8Qhp3+WPovb60Ad5ZRyTSedKAvuO9XrnUJbNGWJ9qKMmuJk1ieJPNY4Q9PXNeV+MPH8mm2s2oSyCMICBk9/pQB5n+0V8bdJ8FaJcXV9KSSjbDnABHqe3TvX5q/sTfAPxN+3x8brj4vfFKB4/A/hy6LQRuP3d1MjcZyfmAKjdx0461R8f6V8QP2r/jfYfAbwQJB9rlE2q3eMrb2gOWHdQW6Cv6GPA3hj4ffs3fC/Tvhp4Ht44LOwiCbehd8csf9onJP1oA9bmksre3h0nTYhbWlqgWKFQFVFAAAwPbNOtroW84ngOxgMcd/evLfDnjCz8SXskxlHP8PvXpscDyAkDbjHXjrQBfuNQubxRHJI2Ce1fMX7Sdrp/iHwv/AMIzrdqLu2v8xSBsMAGGCMH1r6A1TXtE8MWDap4nvIrC2jGS0zqnQdsnmvh/xf8Atx/sY6p4og8IweLbeTVhIEWBzhd2cZ3HjigD8Ff+Czf7F/gP4x/skf8ACIeCtHXTU8NIJ7P5cMXj+YqDjIDng5r+D7S/gjrdl4ljGm2bCW3vVLIOcMnDfrX+qx+1Jq/wU8ZeBr/wpJr+nu1/CRnzULAnsMGv46PHH7JWifCv4gXuoao8bQ3NyzwsBlXOSVJI6ZoA5/4W/C7TNAudN8WRESveQo/lDhkYDnOfevs3xb4v0iz0iCa8/e280YiZk5O/0479q+TLy9u0WHVrOeOx+yYWVXAI255xnpx3pfiH49gtdN+16Dcolu0gJuIh5iggdl6ZzxxQB6P4g+H+r6l8E2+JNtC4m+0MoZDjdaxH5nPvk455rwn4deKfFHjv48QfCjQbr/iUxC2u7e6Ynf5b4Jjz9civ0y8Maff6/wDsL2eqWwKTCW7KqAMXMTYZkbP3enFfnD+xx4c0+8+PuqadeBXtmS3ltfJYnyxv4TJx0JPegD+zT4C3lppnxu+H/wAMhEph0fSftJbqd8gC54zX8hv/AAeHftN6p44/au8H/ssWUwbT9Ask1GYA9J7hmGD7hADxX9n/AMBvBEmlftCW3iLVZPltvC8bxh1w2AQpIOMfLgV/mTf8Fx/i4fjZ/wAFVviXrgn+0xaVfGyhYHICwqBgHkYyTQB+WiBYkWCMcAYNKYhjipFjbzas4WgCsIxtqPyleCWI/wASsPyq5gZp/lh1wvX/APVmk1cOtz+4f/g0P8V2eq/Ar4peA9SO6CzeO5ZB94h9wwPrtFf11aLYWmtxDXtWEonEh2WWcYDDCK/uAM1/EV/wZ5eJrJPi98Uvh/qGf9N06GRNp5HlyE5A74zX90HhWLzQbnDzrG8ge4lGx3PTp7etfxT4yZdbM5uS0Z+o8PYjmo2MXR9NtdJmfU7wLe3byFikeCEY8AL3AxjP4mq406SWa4N0+LlmLRBOkYHY9u5wK29V17QrS+/suxmhjaRDwvO0+rMO9eN3tzDqGsWMthcM/wBikfckf7tJTgn94PSv51xkqKn7OCPusFTlNcyLk322zEtwzB7mbDhQV+Vs4BPPoK+F/wDgsL8P2+Kn/BNH4wabImZNL09r5QQMs0Ee/NfYuoFU1OfULFlmuCvm3DAnOw8BQv8As5P1rzv9p3wbqnxE/Ya+Lmh2ztLDqHh+7S2djlnCwNncor7/AMNpN42nJdJGXFMYrDOVz/Hx01lksvsjD/VswOe2TWufl4TpUP2FtP1jVNMk4e3uGXkY+6xHSgE5r/R2k20pd0j8Fr01fQnHWrMczrwGqo27Hy9aehLja9anNM0o7+WMbQBU/wBrJG4+may1ynC/5/nUsTDd846/yoINBbgSPz2p6SFm2+nWqUal32n861oIS2WAxQAxn44qym4D5qU27EYANW/L6ZHagCKIEnHareAOBSRAFcAc1YVMjHU0AVtoJzTicc1PtViUPUdqhfyohk0AN3DGaaXGKpT3MSnJbFUJb1SMI31oA1dyn73bpTWuFRCXPPbvXP8A21VO3OamkdWUbDk0AXxJnoaS4mxZyg/3G/lWWZdqkd6Rpc2crN2Q1pHYql/Eif1hf8EJ23/Aa5A6idhX6BeJFL/8FEvhJt7u/wCpNfn9/wAEHQD8DLkHvcMf1r9AfFDbP+CjnwkjHZ2/m1f5ceKNP/jI8T6z/wDST/QXgz/kWQ9Efvt8RGC+EPEhP/QNm/8ART1/OzqDg/sxfB8dz4rm/wDRlf0SfEdT/wAId4mJ/wCgbP8A+iWr+dW+4/Zm+D5/6mub/wBDNfguUJ89n1l/mfU5erxZ/QNfgr4ftVbvb1ykP+qX6Cuq1NgdEs19LauVh/1S/QV/T3gu7wxF/wC5+TPxjxA/jQ+f6H//1v7Mr/5rC5PpC4/NTX8hvxSXb8A/imc/8zXZf+hv/jX9ed5/yDrr/rk3/oLV/Ib8VOP2f/imf+pqsv8A0OT/AAr/ADI471xEPRn9f8AK8ql+y/U/ot1oAf8ABNTW8f8AQkXH/pIa/ko/YIO34FaeR/z3uf8A0Kv62Na/5Rqa3/2JFx/6SV/JT+wUo/4URp5/6b3H/oVGbq2UULd1+p6/hy/9rxXq/wBD8f8A/gr3/wAlC00+nzfyr8pmYtI2a/Vr/gr1/wAj9px9v8K/KKU7ZmAr+4vA9L+wKb8j+f8AxcSecT/roIyqzAk9KYSTyacQME+9BCEYFfqp+Ui4AG4VGeeak+UcdvWkIB+7QAynKVDBc4Pv0/OkeW1tY2mvZFiT1Y/yr7q/YC/4JoftS/8ABTr4n23w++DWkTWPhiKZf7R1q5Rkt4owRuO7HzNjOFBGaAPmf4F/AT40ftb/ABJtfgb+zd4eu/Eet37+W3kIWjiGeWZhwqjuTge9f6jv/BKb9hCf/glp+w3pHwq8QtC3ivV5vtutTQ8qLllyEDfxbF+XI4r3H/gnT/wS5/Zt/wCCY/wgtPAnwj02O88R3aIt9rM0YNxcyY+bk5KJnkKDivoz9ozWjp2nDTgzSPEu93yMDuR/SgD8sv2z/ipquoadcrDvkFycSIgBLcjj2HHavwK+K1vHqEr3l6ZbbyiAB98rkcjbnDE54+lftb8bobXWtHk1gy7VdTHCGH/LQ5J/DA71+RfxE0XRtNknh1ZTJa2yh5XT5dxHXbjBJx7jpn2oA+arTTrM3DQ2l59qjtULpFKuxskZwzDgjjPNeUeOYElnuE17/W3Gwx/N+7jTbwFA4JrupILm0t5ZbuRLJr2QyI0nB2LyEb+LLLge+fSvPPFQtdW3QAgu6uI4ycMCVAyAOy9vrQByvw8nnudPvpljmubuBdqWaJgIoBw+B19Qa8j0/wAdaprPxDv59bb91EcwouTlsbcAeo74rufB3jeP4b+HNfsbRnbXcGITy8ZjIPAPQYrxPwqunz6mNQ1CUZlJaHb1EjHncc4waAPr/wANeI7/AEWzj1+UtGpcbolU7gSAQT7Zqrf3uoNfyeJNQAUWm7bOzEgt1+VQRnGetQeHta0SCMQXkpklg2/aSUwGVhwAu7jjj3q7ql5pcekvqTKZdrfubePnAzjB5PagDyq4+JUun+JtM0272/ZGaRjKcKFBAJbn7xGa+ef+C2Wp3/ibX/h1e3t3JfaS+k2/kb/9WrAAEqvuDn3rh/GvibVNZ+JI06XCtCk3kwjlY2kIAz7nrX3H/wAFzPhRbeD/ANib9nrx1NH5eo6paRCdiOm23j4B96yq1IxtzGtN2P5u2sLKN8QQouPl6Z4/GrKZQkA49gAMfkKVjvYsMfNznn8qk2nZnA/OtlD2i0QSi2NUR7syFsnpyauN5fllSv0OSDVHz4EI3OgPuwqObVNHgH+kXUa+wOf5U9nYjlktkaOQ6DcS3Xgnio3UoNyEjj2rn5fFGgRZ8mZpCBwFUnJ9Kbb+KIrkgx2NzL7Ip/8AiaVWvTj8TNrSa1RvxxMf3jAGnGFgwHrS+XrqLFdalpN1p9vKuY5LhSiPjrgnGfwqXzY2IKnnrz2q6Uqcl7upk4O2xR1RHj064x18thX+kd/wa6+Ov+Eo/wCCZCWt4+7+zdZu4gM/dztIx/31X+bveSMbKZGGS6kCv72v+DRnxTa+JP2N/G/w6eXE+naqLnb1wJkHJHplK+C8SqXNgGl0PYyma5bH9Xdxb2ls3nSRrJtYlWIBKn61g3uoSQ2wlyE2nlVxuJPcAdq1XHkxygOCjLsYADAI756D0rlftemW17CZUzMyDDHou7pmv4tzOtyz5Ufo2ApKyZtSXWquFWdFZJCAxRvur6n+tZV0Wgm8oSKTkBGHPHpmsnV9NjSY2djK0b3LBpZck7UPXHar8lvAsijT8m1gGAOrN/tZ+tc2Ah+8XMzeronY/lX/AODtHwPJq37Onwy+JUagPpd/d2jt1x5yoy/qpr+GkTmG0e7HLeWT7cjP9a/0TP8Ag5v8If8ACU/8EuX1dYsNo/iGylZgOQHWRf5mv85iO683wu9762zEfUDFf2x4aScsAnI/Kc6i/a3R/e9/waceChbfsM+OPFVhIst/caoY9jdswgrkn8RxX9R9s2mQvJb3OUkSOMS7um4ZBVT3I74r+a3/AINS/sdx/wAE2fFbXO5lOsMH2nDAeQuMEc1/S3rMEGpyro8YVRHHmE4JYMMFs+2Dx71+A+KlO2NqM+yyKrL2a1J7bz49NGMKzqCvPBJBO361Rk+2tGj2zMChO5HPf+ornFEuoMNS+0iC2s2VXQ87mXA46YyPxq0L++guTqbbRaOMKOS2cDBxivx6k5X0Z9KnrdmpGby6s2urciGT73lj5Qzr0r/P5/4OlvHereKf+CgHhzwTJN5kOk+H7dtvoXJdsfjX9+bWlxcTWokyQX3xuM4/4EOlf56X/Bz/AKRe2H/BT+0vJFKJceH7QjA6nkEc+lfvfhHQ5sQpS3PkOIJc0dD8CFIVeKsIvy5qpGoJw3QGraE5KjkV/UFNaI+Fpxk1qUNRRlsZpEYqVQsD7iv7lv8Aggl+w9+wn+0N+wvZfGD41eANH8S+JhqU1tLfaihldipUrv3HGAp9K/hxu08+1kSMdVIP41/dd/wai6/H4k/YT8WeDowLm+0zWZpRG/ON8QVWx2wVr4rj7EVaOEdSm9T2MroRcnzI/eDwr+yl+y58N7Wa98BfCfwvpjWzBI5INOt97ZPDK238eOa+ytA0SOb4baj4cjgiSCa2ZFijRUhORnaFAH0Nc7q+nQ2zW5uYWmMLIvlp1Vm6n3ArvrG8ilml8K6eC6tC7B1IGHPJHTrivyngzOqlXHWqM9vHYdKldI/HH486D4bm8GWt9fweVpAvJLW+ht3+a3ZsbZF9Np5r43/a08ZzeKfhRd/CPxFHHrXiDQLUNJat+4vNSsEXdbalYzdGuIhxx8xK19/fH3T7LSm1rwrqLKul+IwrJK2FCTBirID0LEnP4V+c+ofB+5+LWgXPwr8SagbD4g+Do2v/AAnrBOBNCMt9lkJwSDzgEc54r+iz4xn5Q+Av+CqPxT/ZS1izk+IEl1448MoyhNeO4XSRgYW3u4myfMj6c4r95/2eP+Cyf7L3xa8I2ut2Gu+S0iAi23DzIn77oydwx9CK/m//AGnv2dIH8Q2PxCeyls9L8Uyh722j+VLbUYSVuFKdNpI3BcDOcV+dfiX9lXRbzXH8deFJrjwy80rIvkOUWRlPDKGJ9fmHQdqAP7gPGX/BQH4JeJb1NU8P6tG8xyss6DYXyMAFj6H2r4b8d+NNN8SaxPq/gGc3UAk8y5uSwLNOTuCg9x247V/KjefBb42aTo90t54uupHt4nl04Qgt5sytwrN/CPTIOa/Sv9h7xnrej/DhdL8Z3k0uoySC4vPObJjnXIRCB1BFAH75fC/4j2skdtZOWBnIbGeQe5Y19qaD4paTU0kiPzLhQ46HPpX4tfC3xTGdfuVgk8u5mPmSgNuCjqMDsGBFfpr8OtZnlhhmkbbxwvXj1oA/TXwrcxPo6XJYepOeT6il1qW2YvtbGwbh7+1eFeAvFVu9lJHKx8tOgB712+q33+jC+tfmleM9eij1oA6i2vPPhLQKTngHvmr1jEph33AJYAj8e1cr4TuoTZ/bfNL8fN6E+gruIJ1lkCjonUUAJeQwRWjSzNvJyAB2wK+N/il4dm8RtLZ23mM28CNVyQWPQkCvszX7iOz0qMWKCVpjyPc1l6N4as7Mf2xOA0gO5gRkDjnH0oA8/wD2evg94Y/Zp8EX3i3VZ1Osah+9urhxhguc7T/sgdPQ18D/ALWP/BRzwb4MkD299GlsGZFnZhkvnHA6n06GvnP/AIKzft7aX8GfBlx4Qg1eOyaRT++LYZxg/IAO9fyHfB/4R/8ABQP/AIKx/GCbwZ+y/pV6mho+y41W7BW3gQ43N5hUBeDkKOSOe9AH9Ymnf8Ftf2dfgnpyaz488Q20RLf6stmRyQTwigtz6EV85fEz/g4w/aw+Od7N4R/4J2fBfXfFcDfINWeylaDeeAQNmAPxr6a/Y5/4Nof2Lf2M/D0Hxb/bE1CT4l+LbYCVo7gsLWOTH3VjLHcAe7Aiuh/bk/4Kuat+wz8PLrRP2WfhrbafZWkfJ02BY4QvRW3iMD68UAflr4k+CX/Bzf8AtcaM2q6z4U0rR7W/BKJe3cFvJGrdthcsPyFfnF8Xf+CSf/BdX4QvL4x8R+BrfW2t8uX028iuJD0J2qH3H8BXI+Iv+DlH/gon4x1eTUbXUIdNhDELEIhL065JIH6V658Nv+Dn39vHwnJHH4kvbfUdp/1XkxpkD3w39PxoA/KDx78Uf22vhP4gk1X4ueEfE+gTQuGL3NvcRRxOvG4Fl2kDHrzX0B+zR/wUX1nVdYk8OfGLUG1ixvpR9oMuS8JPyo6k+hPIHav001L/AIOVNd+JlnfaL8afhzpuuR3oA/eOOgOSdmwrnrXx38Tvhx+xP+3zpV5rXwft4/h946mAn01ojstbiXGTbyKoHzHopAHNAH1vqWj29zJc6+rGYXMfyv8AeikiK5DKPXFfPdzKV0e70+OB7qSGTfDEo2bBn7+D1x6V87/s9ftA+P8AR9Buv2a/jDEbDxN4Yk8lBMpDTQJ2yepHUEdRX1DY3dnHqT6pEmdKu2ZVckb1kx0HcDr9aAP2Q/ZXnl8e/siaz4Y1ZVEul3cBSdQd6/aflYP/ALPY182fAL4XT/DL9oC98P6nZGOKWdUjST70cayBldemUbqK98/YI1mZrzXPhZeSoE8TWphd+qo+MwsMdCCa77Qvh58QbT456PqPi62klK3n2G7kClpI4YnCRuPYqOpoA/os/au+Men/ALJv7KHif9o/xfqCi2sfDAtrK1Ixl2Xh89clioxX+P14x8V6z8RfiV4j+IGvuZbvWb2a4aRvvHzGJzn6Gv7Yv+DlL9trxJ4u0q2/Zg8PXLRaLZW0clxEuRuZVwC2OvTI7V/EWi24I8sFGXjpQA6IAIWqNyykccVaUKOO1RyDnI6UAVvM3NhRVhSyMvFCoi4wOtWAoZgp5FAH9Nf/AAadeLj4d/4KA6n4ZAz/AGrplwB6/u03j9RX9+kniHUdWR41ila2tpWL7PvFndsL+Vf5pv8Awbs/EGD4ef8ABWTwQbyc21rfia2Y54LTQsig/wDAiK/00L3T5bCK/isZxCyyn91x84bk/iexr+SfHejL6w2ux+n8GP3dTzy5tb3Uolup4TCkRKG1ABaQZ4+Ze/uadNp92tqn2yEWUCszQwlN0pODjdjqCT1rttLv7Xw7OtrcIJVMe6MA5x6k+4NPn8d2ejWqapBZG4t1yN8/DDPYe3Wv5fwOHoy96crH6FUxVX4acLljSfD+nwaHDfTTRfbZXDNKFySM8Jj6DkVR+IfhhJPh74y0HRpVNtqGkzqY1HKyOrAgAdMjrXjNn468m+OqNugt3mxboD1f1PtgV6/4e1VvFV1NbQgW9tc2s6THPzyXAQ8gH+Ec5r7Tg3MKdLERjT3vuePnmXzVJtyvfc/xnPihpzaL8afF2lN96HVLpB9FmYVyKovcYr6K/bP8Ot4T/bI+IXh9h5bRaxd4/wC/rH+VfPSoWIH3sGv9F8vqc+Hpy8kfimJVqriAUFsEcetKkZ3hQOvSr8UIcbSOKsrABtdSBkd66zknuZJinC5281NHCx2seM1qpFKgXMisQcEVKLdi5IGQvJI6UEEUNqV5XnPftV+0jaVgoPNPiiaOLLgHHv8A0pN4hX5eN/H6UAXcbDuzwODVWaVQpbuKgbUY8hG6DvWRd3DTlsHb0x70Ab8V4EkO4AirP2qFEMgPNcWZ5AgIOSTg095jsKMeR0NAHTNqMcZ3N0PasLUNTmuHCoeKyXJ3YBqJg5PHA9KAJmYt827moJZGY7WBOPSqsgdTuBqu5mHKnBPWgCyAA+7nj1q8bry+gqjGR1fmrBViuD1oAsbi4JpWBFpKp6FD/KmRK1X5I82cp/2D/KtaOsGyKcn7SPqf1ff8EHQf+FG3HPWdv5iv0D8SIX/4KT/CRPV3/QtXwB/wQbRj8C5z/wBN3/8AQhX6B6+H/wCHlfwjQf35D+rV/l94o6cS4i3ef5H+hPBj/wCEyHoj9/viRGT4O8Tf9gyf/wBEtX8599GB+zB8IG7/APCWzD/x81/Rz8SePBniQ+umT/8Aolq/nI1MkfsxfCADv4um/wDQ6/A8q+L5n0OWVHys/oA1OP8A4lNoF6G3A/OuMSYqgXHQV39+jHR7IetuK84LBCUPUcV/S/gr/DxH/bv/ALcfjXiBN+2h8/0P/9f+zW8YDS7nI/5Zt/6Ca/kJ+Kn/ACQH4p/9jXZ/+hyV/XXfSj+zbrnpGx/8dNfyJ/FBgfgF8UwOf+Krsj/4/JX+YfH87YiHo/0P7A8P42lP0X6n9GOtsD/wTU1vH/Qk3H/pGa/kp/YM/wCSEad/13uP/Qq/rK1iSMf8E1NZTPI8ETEj62Zr+TH9gggfAnTiT/y3uP8A0Klj582UUPVfkz3vDiNsTivV/ofkJ/wV5/5H/Tfp/hX5RTf6xz7iv1d/4K8/8lD036ivyjn++y9+K/unwT/5EFP0R/O3jCv+FiTX9aIduVOSM1E4APFNPU1Tu9Rg02MTXR3FiERFHLsemOlfqh+VFonC4PQ++KuaQl/rOpQeH/CFq+rapcuI4oIFMuWY4AxgknPav6V/2Mv+DWz9qr9rb4S6F8avGPi7TvC2leIIUuI7WZZHuBC4yDtTABK8jJH1r+vP/gm5/wAED/2K/wDgnda2/iezs18YeMUUM+rahEh8tyOfIi5VAOxyT70Afy2f8Etf+DWr4xftBXWl/HP9uh5PDXhmULcQ6EMi7nT7wDRnPlqwPf5j27V/oAfs/wD7O/wc/Zj+Gun/AAq+COgW2gaLYRqscNtGqZIHLuQNzOe5bJ7V6deeINO0y080/MVG1I05OR2H4VHY6/8AbrZbhoihbPyHqMHHNAG5MMRtc9RGCfrX48ftKfEu/wBS1+6gjgnHnSFFRFzhUPLHHODX7CQ3UV3GYyMdiK8a8ffs/wDgPx3ZypexGGZwQs0eNwB6+3NAH89HjD4gWl9aXWn69Ggt71fLEQILZT7rqME59R/hX5gfFbVYfC3m3eoXC3K5YwwnLFdp+UkFeASRxX9E/wAdP+CVt14v0aWH4d65Hb3DA7WuUPB64BU8Z9a/MXxn/wAEcP2qrKNrvSpLW/kjGSHcOHUdlJGQfrQB/P5478Q3eratHqV0TPJKxkkjQBUjVTlmHA71BoFrbefda1eky35AKvK37qKN/ugDpuPtzX6I+Ov+Cc37YXheS4mu/h5L+9fGyBxIm0A/Mu1eM9Svc18y6r+zh8c/BF3Pp+p+B9QZpB5rK8MwjDgYAztxxQB4L4stvDfiSwaxitRLFdqRPLGBhSByS3WvkDTtE8R6VMsMSpHBbyFVGedueCPevtjxl4a+Ieh6elpq/g7VoLXcTcvbwyJ5g/757V8teK9U8LzSC31YS6UEXCmRwki89GjJzn3oA14fGEdrcLBqWFSEiMqxxuA4+9+NdVeePNTfT3uUjWGBQyojnrgHbsPc+tfNV18Q7TSrkvp9xBOYBu2sMxsPQyHlW9a8417416HDbqsV0pvLjcxXcpjQZ54znIB44oA8L8c/Eabw78TbwpI7zsy3FwcY24YkAfgBX9Pf7a3gPWf+Cv3/AASQ+D8v7GkKeKvGXgGdY9Z0qxKveW4EZiO6M8gcKQRX8sOmfBL48ftE+O/+ER+AnhPUvEGpaw3kxGCCRk+YbSfM24B9fTrX97H/AAQ4/wCCWfib/glB8PpvG3xv8QMPHPi6OKO40a1/eRW8bFflYjrIpJPOAACMnNc2LoucLrobUE3KyP5ZPh9/wbcf8FXviPaQJrGhxaDHOAzfbXWEqD/fHUH6V9teBv8Ag0M/a61KNJPiN460qzjYgkQzM/HfHGOK/wBAPV7u3upUg1GeTeBkoCwG73Yfy6VzMU91aavcwQy7opPLPksSwjwPvKT2PpX4Hn3iXi8JWlTUrWPsqGVKUU4o/jd8E/8ABnp8KrRgfiV8WJhKOWSFIyMd/vMP5V9p+Av+DUT/AIJ6eECU8Wa9qut+WAxY7I0OQOpUGv6a5hEjrOlvGWjkdzjBd8Jg446EkcdOKrJdG4t5dR8iRoE5EEmA4OcnHPPP+cV8rW8ScXOPM6h0xyq26Pxz8Ff8G9v/AASe8IwRXUPgOTUthDLJPPJsJXrnlV596+q/B/7AH7Cfw3aCPwN8JtHkE5MQdoopFXYoOGZgSG+nWvtS6lvNbv7K5in8i1QbpIJOGbAPAHT86xBBcx3PnW4AgeRpBAv3ieBnPQfSvna/G2MqVFeozupZPTauz+Rz/g66+EPg/Sf2PPAHxD+H3h+z0KCyvTCyWsKwmMseFOwDIwDye+K/h5hZpLaC4ZstJGrfmBX+ib/wdA+HLTxT/wAErF1myGF07XraQgfwhy+4H8TX+dfpMguNGtLlOcoF+gHFf0z4c4+dfL+eb1ufM5thvZ6I07r5gU7cf4V/Y1/wZ4+Mmi174zeA42PmC0s5kxyFxK6k49t3PtX8cksavF8vJ4r+n7/g0a8Zr4c/bU8f+AXJB1/R/u5wT5Mqtx+ZNerxpD2mW1FY8rAy5aiZ/fVdQXWoCNZmNvFGR8r/AHpNp547g019K03UlMcYYIw+YNwxUentVc6bd2/yjDiJ3CFjnYM9c+o7VHcSGWJLW3uPs87Dckj8h07j2NfwtnCSqn6zhYpQUkat8llND5c7jzIgFVRwQO3NW457a336xbIZECqrMo+Uc8gDvWLpgk1FCB5bnO1IyCGYjruz2rWtGbSGe0jRFVRlYmbKmT0X1+lZZfJKopGeKaV7H5bf8FzfAcHxC/4JYfE6FUMKWUUWpIT1ZoGBz7Zya/y0dESO70AWZ+4YpU/AZr/W2/4KV+GrjXf+Cd/xh024gEf2nw5dNhG3AlEzgL/CePxr/JG8MF0+0r0SO5eIj13YOa/sbwlxPtsPKPY/MM7+I/un/wCDQ7x1Jqn7Lvj74b27B5LW+W5VD6NE0f5E4zX9b8Hn6VGLHd51xKV8xz8wTIGcY44PSv4UP+DQz4p2Ph74w/E34KXUogutT0wz2pbn95FKBjHptYk1/bnpd9qW9biBCZIixkRMsHlB2YBPGOMn0zivx7xXpyjjJxsfTZI/3aOlvzbx3LpeRIIXYFWLYORxnH1obTbgahDfgsYk+8Nvy47gfTirv9iXqKlxeTJDv+aSIgvnPOFA4U1radLYJcyxxrIjOQN0jFhj/dxgfhX5FQoXPoJ4rSyR0lvZ2UcRknC+WcYHUH0r+F7/AIO7PhA2l/Fn4Y/H61iPkalaSaZLKOBvt3D4+uxx+Vf26TrdtM99eAqsXEYHP/AtvfHavxt/4LtfskXf7ZX/AATt8RWfhu2jufEXgyT+2LJI87ykQPnAf7TJzj2Ir9h8PMzjh8RGm+p8xmlBzi2f5nanc3y9CKvxrtUZOB3rmrGW5ETW0yFZ7dvKlUjkEY4IrWiuXVcMAPp1r+qnVU9YnyE6TgrF5eE44Getf2Jf8GgHjNE/4Wz4KVmkaLyrjyxz1lKk/lX8cy3ClCJMAEZ46V/TV/waifGDwJ8Kf2ovibZ+O9XstGs7zS43Wa9lWFWKShiAzEDpXzPF+EnWwMoR3Kw1dxkkf3seIYPEmo6kuk+Hz9jTAeW6k5f5j9xR9K3tDuF0vWrS0RMWiDZv/icsNoOa/OP4l/8ABUL/AIJ8/DvxHcyeMPjJpSxksot4f3pUDr88bHofzr5B8Rf8HCf/AASu+HN5Jqel+Npdfe3BBWCCZmynAKqcLzX4HleRYqlieaMHfufV1sTTdHU+zv2mvB+madeat4M1WKW40y5l81XA3PbSPlxIuO2T19K+DPiP8GPEPxNtNK8I6JfLF430RVv9OmRyg1C1jYYTjGX46d+a+tP2Iv8Agpb+yZ/wVy07xK/wQS5sNd8PptnsdQVA81ux2iTCs3fI46E13OqfCqR4LXwK0UlhrFncmXw9fsSGVydxtXboAxBwMnrX9NYP4I37HxLiz4k+N37Op+I3iCw8bXcLLZeIbT/iYWRQYt51XbMQh9ZQpr8hPiz+yxNoXi+fR7eFri1tQ32cEHnDHJwOB9Pav6wtHS8+JPhmLVtY0xrHXLcMt/bkYDup8t2+jfez3xXyr8RfhZpmqaj5dvCGkQ7ivAOT23e/X8a2EfzN3fwIlttIEl3bAXJG6B2J+6OfnB9jwfWvj8yX3wi+It1elSbO+27y/wDz2TOOO5r+tnx5+x1o/jLQmubGMR3DICyADcoC/Nzkc89q/nV/a3+AOr/D2/khtdPYWdlIRbj5gXkB4Yk9SvpQBk+G/if/AMI74gsn0PiJYlmvHckhnk+6FPtnGK/Y/wCA3xKh1vT4VMm6e4wEX+4vev5lNL8Xano+nXPg/VYytws/2iWXB8zBGURR02gHJr9Cf2ZPj5bWuJ9SuyJjhRtZcgY6ED6/pQB/SB4V8TQoiXVn/wAsGwy9nHuO5Nev23ihJomklIRs4VAOcHqDX5weEPitFf29pa2lwDvUZCNwvcMfwzmvQ7P4sA3rgGRo4jtRBzuYfx/SgD9CtF1jyL5Uyv2FhnaByJOhA9Oa9Hudc0mwIO7aWGST8uc9BgdxXwJo/wAUDZlWOI45QHJzzuPcDvWhN8SV1aQ3kUhKW4ICtwGIHegD7q+3xSosll+8U8n5jivEf2hfi3f+D/At5J4fi8y6jiOAmSQMck+1cV4Y8fNLoyveEFycFUfke+PSvIPir4m1/wAVsPD+h24uA52ENxgHrz3oA/PT4Cf8Euvh7+2T8Q5Pi5+2PqbanZGbz7TT/MxGozwpPJ/Cv6GtE1T9n/8AZF+G6eAPg3pOn+HNI06MhY7ONEMmBklmUDJOeTXxF8JfhR410nThYWbfYIlVgm3qu7qcd67kfsNaR42/feJNRu7lywdmlkc5Psg+XHtQB8h/GH9uTxF4415ovDFvNepvMQhUbowCerdq+edas/jD+0jbXXw2XwokUCERMzQh2lWT72FII289cV+7nwv/AGVvhd4GgNrcadDO/TcyquQO9fTGk6d4U8JFJdNtIbVYlKh1UAgdsnbzQB/A3+0t/wAGx37Xs0tx4r+Dtusi3rM4tSUAjQ8gL3/DFfjd8SP+CHP/AAUp+Hcstrqnw51e88o8Nb2rSKxHfKgjH1r/AFadb8X+WjJa3srXE2QsZk4Bx16DA78V5FdeL9R0fT5I9Q1uSa9Q+YrlvM+U/wAAUgDHvyaAP8dzxf8AAz4v+ANcn0TxlpFzpt3E5idZkKeWy9VYMAAa9B+F2neLfCOrW+oKWgRWDBugjcfdYEV/cr/wVu8F6B8WNMOu6joOnS3ssctuk6wiPG7J3O44LgnK/lX8o3i79mvxn8PEmudMgFxZwLu3yMcumOfkPHuPpQByH7Yia74x0Dw1+0n4QXPiHR1S11OWLnzFQYWRvXPQk16B+zx8SpfHCRWmuAfaZFS4VEP7sSA7iAfUEcCqPwq8U28GjXnhDW0W40+/HlzwMOH/AN30Ir1P4PfB61+F17M81mJLF5TLYncOjc4LD+7/AEoA/YP9gmS7Pxs06wu22Sy+VdXIPB3o2SpH+6K/oS17wXpevfEvTL3ScJL9pe/ulI4ltYYd4cfjgV/NT+wnqZg/aC0yFpDl52jCn5R90KPn9Mjmv6XfjR8QfDHwL8H+MP2gL+SR18H+GHtJ7YrhI3cFi0b/AMQwM5ppX2A/gG/4KuftE3nxT/bc+IGgRMGsrOU2uTzgoQP/AELIr8rHjVFwOw61q+NPFt78QfiF4j+Impk+brWpz3GWOTsaRjg/nWPGcnNFgEkix0qtHGWJB5q/9aakWDx0NICDysCoACsmc1rFF2Zqt5a9+a0hO2gH2D/wTl8YN4D/AG/vhh4lR/LUa3YI3PUNOq4/Wv8AWU8TeINA/wCEslmYvcXSqDHEo+RRsyST7Dp6V/j5fA/UoPDnx68FeIJCVW31i0d8f3EmQn8RX+u/ZeJtO1rw3bX2mIr291p9tNbkj947OAdxPpjFfy99IWhOPLVXY/SuBKkefkY3SrmeXX21ISCGJ1Oy2blnb0yecVc8S384tYbKS2G+5yv2WJjtj9CQOM/41zseu3NzqDBbfyZbf5CF+YuTznPQfUVtXGv6TpeI7nzGeVgGeL5jHnJ6+2OtfxbSr03CUL63P2n6ryvmMOPSEm1I6Vq8ReSSNRApTKpg89c4rtNC1O80vxNptrYQq2mM1xBIScOr+S53g+pIArFsVht73zrtHkhWExRTRnc8uTnP15/nW14djtNJ1iHV7xl3NcCMwM25lV1Khgp5B55r1OGajjiEonlZtGMqMos/ysf+CwfhC38F/wDBSr4gaXHH8s9yZh/vSoGr86bOORGAI5NfuT/wcceAf+EK/wCCrWu3Lrsi1OKGYYHH3QvH5V+IQjbeSgA2nFf6ccK1XPL6MvI/nPMFy15F5I41GQc+uad+7TdM/wB0cE+gpY9y4LciowCGVnGQcgivpZHBN6gsio3mKeRyfp61Ziu4zujkBy3X/dPINUhDLtbJHA5NV41cHarEt+XHoTUkGx5qzf6xCGf5QB6jvWW8qsnmAN8rEYJ4qWNV24ACg8kD0PQD6U0KEXqd+M59aAM+4V/NbjhBmo3QkhWBLEZXFXWjCv5bDco6470gVY8kcKOn49qAKCw/vPnyu8cD3qKQNu2uOnatOKPoCOfXvmkEEZ+8CT60AZSRqOc5JoMZHNa3kRDkL0/z61E0Tud6nb7DpQBlGPPWqkiHzMeta7xKnL8qfu+1VWi+XPrQBUEIBxnNaEQywzTQOMCpED568UASxRZYitB0VbKUZydh/lUEHUVYuf8Aj1l/3D/Kr+ywj8aP6vP+CDf/ACQq5/67t/MV9/61z/wUu+Ef1k/rX5//APBBsH/hRdwexmb/ANCr9BtVBP8AwUu+EgH96T+T1/mD4nr/AIyTE+s/yP774Ov/AGZC3ZH7+/Efnwj4kH/UPnH/AJCNfzm6ioP7MXwd9/Fsv/oVf0f/ABFj/wCKR8Q7hyNPnz/37av5vrwf8YyfByMdR4qm4/4HX4HlWkte7PpcvfuO39aH9DN1GP7MsT1/cj+Qrxm4LfaJP94/zr3eaFjpNltGf3I/kBXiF0CLmQHqGP8AOv6b8E1+6xHrH/24/FvEB/v4fP8AQ//Q/sg1Aj7Bdj0if9FNfyLfEjB+A3xT/wCxqsx+rGv63r+QGyvf+uMn8jX8jvxHOfgJ8U29fFdmv86/y44+rXqxt5n9j8C355t9j+iDW/8AlG7rrj/oRpB+Vma/k+/YMU/8KI09R/z2uD/49j+lf1ea9MF/4Jt617+BpP8A0jNfyj/sGAj4F6eP+mtx/wChmitUvlUPVfkz6Dw8/wB6xXqz8hP+CvJx8RdM/L9a/KO4/wCPlm96/Vv/AIK8/N8RNM9j/WvyjuP9ey/Sv7y8E/8AkQUvRH83eLH/ACNGRNxya3/ht4VPxC+OvgXwKqlv7T1eGIqO4LqBWA/PFfYf/BNbwRP8Qv8AgpJ8IfClvF5v/E4tpGA54EmSfyFfqp+WVItn+wH8EfD8Hgv4LeFPCVoAgstNtrcKBtwqRheldF4jZoNRjgUkDyxwP51Z0vz4NbtdIhAFra2Q3nHRg2APyFcpNqE+o3tzdzdVkKqP9kdKDNRQpeYSeYG+73I4+lbfhmcO9wg+8vJ9s+lcjeyMId27k9qtfDVxc39yWYsDjr1OKBnpJkKOA/P0qZbmVCCGJFdFLYQyfMo5rJltEhPrQA+O+yPmp32+RW2jp7VnFASQOMUoXYuetAE899gFVHzHqSAfwrNlm0qdWW+s4pN3BDIpB+uaWTk7qoywhvmzQBg63oHw61q1+ya1o1tdxnjy3jUjnrjgV8N/FX/gnL+wl8Yb7+0vF3gSztruQn99BCqnPqcA5/GvubVdJd7d3spAki9Cen1r4f8AG/xR+KPhPUHheMOhJwV54HSgD4Y8ff8ABv1/wTe8e+bqeqSalp8EJzKltOsAIHYgLyPpWf8ADH/gll/wR/8AhTLIIfCaeIXtgVLamhk+72+YKefavpi++JfxE8ZXixTBHdMGOPlQcc5bmuYh0DULi6uPEuryRySzMN7KMCNgeAOx59qGxpHqvw6134efDCRfBXwN8Gad4L8NW9uzQXFtAomLklQMgfLk8jJ5r1D4VaFL4t8V2w16RruS1H2m6kk5MhxkfTBwK4TRNMutI003GqqLiZv37RL0dVOVU4+ua9r+G1nd6fpV1qsA2S3o3yHONqhvug/Xt3rxOJMw+q4KdY9DL6DlUVz06XT2i1Sa7llZvOJCoR8iDvxj1rKlgvPIayWSMEL80gGBtHr7ilOoBztvnKQd5CxB3HtSanBFLBGYwSpYAGMEj2LAZJr+I88xMq9WVR7s/UKEFCKib2lQ337zfIjYAMTAc4Gc/nxVvyL24UXkO1HBwwcZz9K46M3ljK5ZjP5jgL5eRsHfIPUfSuli1M2MDyXRMiIOdvX8AeprjpVVypWMatNtt3INRm0uG9NoUMlwiBskHAB9+hrmrq4UQmYLsV5PmGcnPQbPSuml1PTtQwu8jA37SCHAHYiuTeVCwvrja0anKEMQCCfccGlWg+ZNI7IzSp2b1PyJ/wCC6/guf4i/8EqfiHbyQJu0wR3oSNcfLAVIJHr6mv8ALv8ACc3n+HrY9DEXU/i2f6V/rsf8FEfCFr4m/wCCdvxo0eMecZPDl7Ih4Y7liJHPtX+RV4ct1gs7qzj4MF06H+Yr+tfCRv6nys+Bz6tdto6h1zGGXtz+XNfuP/wbReL18N/8FcfDmi+YUTVLG9jcZ+8PILLx9QK/DTeyBVPOQR+dfot/wRo8UzeAv+Crfwx16KXyBNciAv04l/dkZ/GvuuI4ueBqJdjxcDP94rn+qvqksGq3c0GhybGs5GBBH32bnHPpVGWCUx/2nrtof3LYSME/KB/Fx2/Sp9Zt9Qs9RmudPBj2shORwSU5POe9SxXOpTW51LTsP5Y2spI/H5c8+wr+CuII3rs/VsJV/dKxJaanZoU1FVCTHgD+IgdF9/rWhpltZX0Bk+yNDKrEr5py2eu4ZrBtNa8y4c2QjuJVOHG3mM/UkD+dXbi+1J7wo0J3qDmZ+R9OP6Vw4WNmkTiIc2p55+0T4XHin9nTx54NmY3Daj4fvIyxzgsyNgY9cZr/AB074Np3jPxNoRO0W2ouBxggq23p+Ff7Pun6XNrXhrUYJXBhubaaAqvPzMp559q/xvvj7oV74O/ab+IPh27jKSWuq3ZII67bh8fpX9ZeDc3GE0z4DiCkuY/SL/ghX+0C37On/BTPwdrV9cfZ9P1y5W0uhnCulxlMHPo2K/1NgLXQ76VjcxfYpCvlQhf3iySEO2T1IIII9iK/xbtJ8U6x4I8Z6L8RvD2Rc6NeR3GemwK4YfkRX+uL+xB+0dov7XX7KXw8/aF0t4mn1XTkg1BIxuKXsahHViOQRjp6EVz+K2VXpKui8ortpRWh9mXjRq0sW8M6kknOMelQadDDcWjyly8hUkc9PSuZtdKmKLZ3UskqiVpGkPy7ucbepPGeuKu3QVWjhhYr9nOWC/xLzxnv0r+ZalX2c2kfcUqfMrF68v782tvdW6h5I/lZH/jBOOK5mW61QTy6fqFvHJDMMSMduHgAO+Iqf97B4NR3d7dz3ktwj+Xk/uFHZk9R71zN60s2pIiszLLC/mSg4McgOePQEVnSzypGScHaxs8v5lY/zwP+C+n/AATG8VfsJ/tEXXx5+G+nvd/Cvx3ctcxywruWyuJTueFiPu7SSU7Fa/Bu0uoHRJ7ZyyTLvjO4EEfn1Bzx7Gv9er4m/Cz4VftCfCvVPgJ8fdNg1fw3r0RhaGdNy5kXAdGwSrDqCBkV/nlf8FQP+CD37T/7BfjDUfHXwE0y78d/Cq9Z7mCW2jLzWSbvuXCjlWUHhhwRmv6w4B47hjcPHDVZWkvxPz3N8tqUqjfQ/Ffz34l+9uB+fsapyW9pdTrGJZLYsmC8RIZiB91sds+9chH4xjSVra/ge0nB+eOZCMFT0z0HvxWvF4ktL18tInGWG1lwxPYZIPFfrUaPMrSdzxLGvJZRyRxrcmRgV4/eHqvGTknr6VFaWml2482CAKn3zkg5bsvTvVd9Xs4IRI7xRxr8pO5Cwz68k1kRa5a3mpjSNBgl1KTlYhDGx3MT+vPQgVz1sNTpLmuaqm2tGfqR/wAEiP21NQ/YB/by8K/FK1fyND1uX7DrMK/Iht52VWB7fL94d93Nf6fn7RcGn+IfBmj/ABE8OyBLMmO+ingwcGQbkkGD0OB+Br/M/wD2Gv8AgiV+35+3l4h0yew8NzeCvCcE6Ty6tqy+SABjLRq+Hc46bV+uK/00fgj8D7r4Mfsw+EfgTq2tP4ll8M2EenT38iZM5VcA4Jzgc454rnpZrh5z9mpq5FShUitUWfDeoSXM8GrvGLZ7mHN4OnznDAj/AHua8U8Y6LG+si4gPyZGeACc969r0/Qn0/wu1qs7zw2Uu1ZJPvsoJ4I9s1yHju3inS2uolyr7SR6Y716kvdfKc1jE8OXItLeZFUEONoB5IPTP0r4V/bG/Z/0TxxZS3xVHJh3JgcK2Ms31Jr73t4mXCW5DO332IwAnf8AGuF8eW0a6HMNvm4VygPXI6ce9SI/im/av+Cmr/De7XWNOhZnWTbdSYx5cLMAM++OlfJreI5PDXiZNc0cCO2ePERQYVyBjc3v1r+hT9rvwRbf2ZqEWoZ/4mQdwCMgk8Yx6/yr+dDxnZRfDLWH8OX8bXGnzv8ALJ18th0GewJNAH2v8NP2qbjRDbWYuiXlYIMHJGfvH6CvszQ/2nLGK7d1vBJKibODwU/iH1Jr+f69ttX8MazLd20o+0XbCSSNPmEKDoQegzmvR9C+KMtnciKKRkEa4mZuw9RQB/Qh4V+OtiZFgW5dpDlkBYEIM5719T+BNWtPElzDr1/O/klMMAflYjsQcjcfav54vhZ8YYQ6C6lDBWLRlvvOD0B9q/Uz4Q/HrRbeCCLKRPOOUf7sf+7QB+tHhqbUJFOmx7Pn6sigfJ6Z9cV9K/D7wRa2zx3giHlJzuflye/NfBHgX4w+DWuxa2V2lw6DL4YYz9T0r6+8O/H/AMK29hsSRUjTGPmBye/ftQB97eH47LYDtSMZwPU/nXtun3Fq1v5cKruRcsRX5i2n7QOj28jvf3KRRvgQvuBDfh7Umr/tsaL4Ruo9KsE+2XUm0xfwh855PB6AUAfpbdXMIUy7dpHc8dK+e/GnxS/s24kjjbDqwRAxyC39a+Pte/bw/tixex0VI9R1WM/vY0JVImweGJ44x2r52g+N2qeMb+81HVrqKC3JAhCnJjl/iJHQgdsGgD7OHxDk0y9WPVn865vZDgRocAMemTwvvmuM+JnjixstNmbX7v7NLGhWNEwSR2GRXyDqn7Ruh/C3RZtOt9VbVL27YMj53FmYdD1wAa+Nvi38QtT8c6K+s3viA2M0UmZkJ+cIeoQZx+lAHnn7VnjHUtR8I3p0m7M9nHIZ72KVvM+ROflb+Hivzhtbnwj4ms1043wuJ5I0e2llG5CCDmIrXv8A8YviL4C074c3Xh2xuVuru7QrtZ8vMHI5fA9ulfF3ga8vdIu9sE9vNtP7mdRwDgkx/VemaAPk345/Ba78HazP4x0CN/KZ90oUYSM/7C9q4bw58Q9Ss444bjc0U/7sqTkZxxtHbnrX6Za54j0STzTrsSX0k25Z7cjIB4wRX5sfHLRbLwP4q/t3RoA1vdsNkK/8sie+PamkB+jX7IGrmP8AaE0a0tImiLvGrb2+VXPJZPUY9ec1+yP/AAX0+OF/8Fv+CYFzZxDZfeNrkaaZlHDxypyc/wC4uPxNfht+wJpGv/ET9o/wsIYXms9OcSPLztLRjc2SOuBX7Hf8HOGjhf8AglB4FuHjKsmvQlCRysZR8/p0qZ1o0mot7lcj3P4ENN037FpkUHVk5POc7ucmrzRKg+Q596t2imXT7dpzn92o9MgDAzj2p5gXaAnXB/StpvoS0UChAzSJ96pjyMVEBhvpWQEp6FR0quc4zU275d1QBm7dKAgtQtbxtK8R6LqkZIaO8ib6bXB/pX+vV+z/AK34Y+In7LPww8bXMTtLc+HbIoIThmd4k3ofUZGa/wAgTW2VbOKfGGjmRwfof/rV/q5f8EzfGet6/wD8E8fg7d6QiNIdOgt3kK7wiKhy55HTGPxr8C8fsLKeFpyiro+54NqOGI1Pqy00jT7+/vLzWJGtYkbyoUB+XgdT61TtNKZroW1m4dRlcqeHBIHOaj1mR5PEKf8ACNQT6hZwgiVI0YB5SfmIJHHPpmvSvDXhyxu4BINOmALhpY2Kq0Z9ixBwK/iWpw7Xq1LRjuftLzeMIt3K1nZSaPaRG5TzXeXy4RjCxY53fnVu0WINPPGqPqTyRyCQgfOPMXOM9MV0+tx3Ono19rBjhtoH22671+aMj+LBPNeVeJPF/wAN9A0ud7zxRpumq+Ak8jDMYzk9SB+tfRZLwjXpVlJps8TE5pTqRd3qfwjf8HZvg5fD37dHhTxYVx/aenZYjHVZAOufQ1/Mm0WXdTx838q/rI/4Ot7r4WePfFfw3+I3w28T6f4jeC3lt7kWkySujbwQWC5wD2zX8npJaZnPOTur/QXgaVstpxs9O5+EZ1aWIbiL5YyPalYKhwRTgcjNJMv8Z4FfXc6POhB2DC5IbAVhiomiKY3DcQMgenrUu7CkuvXg8ZpCmCFBIxyufX3qiminlX+dDwTxUhwAEPUnJ/wpwto4yUDKCOR6fSneUGPBz+FVyMfKxoUY3EjPeq+ADvXv0PpVoQbW3N07n/61IIQP9W36VJJXAGN2MN/M0cdqmWPf1bmni3GOW/SgCElT975v0qMpu6YBq4IkXgnOaYLdUbI7UAUJY5RH85zzz7+9UmhyRjmtyaMqmc8+lZ7IW5j49aAM9oJCAY1+tSeU2O1W8HOxm59BTVjC53c54P0oAjaQAHbioXmL20o/2D/Kphb7hSPahLWUj+438q0itGhT+OLP6xP+CDT/APFhps9p2P61+hepKT/wUz+EYHrL/Jq/O7/gg6CfgRMg7zv/AOhV+iF427/gpn8I2Pcyn9Gr/MLxMf8AxkmJ9Z/kf37wVL/hNh6L8j+hP4kxsPCfiQ/9Q64H/kM1/NtcD/jG/wCDx9fFco/8fr+lH4kDPg/xGf8AqH3H/oo1/Nhccfs2/BzHfxZL/wCh1+A4JfvL+Z7+Vz9x+i/I/o0Ck6VYn/pkP514Jf8A/H9N/wBdG/ma+hlTdpFnj/nkP5ivnrUOL+cf9NG/ma/pzwU+DE+sf/bj8X8Q3fEQ+f6H/9H+wa6cmyvM/wDPB/5Gv5MPiKd/7PvxRYd/Flp/Wv6x5XZrC9J/55OP0Nfya/EA4/Z8+Knt4rtP5tX+UvG9ZuvFep/anA9CzqX7I/oH8Sykf8E3NaA/6EWT/wBIzX8rn7Bhz8DNMQ95Z/8A0M1/U14gfd/wTW1hu58CSH/ySJr+WX9g7j4H6bjtLcY/77rdT/4S4+q/Jnr8BrlxOJfqfkF/wV4/5KNpi+p/rX5T3KAXDH0r9Wf+CvXHxH00+jEfrX5UT8ysTX9/+CX/ACT9L0R/NfiyrZoykeea/ZD/AIN6PA8/jP8A4K5eDGRS40y1luj7FFPP4Zr8cJPl+7zX9KX/AAagfDrUfGn/AAUw1n4gWyE2GhaJMkj4OA8hEaj8STX6ofmB/pb3BisUu72X5coFyPYf415IRKsPnw9HOSPauw+JWpf2fYQ2kPW6l2j6DrXi2r+JPs9+unRNjYoU0HOdLJLLcEWshCsTkfStbwZqFjpfik6ejYMq8Z/X9a8ylvLvJMbBmYYVj6Vzvh7VrrVvixp9hApAWFt/1FAH3orFsMDxjtVe4eOFd7D86i2NaW+09hXMRtfX1y+ciNKAHXOoxsxWMYaoo5pHXEnFaS6daAbyRk9Aaq3bQ2sZJZS3agCMlR8nP41DMVQfOwH1ryLxT8Sm8PyGKZM7RyQOleIeIfi/quoRsIUKg/d4NAHunjnxvp3hdkmmkLofvKnJzXyL4v8AF9x4tmkCxqufkXI5HfOeua4HxFqPiy91mOO7cxOMNGpOQ49G7c1s6ZDc2qStdKBNK+WVTnBx156UAYlvotst4vkRkXLYEkobGR/jXZpplu8j2EaCO2TqOu5vUmsNN9o5eMbyDuZO+PWtu91CySGCyuX8kSNnIGWJPQcUctyo7mzdyalbaa1xKQsaRsiE9eRgGvXLGSC00DSfDUUmTFBG0snrIRlq8i1a1tvEElrGGYSZCR84DAHJGOle5WGnLc+dKtsUaK0nmi3ZwZVHy59q/NPESvN4ZUP5j6XI5JNzZ0sGi393cSatc2rC3KAKsrKqZXoxz6/WmaDpl1bu9/q1xBCApJbzlwOTjOOBwfSv8z79uD/gtZ/wVYH7S/jr4R6f8RZdGsfD+oTQC3t44YgkcT7VCts3Hg+tfmX8Qf27f28vihvfxn8WdYkEgwyxXckYOO22JlB/EV8Pg/B6rVtV5rJnoV8+abif65Oq/FH4QeA7B5/FXjDSdOmiBXzpZVWMAnodzZJ98184ePv+Cj//AAT28EWRk8ZfF3QYmtwSVjvI8k+w+av8jfV/EnxQ8St5viTxlrF8G5InuZpAT3++5/lXJSeGNLmnWS/nluieod859+ma+kw3hNQg7SkeXPOZt6n+ol4j/wCDgD/gkz4BjmtrrxzNqjNks9kpnL+n3QMelfFfxD/4Osf+CcHhiT7D4P0TV9YSPhVe1Cqf++nHWv8APPg8L+HkUqlorZOR5jE9PY8/nWpFp2nwoTBbRR+4Qf4V7+H8Mcvh8Suc1TOJvY/sz+Pn/B298OfHvgLX/hZ4B+Ev2nTdesZrB5Li5MTBZkKltiqQcA561/Gx5cE2p6lqtmPLivbhp0j/ALgf+EeoHrUjyhECoccYwoIH+FKW3Lljj/61fVZVk9HB39lojhrVZTWoRxgL85Oa99/Y78U3Xgr9tn4XeJIAQqa3aJn0zMuf518/kY6c5rrPh9q7eHfin4N1+E/NaazbyZ6Y2urf0rTH3nhai8mRhqlpo/2SNe1C7F8l/HIXV40JiK/Ltxy2aekmnX8bWkQaMyLuO0kbvzrlvAOpXHij4YeE/FTTjbf6XDI6EZMnmIp4Oc8dz0rtGsZZYJfs0i/u9pjAH3U9M9c/Wv4b4iwjhiJJ9z9QwNaLpIrf2dpN/pTWlrGY5AAHAA3nng89a2IL60R47C5i2wxhgzyHGSOOQOmabJb3EV0b6yZIvMjVGZjjgelV/s5scalrBWaILh8AksSep4rzPZWsazd1oaWjNcC9SBUEEQZ1VDxuTaQD7/Wv8kX/AIKreCm8Af8ABS74qeFmX5E1G4fnI/1jeZ/Wv9Z/R57hvESfbpFu5DJmFI8jy4zjr7DPSv8AMI/4OG/CZ8L/APBXTx7LGpSPU54pow3AYy20ZyfY5r+i/CTENuUUfK55Sd9eh+PB2zW7Kv8AqpAVcdiDX9eX/Brf/wAFAl+HPj7VP2FvifqKRaZ4hc33h+SV/u3wA3ou7jMiAcdyOK/kLibaNsYwMHIPsBWp4c8Y+Lvh/wCLNK+IvgO4kttb0K5ju7OWNiHDxMGUgjnjH1r9gz3JY43C8jPGyyoo7n+zFqEs9tdPb3dxlAxXnjLE46duT/nHNe81FbeDz7yNo1ZSpQEFh/D+vWvy9/4JJf8ABS7wR/wUt/ZbsfHEEtvB490aJLXxBpxYb0uFH+vVD1WXGcgcHrX6U3/2vyDKr4fBOcDOeMjBr+MeK8klgsTKnJH6LlVeMo2vqMEt3czJbxQKJYjviBONyHnk9u/WsrWZrWdALI7UYFHTPHmDnJ78dOtVLjxHcRXP2uCNVhiG13YEk5GDt9cdazJLfT0GdPmZw7ZZgRjYQSSM96/OcQulz6GjRbdya1lVJxfTyBWU7juGVQL028gH616NBqsNlpMlnc26TabeA+cJx5kbgjkbAcFT35x7V51aXNhqs8V8yEpbfKIlwA0fuPei5ub+wvmiuJPPBjLRRY+VB0Iz9O3SvQyrPKmFd4yszLE5dCq9Ufnh+1L/AMEnP+CZP7StxJN8RPhxFYak6NJLd6WPsZGT94iPgk544r8mfGH/AAatfsE6/qEaeBvHGp6S9w5lSB4xcYhIzt3Eg78c81/ScltJd+Vd7y8U25o2HGGXsx64B6V3WkaOps2mL/MCTvKklSRg5J64H41+g5f4nYumtKjPBrcOQ7H87Xwl/wCDWX/gnH8Nrs6l8TNb1HxYI2DLA3+jFl9wjEn61+pPwo/4Jvf8E8P2bpbaH4QfDbTWnQlUmulF04J/iLSBj8p+lfe3/CLx2yx3NxL50PzM0pPJyPuqOmDVa68O2cNnNLaxi2MCkLuIwExwefXrissy8RMfinyuehOBySlB3aMB9WeVTYWv+iWVu4EKw/u4AuMABRjdk9PSu38F+Pm8PyR/2mStrK4j2tk7CTgcd/rXk13Da3GsWKwhp5LhMW0af6lQrhSXPGG3EAKwyeor6q8OfCvTdJiN/qy/apIwCU5KDjJwDyce1fYeHOHx+MrurSWkXqc2f1MPSp8r3I/iBBY2Nqby0j+W45KrxtJ/ix6Gvn7xEC2hgr8zxgFz25yeP/116Z8S/GOlXM8llYOGjkiWMOGBJBPIAHQjH1ry25Aj00Rp8yICGz1IPOf1r+rqHO0nPc/LpNXdinZqssQKcxHI445HvWN4ht45dMZmGXKEfgK3NHXGn/6PzHuJweTyecU7UbIXOnYAwclcn+6e9dBJ+O37Vvw9u9Vs5bvUo97xMWCqOCByoH0Ffzm/tV/DhdQtJr5oNkUjPhEByDx1r+u/4yeFhrNlJbSfNLDkNjoV7elfg1+0t8NS1zPsjMNo24ux53H/AGR1PP0x70Afzs3GpSwRtoOruIXhG2Wc8s8Q6J9T2rhryWaSR7OxHlQ7gXZmzgds/WvpX43/AA4/sfzdRgjO8L5zn0Ib5R/iK+cbfU7OexGmXEY86RgxZhtIOcsT6/QkUAdp4b1aXSZPKkfzJzgxt/dX+9XvWg/FLVGdbcTsWQfIzZCj618wmzRrhbu1OZBngf3aiuLnVYR8zbi/DIDQB9kWX7TXi3RLs2NtfHzFU7mjJHBPcg81614d/bQ8baXHAmoars25wjZJZSegBJx9TX5n3niSC0YLbIAwA3N0zjtXD614rMs73IY7j1G7PT6/0oA/aCf9va3UYimkaNTtVHY/KR1YYArHT9tjXtWupJtPu956Gbf0GMYAJzwOM1+INz4rXUiWjZSQMZbqPzrzfUr67t5/tNvduknJCoxC/kOKAP2i8eftseIdLvfsekX620i8ymM7mPy/xHJ3Hmuds/2/dcUon9pM91GpAhjJCKexPOM+1fiFe6zrWoXRaeVt4/unr+VMk1HW0yEJUHHzDGTj1oA/Z2X9s7xTHnUHvyId3JPzHcB0HP1rxj4gftxeI9WTaJ5HKggPk5bHrzj9K/MpNa16LBcsVUY2k8Gs/wDtS/kugksRXJyw7YoA+77X42eKvEMa3c03mXM7fK7cbCe46/4V7r8N/EOt3KCO8cpFaEkuCQBI/U9cZx0r4E8NaxFbRmSEBSVwPWvWdL+I+q2kJsYpAtqzBvlUZ3AYGfagD7o1PxrpEAlvZpHluEJIYN80ma8r+J/iaxfRreZ1CM5DzNncVQjuOcelfJmreN9Qa6SaKQr5Z9P/AK9epfDy58RfEvUrTwX4ZRZb7VZ4oWBGXZSwGBnoD3PYU47hc/pK/wCCDn7P+ofE3xfPe25eHSnQEMVOfKzlyD2LYx0r9Gf+DjPwzP8AEX/gmHrMdtZeRb6DqmYU2/6qKDKZPpuH1r8k9D/4Lz/Br/glV4SX9mL4I+Dl8YeKtOiSPXNXzttkuRybdCoyQnfHU1+e37aH/ByD+0J+2l8Fde/Z21fwNpmj6D4iDLPKvmmVAxzlcjH5V8LneGxdavDk+FPU9XAuCg1M/nf0Sd7rR7aT/Z+taUsjKwdeDkfpTLCxj0+1W2tidoHcYNTSx4GW5r7iL0PLkrNogPPFIPlGBUqRl6RVwm/OetMRA7/wVEBipWTLZFCxZPJoKi7FLULU31kbZTgnH51/TZ+yD/wcxeIv2Mv2RtA/Zl8O/DxNc1LQQ8ZvnuSiujHIG3Yx4+tfzL3LCJhH75H1xWa2CeQM5znAz+dedmeT4bGwjDEq6R1YfGzpvmif0w+N/wDg6p/bn1mZz8MvDNjoUDnKI7GcKfUZVa+Q/HH/AAcK/wDBWLx7d75fFtpppbJPk2cSnB9SQfWvxaZW248wnHqc1KlztB4Bz1zXm0+Csso/wqKPRnm9Zvc+2/iL/wAFIf8Agoh8VZmfxp8UdSYMSdsE7RKuf7qoQBXzvrfxe+PPieIp4n8fazdxnqj3U7L+RcivN0mV3XKqCOmBWkzswxnmvUw2U4aD92ikc08fUe7KX+kOzS3t9c3zP1EzFgT2OPanCMgkVOQX4fIx3zU2z0IzXoxhGK5YxscVSSnsUHi6Ek8+2KcB26+1XGRyPm5H1qPbt5x+XJq+VbtGDbRXKOeo3D/PvSlZCMIpX19ateVLsLOAq+rcH+dU3vbG2GJbqFPYuM/lS5L7FNaXuKwdFEQU7c5+7SrvLFsbN3IIGePYetZ7a/pfmrD9q3bvulOR+PtWpOfLVVb5XJOM9wOuMVblrYftE0RMysQ3ccdetOO0LnHNRlEAMijIYkDFNdkIy6bscYI5+orAgcYgoyeM0wMn96lZSy7VAx7DHHrUX2dv4MY9/wD9dAEhKMfvc1cXdswcAis/7PJ6qKlEqowGdxHWgBkqox2jK4OfaotrA521pLGJVPHQ8Uxohn1zz9BQBQ2ZO7AzSFGPP+f51fEWOhp3l8gbqAM+ONx1qScZs5B/sN/KrRVlU/So5FH2aX2Q/wAq0i9Gx8vwrzP6p/8Agg+CPgVL7Tt/6FX6EXf/ACky+EfsZh+jV+ff/BCHn4GTD/pq/wD6FX6FSx7/APgpn8JSezTfyav8v/Ex/wDGSYn1n+R/fnBdJvLYPy/Q/oZ+JPy+D/EgH/QPuP8A0Ua/mrdgP2cfg4v/AFNsw/8AH6/pW+JK/wDFF+JSev2C4/8ARRr+Z+4Yj9nP4OY/6G6b/wBDNfhWAjebXn/mezlDvBvyX5H9LCxr/Y9n/wBcl/mPevnLUY1/tCf/AK6N/M+9fSyx40ax90QH8SK+WdYnlTV7pVbAEzgf99Gv6a8Fab5MT/27/wC3H41x8uavG3mf/9L+viQn7HeenlyfyNfyb/EA4/Z9+KpP/Q12n/s1f1jtzY3eP+eTn9DX8nfxBBP7O/xVx38WWn/s1f5N8ay/2qK9T+4uCKd3V9F+p+++unH/AATW1nP/AEIkn/pEa/lp/YQ/5Ibpx/6bz/8Aodf1Ja4c/wDBNrWP+xEf/wBIjX8tX7BX/JCdO/67Tf8AoZrsb/4So/4o/jc7uC42xGI+Z+Rf/BXr/koum4/vH+dflLcH942Otfqz/wAFeR/xcXTfeT/CvyqkA81mPTI/z/8AWr/QLwRf/GP0fPT7j+aPFpf8Ksv66FeNBtMzfdjVpD/upy2a/vf/AODOn4A6Vo37PPjb9oS/j36j4i1JYElPGI4QTtHtuP8AKv8APz8f60dO05dF0+QC8uf9bzjbHn5V/wCBHr7V/rM/8G9vwBH7PX/BLz4daFNCIrrVbU6pOcD5jdEspzyeBjrX6sflr2P0s+K3iCEeN7DT5OVgiMhA9Sa+YPFPidX1uSS15Al5+hr0zxxdw6r4u1y/tX2mI+SpbsVr5VvmeLxMsKtmS3Vizk/Lkjv2NBgfRFvruNIkuLgeUtuANzcZ3Htn+leo/A6zstQ8RzareR7Z4kxEe5U96+Ptd8R6rruiaXot4o8+a7MhVDwIIjw7D37Cvrz9n+G6uvEc14+dirhQfQDFAH2BJtcYPNNWJI0Kxjip4yrcqMVIwyMUAcpq9ncTQqLYfMa8o1OXVLCfyb6IsufvV77saqV1p9rdArcRg59eaAPCW07TtTYR3dsskbgZLUt94M8PLbAi1jG7np0xXsdzolgIflULtHGK8W8V6q9rctplk/mnqc9EH1oA+ZfH+maVpkkr2Kb3YHdu6xn/AGa8usifLQOrLIoz8xzurp/FGof2pqVzYvISx6Mp4/OqNtpdojqpc+bjgk96AKP2Z4ZN1oG3jkl+vP8AhUmnWElvvurxhM4PysezE+narY8z7UbfO7HJboPzrmLycTasDGWKKCxKnj5f0ppBex6ro1pPJqNk4g/1L/ffgkvx8o9q+qdA0sny4rqQnfHIjK38QIx26V8eWfiS9TU9Kv7tvna6jiVmHykZweO5AxX1pYajFZX8Ons5812yXPI542j61+U+I9fkrUz6LLYfu+Y/yRf+CsvhJfCf/BU74saRAmyObVbpwD6Eq1fBgjKyZ449K/Zb/g4Y8LL4G/4K1+JiqBBqcMc5wMZMykZ/8dr8bscZ+n8q/Rsore2wsKkux5eKaU9RCBvJxS5NJSkEda74pLY4pau6Jk4HFLlv4zTV4AB70vBFD3Eh3J60nXrTACDgHIpwIPSqlFNWNPaC1narcz2KWWo2vElreRyA+mATV9h74rK1hwmmSl+V4I+ucVFWKlTlHpYdD4kf7BH7EOtL43/Yf+EnjLUpGMl74ZsQzRjON0I3Y92Ir6esdLgVitvPI4YKjb/QDOeK/NT/AIIweOZPiB/wTE+F01sfOW205LBjg5Xyiwb/AOtX6jXbzafYi305hPKTglgASo689P1r+MuLsKpY2d9D73ASajYRovsILnEwI4LHaiDvk1w1rPHqWpTixne7KA/dGI3H90e/rXQa4upIqz+bvgC8wqB82eozXGDQY7K+8zS2byZPmiRSS0bnrnHb618HjppSSR7eHi/iE093s5EgmuBAqSBhKuTKxzymBk4HSv8APZ/4OufB9t4b/wCCi2j+J0j8v+2bCKV29di7FP5AV/omaJa21pILyFHlnnYxjcflVgRkjI45r+F3/g8f8M3Fp8cPhh45ZcxS6XJCSF6skw6nr349q/cvB7Er6zr1PAz7Vtn8jBkYht33snH0qvJPcQYltiVkTBB9KmlRfMckjGf51U+0LvPbPb6V/TPw3SPhJ3jsz6j/AGHP24fjT/wTv/aI0r9ob4NXsjRrMF1bTWJ8q8tyQZEYDI9wcZGK/wBP79jT9vj4Kf8ABRP4MWXxj/Z8vIJrp4gNW0qVl+1WU+0blManO0H7rdxX+Su8ucgcZ449DxyOMj8a+gP2T/2tv2gP2F/i/a/GP9nPXJ9MuIJA89qGPkTpxujkj+66tjoenrXwvGfBNHNKfMlaSPXyrMnSkubY/wBbWCeaGxkt0iDSx5ESv0Izh2x2IJrJupXEjpCgaZMKYl4OGH3jX4mf8E9P+C9v7J37a+mWXhX4sXdv8PPiTMEV1uDtsLuVcE7XbhNxJGOOvFft1e6XqWkWLazbW4vLa4IcXlu3nQiMncACuTj/AGjX8ecVcHYjCVWnGx+uZXmlOrDckt7SSytEg3qDckM54GAvb/61ZupXAtbGW8WT/XEpDyAct6E9qwHOoXlysV7KFgnViVjY5EY6gZOMgd+lXxeWc6iFrcJDD/x7JKBu3AfTn1r87q4KcX7yPoac4dSzowms4/7FeXMV1JvTkExYGWzx0JPWuu1K91Gyka7NwFtkA/c4BZh6r7tWJoK6TBdSTWMb3QRP9M6kx7uTg9D9Bnii8PhVZbebWZZVsZTvjcHJViflU4yfoDXLGk77Cryj0ZsjX7vzoFmZ4mI85YZR9yJeBnGRknPJrpms313XV0i/uA1nGvnJGuRIzDklzyNo6e9cJY29tZPP4intZI98hSGPky3JU5QDPQcngDAzmv5tv+DhP/grLrn7C3w+h/Zi/Z/1cWnxJ8Wx/aNXvIWBl020blYY252Mw6e3XFfpHBHClfM8QqFLqfKZvmMMPG7P6OrfXPD2jfE2BNa8QaXp85nx5Ul1GJCmQFRY2wSfbt71+kS+U6oyH7o47j/Jr/E9/Zc+Nv7QHxf/AGwvBN5r/iTU9Z1O61e2Baa4lkckyDsWP8q/2ovByzjwxpouclxaxBiT/EEAOfqRmv7L4H4I/selKPNe5+YZtjo4hpn5+/tH+Ctd+HvjWx8WeHF2aLqcoFwD9yCU8n6BsUureJbLT7WLyD55YDzB0yuMZHtxX6D+LPC+k+MvD914a1uMS211GUZSOh7MPQivxk+IMfiT4Z/EObwJqbsyQA+SX+5JH0VlPcjoef8A6/3DdzxpQsfRnhfxpHcJJLBDiMEhM/XH866S51eOeHacJjp9T1zXz94A11rlDDcFjIhyxbJwCeQecEgjsK9HilZogVOGAyc0iDg/HcNtJDLsXbIwO49dw+lflB+0p4It9UtX1FlPlLxJg4wRwCf/ANdfq9qlpPrFpIyj+LbF/eIJwxx6D8vwr5B+LXhQQ6Nc2DJv+05IVuSGxk/U8/hQB/Mn8dfhbYy620sUpuzHIGWLtIT91QOv4+n1r84/HPgea11S7aRgJpWLTg8YzyEI7Y6e1fu58a/hzYJeSadArq5kysjcZZvvHI/hUn5cEDt1Ffmh8R/hnZsst0iyCGFwsOSV3uOqljk5HLYPT8aAPzlvLjUNHnIViN3yq2e1Fv4glbzDG/U4LEetel+L/CV20j20vysMkE9fpXz5f/adPnaCRCD6Hv70AbGqRLLkySncfSuQutNjyRKDj171WuPEDZ+zsOV6t/SoBqP2xtkhOR/n0qFO4HNXOl3DytKy7MenesltHkY7nGd1eguqEYLZx1zVN/3g+UYx0qwONtPD0Czb347Vvf2JZKhq+kH8TdankGBtNAHMz6HARuQ4Irnp9LX7RlhjFdjcTMnBOBmsO5ul3M3cUAUCluhRI227etIuqeQ2xeAMks3SseTzLq4+X7vfB5q/ZeH9Y1O1H2W2ldd20naeQOgquRgclrXiw2jNIh89nO0KOOTxxX2J8I/i3b/s2eCrj4iXied471SFo9MtjgrapIpXzn/ukA8L1718prZ2PgbVxrmvLHNfR8wWjYZY8fxOOcmuP1fV5te1B9W1GXzZZOS5OAPQAHoAOOK0UCbvsNe4uZb251a/nZ7vUJWmuZM5Z5HOSSTk85FDSSyfLIxYj8qz2lwNqgkt933PtVNZZQNxQhs4wCOvuKhU5aqKNFrsaZCA1BKVJAzUK3AE6wyYXIJIzWXqGuaXYXH2fUpAkigEKASSD0PAxUQulaaD3noa0R42560uEDY5yPyrkF8WaXK5W3Esp9FXmu20Hw98SvFDBPCPg/VNSLdGhtpGz+KKaznWhF+80i3RkuhSfk7ulQ+aA2MfjX0b4M/Yw/bd+I8oXwx8LtYZT/HPayxqM9tzqoB9jzX174Y/4Ikf8FP/ABSiz2fgWCyU4OLm6iViD/slif8A69eZis9wlJ+9UX3l0sJUntE/K6eIzMXVs/hVQ274JKnjqa/oa8B/8Gw//BSTxO0Q8ZS2OgRz5IAk88j1BCZxjuDjHevq7wV/waZfF68CDx/8U7Wxbf5bxrbucE9hlhnP0rxMVx/lVFXlVR6NHIsRN25T+TNolUZY8fWsee9soXIeZQPQ81/dB4R/4NRP2UNG05NW+JXxDv76GFsTvbssQ3A4I+4xAzxX258Mv+DbP/gld4Huft+qaXrOrXMK+Z5d5dlkZB1Y7FUY9t3fp3r5+v4z5NDaTPZhwjin0P8AOCj1qwVwIXLseyjk10Vkdf1aQW+iaTfXsxHCxQs5I+i1/qN+Bf8AgkZ/wTV8J3S3Pg/4X6KYtu+G6voBKspUgsvzljkY4OPpX1p8P/gF+yj8NdVTW/CPgzRbaVYGYzpaIrqCSFjRQMD8q+Vx3j7hIfwYNnXHg6pf3pH+T34X+Bn7TPjC5W38L+AdZu2k5XNlMR/Kvpzwd/wTC/4KOfEKZR4a+HF+yOQRvg8r/wBDxxX+qpcXE+n6PDc6Fpdna2k+SreSpKjuDjB57V56PE2pyyya3elILSFTiIqqMSOFKjaK+UxX0in9iFvmethPD+E3ds/zxPh9/wAG7v8AwVI8fywpd+GYdIjlIBkuZ4kCE9yAWb8hX274R/4NKP2wb6+SLxz8TPDWmtgNLGrzyMgPdgqgD86/tj8N+IL211M3MMk32q5t9kZkJMah/mMjZ6Hj5fatS01VNHsIbW4n/tE3M4S+uDkk7j90N6fpXyGP+kLi5fDI9iXh5BbH8rXgH/g0Y+Femok3xc+Kl1qEhXcRpNsNh+hlc5+vH0r668Cf8GsX/BNrTY1vdb8ReItRntV33ELtAmAO5AQkA46bjX9BniKythbNBqDmeytxxCjFWiHVSu3lulMvG1B1s9Zlbyrh2WKGJcBmVuhlHcY55r5ep45Y6rLl9pYzfBVKG6PxM/an/wCCH3/BMr4S/sb/ABE8QfCLwCr69pOh3d1a6leu7fPFA0gZTnbkbewr/N30y5l/s2MTOGaKSRNrdQtf7H/xl0Sw8U/s4+OvBQlaad/D1+k7FcB3kt5ANh6YBIzjIxX+OtqOitpHizW9KkyrWV9JDg9QMtX9P+EfEOIx1GTrS5mj8+z/AC6NGVoqwiJtTg428imBWf8AepmQjkN0HPWnyR4ZWYdOjDPB7cDNO8liFkn+YgYwDjr3wOlfr58yQlsDEeOcjjrnHSkUnYNvQ8c+tTeVtZo8AHHbvjoQf50kaExtKw+o9D60AQHA59Kc8URQOv3j6U9VBBZTkjrUsIZk3DO0j0FAEIeRV2r1pVkdeG4q2IjgbeccD3HrS+WeNyjr3oAqMzk8U3zMdTV4xyluSBnpxTGhkA3Lhu9AFbeTxRKMWkv+438qsohCndxxTLsAWshB/gb+VbKPusIVLySP6o/+CEAP/CjZj/01f/0Kv0RVd3/BTH4T/wC/L/J6/PP/AIIR/wDJCpj/ANNZP5mv0Ms03f8ABTX4UH/am/8AQWr/AC78T/8Ako8R6y/I/v8A4NqcuVJ/3T+hf4jrjwR4jH/Thcf+ijX80DgH9nP4On/qbpv/AEOv6ZPiUMeCPEeP+fCf/wBFtX8zkALfs6/BxT/0N02P++6/EsLT5Z38z0sll+6kz+mpId2maeMdY4/5ivkrXY8a3eD/AKbyf+hH3r7NtYt2m6av/TNP5ivjvxCYl1++U9riX/0M1/TfgzD3MQ/8P/tx+M8Z1OarH5/of//T/r1Y7bC7z/zwf+Rr+T74gHH7O3xTP/U2Wf8AWv6wZObC6/64P/I1/J98QPm/Z4+Kif8AU12n9a/yb42X+1Rfqf3TwHH3qvov1P3v1kg/8E2tX9/Acn/pGa/ls/YKYf8ACitOHpLN/wChmv6kdW5/4Js6uf8AqQ5B/wCSZr+Wz9gn5vgXp/8A11m/9DNdS1ypf4o/qdPBq/2rELzZ+Sf/AAVyXPxN0rcfl3n+gFfkrdS36yLZaTD59/dMRHEf4ABkyN9BX6sf8Fg9Xi0j4hafeSJvaNmK89weP5V+O/hn4j2Wl6BrVxdbjruoBYopgOEhP3wPQnp9K/0B8FlJcPUmu5/MfixL/hWkv62LXwi+Hes/F34x6T8JdAU3upa5qkFnE+NxZ5JApx3xk+n4V/tk/s/fD7/hQf7MnhXwBNhj4a0K1s2J4y0EKqfTqa/yq/8Ag3a+B3/C5P8Agq78OoZ4PtFtpE/9qSHGVj+zr5hLf7p/Wv8AWa+KTSyeFH0KyVml1Ei1VV6gMRuP4L1NfrTR+Wc7PzrsdZu9b8I3Wta1lJ9Su5HZUPPlhsAj8q5XxH4E0/xxMxgvprRNPZJrSROPNlXoknqh6GvtP4ifDKSztbLUNKt8RWsQiKqBjGOTjFeJT2cxASSMLEv3UTikQea23hnUdfxd36iymaZDcBD9yJAPlU9cFsnGO9fenwNsIrewnvFHfA9cdq+U0gdGV3BUdOeM/X1r7G+DMBh8POkgxvbIPtmgD2SP5WOanpAckj0paACoJnVBlu1SOx6Lyayb4/uiScY9aAKOqarZw2sjSPtAFfIvj7xfYzs2lWJAM3+sccEj0zXrfju9jt9NkO4sdpxjsfevj1R527V9UlUSiQ7QfugUAcZK9xFdrJ5OyJGxtHJPPeujljgli3QfMTxnpg+1UmN3JcSMXDRz48t+2R1rQ08W1qpe9L3LjiIp9wN6nFAGbc6fezWbWyBvm/U+lQR2QstIO9Aj7Ssw9B7H1q9LqFxblV1OZVZcnIPr6+lUtU1qG5uI9KFvI0F2P9aQQMrznPtRew7XLDAv4g8PQzAF7u9RLdACRGqgMztxwcV9Oz3YfXVfyZD5U6AMFPUH7w9jX5R/tuftX+D/ANibQvCHxY+J0wTTbnV7exCKMSSByclQSOcDtX6veEPGNp408O6X8QNNIXT9WtY54HbgMsgDIw+qkGvxnxQ53ON0fS5Xb2dmf52//B1l4ROgf8FO9H8SumIdQ0iyw/qfnB/Gv50HC72K5wCR/wCPGv64/wDg8W8DJpXxd+FvxMiX/j/iaFmxxiLaw5/Gv5InZgzLjjJ/nn+tfo3CEm8vhfsePj7c+hXxgA+tKxBORRtZmzSiKQjOOK+gONRY4kYU+lGfSmrkEn0pSCoyooJFXqaEIA5pEzycUINwwRSsApBYg9AKy9fj8/SJ4l67CfyrTBbvTJYxLBKG7Ruf0ptXTRpTep/pkf8ABs54rHiv/gk7osBLOdN1S+tiQfmAUo/GCT0biv3RN4IppVXCWq8BupU98/5Nfyy/8GkXxFbWf2DPF/gq5lMSaVqr3G/PKiSMKcf98V/U215YaeI9SvnSGCX5UduVZz93Ix/EeBX8ocf5fNYuagj7fLKyULyKWsrcpALSyI4XehIyDn1zisXS475beKy09SpuG3TzhshMdQPTNT6xoPiHUb5dL0wtHESJHlZiFCnpg8dq6C58KajYaebHQHW3hYqz3EjbwCDknaT/AFr81lkGKqO7iz2Y4+CVjgzqsn9pzm0MkluyGBlxgiQHOR3ya/kf/wCDvzwhc33wB+G3j54mX7K5ty7cnkbsE+vFf19Xfijw14ZmN94i1WytIwzedK7oqnI4bJIAI/lX8r3/AAdLfG39m/4x/sHWHh7wL410fW9f0TWUkNja3CPOyFGU4RSTgHqelfr/AIY5LiKWKjJxaR4ebYqM1ofwNs7yAueAQh477hVEtlyz9as2MjS2VuZh8/lKGHfIpNi7t1f05BX5m+h8TOV2QKd5wKcMfxCpsEH5BTPLcn5qVxRV9DMu7QyTpe2srWk0eCs0Zwykcg8YP61+tH7Gf/Bbj/goL+xIltpug+IZPFnhpGAk0/UHMyhB0ClslPwr8qXjKj2PWlEbKBIp2lTyV449CK8/H5VhsVHlrwTO/D4mdF3Uj+679m3/AIOpv2R/inLBoP7S3hOfwpdMu1rmH9/HvPX5lClRn26V+wvgz/gpf/wT4+MlvbX3w/8AiVpqsVG2Ga5iEg3ckbHcMCO3Ff5ZFzp2nXi4vYUlDDOSo3ce9ZA8OaXHcLcWEk1q68ho3GR9NwP86/PMz8H8vxCbg+Vnv0OLK0Forn+wF4b8f/C/VY4X8D+N7GeNxvMiruMh64Z1OMV6HYy+DtX00Xmr6/YgEiaRH4SP+6y7sfjX+Prp3iP4paJbeX4d8Y63aKRwqXMqjB68I44Na+pfGL9om1tN+rfEnxALRSNy/bLhiEzzxuwfzr45+ANPm0qm8uNqltYn+o7/AMFFv+CgXws/4Jufs03v7QHi/WINf1q9WSPw1ZR9ZrplO3p/Aucs2OBgDNf5Rf7Rnx6+I/7UHxk1744fFXUHv9a8Q3cl3NJIS2N5JCLnoqA7VHoKx/iF8YPir8Sre20vx94m1LX7LTsrZpf3EkwhQn+BXYhM98c15U+ZDlvyr9U4Q4Hw+T0XGLvLvY8DMs2linzNn0r+x78Wz8CP2l/B/wAWlUOuhalBcOD02o4J/Sv9rz9mD43+BP2ifgP4W+MHw3vEvdJ1mwimjdD91tvzow5wytkEV/haWrtFIsicYIOOhNf3tf8ABrd/wU3i8H65b/scfEnUgdF8TPv0Z5n/AOPe+PBhyenmYxj1xX20pxaOCeruf33FkKHP+RX5s/tYfEv9lv4h+Kx8A/FfiWLRvGUcZaxvNuEtpW4VJJenzEYKmv0M1G8a10a4u0yTHEz/AC9cgdPXr/Kv4StLurL49/GX4hQeNlaxvk1h0S/Mrm5AErnCRt8uR3OOmMYxWBlzXdj99tCsfG/wx1KHwT8TIdt+ZQYr2Bt9tdw4JDJIOCcYyCAc173ZaiL+FrgbUQ5wScGMe/HU1+fv7Nf7RXxH+CukP4K+NEY8ceBECpbyMBLe2ozklQQXxzkjOB2NfofLoHhPxX4RT4nfCq6GqeHJwGdFyJLd/wC5IuSR+NATjYwTHC0JaRzGID80medp9vTv714H8QYbXxFdTTQH9zGAIkAxwp5yc9ccn8BXpMesmb9w2WbkyDGQyA9OvYV5P49ms7eB3sWIeX5dg42/3v0xQQfn78XfB03iO1aVbdX8o+WhHDFyTtQHA+UdfQE9a/Mv4qfDiQho7yLEVupVEI4ZicnPT5s/xdwMdK/anxa9rcWpkS4EG0fLtAJdh1P3Tg4r40+LPhseI2k1llUeREheKPJyMDIUZ69+tErqLb0KhFt2SPwc8d/Dx4Fe+ugUjViQ2MZPpXyN408M3EvmQzW2xl43EEbs1+vXxW0WzF60epxfaIlGIUXja3+0PWvjDxJ8PPFHiWWWz0zTJbklgsIiR2YE8DoDnntXKsfh4wvOol8zenhZt/Cz8x9W8LeVO0KEeYeqA8j68Vykmnarp6mSVBsB6jn/AANfpd/wwr+1J4iAXw74C1a9ll5Mi20nPp1XtXoOif8ABGz/AIKJ+MlS5s/BNzYrJjD3S+Wv055/SvJr8U5bR+Kqmzq/sjEt6QZ+SCwS3GAXK89e2frVxRIG8rO4jvX7x+FP+Dc39vDxXbzX/iObSdLihyXRrkDaQM4KqDzjtX4e+NdIvfBXxB1r4ba0US60C8lsJyhyHaI7Sy+2RW2W8Q4TFrmoSuc1fBVaS/eKxkRF1wVGaq3TOzbj+lV3nhXckRI2DnntVCW9Ecfl/mfSvca0RylDUJGjJ5D56Adz7cVgi3vLl8FNoY1tCzlnxcRj5c/IfSvXvCHhi41SSKMIHZyAMep71IDvgx+z547+KniODQ/h3plxrWqTyiNbO3QyOc452gE455PQVo/EX4WftZ6b4mvfhr4H+HOptdafI0VyUhdwrocH7uRj8a/aj/gjD46uPgj/AMFHvCnhPS0huLvXbea0+cD70qHp1wQB61/a14iv7ex8UXqzaLo5uYJiCFtAJZR1LM+MdOTkV+Tcc+JEsorWcL2R9ZkHDf11bn+XZ4R/4Jnf8FIfiLqJvNE+GWpQyXOMzzwuitn3cECvsD4ff8G8v/BVr4mRpcJolnpcTHDGeeNCP+A4ya/0ZLr4g31/KmiaPc29lald0ksCqghTHq2QfyFc2niDxUIbi7i1K+vNLY+UksZ2gNnGQEAJ59K/Hcy+kfiI/wAKCPtafh9G12z+H/wR/wAGp37Zmt3ca/EnxbaaTbNw7R4dg3ZcblGCfevtTwD/AMGjHgeOKL/hZnxY824ZXaaCGNVbKjO1dzH8cZx6V/VtZ2F1BcfYYH+3yXirNIJJWYoOz4YnBHpW14X8GtaeJbF7kW9xJHLNIkjEM26RGHQnPPpXn4bxtzDF11Bysi8VwJRpQ507n+TH+1L8HrX9nv8Aaa8X/APTnLWnhq6mitmfl3EfGSe+etf0Af8ABtj+yR+yV+15Z/EKL9pfw9Hr934cRLyDzI1crEPvKM5zk9jivzV/4LZeGv8AhFf+Cr3xBsrePYJrp2UAYB3xjgD3r9Rv+DTbxX/Z37SXj74e3GfK1bSvKx0wPM+Yj3wa/obiHNq39hfWYN81tz8/yzDR+ueyqI/re+HX7AX/AATn8Li11HRPhVo0NvOu5bieytwFO3AD/LwSO3rxX1RpHgP4QfDmGKLwT4H0rTYHbbG9vCibQOjMoXGD2waxonSydtJitzPbW0vzhwFiCKSQzbRgnj8+a2C08VhJebyhlYhi/wDqlTGVC/4V/EmeeI2PhiJU+dv5n7BDIKFvhO7uPG9xPBb6eltFp0IIFz5MYkwPRG4wfU4yKg1fW5J9cjso5ES3scSm4dA2eOBngsxzx6ehrh9I12PT1le/syw24tePlZm6sfYnpmr2k/Y2vEk1BSunxnzHBUks/quT2PP0r5qtxtiKzSqNnVTyqlBe7A2de1kjxFFq32yQ3QV9lvIxxtZQA20HgfXJrgBqWkSWFxcxh7a/81YvMyWWViSSQScbsfiK0vGmvaIokupIZrmEYWWbaQzZ+6owflAPX2rlNMSK5vIbHUYt6Woa7VlfCmWT7i8Zz8ucivJxnENS9j08PgoW0iLcxWtppvm3w3Wrk74x7Hg+5JyTnjpzVvTtZjtrSK2MUs8t58iljukCn+DBxx3Pt+vXPBommW7DU1E4fYyqG2l5ewA64HpWzB4iuLq6GrSaWBJbofNmUH90hGARn+LNc8swqys1uXPnjtEoaKH0+zt9Nnt/3d4PJgXOFjySD0B59v5Vt2nhlfD8V00Rh+0QSjZPNzGEXqMYqTw7FFb2IfT7v7Wl4QYFdCJFIPzy559euB2rM8T+I9Bvt9nfwyXNlGSyiI5/2fnUcn5qMViK0UnJnG4OUrtHJapq+q61bXFvEkkWkROPPkHBJZuNg6kGsDUmtL69gv8ARrcXVtAoiiUk4IzjD8HljyfSu/1S4ml0+C+84RooXMI+4ygd0AyT+NchaXyao8Ulq/kRK5MVukW0sV/v8frXkYjFSkrXPZwkbbmIsF3qml3V34hkeDfKqbIh/Gp+WMdDtA9PxrT0meyj06S01uNnmd9hgjGAg6K+c+nrirHiNlitrWxtCYHlZnSBRv3sDjex7EHBFN0OOxjNxPNDuk8rZNdtnIA7FO2D615soNu6PTlUVjeNheJBsvriFIraPb55fcT/AHcr3wPUiraWdjp0DajZB7t2Gx2XnzWPQx88Y744qlpWnWtx4dbWJLdnMKHfGhVxNEDyQPp+NZXh+7bT7GW5muhBbMHXTof4sAZbnsegH0qsNBqrdo8+vWR6Nefata8PX2j6tF9kMum3EFosbbi6Mm0lx2b2r/Iz/aj0KPwl+1l8UfDZUKtrr90igdlWZgMD6V/rc/CKHxFo979rktdsV48gmF/IVkAwSoi3cMT7YBr/ACuv+Cm+gP4V/wCClfxdsJV8vztYvJkB6MHkJOBjv29K/uX6OuLlerCXY/E+N6dpaHxM/l7witwO46j3o2KGIT7zdv7w7nNPYAoOxX/PNPAO0qAB6EH1681/Up+bkRRMeST8oUqvoM9RUnlhVA6EKEA7EUilT8pHyjoPftTXDEAtzg8ex9KABYQsgUf8CoTzEjCgDuP1zUgAbKtwe9KeBhe4/UUAN6AJH/F0z1+lKhCE9d3cd6GXnggdDz+tG4A8nn1HNACRklWRj8wPFOLEDHYcio/M2/MqkjPWn7tzFj0PQUANdY1HfNVbkg2sg9Eb+VWn+eqtyjfZpB6qf5V0x+FhCK5kf1Vf8EIefgRL/wBdZP5mv0Q08Z/4KbfCkf3TN/I/4V+dn/BCJwnwJkXv5sn88V+iWkN5v/BTb4Vt05m/k1f5b+J//JSYj/FL8j++uFNMqj/hR/RL8R7ct4L8QRjqbCf9I2r+ZaBcfs8/Bsf9TdOfwD1/Tr8RRt8J+IfawnP5xtX8xkRA/Z8+DQ/6my4H/j9fjcY2nZdz0silelJf1sf1G6bbn7BprHoYo/1Ir4u8TRqPEmoD/p5l/wDQz719x6fH/wASrS/+ucf8xXw94rJj8U6lH123Uw/JzX9T+DuGiqVZr+7/AO3H4jxhUftI/P8AQ//U/rykJ/s27PpC/wDI1/KB4/4/Z6+Kh/6mu0/9mr+r5/8AkGXn/XF/5Gv5QfiB/wAm8/FT/sa7T+bV/k5xr/vUfmf3XwF8VX0X6n736sMf8E29XX/qQ5f/AEiNfy1fsDH/AIsTpp9ZJv8A0Ya/qZ1cAf8ABN3WP+xEk/8ASJq/ln/YIGPgXpw9JZv/AEY1dC/5FS/xR/U34Of+1Yj1Z+M//BaRGXxrYMvTLH+X+Nfg1KyZZl696/oD/wCCxtmL3xzZQt0Kuc+4Ga/nzl3KzZr/AEG8FaifD1KP9bn8w+LP/I3m/wCtj++X/gzV+FfwPh/4Tf4yavr1jL45kcadaaXIwF1DblQWkQHkiTpwDX98kMR+1C7lGSOIyecZ6/nX+Ez8Evjx8Xf2ePHNl8R/g7r13oOr2EiyRXFrK0bAj6EZr+x/9iH/AIPE/i54EsbXwf8Ati+Fo/FFrCoiGp2LCC7OB96RTmNz74r9Xluz8xSVj/RhlRZYisg3AjkHpXhXjT4WPcSvqegsq558sjv/APXr+ff4X/8AB2F/wTM8drGPEl5qPht2A3C6i8wLnrzH/hX1zof/AAcVf8Emdc2mH4n2ybuAJIpF/muakj2bPunT/h94k1G/NrcxuHVgWXHygfWvsDQdJi0TT4oEGCqgEV+UVp/wXT/4JZ3lvJeQ/FTTNsYyeGz9Oma8o8Tf8HGn/BJvwyfLn+JEUzf9MoZW/pQP2Z+6wkXqO9QyXG3pX88es/8ABzx/wSd0zTpLy08bSXTp/wAs0t5dxx/wGvm3V/8Ag7l/4JuWEkkdpBql3tPDLEACPxoJlGx/Uxd3k4OIeK4zWJPEMiMlsQVP905P41/Kfrn/AAeJfsA2Cn7D4U1u+x0K+Wv8ya+f/G3/AAejfs6WdtLF4G+GGqzTY/dvNcRqv4gDJoJP6xfE3hDVNeXyLppevzEZA9gT05rybxXpn2KNdC1C2kW5jG6K3t4zIXHqzAYFfxZ+OP8Ag86+NN1qcMvgLwBZW9kqsJYrgM7MT935gwAx9K+A/ib/AMHX/wDwUK8dB7fRrfStIUyGRHt4mDgHopOc8fWgD/QMt9I1e9gt7e3s388OAIiNqxgHlmJ6VdfSobBi1pe2YtYjiVZbqKHB7kAnJ59ua/zAPiR/wXn/AOClvxGu5NSl8ZS6VHKuyVbFWj3EDqeetfFuufty/tn+Lr99X1Px7q/mS+lww759aAP9W3xN+0r+zj4F0q7n8a+PtA02Kzkb7R5rqzIqnocsCfwBr8s/2mv+DgD/AIJdfAaCa+8L+ILv4iaggZLey05WWFX7bi4Ubc9xmv8ANx13xB8WPHl9LqXizXbu9lnO6R5pnYsfU84q/onhTRrMrd3StNOhBXccjd6kdxTVuoH6r/8ABQ//AIKjfHr/AIKo/HfwjfeIdOGj+ENK1KG20fSbcnYGeRRufoWcrgE9ucV/qW/C/QbnSPhD4Z8G6W0cNvp2l2sWWy+3y4lGM98Yr/Ky/wCCYng/4U+P/wBu/wCHNj8adTg0fwrpV79vv5bgiOL9yC6qWYhVBZQPev8ARa8Yf8Fn/wDgld8J4X0nVfiTbS/Z0CFLYtJwnX7mQfwyK/NvEjC1sVKEKKPey+qobn4cf8HjfhB5v2c/hd4xRBL9j1KaJ5F4xmIevYla/h4kABRxyHjQj/vkV/X1/wAHAX/BWr9gn9vf9kmL4H/s+am+reILC9jurV2jcKFUFXALL1x71/IDby/6LBE4+dIkVvqFAP8AKvpODsNOlhPZ1N0efmEk53RImMEUBgeWNIz56Uz5v4RmvppbnIqltCYKpBx3qIE9B3p6E55qOaRLaF7iX5Y4+STUkNkiqV7UwNtJCiuE1r4lWFhhNMhEzerdK5OT4panJwlrGv0yaAPZxyanWJWGzJG7Kk4JGCK+e5fHniKUlldV9guKqP4v8Sygq07DPoSKL2ZUdz+h3/gk9/wWF8Wf8EovBXivwnoHhS28Uf8ACTtG6G5lZI4mjz1Vc9c19m/ET/g60/bk8UIW0Tw54e0uJW3IvlmQgj+LDP1Hav5B5NV1SRSrXDsz8nk9fzqg0sz8MxPpkmvAxHC+DrVXVrK9z0Pr0oq0T+jP4g/8HFP/AAVW+It491ZfEYaBEw2iKyggjAHpn5mr44+IP/BS79vX4rQTQ+Ovi7rVytwMSBLx4wQfZCuPwr8j1luEbG4gVI9xOR/rMfU12wybCx92ECfr9Q+uta+J/wATPE748S+ONWvV/uy38zr+TuRXIRRLHdfa5L83T9QZZAxz68183ZcjezZI9KPNuXG9W4rspYeFPSKsc1TETk7tn03FGk7Eo6bs5+VgSPale2ZCDzz7cV82QXtzBJuVmH0NdJB4z1+BdkMjMo7PW6Zge5xIc4bpT5I1AzXkWn/EHWC+26iQqOSQMmu2tvHOgXgEcrGJu+V4pAdDIuWwB0qJkXnOc+3SsK78Y6FYq0kMvnuo3AD+ua8y1Xxbr+pMdzCGInICDtSZcIpntphMi5bHA9RSLafPjHAGc9R9K+bzqd8pDeY+D6GvXPhJ8PvjT8XfEtr4L+EmlX2uahcShI4rVGk+ZvXHA/E4oquMYc0pWQ6sXKyjudVqmpWuiWq319jHRc9SfTHpXimra/e6zcOssnynIA7YPToDX9Nn7Kn/AAbJftf/AB4a18W/tH6nH4O0wqJJIXAe5MZ64JPlqfwNf0nfs3f8G6P/AATN+AOnprniDTpvGmowBkuf7YZJ4zIE3Hy41ULwRnA618HmvibleBunLnfke7huGcVVtd2P80nT/DfiTWMHSNNubsSZCGCF2BPtgHPNezeE/wBkX9p3x3MsXhHwHrV88nKhLSQEg9/mAHT3r/Wa+Ff7Kn7Jnw/0iHw74S8F2OnWoYG0VIkxAuNwz8vTJr1W6udN0pLPwnoWh25AlVJwkSAKgGCwwtfnmP8ApC0KT/cU2z3aPA7tZs/yYPDn/BNv9u/xUJW0H4Va/d+Q2yT/AEVlKtjODu29q+sfgb+wB/wVQ+CXie18aeEfhHryzWsy3sMqhA8LwHzA6lZMgjbnHUkCv9R6O3TQp1vdHhtYIFJe4iMQead1OPkPYbeuAKuT+LLzUkg1C10yBrW5l8vCIB5RUfx4656cGvAX0i6j3pxN6nBMr6SMn/gmd+1t4x/ak/ZK0Lx/8Z9Kl8OeKkjNjqFvdDyjLPEAnmp5mCQ4+bp61/IR8Z4dY+F/7b/iebxdbTQR3GrXEiybCqOPNbGGwAQQc5U8Zr+rTU5dJk1W2tI4/tGo5dQEB8mNB8+7aBxgYJ9Rkd65zWPhR8INV0tx8TvDVvq2kgNJA1wgfcz4ZyFwWLdADn1wOtdOA+kFSrNqpFKxnLgeaV0w+Dnw7+HmufCSwvBaRTR6hFE3Dq5RtoIDzjJK9yOo6UzRPBfiP9n/AMaTeNfhBIbrT7vDatopP7p4uheMHjd6iqPwj8K6d8NI77RvCcH2TTLwvPNbzMxSNIh8i2/PyNjscjHvX0f4Z+JHgrxVbrpltMdNncGG2SXDbtp2ku21cE9q/Vsg8Scsx8Uozs2ePmHDGIowcmjgfjB4G03VPDcfxk+EK/atMI8y6tIeJYGPLHb7HII9K/P+78Y6RqtxPdQOZHC/MTj5fYL3PrX6Z+GtK134P+JLvxV4fie40+6ONRsyweJs9XTsOOor5P8A20f2Tobrw5J+0X+zgrTRyZmvdOTkj1aNBjBB6qf64r7mlXU/hd0fLuLWjVj4H8ZarHHHayKhTzQzAqcDBPQgHofWvSP2X/CHwq+KV1qegeOtKTVtQsEMoDOwiWKQhdhIPXNfnJd/G4SFbC4hZ3VmiNsTh1dj1H0J9segxX2r/wAE+PGejf8ACb+NdI1gC5Z4LcoIzgBy2OSPf1+tfIeItVUspnWg7NHr5J/vEYvqfcd/8JPgR4Tvo5fD/hPTUuekkUkAIHJw25s5Bq081jpKItrpWnxbVYpb2dvGpbONuXwGU8545rqde8RtqOkJpmrxoGBEcUkeDIFJb5XPIwOuT2rnF8OSTXsk6hi1ooKlVwJFY7i+D93p07V/Bebcb4z2nI5P7z+isBlEHTU7I9EPjP8Asmzhj06XbDPFulYsWaBz0Geh6dB61z2seO/E2uxW/h66u7mESttjdXZcsG4OVwRj1zzXJXF9b2kT2skfmMoLIFH3zj7307VauLn7ZbQW0KYZowWK8bG9BXzOI4sxNR7npLK4JaHrmiarreqeJLQGIs8SPBcs7sxmGPvDJ5Ir/Nl/bL8Knw7+3D8TbCUZD6vcyLuHO1pf/r1/o4eFPETWWp2VigLbJOG9G9+9fwTf8FWfBT+DP+CifjKzRNgvo/tJPYvMA+eeevpX9NeAuYyq4l03sfkvHeCUIqTR+bz2bTEscAsCcDjvWZ9iWKTfI2CG4GM5Fd4bLJLHj5TnHY56CsyazmjPmzRn2r+uqqtJxPyboULHSzfXKCGNv3ncdAPTFfWnwn0W1gOy9Bji2n94FJwRxk46cmvGPC+mXUV1E8RwZEY4PZgOP0r6V8FarbabbXDTA7FUmVh0IJ6fpWYi1/wTa+JNxpv/AAWF8Fanre14INXtrRUjPAUnaGHvzzX+jt4n1ifUNavNKu5N179pkNuVURyiBQDgt/GGPHHPav8AKo/Yr8R3mm/tt+GvHSM0ECeK4DA+Rv2i5XPvgCv9UOa/is7601y2iE140Z3Xe1dyBm+X72Qea/kf6QSkq6s+h+s+HkE1LQrabJpuvwhZmgYM5DwSRbGAHTcOoH1qG+fUpfOW1nS4eDCRJbZWLZkdCMANjisbxCbOTxHJZq32nVXAD7OQxIyN3+HaqOiQRatrMWk61PHZlQcpEpIyOeG/vHHfiv4+lGUnZs/XVFLU0bK7tIbFxHabI5JCZJVfbK7H7yepAFbWk3y2V7aatZWU06R3EaQRJ80lurOFZ3yeQQcfSsdLi0His2WnWRuYYFEIhJBKyPnLNn7pGAa6aDUUudRZbGdlFo0YynymYgg+nQEY4r2sjqKFZN7mOLjzQaZ/nvf8HKPgyDw3/wAFQF1iwUxnVbVJnC9AynZkfhWv/wAGzXi6Pwp/wU9t/DdzKRFrFtdw+xKxbxx+Fe5f8HXvhQaJ+2H4D8a26lX1DTPnBOcYm/DtX57/APBErxiPAP8AwVZ+H2oFwq3F01vn+ECVWT+tf6E4Oq8Rwqlv7p+B1EoZlex/paa/Atjdx6hc3aXETXJFrFFxGmdwzKoxkk8ex4qC/h02fUWbXyT5CgiHkJ5rY2ttHRfertvoq6XrV3f3y/apUkP2dIwVWIOBy2eC2TnmuevDEvlfZGN7bzOzzPIQWjdTwSR95evHtX8CZ9gJyxEpNan7JgcRz0k2zoIobc6cBFuZ4nLSyE5VSDyFH8S/3fas2Wz0eW/GrxmeaMLnL/KinpxGMde5PNUYZm8QyW0Oob8q5kAQ7d0Y7sAK37vS54r1727uo0+XZHCOQq9yR69Pzr5+GW129Fod6rJLczNYsrae4NpboWuApJO0CIIw4H1ApumeH9L0ySKcxo1vbIoiSJ/9Y7d3GOMdAPStKLwva3UUUc8lzIC++DZ1fHcnB471I+ma3bWsMk2mT3f2eV3iC4jUjorSc/w12vKqz3gxfWadrcxv60buOzttUDxWyliokK7nhB4AAI5qvfRS6pogfXZpZVt3EiMhMTzg5UBwB93k8Yq75ljerHquouJLhQFihT/VmTP3j6qD15rmbO11GxvL64muxLfyjEy5/dRRdfl9D26965sXB0NZ6pnPCPNp2DWZmttRil0uMgwhFlmU7USJeqdO5P41XaW9Mk+pRQR6fPsaQ4I27STgAY/ip9g2o3yxaVPLvsGJXbyPM/iwWGT8uOfrVe3On3ixW80nmJI7q5Xpnsvc8V41So7nfRppasrReI7m5a20tblYHk5+zKMsRn727Hr71cu9Re0jmW+uGlhQqsrwqod2YdOaqzaHPDqEVxCY7b5ikYIyzc9Bnmvxf/bz/wCC+HwC/wCCd/xmT4L+O/B994h1mODz55rd4kiVyPl4K/mO1fccKcG4jNq6o0I3ZwY7NaeGg5zP2SlvLRNPW2u3g0zTmPlMow0wIIwSwPAPetqyvLk6Zc2UiERSY8qa1RpxNGB0bYp5I461/HL4w/4O39auLQaf8NfhpbJJuctJdxrIGUnIG0d/U18bePv+Dp//AIKC+LoRpXgfQdC0e3TcuEtZA3P0lAz+FfsuW+AGYSsqkLHyWI45prRH96/h/S9ZvFMUmkanbwOQLdY4ise3nO4cMoPv2r0LTvB1rp+i2dreQ20ZhLqzXUqIyIxJIHvmv8yPxt/wXl/4Kt+NoHhtPGcujRSdRY/uxj6ksa+WPEn/AAUL/b88axlPF/xN1idZDuObh+p+nFfY4T6O1ZO7aPExHHbex/qpyeJ/h/4S1uyfxB4p0ay/s1yqy3l5FJmNxghVLjaQOAT0r/ND/wCC5lp4esf+CpnjHUPCOpW+p2GqxLdLcWjrJGRMpJBKlhkEc81+bHiH4i/GPxhdyX3ijxbfXZc/PulkZiM9fvVxyQvgzzO07uSHmlJL8dueRX7JwD4cxyas5826PkM7z/60PCq8QkzyDyPWkAKqU6BiMe3rSjI+ZhjHb1FKzqwEf3v4sd8e1fqh8wNXkjYRnBBHr705iYRyACBj5jijG9P3XTqvv9acPljDMfp70ANRNzEAHPr2pi5GHHY4pAyn5CdmfWnltx+fgjg/TsaAF6fKR70hwewoygPzNkmgBVO45YUAOBYKSo/WmgNu2njnINVWYAkHP40ruxTGeKALYX5selNuOIXA/un+VRITvH1pbgny3/3W/lWifusqG6P6lv8AghRz8Cpn/wCmsn/oVfo54eUf8PMfhUfef+TV+cf/AAQn/wCSETf9dZP/AEKv0d8Pf8pMPhV9Z/5NX+XXiZ/yUuI/xS/I/vbhLXKI+n6H9GfxFAPhDxGf+ofP/wCi2r+YIHHwD+DSj/obLg/+PV/T58Rs/wDCGeJCP+gfc/8Aotq/mEYY+A3waH/U2XP/AKHX5IornXqd/D38OXovyP6r7D/kFaWP+mUZ/wDQa+FPGA/4q7Vef+Xyf/0Y3tX3ZY/8g7Sh/wBMo/6V8KeMf+Ru1X/r8n/9GNX9X+EMF7Kt/wBu/qfhHGk2qkNe/wCZ/9X+vOT/AJB17/1xf+Rr+T34jf8AJvnxW/7Gyz/rX9YUn/IOvf8ArjJ/I1/J78Ref2e/it/2Nln/AFr/ACb42/3yHoz+6uAtJ1PRfqfvlrP/ACjd1n/sRJP/AEiNfy1fsD/8kP00/wDTWb/0Y1f1K62f+NbmsH08CSf+kTV/LX+wOP8AixenH/prP+j11R/5Fi/xx/U6ODv96xHzPyT/AOCu/wDyUPTv+uMn/oNfzzy8SNn1r+hj/grmC/xH0u3QZd42QD3I2j9a/nruY2WZo26qcH8DX+gHggv+ECC/rc/mLxY/5G8v66EFEnLcetFFfrb3PyoKco2chiM+lNopASb37SGmEknk596SigA+tPjjjLDGaYRnipYlKsCaAL6WMDLk81t2ek2hAz1rPtyMV0VoDndQBH/ZtovABP0o/su0POKvqQowakoAfDHGkO0VcjdU2qopibBwaexiUbsim13A2oJiq4HeuhsZYtoA5NclBIHwI+fpW9Zgxke9VKly6jszqrq1ttTs/sl6WEfXKnB/Oufj8H6CqbBG7g/3nNdFAskiD09asLgjikqV90VGTRz9poumaXJus4hG/wBS369K2UR1IPUGnSRfNtPFORXUAEHnsf8ACrVGxMp3Gv8AepyEAYNPaORuinj2qqzxocuyr25NZyVjKUHvYsr/AKwtkAKpYueAoA5/OvAPE3ii51y7NtCfLtozge/Ndz481yRbH+yNNDM85HmMnPyryACK83sfCHi/Vplj03Tbmd5D8ojiZiT7YFYyrQWrZ0QozktEYMiKDwxJqMIqsE/GvrPwf+wz+2B4+hSTwj8OdfvxLgoYrKYg56YO2vqv4b/8ETf+CmPxLYnTvhlqunxKQrS6hGLZFLdAWkK1w1s5wlPWdVL5o1WArdEflK+Fwuab7V/Rx4P/AODXf/gpz4oZG1DTdI09Gx809/HnB6nCg9Kh/ba/4N2vjz+wz+yDqv7VHxB8U6VqI0iaCGewsmaQqZn2bt5ABxnpXFR4vyypUVKNW7fmb/2XVjHnkj+c3B60uQeNhr9jP+CJ3/BP74a/8FIv2uv+FCfEzW59Es1sJrtZLdVeSRohnYA2AOK/sWs/+Dav/gmL8P5Wl1S38Q+I2tpRHK3niBd+7OWAVf8AA15vE3HOCyupy4m7Z3YLJ5Yt+4z/ADYPIl27lib/AL5NaNhoWv6jIItPsZ5mOBhY2P8ASv8AUj8G/wDBID/gmD8PpodQ0P4XtqC2hI8vULjzxknOCp54+lfb3gH9mL9h/wAG2u7wj8KfDdjOmGWV7JG2DuMkZzX55i/HvL4r3INnvPgWtuf5Lugfsz/tD+KQg8O+CtX1DzfuiCzkkz+CKa+nvhz/AMEnf+CgvxR2f8It8NdWXepZTcwNbjaOcjzQvHvX+s14avvCvhRzqvhXRdO03T4EAWC2s1BPYPkEADPbFereE/FGp6nrEUetTokdzHIPIXaAMqcbU69vXPpXnYLx2p16qpwgjCtwdUpx5pan+Jj8Q/h94x+E/jrUfht48s5NP1jSJ2t7u2Y/PE65DqT0zXGqcHNfqZ/wWp8NzeGP+CnPxYtZhjzdYllBYHDLIAQRn61+WanB5r9+weJVajGsup8dXhy1OQsxHeNp9aZJBvc5ohyORUzNglm6V0GUldFdYxCScbsdcelWYd88qwWyM7ucKqjJJ9gBWloui6n4j1WHRdEhe6u7phDDEg3FnbgAAck1/dh/wRa/4N//AIc/C/R9N/aX/bisP7V8UTol1o/heQAQwIfnE131y3AIQ44r5/iHifC5XRdbEyS8jqy/LauImoQR+Q3/AASr/wCDdj46/tm/Y/jH+0MJvAvw4b98bi5Xy7i6QdVhjbacEdW6V/dd+zV+xJ+yV+wn8Prfw/8As2eGLKxTCxz6hfJ5l5fMo4wzfNnPOMV7Bqni+58Vy22n6YsVpptqFgXbG3kwBRgCNFAxjpnHvWzrGlNqWsRiGRZbO2VVWeNhuTHJYjuc9hziv4w4/wDGLF4ycoQlaPRH6/k3B0KNpT3NXTbG91v7V4mu5meznAhtrZ2ATywcsrAAcFuxrfs/DOmtczQeIygvJVDpFCR+4X0JX0x16GuMk1O/0DU4VXD2flfOLU/MqknlVPKOSORzn1okmvJ7V9W0uUm5O0/ZYMJMUdtvXlGPPKnivw2rn9ao9z62OCUVZG2Y0vkm1u1SWQcwJC4I85AclgM4U9Qem7p1rKm16Twxey316DLqDQ+UiZJBjzlgxBKhlHfdkjisW0ay1CM219JeJqcDEK8DiQLswRGCowrEnnI56HNGtQStqRtdUds3Q2i3RDJIC2Ad7ghQCQcqc46gk158sZUb3OmlSsdTod+qauhlANxKoIlY7sbj8qKTnB+pGO1UdVstQtdSEFrJ9l1LVciUKw8qOMDLTbOu7Hcd6dY+GP7PtY4/D0f2e2yGg+0uXeQnk7VJ3BQ3IzjA6VrT6bE9pdJPOLe8kJSS7Zt7ySEY2Rg/7PA54rmVRmbtumeZ3uqW3h27hi0izuE2f6OzMHZpTwGkdV7jpuNQfELVNTtkVr65AjiTELFiFUkc7hu5fphscdO5rqdU1qzjW3tY3e9vre2iiLyqcxySsMs7+w79c+5rzC+e0EPmDzWUsRi7IcmRSfuZHCZJPU/SrjLXRnbhkpKxys9hr97aJqOqM32UyIssjggvK/ACrksqgnqAFBzzzmt+w8KT3CuHDPespOUVkVYxyzxjPBXv3btUay32oj7T4gndxMphMcTF40PA3uBs4BGeh7V0eo292+oQCyuWZvLVVhRhujjXl235C7WPO0j8a9rBZvVo6p2OutglUjyvY3fhn8WvG3hiUWEYF/YbERY5MbzHGAo+uEIxnkg19P8Aw/8AiXoGpXJvPC8fkSOxF3pOAVdf78YPG4dce1fIXhY6lNqZtYne5Qb3m88FVUMMDacYPTIyeM4rrdL1KXw/r8epeHXSctnzJHOJVVR/Aw+Xgnv1r9w4G8W8dhq0YyleGx8DnvBNCcHOOjPEf23v+CWvg/482918bf2ddmmeKFBle0ACxXEi8lcdI5D3Pcmvyb/4J6+HviJ8Nf2qNf8ABXxO0S60vUbm3/ewXKMu54GzlVYDOc9e9f1CfDrx7eX4u797Wa1MIWM7htWdiB+87cD1FUPjD4f8La3pc3j4adbt4j0obLa+RQJQrY3DOTlSOqt1r+qOIsypZnkE5pWuj8rwdGWHx0Y36n5/XaWn2zVJbRGM+doEg+SJec8d6u6XqeoRWxju5DcSIDGzfMCyHg5B/u9a1bWNYpZtV1FmvJ1ZXS2TEas0hOS7NkNjpgdqzYb7TdQvSly0qiMlTGkeN4ZuI1bGAPTP3etf5157C2I0P6XwEk6KRzN+hv5FdzhUPyj+JM9wPepLrW44kNv5RMkqBc4+5z1Hv3z2NdlpGnXN9qV3tji82QkrHcMSkYXnBx3FcUkPnyzR2RkN5KMK8h2wtyPlX/Z9uteFON3qepOSeiO88AQxSeIo9Y1VRM8zjyfl3KAfvP8AXA5OK/jU/wCC9/hiCy/4KFT6+6+Xb3mm2uOnOIyM8YHUV/Yxpi3c2mPLdxuhtsBZrQBCh5UKd45yPzOcV/MT/wAHCXh+3Hxu8G+NIoENvcwMpbOXcpjdnHy+oFf054BYxrHpH5R4gUE6Ej+do2bHL9gdrE9cN0FXGtYUty24KFboTyc1pTwPFcvCkWVifh8jA29CR3zS4heNjJxg5Br+363xNo/C32I9NttSsbhbiMBYTwxbpjrg1621/APB9/PC2+OOMynjHIB4964fwppr6vfSiTMkSLlh/DzxXpWqeE3l8B6lapiEGMhcHavQjByayA/Ov4QXc2k+MNL8UKuFTU/tQb2Vgzc+1f6rHhrVLfVvBvh3WvtIJv8ATrGSQHLgRGMNkdh1r/Kx8ASBNKW38gSGyvGDOuCqg8Ec8HNf6b37K3imD4h/sr/DfxDpVw01hd6DbCS1SM+cZI4wGw2CApKn8a/mf6QeWJ0o1T9Q4AxNm4HuEd42h35s9GtWkm1VeJwDJIYycbVAzjNaSQ6hHcjQ47WN79SBGxGZFBP8bdAB79K2dEt72zguNa1Nfs5DCK0i63G5cYznoPwqTWvEdxNG0UJjs5p1EbiRd00jMcYXuPf2zX8Qz0dmfsid/hGXOpP4e1a60zahhkUHzIipMtwykFeOgB6n8apadEYp7i0soWN0kkUUiRyCNEAXHlj1J79jWdPplpbuFvDJHLsAt/KwNrdSOTk5xWx4b02WzUsjMZlLB3H/AC1cg8HIPIHU104CrBVU4mdWnPlfMfyTf8HdHgS1tLX4W+O4clwz2zE84XaG2k9Mg1/M/wDsOeN7b4e/tz/DTx1fzJbwxaxZ+Y7sFVVaYZZiTgDBJya/sH/4OqfhU4/YE8DeNJoyLmy1wK/O7ajQvgDvg4r+F21l+26NBGZGiE1tCQ8YBdeBk5PI9Riv9GvDeKxmRxpTla6sfz5n8/Z43nR/rYfEv9tT9jTwxb3fhvVviVottfTQiSRl1O03CNRzjfJ94ivz+8ef8Fff+CUvwj0ISX/xDhuvOBRo7WQXL57l1hBKnPbvX+ZxJ4R0Kd/OupLq9lOfmmfGAOndjmmt4U8N7l8iyRSvPLM39cVxT8FMsnJ1Kk7hHi2tBcsT+/rxX/wc5/8ABNHwrp5h8PLfaveW6lFdLC4G4LwAC20DIr4+1z/g7b+F2ma1PdeAPhjdXYYbVdnjiZlH4E/mc1/G0tjp0ZHk2kKkdDtBx+YNaSztFhYgEHX5Qo5/AV6FDwdyWLTUG/nYwnxViZq1z+oT4k/8Hbv7T+vL5fwp+H0OmHB2tclpx/46Bivme1/4OW/+CkHivx/oI1aPTtK064vY4bpYrdt0sbsMoxYnA5r8FriaSaMglt3oT/hXKa1LLYi01DcwkguImzngHcMV9BW8Osnp0ZctFXOeGf4mL3P9iTw/La+J/D+k+I7CRI7e60+K4kjPVWkUSMyD6ng1hf8ACQQXqmFJTBaK37qQglrh8/cbHX1/CvIv2R/Ed540/ZS8A+Jfkmhn0yzzMzABQLdOGXuM9a9ludFW61EW9gY5iCGHJSOM5B3IenTPvzX+cnHGD9hi5wj0Z+8ZHNVKKch89/eTeVbRIumiwTzHGcKpJwx2jkllP4fjWJp8jX8sukyWYjtI3ZllKlcjr5vz456VHcabPFqc2i205uLh13M0ufkYnoztgc8YFdDql6EtI5rmQva2o8m7ZehcHnae+Mdq+Dl7r0PoKXLHQp2civ4lgvL5XlMG0K7khSC2BjPf3r+DH/g6J8ExeBP+CiXhPxrpqJ/xOdGV3LLkPIJZIzuzwTg1/eVHd2Vw2ycSyh8SQA/JhR0yT157V/F7/wAHX3g57T4i/DD4lXQO+SNrUk9ANwk/9mzX9S/R3mqOawfdM/PuPoc2FaR/KdDHcQQiAvt8vjbgAgkDPIHI46U3yzKm8tz6VoSKBKxPck/nioRhcCv7nqVOY/CupDG0cY2upzUpw/DHj0pJMnuAPQ0u5QAAKyAascaye1JJErKEPQdaVj82PU0hTb9w59aAI3SRVwfT5v8AaHtTPLcRgwdGH6dqsKrcuhY4+6MfpzSLGc5yABk/n2P0oAgLFCFTsNw+tMMUbngH+8fqasNwAfQYz9KgVWU5J+v40ACYY+axyvTA7U6Qxvxk+2acDtf5cFvVun6UwtuclVwR19/pQAOAzAEZFN4JI2mldWUhh25p7MpXcDjNAFTIHtTD90/Wm4449afgkH3oAliYI+5ufQ067kzbyN/sn+VVm4QA068OLKQj+6a1m9GK3vI/qq/4ITQl/gbcN/02c/8Aj1foloIx/wAFPvhX9Zv5NX53f8EIpD/woycHvM/86/RHQT/xs++FZPrN/wCgtX+W/iWv+MkxH+KX5H998If8ie390/o2+IX/ACJ3iP8A68J//RbV/L9g/wDChvgyf+psuf8A0Ov6gfiHhfBviQn/AJ8Lj9I2r+YFv+SCfBn/ALGu5/8AQ6/JX8a9TuyFr2c/l+R/Vlp/On6UR/cj/mK+FPFv/I1an/19zf8AoZr7s03jTdKU9dkf81r4T8Wf8jVqf/X3N/6G1f1t4OL9zW/7d/8Abj8C4zX7yPz/ADP/1v685P8AkHXv/XGT+Rr+T74if8m9fFf/ALGyz/8AZq/q/mbGmXh9Y3H6Gv5QfiGP+Me/it7+LbMf+hV/k1xx/vcV5M/uvgSLcqvoj97ta5/4Jta1/wBiLJ/6RNX8t37A3/JCNP8A+utx/wChD/Gv6kda/wCUbOtH/qQ5D/5JNX8tX7ArH/hRGne884/MiuxRtlcf8cf1N+DX/tOJ9Wfj/wD8FjZbqDx1Yz2ZIkRGIK9eGzX8/wBM3mSM5Jyev1r+hn/grhI8fxN0d0AOTkg9CM8j8jX8/wB4nht7XxDd29rzGsjbfpmv9AfBLXI6S/rc/mHxZds3k/62MSiiiv1mW5+VhRRRSAKKKKAFHBzTi/FMooA07dyRgV11hyuCa4mGUIMtXSWV6CBjFAG033jUw6Cq+5Tzmp1ZcChATyMFU1nT3sEBKO2G+mf0qO4uih9a/ej/AINxvgV+zh+0r+3VL8Kf2j9Ai8RWV5pk01pDPnaksLB88EE/KDmuTMMbDC0ZVaiuomtGk5y5EfhTp2sW4PkLHLM2ePLTB/SvbPA3w1+MXxCm8nwP4J1nV2C7gLeCRjjjnAXnrX+sDpX7JX7FXwU1Cx0nwd8K7K2S8JitiYEIDoxHJYMQMc8mvQLqx8OeEbQWll4Y0vT9RtXZgwt18lrbOccYyxGB9a/Dsy8dsLRnyxpfifY4Tg2pPdn+Un4o/Zk/a5+HOjWniD4gfDDXNP03U5PKtZpbeVfMcfwjAJz+FeneE/2FP29/HEKXHhH4Pa9LHJjDS27oOemdwFf6meo+OvCGoeH3j8TeHbAGRQbC3MQwUIwcjtgivKbDxbfQwrYW9haWstuds8cSKqlW6bWPJ5I6Dj1rx8R9IlJfu6Z6VHgOUnqz/PV8Ff8ABDv/AIKnfEWNGtfBKaVG+NzXCNtUHuSqsBX0r4J/4Nqv2/8AxQ6R614p0TT4lBMpJcsrL1TOzkiv71NC+Kms/wDCP3tlpsYRYmPmTZYMi5wQAR36Ag9awIdUubTXNPvdVVltJlPkRqwbe0uQC3uCep618ljvpCY/amkke1h/Dqn1Z/HN4T/4NYviRqLQy+O/iU0auSGFuoJ3DsFbnP4GvsLwT/war/su6bNbS/EH4ia3fzTuoFugjj3E9iVOQpwRzX9Mj2F34ftot8uJ4Lhnjd+oY8yDgZPGMGrtjommK82szZSO7/eI5PzM5GAV7jGMfU18bmHjtmk9I1WvQ93D8DYeEVfU+S/hV/wS5/4Jt/s+aPpfgLwh8LdIuNRt4wpnu7VL24uWI3Fi8wOTn/DtX1JoXwz+Dnge4i0/T/Anh/Q4LdHll8nTrZZYm/5Z5CIDyOvI59Kv6fquoadqq6hZlGey5xP975uFCk+h4IGK6+9ubh/Ez67YwiRrmMpcpIP3Ss2Cu/uM+uOfavicf4l43Eauoyp8NU4P3Yo3bWS0sBLBp1gtjE6Ew3BAjDsRwFC8DnHU1y2oeJ9T1RP7Jtr0wIJAl0gVWkIXrhzyBnritK51LV5Aln4ihMYJ8sbBxASCPMyOMEc1j+IvBsF9oy/2LII7e0k3/aP+Wk7n7wBHJGetfN1eL8TLdv7zvo4Cin7xq6zr1xrKW+lLMIQH8uFoF2tIMc7sc8j06+lfl7/wW1+Glv4w/wCCTnxSs9SiSO+svs91AsZ/gjmQ5KL1ODzkZr9LRb5I1iKP7PKwEasQQIlwDux1OR1968O/bs8AQeK/2KPjBpTzSTNJoE8kgYAqwhgeRQgA4wwBPNfa8AZ9UnjaV31R53EWFprDtRif563/AAbi+N3+H3/BU3wm6Ps+2Q3dqCOPmkiO0fnX+kxdQajr3iLUJIrifUb23wtxDgKDvIIYjplAeoNf5Yn/AASC8XSeDv8Agpn8ML5WEO/xDBAxJz8sr7WBPvmv9ajxMskWpQzaS6QSqEWcbQBOhHReDknFfsn0gXONaPK94nxfCTXM5I+ah4budPult7Ofyri4bzpLiEb1KnjaXORuHQ16bo3h6DULpdJmUWFrEpkeBseZcvgjcCe2a2ntLTT7iSwW38y1Eq7oz8xjUYJPBGOTT5NLXWbiTWtSka3EIAt5Mgfu+jE47V/KNPE1JStc/SKlW6sjimu7ix1n+ydRuvLtIIissQxjoSv16U3wzbXba7ZJYo7W88zt9pYhXWQnAABB+XHrXq0XgrwxqYWO5hLKf3iTcZfA6nPr/KuhlksPDFnHfZjKrIomDcsF3KRtAPJAIyK9/JcJP6xzcxw4zFx9ny21P8tn/g4y8IyeFf8Agp14rN0Tvu0imJIwDnAz+lfhLtQgsHFf1j/8HVfw4sl/4KQ+HNVuUC2+t6NESVGAzByB0+tfzr2nwh0lLX7RcwqCT8wJPA5r/R/g6upZZQb7H4Rma/fM+ZYWQj7wqUqsp8qI7pDwAvOSTivq+2+Fvg6VSskI+b5Rgkdep/Kv1R/4Itf8Ey9J/bh/a+j1XUoGTwH4IeO51WQg7ZWjJKxKx4y+059hXoZtm1LCYeWJqPRHNhKXtp8kT9hf+DeH/gj3ofgDQtL/AG9P2ptLik1C/YP4T0q/TK/9fcsZB4B+6GGO9f15aqdTv9OlXwrqKTJG+Lq3VQJJpmbKlXwGATlQBwRXFPrujrcw29lpywaTpcS2NpaxjBjiRAqY6LhlK9M1Cmja5pd1JpolaKdwvmyryIlwGU5ByeSF6ZzzX8IeIPHVfNq8pTdovZH7XkuUU6EFZamNZJf2UK6Dp928ZLu93NKDvDk58oEnvjtTGns5tTm8L7HYXAEqS5XDEAhXkGcFf4TjGCRzmug/szUNNuoodb077Rqcj/6KME5Vzt3NkhTwCQTzg5wK0oYZ586fMrX967lZ5jgwgbh8qnKnJ9AuMAnk1+P4+k27n2znFRV2RaFHDeSTSzEWVlAdizuAWllHIJAOdgzj+prXsTeWNxL5zpCI0RYYwNzEhstIrDB2kc1q+ILbVr68s9P0xI47FYXhknkyFjAAzsxncc56gGse9ij0lYo0aS71KeMW9rKifPJGuMjg5AxnnBNc+HympUfuowniYrRsboPiaGw8uwh2aTD5zS+egIE7rjG4nOS3p71gvqmox6kWhlkt3nnHnJOdsbnOQ4Jx97rWJqGp+DvDImvPipr2naFp+SYYZpo/MRVGdxDsqgk9eT9a+QPHH/BVT/glv8L7aez8c/FKxnuYW+ZEl3PuQZAAh8wHA4+9X22W+HWOxMU6dJnh4nOqVJ3lI/QuwvY/sN/qaytFNOQiPIMMhwV+X25J3Vla14i1C2t4NKEPn3IiZFnVcpG2wkysw53cDB9a/MHWP+DgD/gkncrb3h8cWss8YEZQfaAABxuP7nBPvWh4f/4LMf8ABJr4hQyWVr8SLawku5NrDzHzjHUebGoFfQz8I8xiruk/uMIcVYd9T9GNH06zOjHT5LiW4zKDdmQgSuMjAJIOFJ5H0Fcpq6zPcT3VpCbiEZWJW5dB975QMZwT6Vy3wr/bH/Yk8eaktp4A+INhf2tzEPMjkuIWDGMjG078qPbbXsOr6rf+M9akuvBX2G/tgUWBraddpj/vFh3wOlfO5hwBiqHxwf3Hq4bOKVT4WcZaw2Ou6R59oxfY4yUGz7vDBh1xkc1nafHqh1DKJ9ntZJljWMjmQfxHceQp6mt2Kw1PTvObUVeMDEbIVCli3IOAefrkZro7G9tl1G1vrxCyZ8iIMceWM8nAzyfTtXy9bLJwXKe3DG+7udLb6FHBPLqc92LxWKxiGNsogHHysCPWuPupNuvLpQH2lDIFtorbgqwz8sgHvXo0emWVna3eqafIY7FRJsDkYEuMkg85Ga7v9mvwg3iXVp/GmqqUMTEKuPlaVs5IPQlc4+tff+HXDc8XjoU7dT5viHNlRoOTZ3uh3tyumwWaqsrxgJcQngYIHC+4PFReIvDtung/UNYtQ0kMH3w4O48jj6DNd34l8Aaho979q0aQrG8jSj1DnnnHaqknjS/utFvtL1e0YlLSQsQuVkdQcH6V/eGOyfky6dCm7Kzt9x+G0a7lio1Zdz4I1ix0m5tXuDMYmlKCKMYAVtzLvwoGeRwCcn1rFW1W0tJYtYZ11K3VjAsO1Y3JO7LcDoP0461JYXDC6u7wzlrsbPJgIykPON2e+efpmsQ2j2U1v/a0vmmYFjIo+Vn3ZUEnJGPXvX+b3FceSu7H9LZVLmpJo9LsfDeieI/s+oT6tHavCircIg2lmUHkr0Y/X6mvKb2xlS9Meml44Y3WOIyv5gRmbHmbznB7k+vTFbMFrqsIkkiiDtIFULklmZ/7uBkn6ZX3rGmsxFFcT6jJ5l1HIsUVumNxZT99z2B/Ovkvbp6Hrwg1JtmzNZxxalPply63EoY+Zlm2TDPzMMAgNgcHqDyOtfgv/wAHDXhUa74S8Aa5pCC3t4klBduSQxyoJwOccZr+h3SI7OKWPVNRuGuBKT8ikna4Bwu7uvrX5Ff8FtdEtta/ZOsNVtFiRrGeNZfTJLDA9ziv33wOzRUszpU+7PguNqHPh5M/iuvC1vqFwSAgVsHpz789aktw0w2M3yv6HnHrWv4+sbLQL1Lu3mSSJokYknG35RuH4GvL08ZaI58u2u1DOduVU7sd+MdK/wBAKkowbTkfz64SbukfQngCGC61KRGYW0KbcRqeZmB/H8a+vtR+H9nfeGJytob+W4gJltm+UcnOVzivif4aanbXniawvptPu71bNikKQxna5Ixk4Gfwr9X/AA54P8V+KNGTUrLQrgzygIJXSRWRRgYICmuGtmeHp/HNIuOFqPaLP50PAsUula5rWkeQYEs7538sdUwSpwMnd0r/AEgf+CX/AIsvNZ/4J5fCjxVGrzqli9sZLf5BEQ7qWlA6gDpnvX8I9h/wT+/b1174leKY/C/wzuru2vnuHguJI2UYZjteIttySOi9/av7mf8AglD8Kvib+z7+wf4Q+Ef7RKTaBrFq1y81nJtMjRO2YgwVjjO7pmvwLxwzXCYjAxjSqJteZ+i8CYepTrNzifeI8QwQ3UMnnXUtvCSsk5AeSQdyCe1dY5t7mNNSgnjsTuxE0r5kZTwMKQeSTwe1ZUnhi5tVXUPEeLa02Bba2O3dMQflwoPyr3OeTS69Nb6TYW0shF1fFwNkZBWKPoocdN2ea/hTF025tn7XRqQexuaRZQThfMj3G3uGkZ26/KODk5PNRT61fxX8lhLJGxZDOrYwiFjx9TjrVKO01PV9HlsdIbypo3L8nl93UDpyOwrJu5Le0mW304eawHlRhxgB2HzSMT79qWXwarRbNa9SLifjj/wcfaDP4t/4JoXc94vmS6Repcs0f3RhtgOOnRq/zydI+fSrRlYAfZ0GFPI2qOtf6X3/AAWB8Hnxl/wS8+JVjH88enWkkhZhksdyscHvg1/mZeFXlk0CJpGYhXeNQT2XAH86/wBCvBTEe1yvlfRn898Y0YxxLsdLH938KcOeMc+1JH938KbuIORX7dFcuh8Q7EhyuMCmkDbgd+aA5Yc0mfmxQ2Q5JC1z/ieNn0aSRRnynRz9Aa6Fhg4rM1lXbRb1VHPkHH4HOad+ZNM0g9Uz/Ty/4JNeIbTxN/wTS+Feuwyeej6dsnkkOQpjJQjHrwBX3bPPbSWU2mzxTXbwENHBESgkG4AYA5JGenpk9q/IP/g3u8TQeLf+CTnhrQ43VptON1GzNk7SZyy/oa/Yaw06ykvitrckara7iy44k45H5ZFf5o+LuH9lmNVLuf0NwtW5qCGrd2iTpcalDLJJfw4khGZA7rgqu3PylQMGtSS71lLKzbXCqX6ku0WFCrGw+Usg4zyOOo781h6fcS2OmTpDciXczTlypfygflCKexIHNY2kbWuNSu7SYmfiQiTLOgY4PDDHJ/2uPSvx51ZNWZ9Vo3odheWaGcxeIZY2jUb1kztA46cdOa/lj/4O1PCWm337MHw08aadGyzwasYTnJ+UW/XP1Ff1HXsccs8M17CbqZI8rkfKSTg4Ht3r+fn/AIOdvAs3iD/gnXYa+W89tB1VZi+DwG3Ltx2xkDrX9B+B2PlTzSkmfE8a64eVj+CMSF1RycZH9BQPk+TAH1qtYOs+mW8zHkxIfxxVgN0U8kjrX+hVn1PwO1hQobORnHPNMGOAeM9BSeZtbcvQ8c04llU7cAn+VADGcRM3qvH496FKbTjPzNn8ajdmjdfQckdyp6Uqy7gFPTkfh2oAeATgFjuH8qlYgDdjp196Yr7ThBxShsbioyT0oAY/YkcYP4ComUjDjqAB9Qac4/eBmztbg0hBWPaTu7Z+lADB5IkAB68c0PjeQTjb0oByNx5B9O1Ee3GR0yRQAO+VD44JxSjaflJpgGcDtnigqQ/uKAIJMoeKQN8uaGJAOaQKNuKAEAbaAwqK8ybd/Taf5VMM7goORT7qFTavz/Cf5USfutFQ3R/VL/wQhH/Fj5h/02k/rX6JaH/yk++Fi+hn/k1fnX/wQkcj4KTJ/wBNpP51+inh395/wVF+F8Z6Dzz+jV/mD4k/8lHiH5y/I/vjhL/kUR9P0P6NfiKf+KK8R++n3I/8htX8wj/8kF+DQ/6my6/9Dr+nz4jqF8GeIB62Fz/6Lav5hWG74C/Bon/oa7n9Wr8fTvUSXc6uH/4T9P0P6sdN507Sn/2I/wCa18J+LP8AkatT/wCvub/0Nq+79OUDTtKX/Zi/mtfCnixAfFOpH/p6m/8AQz71/XPg9FqjWv8A3f1PwbjTSpD5/mf/1/67p/8AkHXg/wCmUn8jX8o3xC/5N6+Kv/Y3Wf8AWv6uZ/8AkH3n/XKT/wBBr+Ub4h/8m9fFX/sbrP8ArX+TXHH+9w9Gf3dwD8VX+u5+9etf8o19a/7EKX/0iNfy2fsCKD8BtPPpNOf1Ff1J63/yjW1r/sQpf/SI1/Ld+wPx8B9Px/z2n/mK7ZS/4TIr+9H9S+Df95xPqz8kP+Cu3/JRtM2HkBlUHpyK/nxv0lW9kFxnzAx3Z9a/oO/4K6QCb4h6SCcZZc546kc5+lfgh41ms5/FN7JYY8nzSF29MDiv9AvBFWySmj+X/Fz/AJG0v66HLUUUV+sT3Z+XBRRRUgFFFFABRRRQBKoBXBq/bTqrYHas5Cc4qVcKcigDr4Jg0eauiRcD/P8ASuctbkhMVda8wOKAKt3cEZyeK/bH/g3d8fxeAv8Agqj4E1OV9kU32iBhnAIkiZMHH1r8PriTzCPSv0T/AOCSHjGPwR/wUI+GmsytsV9VhhJHH+tdU/rXjcSwU8vrLyf5Hdl/8ZPzP9YXxp4xuJ576z0QNDFaShzcTA7FZlDEJ7dfxribPXb7X7UweIIFlsoYtwuQQGPfcMc7e/8AStPxxYm31a4tjqJghnMbJEyl1KBBnB9DzxXlEUtpbalBcqgePTXDRRZLJtx0GOxHUGv8xOLakvb6Pqz+kcmpwdPmsdNf3B1G2Q3wTURIrRWE6jGOMt6Y2iszRLWI27T6jbPeSWSlGhHBlx3kAUsQM5ODxkHpxWfFf3OpakUvU8qGVi8dovG1HGWMeOFz3J+leg6f4gt7RjNdILdF2CB8ncsYPr2Y988kk18xCrJdT1o1FqkjH1extIfDUN0s5kv7hyyQwDESIcbhJu/iGOBk+1YNm8kJS8jlURMoVOCTGR0BB7Z9K3NS1P7XNJqVwgEEnzgLyWzwpYDAz656VDLpVqskep3zsI2CtGF+ZfMUcDnpzW95NlUotX5mdRHZP4n2XTZgu7tAkkpIKoy8AgcYLdvcUuowXseiGJZmnW0JH2mVMZK5xtUYx8wIbj3FatvpNlNbeZCMyzAS7Q23bIBg5zxgn3rUlmaIhroR/wBsNGvmRMNyAAkKwI4PHTrW7oya0RM6sYnn/huxGqy2WszxiYBiZ1BO4kqSpYE8qrAY75r0+6u5D4ZGqXDbh5padUVjvATIBwSQcH25rhLG5bw94ngN2AYrshPtClTscZfBQnIGe9enjVm1iSTSYxGJnYrK6jKMwGQVxn5hVUcDVfQ8+vXTJNLnktv+QlP5xKM+wtuRkI+VCDzkA4FOtNI36lNqWhtG6woBFaSMdsbHnf8AWuZ1DRrXTpJrnaZLgfI8wO1vmHc/41XstQl8MafLZ6m6zW748vIPnMx6DIB3D2OK6YZNXfQ8ytVjHS50xbXNWmaWRFMgbypkPyiTHICnGOea8/8Aif4d1jxF8G/iD4Tn2fY77wzqMIjx+9DmBxlsHByDgZr1fSr6VrKO21q0O1CH5Xaysfu42k5P1ArtIdKuNTiv9KvLEeZfWc1u8+5VbDocIx69Bx2r7ng/J69LE05NdUfPZzjoujJX6H+Od+z1rT/BX9uzw1qtyuw6H4ot3IJwQIrhc/yNf7C0vibRrq10/VLpsC9SG4tAoG2NpBuGT2ABHWv8eL9qvS7v4e/t7eNdFulKSaT4qu4yCeV2XDDr7V/ra/CqSDxn8Efh14w1SQrY6l4f092EX35JPIQ7WcEAD37njpX9JeNuC9phqNd/y2/I+I4ZqtVHBdT2ZpH0yeQxxCS4vHKSAsCuRyz+uMdKx7/XbAQyTys91Zptt4Y48AyMBz6Y561Jqdzd6zbTQ6FaLb3cQC+ZOeUQDAK5Azx3G4e9cVaya80kulW0lvcmVVEsipiKE9zn+FsdsnNfx9XiotwR+pUaTa1Otu9TuBPPpk80izwRhj5WCsUWAdvAGW9MfjWNda/omq2yW8a3DzxhWtJeMgqMktwBy2Ay4ORWNdWkWn2KrbtM8EUhS6CYUXO/hRg88Y59qfd6n4ht/wB7ZTNZNEqiGNACyqOQwXpjtz+FdGUVJQrLlIxNBWP40P8Ag7V8J3Vn8Y/hJ8Tprf7O88C27ZBCqVIkI57DNfy/S3hlv32tklyrAcBhnjaK/sY/4O4fDuv6l+zh8K/iZq0fNvqgjztKkboSckZ43Y6V/GBeXN0839oNKshcBlKj+8Bha/0S8PKkqmUU32PwzN0libM6TUr2/WzW00gGTULyVbS0hHJZpDtJIHJ4/XFf6Pn/AASy/Yk0P9jD9inwx4WkH2XWNegGo6y6gJNOZUEhAY/88wwUD3PvX8O3/BI39mr/AIa3/wCCi/gXwTqFv5ul+G/+JxfBBwwtB5vlse5d9q8+tf6dOsDRfETHw7NapLYWEASIsMBCBySR2znj2r8x8bM9lRoxw9N77n03C2CjzOpY8r1OxknmOoW8RitJsiFZAd+wY5JXgkdq1pJZ7S3gsL2J5I9gLq5zIxP3UXHB/wBoHnkYOK77wj4hvNUkHhwPCILBtskkSEIYgMlc+prqvDtpb2lpPF4ctZbUXVxvYyZYAAcFSc446V/HtVyc22fpMcY4rlPK9burWfforagAyrzAgCvbg8bMgfd/3iWJ74qbwuLnVbg6Npcb28Hk4Ak4dMJje2By5Jzxx6Vo3XhnR7Sa5XUkGyOYSpPzvd+qhSOepxirT6j4hvoPKsiLOV1RUTAaRlVQGB9AB06VphsP7SaiwnifdfQXQ/B+m+HLXVta+IV6LjTrFN8xu2EcMEIUNJJvJU7cL36c9c1/IR/wVM/4Ob/BXw61nVPgh/wT8062vr6ydrSXxLcr5lum3IJtE4JJORvJx3AryT/g5P8A+CxHiaw1e8/4J4fs+arNFb2qqfFupQPh7idlBNqjjBKKMb+eTkdK/iSkMn3mYncOefXtX9p+GXhbh4UI4nGQu7XR+Y5zxFUlNwgz6P8Ajf8AtXftIftE69J4p+NvjHVdcnmY4+0TsUUk5wqjAAHQACvnmSUSsXcl8+pJ612/w61HwWuu29h8QoJZ9OJxmNtvllj944BJFfoboXwA+CV1HAkVkJGulDBg7MqqRkMu51JyP9mv3bCYWFKPLBI+QxGIlU3Z+WSIpkKICc1ZEaQN5jLIpHOV6j86/ZW9+A3w0uBnQtAsreWJSFimXJkHZgc8k1gD4Z/D3T5obkaHavFCd1xugGAmcFeSckGtJJW3MFSl3Pyp0W78QfbA3h6e7WVGyrQswcH/AIDX6Zfs9/tZf8FL/hDZxXPw0+IeqabZQkbLO9uQ8UigDgpMGGO3augbw1o+kW0kvha2itVdmMZhjVCcnIBI56ZqndwJNHt04K7uo3I7feY9uTivOxcKNVKNSmn8jqpVqsHeMj9oPgd/wc4/tZfA+5t/Dv7Wng6w8T6TCiwm70wGKQnjBYtvjJA7YBNfv5+yj/wW1/4J5/tf3MFvpPiFfBPia62gafquIkZ26/vD+75PYEZ9K/gI+Jr6fceEJbTVgWRJB5cfQhxwGBHX3r5R1HSFhkEq5iVGG6WMEEFh8qnn5seo6V8Bn/hVlOKXNCnyt9UfR4PiavBWkz/Xm8R2WvWgtfBOgFLlNYk8wSRsHEwkPyGF1ONo4z7V+o3w78F2ngXwnZaBbL/x7oNzHq0h+8T6nPf3r+AP/g2R/wCCuMmifFiD9iz9q7WHvra4VV8L6lqEgkNpIAT5AdmyquCAoGQG44Ff6G8SLxg7gRn1/wDrdKx4J8PqWWTnK1+zOPPs8qYqKiiR0R4yjgENnIPeuK1nw7aPaTfZ8x7oXjKAA8MprveANtU57fcCynGeK/RsdFSpNLs/xR4mFqWcb9D8XNRt9dRdTt41igs7GYAsceY/UkZ64B7dKgtbmyj8m2tYWkiUkPGx+cZb+ADHK9RzXoPi/wAN27+PdXF8wsTbXTyxzyIxDNuPyA46MOlY7Jp94I7jSoJfsdupFxHcnATPysY92Ouc5xz25r/Mnj3DunjKlN9G/wAz+m+H8SpYZMoNp2oaUq29tdzQ3F5HJcRFcD7Oo24VicncQSAM1ztlbwpDB4g1PMcLytuZARM7K3zDa3GB3JHc4r1FLHwzJYLo0s0ryIouRPCuTKQCVQEfxL1571xzDVb/AFiCy19LtvPC77YLulKLzukJ6cdfavzxRdz6B1l0Osn1SyjsXewgSOO5jGM/wRjq/wDvV4J+0t+z14G/al+DsXwj+I90NJ0kzJcQ3NsCbp/LyQcEFCCDg5H616xdXdncka3dyW8Nu7mA26Luj9goHp37Zra090ih36pbLEin/R7gkMzKv3kwMkZ6DjtX02SZ3PBVFVpOzXU8nFYWNaPLNaH5Jab/AMEQP2B5Io9c8S3+tajbuRCkS7AAVHIOVz9c17x4c/4JXf8ABNDwIItWi8ANfRxqYYhdBSJdxBMmMAll/vV+kwuNWuJGVUMcM8QRY9+Nz8Zx/dz0HpXm+o2dubmbSdMe4h+yMkaRKpYB5OXKFuuOjHpzX2cvFHM5/wASq2ePDhXCr7J5Po/7PH7L/wAJdOW/8B/C/R7YmWJIJJ1JkZSwBdcE8AckYzXs13oj2EP2zQ7fTrezhjZ5XtoCGxjIADDnP6fjXV6UllPOjwxxObfMNqrL5kzNjBc54wCTyOlc/r2oT6ePs1nM01vGpN9KoPIH8OM/w4P514+M46xlZ+/Ub+Z1UsooQlZRM/S/E/jc69b20zn7HGwaCJIIw8ykAZ3cYHHPNdLpLpYarLrfih1v2VPLmnlGCHPAREB2hs8jHGMk15VHqa+J7NLbw885hmnCwu7eXHHEMFy+edvGOPSug8QXsdqlvpuk7orWKUuZFQmNlxz5fvnge1fL4nO605O7v6npLDRjpFWOl8a3llp9tJLd3X9oavJ/x7p8w8mM9C4BwDjj9cUv9mafplhY3Wm25xHiW8MxzvfB2gck7s9MVwMthH9kFrLA6RyTZ3QH5pVBAwzn7vXtXUX+g/YtOW406HKmX5ILc75kwQcuTxXJLESk9TeMUibStRgnij1G8nexmildrRTlppGk/hYdgtegy2Xh5EfRry4xcOym4wpLEYzhCOmPU15/o8zi7fU4Ix9unBjjkIZ2jUDBkYkbAx6ZHNaI0240SKf+3pftXnoANzLlyORuP610YWoo1E5CqUnKLdzxn9urwtp/jf8AYd+InhLT12aW+kTrEVbLswRnOR13HHfpX+UT4eBj024sm4a3vZlH4kYr/Wl+I1lceIPhB4r0bXxERf6Pdi3SAhwcREHcPxr/ACc9UsX0rxv4l0Ygj7JqEgxz1LN/hX9zfR+ruWGnT87n4xx5hbTUyT7owKZ2/pQhJzR3yetf0Ve+p+YLa4ZwDgYpVOTn2pGOHC+tPUAMaAaTQ9/vVFPH5tpMhON0Ui/Ubc/zpwQt82TSleNp7hh+YxSjc1g46H923/Bqlr//AAl/7B/izwPLJt+w6pJDnIBXfErcE9Opr+jceEdcnlfyWFu1ooKyAh2mG4g8gcAjt1zX8mX/AAaMeMbWP4efFDwHqhLrHqSTBRknmLacAfSv7CrHVp59XKWULETw7nmbKrGgI+9/tHHFfwH44YFRzKrfuftXCOJfsLHG6Uk+iM2n3X2eA6hJ+66so2jowz1xWTPAmnaG19bRoSxKTNLyLg5OBxztHUD1rr5dJ07U7lrZfMeO8uWmkPQKqqM84OAccY6j61z0MsE0Fzq0WnyKgJt1gxw4zwY1PAx1r+eq8YqJ9zTqaljwvaNHoDWmvBllYCVGUHIBP3cknr3r8p/+C/8A4WsPEn/BI34hPp1qESziinBJDbWSePkd8H86/Wnwnp/2e2leUwRIAQrN8xBb+Egc59a+Q/8AgqX4KsviJ/wTM+Lvw9hs5IxHpNzIFwf3hjxNvAzwp29OlfrvhLXUMfSl5o+Q4tnzUpRR/lEeGnaXQ7bzD8wUKPwBrcCkpkjJHSsnwtE8WlGEDhJXTnnoT/hW48Y5BJ9xX+kid1c/B5KzsV2PmH97yOhx0FP+YgA9uPqPWmugiTcvTpilJfjjnHAHGB3piIiqg7Q2AOAfYVDLkNzwSAMCpXZMgpztHC/3h60w53/uxvHr0/OgBRuRgOxqyV2nA6rg/lVbaPvbi3zYyP4an3KpL53Y4z65oAXABD5+Uc4+tIFUAY5pUU/cfnHFKuQPlFAEMgCzIwGAetRsuGPp1FSSyc89qi+9360AKOmzsf0oX5PlBz70nzICF54psRDRkYwRQBAQTkNS0qnJOaiBOM+lAEgG3pUtz/qSOxU/ypkfLLn0qS4/1b/Q/wAq2nFcjKhuj+pr/ghIf+LIzN38+T/0Kv0Y8Mj/AI2lfC8e0/8A6C1fnN/wQk/5IhN/13k/9Cr9GPDH/KUz4X/Sf/0Fq/y78Sv+SixPrL8j+9uEv+RPH/D+h/Rx8Sf+RN1//sH3P/os1/MKP+SC/Bn/ALGy5/8AQq/p2+Ipz4O8Q/8AXhc/+izX8xJ/5IN8Gv8AsbLn/wBCr8dpfxonVw//AAn6fof1ZaaSdO0kn+5F/MV8L+K/+Ro1L/r6m/8AQzX3dpwH9naT/uxfzFfCPi0geKtTH/T3N/6Ga/r7wh/g1f8At39T8H44/iQ+f5n/0P675wRp94P+mUn8q/lG+In/ACb58VB/1Ntn/Nq/q8uhnT7w+sbj9DX8ofxDOf2ffiq3/U22f9a/yY45f+2Q+Z/dvAXxVT969cGf+CausEd/AU3/AKRGv5bv2BwT8CLDH/Pef/0Kv6k9Z/5Rpat7eApB/wCSNfy3/sC/8kJsP+vif/0OutO+XJf34/qa8G/7zifVn5G/8FcSP+Fj6Tv+4CNw/EYr8C/GGlPoviW805zkpITn68/1r9+/+CtUQk+JukgnGXA/WvwE8XXtxqXiO8vLk7nMjAn/AHTiv9CvBNL+w6T9Ufy94u/8jaX9dDmqKXA9f8/lSV+pt3dz8uCiiikAUUUUAFFFFACgkcineY3+f/1UyigC/bzlRirDztjNZSsVPFStNkcUALX0H+yhrk3hr9pbwLr1vkPa63ZyDBweJVzzXzz5i/5//VXY+A9Sk0XxnperRnBt7qNgR6qwNcuNhzUZx8mdGCm+dM/2PtZtbnWtI0nxZbDEl9ZQyGP7wlxx8o7cHn1rlLjww2gJOdUUQm1/eFFOQQei0z4I3el+M/2ZPhb4m1Zpr2+u/Dli1v5BYEGSIFmJ46cda9t8ReFrzW4bUa5FDbS2/BywzMo5AOM1/mvxxgFDE1I26s/onh/EXpRR4ZYzWKac8SW+LtpFuknY/cGPlQD0NaOoarb6jtvtRxPfTovmrHjy8g4GB2wKZL4bbVNVjt4JY4S0hG6UlVjCjIXAP86fJo8Eky6rosLCNFxO2DgtnBbHYE818F9XZ9C4xbvcls4fstvc3MhUdI1HbA6ZHaqupeIfDvhjw+s/iLU7LSIZWCI99KEQupyxUkj/AAo09pbfz7m4O+JzgKp+bPtX8f3/AAdD6V4t0T43/DnWIdZvNN0vVraWA20MkgjTySP3gVTglg3OR1r9Z8OOC6Wa4pYecrHz+e5s8LRc0f16+BfHfwv8eXt3qnw18ZaVrC2TiK/+zyCRYWbOFcqxwRgnnFavif4v/AzwLoks3jn4gaHo91By81zchW69ACwOMdq/yRPEPxI+JPw8B07wZ4o1XTheKTcCC6liEyg/KWKMu7v1rxzWfHPjbXpC+vateX7tyWuJ5JWz6kuxPtX9I4f6P1BR9+qj8unxzOT0R/rKeIP+Ck//AATf8Ht/anif4waTP8mx4ra6hcAjqwwSefpXyz4j/wCDh7/gkn8IkaG38S6prb2zvJAILfzVLkc/NleD0Ff5dLXEzMS7E56kk5qu43n1r38B4F5ZT1nK/wBxzV+LK01aCZ/oyePf+Dsz9gzwxZTyfDPwXqesTS5LJcRLAHJ67iS34YFfF3jf/g8aju7M2fg74K2kTRMTA8t+crjgHCxV/DWYSBnNCjZk9a+owvhflVP/AJd3PEq51iJa3P6p/iB/wdq/t9a/Ncf8IFp+laBHK2UBjNyUHplyM/kK+NvG/wDwcff8FWfG9y86+PIbDzM5FrZQxnnHcgmvwfMa5zUkalee9ezQ4Ty2jrCijinmFV/Ez0Tx18SfF3xQ+Jl98VPiBdm/1rWb1r29uGABkldtzMQMAZOelf64H/BO/wCJk3xH/YM+EGo2d3kHw3DFcbhnBiRUynbKspB9jX+P6y8Biec5r/VH/wCCF2pp8TP+CUHw0v7xirabLc2qspIbCyEdsdR+tfmXjbh3/ZsZxW2h9HwnUTxdmfrJckahHbXjtKbu3DIADnco78EA/Q1jNf6rodi2sXsKXtuxPkwoSGLDkGQDgc9q0LqKO0WKC5Jkh37OOq9xyDkD+tWY/tt9efY1T7IsS/u3ONjKuTz7mv4cxNP95K5+0xa5bopz32vanZR6FawIkty/2jeCV2gruKj0/me3ekgMVhAsqu010V6Pz5ZXg5bv+VWb3QpLmyh1DT7gLJI6gJuO7I+9+FdVdeGnWI/KFgGPMb3PJxxnFdWXx5a0Tiru8Wz+dD/g580nUviP/wAE4INYuF8z/hHL+GaRkxgc+Xu/DcM1/BTGkWoabZg8F7eFyF4yQvT9K/0i/wDgux4QtPEH/BJP4mvaKGksYEYEDIwJ4ySPwFf5sejm6PhPR79XBD28gy3QeUzLj9K/vbwjxMp5Step+OcQUYxrXSP7Bv8Ag1D+E9jqcXxZ/aS1a2ysM8FlZui5fyk+eQKT/eAXNf13alAw0WFlmEguN7OkZ+YAnofrn8K/n9/4Ne/BM+k/8E05teQGBtZ1K9DzKRg7CiA/lX9EVlpNhDJLpUCZyobzcdQOpH581/P3jFjZPGyUuh9dw7BOlc3tNe3trQ24tViSA70jjUZk+XGGPfnmtey0jUL9Y7m5ldCiMDGM4DMOD6dOKsW+gXNwY/7MTLbceZn7uO5JrF1TWobWZ4raWSe4Ee1YlyVZs/M27/ZH0r8QnTVuY9+U1eyKM1t4kS0RL0KbfcFQBVypU7hj6cge/c180/tv/GHR/wBlv9ljxr+0XdMLfVtB06ePT5JSN0k7Dao2g4yWx9RX0nDPd2ytqtzOHnmTyoYQo2ptPY+uenvX80H/AAdL/GTUvhv+w54W+HAuGW713W4JJlJwzxqkhZT6jdjNfoXh9kf1nHUk1fVHkZ5XcKDZ/IZqWm6D8b47/wAXfFC2F/qOsXUl9JeMP3ztOxOGbrjdu+gr5o+I/wCx75a/avh/dKZCSzW0zbRjGfkfp9BXtPgbxfZxaWNLkYn5UwVONvA4r1+w1a2u/kkbIfGCcdB9a/v6hSdOChfY/HpScne5+LPiDw/rXhXUH0rXrSS1uU+8sgIP1Geo+nFfRfwB+NkHgy+XSfF0ri1YBYpcb/LwMAFeuOwr9E/if4E8MfFjwa/hnXrOJbuH57LUmADRtnmNiOSpHrxX9Uv/AATS/wCCHv8AwTJ8WfsZ+Cvi38XfCj+Jtf1OKT7ZP584ieVXYY2o6r8p4yfSvI4j4lo5ZS9pXO3A4CdeXLE/mT8DeLdC1zQP+JVLJcXO/dDdRRyOox1jPy8HBrrrjwBfeIF2aHol9JNNhyka7t7/AMXykZANf3d+Df2Av+Cfvw6tba18A/CzToY7VlMXm5kOTzkiQsDgevNfTFt4e+G/hlvI0nwxpdrLCcKkdtE21ccHhePpX4/jPHLDw/hQPqqfCVWR/ncxfsx/tH3mpSXXw58C6tqc07qRHNbuYo2A7bQP19K9P0v/AIJbf8FJviHatHYeA5NPWU7g0tqVw3UfOx4HPpX+gEmo3UiRWsEUFvcycDyUVdoPfAxitZ7/AMQW7PZXF3JMIlBLKTtKjPocZr57FePFWSajFI9LD8Exl/EZ/BzY/wDBvj/wUx+IUXmeML7SdNglURsWlj8xV4yNijn617d4R/4NN/jL4pJn8a/FKO2VMGRYLfzsE/3f3gBx9K/s7me5ljW5BYxyk7SRnJ+lRPqurGzXR9Mma2KHeZQSNwz04xXy2J8bcek1Tme3T4OoR6H8unws/wCDUr4afDvxLp3je8+MGpm90+fzVe2sEjIdGGMZkPIIr+q/wr8Wvif4X8I6d4Cg1Nrw6PbR2zXssYWabyxgO45AYgc4ri55rmzhee0LsZcbixyu4gEtzz1rVsdG1GJYTcKokl5DYPOe9fMYrxbzKtNKVVm64YoJc1j2f4YfEP4iX/j7T4Nf1R5rWZyGjwvccA8dq+9opDMgLDAbOK/NbwNOdI8U2KGNvNjuFMjN3ycDH4V+ktsDsGDnHSv6J8J87qY2hUVWVz4HivBwozi4Kx+evxn0GKPx/P8AZZmkmR/P8gD5Wzzg5yM46V5Dc2F5rGpvNp/mXCvkGA/KiR9WI/vFfevoD49nUE+IZ/s2RYHKxurEZ6Akqf8AexivD01nxBcXsF3ZgQ/2gx8oAYBK9R7A9/av5F8W8KqWZVY/3rH63wvim8HBENnpWrRtdGAxlJ28m0hR/niyPmkbjOe/4VLpnhvX2iZNFuQk0Y2z3Vw5V5/7232xxWtfGbT7OCys8DUdQyt5LDhyg2tgAgZA46iut8D6RdLp9ppN9vkAPnyPIBu5zhVU5OPpX5C07pJHvVcZZXZw1noWhQa1a31tGkVlbsw2Ph+do3MR65PBrQ1TQdH8P2C2ypL+8m+0NLMwCRqCSQhxx16V7pa+H9N1K0mjtoM27kySknOT/CvzcjnntzXK+JfBGpRW63Nwk+phBttbOMgLGh/vsfvEetdyyis48/Q82WcJPRnn0lxpcto4ddsVzsaKQOCwYDPIHTPpXOpq8E7y6j4lCefp0m+KGEHfJER95h616xD4euHs5WNg8bSAHExyFIA3Yzx64xWbF4KfQ7yB4LRXO7aJQAZWDcuWz/CB71yvDyi7WO6GYKUdzl9T07VdT8OtrSLHYzuR9nkhO3bA2D+eOo6nkVwSmxFuNJ0FFjtFfN1dSE/eb+6D1zyeT0yOvNe3appMem2EssreRBvJihY7vmP8ffjHauOtfDZvrp3mjaWKRMg8CNm7fJ7ZrkrcylsbYeqrXOQWz0kR+dp8bx3MRk+zxBMLMCcYYA4IY8r6Kcdqi1LRPFIs/sevzxeTJGWS0hXAEgHIBHICg5xXWz6Q1lCs5uJC1o+yRVAGJD/q0THPBOfxrF1rUNZt76O01G5jjtohvmZRukL5+YZxxUKDOmFeLepnf8I/pOn2dtJf3DSo0WyCA5Du45GQTxz+dZUzWUUE1hHM0T2ZV72Zeh5+4p9+nHepdWvGvJR4j1RPs0BIjiiUfvTgHDA+vesYpc2f2J9XvBagESLbAiQuQCQHU8cnqSfwrdGxvWmq6nrbz3kUy6bayJ5UUZHzLEgz07sx55rnNT1bQ5LaDT9OE9xezfKQQR06n8q25b6PVpP7Vt4xbyXBIYz8pHIBhpB0yDwMAcVnW19p8czWEEkYuwB5mo5wm7uqe5qk22ka05291EC27xWupyalItpDJYzW62Aw0jsygBj3Wv8ALZ/ak0JfCn7XfxR8KQxmL7LrcoCEYICucDH0Ir/Uy0cvd+L0jnVZQ0Wbp3x+8jJxwSPpiv4hv+CyH/BKbxZ4X/ba1vx38GdRF4PGscutSw3AKeS7feiDLx/umv7P+jvjowrThJ7o/KvEajaF49D+eBiMEU7cCpA710HivwF49+H97/Z/jrSrixkIJVpEO1gOMgjI57VysEizEmH5gOpHT8+h/DOK/rCUUlZH4xsrFkpvx7AUhiA+9UiMop0g71IhqtsG0DinKhZh7mogcinqATitFUsCP6aP+DUHx7L4e/aa8feE0J2XNm0yx+6yYyfUjP41/cxJq+r3UCW+l5aK0aRryQjZk8gjGDnGfu9q/wA+b/g2Z8Yw+B/+ClV/ot421NR0102kZ3bip4B71/oA61PdN4gvtZ0q3miis5XWUMAFOcDcyjgrz/jX8PfSEwjp5jOolpp+J+zcGtOkixp2oSmS6kikN1bIhe03NtLSuABERjnGCfXmmaRc3um3st3cK0klxkyu4wkJJwCg6YxUHhnTp9ZjSDWJIVZbl7lYV4ZVUYUrjvnqfSqF1Ne39lF/ZETTQqz2nlbiRMGOSAT3B71/KWKbbsj9DjCza7HoWiGw0+4a+0zCozDzGYEiX1wDxn3rD/aN0nWPiD+zv450PT14utCvog8i7fm+zSAAKeuSAc1XXUobS6juHjlFtpoGIeR5TL/ePfNdNY643iPS9YtNWvHMl5YTobVkIRonjba6Z6HawJHUd6/TPDebjiop9Gj5TPlzJn+OfbQf2ZfahpOCDBdyjB9mP6Ve3McHFd58YvDbeDPj34z8Hldv9n6pcIR6fvGGK4lwok+Wv9NcDU58PTl5H4lmFFRmyE7iDkd6rFc7iRyDgH0Bq1IQvzGoJQznA6HrXXNWV0edHVleVNrjZwAOPoKi+ULzyp6nofypZC4ccZwCKQgFiG6D+fpUjYjMy8txjoB/WrcWACvXHeqafLkDke9XQJCoCgAHr60CHnDLkdaRSQuW4pvmYO1v0oLAnnpQAgRJHJYZqvPHxhAFFWyO68VUncg4NACA4XLDk8UmNnz/AOcVKRlBUfTKtQAn7g/vAOvamSBWHy8GpolRgcdqjaQqM4zQApVVGTimzkeVI3bYf5UKd67WHIptyxNtIO2xv5V0xV4tFR3P6mf+CExI+B82OplkH4lq/R/w1GR/wVK+GB/vJMf/AB1q/OD/AIIScfBKQ+lw5/Wv0n8NAn/gqX8Lh/0zl/k1f5aeKMnHiPEW7y/I/vbhPTJl5R/Q/on+ISl/BniIrziwuc/9+zX8xDMo+AvwZJ7+LLn/ANDr+nvxv/yJXiX/AK8bn/0W1fy+y8/AL4Lj08W3P/odfkNH+LFnVkWkJLsl+R/V1p7N/ZukqevlxfzFfB3jFGbxdqrAcG8n/wDRjV942QP2LSP+ucX/AKEtfC/iv/kaNS/6+pv/AEM1/X3hD/Bq/wDbv6n4JxrK9SHz/M//0f687n/kHXf/AFzf+Rr+UL4hf8m8/FX/ALG2z/rX9Xl0cafeD0jc/oa/lE+IfH7PnxVX/qbbP+tf5L8c/wC9w+Z/dvAXxVfkfvZrX/KNLV/+xDk/9ITX8tn7ArY+BNgcf8t7g/8Aj9f1I65/yjQ1cnv4CkP/AJI1/Lh+wMP+LCab7zXH/oddsV/wmp/34/qacHP/AGrE+rPyN/4K6TeV8RtNZThlbj8xX4S+PtI/s3XZ5VI2vITge9fup/wV5iWT4iaXkZJk/qtfhZ8Qr5bjxFPBjlZDmv8AQbwT/wCRDRfmz+X/ABc/5G0v66HBlUJyBxmmVJKdr7R05/Wo6/VT8uCiiigAooooAKKKKACiiigAooooAeqhmxnj1rqtLVEsReuMbJUYH6muXtlYnYBzXeeWx0o6fAhJGDkdflIqZxumjSD5ZKx/rn/8Ey/Et942/wCCZvwq8RWjI1/DodtAjSnjaikEcdOmO9fRN3Ya3bWttJch5UmZiVzl89Sq5wfYV+af/BCTxzb+Lv8AglL4Fur+N559NkltAEGRuidtoPGAPm5NfplHc3Gjaw+ozDzCzbY1wCI3x14zkjoMACv89fErBNY6Xqz914ZqfuVZjNR8E2sSy6rPNsnm27ghz5QH97ggk1yk9vfQ3DW1jIRCh255O9MYyTnHPWu7h1xLi+tbfw/stlRj9s8z5hI57bTzUGqols4tS+15C2dw2lSxztx6DpX5s8PZXZ9VCTtqedWtrPa6iUiYoJCNoOAOvUHHSv5f/wDg7D0GOLwV8IPHVxGYjby3cUrgA4Yoh9ef0zX9XaretH/Y16i20EbFzvH7wjHVeOn0NfmH/wAFlv2UNR/a/wD2CvEnwy8FaJL4j8RW8lvcaMsMPnXCy+YM7COQSrEHtX654T5nDDZjCdR2W1z5jiijKpRcUf5bvjzWYNd8RSXVsP3EfyRhemB36nr1rjydxznFf0HeAP8Ag2a/4Kj+P2GzwvbaRxuK391HAVzz8ysxYfiK+yvAH/Bon+2lqrI3xL8UaHpAx8whn89l/AAfzr+058Y5VTVvbJn4vDKsQnblP5JxGDyWAFJtUHhv8/hX9xPgv/g0J8KWl9F/wsT4yxjBy0NtaAt+rn+VfcXgL/g1I/4J+6M0UnjLxNrWvoWVSLX9ySR14CNgH8PrXj4rxMymlvK53RyLEPof5zBHbrQkUk+FiQknpgZNf6oHw9/4N4/+CQHw+vLS1tfB19q93KplAvb2SRWCZyGB2jOexAr7h8Ef8E4f+Cbnw9tYbnwn8HtDmkkYoi3FlFKw2nrmQHAGDk5+leFLxky1StFNnR/q7V3P8fa48IeKrfSv7buNPuY7T/nsY2Ef/fWMVhIrrlGPIr/VP/4Lr/s7/BEf8Ek/idceAvBOl+HptHigltzZW0UXCzJlgYwDgjIr/KwDgSMM96+54ez2nmNL21NaHhY+h7P3XuDHMe7uK/06P+DaTxCPEP8AwScsLK0dnl0vWLhGEZywy6nkH27Cv8xplHl5r/RW/wCDTzX11r/gnx458Ns+46dr4k2h9hCtFuOG9sV8d4vYbnyiVu6PS4WqtYlM/p0h0fVLyR5NEiVkyOVxnnnnORxWBqnh2eO4kt4SyoeZSxIII6+uBWvLrL6dp51KzgmiVlVzOT+7JxgAbcDP0qaP7YNNh1W4mLSXA5UcjB9+5r+F8xwyjUaaP2nD1pN8t9DnobmIeS1r8ojzs/HAJrTvWtnujDPcFrZVBZgOMjt1wc/WsXUIJ7UkSv8APcLlRgDg/TvV7TdNt7nTUtL5WsEUYSKXrIyn72D61zYKC9pfsdGJVo6HzR/wUR8C2/xR/wCCeHxM8EpZvDDLpcuC2CJQo3AgA56iv8r3TtKll+H0dvCmXh+3woq9SRIWA+vOK/1z/izosXjX4DeMfDYBja40q4Q5G0/6ptpAGOOlf5QvhbwrLbya1ot/u3afq1ztQgDKMDnae+SM1/afgbjIywk6XY/JeJYr2yP78v8Ag2zttHtf+CVfhKy1e6EUTXl+7x98eaoHTk5xnGK/duaGGVjLZSeQrfLEccheOSOK/nJ/4NcfEc3iT/gncvhXJM2ialdiVXUnHmhWUD6V/RJPBHbXUyhWkmlOFJJ6ZOBj86/DfFvXHVL9z6Xh3SnY27jUgNmjtKdrNmSYcDaB0GDxmm6Xp2m3ELPOViVmDq5A+bBxgn6VylrfR6HIZbhS21SACR8x+hrptPiebRpb1Iy+SGjibjjGDjOOPwr8bw8HI950E3e9ia/1eyUwx6K0YtgSpQrghg331yK/jb/4PD/Lb4a/Cu6VzMftU48wH5SSBjjHsTnNf1t+IGiMrXEyGCXvFESCNp3AEDsT0PT1Ffzjf8HT/wAFX8Zf8E3dA+Jdpbl7rwzrkIkKjJSCRXQk9Tjdt/Ov3TwjxsIZnTT7nznElJ/VZXZ/BR4W8VSWksbs21xjIJyCMDB6V75o3jQvIrTS8DkY6V8OWOsM0ccg6sig/wDAfl/pXfaV4kztjZypUV/a1T4mflCVkfoI/jBbzQ3gZj5IRiZQORxnaeelf3m/8EMPEVn4+/4JheFSJSZbC7voQmflb9+2ARnOCDxX+cJpXi+W3sZbdZflkRgVHfK1/eF/wa8+Orfxl+wv4o8J+YJJdG1HcqNgYEuGG09uRX5Z4rYXmy5zW59Jw9U/fqJ/QHDpun2ziC/R1vcZRF5RWz95s4zmqtxpwkC3DyeY+SrkDLeuOMcZrrLmxOvQJaXrZZhs/dEbiAfX1pYIo7FXtdMz9otMJl+F+vTk1/DGNqVOeyR+w0KjjojkrXTrdW/coBPccSs/RQP1zipLiGztidN0pzcjgArnn1H0rtZNCgImvZ91vtYNOW7MegB46+1cZKuoW199otGRFlf92oxmvN+r1JS5mbyqroc1Kl3OpjuFZFjB2AcBDuOc1ajsN4SPY28EGMjnfk7QO3U/pXqtj4fuYLM38Vv9ot5wTMG5bIPO0fWu3s9It7G2RreASvuTYCOYhggNyOAB+tarDu6vsNY7lR4ha6VAk/k6xGzu7nFuowdobGW9PYV6o7NLHHBZ2ISWJcRBuAi9yTg11Gl6ZpZgk1OSZXaYghhjhzz165HPBNc7q+sqFl1J/wBzACI2OcNJn+EfXBpKnHn0Ryzxjq9LHLQ2Xk6jHqsThooZk3SdnORnb/Sv0CsWDwrIvOQMH8K/PHXNS0g27Lo6uJk/1SL9yFhyAc5yTX098H/i/wCGfG3w0s/FKz7WUGGYEEESx8OuOvUV/WngPVjFVE9z864zpN8rPHP2k7YWfi2znP7tLpVSZxwTGCdwz6gHivKrzxJocnl2tgkkhiYR28G397knG9gOgB/izzXvP7RehXHi6y0i70l1wSzhnO0H5eP/AK9eJ2emX/h/9/cmOaRmAuHHBVMZxkDt2r8g8bspSzGb76/M+u4RxK+rRTLNrokxmdleOOKRAseWJLP33AEEY9Oa7+1voLNUs1LTXEMYXz2AXcvTaMnt+NU7Dw3a6jdW11Y3BFrABIXAyDnOeRxniuwu9I0vUZrdr3CQNho3AwM/XvX4lhMsrRTkkezi8dG+px1trVzfSSW8qG0srdgLcZ2tO4wG3dtozXXr4gkt53+0IZjbIFKQ9i3Yk/XrVLW7aW7eS2vIBFp/QseHHzDlfrWVfWSWMNvqGuS58gBEZDgup4jDdsk8dO1ehgq80+WWrPLnKEkb1vqDXN0+miOYKAJGMg+VO+zJ71xN/d6ppku90kuMhgHGSFeU9M4/u132j+AvF+uaS7RSLbw3ZJJwEkjXPC9DkY79feu0034T6gZGTUbt5LfZtVck84wD0FfpGX+FmYYymq0YaM4J55h6T5XI+YZvB96kYXUZz5iZMAkfO1D/AKxm7YA6YzXW2s4v4v7K0YNlF2i7jA9MnC8nk17c/wAGLRUMepzvdIB8qso6Z9e2e+K8h+I3w1ufF/gHWfht4WvpvC+r3sbjSdVtJGUxTAHYNw+bg9QMZH0r6bB+AeOqTs1ZGFTjGlTVlqZVzo+tT6lB/orRy2y5YyYUSbRnccA9O2f0rxvUfDV2LuUSTpFA07SzojBpWd+gZecD36V/F3/wUa+KX/BV34BavqXwF+MnjXVLHV9KlebSrm2keNtRsnGJBHcxlS5HDhSd3Udq5f8A4IuftX/G9f8AgoX4aPxC8Z6j4pt/F9k9lMl7PLKVLRM7KwkYnKlOvX3r1cx+jvVw+GniJVNkPL+N41JqNt2f26WuiajbzGfWFBuCpS0MeCsA7Zzjnbnmq3h7RxNq0y6lan5VcXN3LnJ3KcEL0Azg5zxW/wCMNU0PwsU1Nbh9Snfc9rEgBC7zgM/JztJA6CuGvdai1KL7VqV9ctqKZMsEY2rIJMDysjA4GduRyM1/L2Z4H2NRxP1HDV3UXN0DUbbRbz/QrNPsxs3McGWJ8xHxl3JyAucY70+58D2mmRPpN1BLcwzAJG4UMqysM71IxnngD27VlW2taiPK1Wxt1vIAxWWCMBi+OmQOhjrpNQ12W10uKEsZZ4P3hWNiUkUksQx5wVyOO1eQp2kehy9UYU/hWwlsIdJ1Wcx3cZGJLcMfNjDdd3QYPUc1+Rv/AAVc1GLwx8a/CemaoIZrXWLOO3Z24djuJwrDocY4r9ldBs9Q1u3aPVr1dLuLwFgYR5iepQNnrwD1Br8Af+Di3Q77w74e+GnjXR7grfDVfJgzkbnXBGD7t8pFf0x9H/HN5lCMnoz8+45hzUXc/Pbxz8MPh74nsPsOq28esaHqhLRyzAYtXAw0bvyRz0FfmF8df+CYFtq0B8V/s+altkO9zp8+djEc4hkPXPTBFfo18CvjTpHxD8OXOgaxDDFb3W5ZrXIBR8/MCOocN09q7PxzrOpxaXHbaPKhs9Oj3PERtWCOMfKy/wDTQjjBJr+7po/BpRaep/LB4++G3xH+E99/ZvxK0ebTphgGRlPlE+gfGD/npXCwXMd2nnW58xfbn2r+oqDXfhh8bPCs+jeJbePUtBKlJYrqMNLHO/QdiBnv2r4M+L//AATE0i+tX1f4BXL2F7GjSPpt42Fk7/Izc89AMntWZJ+ODZHUYpp5Tctbfjbwd47+G+sTeH/iHpk2l3MZOPNjZQRnsTgHjvWGjxtCjRHcG5oA/Ur/AIIheM28If8ABVLwPFJwNVIt85wfnT174xX+l94k0jxXZ6w90iwNaSSrLMqMS7oRgBl6DnGeTxzX+Ud+w3rFx4e/b5+EWv29z9jJ1m2QzDjaBKOvT6Gv9WrxP4lTzIYp5vs0F1p8LM/d+CcZwepxX8o/SMwSTU+6/I/UeBsW5L2aRwt1bw3tzNaySvFqSqZUmjBEAgGPlLDkAZIGByQefSeTT7iytRY6TK4kDmdYQDsSMdZXbO4bsZHHAqOy1u/06BfDdjpy3EMG1ctlml3ANtQnBPI5GcDsK7jw0p1HVru0glDvIXe5X5d0z8/uFIAyAOOK/imnG7TZ+r4mXJHmZ0Oh2k2r2M0Ila7kADKI1zCjsOrMT81cnJYzT3g0W6k/tbVbZ2Z0RNhi3Zwdy9lB2n14ru7a01K709ILX/QreB8G2U7CPc55O2vRtGthY3ymNkitQqq07IFZ3Y9CxwTlsV+n8KYdLExjD1+4+TzOq1Fyep/khf8ABRTwzd+E/wDgob8XfDs8P2cjXrl/Lx0BckY6etfIaZAw3PvX7Cf8F8fBy+Df+CsPj+WFRs1SX7WMdMSopyPxFfj67qGKnOa/0d4bxcKmCpzj2PxvMZc1V3GyLuWoSxz0qwCGFRn5TjFe1O1tDx0UHDsflqNxkjbya0jHk8cfSo1VkAdAGFSBUHDDIqxl88cZ6j0pHydxYZ29centSBk6k4Qjhv8AEUAKFRXwenr608xnPPFClcA9QBx7+9NWXKZI5zigB6nt6VVlVWfr0qxlcketOKAkEdRQBTfJHpTUBBBPOKuFsnB6Uuwd6AKLhwcoOtKI3Bx2q5uK/KKTLHnigCmQ+7JOPamXCt5Ey4/gPP4VoFAFPenXKr9klP8AsH+VdFF3iVHc/qI/4ITKV+CMn/Xd/wBTX6TeF23/APBU34W/7ko/8davzi/4IVnHwNmI7Tsf1r9FfCLZ/wCCp/wux6TD8lav8tPFT/ko8R6y/I/vXhb/AJEv/bp/Rl47OzwZ4lH/AE43X/otq/l9PzfAP4Mf9jbc/wDodf1AeP8AjwZ4mP8A043X/otq/mATn4CfBcf9TZdfo1fkdH+JE68k+Cb8l+R/V5Y82Wkn0SP+a18K+K/+Ro1L/r6m/wDQzX3Vp4zp+lN/sx/zWvhHxY5HinUx/wBPc3/oZ9q/rzwg/g1f+3f1PwPjT+JD5/of/9L+vC4P+g3g/wCmT/yNfyj/ABD/AOTfPikfXxZafzf/AAr+re4B+xXn/XJ/5Gv5TPiIM/s8/FL/ALGy0/8AZq/yX44/3uHzP7s4E+KofvHr/wDyjN1n28BSf+kNfy5fsDMf+FB6WP8Aptcf+h1/Ud4h/wCUZ2tf9iHJ/wCkNfy3/sDj/iwemf8AXW4/9DruX/IsX+OP6mvB3+9Yn1Z+Sn/BWvB+J2jK3C+aST9MV+APiuc3fiO9uW5zM+Pzr9+/+Cu7eV8RtNmP8Akf/vla/nynl8+d5T/ExP5mv9BPBL/kQ0v66n8v+Lr/AOFaX9dCkTuO6irHTrSEriv1d7n5cQUU87McUykAUUUUAFFFFABRRRQAUUUd8UAamkKslzuIyBXp1pewW2nzkrlmjYDHuK8/0xPJUuetb2Q8flZxuBzimlfQadnc/wBIT/g17+IF/r3/AATFvdBhYPJo+r3hKDrsfacZ/Cv3YS5/s+/NwpE73K4eJhhogP4ga/l2/wCDRfxlc61+zR8UPATj9xptzFOpHUmVTn/0Gv6rEtPNcWV+Y45bwArI4z8pH3eK/iDxawnLjqiXc/YeFcTzUTA017lVub/7MgjzvSYDO5h0zjkYqrMk2p/6XLIssjrlnHXIrvZtN+zXrRRAJaeVtXb91mAx+priYIfKkikhARkADAdM9x9DX4jVR9rSrJakq3eoSWyRXTbmQnDs2WAHQVemvbq0eC706VoJmGGKHGPofWnvpcdztuDwGJBqf7J5c6wEArjkGroYidN3iOa9oUbnW9Ult/LmkuXAwNoY8+5wRV6KxS+kWYqLmdgCiEksT7ilCGD97AoA2kEE85rRsGtbae3v9MXZqTD5yTwq9M4r045vWesnoefWwyWxTksZ7q+WxaNLe7TaCAvzBeSfxrqkvDakSHL2jr5XmdJEkH881YNnDdpNaLIGuJMEXeDlGzn8jjFUbSO+uHg065s98kxJMqE7Qy8Akds+tDzGrPqc/se5FKbO8ju5roEEOEBAwxIPUE98VpWMFpfGSyiZpIUjVJn+6FHoPfH61r3htLSdLTWFWGIsqRyZOGc9D0x1qpq9vdQyjSPMjj08LuuHU4YtkcZ681pSxdTmSZjOzjY+Mf8AgqJ4MufG3/BMX4zeE47cEDQJp7buXEX7zJ9wFr/HavY3gvJYX+8jEH8DX+178ZtBtfG37O3jzwXPlo7/AEO9i8snOFe3kx/P9K/xYvGdi9j4t1Kzk6x3Mq/kxr+0vBurfBziflnENBc5zfm/LtNf3z/8Gb3iD7V4L+KPg+f5olaC52kZHcHj8BX8DPAFf2V/8GfPxGudH/aF+JXgYy7Yrrw+LlU/245lUY/77r7DxAw6qZTM83KI8tdWP727u5nnkZtUVhpoX5UMY657r1Ax3rk7yK6gmVtOuY1iPRPbtj6Vaj8Qaq6SQ6pMPLPHH3sZ6f8A1q5zUZLiwnnmuPLCkjyfK6AHufTPev8AP/OXetI/ZcDeyM29il+2Lps0pmlmBPmZ4jAHA57+laNlLCkSWOqlp5lyyNIRxj0I54rbmjTU0kurGDynjVSx5xnHXr3rCu7Pzl86fLO3AIOCD/OvJp6TVj0pNtO50t1JZal4Yv7EkXM91ZTRhkJ+UOh4Yd8V/l5/FbwND4d/aG8d+CZQXTSfELxskY27gWI4J53cdOlf6fXgzYn2i03KFZDkD/loTkDn6Hmv86L9rnwNrSftyfGrw3KUtG1DxKTAOh28uWXHsea/rLwKxF1Upn5hxhh3GSqI/od/4NitY1XSPhb8RvhXpTQ2d5p2qxMsUvJ2TR8EY5OMc+9f0y3FxZm+YQMZJofklbJAJyTwD6k1/FF/wb4fGi28D/tya38LXuz5firSHuuW5M1sMgDkc4VsV/Zxa2radNLBCPtMlvJ95sguRyCSSc8EdK+K8Zcu5cbKS6nocOVbxOyhtRe3iO8Yk8o/KMDr36+nSur1a7t4bOS1kIiVAC7k52FqwNCvCrSz3sO1gQQfT1FPQ2+pShdRjGBlZAx4IPKtX4ZT9xWPqWrs4CCzsnlV9ZJiWZ8xSM3zSbzgZUcqPrXz3+3f+z3oP7Uv7E3jz9nVpEl1PW9KuBpyTfKRPGu+Ip64Kj619RyabNqMTXcAHmWjlhngso52r3x71xlwY7v7M2jDzL3cGCvjhOc7c8qD0z69eK+o4WzaWFxMay6M5Mzw3tabpn+Mb4t8Maz8N/GGqeAfFMDW2o6TdSWs0bgqytExGMEeuaxIZ8y5U9a/rk/4ObP+CVGo/D34jN+3t8CdOM3hjxEUHiCC1Xetjf8AIZ8DkJLjOT3+tfx/wXBwGIHPoMDNf3/kebwx2GhVh1R+Q4rCOnNxZ6Bp2oz7zaknDgAfXJr+3z/g0P8AGl1f/D/4q+D4U8+UXFq6xgE5AVwOe1fwwWt2qyiZT9wZJ9O2K+6f2Kv+Ci37UH/BP6TxBf8A7MGttpMuvqFvDtSRcJuC4DD3rh4ryZ43BSwy3NsHiPYVFUP9cqHw/rbKk9vYyRMRkO5VFUnuQ20/pVHV428PSxXurXNrbooJkDTx/NnvywPFf5Y/in/gs5/wVC+IwkGv/FvV41l5YJMkYwfZFUfpXz1q/wC1T+0344eR/GPxE1a/WTJlD3EhL+www6/SvxrDeBLq6znqfVf63W1P9WDxj8fPgB4Yg+1fFP4gaNojQEoYrm7j/wCAucPzkV4xq37fv7C+kS7rP4qaPd9mNqzy468jYpA/Ov8AKg+Kdz4s1vwpF4gvdZ1C7u4ZfLuhLKzgKcbMZPQcjNezfsjfGaC2gPgnVbSfWtTu7mKKxgVWdpM8BMocqM9QAS2QO1duL8D8Ph6Mp1JbIwjxhOU1GCP9bD4aeNtF8a+ErDx14X1RNS0vUQXs7pGJEqpkOpUgbeQQCfTnrXWTeKLm+iLM721kW2hmGGc/3fU/hXxh+wX4Z8R+Dv2O/h9ovxH0ptEvoonkawkb541kZnTdnkbwQSO1fZFxPp9xJH9uVLoEbhtOV9sZ/pX8pcQ4eFHESpU3oj7ylF1IqbLd1eQxWLWrusNmufurw3QdR3Feda6QJ7a43b4zkDHIUerD1NJrMmpNZ+VcTj7LCTsjUjIJPc+3eobjQrS1tre4ubndJOocsvQJ6Y9+K8SO1z1KEEUdK0wnU7drPzJkknXbHtwSdwycnsK8Q/Y/+IIj+K3xN+COrN5M2j6o9zArc8TE8AdhzX0NBr1+NXt3som2xYCJ0GO7Zr8gz8RdW+Dn/BWPVdBkk8pPF8aeaJMLxIo2MM993Sv6X8CpP621fSx8RxqlyxP3V1K9uZrVBKQ0cDlsHlo+OoHQj2qLSYrX7XJf4JjlGxJPuhz0HHb60yGy1CzuZLV4Mx2g2MjZ/eBuc5Nbjo09sYhGqRyJiOIgll29enORXl+N2D/29sjhyu/ZNI3bCC0j3u0QTYm3YowFY/pznmmDWINJ26dcTpLchcrFGMhU9/TFcBe3Gs3ciWwLW9gqsrnHzSOBgHnpis2Pwyun2C6fbySxRsplvLnfukJ2/dDdQK/B6uYcsHE9z6o5PVi6z4uMmqRapots2rmQNGFiG1RjrnPGQa5BtV168T7Xet5USuSbdk8wBugbpxtxge9dmdEt4rdLvw5dnT1tCzNt+ZHGBzzyc+tVdS1aN7eLW7PapWQiUD5Q6jqxBrz8qtKsm+53OmlG1j6o+F+oR6r4RtrxTuJXHIwePbt9K9HKDr27CvMvhdqenaloJ/s+VZVjOG42lT6EGvT1Kuwiz0r/AEY4Gdssp27H4xmqtiZmfOqmTy24DDBry/xf4WXUInFuxibOQ68YPqPT8K9KvXbcAvUVz9+xZWV+9fYKBwH5p/tx/sP/AA8/4KDfBC/+FHj+FbLxPpcZbQ9WAAkjnA+Rs45Unhhnoc/X/Pt8B+Bfi5+wJ+314fT4naS9jrvgrWhBcIwKxzQXBKpKhxgoQx2sPUZxX+n1qcdtOvk3biPDZRx1Ddj+dfkh/wAFZP2APD37X3wyh+MHhTTkj+IHg8o87QJ+8vbNTueM45J4DIQMgg1w5tR9phalO26OjCe5VhLzPoG+0zTta0ay8VeG9RSe4voIpXgXarxDyxu5HUnvXQWHhfSNYMBuJXia4j4XaAA68nBHoR0r5q+DN/dH4Q+FmubU8Wge4deJomACkc9V46etfTelXsuqW1vcH91vjLWhAOUdejHHB56iv8yvEGiqWMcUj+kcmrXoaHAw6VYaFcGK3vAlzv8ANRYkcCVedzPjoB0PPWmLp3lPHdp+/urhiBa27hluVY53M38Ax1rodQtr5Jxfxyie6RD5LxjEUySnEiHPQqecA9qoTWI8JxW2m63cKBCFEU9uo3bWLERuOvQ8V+dVX1Pbo1b6GPoLQWltJJButbO3ykkG0Sq0xI2hemMZPPpX4Jf8HJmlm+/Yu8LePrIy213oerGRnul2uGYYUbeVyCByD2r+i/SbW0tDHcQyhLQQEi3YElpW4Vm5PUDHGPWvB/2l/wBi34fft/fBWT9mb4rPe2+kalOlwNRt9rT28ivuCgsGHPI57V+4+C+LcMypW7ny3F0E6Ej+ArwJ8SdE12wh+JPhS9sYvFJiimv7FZ18u7SRAWnTOMSqwO5a/UD4P+PvDPxN0Sc6+8cMMyI0cSLvaeTGScjPGe3Wv6R/gx/wbJf8E7fhLHF59nf6+6jDtqEqnefUiJI6/AD/AILgfsp/Cj/glZ8YfBWv/AaRrPQ/Gwnd9NZ22WcluUXfDznBL85Pav8ARmW5/OspXZHrXw80i5s49cuo7fTrhzu8u2AZJccKswGMEn8q4q50/W7eJdQ1y8+yxPIYooP9cyyY4w/RBkdD2pvwQ+OekeKNEGs38iXNxPALWKBQhMjnjf8AMODnkEV6Z4y8JRiGW28N3QttVk5e3lIaKRjjv/CwGBkVIjxPx74X8HfGrSB4J+I2kx6pNaRhrkXpCzybuQ1tKo4xn7ua/J/4/wD/AATf8U6B5/jH4CudUsIhvn0uUgXcBPOBn735dK/WWx8T2cd+vhrxBDJoeoWcpDi4I8tjzt8pj2z15rvdDllW2h1iaLagmJnZcfaWPcDB5wOhxyKAP5NdFv7rwf8AGPwvJKkthqWnaqA0MgZHjw64Jzjkt0wa/wBczRdYg1j4eeGNXtZ8pe6REzqkfmO2YkJxjphj39a/h4+LP7KHwO/aU8S6dH4x2aDqFrqq/wDExRE87yD8wQ4GMn1Oea/ta8AeHdW+H3wW8Nab4SlafTbLTo4BcvgSIuxMtLkZJ4AGOK/mX6Rn8Ol6H6PwA/3jJrnTpdYaDTtJt2uLi3EZSdAQqSFjwWz1AJzXZwaG2izzWi7rOOSUym5kf5mwOqMfund2Fcdb+LZFv20/w4h8tUSRIs8OrnDSsw5Dk54BrpNM1RvEFjNqWqz50yGXckQAaQhTtJH4jvzX8IqVup+y4m7ijqTLLb6XDdWkVzOkbHfMcq5B6/K+WOfUGna34rudTgOj2TfalZN1uDgbT1xIM5Bz05rEvtV1X+zJr/TmkuFG0LI5KoseDkdOTXn+j6JYXU8mmXF3NaW0pWWacfLI5U5EYPp7HrX0GQ5hVpYhNM8jFYdThqfwh/8AByfoljo//BRvT9ZsyXTUdFsy5YYJYKyHOevocd8V+A93HiQA/exz+df1G/8AB1l4VutG/ae+HfjSeFIl1DTRCG24/wBXIOOM84OTmv5gtRULOzDPJPPbqa/0u8N8Q3lFGU+x+D59DkrtIx1ygwKcCpGG6nmpicLyB9ah+XIT+90z1r7o8FCkAuAvfkVA7EYZgXOeNvB/EVPtBYHgd8YOcioplZzyPmPP4+lAyAD5o1D85OMdAfepAxLGRRlgcYPQepoCggqMqOjDFMw5QMMHGQOeCPc0AOkZg3B/wx60MQDhTkDkUnzNhYwcDpkdB6ZqZklRsooK9qAGZI685p5OBmkVWjb5xnNNaNy33fzoAAw5xTY+9KI5F5CgU5c4y1ADWXceKTaD8v8AEeh7fjS/x57Up/2etAAQ+OtF2SLGT12H+VOK8k57U28/48ZP9w/yqteR2HHc/qU/4IVgH4FT/wDXd/51+iXgoZ/4KofC/PpN/wCgyV+d3/BCv/khU/8A13f+dfof4MB/4eofC76S/wDoL1/l74ma8RYj1l+R/enC/wDyJP8At0/o2+IIA8EeJP8Arwuv/RbV/L3Dz8CfgwD0/wCEtu//AEKv6ifHv/IkeJf+vC5/9FNX8vKcfAf4Ln/qbbr/ANDr8npxXtIndw/Z0qny/I/rA0kBtN0rd/di/mK+D/FqL/wlWp/9fc3/AKGa+99KH/Er0vH92L+Yr4K8Wf8AI1an/wBfc3/obV/XHhGv3NX/ALd/U/AeM3+8j8z/0/685/8AjyvP+uLf1r+Un4h/8m9fFL/sbLT/ANmr+reYE2N23rC/6Zr+Uf4h8/s8/FE+viy0/mwr/Jbjd3xUGvM/uzgJ+9VP3l8QDP8AwTO1of8AUhyf+kNfy3/sEZX4CaWD3mn/APQ6/qP8QnH/AATM1pvXwHJ/6Q1/Lh+wJ83wE0xj2mn/APQ67k75Wv8AHH9TXg7/AHrE+rPx3/4LH6i1n48tJQM7VkUfiK/Ac9a/eL/gs9uHjO0cnqxH6V+DYORmv9B/BRWyCk/63P5f8XNc3l/XQV/mGBVerDfKu7rVev1Vn5cFFFFIAooooAKKKKACiiigAqW3j82YVFWpYIN2TQBqQgqhzV62Zy4Cjk/1pIzER0q9AsasDnvVJ8rTA/tB/wCDPTxfLbeNvin4LZtyz2tvJs7cOwzj6Gv7Tr2TUUmadQsjNiIpgfKGJGR9AP1r/P5/4NN/FM2l/wDBQDXvBcUxSLVNImJUHAYxYI/H0r/QQggkgu30i1ZGKysW8w59PxBr+Q/G3CcmPk+5+m8JP9y0XLsfYLOzu9TQkSAlIlzwB0JrnbuD7ORcwhcN2yP1rV1PxJdD/R3VZYpCfmYgmMDjA+tczcv5qG8SNlhYBWYfd3Drjv8ApX83zh0R9rTi2yexElxKkJOI5yfm7AjrzSTQOt7LaSMT5BHzDvUtst1c+Xo8SgxEeYGc/Nu+vpWvdvbzXO+0Qr9nKRyNxtZuOh79aIU7npRqcqM42EkjboVJCDPXqf8A61adtp8dpb/brjAkkxtBIB+nNbEqz2LzrY+X5p5RW6nPUCskRw3unsWja4nU5VCDgScZ/IV008M2tDmq42GxbuDHA9tJPMY7d/vYwMuR8orq9HgfT4PM1ckTS53c9Y+gK1x1loVxdz/br6YyRkrmPbxGyHIBH9RmtyWDVry/S7mV5YppCgCjmFeh4OODXqYbJKs9jyauMh0ZuzNBYxNYXts11Cqh0Z/4OCc5P6Vlw+GoPE5h0653+Xgv5ikg9eOfXGfar+r6JrMCq+rXUZCODu3bV8tccSZ6VS1v4yfB7wZYK2ueK9I0uIKczTXMaqDnopLD/HGa+hwvCdeo03Fux49XMFZq5qLpdleabfaXqDjZcxTWiDgYRkZBuA4JAJJ55r/GH/bH+HF78LP2oPH3ge4QgaTrl5bk4wPllbA/Kv8AXD8V/wDBSP8AYM8BQTS+KfifoLyoCHjiu0k9vlVcnJ71/l2f8FLfGnge6/b4+I/jHwVKus+DPFOrT3FvcKMJLFK2RIpPOVzjtX9PeD+Br0ITjUVkfE55XjJ3ufljJwufSv6a/wDg1b8Yt4c/4KKp4ZB+XxFpVzYsCfbzFH5pX84Hizw6PD+oBbZ1mtZhvhkU8MnXn0I7iv2Q/wCDerx1H4I/4KpfC+Od9seo6gbUnpkyROgH5mv1HianzYCqvI83LpL2yP8AUbv/AA5a2dxdTSXIcRORt3AucnHzDPGO1P0+98PLF9qtwJgvyyLIc/l2pviSxg+0TGKLChyTzhuSeSe/WuWFnaWsrW1sGVSN5OBgkc4r/PDiGlarZH7PgZKyfka1tdaxql01tp7YtZSWkP8AdVe1Zd7JJbTtFaNum3MSh546AjtzWv5dxBoitpk4WZ9xYdmz246dO+KpeH5Vin+1XcQZnJDOfvKM9B7V48Y++mdtF2WpD4fS80678qNHYFwEGwYP459a/gE/4KnRz+AP+ConjfQ7+Zl/tRTqAHA2CVV7dyuD+Ff6HNneRXN7GtkioFYbpWOMD/ZHc1/Aj/wcLaRf+B/+CsVnrOlWwkbVvC0TJ5gO0szSJknjoAK/pnwLrr6yz8840q/ukj5Q+DHjiw/Zq+Pnw9/aB8P3qR/2LqUSXWw7HlsnOSWHUblJGCM+1f6U+harpPjXwhovxH0e4hOnatbRXBbOCQ6bl/8AHRX+YPDNF4p0W58K29vahpI1Q3Gcu0kZHlmJtp/iAH0zX9k//BB79rY/tBfs0N+zP4/ut3izwR+7MMh+d7bJCuPUoBsPsRX3/jDkUatP21OJ42QY/kaSP3ss9b0/UNl5pREiSj90WGAzDPY1O1pa3lxM+drSqFwDhQ3vnvVS0tLXQgJ5HUWw4Ee3iM5xgH1/rWbNpWoWtt9ltI3uvNk85HyBgjn5skdBX8aYujyTdz9D9ut0WrjwyYbySYyssYQDg4yfSorPw/deebi5Agt2YbWDdfwHQfWrP9rXc/l28m0PHgy7Pl6HPBbg07xBceZbNKTvRBxG3UH1OSMj6VcKvLblBylLQwPGXwr8F/Enwlq/wr8f6Rb6v4b1i1a2vbWZQyzLJwchuOAc57etf58n/BYX/g2r+NH7Nmu6r8d/2NbC48V+A5Xed9PhHmXunqedu0cyRr2YDpX+hLBa36L9t+0rJNtwgXIAUducA/TvXR6JreoRN5OqWzIrkbn6rKPTDEYB7jH0NfrnBfiRWyyaS1XY+fzjK1Vvbc/xEtT0zU/DNzLpGv2txYXsJIkinRkYEdQQ3IPsaS2u4XxMx+YdCO317Gv9d/8Aar/4Je/8E7/2rr2eb41/Dy2h1OctI+pabELe4kPqzJj5s/3s1+QvxE/4NRf+CeXiK5F58M/E2s6KsoysdzIkw55xwimv6By/xcy+pDmqXTPjauQ1W7XP87ODWtPhXEkgPsOc/jXWaBqd1e3sel6LaS31xMRtWFWJwewGM1/od/Dj/g17/wCCZfhjW1sfGF9ruvXMABkKzrbxkg9gYiCPUBs1+q/wD/4Ji/8ABPL9my4jtfhH8M9PvbyyAkOp6kguXRs4CBm/i7nHFLGeMGCp60Vdg+Gaj0bP8/P9i/8A4I7/ALf/AO3KX0zwv4Wn0PwvqEi/adR1NPJjRUzyDLgtx/dr+zb/AIJu/wDBDP8AY6/4J0tbeOdYij8e/Ei2CtJqE6hrWxfHWFSDz74J/Cv3B1a7W1jHhyxkjgESY+ywIIYFQc5woyR261z0M9kEEErKjA/vAn3DuA2gZ6mvxjjXxex+NjKnGSSfQ+pyrhmELNmU/wDxMroyXM/midtqqT13HtjspyBj+Vd2vhpILRY5n8okbwTyVxwF4qHwpZ2wea9urQqUYBFk+YoV5yp6AHrxmqet+IZWZ41DMSc5A7j0r8Nxc1NKXXqfaxVtFscdqWLacm4XMaHoMcn1/DrVYaU+pwvEiGd5tpPXgIeRxwOtXr1v7QIuL9CnlEEInPmdzkdeRwauadd38LOzKIZFOQqDKqOeSTjbnjrXn0aTnojeM2tEXpdIWWZTh7W2VfkkBGVYDoT6Z9a/mF/4LN+JNb+F/wDwUO8H+NtDd0u4NPsbs/wl/KY78f5xX9TT3NjrFidIvGa2mlxuKr8zEn5cEZyCfav5L/8Ag4R+LvgW6/aQ8BaD4KvY7zxh4fjEGqBCHSNN3ypJj+PBbK/Sv6J8HL08dGKWjR8LxjUU4rmex/Xl8FtU0D4ufA7Qvi7DK7Taxp8LzMrch9g3Adsinah5GjyWht4nnllYRB1x8pZhliMZHHNfmT/wQx/aNuPix+zNqfw61gAX2gTGZARj93ITxtJ4wy1+oZ1TSdTtLsw3UTuj/vJEPKg/dyP0NfV+OmXwVSM/I8zhStvAtTuZIxHGVMaIecg5PcD3rlpreK60SWUSSRQSkh15Dk4xgAjNZkixW8S6Xp0hVIky6M2ZNrchyw7D0rh59X1prwagzGSycCNzn73YbfRvrgV/HuLcnN3R+jUqa6m7ql88NssgYy2sKiKS1A+dSehO3PpWLJ4j0CJru6mVpY/L2T2wA/1ZAAJ49Oa3lW+s2+3Wtqsc4YROXHzSRHnd+GMVy+oiwtHmDK0Mb4k8/KtIgAJwVOP93BrDLqnLXR0yoJ7H018DrqC60uf7PHBBFMd8SQkbgo/hfAHP+c19Axuc/MMNXx9+z266XLf6hqJjVJiSrK24hST94duvpX1zCyvCGt/mJHWv9E/CvFe1ySC7H4zxFQ5cTKxYkRX+VuprntTtmhG5unNdLEAF4YHuapakvnQfNX6SpKx4B4zq1ujMZpRmM/L6Yz9e9c8ZNRsL7Tr/AE6XHkTiC4RhnzIJONpHfnFdlrEYWJkI3DBwPf1rh/tSpqsW7P3ogT7hs1NV6S9BrufN2vaP4es/iVeyXkfl2c0kyJEADHGV6kqOmQemMVmxaZqk9hHZeGZk0ea3OIMNxJGD82F9DnPTOa7vxxBew/ETUG0SzS6Dy5uQ/wDACoO/BI6deDXHRa7oevW8Fk8NvPcW4G2WUEPIoPAiyQQR3z6V/mf4qYdrMap/QWQVr4WNjKtrfX7zTbprEHFsW+xwykBmd+JJPXC8nB9aoaEunxWpvLBke8swbaOacbRI55OPMIzgZ6D6V1WtS6obE6rOLeHVLcHZGG3RqjHByR3I64zg1yd+2kahaW9hdWcmyRvMaFWDCIbf9YGXJUZHevyKNKV9j6rDtblnwlJowkNhiN7kBipZQFDORwrH3GQDyBmvQ/AGq6jo3jnS9JjvNiTzgXFuuCHkY8s+BgDbgDkHKnjmvBLW1/tS7XT9Fmjj02EB2knwzxhc5JKkZJ7Zz9K9i8HalFPe6Xe6dYnT5hdIVvrpwRcDO7aoGCwPY44FfrXhrVlSxlOfmeBxPaVKVux+ly/6kt7V/nVf8HP/AMfdA+PP7fnhP4F6S7bPh1bSG9lDYDvPtmKJnjKqAD65r/RRil3Wm5Op6Zr8IP8AgqX/AMEMv2fv+Cglrd/Erw8R4T+IyRfutUtxiO4Zfui4UdeMDcMEe9f6VUJqUFJdUj+ceTl0P87H4N/F66+Efi2OK6umk028kY2UzjHkuG5DJ25PTv1FfvJ8JvH+gfGDwqLC3n+y6hcAmW4Q/MCvTHcBu3pX4t/tY/sgfF39mP4o6r8Av2kNJfTtahZ2069RcQTgHCPGwAVt2ByAMnqBWJ+yb+0B4k+GPjyPw5rAKzI5SdmYgtHjuPWtQP2y+KXgTUvGvh+Lw98StOeWPTCkgktpQZ5IQfllByGBUH5geTivPbPx3Honi+w8LW7HUJrMpNFdAjdHA67Pm5GWHGQec+1e822u+E/G+iWninwjq11bm2wdzjcs0hXBhYsc7fbFeTaz4c0LXJby6udOkU2rpNiKMQT+bnlVchkeI0Ad74gufEOoSQabpFnb3I0q9jmnMLKu4SHiRsHlscNX9Ulp4j1K+8EeFtbuLg2xurcRwrGM+aFjB2MB8uMcjPpzzX8kGmxXQ1C9vEtGhR5YJbmQNuWB1BASTp97rhRgetf0p/Bz9qf9nKz+Duix+JtWgnv1tBHsZy/kzLGP9UOMdO5zX4T40ZBVx1OMKEbs+84Nx0aM3KZ9MWN1p4tDvtmsdPZ1Eahsyzz5+UYGWA3HOOBV+Xw3b6TeRC8JubnTYhGIEX5PPcbic9FHPzHFfCrft9/s5+CWS51fV5r66MZkknWB3VfRVAGAwB4IzUOuf8FVPhCnh9tE8H6PfX7ybWuLkIFaVWPD8tw3scGv5mw/gxmFeb/dH6jiOLcNGOrPv+GPxP4paQQTG4eIqtzDEwAjDDjOTg/hmvUfEnh+9t7OyuLaO2uIIQCs1w4A8zqAwwSVHbFfx1/8FM/+ClP7eWhPBqf7Jdnb+GvDUEJa9NyI57uZs5LMucKPzNfgH4k/4KSf8FGPH7GDxD8W7u1s5wT5emsVSMnJK7FK45GK/Tsg+j7i3Dnm0u99z5LMuNoJ8sNj+if/AIOt/DEWs/C74R/EKS6gubyyv7m2mWA5xuUMPfGRgZr+PDUF3y7/ALoc7semRXpPjv4t/GX4ozJH8WvG+qeK0tnzHBfSvJHGT/EocnB+lebai8mQSQ2Op6fhX9N8KZLLAYOOGk72PzTM8VGrUc11M5mUjD8Gq5YknHHfJ55HGB+FShArNu5yOKjY4OAK+mPKBnQoCvA9O+e9Pb5mUA/e4z9OhqMtj5i/XhhjoKdyMDvnj6UAKqyOemckpnIHzCmonyk9cHDDBwPf8aXy9xI/vdycDJ9Pekyu7PLA8c8dKBXRKJAe2KQg569entSKCMEDA+uacQxyfyoGKcD5TzUIKA5UHI9TTx8pxUY4JPXNADmYkfTpTSpIIFKAx4xipApGQe9AEKjAxTe/y9alKkDNIu0HmgBpGRimXnFjIM5+Q/yp7cA96hustZysT0Q/yralpFji7NH9S/8AwQs/5IXP/wBd3/mK/RTwccf8FUPhf9Jv/QXr87P+CFn/ACQuYf8ATd/5iv0R8G/N/wAFUfheB/dm/VXr/LjxIf8AxkeK9Zfkz+9eFWlkmv8AKf0eePAW8C+JCP8Anxuv/RbV/LsoI+A3wYP/AFNt3/6FX9RvjsbPAniPPexuv/RbV/LxsI+AfwZP/U3Xf/oVflVP+JFM6+G3+6qL0/I/rG0kZ0jSf9yL+Yr4G8Wf8jVqf/X3N/6G1ffWkHGjaU3pHH/MV8CeL2C+LNUU9rucf+RG9q/rfwk/g1f+3f1PwDjBfvI/P9D/1P685Hzpt03/AEykH6Gv5SPiEP8AjHj4p/7Piy0/mx/rX9Wcxxpl4B2hk/ka/lN+IPP7OvxRP97xba5/DNf5KcZK+Ih8z+7PD/X2r9P1P3i8Q8/8EytZ/wCxEk/9Ia/lz/YFXHwD0wes05/8fr+ozxN8n/BM3WAv/QiSf+kVfy7/ALAgB+Aul5/57Tj/AMfr0IprKl/jj+prwav9qxPqz8X/APgtEoHjCz/3z/6DX4LfdAHrX72f8FpRjxjZj/bP/oNfgfIxBXHtX+hPgx/yT9H+up/MPiz/AMjeX9dEOL8FTUdKeppK/Uj8sCiiigAooooAKKKKACiiigAAJOKvwkxYbrVRGA4NT+aP8n/61AG7E/vV+CUMcP0FZEbLsyOtWouBn6UVdY2Qmf0Hf8G1fi238Jf8FWfD8Mj+Wmo2lzb5zjlosj8fl4r/AEsta021TUr7TpLgS3xIY+Wu1tqgdffHU1/k+/8ABHzxfc+DP+CmHws1m2lMPn6vbwO6nB2yMEI/EHFf6w/i5xp+uX1yhEcOBtk53bpDg4PpX8yePFC1dTfVH6NwhNuNjlEsbFZjFexRGDbmNuS7v6H8aFQLbGGO3lhlJO2IncpH94D0NVpPEH9m6edH+yb7i4YyLKPmwo4HPf3rYj1C0udOhvtKkJuQoLFui5OCAfQdK/lSS1ufoVBNFu3ksLLT2geNmuWHyHHIB7ZqCwicRCLYC7lQwOCqH1Az1pYNa8mdYL35tvK88k9xV7R7jStQ1BJp1a2Z3G6Jck7lYZyfTFellVKMp2kPE1OWLsfhD/wUN/4LufDP9hL40an8A9c8At4g1vRVjk+0yTlFfzFDjAUe+Opr8rdZ/wCDq74va15n/CC/C7RtKV/lSR5XkkUeuOBXwr/wdbaTrHw0/wCCjFt4t0ZhEmu6Naz5A64G0+3UV/Or4W+M0Vw6QayhgVT88ikAYwOcetf2jwl4cZZVy6FecLtn5Pj84qxm0j+pzW/+Djf/AIKA6/qQg8PXNhpNtIpEnl2sRCg9PmfJHPevI/F3/BXL/goj4/K6RrPxEvLVrhCwa22QHB941GB2r8SPCnijR9an26ZcLNC3DEkEEY7jrnNdxDfTwNCzTvDd79oVunl9q+6w/BmW03pSR89WzGrPqfYvi39oj9q/XbBLvWvH+vXkV+2yWOTUpjvznPybsY79K8Y8R+K/EZtEXUtUu7mzlPltJMTII27hg2e/c1xv/CYX9pMkOqR+eIiFjOcFV/vHn1q3qev2GrGTV5JQNOwYpoieXbHp7mvXp5RhoL3YIxWKn1Zkah4Q8PaxKL7Qo/tmpIxdwGwrLjkLggcDmvLPGfh+K6s54dY08R2kjCOVHBPlZHDxk5PHcCuL8VeIfE/wov4tVsZRNpVyQ0Rc/wCpOc7f6e9d5oPxc8J/Ea0ayvWEd0yEIJOj564/pXbRoxgrRMJybd2z428b+C9R8F6SYsre6RcvutrlP4X9D3HuDX0z/wAEsvGo8Cf8FAvhb4pY7Bba9bMT9ZB/jXnfxC0xNO0+8s7AE27ocwHna/8AfGa8x/Zu8Qt4Q+P/AIT1rds+y6ratu9P3qjP5VhmVJTwtSPkbYaTU1Y/2a/Fx1jUPE0On2ttLLFcW0cwmEbCIBieGfG3P41mJpT2zoXbcIm2N3G49Me1d1pV5cav4b0S9tlH2S7sLdhIh5IMQb/2amS6SrTEEPElvhg5A5PvyK/zv4sw7hiZJ9Gfs2X1l7OKZyqi90oXVtbLHLg5mIUFSWHb0IFZempcjEccRJkJ68YGT613zPBd3v2ezCworB7kY++AOnX6VZsLIxuNUWI3au5QAgBUGcV84lc9FzsT6ZoLRRmS7iFwyDMW4ZCZGeMV/DR/wdf+FJfD/wC1Z8KfHsUbj+0NLNnLJGSGYJMWZeo5CvX94nmWojks7a4Cy4J+U/c7c1/GJ/weBeGLmy+Hfwe+JGnhXmg1S8hacnr8kbKD26qa/obwaSp4yMT4Li6DnC6P5h/hp4tsDZ21kx8jyvMPmzsR5p59/wCEDgdjX6T/ALEn7S3iD9lD9pPRv2kPCMktza+atrrEScGSF8Bv+AsOhPQjPavxG8EalJHFG2rYuG27gR/eY5wPfn8q/Qf4da3O+nf8TybNvdJsjEQ24BGArk8Y96/qjG4OGJoyo1VufB4arOD06H+m54Q+MPg/4yfDfSfjF8O76PUPD+uwC4AiUELMV3Mrc5DZ4KkcNXpXh4ibTUtwpjZ4z5kTEmRCeueK/iq/4JZ/8FHLj9jfxuvwg+LUkl58LdfcKZ2+ZrCZsBZFzxgcFhnkcjmv7MfD2vaLrGkw+LfBV9Hqun6nGJYryF96PBgHIZQRnB6da/kHxB4GnhMTJ8vu+R+hZTmUZw5ep1l7p6JZICyqkHKPJ2PbNcr9i0+8u0vdn2h1OPMlH3sddq9h26VoX179si+x6mRK0+DHGPvAEZyT6iqbyXEBjgiwWHyGTgNt9Me3rX4/iKCpuzPrMPqjSvdWthK1jdsgWLb5QTjB9+1Vo5pnQwPLJdO53IZOQp7fQe9clc6VJf3pXDNAFJ8zOCSDTU8RXNq7CVRGqDCsf4iPTFefPESi7nQ8PE6W6t7qWQwsnmXJ+Z2YkjZ6elPvbKyswTfxhIQgYYHzKT/d9qr2nipUiQzLh2xz1PPvU76jbajqO+2HnovUHoD6HNbU8xqLqT7Fdjn5NN0TXNUtdSRpbie0DC3fcVKk9VYZwc98itmHSpdr38Z/eOmySGLCxqQc5K/xH3q7NDDYPF/ZiecY5CzkdeR+prO8QatNbBrmD9xIo2hwO3fPvWNXHVZLcmVJW2I9d2Q6a17rDEqxSMBFw/JwCT/d55FVbzTLJNNt9Qswk0ca7ZCw56fwj19DU+seRqGjtq1pJh1QL838Skg5xXnz6tIgWJC0zDcsa/w8YH6VhCvJv3jSFPojejSW5iCs7rCOVizhkx0389DVDxS7BIpbGVoViH7wr8wbPYV2mqaNHdW6TRFYLlVDSc53bR8qt9a87vXfUbwWd4UiSVQyIc5R15YHHpx9c13YalOrLlijR6Cqby2t0lcgm7IjKA5kTf8AKGJGeOc11+k6XFd+ZYpG5llUFImUsJWGT85/UA4z9adp+k2P9kXF9fGO0iVS17czMEijCKTkEkfwjPHev5+v+Cnv/BaTwX8OvD17+zj+xJff2h4iu18m+16I/u4BkBhG3OW7bh0r7/hHgfEY+vFU46dTws0zyFGDjDc9c/4K4f8ABXfwX+xR4ek+CfwPlttb+KmpQeUxi2vb6SGGC7kHBlUNkLn5e9fw5alr/iXWtZuPiF4z1F9U17UL57u5u5XLySOTu3+YTg88A/hWvq/2/UvEl5r3iO/k1TUtTkL3l5M29yX5ZAT6E9fevKNTZo5JNPYBYQGHkA/eAP3vTj0r+zOFOFKGVUFGEbyPyzNMdLETvJn9b/8Awb4/HkaR+0VP4Y1O6YweJLZowHPy+Z95eO+GzX9SXia11/S2u7K++zxyGVyqxKBuQP8ALluDnH86/wA8/wD4Jf8Ax1tPhl8dfCXi21Lq+lXyLIkhx8hYcnHqCeK/0H/G+qTa3qrapExa21K3guIWP3DvUHgnnnFfmvjfQnVwsKltUfQcIpKTuZ8SRacItasI2Ml6pQ72ZsBecOD2qj4lbS9U2wXitHFCCR5MpiLMTwEIxwemOaspItrDJNp7PcXL5SSNidiKRj5T+dYE1xo+mwfZdfCz2lvGrJs3F0lxyBzzX8e18tqylex+oU5xvqbmu6jqOk2Z8xzFajYMo5edQQSqKcZ42nNeY2t5p+q3EmyOWdLgE3MkjbSy7e/YGtjxJLLZRW+sJMzPc4khD5KqvQK2P6iobWL7ZDM1xAWhgXkRjAmZ+T09DRgeHakqyk1ojsnWppbnqXwVu7Wy8T3sVrZpa6S8Ri+YESS8/e3N1r7CsLz+wljNtK0lntBw3zMM9Oa+AJdWvvBqw6nOWNvOypyOIeOF68A17t4N+KCziO3eTfAwxwcjBr+4fCWhVo5YqUz8g4mnB124s+w7S7sryEXFodwPUCrE0TTJgDGeCK8609ViRbrS5dyOASFNehWV4lxAMn5/Sv1dKyPkuWx5xr9q0DuhHqPzryTUY2gkeVuoaMj6Ka+m9R02O/iw4+avD/EmmvbzODydpGPT3qpawa6jufJ/xmuIIfG0zXF39iFywdJNxGVMY+Vse9cPoVrea7exNaxxQ3Q2JKZBuaNCcNLH7EflX1TY+C/DPjGYat4rhFyYiISevTpmvb9N+FXgixdr6wtE/frgn29K/mPi3wXxGOxcq0FufoOWcWLD0VTR+dd74V0G/wBOu5rmK+EVlMpsmtGYGR8nJLDPGcZB9a1Ley1KVU1O00t4dSljLTyRuwyMY2OduGr9MLbwjoNvAscNugC8gY7+v1rTj0bTI1wIFORjp615eE+js3Je1nY6pcfTWy0Pyksfhx44vrvFhoxhSRmfbCcByBwXGOR7V6XoPwT+JmnzWepbYrl4JhKiTgFbdM8bQWG3jsORX6Nx2ltEQY4gMdMDpUjQ7+o4HbNfcZf4HYPDNT9o21sePjeMqtWLio2uVrNWiiCnnPFXjGD3pAi5HPSrSqCM1+2YKh7OCh2Pjpyu7n4S/wDBeX/gnn4c/bV/Y91fXdKtceMvBkL6npd1GAJpFhG6SEsMEgoCQPUCv81LxFol7r+nWn9og6Xqlg5gjvApImlhOB5jDGM+p61/s36zplpq+nz6ZfIskNxG8TqwyCHGCD7Yr+JH/goh/wAG1vxsvvHHiX4o/seavZzWOqNJcJpNzuWVXbLGOPIKYyeO/NdZB+CH7DX7WUv2s+D/ABD5JnVltrhZmUwb2O1mGfuv6V+qmtWejeLbKa70nUrlY9C4lsxwbu3b+FXGAwU88ZNfy8+P/Cvxb/Zk+NN/4D+M2lT6L4w0yUre2sieWs9uBnOB/EByrDqMV+vX7LP7W+lLHpPgPVZftNnjzNMuc/Ntxl439x0wcmgD7ImtNI1tbSK0nhUmLENncOYmm9HZwQC2Rjmus0vxJfyahcRXQgluSpEcEgEkUSEbc/JxkZI55rptei0e9hHjLw5ZW5h1bMVsGyWSTA3ehQkgkcV5j9nGqJeWdq8ukQ26q16wH715MgHaOBtJwadSFN2dtUbU68oqyLmproms6W9q0si2+nBbq1kiUDKgAOG5yyhhwPr61s6Zq3ijxBqFx4ftby1e9vV+0eVBCI4ykfAL4Aw2OQfWsyTV7/xNpIjt7NLSaOJIbONSqs2eHaQHJIYDNc14vvUtbt737csNrexpbQTRABwAMswI4IDgioq01KPu6MzlOTerueiaboOi+LLa98N6mrPJIDDgKGYMRyWY5yhNfzMftU/Dq6+BPxu1Tw8LYW0DsZVCjghySCpOcjmv6Q7TUNVvWt47KZYbmyTMojxl8j5SSO5Ffl9/wUq8CT+ItC0r4h3EeZbcfZ5iOpB+7/8AWqW3G3vEW7I/Hhbl3j3o2QOfxPrVK4KXGQg575pvkGJzD83Hc9KlZAD8p4ro5W9YouzfQpSRNjnA+lRiItjkD/61aB2jhqZ+7X5sZpezl2Bxa3Kauq9cHsfeoi5wVx8w7/4VpCGIjdn8FUnFUDEN5IBx3BOMfpTcPMliZ3AIOUI4z2prZMex+fQ55wKmk2w/MxRQepLUqIF+/wB+cfyNJwd7FuxXDsKeJBjn/P6U4bSp3HBXjGKHXAG0daggY2duTzQUIGQf8/nU5H7vcego2gnafTNAFdWIPzHNKzZwBU3lqCfYUbV25I9qAI2wV47UgTIz/n+dIBtG0DIp2cOE7Hv6UAIIwBg81DcxZtZRn+Bv5VZDKSBUU5zazH0Rv5VrBXi2L7SP6jP+CFjn/hRc47iZj+tfor4LXH/BVf4Yr6JJ/wCgvX5y/wDBCon/AIUdc+0rj/x6v0a8EHd/wVc+GYP9yb9Eev8ALnxIX/GR4n/FL8mf3zkCSyP/ALdP6QfiBx4E8Q/9eN1/6Lav5eX+X4CfBhfXxddfzr+orx+o/wCEF8QD/pxuf/RbV/LtJz8Bfguf+ptuT/4/ivypP99E24dleFT+uh/WBpTY0XS19Uj/AJrXwJ4y/wCRv1X/AK/J/wD0Y1ffOmf8gbSv+ucX8xXwN4y/5G/Vf+vyf/0Y1f1v4Sfwav8A27+p+C8Z/wASPz/M/9X+uqUn+y7z/rk/8jX8qfxC/wCTdfif/wBjZa/zav6pnP8AxLb73jf+tfyrfELJ/Z7+KeP+hstP/Zq/yQ4tq82KivU/u3gFcqqfL9T94fEpJ/4Jnazn/oRJP/SKv5fP2Ax/xYLTT/02n/8AQ6/p+8Vt/wAaztXB/wChEf8A9Iq/mD/YJyvwK0on/nrcf+h16lOV8sS/vx/U34NjfE4l+p+L3/BaP/kbrMn++f5V+Bzcnmv3/wD+Cx8DXXjWKJRnBZvyFfgCwwxBr/QfwZn/AMIFKP8AW5/L/izH/hXl/XQbRRRX6oflYUUUUAFFFFABRRRQAUUUUAKpUHmpt6DsKgp6daANaOdEQBhVwSDZvHArGjOMmtOM+ZtXtQxS2PsH9iTxb/whX7YHw48VRf8ALrrNk5xxwJVzX+v/AOLtUk1iHTLnT4w8VxYRSsO7M/Qe9f4wfgPVZPDXjPQNegba1pdxy5HUFGDD+Vf7FPgbWbrXvgb8PfFto7M11oFpKWU9WMMbD+dfgXjZQ5owmz73g5W6mz4hkvrbT4LASlB8xlbbyrk8ID2wa1LTULm1s2lsbZPLHyzBVA2k8/zrJuY79pna/ZoyY/MKHlWY/wAQrV0S4trBRPc3Q2gFflBxIT2Pav46xCtNo/UKXwmE15c2pWaa2Ls/MT4PyH1JNdXGJdLube9xu1C4TbvlGIxkcPjvn+dR3U7XVtvVhbwjBMONpbPf6Gnw6rDaWcNoWwqnEDHkoSe3vXXlsrTuZYmN0fxX/wDB3H4Cur/4r/CLxvNE0zX2jy2rxqT5jNDIMkZzjrxX8feo+EvDmr3L2uirPpV0hwIL3JDkcYVtqnPtnFf3D/8AB2x4Mmvf2fPhJ8StLkbOlXl5pzyMPmDsqyDn14OK/iK0L4zW9zAun+PbUX6Ku1ZtoaReBjO77w65wQfQmv8AQDw8r8+VJo/Fs5jy12jzm68PeM/BmoZkjlt5EG4OhO3HXqDj869N8JfHvWrK7SDxan9oWwwuV+WQfj0Nem6Jplx4k0WW28AaglxE7BpLKRwySD02vtdcdMjNeUeL/AthHP8AZLqzk0K+A4R/nt5Semxx93J9eK+2R4J9baH4s8K+NZpr3QL4SXEiqXhJG5UHGMYzkVleJLWfTXGxG2OD+7zkFiOG+uMmvgCSDWfDt/vuJGtbiAhkwDzjoQRxX0f8OvjmbmA6J42cy+YcCduCKYG1Pr83iTQZPB/icgRMxihbPGc/KfrXzPq9jqfgrX2tLslZrc/JtPcdCCP1r628Q6Fp2owGTSZPOspuhPVWPcV4f4r0sm2Oh3+GlT/VXDeg7GgDc0b4hS+NYEsNQCpqAUp5xbiQHovPGa8p0ZH0j4i2IkO0w30ROOwDg1xbm4sbgrEQrJzkd66rW9b/ALTms9ZXidCA3POV7/jSmrxaLpysz/aK/Zp8UN4p/ZL8B+JUeN/tGi2j7n5IzEnOPpXqcmv2tzYiK4kVnABkB/jToCP518Bf8ElfFsfjf/gmb8GvEOoBJpU0WFd8mMZDMu0E8ZwK/Qe50a/kQN5kFpFI2RGhOTnuRgc1/AniJg+TG1Ldz9UyWt7qTOXn1b7bei30j5YJmGxhxuA6qa0Jdcup822iReRGpO4qpG9geelVovDxEU0dtdK0+5dxGd4AOflzgDI75rmGm1LUnmWC48tbcsmXJDYz04GCfrX53Sn71j6WST0N1ks101tQlb7JEX2zyTbh5noBluh61/Mr/wAHUnh+28V/8E8vDviXTlAXRNdjddoOAs6FOrc8kZr+la6mt3cW5aXzY937yVQwVeASO2GBx6ivxH/4OMtIXxh/wSY8b3unxnFlc2dxiVTvwk4UsCeNpz8uO1fr/hhi5QzCkvNfmfL8QU70j/OO8BeKLuK3UN8rELt+oxk19/8Awl8SRq1vHCoERyXmblVBxxzwOe56V+W3hO+KiNjkgKDyeRzzxX1p8LtZkW5NtdXT/ZpAD5anAyD39hX9tRSadz8ti2pM/TG6n1G70efQLxVlsSBGp3Ep6Fy3T0wR07V+gX/BOP8A4K2/Gn/gnvr8fgTxhHL4s+FV5Nl1f57mwJOHaNmJwh/unr2r8ufCF/Pd26abdSb3xhY1YFNmehr0HVNJ1kmM24zNIgPlsw2YXnDDqeOgPFcGY5bRxcOSvG5thsTOm/dZ/ou/s/ftMfAP9sHwIvxE/Z+8QQ6xby/PJAG2zwt/zzKHDKQfXg9ieleqamU0+ylknO2UjvjByc9ucgZr/Mq8BfE74xfs0+Lrf4r/ALPPiS68Ja1FIdyREiGfbJhklUfKFPv2r99/2Of+Dnzwyb6LwZ+3n4Xm0++wITr+koHQgjHmNCxB5x1Qnk9K/njivwqm5Oph46H3mXZ9paZ/WBDcSKIbWFS0U7FcjkAHFWr+2aSJlXaLeIkBVPzZHfFfNXwN/bN/Ys/ag0ODUvgN8SdI1K4cc29xMtvec9AIpNh3H8R719QT6VrtzAmoW9o0gHyZDJIxUfxH5yMdxX4fmvBeMoX5oM+lo5pBrUyYNNuJLQTLlIuoJ4Ofaq039o2pDJ8gI5j7n3Ndo2l6lAA7gtKyDblBsx/tdeay7mx1O4vZLG5URxrt2ueSx9FP8NfO0skrS3Vj0I4mD6lLT9WWVfKVvIiLZfJIJIHqe1Y1xrP2vVJJLtCAqkLE+PnXHDDHXNWIdNuU1Wa0mifY4Vlznk9OTg8AcD35rQ1bwrqUkkL21tKnlKd+CoQnr8pPNdMMjrOWiuRLFQXUwJY5TKIbdHnaZFxt6IOPlNc9mW3uI76VPLS1kY+QfvNzyP0rO8eeOPhJ8LdObVfiT4q0bwvG67pf7TvI4pAo5yqgnJ/Gvxv/AGqv+DhL/gmt+zi89tpGs3vxD1SFCqWmmIPsxccjMzEDk+mcelfWZV4f43ESXJTPNxWd0aez1P3EgtNZ13xFHHpRZY7tQ00efmQRd/x718Y/tbf8FEP2K/8Agn7pk+q/tF+L7WfWbnm10e0kWW5cg8ZRMlSe5fA+tfw5ftp/8HO37av7Qct74a+ATr8M/D9ySo+xMGvihGNrXGM8juor+cvxJ8QPFnjXxhJ438balPq+o3EwnmuLyRpnkYHJ3Mctya/eOF/BiNNKrjdH2PmMfxbKScKZ/ah+2n/wVZ/aI/b4juPDHgZp/h74C4eKzibbc3sWRteRgAcsOQpO3FflTd6Tovh+FUEM042sShyZZTkfO5PT/gPHNcB8CfiLdeLPBFrrKzfaiioTEchl4x8pPHTgivWPE1019ZnU5jmVhw5IG0f3SK/Z8ryGhhIqNJWsfI1cTObvJngeqC5tUMKwAXUauY4+uC/3c++P5V4drBisbmLU5CWeL7vJxuP3gc8cGvZfE82pODMJnUxDAkIOIt33SpHGeK8S8UatbtGscJLsMhgcjk9Tz1z1r3+ZXucU9z1P4BeNbvwv8SI7ydlP2qVXynKq3B7dCPav9NX9ia/l/aZ/Zj8E/EbT51IitWs5g3HMA2An1ORX+WT4K1K40zVIoLVQVlOfNIw6Y6hR79q/0TP+DcT4w6h4v/Z21b4dasyE6VMk8ABGSsg+bI9c8189nfD2Hx8eWvsdOFxcqXwn7YXHwJn1JFS+njQAYO3PI/CtGx/Z08HWJF5cSOxU7iBjBP0r6GG5ZM1IWJ4NeRh+AMsg7+zudTzrE9JHj9l8FPBlkjpKjSq42/OeAB6Curs/h94S0uFY7exjOBgEjPSu0HUVKUBOa9SHC+X09YUUYVMyrzXvSOC1n4deEvEWhz6Df2MQguBhtoGQw6MOOo9etfn945+Dnij4P3TalZE3elB/3bqfmRT2ceg9a/UAccVTvbO3vbd7e5jEqOMMjdCD25r1qdGnTVqasjl9q3ufBnw9+K00YWKGTzQMcA8e+a+r9J1y31WKO708/Mw/eY7V5D4x/Z8js7ptX8DN5QyWNsT8uepwT29qwPD/AInmsgdOnQ2t0hCshGMkfXqK6U7kydz63tdQSYbpBhk4auD8baQcJqUH3XG1vxrK0fxEbrAkyroPxNdrDcWOpWhtJ2O1vXqPpTJPIfDGnO1/NpLHyo5TvLdgfb3r2Dw3e72fS5yGaLlT6r0rhdY8PXGnX6TurNbp0bNdHphW3v4r8kL2wO+RjmtFU92zHdno4AHSio3xLEWB4PIp4xjI5pWTVxNsXYTzRsH940gkI4FSBmA6Vny3QAI+e1S1WJ4O3qKQy4jyxzUKSQou5Odo5IqLam8lQBx/jUayADNQT3MajczgAepFOVWEVeTL5dbH8H3/AAdv/sg2dz8TPh5+0z4Z09Y7q+J06+nQbQyQYZd+31UsOeoFfx4fDPxRJ4J8Q3XgvULg28YnElpLziCdWOwA9kfoSK/1uf8Agpf+yT4Y/bi/Zb1z4MTXdrZ6rMon064mIwlzEdyA+ivjaT2Br/ML+N//AAS5/bkm+ImoeFfBfw012+utOuXs5rmC1leCZ4n4ZXAwR3z6Vx1s0w0PiqI1jhpvofsP+zH8a1+Mngm1/taQ2up2si/a416AxrhHUej/AMzXs/i/WtNk1JLy8njeTDoocbXVApKnC9SWGfm9K+VP2Lf+CW3/AAVU8N6nBqvibwNY6dbTMizS3l3HbyNGFxtdAzEjHH3a/cjTP+CZnx78R6f5Piy80jS2JBjImNwY/YbUzgV5GI4vwFN6zOunlVaWyPyY/smawvYfFutXbuLQpf3AfChiw2pFGB6hecVd8deFdK8a+F7kaepg0uyha5nRV2ujOCyJGO5PBNftNb/8EkdH1G3tNI8S+OoikB8/ZDbEoJvqSCQO2fWvcfAX/BNX4JeBYRHfalqGoRNL50sYKLG79CcZJb24rx63iRlkHbmbO2lw7Xl0P5NPhX8XLXwvqr2niGcSNNKqRDOGxjClh/s969n/AGivh7F8SPAmoWN5E8c+qWji2kzm2aRELqwPY/L0r+mFP+CV/wCwc3itvG99oGqXGqOS3NwqpnOeAvT8q+jfDP7MP7OXhjS08P2fgrTZ7ZSCE1EtdbeODg8cDsOa8TEeL2Ch/Dj956EeEKj+Jn+U3qb3OjXX2bULWWIqzrg5Ykgkf0z9Ks2WneItVTzdG0q6uSegC9foBzX+px4h/Y5/Yz8SalbX+ufCjwpNNZ58thYBUwfUDqc+or0/wt8HfgP4WZIvA3w/8N6OYznzLXTo1YAdcYWvHreNUUrwj/X3HVS4Md9Wz/Le8Hfsw/tT+O5F/wCEP+H2rXe8ZybSdlx9dv8AI19beBf+COH/AAUz+KKC58P/AA7vbdOAC8RiXn3k/wAa/wBNS08VaraRfZtDn+yxKML5cKL+GAKxtc8aeIrlo7U3sokHWQEoQP8AgNeNX8a8Q1eGh6dPhKKVmz+ADwH/AMGyn/BTrxqqzeIrOLREfr59xGm38s19aeFP+DST4/uyz+P/AB9pljkZc72b9cY/Kv7P59bvzbiFpJGA+9M7ljz3PPeudFnFqN9bPb2EckwcgTnLFQfvEFj1r5nG+MONk/dkd9HhWC3P5i/An/Bp/wDAu30y/f4g/E3+0b62tnmigsM5LIpbDFskjIr+MnxGtxpfj7xD4MmAMeiXslpExBUlI3ZBn3wtf7APh1rdNRktrTe/7meKSR1ALlUyMe1f5K/7UfhtfCf7XfxO8PKPLaPUrhgCONvnkn+dfqvhhxRiMdOaryufL8Q5TCgrRPFsKPnPA9Qcj8aVmZiGP4nsPpQY1wyJyuBuwMcYoOR96v1xxsz4+UbArqcr1Pp2qTzFX5sVF39PpS4XsuKRArcfMSBn1pjzFk4wQtLSH7tACLnaM07AqIEKOSeaYw5K9xyDQBIEYHP+f51HdcWkuP7jfyqQOc4NMusfZ5dq/wAB/lW1L4GL7SP6if8Aghbx8C58f89G/mK/RrwL/wApXvhp/wBc5v8A0CSvzu/4IVoF+BsrD+KZ/wD0Kv0Y8BoW/wCCr/wz/wB2X/0B6/y38SJW4jxP+KX5M/vbIan/AAi2/un9H3xA/wCRF8Q4/wCfG5/9FvX8ujHP7P8A8FCep8W3X/odf1JfEZM+DPEQz/y5XP8A6Lav5cMY+AXwX/7Gy5/9Dr8tkv30UbcMvmhPz/yP6vdK/wCQPpf/AFyi/mK+BfGX/I36r/1+T/8Aoxq+/tI50XSz/wBM4v5ivz68Z/8AI4at/wBfk/8A6Mav628JValV/wC3f1PwjjP+LH5/mf/W/rgMijTbwHtFJ/I1/K54/Oz9nj4pueg8WWef1r+pt+dNvT/0yf8A9BNfyyfEQbv2c/it7+LbQfzr/IfinTFx+Z/ePA6/ifI/dnxZ83/BNPWFHUeBZB/5JV/MH+wicfAjSgP+es5/NzX9PfinCf8ABNnWh1/4oaT/ANI6/mE/YQG74EaSR/fm/wDQzXs0X/wmr/HH9Tfg5f7TifmfkV/wViWKb4p2Fvc/clco30YYr+fDU7ZrLUZ7NxgxOy/ka/oC/wCCuTunxItHi4ZXwPxxX4XfEm0itPEk7xcCQ78fXrX+hPgtG+QU2fy94tf8jeX9dDgKKVuGA9aXaSTjnFfq7PygbRRRSAKKKKACiiigAooooAKchAPNNooAspIg61saYBOTiufHWtnTJQrYBxiqgrsDfvJRatbzrnEUitx+tf6+P7A/jKTxx+wX8IPGVowmddIgifPIO2ELg/lX+QHf3Ae2x7jP0zX+qp/wRU8TN4t/4JI/Dm6hlwLMvCzjqArYxX414y0+bAwnbufU8L13Gqfp3eanYanE0V3AZHBKlxx5SE8j3rOubOygso4lVZ7eP90gU5OBgbyf501LFFjmurdyVd9hB7+5FSXVpGkJvNNt2V1+V4hkDcOCQPQnmv4jqwbm9D9cp10lYu2drq9prIs7sLPLg7P7roOdtbdh4Otr69lvLp/KidgXgGCIGB4NY3hi11YX7RgG5IO7BOSu4cAH+lelLbyaZKdO0hU+0TyCa4VzklSePyrqy+D9qk1oc+KqXWh/OJ/wdT+Ak1T/AIJmaVraxHzNG8UR/NgDKyQSAn8wK/zN3Q5JHbFf6yX/AAXy8ES/Ef8A4JYfEe61EC6bQrlb1G4+6hx8v0DV/lq6Rp/wr8Q2lta3s0mlXMaeXK5+ZHfJ+fnp9K/unwnxCeXumlsfj2fO1a55Np+q3+lzpdaa7QzxnIkQkH/Cvovw98dLnWbYaH46RLq3ACqXAJzn16iqNt8FfCept5thrqyRjHIC8/qP5VS1X4RaLpalodTWU44GF/xr9Ne54aPU9T8BeF/E2gO2jTC4RuUDn95ExPY91r5Q8S+GdV8MXpstTXkH745B9CDXZWeraj4duDHHcbF+6dp4IFehTa/pvj3QzoOpbBIo3JIeuRxjP40gPP8AwD8TdR8MyLbag7XFr90IegB4yD7V6P4itoNQshe27mWDllY9cHpXzrq2mXmkXD2eooVYcDHQ+hFdT4P8YXGhy/YrwmS2lG3B5C5oA5LVIWiv2TBxjiqILBQp6A5rufHOk/Zb2O8ib91OPlxXENgcDnNNW6hfU/1jf+DdXxRB4v8A+CS/gmDUh9pbTXltkB+bGxsqMf8AAq/Xi8kit9TmivGV23AxsxIUZ6jb2Ir+Nz/g30/4Kx/sV/ssf8E5L74XftN+OrHQdWt9ZuHgs5ZGE5gZU2sgRWPWvvj4j/8AByv/AMErPCdrO2nSXniOTIfNmsku8jjgy7Pyr+VuOeAsbjMXOVGF02fe5ZmcKcVc/oB1jXZLy7eztrZWlJwSC2flxhiRxXPTTuHW/wBVjaR4MxtGN5MnbGB0A/Wv5U/Ff/B3p+y9pHmR/Dz4cardMOI2uI7dBx/wNjXyR8SP+Dxv4yanG1r8PvhrZWqZOx552B9vuf0rx8D4LZhLaB6lbiqlA/uX0W01cTJaanZTXFlMN8e2NsIWH3W9scY4r8+v+CwPwr1Px7/wTL+LfhWCwYRw6TJPCskgLlIMSk4bn5cHA9K/iT8ff8HXv/BRHxHDJbeFE0/QVc/8sleU/m5NfAvxr/4Lx/8ABTT4+eFdR8CePfiFO+jarDJbXNtDFFEHilG1kLKu7BB9a/Q+GfCbEYWvGtUa91ng5hxDGtHlR+VuhX5gZIFONhODjJIPIzmvofwVrrRzbM7GUZZjjDDqQQK+VrFtswlc89z79K9m8LahHIzZ5Hyg/Tv/ACr92sfJT6s/ST4Y+INElWLWHzFGMFkhb5tw6E57CvryHxF54j1G5cxwyYDIfvM2MDHp64r8wPA2vR2d9A9kB1A2k8M3YfT1r7c+H+vanDqFxHdH7VeXKZBYApEw6Be2MVq6SaMT0HxNYXV/bX7y25lgmO0yMvBJJPA7kdgOh7mvhH4k+H3u2eKWIulmhP73LEgA7sdMccZr9Dm1uPUkgW9IMNtjdGuf9cuDkY4yeleC/ELSdQ163n1Ca2EC2v3lXhjnsPUHvUOFlZDi2ndH5fi68S+EtTjv/B2p3WmzIoczQSsrBiT8wIwwxjHFfV/wt/4Ky/8ABRL9nm9jT4bfEzVSkIAUXMhukI9Cs24fpXmXjfw1YPd+dbKI5Cu50GMZxwMg18167pOy9L8LuGcdP8awr5fQqq1SCN44uotmfvB4W/4Oh/8Agqx4Zt0h1rX7HVguD++s4U6dsxqpr0iP/g7E/wCCjqK6SwaTudGAKwnIJPB5J6V/NfcWjxqfmyaw5IiFLEYJry3wjlj1dJGix9VdT+ijxF/wdPf8FQdWtFg07WbCwmzjzUtUY49MMCD+NfDfxf8A+C33/BTH42209l4v+JuoRQTk7o7PbbAg+8QUj8K/KKZSp5FV1UseK6aHC2X03eNJFPMKr3Z7L4t+OPxc+Jd2bzx/4n1TVW6f6TcySnB7DeWH61ynlxf2XIcBzgktJy2T39K5eMbV3DqOlbMTvLburnnGT716kaNGHuwgkZupJu9zlcM7E9ag8t89Ksq5jJA5qXzGK1Vibvqfo7+wv40QW0/huY/vYHxACxA/engHvgGv0E1W40Wz+1WutRPNKF3tgnaXxwv0r8Nfgb4tn8I/ESyniYrDPIsbDucnj9a/bjVxbQ+Hba5t4/OVo8ynqwx1FMiUrHkWoT392vlQkwfaU2mDqgX1NeGeIftmmXklpHKJYFO0EAZ/OvaNf+02lyo3Am7UCPac7FPY+h9q8X8YscecRhd2wBTyCOpNBm3c5ONjBeQzWxber7iXOR9DX9l3/Bsh8QYIfjje+HDKY21HT5WKdEYqFcYHtyK/jKtpDOQqZLLzJ7iv6Df+CHPxTufAX7Z/gm5EzQ2t1dR2JOSAVl/dkH86BH+lpKeCR/nFRRtzzxTywdd2epz+BpPKBGc+9JzX9Mpxsr2JlHftUjOqjLGqclxBCo3Nj64rGvde0i3X/SbiNP8AgQ/xrjlmdGm/3kkaQpc3wnTiWEjOajWWNhlTmvK7z4g+DLMkXOpwrzjAJJrf0/VLbUrBdR0qYSQvnaw74qIZjh6s+WlK5bws0rtHalldSOSPauW1/wAFaF4kgKalbhmboy8MMehFCXtxH0Oa2oNUXb+8Oa70raHMeOt8MtU0MvJo100qfwRv1H41rWVtrlqgN5EzsvJAH3q9QfUo26HilQxzfMp6+tV0bNFA5ux1W11JHtLw5DDJjJGVFYk8drpz+XLPEIlbKsTgqPQ1nfFvQ7e/8H3k8L+RPCuRIhKnA7Ejrmvh+1upbixhHmtlRhiCc5z3yfaviOKuMY5ZJc0b3R6OAy/275UfoM/jXwlawqkuow5HUbuaxbr4t+CLTIN2Hx/cr4PaJGJ3cn1qv9iiJ6V+a4nxeqOV4RsfRUuFU9eY+1bn47+DYc+UJXP0rmdW/aK0y2hLWFo7n/aOK+U1tFQZ5NV7iBHBU845rx5+KeIrVOWWiOuHC8Y/Efevwv8AiFc+PbC5uriAQvC+0AHIIIzXI/HHxZ4p8KWlnJ4fufswk3CT5Q3PUcmud/ZvdxaahH3DIf0xW7+0PbtN4ZgmYdJ9v0BFfqkM4q1MmeJg7M+ZjhoxxapW0ufOl/8AEjxvfwKj6jMzY5wQoJ/CuXfXPEc/Nzcyc/7ZNQbFibbGOP8ADinyHsa/nbMeLsVzcrmz9GoZTRSvylRrq5llEk0rMV/vc/lUg17UIEYQSFOucEZY+59MdVxiomWIn5qozon8Ar5rE8R1L6tnbHAU19kkbU724XLszH36CqZeQne3PtjFOikfYVAqMy5baa8etnVSts2ejRy6N7IUHIZWwN5HI7GrKA52yMWPc+v4VSc4wen+frU8UikDYdzjrXBUzKtHZnbPApLU0oYlZvLB47Z7H1q1dIsEeZtrSf3wKxjJI2dvWpFmjlQrcMQRXHUzKq/ikZwoRjrEhKJISsvRu9aVvqLLnTbbCKAQX7mqbS2iR/KdzY4qkL6APskQFjwPrXPPMJt7nVCm3qX/AD4bZjMrAuBjnp9ap4WcMImDM+BkjoSelAgsREY5VCOT3J70z+zpbN1O5SC4IwewrKWIlLVmyw66kaWF1fmQJLgRsBIMDGP610i2DWdwlx9rAtyPkjUc7u5z2qhNpM7Qm3a8SPOHJQA5HYfWt1LSG3tIZoJgsTDgHGcD1B6Zpwk9zGtG2xneHXvT4gskgLsJpZo2kP3cNGcfma/zE/8AgrX4V/4V/wD8FSvij4VjTy4bm9l2DH95Q9f6fdh4geHW9OhmH7hLmOMRKM5BO3JxX+cr/wAHDfhqz8Kf8FYte1aRyn9qKs59j5ezH6V/Tnglif8AaHHuj874yo2hzH47rJlBng7FH44prlFjLkMcdSpxWO17HFEpByNvXOeRxWNNqV2pG04wpZT157j8q/pma6n5k5XOwEiB8k4G3PPpUbXEakBiBnvXCrqc8qq0Tb1Yck9vrUb3c0gLk5JGBjpntWZJ6GJEZCVOe1CyL5f0ribXV7iFcrgBVyc98dcVqReIraZgsgKnqOOCD70AdEJBGdpwSajYEMV/GsMaxarKEfqe9LLrdvgkHGFoA3EUxE7xkGm3Mi+RIc8BG/lXLtrZkHyPnIzWTc6jM8bjPVT/ACral8DJ+0j+s7/ghXIp+BTEf89X/wDQq/SH4fMG/wCCrvw1I7JL/wCgPX5qf8EIlZ/gOx/6ayD8jn+lfpR8OBu/4Ku/DcdP3Up/8cev8t/Exf8AGR4r/FL9T+88jf8Awi3/ALn6H9InxE58FeIXHQ2Vz/6Lev5b2/5IF8F/+xsuf/Q6/qP8fnPgTxB/15XP/ot6/lwb/kgXwX/7Gy5/9Dr8tl/GgdPC+il/XQ/q/wBF/wCQJpg/6ZxfoRX59eM/+Rw1b/r8n/8ARjV+gui/8gXTP+ucf8xX59eM/wDkcNW/6/J//RjV/XHhP/Cq/wDbv6n4Txn/ABY/P9D/1/6z0kEmm3+7tCx4+hr+W34hH/jHD4rN/wBTbafyNf1ERMv9lX5/6YN/I1/Ln8QD/wAY3/FQf9TbafyNf5BcRVObFL5n968FRsqnyP3T8WMR/wAE39ZTt/whEg/8kzX8x/7Ax3/AfSg39+f9HNf02eLGz/wTj1kf9STJ/wCkZr+ZH9gT/khGlf8AXSf/ANDNe3Rf/CZ/2/H8pHocFU08TiLrufkF/wAFaEV/ibag/wDPT+lfi/8AFDTo5dLTViMMH2mv2g/4Kx8/FSzB/wCep/lX48fEsgeFHB7XAH4Yr/RDwUiv7Civ66n8peLq/wCFaX9dD5xTa3zScYpckZxxmmxgMeemaWv1I/JwooooAKKKKACiiigAooooAKKKKAFCtngiti3iCKD/ABe1Y8IyQT1rWhnIwpFOe+gEk254XU9hX+mX/wAG2Pi9vFH/AASpOmytvOkX0q7CcAb5BgA9uelf5nKESt5eM7sj05I4r+nX/gkH/wAF5fh7/wAEzf2YfEHwL8X+CrjxVe6jdi5gKXAjiGCCA2c5wRnIr5DjfJJY/BRpU1qetk+JdKem5/oMukr2rSxJiTcEKjOQOxOB1HevW7HRLRbKKV2a7uhhlaLJABH8YIHFfwxa3/weA/FDEsfw0+GFlZTS9GuH8/kdOiqa+QPiF/wdSf8ABSnVBLqGgWGjaLCxC/8AHnuOPQ7mOa/AqHg7i5SalFH2dTiVR0kz/RjtNEukunm0G2K7m3Tscpx325z1ps+kNYySX1zeQK84IbzX2lEAPBbv+AFf5aPxa/4L3/8ABVnxfo8Oov8AESfRbS8BQLparBgjk9ORxXwL41/4KTft4/EB3m8XfFbxNdo/DK2oTKuPTAbFe3hfAurzJuaRxz4qTR/qJf8ABULUPhVaf8E6Pi/4GufEmkQy6nocr2dq13GZDLgbuGbcc+3pX+RFeWU7yTSLFvSN2BdR8vXPWvWZ/ip4u+Jkklp8R/EWo3M8uFjmuJ5JFyez5J4PFcDcJrHhK7fTrsF4ic4BzG46ZFftXCPD6yuj7GTu2fLZhiFiJcyORNxcRSN9mJCsSeDUkE9/5mNzH61ry6jZSSBygX2HH8qbHeWm/cRX07PLJGgadB5nJPWuk0yI2ar5Z+tc59stlcMh4q0NS2sAvQ0gN/X4DrduXTmSEbvrXmg8xcj7pPOK72zvZIpg+d27qK5/XLGMSm7gORnkUAC6hNe2H9nai5+TmMmufyY32jmmq0gfI52mlPJ3UAP3knJ7UeY3UdfXvTKKFpsVzvYlBUkk1KJcHcuB+VVaKrmZJLJK8h5NMX71NpVODmk2NOxpW4BIzXZaVOUcLAdp7muKt5MH5a3baRlZWGRmpshuTPfvDus3VkyTOR8vKnsCe45619bfDfxfcSRyafI24fLKhDYbd3JPp7V8I6ZczQoobleOPSvo/wAI6pap5bznaqgZ29SPX88CquSfo74D8RWt156XoZoYo8s6naGfnDe9dLe6bHPp3mhybg7tgYfKUPPJz1r58+Evii00yKN9duVKZI8vA6dlbI/U177M9rdwXOrwAPEikIDlVw3THrjk/QCkB8o/Fjwzb6akT/Z1RixZQh3OcHncPQ18N+KNHvhemSSJ9sZOODkDPGcV+o3xBsv9FDRlZXVPMkIHVCcfKR3FfEXxPtbTSLf+0nkKwXALwqWJlkVuAAFyAQc9RVprq0XBN6JHyrfQwK5idgCOrA5GfT1rjb5EinBLEDGSrDBOfSv05/Za/wCCbX7Zf7cmpLZ/AXwJcyWCBS2oagptoAG/iEhCqfXoa/oN+Av/AAaW30cdrrH7XnxEW1dsFrDTACwOeVExzn04X6Gvnc04pwGDv7eovRHfSymtPZH8TclzbOdrkg49O+fx7UyO0u7hj5ETkj+6N3Wv9O34P/8ABvr/AMEsfhHbR29/4Tl8USxEMZtRlkl3MPUBkH6V95eEv2AP+CefgS2W38J/BrwwoXHzy2KSNkepbca+LxvjFgKb/dRbPXo8J4hvXQ/yMo/DPiiZhHDZTuW/uoxP5AV1Fp4K8dwwkyaLeBR/E0Tgfqtf6/tp8BP2cNPWNtJ+Gnhy3Cn5dlhEpUf98DBrbb4a/BooEu/A2iSxHgqbKNh/6Ca8yfjTQ6wOx8I10rtn+NtdeHtdtZCLm0lj7/Mh4/GqG1QDHISrDrxx/Mfyr/Y6179ln9jfxdZvF4l+EPhe9DjDFrCFWP8A44DXxl8WP+CLH/BKj4zWjw658LbPQHnBHn6UXt2Un/rkcZ/Cu3CeMGDm7Tic9XhqrFXP8pSxun0/UIL62f54XWRSOxU55r9xPhP4gbxB8PYb5HF25jD3Ck4kDEcbfXPXpX70/tPf8GjvgDxJa3PiT9jzx+1pMFLR6Zq6M+4noqyjB9snNfihq/7En7a37A91N4I/aO8FXVrp8ZYW+sWsRubfAPUyoCoXjgHBr7nLeLsBil+7mjxsTlVeD95HjuuwPHZmKBjJ++81yPvpzwP5Z/pXj3ia2ltUldkKy7SSHGMZ/HrXrWqRWtxqzanp1wJEZT5gjf7zEcZVvmGMV414jf7Vuu9RkZpZePmXO3HbmvoVUjbR3PMlFp2Z51aXtzb3CymT/WNhsjGRX9Bv/BBf4M+Gv2j/ANqlfDXi3V59NuPDKSavZNabS0klqfMVX3ZwpODxztr+fCdyPlGMBgBwOpr98/8Ag3m8YSeDf2/bLT0mONTsbi3BZicmSLjGc+navAz7EVqWGqVaXQ6cDBSqqLP7/Ln44eObmH7KsiQBPkDRqcnbxnknFc/L8TfH06FH1OVfy/wrjtRtfI1GaMDG2Rgf51BtYnNfy1m3G2KdRx53ofpuDyai9WjSn17xReMWvNQmlz/tEfyrMmiNx/x8sz565Y0/95jGaQ7xgKK+YrcV1pP3mz0ZZVTS91EH2aKJcIMY45J/rX3h8IY2vvA9kAfu7hgcdK+GZB+7565r7V/Z6uvP8JGLP+plZfzANfrPhhi5VsXHmPleIcP7OldHr39nP/n/APVS/wBmnuK6BQCBmjGHxX9I3ufAmJHYIhAYdaQWzLgIcVrSKS2fSm+Wp5Yc0X6GkGeH/G/xXc+FvAri3iMz3haHIGVAI5Y/0r4qtR9ls1j4yR831HX+dfoX8RbeCTwheB1DHa20EZwegxmvzpHmKzRS9c4/LpX4h4vxtCEkfZ8Ipc7Za84j56cZGdgFOKrtgR8+tIiseCa/mCp8TufodtLIvlXCZzyPSoFRi+W6twatQoOFJqN2CSFY/mwa68FVuiZrQ9//AGdtR8rW73TiD+8QH/vk4r1v43Wv2rwTIzfwTKx9hnFfP/wHmW38exxMeZ4pPx719L/F6Iy+BNQVO0e/8RzX9QcNVPbcPTh2PzPHR5camfBiSpyJOoJ/nTpGVjt6cYFUlAlhVu5AJ+tWMbAGNfzTmz5Z6H6bQXupjWRFOHHSs2aWMNtCk54GK0n+dzIOh4/GrEKwQDggu3TPrXhV5M0Wxh+XtbMoIxVZrYyZlQ4HvW3Ld2iEtqvEh6Ben6Vkz3QmfbEucDqeK5qkHGF0aqTWxWSJQPmzmopY5AAYTt9TUglKg8E5/SkeZN4hkQnAyPc15dSrLqdsHpqNdmi2k5we9OTyHYB8nJ6jio4xcopfIfPTOOKB5lzwTtzwenBHWvOqVnLqegqSfQaIY43Mjt07VWQx3VxvKlSnIq5LZjBaNsleCT3Xua5fxT4y8EfD2A3HxM17T/CunurPFd6hMkXnBPvCLeQGI6Y5r0cqy6rians6auZ1sRCjHU64RzyBplhd9oxnPAz3NV3eRMxumCuFOWyWDcAjtx35r8Efi/8A8HJ3/BP34W+ItQ8G+HdM1TxRcabM0DXCO8UMpRiCy7Oq+/SvhLxp/wAHYHw7sLyW0+F/wndyzHEs94W9ujAmv1TL/CnMqln7M+exHFOGpr3pH9dUQjggaKE7FQhgMAn6nk8GpbaLUdQkmSbfKHUlnRfyCdAfev4dPHf/AAdiftg6qJLP4b+CNG01NuFM9sZnH4nANfJHiv8A4OPP+CoXioh7bUdM0s/OQtrZRxld3QndmvqaXgfj5K8rI8evxdRezP8ARij8N3lveWF9eWsiRq8TK4IyjAg/vPQetfwLf8HYXgi28O/t9+HPFWnbTFqukq7yJyC6SkHJzyemelflb8RP+Crf/BSj4o3ctz4p+LOsQJN1it7xoUHttjIr438ffEr4s/GLWF174weJL/xZdwoVhe9uHnaPPP3pCSF9QK/WuAvDjE5VX9tNrY+PzzPViYuBwbO0bFASuCeR0OeeKiaeRWUofLIOdp5PTH61K0DFdzngDOR6ew+uaRYvIj+YKxPqcn61+tc/Mz5Ga0K5VieWP+5wKG87/dbtjkfpVooCMlPlX7xznioDcqGLxZI6DHAqjMjXz/MGWOCf7v8AnrSAMFwN2ATgAcCpDcNkDnjnrSJIzOFAb86AIjkK3LA8dqjuIw+dxbOMdKuszqdjM3qR7fWplQyAsSTjpQBlouwjA6cUryfuHA/umrflgkFc0vkgwTbx/wAsyR9a2pfAyftI/rX/AOCD5x8Ayf8AprJ/U1+knwzO/wD4Ku/DbP8Azym/SN6/Nn/ghJ8vwBcjtLJ/Wv0l+GfH/BWH4bqOnlT/APoDV/lt4m/8lJiv8UvyZ/eGSu2Sf9uH9H3xEYp4E8Q7f+fG5P8A5Dav5b1cv8AfgsT38W3X6NX9R/xI48Ea+O32G5/9FtX8tkf/ACb/APBb/sbbv/0KvzCS/ewPR4XjpL+uh/WLozEaNpo9I4/5ivz88Zc+MNVP/T5P/wCjGr7/ANHJGkaZ7xx/zWvgDxl/yN+q/wDX5P8A+jGr+tPCV/uqv/bv6n4PxsrVY/P9D//Q/q7icf2ffj/pi/8AI1/L58QP+Tc/it/2N1t/Wv6dlI+x36558l/5V/Mb8RPm/Z0+KmO/i61/rX+PGb1E8Sr+Z/f3CEX7/wAj9xfFz4/4J3axH6+CpP8A0jr+Zb9gg/8AFhdKP+3N/wChmv6Y/GB/4146uP8AqSpP/SKv5lv2B8/8KI0vH9+b/wBDNfSYd3yv/t+P5SO7hHTFV7+Z+RX/AAVjyvxSsDj/AJaH+Vfj58QYt/hS4J52Oh/HNfsX/wAFaEI+J2nj/bJ/SvyI8bRed4UvohychsfSv9EvBR/8Icf66s/k3xdT/teR8rR5DU+m5+Q5p1fqJ+ShRRRQAUUUUAFFFFABRRRQAUUUUAPjwKtxsMA9ao1Mh+XI7UDW5rI6lcetWLOZoJ8kBlHJzWZGx4zWhGMDBGc07M0lLQ9Fs5dyqYTtDdsVzfiu4nuGj0/dlUOS3b6Yq2l08doJAcMBjFc6JTcrO0rZ25Yfy/lQ73sZtdT0jwVcL4m8Fap4SuwGkgzPA/cEDnH1rxAowyG6/wD18V6P8L9UOmeJoVGNs2VYHuM1V8faAnh/xZNFGf3cpM0eOmGJOPwod1uJeRwIaSP5l+n4V22keJA1smm64n2qzA2g/wAcY7bSauSac/iTw5N4hj2LNp4CzoAFLqxwrAe2OfwrgjIY8KowAccd6VtRq5t694fk0tlubV/PtpfuSAdfY+9c5tGcAV3fhvxBEsc+h6mDJZXIwc9Ufsyk9Peub1XR7rS5tk6kxE/JIPut9D3ptMLGQqDPH+f1q4h2jJNRBArYOeBn8Kl2bhlMtj0pXCxYW5lU5R8VDLcOylGbOf1q5baNqt5n7JbSS4GfkUtx+FdNo/wv+IviW4W00LRL26kY4CxQuxJPpgVhPFUo/FJL5mv1ap2PP1yq56VPtHf6V9ueCv8AgnP+274/WKHwl8NdbvGm+5i1kycexHFe6a//AMEbv29/B3wl8QfGbx54LutE0fwxbC6vjeARuIz3Veckd+471wyz/BRkouqrvzR0Qy6s4uXK9PI/Ktkw1IVYV9bfsX/sseJP20v2jdE/Z48H3sGm6hrkjpHPckrGuxSzE49hX9PHg/8A4NQdbF2bH4g/ERYZ7dlE0dpFE4ywyoBLd+2a5M74twGX/wC9VLO1zowGT1sQr04n8Z9KATwBX99Pgj/g1m/ZQ0dlh8VeONa1OfjfAsUKlcjJYBVLYXHzc4HHqM/Yvw6/4N9P+CWPgtP7a8RaFc67DbMEY3NxMitIPURsvJxxgcCvzrFeOmSU20m2e5S4Ixk9D/Nbjsb2fAhhd8/3VJrp9F+HvjbX7yOx0jSby6llO1EiiZmY+gAHNf6s/gf9gT/gnZ8K2XTPDPwl0wWSxho5Zo47hjIOgBkBJI9SfrmvdbPwP8D/AAWsev8Ahf4caPBd+ahi/wBFt0RSpGSSkYIIHTHBryJeP2Bm7UaZ3w4BrqPNJn+RD4k8LeJfA+sS6F4t0+fTL2HHmQXMbRyDPIyrDIqjDc/lX9CP/Bzr4JtPDH/BTLX9Q0+CO3h1C0s5USFQq4MKnOB65r+d+EkMFr9ryjMo4vDRxEep8fmWH9lP2fY7+wuWMeB7V6x4Z1mNlNpN+7J43jk4PTr714XbXO3ANd74fnAkLucjaM/gcivSsecfZ/hvU5ZtPS1aD97MwSNs53k8AH6mvqay1O9sYoNNtiZI3UJdbshVVRwBxjOF5z26V+feja5Lpysl9J/ouwy7wSDHj0Pr6V++H/BKD/gmV8ZP+Cg2pw+OfG8k3hj4XaTIrz3zj95eFekcQb72R0bkKMnkivKzXOaOCp+1r/CduDwsqr5YnjX7OP7Ofxt/az8UnwL8FNFkvbpl+eZxtggjJ6lm+UAdct+Vf04fsff8EO/2PP2b/s/iz9oqOL4i+L4QHmgPNhC5z8qoy4ZQTwx69Qtfrh8H/hn8GP2f/h5a/DT4JaTBoOm2oEX2lEAmuAOGeSTlmJ7kn6V31wmgsC0O2NyTuPOWPfPtX8v8beKtWpJwoOyP03K+GoRSdi1pb6R4d0eLSPBEEGi6VagJb21nEIoQo4xgBSPbikv9Rsb9XknPOB857VjMI5f3RlDRrg7Rnio5b+CZfNSDfFFnaSOTj1HcV+K43iStWbbep9hQyyMNUjn5HmtgIgSp6qfb3rptN2P5hdiRgknPB6dq4+9v/wC0LhrvH8IXA7VJFePFEvOVj6ivL/tF7GzpL7R6daskaus7YMpynvUUaO85WUHYOOveuMbVp3CZAwp+Q+1aVprDfaGWU4AH61cMZruZypp6HcxrGqbJDjHPXpWZqEy7eD+Ncq9/c3O8g/KOfyrPW7uZ2ErZ2jtXpwxckro5FRi2+Y6SW9VVAQ7SPu9u/H61X1i5sPEulS+H/GFjBq1hOpWW2u081XXv1z0OKz4p8H7oY9ge1TIYZEJTr713YTiGtSalF6kVsBTnGzPxX/bB/wCCEX7L/wC0sl34t+BV2fAPip8yr5WTZyN6FB9zJ7gnHpX8h37bf7Cv7WH7FmqNYfHjw7LcadvbydcswZbaRQeMsAAMj15Ff6RXmM0hRBgDvnH61Prmi+GPHvha78D/ABI0u28Q6DeoyXNpexrIm0jBxuBx7HrX7Pwr4n4mDUauqPkM14bg1eB/k4w38N/H51owkjZlIdW+6R13DHHtX6x/8Eg/G3/CN/t//DrUYF8pG1K1tJj14lcxlu3XNfZf/Ba7/gkT8Gv2DY7P9pf4Ea19l8P+Kp2iXw7cnLxyMdxFuTyyjPfp0r8xv2EtYm8JftPeA/EpPlPZ6rayMrAD5VlVsH3FfvksxhjsrqVKfVHxbwns6yS6H+mp4hIXXblkbKmRsDp1wax3kz04purXwmuY7teftMUcgI9GXNUzKiAqetfxZn8OSq15n6rlutNFxW75P9KmDccmq0KmaMleMUsa4fB6V87UqnppNaWLStlT35r6v/ZuvR9jvrLp86yY+oxXycsoHy4znp9K+i/2b7pf7ev7YH/lirfqa/a/CzG8uNpx7nyHF0P3FrH2b70nGeaYrjbUZkUMSxx6V/WrPypMnwKry9cCkknRR8xrOFyZJQY+SWx+FOzGeJ/HvxbF4b8Nx2sUoE9y4RY88mvju6idrhnmXy3YgkfUV1P7RHiWzvPiAuxhNLaMIok7K/ckVyd7He2U6x6i4ed4w745Az0x+Ffk3i3RUsHGXY+z4VTVVtkLwEe9MXcrcU0zttGKZHIS21R171/IGLlaoz9KhsXWSWQbo80iSRRhC33s80+W3v4oVlh5TB5zXNyy3ccm+QjFZUa+u5qqbPUPhlqqWvxI05o+AWK/gxr7g+IEH2vwZqMA5Jt3P6V+eXg1/I8XaXeTNjbcIv5sK/S67gt9SspLOY/JOpVsehr+q/CtSxOXVqS/rQ/MeJouniVI/LaHVraOJVk6hQMe+KpTeIE35wSPav0EsfgT8OIG3tYiVuDlyTXXW3w68F2WFg023XH+wCf1rzZ+EdSs3OU7X6GseL7JKx+aVpqd1fybbaCVgPQcVpy6T451SQR6do88qeu3H41+m0HhzSbT/j1tYkx6Io/kK1oraJB8igH2AH8q7cN4NU1/EmYVeLJvWCPzItPhJ8XdVlVv7NMIzwZiMCuU+O0Hij9nP4T3Pxc8bWSapDZSKjWVsSh+Y7QS+D3r9ayADivHfj74Zm8X/CLXPD1oEMtxayBPMUMoZVLA4II7V31/BvAqk7ybZNLivEc65nofnLp2pQa14W0Xxfa8Weu2Md6EPJiV+dgbPJBOOgrR3O8nnqpUA4IJxj3rg/hNKqfBjQNKvpN/9ni5hf8A3RJ8gH+fSu/hsL1rL99jzZCVTcfTrnHtX8k5/l6oYmdKOyZ+tZdiXKkpixQ2VxGfLucMOTxVCC73GQQDevXPf61sS+HHgsY47TPJ3SN9OwNUvtKab5t1ZWoIkUIueSvqa+YlCzPYjK+w8y/ZSiycqwKKO5Uj/GvxM/4OFdB0TxV+xh4c8XXdo7tpsjwQMh4Te3O78Vr9k9bvYlS0ihQXDW4Msj5wMnjaMV+ef/BVTw/b+JP+CdWs213ALiBL7dGcZKODuI5r9D8O6ijj4NvdnhcSQ/cOR/mr/EXS7K0+IWqtawoiyFCyYBUBgOnpXNqJLZSLcqgbjgYrsviHAx8e3qAMAdpI9QOlcnKgySyk55A7jNf31g3ywSP5+re9q2VGkuwcLMVxycd6ga3VAHZeDwTnnNaccQPGN1QMBt56YzXc5GdNFaCN8EofzpRuCndzVjB6hgB0x70JBIy4bjnv1/KsnUbJmropSxZbjpjJJ65quYN255xyPT0PFaLRNvbzTgZx9Qf/AK4p5in8ggkAgfieckVI4xsjCaEDaqJt6/N649qYqCQ5bP4gYq9IFZfl+XHK+3rUkSheRgF+Bn19aBmSUOC/ocVMEBOQOlaISJnIxw/BBzjcOv500KsZDbBk8HHpQBnk/KZF4xgcd6uBC0ZLcFemKlECAGMdfSpAEjb5vutk0ARpFiTBPHr6/hSOjfZ5SOnlGrQVi5Gac8e20lb0iYVtR+BmM0+ePqf1c/8ABCBgPgLID/z3f+dfpJ8MBv8A+Csvw4/65Tf+gNX5r/8ABCP/AJIRKf8Apq3/AKFX6V/Cvn/grR8OSP8AnnOf/HGr/LnxIX/GR4n/ABS/Jn945T/yI/8Atw/pF+JMf/FDeIvawuv/AEW1fywgEfs//Bb/ALG27/8AQq/ql+Jf/IjeIfewuv1jav5YQpb9n74LY/6G27/9Cr8vqK1SJ2cKP3Zf10P6utN40rS8f3I/5ivgDxl/yN+q/wDX5P8A+jGr7/03/kFaUPVI/wCYr4B8YqT4u1UjveT/APoxq/rHwk/hVf8At39T8N40f72Pz/M//9H+qKKQvDfL/wBMX/rX8y3xAYH9nT4pD/qbrX+tf0uW7/ub4+sLn9DX80Pjtd/7OXxRb/qbbb+tf405lVvikvU/0K4SWkvRH7geMHB/4J6auPTwVJ/6Rmv5nf2BR/xYnTB6GY/+PGv6WvF7E/8ABPbVwOp8FyD/AMkzX81X7BSbfgTpa5/im/8AQzX1eAknlbX9+P5SNOGYP6xX9H+aPyN/4K0uB8T9Oz/fx+lfk7qFst3bXNpJ0libH196/V7/AIK5usPxN00n+9n9K/Kxl3OGBr/RnwTssih/XVn8meMFRf2xP5nxvNG0UjxN1DEYpK7Hxxpi6f4mliQYWX5h+PNcgwwcV+pH5INooooAKKKKACiiigAooooAKKKKACpo/umoamj4U0DW5Ikjxt2IrSWXIX1JxWWRwDX2h/wT9+EHw8/aE/bA8BfBP4pNcJofiXVYLG5a1cJKqyHGVZhgGscZiY0qLqS2Wp2UMMqk1A+TmvcxsCe3y56D6YqjZ/aZWkWNGLOpGVGefev9HIf8ECf+CY/w41qfwvf6Vq1wy3Qjt5b5/MWXb/cZQAQT9M17d4M/4Js/sK+Cb24TR/hXpbrbM4c3EasdijIOMkknuOor8VzLxzy3Dt+42z7mhwBWmk1Lc/zO9G8GeMdRvY00nTru4mYgxiOJyT9MD8q+lR+zd+0L8TUt9N0zwPq51NT+6U20o8wHqMsB0PI9q/03vhx8Hv2fvBVumt+FvhlpMFwUT7P5UC5jz13Bl3Ajr0ruNLubnX9NTU7i002y1Rbt7a322+UWPf8ALLjIO4Ac5PNfH4r6SVNJ+yo29WetT8MZX9+R/m5/Cz/glP8A8FFtfnN5oPwy1FreXMEvnhEQhgSQQzA9genXFfSnhH/g3Y/4KMeKb5f7Y8NwaNBLzFJczph/YBdxH/AgAD3r/RG1TxZf6jbanoOjXEaz6fCpS5hhEcbP/wAtSFJ5J/h9CPbFeeaRrur2vh/TrPR5rvUXsWZpPtjEuHJOZHK7QQM8Z44r5HMPpL43ekkkerhvDXDL3Ztn8ZHhL/g1l/aBvILRvG/j3RdJluSm+Aea8iAk9fkCnp1Bx719+eFv+DUz4Hp4e0/WvG/xRvLqALtnjttjFJM87cbtqgcnI471/QLdS6nLezz315EtzMoP9ogb0VQeEwTxznkd63dH1TQopTr9hHIU0ovBdwlfluoWHDRA8EluScdq+Txf0h80qK6qJHr0vDfBLoz8kvhh/wAGyX/BN7Q5Bqur63qniG2uUJi89gItqqd0i7NpwD6n047V9aH/AIIk/wDBI34a+Goryx8DQandW7CMzXLS7pHx/dJxjHfGD61+gOn6vq2kta6V4jdIFuwLxIYthMKE7xECM/fxz3HbpWfLrq6xJJcRQLtX5ZEm2goSePKUjnj7p+uc9vjavjbm9ZWeIl6HbT4EwqakkfInhr9lr9kL4ZTw618N/hjo+mWEMY/dzw5kkIOAVR0LZB5Hr9K9w0GHw3o/2i88J+GdF01UkV5Zfs0I4yDgBBwQAScivTf+EK12/luG1eERLp6mSJnOH/2duCCwwe2cV59eeD9I0XQEvpbmV7eR2FvCpLtJcMDvDLyFVVJ9+a+Wx3iLmNX4qjfzPqcPkGGtblV0Sa18VnEnl+Ghb29kgw08cSqxaQbRs4Ofm64FfNf7X2n+KPE37HfxZ8I6vNdNd6ho4ZElckSRkMTjBK5K/e556V9CWfhm61XW7SDVI4LECMt5ZKCNFjBIfkcsSMnkYrA+IPgfXPG3wp8TvaTXFzZS6dLGspb5VKxOApUKoZSw4PQnmva4K4qrVMdTlOT+JXuY5llVJUJxUVqj/N6/4JreK1+HP/BQLwRqr5Ty9YWD3Hmt5fb61/ql6R4YsbbTr3Q9QsFu7uOSK9U4KNJIEUckgYxjjk1/kpfAy+XwL+2b4ev75iosfEsBbjkbbkc4/pX+rz4w+IEtxc6br9/qUlraSWUcsJhzlmwpZGHzA56dsV/R/j7VdJ0qy6wZ+XcCYZVHOPWLZ2yeFvAdvo0ssbSQ3cjb5jkgyS5bZDu6nDHJCnsM8Vwlne3yS22g6xPG0ZdyRFubYvXLIfvPg9gfauOk8X6z4hvI7TTDb2+jQ3TXiSzjaN+VOxlzuzycYbr2NejL4i8HHRV1DVreeSdn3+XauQ3y9AA3Zh97kZ7AV/GGKzKdZ2TsfqcMByLmINK0eTQrRtK0O8ivYJmyZLn7ySdxGMHJHQdKxvFOsaBo+l+TbXDwzEHz0nBJSXtIqjJKjuBXTeNjY6f4ckTV7EW+pLEwtLeNmDIhOd5Ocb/XjrXjulXeo3ltpep3Mi31+JGChCPMKg/LG3YHPfmu/K8ZZ8nU1xGFg6R/Gz/wdTeFLy1/aQ8FfES+2NNr2joXaP7rCH5Aw6H5hzjHHSv5TElYyZPFf2Nf8HRvge+Twt8KvGl580hhu4m53eX5kxYR7hwdpzyOD2r+OVojFIAT2Ff6XeGGI9pklH0P5u4xwihi3Y2rVlYjf612umPHAxKNyBkg9dvr6VwttIFBOOetfUH7I37Ofj/9sD47+Hf2fPh3BJLqGv3SJLIoysNup/eO2OgVck819zWxcaEXVnstz5alRc5qHc/V/wD4Izf8Ex/Ef/BSH40r4g8eB9M+F3hKRJtRuGUj7Uy/N5CnuzY59BzycA/6EGgeGvD3gDwbp/w1+EWkx6b4Z0ONILaxtgVYBFwHfGAeM5PU5rwX9nb4I/Dv9jn9nrRP2YvhTYJY6PpUIhu7rhJbu7YDfI2RklyeD6ADPevoqC9ls4/sMS+S0bbs8l5BwAF5GfSv4p8UePZYzFThGVorZI/auHOGYwinJanSfYbew0iCe6mQGVgVg6tz169BWZdfZFtWuI03tk9Cc59sgVzhuXu3N35bSz+YFZXHCD2Xrx39K7HTLK3gldJW8wzt8m48L71+FLGynKzPtY4dQ90o2yoqx3Lt5SuMEnr9KzppTJJJbwbjGrYLZ4wa6jV4ILe3ZCQ67j0B2j3z6Vz8NhdXxJjkQGLBIBxkD1+tduHoSlK0UZ1ZKOr2GxQ2rIBGwRG6jmo4IIjMY5v3eOxPDV3lj4Vk1Kyn1WwHlrHw7zEJGv1PP4cV4z4x+KPwM8FQSXPjDx1omnqoyTJeQggjqMM46V9HgeFcRWV4xbPJrZpTirs6maSTJCgcnaoyM/hzVu1Fsq+TeNsxwCe9fK037cv7BdrJ5V38WtD830F5AMMOh+/W5Y/tg/saeKbqO30T4o6BOwOVR763yT9RJ/SvoI8AYxRv7N/cZ085oN6tH03bWl0i+dEQVY4+ook8m2RowdxJOcdvrXLaJ498B+I4BP4S8TaXqaAj5Le6jc5J6fKTXe6j4bv0iW/WNljf7+PmB+hHWvLxHDuJp6Si0X9cpSejOZWYRzBN2A3eteMC9uPIxswOSeKwXRPtG64GwxkAITyR61uW0vnSbBwScD6V50sBUTsEpJ6osSWr7vKI/dp1YV0OgaUt9eJDMyx2iqZJmY/KIl5Yk/QViXc0xmVLcBgPXp75r4A/4KhftTv+yR+xzrOo6RKbbxT42DaVpwB5jikH72VR14Xp6HntivseE8sq1cTCiup4+bVlGk2fyRf8Fq/2uta/bJ/bTvk0Nmk8E+AZDp1lEpzEZUO1pAMlSWIH4DrX5x/DSf7B8QtJ1hrwLcxX0LCMZDFcg5Ht+NXtV8N35ieJZzeNcyebLGqsWMjZJYnPzdce1U9A09bHUorucILm2nj3HqeWAGPp3Ff2rh8rhQwXsYdFr9x+R0sRKVVzkf6cPhe6TVvBPhzWIvmFzpNk+R7xKf5mtqFfNG9uM15V+yrqA8W/sp/DvxbneZdIt1Y5zyqBf6V6/fQ7GQRdME8fWv4m40ShiJW7n6zkz/dpkEW5S2DgdKtx8oTWe00UBAlbcCCcDqPrTPtsUsYMfyj1r4X2nY9pzjdWLG9z8o9cfnXtX7Oc81n4/nt5Cds1uQPqpzXhCykt8vPBGR7969b+C2pxxfEOyhP3pd65+q5/pX6r4aYhLMaV31PnuJoRlhpM/QlLkbc+tZlzNIfuninxKQoDc9aR4lI6V/bVWrG+5+OzppOyMgtKWyXJrTgkS3iNzMcJEpZj+FRfZz2HTmsnxXqUem+C9Uvzx5FpKwJ/3T/WtniKaV+ZEcr2PyZ+IN9d6l8Sb7xHcRH7LLKxhdTyxJwMDivRDcQrJbWKyGV3jDOx/hOM4P0r5h8KXj6xrM5mMst5I5Co2WQL6qBwDX0HbWZ2P5S/NJgOD94dsV+Q+LOOo/2fyqSvc+64eoz7G7JIqS+UDuA7jofpXQLHbtbKkZG49fWuIknkj2WKDiLC/XNatml2Szxg70JA+nrX8a4qsvaH6HCD0RfuHurJNm/euflTuM96oSwI5JmGSxzUMt1sv1nu2CnGACadf6kTCWgZDj0PSuX2lnoepRp9x+nXcUerQzRjDxSrIo+hzX6eaZcefBG4/jjVvzFfkvbXtxJL9pTGU4OOuK/VXwtIZ/D9jMB96BDn6iv6r8D8RKUpwT0PzDjmk4yXmdSG29KmjO7k1nlWJGKuIGx1r+hfI/OkraMuUittPQ0ifdFScY+7SGMU5Bz1Fc74vIXwvqDM2wC3kJY9gFOTXRY+bNcl4/ljg8EatPNjYlpKxz0wENRUV00XFNO5+QHwtTSdb+GEXiO0mMrxapeW0EMS8PJ8pGfbmvY9P0m0giWaeZmdW38/wsw+6foetfMf7GfjS2ufgdebomka38TTABP4VdFAYHHtXvOr+JpmmM1nEUjd8MzYIzjp/wDXr+B/EKCo46p6n7tw5J1KEYs6nVNatrYfZvMEygDcAehNcHPfpBcNHDJvjl/1dcve6rFbTSIDhnbIBzlz6Ci3ULBJIGCg5OG4Of8AZFflU8S7n18aLgh8Mb2trc2VsuYZWB3E8oc5P4HpXzh+25o//CQfsX+OdEc7LezzcKOucR5JHHrXumoagJLSSGCXyoXwGB4LDPVT9a5L4xaLBr37OXxA8OTK5jk0eWSNnOcnyyOM46V9rwPibYym/M8nOsPzUJX7H+Xl8adDn8MfEqSzlcGOSEMrep5zXlDxb3y/WvsD9rzwx9k12y121BIhlkt34Jwc5A/I18jzABfl7k1/ophZ81OLXZH841o2m0VAiqdpP0xTJFAbdjn09qlCqNjvwQSTnvTWOD6nOc/0q+d3sZkDdCxwecgAcn6U7uWY5z0PelVGU5TqOV9j3p67d4wvArQCBQxGD3zj9MVOVYRlj16H0z3qfbtH97nI+nepxB5cBjPzYAbNAGVcQRRjf1X1NQpaBSXH1Ga1ZI4kG0Elm6gjjFIw2fJ94joenHpQBAiKB0HLD+RzUiQLJEdw6ZPHeplXcDEgyeuParyIEfb0GOKAKLWyJEssS9R3rPkTewdlwCcY/nXQspCcflTDErqNw6c0Ac35SK2cmkk2i1mXuUb+VaU0Dxt81VJlJgkXsVIz+FdVF+64jteUbdz+q7/ghIpHwHl/67N/6FX6U/ChSP8AgrN8Ov8ArlP+ivX58/8ABDXw3f6f+z19ucZSaR2H4NX6G/CVN/8AwVl+HOeM287f+OPX+WniHOMuJMS1/NL9T+68qTWRt/3D+kb4lceB/EH/AF4XP/otq/ljg/5N++Cv/Y2Xf/oVf1RfEmPPgjxDz0sLn/0W1fytI6x/s/8AwWxzjxZd/wDoVfm2KVqsEdPCc1yT/rof1daZxpmkH/Zj/mtfA/i1CfFepn/p7m/9GN7195WMoTTNIwM/LH/Na+DfFkmfFOpnH/L1N/6Gfav6r8JXelW/7d/U/DuM1+9i/X9D/9L+oWKUC0vHX/ni38jX813jiXH7NnxRfv8A8JZan+df0cWtwWsbvJ6wP/6DX84njoAfsyfFJsf8zXbfzr/GHGSTxia8z/RbhOlaMr9kftp4tm/416au3f8A4Qx//SM1/Nt+wY4/4UZpf+9L/wChmv6NPFkuf+CemrDP/Mmv/wCklfzm/sHIq/AzTB33TH/x5q+py2snl7X9+P5SNMhhy4is/X9D8cP+Cws4j+J2nD/bP8q/LyF90YIr9Ov+CxKbviVppHXcf5CvyutbsLAozX+kXgvpkVP+urP458Xo/wDCzUXmzz34o2JaGHVEH3cqT/KvFSSfr3r6V8TpHfeH7iBgCcFh7EdK+ZgrbyPTrX6o9z8rH0UUUgCiiigAooooAKKKKACiiigAqZB8tQ1Mn3aAvbUkB/hr7J/4J6+Ko/A/7a/w08UzMEjsdfs5mY44CyD19K+N0GTXofwn1geHfijoOuHgW17FIf8AgLZrizGnz4epF9U/yO7B1LVItdz/AF7vFmjWc2vtq9lbzXUuoRW9/CcF0jZl5ZTgqpIHQ/lXNeJPD1ul9HrtrHHC0DNw/wAz75OoCeoP3eOGr0XwNrljqHw88I+MIGSSzvfDlpNNByXfEK9B3zk1Sttf0S08v/hEYlWF2MxkmYMyDGGBLB+Ryw4HSv8AK7jbnhjpwvazaP6gyeX7mLS6F7S/D2rqsGoaWyS3vLG5ul2DZj7jDv8AgM1yvifwGNUsrvXdCiMl2z+WyA7Y4WxkuB1YHkqRyO/Ne3WvivwNcWv2PVpWmkkH/Hw+Iw/OMdc856n0riNa8b2Oj6FPqSuHlmMn2eKMDYFGf9ZkZ5AwSM+o618hjIuMdJHpRxE5O3LY+eLPw0ZvEES65dzQ3MzN9muYiCkrqASjIf7w4/zz0/ivTdatXGloX8vd5Tiy+YSL95vN745IxxyK1dA1jw3davBaWpSM21tulkeTfsOW8xUyAPMA27e2M8Ht6BpGo+Cb27W2gkL2E5J86ThmfIJLKOnPrjqK8GzekmdMWlueSr4f0KPQY9WurOSBBFlWtkHltk7QssbEsMk4JHpmm3Gl2/hqzh1FZ4PPhjyY1YCSN2B2xhSOUx3966PVfGmh+TffY4WN+4HkAqDFChPBOOCSo/A151c2F3qunR3mlzreXAd3MkuSoCDLRE55K/wnHOa6ZYey2ud8XGxo6Xp/hzXpprawWU6jbIk0bTMRCwYFtyn+8vTnjNeoDwTZ2/hqTUdamkkvr6IEXAX/AFJjzhAADwQa8K8NX8NpOsNlG2dvmQpKxxtUHzBnpyeAD0r1vTtWubvRP+Eh8MX2683FJbCbnOeTtHfGMg/nxWuGo1JaRWphVkovU870fxDqGt3InkuGsv7FAha6OX8qELu3Ac53dOa17vU9Mu9TM3hMpYzxxebc4kAWaLg7lTOVc/nWPd29lptld2N/EsJvlMsscLEq0PVlJHQhsgfl0rk4tH03UPssmnwGDU2ULDNI+CkZ4BZR8uR717EMurcrbiOFRLVHcQW9n4j0uS61GOS8jkLJbI+Gug/zBwo6EL1BPUUR6oJ5p9IuJJLBY9MnsIbWU7MxogXBi4Xep5zjNc62otpGtWt5pU23VNP2q8v3om3fUdODk9s1Pogk1LxU7CO6uZ7kyK2IQw3N1BYAYGeeBjGK+g4YwVaFXmtr0OfGzUoNH+X7+0Jph+F/7bviGyQeX/ZPiJ3BP8OybcDX+nb8P57P4o/CzwZ42urUONQ0K1uvtyKXMRmKNKFxwN45ziv83P8A4KyeFr7wL/wUX+JGjX8LROusySBWG0lXO4f4V/f5+x9rQ8RfsOfBy7N44Wbw/p6XFvx+/WOE+ZtYHOVIr+uPHCDqZJhMRLfls/mkfkPA81DH16fmfZ2mxaEb0XF9AslxbSSXljbttaSdW+XDIRy64yMmulin8bXGrR2tpFaF2G4vJGFlZDlijEEAMMAAjnGKwvBl54a1vVLe51pnRJkItZwfmgKdDKo6ccE16Zq99BElvaTp5l15/wDo4gAYGNWwrMx43M3QHFfxBXVnofss1rY8MudV1DVrcwyyzXs8bs+ZRvMKAffVmPKknpkmt/4ZWdpaie5kkMc9yTGlxt2iXAwdoxxk/pXS+KdNE+rx3iQlbi3Ia4tQioVQL9wbcknacketUrfw9fXIub7w8XgsrcmWFXJGxW+XIyCMk13ZbL9+mY1bOJ/Oz/wc7/DGz039hHwb4nVIo3stX+zKkBLogfzGIDHnnriv4HU5G4nNf6Q3/Bwt8IbzVP8AglHfa1cTSXLad4gtbhVZCrIro+7PJHJ6dK/zdeR049q/0l8Ga7nksV2P5q45n/t8n0NK2OdwJxhc89MD3r+4f/g2q/ZDt/hR8FNb/bQ8U2h/tXxO507Sy0e6SCzTPnTxk8je21cjsDX8Z37Pfwk8R/Hj4x+HfhL4Xga5vNdv4LOONASxMzhO3YZ59q/1cvhP8E9P+A3wk8O/ALwnZotl4XsbeztJMn5tqnzy47kuTj61weNHE31TAfVoP3pfka8F5X7et7WS0R6v4XtNK1a0uNWjWW9tDuLLcjdIuGzlemNvb0oviviS+itbO7GyJMoUyGiGVIX+mDz+FYel2esXsX262+RuYpowSAE+6SRjGW4PPrXoXhPTLX/hH7u5uH8lIHUrM4+fIGADtIyW9ewr+DsXiXKW9z9zpUVHVFWO+t5ViYRs0sSNHCHGCjZ5Ptnrio5Ue3ZLe6kVpoQGl29Gz/CByc471veIPsrraz2qkXEsX7whQFBbG0r1Jyo5/u1g3Ns7XCWVvhBIu8NnO4gnC5wetGCp88nYeIkuXmJoNRXXZ4NOtbKQxrKxEEhOHzgEf7v9a/Lv/goD/wAFY/gP+wdb3HhK9aLxV44YDyfD1k37i0J7zyL3xztznsapf8FeP+CgkH7CXwqtvh/4AvUufij4qgKwRptY6bbE4adumGYHC9+9fw4/EF9Q1y/PjjxbdSapq+ou8s91IxclmYsSS3O7Jr+pfCrwx+swWKxfwn5txBxMqadOL1Pbv2z/APgsX+3/APtQazcrfeLbjwtokysi6Zo8j20AjPRGCY3cetfi34p8UeL9aunOvapcXjNksZZWfJPU/MTXtHjgSC4O0nncefpXzzqyEXBLda/qPLchw2Fp8lOKPyevi69R3cjHCOV2s5496tW6uG+V3AHoT1rOlJEmRU6M2etd0opOxyOM1qpanpXhr4ufFPwNKreEPEN/prRkFTBO6FT14weOfSv00/Z6/wCC5P8AwUZ/Z2eC28O+O7zVbOHH7jU/9KTH/bTn9a/IrJLnNQ7cZrCvlGCrw5a1NM7KONrU9eY/s7/Z2/4Ou9XubiHTv2ofh9aagWwsuo6YfIlCjqxRvkJx71/R/wDsff8ABTP9gT9ueOLTfg744j0nxC64Gl6zi3ldiM7Y2OFY+wOTiv8AKAmZgFx26Vr+HPFHiHwtqsWt+Hb2ayurc7o5oWKsh7EEHIr89zfwny+vFuh7rPewvFNaOkj/AGgtM8H6lpmsGHXE8lV5Z2JMJjxneHHy9OTX8NP/AAVH/bIj/bM/bO1ZPD12ZvBngqRtK0xEbMUjxNtlmAzjLMPyr8/Pgb/wcR/tt/C79mPxP+zP4uvT4mt9WsZLLTdSuZWW7sPMXYcN8xddpOATwcV8l/sheK4dR0Q2V8XedpmLzsQwJYZIJODuPrXDwT4f/wBn4l1MRqlsx5txCq9NQufQPjGOXT99xFM9s+3KNGOma4PUZoLJI9StUDMFTJPUvuALV7vq1npuy7ttZaKLzBlFd+XBGcL715fc6fYadZ+ffW7xwuhSKHksWPAPzfnX6tWhzRnbqfOKabTif6Bf/BMjxTZeIP8Agnd8N9UmlDSi2kgI9CkjDH4819eahc+Vtt7dfMlHIA5wD61+VH/BE/xNFq//AAT002ynbzJdGvpY48AEDJ6Y9RuNfqkbyG0jSaIbnlwM92A6k+mfSv4V8RKPJjJw8z9nyGF6SaGW2kefMtwDtjOS0g5zx0p8Om2yXfku37krkVmPO10+y0JUqSQg6CtCDRtTeJbi4KxtKdqZ6jmvzSNpHvSpkRKwsYdOGfXjNdD4T1EeF/Eln4kmjLeQWbYOCTtx/Wojcado9pIkIDzp/rGPr3C/Q1lDUPt7wxQndKFJYn0r28tzD6tUVWm9UY1sLCrBwnG6PpO8/aYuRbia203az9C+cD8q4qb9pjxzdv5NhDBAWO0Eq2MnpnmvBb3VStyYI/3uOqenviuc1CWRFM5IQNjCjrX28vErHNNuo0eLDhLDX+A921z46fFOWX7Lczi2ZOphHB9+c1x03j/xTrML2mq6rcXEUqssiFvkwecNxXA+XezKl5cniRCE9gK054IRDEYwAwU5JOMnIrx6/iFjG3+8Z61HhzDRVuU39NTR7dP9BCW6jk+WoDbh6GpbvV03NNaMHY4D54JB4zj171z/AJyJjYMMOMduetSLZLJIv2RSXkIDFvf0r5rHcWV6+lR3R0xyuMdII1brWNO+yERqd0fylwOSabZ6td3FqHtcoUHJfjNUCLS1lfT72ATFGA4Jzn8K0ri4SCxe2t1UOxOG5AQfj1NeHUxSerNlgmtbGbqDTDy9Ruiso3fcViKtaqbK7hjOkQ7G25kVs9fripdGsY4o90mLmR+jkcDFNmvryG5kk8vYifec+nHA9+ax+sXLUuVpMWUrb6Z/okZJlUbsgBhX6TfC++XUvAWn3Kd4lU/8BGK/OK31HTEtJ5jGyyNtVC/oe9fd/wCz1f8A9o/DS1mOMo7oQOgw1f1B4HYu2Ja8j8845ivZKfme3CI4zT9jU9CTnNLHz19a/qWMrq5+WS3FUYGKlUkoc0/C0AADApkkFedfFu+t9N+Gut3t3jyo7Obdn3Qj+dekNhTXy3+2RrzeHv2cfE+pxgMyWwUAkjJdgvb60aXbZsqiPxp/Y0uJF8B65o99Ku37cbuJUOcRcLLkD0+Wvqu3v7fVtOm/fN/Z9tthiYptDleMqDznPevg/wDYwj8y08SWyDZeLDFcBgSdoeTDD8a+3NT26jOulyDEUIJCLx8/Ut+Zr+EPFzDuGOqI/d+EpKVBNHP6je2w1ASQFpHGFdMcoD0P410d9YLdaarwlZWU85BBT6GsZNKs5JFubyI+duxG4ON2Om72rW8QXDR6cRdSbcKR5acENjjvX4PKo27n3Uo3Vjjkwk6ebEJFgfCI3I98VvXljfeJtE8R6d9qW4il0qSJopDh0ByMKvcDNY7s9kY5Z4j8jBj7DHU+5rr/AAvOLzXDfRWwZ5beWEzZ4CkZ2tX1PCVaSxMX5o4M0pfuuVn+dt+0loMOp+HPH1nbBy+g687kKo4jG9NzA84yMcV+TCqxHT2I96/bX9pnwxeR/tB/Ff4U30kNq9/cSyQbm2/M0pK7vUHJ/Ovxlv8ASbvSJrjSrv8A4+baVo2AHcEg1/pVk1TmwtN+R/MmOp2rSXmYrIUO7OMioFBeQAjHGa0Baqz7XOcdPc+lSeSDyB+Xp6H3r0FHU4ikI2O5cZJPH41ILdlHlSDGMndV9Il28A/jThGwTOMjvWgFWKFVUF+mCVPqaVgQFJGGx09c1fiXaMv8o7evNNbYASvGe1AGNKJFU9cqMe5+lRm5LAFRjjHPWr0yFnCrxs/XNVlRUJXDHn0oAN64VsYZeDipUfzAEPY5pGiwcOeTzkdKEiAPBzQBdLFSB1qXaA+D0NVlQKeTU7SD+H5qAIpUJ+9zWZdwgQu3Tjp9a2GkwcLVC9+aGQn0pudlJl4aadSPqf2Mf8EWh5X7LFjuHXf/AOhH/CvrH4ONu/4Kz/Dr2tpx/wCOPXy1/wAEXwD+yjYseoD/APoZr6h+DHP/AAVr+Hg/6dJz+Ox6/wAsuLk5cQV/WR/eWGhbJJRX8h/Sl8RefA3iI/8AThc/+i3r+UouP+FAfBcH/obbv/0Kv6s/iKf+KE8Qn/pwuf8A0W1fylMo/wCGfvgyf+ptuv8A0Ovg8arV4oy4Uj7lR/1sf1Z2r407RwP7sX81r4Y8V/8AI0al/wBfU3/oZr7ktQP7L0k+iR/zFfEviZFPiTUCRybmX/0M1/UvhBK9Gt/27+p+NcZUm6kPn+h//9P+lW0n22l2p/54Sf8AoNfzqeMc/wDDL/xSbt/wldt/Ov6GoZMxXir/AM8ZP/Qa/nn8Xn/jFj4nj/qa7f8AnX+LU9cXr5n+kHDVNKDfofst4tlB/wCCe+rY/wChOb/0kr+dv9hMbfgrpQ7Zm/8AQmr+hHxi/l/8E/dURuMeD3/9Ja/nv/YX5+CemH3l/wDQ2r6fKnfAP/HH8pFZVC1ar6P9D8cf+CvMYf4jWIPqf5V+RMAYL1xX69f8FdNz/EjTwvOXb+VfknHATx3r/SvwX/5EVP8Arqfxn4vK2dVPVkVzETpkv+6xr5kAO9uOlfVxjBs54267G/8AQa+WSrBpQfWv1R7n5SVqKKKQBRRRQAUUUUAFFFFABRRRQAVMn3ahqePpQgZJGu/Pp3Na2juYNYtNo5WZDn6GodJgaTdJj5V7jr+FU/tUhvRPljg8E4zkfSirrFo3w0rTR/rHfsheIdX8S/shfCr4nLLi0v8AQ4LWWJwBnYmwYbgg5XpmvcrQ6FeXY0/xf/xKVTL78bnuVC5G0ru5Ddgelfmp/wAExPEPiD4pf8Es/hVqUsck0GnWdxHKIWAZgsrIu4EZPI4xmvv7Qdcm1VT4gR5YL6SHy5GIJnXaoCrGjDaWPcCv8uPFGjbMq91a0mf1Lw9NTw0ZXNLxPb6W/hhrnxAHe3ZyllFAFMpj7sOchW5GeoNZsV7YWhgtpJDAlukU0NletuYqxJ2PIfmBCjA5GCcVq6RYahr+peRq11GsQiG2RlK3ce7rmMcEhhkgV0P/AAr7Sdc0S10u6v7fUJLZ3kt7w7kFw8Z3FJ1z8oXGK/I4Kc+p9NKSS2OFOoaK0z2lqkrRyo09uwEe9XbGUkYYyMZAYkt+tX7bRtTvL/dZ2skVrKDO1pbhi+wHaGX6kdY25rpbXxHplzpF7HLCmnDehvPsoV2kIDGNI93HlkjNfnj/AMFRvj18SP2aP2FNT+PP7PTS6X4htJityZXW4WKHcEJiL5xztwNoxX03DHDc8dioYdNXk0keRmGNjh4ucj7PEN8VlmFmbeTTpdkdnKVR3Q/KX5+bHc5qlZi5sbuTS59TsYGuZBI6xSAqkPUqxxgv+PtX+cj4t/4LQf8ABSDxhrC6ze/E/U7aZQUDWwSMlT2JUDNfLPjf9t39q34hSXMvi/x5rN8bvPm7rlwHz2IBFf15gfoy1b2rVUvkfmdXxNo3tGLP9P8A8eeIvAXg6d77xJ4qs7VJw7W/lyRZVQfu5dgOe+K8V1n/AIKTf8E6vhyfsfjr4m6XYarAF2KtxHuBHXd5QZRz1zX+XNe+OvGWqKI9S1W7uAvQSTSNjvxkmsKW6nuG33Dl2/2iT+tfa4T6NuCpu9Wrp6I8fEeJc38MT/SW8Z/8F5/+CW/hPV7rV9N1y11O6tQYysIuZo7hcdApATk5ORivibxB/wAHKP7DPgrXB4p8E+GdV1W6lwsqbMxBeoCLO5QYP+yCPev4OvlJpQmOV5FfVYTwRySl8UWzzKnHuPl8Lsj+yjxT/wAHTGmWmoXTeAvA85tpW3xpdeR8pPLD5Vr5C8V/8HPP7V93rAvvBfhjR9PVX3fvGmlz9QXA/I1/MpIwWPK9e9NHPNfSYLwwyOjecKKPHxHF2Pqq0pn0l+1b+0949/a/+N+qfHf4lxwR6vqxTzRbApGNgwuAxJ6e9f6FP/BIXXrf4g/8Eyvhv4mu5zGNHuP7PaRAGYJEDkEYJwQe3Nf5oe7HQV/osf8ABuL4ks9Z/wCCYEuieILY31vDr00cQBA8t3VFRjk8AE+hr4rx1ymCySKpqyie/wCH+NcsbLmerP2R0/QC4u9VWUAPLEkVrH8rOjE5ODhQOMnH4812lpbWUbajaWF1NDexosjfaAvlhF52oR8xPB5/pUmoWms6Lpr2dvaiC2gdUuYchWmLZ+dCcjaBj7ozXMar411KO1ksTaRQ28EWDcDPmbQuACd2GHTOR68V/nXmXu1Wmf0TTp31Lgu5LqdL8zmC8uJWiMqMS211Iw69CWGBmvR76W6jOn6NLItq9suJnLsAVX5gCoOCB9O9eB6JdLoskjaNci6jnJktljGJISTgsQeOPfFOOvN4g0KfU0vxFrKuYlaZS7SAHJZAOO2OTWGGqqNRNM2q0k9TwT/grzod345/4JW/FjSbWI3M2nKl5cEhgB5C8OgI+4QBiv8AKsMbR7lPY4/Kv9cH9tCC38W/sQfFDRbXWIrnzfC88cmODFMV5j2Y5BPQ88+1f5Jmtwm01i4tB0jlcZ+hxX+iP0eMe6mWTpS6H8y+IFBxxV+5/Rl/wbA/AO3+LX/BRHTPG19H5lv4Otp9UOeQHRdqZ/4EeK/0C5ZraXxTFPez3M0KGbz/AJgRh3wrqV6oO7dK/kF/4NKvDGk+Hp/id8WtSCp5emvaeZJgKVx5jLzweB0OK/qi/wCEyvZtOtzZW0tteXSLHapbEMEhC4YktyEOQcdRX479IDNJvMpU09Io+04Bpf7Pex9I+b4U89wl4sjxElWjbKPgZCSZOD7cjNccPFlzq9xf2MFikm/KorABEI+XOFAXC5+Xgkeua8q0DUhaoW1tIbprE5i81nBLqeANow3NegX3i1ruGGa8h8m4MYd58BYYR02pjksfev5ohX5kmz9Aq0G3YvaTsGkCz0pzNdTNJt8w5WELkHLHJ2r24wM1v6nrnhDwPpOreJbthdR+H7KW/lmfARZYgznaOOMZHArIj0dltbebTphJFdAD7IoHmO7H77nGVU9xwcV+ev8AwWR+J15+z5/wS/8AiT4ws5UtNT1OFbK0WBiQsU7i3OGycjDk/hX6PwDlyxWKhT7tHz+e1HSotn8Svxx/ae1n9sL9q3xx+0B4iuVuDqN21ppiSnKraox2Iuc9FAxjHU14v40tLGb9zasbe3hUoQSx/eH25wD39K+KPhD42XSXt4pflEUrS/UtxX3Lq1zFrumx3fhxftDyKDJ5vG1sfw9OPSv9Jsry+GGw0MPFWsfzrjqrqVXJnxB47SWBiLlNrg4OeCQe9fOurYN0cc5BxX1D8WBqXnSNcq0sihsvgYIH0r9+v+CMv/BEz9nL/goH+zbrP7QHxf8AE2pWt3purHTxp+mxq37sIGyzNznnjAxjqc1lnWd0MDRdarsdOW5XUxErQP5QmXEo3A1ZjhndwIY2bd0wCc/Sv9Inwf8A8G7X/BL/AMNGGG9tdd1m/iZWMVzKqkqeACAAO3qMV9W+H/8Aglr/AME1Phpp5uLP4Q6Z+5yC947STkr/AH8ZUfnX5RmXjTllKXKk2fVw4IxDV7o/y57Pwx4pv5RHZadcTE9AInP8hXrnhL9lv9ofx64Twp4O1S9LHAEdrIST+C1/qZeDvgV+zv4NiCfD34b6BokKgMkgtlfeeoOSGx6V9J6J45sPCFnAsem2ESuuSsFmgPp25A+uK+fr+PVGKtTp/eejS4Fm17zP8vT4df8ABHP/AIKN/FDY3hX4X6xKkgO2RoCBx1GWr7Z+HX/Bs5/wUz8aeU+seGhoiSdfteRge4Ff6IMnjfV01qaPS7s2cRTevlIqAnGecd+3BrE1fWtb1OziuY9UuJWc/vMyMAnPsTXg43x8xKTdJJfK530vD6H20fxQeCf+DSb9rHUbuI+NPF+kabASPM5bev0DACvun4M/8GvnhD4X6rb3fjL4oqwdhmGBkHmEegVu1f0sx3FnFcGTUWImRsqcszkdiAeua6y3810eazfYJgXiygymDyevGfevjcR41ZhW0lUt8j0ZcD4eMbch+N/iz/gh/wDsf+Ffhdr3iZNe1HWPEWkWMtxbMpyiyIGCltw5AIzX8lmtjxNe6nPH4iCzXcV1JC0gAwQidgOh4r/SGk0bTdR8Fa3a3ab3vdPkjYnALEg54/Gv86Tx3o9vp3jjxdayQylrTWJYQwYYG4so4z6Gv2zwo4nr5hze2dz4jifKoYe3s1Y/qZ/4N+NZudc/ZE8YeHlRml0/Wo2QJjcA8THIz/u8V+32l2sl1LNZKNzRpvLHPJxk+w96/nR/4NzPEmnHS/iV8OJ3aIQ+RcK0RyxKB05zx3r+jmXxvaXP/EsZDHFF9yNioZmCgjLJnOa/C/FuDjmNRJH3HB8n7BJipdQXqIJ42UYwu0HgjqTVDU9TuLqRd7skI/d5x0A70tx4kM1s5aQQmbaPk+aT6KMdaqxCeXVTp/ltGZFBCsOXyOC3ofWvxG+lj7NwLcAtlOYn88xdDnO5qkiBsYPtVuADPkSSf3fYVWUqxWykt9k8IPyL90ehGOSSOtTXTzWk72+oosIyu7uUTucDP51zuo72TJ5VfQzpVjgJlQbccBhz165rmzPcS3f2UDMx5GeCFPcDuK2r7y7i9l/s1Geyxsimcf6zH90H1rnZoYrWS3juVYMoLOD8j7BjI5qnexvFWZ2ixJEIo4iXYcZI4J7gVFLIscSSyxlo5d2RyeB3x6U4yQPFGdNM0cM/KRyYygXBJzS6xc241VI4/wDj1EWVHTkjnn61k4yFJXZQgtrm0C3GSUl+aMZHFTRX99NYHTbYgpI/zuCBs5ycGuaiu/Ku1tlR3uSduQ5K7e2B0FdAtiIVeG7uCDOPlCfwEc8kcc9K1urbHQ6MVqSQxpHdAMcuhDod3LA8HJq3qt6bohNrs0ZOQpyvJrnLHTJ4JDdp8p6fOclsEdMV1kbA2jSXMwTzD8vA59cc1EZ62ZlzNl6IxzwpJZnyfK+/ngZ9Oe5qjLPd6jvspPmeYlkyMYI9agRLGWBl3F4i+Qx4BbsMCqsE15Jdtp0bItzkAnICIvckjmmpJuxjUocx01ns+xveTP5wh/dup6Iw6Ef0r7B/Zfv47rwfcacpH+jz5x/vjNfEB0vXdQnNlBCskp3PJITtjVBxuB/iNfRPwD8Z6b4Ha70+8JdblkCBT9045ya/onwPxi+upS6o/OeN8NJ4bQ+9EQKTTov61m6Xf29/bfabZ1dT/dOSPrWlERxX9lWPyJstUUm4UtAiu3yjLDpXwD/wUT8QQaf8B5/D7ttbVpPLBBxwgMmeP93NfoBKCcheuOK/F7/gqr46eCLQ/BVqskQY+a8q88NkYI9OB+eKipe2gm7H56fsyanFp/xR1Ox065jeOWxSGPafmlKsGLMPbmv0D17WNOit1vdPjJltMruABMwPOT9M1+TP7MWoLbftFW91bxo4lt54FQlo2TA3EMpH8XY1+mcSTJaoiANA2N7ZyUc8hRnkgV/FHjhheTHykfunBFXmwyOjttbYzi4mYl2UFR6E+1cxc6s7Z85S00rYyx+Un0p+m3RsGmuZYpHyNu0YJDdjnpWYlnfRp9tuFynzF0PJXI/Sv5xjNLc/S40ruxXkl1NMLPKWLSYYNwCuPu/l0rpLLV7XTb21geR1DS7XCejKQM1yTbpJ4Zk3vbA+cpXkP2xz71q2dxENeBuJI42lkVnTOAgbgY75+le/kFZKsmu5hmFO8T+Gj/gqR4QtPDn/AAUD8bafakrLOQ8G5sNnAZuOpOM4r8g/iVNZ3Hj3UJ7HJidwQT1OVGSfcmv3r/4LUeGF0X/gpHaSwKsSanGoa4Vs7v3TKevvgV/P34qglt/El1DN95XwcnOcd+K/0l4SrqpgKUl2R/LGdQlHFTXmYR4cU/A7KaUBT96kJlAyR+tfSctmeexwfd8xU4/mKHKhiDznkY7Y6ClzldnJA6YphO3qaADzMjfjg8EexqB1ZnAPQUbWpNsnYmgAkD4+U5xRiQOSTjIFS4IHH40wnIz36fhQAxouNu7PekwQpFSqD1FOIOCO1AFEylARiq6ylxkcEVNKpC1AkbbsY470AaQIPSoLri3fPpVqNBjiob1WWzlJHRTzVVYJRbCl7s4tH9jP/BGEH/hlSxHoGB/77NfTHwTP/G3H4ej0s7j/ANAevmv/AIIwkH9la2I/vS/+jDX0n8FGC/8ABXH4fk/8+s//AKA9f5ZcUf8AI/rt95H99YRXySUv7iP6V/iKceB/EOf+fC5/9FtX8p0v/Jv3wZ/7G65/9Dr+qn4kMf8AhCfEJH8Njc5/79tX8qzg/wDDPvwZ9vFtz/6HX5/jJP2yZnwrD91U/rof1URMBp2kgnHyR/0r4n8Tlf8AhJdQ/wCvmX/0M19mCTNlpH+5H/7LXxZ4m/5GTUP+vmX/ANDNf1J4NSUqNb/t39T8d4yXvw+f6H//1P6NrKZWS7IH/LCQ/wDjtfz6eLuf2WPief8Aqa7f+Zr+gLTcGK8z2t3/APQa/n98W/8AJqnxP/7Gu3/nX+KtV/7Z95/pFkV1Tdj9d/HUmf2A9Uwevg5z/wCStfz6fsJsX+COmY42mX/0Jq/fzxtIT+wBqZ9fBzf+ktfgL+wcufgfp2P703/oTV9Nkrf9nyb/AJ1+TOjL42q1PR/mj8hP+Ctm0/EnThj+Jj+lfk7EoEmfev1m/wCCtSf8XK0/Pv8Ayr8nVG2Qj6V/pb4Kyf8AYkF/W7P4u8YF/wALM35j2UFJh6o3/oNfKVyGNxLt5GSPyr6wQL5xGfvAj8xivlrWs22o3FtGMYkNfrD3PyYxypHNJSlieKSkAUUUUAFFFFABRRRQAUUUUAFSKcjbUdKDg5oA0LTUZrKJreP7rVRQ/Nuf1zTDzzS8gU0r6Fw3P9Kr/g3z8R2vin/glpobTNF5mg389tE0/wBwSvJvAPIyCG5BPNftNYat/wAJdLeQWQtraS1aMsgIMiXGclYzwfYZ/Gv5ov8Ag2D8cz61+wh488FyBGj0vXYZN8nIRZIsngjqCMg1/QrY+K9D0+eTV/tCtIisLWWJQRdyKOsh4zz27V/m542YFUs1rJdWf0lwjWbwcGdJ4jvP7H15td1OKO2ZEVXjUjzg7j7/AB0G4A/SuIvPGmtS6S3hm0tIVurMCWWaNlCrDJklgc8uQec8YNb1nqcHju5ae3t5IvET4aFpYwYpoQOBgkgNwcCqzeCbe3voZ7tmsra4liW+Z1wbZgeFK45DH19a/n2nTZ9oqvRkH/COXN14UnsL9f7MW1Iu7W9KATSkjHlg8jAyACK+CP8Agp78IT4+/wCCaHxTutV0uS11a208slw7Avdx71kExA+XIIKEhR92v0+v/D0OrL/aHibUF1LS9Om3CGHspxj8MgZHtXk37VPhJ/F/7JvxP8E6fI13f32hTyWsUu1TGqoxWNOAME8+uTX6n4azhTx9GpUdrSWp8/xHDmw8lFX0P8hqZPLmeP8Aukj8qixnivq7RP2NP2mfiHqd6/gTwXq2qJHcPHmG2Zju3HrgD9M19J+CP+COn/BQbxxqCaba/D3UrSWRFdVuY/Kba3GcPjjPSv8ATyfEmDhBSdZfefzU8nxU37sGfl8sLbuKUjBwcD61+8vhj/g3V/4KHa9diDW9ItdGXJB+2TBTgd8KG/Kvsr4d/wDBrZ8cdcnWPxn4z0+xHBbyB5mF9Tkgjt1rwa/iNktP48RH5HdR4Vx83aMGfyo4BwMjmkXDcd/av7PtK/4Njfgx4fEY8Y/EqS5l8zbJGkaIPl64O4mvq/Q/+De3/gnJoUMMup399rUuFLokspAHTO4IBjPXmvmcX425DRdlJy9D2sPwFmL6WP4FGRGYIMnpx9aeu0YHqM1/olfEX/gjt/wTr8Efs2/Ee88CeDZVvbPw/dTWV3cxs5aWKEvuhduQVYc1/nb3SNa3csLA5VyuPpkf0r67hTjHDZxSlUwyaS7ni5tkNbBNe26kTMG+Wv73f+DUrxlpmpfsy/EXwNqdmNRXT50uooHYhdzAn8MkD8q/geGXYEV/ZF/wam/EO2sZPix4HuZzBLc6fDJA3o67hnFfPeL9LnyKq+x6PBclHGKL6n9cWt+IbPxvPc3WkSrbzoSlzbXTEJD5YGFjY+vtXnq6lqWtS33nW0srW64ZIxkQKoGJETpgge+eveug1YSah4Vttb1pooZLaXAEZAkmGTl2A65GK5/U9Q1JNXbVtMVW3lXSGJsGWHABDEdeB0r/ADGz53qs/qvAxtT16G1q+jTW4ju7JY5Jb1GG6M7S4Vuhx0OO3et5dfuNCt7W8uNLt0voz5VrGyYxEuCTs6tkknNWdC0+0trKa/tpkmtpIhLJA4yYGDY2ZPc9RipLIaHdy22tSE3l9cCWNMtgQRLxk+/tXgQm1JNGlbZnJa7rsHxK8OeNfAfiUwPLqGkNJaCOIJGUjf8AeK2OrHPBNf5Ovxm0kaN8WvEmlgACDUrmPC9BtlIwK/10dHsdK1nWLGzhtVNmdOmt1usYEjiMsVBHXJGfwr/J4/bG0VvDv7UHjnR2XZ5Os3eF6ceaxFf379GrGpxqUvJH4D4j4dc8Zn9jP/BqhbwH9m74oPeW8M8bSlYkulBhlkMJAQk4wTnsa/o91e5vzfW/hy1to5pLaBdyyZiVA2MhcclV6D1r+Vr/AINafFGpX3w/+J/gC0ZbiKGzbUvspxuLoAgZc5AOCcV/UH4a17VJ/Ke6twZdm8zYOFiBBVHZumemefpX5N4+t/2rVZ9NwFBPCRkeh6bFe3Gkpp+l+TcXUcjGZGUK8CouW2HuTyc8/nXolroiQahb6dp0e5yvnTNOA25SQcbT0GOMdckV5nZavaXWrHVHg+xyxBtstuS3m56Rt93I9faum1/Ub+C7hW5ulje6O57lGOI0wML0XaOcEZPGRmv5xo1mkkfoXs10OlsjNPrF5ezwNI90QkESOVO0YGRgfKMDgj3r8X/+DkbzrT/gljqSXDPE5vbdVQ/NkC4RiS3fIHUda/dDQNWgFrbane/uVL7VdhgFOg2+ncYBI61+S/8AwXu8BH4n/wDBLfx5pWhQMb7RzbXfknLtGnnqXI9tmSK/avCWqo5nSk31R8VxrTbw75T/ADJ/DF60TIUwdvQH6190+D/FpuPDsVsjgR5Bk28c/XrXwJpBEMgVgQy5U546GvafC3iX+zLCe3Z8Kei1/pXVkrXTP5qmmm0z0D4tXbKrSM21gjIU6LyO57N7V/WT/wAGu3xBltP2YPiP4St5G3xaolyUB5UNGFzkfSv4ufHHiG91kjzmJAzgZyK/qr/4NS/EQPjb4peFrp8QNpCXAB6blkxnFfmfidR58lqNdLfifXcHzaxcYs/r4GtO8xurdTvkCjzW5cgHkH2rsb0w3tk8MU8dsXQsXcBue2Qev1rzWK8hlkSeGRZNyDIHTgdqjurqKW2aEOQ2NxyevtX+eWb4qrGq4pn9I4fDw2sbNl5CaHdx3AMO0YYI2Vc5BDD2JrP0fWJPOmgimSWS6IjUOBhQPQ+naslJ7dMX8zsIMYEZGeehzU9jPAfMuIoAEQh4ARz6EH2rzKeIqt9TSdCCeiOgeS41STy2KQvBuDEH5M9B+NaUcF7b6Y0CQqR95yOQ2O5rL0iE6nLLbNgs77vk4GQfu1113ez2iy6b5gYONr8/c+tXUrVG/eYezRh20tvujvJMM5K4YAdOce2K7Ozu2g33V45LL+6K44BboT9KyrTw9HbyxWt248qIqsoHYtyp+lXpbLV5ZGa0KLEp/fknsDgEepNKlUV9TOskdV4YszealLFG7uWjaMqzEKBt+8BX+ft+1foaeFf2p/HnhO0nLWY1CW4m2DIV/MIUHPua/vunnuLe8t7aK5MNzECY1QZeVQvQiv4gP+CknhZPC/7c/jm0YeX9ugWd4iOWdgGI+pPT3r+tfAHHr2rprqfjHiBR5XzLY/QX/g3o1O1tv2jfHfg67j+1T3mk+eiEYVlSQfwjk55r+qK18NardaVDY2NsIdrmSNZwEY4P3T3IHQV/Hd/wQi8TQeEf+Cg8Ud8pSbWdLlthGOqdXAOOf4a/td1zXbeK9M0ruJnZyrFQHCj25x6Dr71weNeFjDMJN9UdHB9duikjzi0077KJ9UtvKd3ZVBQAi2ccMVz1P1rUurjULSye4kVIATg3J/1j888++e1M12a2S0ITMcV0QXUDG05+82O9cnqcsc+oRwJOLqZF3RxgnaUUenSv5prVFqj9H9k2iWHTF0+WO6jRUvpc/fYlo1PVzk/xHpmqNteW7Ld6PYRJHIpYz3NyxLSE88egPYVnSaymq3sF1dtuvpV27QRkIOxHcUW8FprN+WsUNylur5Ax87jqCT/c/wD1VGHs56i9nbdHqcWixjwnaw3Ef2p48eWfurCzdCO/vzXMS6Xbyo7+LJVa6jbfuUjMqD+EexxXO+JfiN8OfB2oiy8T60sN8sS+fa7zuYkArtUA5OOP515Ynxt8BxX39opcRysgKLG7ENGG5BYY4Ar9CyrgnGYmKlTpuzPArZ/Qpy5W1dHq9oq6vcPd3CNbXL7lVSSAkeBgkVzctq+lwTRMfPuE5DO3yFf9nPFbfhLXtH8QQHVjfRXKzEJuiOd0TdeTjkele0W/wP8AAfi4Ddr3lxIu5FHYZwCa+vwXg/mlVX9noc9XirCx15j5zsk3RPY3L7LeYZ3KQGDd/m9K6L/hINC0y2h0K1uFkjK7JSFLs7E8c9ete8H4LaBpV/8A6ddSS2qgRKQOD6t+Net+Hfhr8Grywkh06Ereoh+UnnPTIFe9V8DMyjTcpJKyPMlx1heZRjrc+ONOj1CEW0U0JQOzHeT8yovXIPSt230u7v5INQtYoWskcshPJyPr6muaOtwG+v8ARMSXN087wyuVO0BDxz26DNPaN72+BluiluygH7P8yxsPYcH3r+ds4wjw9aSl0dj7vCVOd3W1jpNUu1s0fUbryEnLiM20f3VX/npj2qgmtaXDqP8AZNtOJ4nA82WIZZyf4FOOoritasbaCc/2OxklHySsw+aRe5ANN03SLRWitLEbVRvNRiSAr57/AIV5KxCTud0oaWO51nxxZrZyXd9E9vaQlY4o14cem7HXn8Kf4D1ay1u6nvbYFZImV9vYnGATXG6g18tzcahLGLtr1QARgqqHq2Paut+FsEcWvSxuuRJFjAHUjofpzxX7f4R4yMMxo9m7HxfF1Plwkj2zwZ8SNa0DU5JIJH2BiZYxyATXptx+0be2c8UcUPDNtUMOteSaX4E1m41L7XaxnyOfNHPLH/61emW3w2toLR2uI/ML/dJ/h9q/vh26H8+XPon4d/Ei28dW8rBPIki4YHgE+1eqr90V8z+D9Pl0ww20Q2hT+J5719IJM2wFxjikA+UkZIBPHav5uP26fH0fjP8AaIuVjs31FNHLKIwWAjCcBzjjAPNfvz8YPiFYfDX4f6l4svCM28REak43SMPkAP1NfyY65rnirxd8T7rxTHcFBqkrPPc5xGiFz+7LfxcnGPbNXTSvqTNaGR4E8Sx6d8e9B8SXd2skk+omKZjgMm5AoGB1696/WO+kF9F5FqPNmtQGxjb5uT198Cvxy1q2m8OfGGw8Ww2yR3ZvrYXAfBj+8ArL2ww/Gv2Xni+xTx38imS481pVCniEfd2t+PNfx/4+YZxrqo+p+z8A4i9DlM7S7bT9TnksbyVrZImyzxjJd8H5Tn0rsvsl5pzLqj7I7qJ9sbnncp6B16Gn6dHZSWpOnQhrtdzSjGNw6/LSX32wwmTUMIG+dywwTz8tfyLVqO9j9dvZo4t0e4mOo7MwGQhAvChvQD0zzWDJpFxZ65FPIAHjkWXJAw2GB2k16K+qXNtGba6twjOp2gDhBjgn3NZWp2L6qItOk+SKMK3mHu45Bz6V6WS4pxq2FiIto/kX/wCDim4i8J/tleAvGFpZIseoQb5EI+Q8lW49s5r+ZzxijL4nuMAYZ2IIGAQDiv63P+DlvwTBdXXw38dXIX9wrW3mDoWJU8V/KX8RLWK3uU7SB3X/AIDkHP61/pP4Y1VPKoM/mLi2ko41wR5sSCSR0ph3Hjinnr6UDk4r79nzYA8YpSy8Ain+WP8AP/66iIG76UgHBckDJGfT/wDXQWZTtHOKevzLg1GwwcUAJ1pCu3qKcOtIQzsMHigCPdjnsaM7jxUphJBOfekMYjOSeKAIygbNRKoU81bEZx1pp44oAURMo61TvQxs5Qf7pq0eBmq14w+xSN321rUlFxaLSXOvU/sa/wCCLnz/ALKlqw/ieX/0PNfSfwX4/wCCt3gE+lrMP/HHr5q/4IsH/jFKzH+1L/6FX038FUDf8Fa/AbeltP8A+gPX+U3GM2s/r27yP76y+N8ka/uI/pH+JDhfBXiVev8AoF3/AOi2r+Vz7/7P/wAG06f8Vbcj/wAfr+pf4hvu8E+Jc9RY3Y/8htX8tEo2/AP4Ngf9Dfcf+hV8Jjal6kUg4Tp/up38vyP6kRIps9KUDokZ/LFfHPiOIt4hv2B63Ep/8fNfXSt/o2ltnrEn9BXyPr8jHXb04/5byf8AoR9q/pjwTk1Rrrzj+p+Pca017SHz/Q//1f6I9Mk/dXZHeCTP/fNfgN4uP/GKfxP/AOxrt/51+9Gmy83Q7eRJ/wCg1+BvjAn/AIZX+KAB4/4Su3r/ABUn/vv3n+lOQwvTZ+s/jdgv7AmqKvbwg4H0+y1+C/7Bwx8EtLA7tL/6E1fvB42P/GA+qY/6FGT/ANJa/B79hH/kh+lkf3pf/Qmr6bJP+RfL/GvyZ0UI2rzX91/mj8iv+CtQz8StLJ75z+VfksP9afrX6x/8FZn/AOLl6Wp9/wCVflB5R8w49a/0r8FP+RLD+urP4p8Yf+RzP1YRDdIGPXcRXg3xK0xdP8RvNEMJcKHB9+9e9LneccbDn61x3j3RDqmhtOozLanf77TX629z8kPnOilxyR6UlIAooooAKKKKACiiigAooooAKKKKAClzSUVdN+8h3sf2Xf8ABrf8ULa18F/E/wCF2qwm6tZGtL5oQSCwBdG6c8AfjX9XA8O6HD4ZMM5tP7Kmuj9ltIpGaWFHIxk9V29+elfxUf8ABrr4ms7P9pnxn4V1GTyo77QWcNgk5hk3ZwOcDcf1r+1aPU/CN5jT0sPO1NECRy27gRvH/A6ISM5PXPPrX8DfSHwqhmk5dz+h/D6XPg1foaE/imbwZpt1oUs8U5tmH2F4si4gwRuUs2cgdetdbpHxS1K4sf7E8WpCjXAEkktwoWOZNvyyFx33cjHNeV6wmqjU4fDXiH7ICN832ZIhJMxYc72UnnAGQTzVHULyTU9FkvJ9Ot7vT7ExSRIzkNmVv9UqZLhcjkdK/lalOzaP0pYZPU77w7LIL210y6V7S5sIXe0WE7vtbbs7iG4YMM4zzxW5498V+KI/DIkmWK8mh3KZm2xsrggtHLGpH0AORgV57r3xC1dGlttYtvJvNNdTFKxO2CNh/qUwV+YHGOcgZryX+2r13uRuDC6cm4Mkg2scE5jJOWOc9ST2r1cPiHB+4y/qKlq0ezw/FhtC0a5j8M2On2N5IztNHDZxxKE6iRcL8xJ4ycgelec6J4/8QXepjUvEWrzySsA1w0e1SsY+6sYUY+Xqa5W4eK7kSeaTHln92XQhwT0GSvfpVeLwtrPny77aP7XIq4KNllZs7gVPyqNvOMc178uJsQ1aUmyJZTSjtFHpHiGTVvFUg1PUbud7e5YGyaSUjzNgIVAq/wAR9xzWtY6Y2hWE2jT5jeUiaY+YWuFZF4G3J657YFO8Ix2Gj2c0k6hbizlV7O5t/mUOB/q5FbgfN1xT4Nbkt7hvE2nxR22qXzskFzCxKME/1hkDkgMT90e1edVz+qnds7KGFpIpJ4ItGhtPFt4qXq3jPFJa4AkY4+9twclTgr713On/AA9sPCkNit08dha3bbJraU5l3NyCTuzjue1eF6rq1sbeS6sHuVvg2bgXEojjODx5Ui4O0k5OOlWI9P1RZ5JrrUI7SyhQvLKD51w8h67FOTx0HcjnFccszqVnZsyxGHsttD1fxmfD58OeKfB5uhqi3WnTW80q4W2hSVGTYCQ25iOGAr/Jk+L2mHQ/ilrujhdgtr6ePaO21yD+tf6+Xwkg0g3NrYabdbNOitPMuI57cETPLkh0Jy24Hknpj2r/ACcf24vD48MftbfEHRIlCR2+uXqoAMDb57Y4r+5vo3YtulUoeS/U/CPEiklFep8qsdg3Cv6ev+DXHxFNa/tkaz4UWPzhqWkXB2deYl3j/wCvX8wx4Getfvz/AMG2/jaz8I/8FQfCNtqMnlwanFd2bZ+6TLbuFB/4EAK/dfEDCqrk1aFuh8HwzPlzCD8z+7k2FzpFvb3NxbjULsh4zEjHbIC/QYIxt/pS+FNRi+1GzsGaO409/MzABNKoGT5ZjIxg5znmu71bSdF0rUJknE/2dHfKMQ/2cs/yMzehPK1meANMsLxbhL63F7dRsVVlcxSAENgxlcEk9wehyOlf5V8RU+Ws0f1hgsTemLrGm2tv5Pi7T4pWsI5g09m5+fcAQWcLjAJ55zmuo1zUJbPQvtExjsZbrbJ5kaj57Y/djC9c5645rzfUBcSXc+rQQ3CyxssS2+4eU7E8mQdcnp6Cug1GZbTUreG/iCyQxxx+cSZFgYNvdUVcjgEcmvmJM6nK6NrwhfanY+INJ0XRYvKtjfCM27hmEcbwupLEHCOd2cnjHFf5mn/BXLwbJ4E/4KAfEDRWTy9155wH/XRQSfxPNf6lHhnUPBOl6zps+rz3c2oyzLc3D2w/cb87AZB2A3Yx71/m+/8ABxH4Mt/CP/BTXxg1lJHLHfCKbfFwu7aARjtjAr+4fo2V+TFzj3ij8K8SKvuJn3n/AMGpXiDVYf2kPHvhiwDOL7wzcAKhAO5WDA89cenr7V/Z5ouk6MdOu9H1G+ubyW4UC4nKKv2dUPyxnG3nA9DX+dd/wb+/tDv+z3/wUs8A6hdX/wDZ+m6xeHTLx2xsZLpGiUN7b2U1/oweKviF4hS8vYPG12krJcOrRwxqrRGOQ7H3KeflPAI6V5H0i8q9lj/bvaaudnhtjZTo+zeyKmmX+seGbKW91qJNQ0AgwxW0qATIW480qvze/Wqentaza5PB+8vrErsVVIZyThQMnoOeh/8Ar027utFXR2tpfNt9akHmIbYEo8J6b+yMOtZOo2sqaQsWk6WZDcAGJ45GZJCACQQuCrnn5s7frX8mcp+v4dbnfS+FNVUldU8x7eTdIeii2TOdwOcYB65HJqD4keArH4vfDvxJ8IPFl5HdP4i0q6so9yEGZmhKQeWcYb5iDzzWb4X8Z3ekLb6brga6twmXlL5MTbifKcKPmUAYySSK9hsvGVvHeWVh4b1ODUhcEy2xjCGOPncInBG5CfYqc9K+34OzD6tiIVuzPFz/AAaqwat0P8iz43fCnxH8DfjT4m+E3iyA2+oaJqE9rJGwwd0bkGvM4JXRiZOh7j0r+xj/AIOUP+Cb02syH/gox8DdIktYZWWz8V6dHGfMguVGPtZwNuyTIBIr+OIXdulut5DwH+8vofSv9MeFM4p5ngqdam9ep/K+cYN0KzU+pma1cRZ8uMZr+kD/AINg/FMWkftf+JPC00hA1rQ3hVP7zK+eB64r+aS4n85y47V9l/sJ/tsfET9gj442nx9+GVpb32p2EboIbtS8REikHIBHTP4V0cU5bPF5fVw1Pd6f5HXkmKVLERqvZH+nXbpaWN60WNjw/u+OxXjkHjkjNRGO8kdjbIsh3DLEHHPXOOgx6V/CF46/4ON/26/Fk1xc6cmi6XJcOX3wWaswJOer5z9TXzzrv/Bc3/gpbratBa/EWfTkk6/ZIbeH8iiA/rX80R8A8fXm3UklfyP1h+I1Cmkf6KVnpmpXlw1nGjKkY3Avx+uOlN1a60DR4Y9T1jWrGwQFo5DcXEcYGMdmYdPwr/MN+If/AAUe/bi+KFq1j44+Jmv3sLZBjN5Kq4PspAr5a1H4l/ETV5M6lrd9OScnzLiRsk9+Wr3ML9G5r3q9VW8jzq/ifDeCuf63PgzxJ8P9X09r/wAGatb6tYyytHJcWEqzokwPI3qWAI75PFekadeabcaU1/c2LsEwjFjgtk/eYDnjGR6/TNfzj/8ABtppmval+wDr1r4jhuIvJ126uLGeckKytGN3l56jcDk+tf0LaPq5sDJp1g5/tCfBd5ScRJ3JXPzdtuMn2r+Y+PskhlOYVMFGXMo7M/Ssjx7xNBVn1O1urRYLkXbymLT5YlUtOuDIB82Qei7c46dBWGBaxEwOkrm2/eBnfEbnqpzxkYpmoNeQ3j3sq/axaNsnnuQdvzYI2xgD5c4zge5q1qMUl9CdP1oJq1/jzIo23RrtP3P++TyMn0r4KlWu7npVti3okdld63aXes2xl82bck85MSIWOMI3GR9a/kl/4LQ6FY6d/wAFEDqOkWplTWLdY2YMCrOIyMr6BcA88mv63L2WS3tbOy8aMl9LJIvk2jsDHAxb5Wdlyfx7d6/lo/4LqWP9n/tQ+CfE9yPKuLhSjtsJjOwlcA+9f0t4E4y2YRSPyjj/AAzeHlUPjH/gmzr/APwgX/BRb4fa9aSPJ9oZ4JARhnbaVwOx5OBnmv7rtT1JrS/MljpxRbk+ZPLOcsiPnaQvqBjgcetfwK/s0Xs+nftbfD/xXaSNai3voUdSwVlcvycHpn171/drr2q6gL5LuaOWWIJBFcHgTRKehTjGPQ19l9IOnyYtT/unlcC/CzSv9R06yvv+Ee1q72Dyt6lvvTsR6KOMcYFcrGkMV9BFZQMtygJWZgREi9wT0NWptVgsbzUprI+X+72wgKSzsQf9Y2SBz6YqtPqL3FjYaZfyeQs3EiF96KBjOCORn0r+Oa+M95n7HTW2hyTw2UDzaxbSb5tx3XOBsj3MdyqRjGTnb6Cr+nXCwXMd1o1x5K3ETHbtOFBOC5Oenv1rzrXL6zbUI7QzKmk25byIivLyBuCwHUHrzWrpMt1JfqGlCy+Sd0r/ADIgySFA9PauvK6/NUsdNWmmrI6KP9kS5/aDeTxn4bmjiurR/KL3OcSsvO4YPX09qwpv2BPidpnmXUGmxzXspKyssi7WX1CnFfcn7FGoSy2Go2Hn+ZHDhlUHpuJywHoe1ffI6YPfrX+kHhdi3LJ6PKvmfzBxXQtjZ2Pw70P9mr4o+EcyS6TNEqqUSJUyi/7QIJHNegWPh3xRogSG30+YLCPncq5Mh6gDkDANfsLSJDFyu0YPUYHev0n2zXU+YjRj3Pyz0Hxj42NlLa60jSzsdsZwQqR9twzjcD1/Cuw8MeKo7e6lsZ8W93ECY5pON2QevPr2r9Fn0vTHQpJbRMp6gopB/SuQ174eeDNbQnUdOt5iw5yi59PSvOxkeanLvZnTRm4yTPyu8i5g166js5o4ZnmaSQyYAkB6lCOcGqRuNNhna90adre0kJSWJEDRiQHBZiTxk1f8d+HtI0T4jan4eK+QQw+yuwYiPPbPp3rmopbeB7zTg/kwwMftI2lY5SehB7gmv82/EKl7PGVF5s/pzIZ89BS8jsdTuYXhiSOSIiL78wxg+wHNc1cSaOkTyvJJHHJICxjUsA3TAx2b9KrzaVbTLHbEbZXGQE4BB6AfSt200j+14YYdNtBJ5YJZTnaB23n+8fWvzGVW+x7SVtzFewvZPtFtoJE8rEAxxcuI/wCLCnpivTvgDeXEfxLt49UtWVZGMW2VcY4/+tXEyWM+kRLrkE6WzwOAVjIEwDdW3dwewPFd54KubK08eafqyiRvMljcTM3L5OPmAwFPtiv1nw2xXs8ZTl5nynE8ObDtPsfp3baZp8MG1YVVDzwOtV7zT7CeHbGgQLk+lWjcmC1OwYOB0965eTV5pS0LcjFf6R4WLlSjLyP5xkrNo4FdS+z6uIyAArDBP1r3WJvMgWUngrmvm/xNpdyblb23PQ5I+leweCNdj1XSVt5OZ4fkcHp7GtrEn5L/APBVH44WekaJa/DTT70RSLiW5I5Kl+ApA/2ea/ATXPiJp2g6FJHPM88c/wA0MMGHMPbdLwME45zX1D/wUF8Y+IJv2pfE9lZvsntbo5imAcfKAPkVshj3HFfjD48+I+oXmsPp2kSXMMc/N48ybHYAn7wHADNwPanGVnccdz6a8ZfEbxDqMmn3l5exf2lY3EN1KI2zAbZCMbumHGPxr+luT+w9a8PWGp6ddu66nbR3WUAw5dAdrE9Fwc5FfwR/G/4oavonh+41C4Xy54jHA67tojQMSCMdSeMn0r+5r4J3sPiD9mHwH4y0V49RTV9HsM264VlLwLkhsg4FfzX9IDCJ04VbH6d4e1vfkjv9P1TzboW+m20lxcW4xshG5Rjsx4PP1rak1e21N/N1q2wEUyyBiVAwdoTnPWsW9nOl3TRRW4aLykD/ADiMQZ7kjmTH1NY9/fXWlhJHuQlrN84u2Iljdv7mB27V/CWJfvux+8qGlyxMl7LbPc2JaTaP3xGGV4yeNvuBxxVg7tVhit9Wikjt2TbHIo2lMDkkD730rAtJbfz47q/YxNLlbQRqVUD+IlT1wfTtWykrf2Y815Mk7RMTIEJy3+0vc+4FbZbJ+1Lt7p/Px/wcpeHbS4/ZL8Ea3ayGd7HVEjV8bSy+WxJZex4BHrX8bXxJHnahFdIwYNEHIH+0Aa/us/4Lw6Jc+PP+CampeJJ3inudIuxcRui42JE20ZHYhWr+DHUJZL7wvpF+UMbz2qbyT9584/Iiv9H/AAXrueU69GfzTx7S5cfc5T9aOnNIAVAVuopa/XJbnxQ/e2OKZUqgEZNOwtICEMR0o3L361IwXPPFN8tTz/SgBhpwGEOKb04oyelAB7VIp6t3qOjJoAKKMY+ajOeaAA9Oao3i/wCjSEdMVdPQ1Vuf+PRv896l/C/QE/eR/Yz/AMEWuP2V7Jf9qX/0Kvp34KkD/grP4F9fss5H/fD180f8EWwP+GVbE/7Un/oZr6S+DTBf+Cs3gT/r2m/9Akr/ACo41ds9rvzkf6AZYv8AhH/7c/Q/oz8fyD/hD/Eo/wCnG7/9FtX8uc//ACb/APBpu/8Awl9x/wChV/T949YnwR4kYf8APjd/+i2r+X2c7P2ePgyfXxbdf+hivzqrO9WJ0cLQ/dy+X5H9QBbZYaU/ogH4cV8ma9zrl6f+m8n/AKEa+rmI/s7TAT/yzH9K+SNcZv7avOf+W8n/AKEa/pvwSm/ZYjXrH9T8Z44X7yHz/M//1v3+0yUtJdHv5Mn/AKCa/CTxcf8AjFb4qE/9DVb/AMhX7paScSXWe8Up/Q1+FPjH/k1L4psOc+Krf+Qr/FOKf175M/00yZfuD9VfF0n/ABgLqWe3g5//AElr8Jf2D2LfArSwfWb/ANCav3P8XPn9gbUx/wBShJ/6TV+GH7CB2fA7Sg3dpT/4+1fS5E/9hqX/AOfkfyka0FavK/8AL+qPyH/4Kzqf+Fpadx3I/QV+V6f61vrX6q/8FZSG+KOnf7zfyr8qOjk+9f6XeCr/AOEWH9dT+IPF/wD5HVR+bDvilCK4IcZDKQR9aYQSS3ep06V+tPc/JT5m8aeG5NCv8xgmGQlge3NcXX2Fe6ZY6vAdP1Fd8ZBGccr7ivC/EHwy1jTi9xpzC6gXpj72PpSA8xoqR4nicxTDYw7NwaYw2NtagBKKKTK0ALRSZHbmgHNAC0U4LmkYFeDzQAlFH05+lKKAEopcZ6c04I2QCOT26/yql1GnY/oJ/wCDbfxjceHv+Ch2l6FaYJ1yxuLJ89lZS2QO/QZr+8LxjfXOmPcLcGAX8MjQIsAwTHERl1+gOcZ5Oa/zi/8Agi34uuvBX/BRf4b6pCGw+orA23P3ZFYEHH1r/RsXQdIsZJPFxeGWykuM+fI5byZMkujq+RgsSPTnpxX8XfSXwbjiFPuj988MsQnh3FHNWl9oviDTl1+O5linV9ss8iHd5jnB2/MM7gMhhnpg4qpqFlbw3bW0fmSTWlsLqeJRhdqZIbd1UsP4TXYatfP4vun1KER22IUjhdAqWoMWTtOMBm3c/jVdteubW3to5bxbfSb5BDeAxruknhBJ+ZhuKOcAZOK/jaqrTP2ai7M8r1+DV7u1ivdVV5dPv8zedKPvPgBlB7gEDNU10uCLQpZ/Ezut6jD7LFCAqMnBBLt06cDrXr1rbx69pdvd2dsL4C5e3/syXKkDn96EX+Ej07iuThk/4Rxbqx0y6ErqxR3KmQQr6EvnnrjtjFbwq6WR1867lXwprl1osx8UvaLfJtKzwSRqy/MNoIxn5gcYOODzWpp/n33mWSWss+ozsk6OG3FFJ+RTnGSD+lVrOSG81i0065SUNLudlVQCiFM7mAwAM8g+vvW7pniCDwQfK8KSTeeJcxyXKjzZpBwMAg4UVvDL3N2W5xSkm20T+I9b0+2v7TT5LYqdNKpcQRsFE0rHc/PGCScZrzbUbu2WQ3k8jGxleQiwiI3RkMFBdgTyNxA9c11lh4ltJ9Ri1rU4Wur6MyIUCEbbhgSZGwPm2nJ9OKr+Efh/4v8AF2sPL4etLiR7OX7TOGQbZS3JB3EjDDOP8a6VkFd6WZy1cVCC1Zd+F/hW18Tam97rkh8nT8sUkG/7SvaNR+QzX0VpHgrR57B08eworzlnutoAa3Lj90p79B3rlIoL3SpLjxnpNrbWk2p3AjSKWQL9jkVcYaPOFBI5zjmuRPhHxX8QLua61bVLRb58tdwmfCSAL8oUqcH69q9fBcLVnJaM8/EZtCMb3OvvfEXhOwn07SNV1NIINNn2W88Z2CY7MImeSBg7ScGv81j/AILS+EIPB3/BRn4i2Vogjiub0XSKO3nKH/rX+ltpFr+zv4P01de+KniSz0z7GBthmnhKwlev3uT9cV/nm/8ABw9qXwo8Qf8ABSDW/EXwd1e21vSr3T7OQ3FpIskZfywGG5SRkY5r+v8AwHy2rhsXOUlpyn41x7jIVqNoPW5+FeCSK/T/AP4I6eJF8K/8FEvhhqjSLFnXLOLLcA+ZKqEZ7ZDHmvzIwq/NX0v+xjrsHh79qnwFq9y5jit9esJHYdQqXCMxz24Br+leIIKrga0fL9D80y+oo4iLP9abx/Zy2Xim78KvOskNvKZrqcKAVtgAVRgPvFSeM9RXN3Nv4O0q6bUPC8sj3dyNypEuWDFMMUQY64yM+9en/EPxBpfh++i12SCCXT7yFZZGjfdPcRyIoXcOuATj6V5C1lbRahbDw9L5OsPiS2VtvlBXXKxktjDdh7+lf5V8WU+TFSj5n9Q5LJypJspWUNxJqNyNJZ5b+QGW9uJRiPycHkD7oIbqQcg8GsjT/sWhW9rdaLb/ANqRbl2RzjYTMQTJvQf7PQmrej6VcaWl5oGtN5s+8eZbAn7SzhvmIHQqc5J6fWu00jS7Lwnb30eowhJnvlSPc28xqIs4AzgNg4JJzXxc4tH0XtFsUfEDWGqT/aQztvljmjtIVxsUMpYMwI4GD0r+F3/g6W+Hr+D/ANtDQfEghEaa3pjXAPOTsmK4OfTtX9ymveO/DenaJeX2lTwJNk2yRMMMxzjOfTPXtjvX8fX/AAdd3Nv408XfC74gWUARP7Je3dgQcsWD9R9eK/rH6PGKdPNIxf2lb8D8l8RcNzYeyP5M/hh4ovvBPjjTfFunOYp9PuoriNh2ZGBBr/Vu/Z0/af0b42/BnwX8b9C0Rda1DxdoVuLi5PzpEYgqTqVAPzo2SQSM9B0r/JVSVo8Muc9/Q1/a9/wbMftcS/Fnwlqv7CPiW9W21XSZTr3hyV5WRnRSReWoIIO1wVYDnHPrX9A+O/BrxuX/AFmGrgfD8BZtTpzVGWlz+oy50vULbVblLyJsOjiO4VT++DR/KiKSWG3C5BPXNW77xHrniq++33cMelT2LIqonMSqvzASE44JGDxkE9K05fF11JPeajJYXFzYWTfZ3EQ+SGQY5Rjzwwxxya3vEfiTw+PClpqesaa408FPsxjzulLDB3EdixHHORmv86szwzpS1P6HhUU9InO6hp3hDVbeLU7QNbR3YkdELDalwnVCTxsbkj+lcNF4b1awsBquik298SJJYkIzt6hgB6cZrVvtXv8AxhcifUYEgNtEqy2MA+RYuGSRuAyvjGcgcVHFeeMreK4uxN58LMsctyQu1Y8keXnsccD14HU4rxaeMnTneLNeRyVhF1K5+IHhXV/h/wCM7W31TSdbia11OG7GI7mJwUcNu4z/AHSOc1/Ed/wVc/4IJ/Ef9mvU9Q+OX7KEUvirwBeO801rCfNutOLctGyoDujTO0N1wOa/uAbTNOS/uIdMBMhiQPAx+5klg553K3cHGRULvrun6wINKvYbhFQrNaFUe3mBOWEmcDOeCe3vX7d4ceLmOyedoy5oPdM+O4k4Lw2NjdqzP8imeyudMuXtr9HhkU4KuCpB9wajeYwKfLOe/wCFf6VP7Tv/AASJ/YL/AGstaOsfEPw3J4P8Q3+W/tHSFxDMdpJLBBs6DONtflL4g/4NVfh54qtJNV+CvxYt763ilaObzxGBEAejFW4bHqBX9n5F455JiKXNUfKz8ex/AmNpVHGKVj+KfDkHZwq0n71TX9m2gf8ABqbpz6xbxa98UbdbVi4kMAjZy4B2hAxwcnHU1+knwB/4Nxf+Cdfwivli+It7deL9UtMTlrxmjg3ddjCE7Tz1BPfpXdi/GrJYRcozvbysedDgPHznblR/BR8D/wBl39oD9o/XIvD/AMG/C99rEzuEMkMTGJNx6u+NqgdzX9an/BP3/g248M+Dn0/4sftx6mt9OpWSDw/ZHMTyHBWOSXq3+0AuK/pj8D/Cn4cfB7w5beAfhZ4dsfDGgichjZKv2hl5YlCAvyk8ZOSBxXvWganc3sUkOkoLi8tHeG0jchoyGGOWwGGOuTzX4Zxt9IXEYinKjg/ci9u5+h5L4c4ejadV3f4GB4M8C6J4Mt7L4feG7C30qy0+2X7Hp1tCscCQg/JnZ8u8Yye/rV2S1mma4mMIjaNx5wHzklSPu+gHWuingubbQLOzs51jmMiJd3QJYrKrZdCewI4PtUcOp67bXt1f6pbGzSwRlEIAY3IbGHU/xDjjHSv5RzfOJ4mo5zd31P1CjRUIqMVoX9N1eTxJPPNod9FJaxJ5LM6jD44ZB75xz+dZWoeHLuygg+2TbUkl/fMqjdGONiDBGc4qaPUtSjis9VsLKOBmQyC12hDkjhnUDHfmuf8AsOp3t5ZS61cIq3pdpFRiYywyA2eAOa8eizQ7W00/w1rU4OnfuHtGJuvNJGY88bcnkHue1fzv/wDBwl4Z0i31XwD4wtirQpIQj/eRQzDaD3P1Nf0JzeApL7yBYM82pRsAoiyyMM5CsD2x9ea/B3/g4xl8E+Dvgz4F8M61q9rF4qvNQgKaYGDSspzvZVHOF49vSv6O8D8JX/tCMktD8343qx9hKnc/Dn4NTw6D8WdG8Ra/GoEOo25Qg/Nt8xTkn6dK/vC8Z+Modc0ltd0G6jXT2tIo40AAO8RqxDk8d+tfwMyyLYwxak0uSGhk3cfKquoB5+npxX9zHwk07RvGH7PHgr4gauIvIutFimkMWcTAoq7mXpnjkiv2D6Q2Gap0prsfJ8Bzi5PUytE1y3tyt3YRNNANv2ldxYgc/IC3HBOeew+lS3qaXqOnDR9LVka6YyJLkEYBwq8gdCPXNdYug29rewRabMd7ymdZP4RCDwCQAuWGBzzxS61pLzaZfLajaqbjvCHy1kzklGA25z1APqa/hnE/Gz9wpxVlY8ZXU2tytzAv2lQWgnYj7qE7S69eeO1aetRXcKWltZx/8S+7jZX3OAeehPQ5ODXXaVo2j6fJaf2o3nRW6cQKMu5Jz823sAcnPQdcVnX2kfbtXXw/a/OEfzXER+VVPRQenB6iunKp2rI0qJOB9U/sPX0qeLNX09ofssP2eNIomPzYjPX8e9fpmzLncDX4Gz/F/wAV/BnTb74teF3tri9tJxHdrktH5Zym3ng8gEjj1619OfDX/gqF8MNSi07TvHVvJZ3V0AGeIh41zjk557+5x9K/0Z8FsT7bJeTs2fzZx6uXHNrqfq9EoK81MBgYrivCnjbwp4002PV/Cd/DqFtMAVkicOOQDjIPXHUDpXWrIenT/P4V+v2Pi2tSwVFULhMRsQOgq+N3eqtwQ6soOO2amcbpoV7an5R/tC6Pdy/Gq4ZoiYpYIt/ZduSCQfUe1ee3si/2nPpsQDWcbr88R3Iy7QOV9QetfVP7RunXVr4pTVRKpVoVSJMc8ElgfUGvlmO6u9Ati2nxxtbl1neMAGTcxyQc5+X1r/OnxZpcuY1V5n9K8EVlLCwdzrrLQ7uHTHZnUtvyNw5CkcFfSoNWN3pGnLdWsxKwtuZsYMxP8OPr2rz62+IWlWuohr0O9uuMbF+8zc7SM84rU1H4g6Xqlu1u1hiKzJMUAODlgSCcfWvxVJ3PsKlFyOkv5tH8T2o+xoyL8sskmzkEcBMd/pW34atLSC/tr2YNEVkXdC56AEYxn1615XF481CHR5La1WLL5kVcD5pCMgfh6Vma54p1W2ntdYv0O/bGGjLEbjkZcDpX23BWLdHFRdup85n+FToS11sftska3mnjb1ZQc/UV5pqCNp8jCZeT0PtXc+Dbs3vhqyuiMeZBG35qK1dS0221GAxSpzjrX+nWUYhVMNTa7I/mPEK02jxszNIhJUMp70unuuiXp1C06uAHQdDTda0y/wDD93ypNu3Jb0qkLqOW38y2bhu9ekYn4r/8Fof2Xdc1HTrD9rX4Yp8+kKqarCin5kHImOPvcfKT2FfyI+LfHOjah4xn1FJpPJuI2yXGQGJB8v22npX+jNe69o9zBfeC/G8a3Oi6tC1tJHIAyBHG05B6g5r/AD5/+Cxn7Knjb/gn38VtXubG1kvfh/4jZ59PvI1JFu5y6qSOM8H8MelVHcD8O/2mvGsl7b3lot1J9ojU+YvYYbgkeuOtf3t/8EqPibqPxF/4J0fC/UY0Vo7bS0tJWJxuFuTESG7Y21/mseMPG13rtvPK0/nS3m+eaVvUggL7dOlf3bf8EEPi/wDDI/8ABLTRrL4m+M7TQ00y9v7ZlnaMFUM24FizAjrX434zZTUxWWp01dp9D7LgjFqnV5ZM/bizuNR0qx/sjW1M1uCWjuMZ2jdkIx7irWnazf3l6bDT4o0SEjyXb/VMO+ARjjt718YfEP8A4KQf8E9fCNtFDqXxe0Q29swE9ss6hpCOOSM180/EX/gvT/wS7+H2yfTdcbXCoINvYhpdvum8KoP0Nfx9hfCfH19YUm/kz92pcVYenTtOZ+wNpZ6neySTzSx3620+UbAAt8kbg3qCM8Vj+IdTOlzte6ZD5rQNiK3jXJV27jH3getfz8a1/wAHR37E3hWCbT/hn4K1aZbldk2+CP8AeH1OXP8AKvnS7/4Oatan1CK18B/D0iDOyGScCOTDH244r6DC+BWaJxm6f4HlT43wCbXMfuh/wVC+H914k/4Jy+PrCOOW/wBQubCW6uisRVImI42g8Ajoa/ztbSxlHgCSJo+dORF5z1DEHrX9Meof8Fmv2sf2kNE1z4Op4ZsLLStVhkFw09ySBGVOd4JwcjoPWvws+I3hjTW+Hus694cHlwQsY7wEBR5uT90An5fSv638MeGsRlmElTraXPxni7M6eLxKnSZ8aRz+dGGcYOOlOm+7WfbFDGpYZOBk+tWJJcgLX6YfJDuCuMZpqld2AMY61EWI5UGn7i5+6PxoAlwCD65qL5jy3WmgkjIGO1OU8H3oAfGQDk+lDMuKjHAxT1Td16UAIOop527jmmcg/N2pS2TnFADgqHgGl8tf8/8A66aGx1H5UgYjigBMGoLkHyGNWdwUFTUN0dtq2fT+tRU+Fgl7yP7DP+CMIz+yxYf70n/oZr6X+D3/AClj8Cn/AKd5j/449fNf/BGAY/ZYsM+sn/oZr6U+DQL/APBWDwPj/n1m/wDQHr/Kfjd2zzEP/Ef3/l3/ACJn/gX5H9E3jwj/AIQjxF/143X/AKLav5fr7/k3T4Kn/qbbr/0Ytf0+ePP+RK8RD/pxuv1jav5i54w/7N/wXf08XXQ/8fFfnEKnvRO7h/Tm/rof0vzsTbaQf9lf6V8qayB/bF3/ANdpP/QjX1RM2LfSlPZF/pXyxrP/ACF7r/rs/wD6Ea/orwWleniPWP6n4/x1F+0h8/0P/9f96tMl/fXP/XGX/wBBNfhl4oO/9kz4osf+hqgH5Yr9wdKXM1z7RSD9CK/EDxKgP7JPxPHr4qh/pX+KtN/7d8mf6b5JBui2fp74slx+wbqQzx/wh8n/AKS1+Hn7CIMnwS0jtky/+hmv228WE/8ADCOpj/qUXH/ktivxS/YNXb8EdHA55l/9DNfQZE74Co/+nkfyZtyNVZN/y/qfkB/wVlJX4o6cfUk/pX5VlsuV9zX6u/8ABWlVPxM08/3SR/KvyciO5iT6mv8ATHwUX/CJB/1ufw74vO2bzfqT09WxxUf8JPpS1+tM/JCYyLjHWkUkPtHQe/8AWoQPelPLbs4pAZWr+G9J1hf9PhXH94cNXnWofC+2lk/4kcwVfSSvW88YNJgbdtAHg03wq19CfLkib6Ej+lZ8vw38RR9Ilb6GvoZcD7o3fif8adgDnvQB80v4D8TRni0z9GH+NZFxoGsW8nlyW0gPspP8q+rWOeTg49QP8KngneP94p2/SgD5LTw5rkrfurOZv+AN/hVseFfES8y2Mw/3kYf0r6v/AOEi8QwPixuWRfTj/CibxLr9yu25unf64oA+YofBHiq75FqU+vFalt8LtdlYG5KJ65Ne9C5ncFpwT+NRNMjdR+tAHlcXwktlCyXV6OvKomT+ZP8ASu80Twd4E0Qia6sW1Bh/DM5C5+igH9a2RPgYGfzo8/seQexqk1Z3A+pv2OfiFb+C/wBq/wCH2qaLp1pYxQ6zbBRCgBG5wD8zc/xf57f6J19HeeHtXl0zQ7NL63uxGJ7aWNladmHzeVjhyOv9a/zIfA+sXHhz4meG9c0+QRSWmpW0quwBCHzV7fUV/plWHii+js4dXkv/AO07me3VoFgKo6EqN80W0cHJzzx1r+UPpHZf8NR9UftPhbNcskQjRtMnf+ydOadrWCViLebCC2ncALuBJ43d66jxB4mFvqFlD4lsIDqGmxrHdW8q7oriINhJF2kjO35sj0qTw9r1lpdwLyysPMttVRxc3NwDJHO2MhQ+MKwOenOa8ujuhF4lugttcJFZxmK2abnZNNwsLNjawAPy/rX8P46lep7p+5e0S3Pd9A069azuNRjt5bXV7NlktpUxsFswYgBc5Oc855xiub05mgvriLXY4LaZSPLhYbYZoyu7JlGTv4xgivVPC2m6LoT2/jDSLae/tbT9zbrNKPM85xh45umRnuR6YxXld/rVjo2heIfDmvae5uL2Xfb25yD5gO4lSeUG0gZzg4rfLcNzSUWc08Q1LQ/PT9tv/gpb+z7+xhrOnXPxpk1LUNV1iEPDb6ZEoVQfV3ZSVHOF5AxX5V+Pf+Dj34FiV7j4d+ANYuLgHaHvGgUAj+7t8xhmvD/+DkTwxDYaP8NfFE0Z+1i9mt5WwTwsaMqh88gc1/OdMqtNLhQqls4AGeR69f1r+6/C7wjyjF5ZSxdaPvvc/F+MOM8XhsU6NPY/ePxp/wAHDfxz1e7F34I8F2drIilImmZ8BSeQQu3PFeMXv/Ben/goHLHMng02Hh+SU72ltkbdxwMbyQMe1fj0kHzYAp7QMo4Ptwa/ZcJ4ZZLSV1SufneK4sxlZ+9I+8PFH/BVn/go94yv59Xv/iDNaNc8OiRx7T7428n1Pevnj4l/ti/tj69oM2ua/wDEzVLh8hDHHMYhsI6YQgY+mK8QljLMG6VBf2P9q6Lc6OTzMh29PvDkdq96jw3l1JWpUUvkeZPOMTLebPEdV+KHxD8RO0uu6/qF256mW5lfI+hYiuGnupbmfdK5kPqTVW4iksrpoJlIaNipH0p4wp3AV61OlTjZRil6HDOtOT96TJn+7Xd/CfUG0b4i6PqqEBoLqNxnoCDx+tcDnecGtLSZTaarbTIcESpj2561hjKSnRnDumVhJ8taMn0Z/rpeC9T0LWvhz4N8WPGt1d614XspbvfLgLEY1JdVPDEHgkY7Vs6JYeF7K+/t7WoyLVCIbSwQeYZmwfnJJ+VQcbu4IOPf46/Za1eDWf2U/gt45utQF1pcXh61tblMHzfOZNqlnXkxjHK19JQ+GtR0TV5LnxJMkazqyxANiNozllZccq2zK+pPPNf5X+JVD2OMl6s/rHImqlCKXYt3Wof8JPZ3DLPBpU0expULNJNJEvzAKBg59SSKkm8N6vqV9Hpuh73aUN++uX2fJGuWkZVDfMwOFJJ+tczZ3ulQwi7t4/st2h4iYM5nfBIZ2GVIAxlSB1555r6Bb7W/hr+37+2gtbfUAqpGjckRcqy/xY7sOgr82nUb1R7NktGfM0mmeJ5boQaWLfToB5j3Ej5MzRBuCm4EMxUEjHHtX89P/Byx4Mjf9jzwJ4r2+Yba+ghWRxhwrxygg8DrtX2r+ouTXp7DXZG8XwRXMVja+Vd+UFaRwy/u9rDngda/A7/g4r0EeK/+CeqTWb/al0XUraYNkMUjO8gMR/d34zX9IeBWN5c0pPzPiONKKlhpd7H+e8vyqAw5r6C/Zi/aH8cfstfG7w78cfh3dPaaloN5HcAoxXein5kJH8LLlSPQ+1fPBlY4yO2Py4o8xiQfTiv9FMRRVaMqFRe69GfzfSqunJTp7o/1rf2W/wBp/wAG/tf/AAB8PftA+ENVa40TVrdA9kgRja34A3wzsPmGxjjJA+pHNep+LrxotEbUJ5JLeZIGC5BKqwIG6KNcbsjk8DjOPQ/55v8AwRh/4Koa1+wX8XG8F+O5Xvfhv4qeO31WzPzLAxwouYt5wsidc85Axiv9AOeTw94z8CaT41+F+qL4g8Oarbiey1QuskTBsFUJXO1kBIKnoa/z48Y/DOvl2JlOEbwlqn2P6H4J4jhiEqcn73Uwb7w1bXMb6ldvm7gSJZ5E3KxTezHYT94EEfeHHQVv6RaXa6ct19t8zTrdgggf5BI2flOOMuhz3IPX0q5qUH9n7NLjkSfULuLeHdQUYx4xG/8AD6gZGcc5rEtr2yu9TgudStZJbi5DRfZgn7qPaPlUg5OFH3STzX8z4jCzi3ofp1JxOq8OQWUfiSedCIpWaMXmo3TAIo5KockMcA9QtdVFfMbZVgtk07TYXd5ZGORcDPWM8nkc4IH1rgI7UQ3ub/T5LjRZG8to0BMiSOfvsRk7P93AHalsDqmkh9Iu5JLyzRwba5dhvQg48pvuiQHoDgZ6dea5lPki0tzVU1J67Gwl5bwPeaqBdzBW3CAAM0IyfmVeBsI43dcEcVy+s6fbgt/ZdtDbRXI/0hI3C7k7yNjAJPTB6+tT3FvOWtzpN7LF5rDyLhsLLKMHdER06AnHpz6Yaf7WijuUXRvtd7Nb/Z2TgsoGWYIVI3YXkj1rvp5jXhHRmzw1Lld0b/2nTrjw/FcaVPFDp+mgQqipi4jkAP7yRec9eOT9amePSrWVdR0uR5/LVN0TldssjA/NKPvLg5xxXCSDVItPe4t1X/TUEOMBbhBEBnfjgkdzzzin6IkUGmt48A+0WTssM8/mKszDGHVowRgqeBlcn8qqnnWIbtzGKwVLex21ve6YmmmCbSJjPfuv2p1ky4XOSsIHBU9DyK6WZ5UhFnYXaCW2k8zT7GHCuVU/NvI5LY4wTXAXscUVyNSt0ktLGGAtaSF9okkY4UnryCQCPareqyRaRdafObYjUHaPdnJYMwZmf5f4TgVlPF1ZatjeChbY9c07VLa81ddTu7U6fDexCS7QZZ4mQc+YhwMMP4hn+tW7fdfxC5jEVzaQzB7eV2YSJz8ocEfKvOM5JHpwa8Ul1+e1ku4NVeTVLmQP52SI41RkIXaTjcFHUZq99u1DTIbTV4mE63KeXKsXSTgBQFHHHPzfX14ilKcnZI8yrSaZ7ReeIrW2a51W70wyXOBHNbQPuZFIAB3H6gn8qjs7CTw9pU2ua7ayW0MyhDGxWTy8dCqA8k+ma850hPE+s3en3kKyS3EjlfJgHPl7jhXxgHByTnn34Ffnl/wUK/4KtfAn/gm3ok3/AAm95B4r+Iao6aX4ctZfMhsjziW5YHOQSOG/Kv03gjg/FZjXjTpU7vqfOZ1mdPC0nKUtT67/AG7/APgod8Kf+CbXwRm+LfxclSTUL6DZoego4F3dXAX5XZQSVjH8TE8e9f5of7QP7dPxg/bD/a9t/wBo74237XVzNqMMkUG4+TbQCQFYYl4ARR+deb/tiftnfHb9t/4yah8ZvjnrEupXt3ITBCx/c20W4lY4k+6qgHHv3r5Ut5WguBIOCpBHsa/0Q4B8PaGT4RRteb3P55zzPamLq6vQ/qj8VRmXQ0uINs0l7biWKNVBUJkN8pA4BPXn39q/tb/4J/TX2u/sH/DLVNLnA/s7TjDMkvH3JGU4BGMDtk81/EV+zLeX3xD/AGd9L1GZvMuZdOEVvKwGQyMQQScngAAfWv7DP+Ceni2Gb9iDQ7LxNKL+bTWWFkXGFIcuAygfMV/X9a+M8eMLfAU5M9TgabjXaPqjx7LpllcyadcySF7xvMhjVC8IUMu7L4G1QDk+n41r31xb2/h5o7bOyRMW6nG3zGyXK7T0XsehPBrgL3xrZXOuND4hcJJLjyo1BWN4u65YkZI6gHNULjxToSXf9m+HY3MEA2lWH/HuHOMqcZYcnlicACv8/wDGYOp7SVkf0BTrRsi5Boc9/dpN4knKOMpaSKw80ls48xFGzrwQpPritP8A4Vzf2MFpBdXLRi4uFeSCM/MmOFZzkHDUv/COjStMuLyXfd2BlE0jgsZXkPdW7D2qtLqptbOWxtJZrphEu9ZOJnGchUYjB259c4rpwOWVIzUpImriFeyOE/aH8KSW/wAGfEem27wO8MqFHiG2MbPnO9hxu9DzzX4/eBrbV2b7BJbQTw5aWBpgRskyDxLgc8crjBNfrt4lB1/wRq8mpzvY/bIHjtoJGBhYhNpYjP3/AHJ4PSvy107TJrbQ59ETM1r5jG4ErbcFGLKUJxnj+71Ff3X4CVJxws6c9j8G4+hF14zR3Phb46/Ev4b5ufAeuT6beyyokyx7mVUUZMuz7oUDk54Pav2n/ZI/4KWeEfiYbLwD8WH/ALM1edALe8l+WG7KnBOSAFY9uea/ne8T6vr0V9byTi1jezVBbSbQ32mJNrssynI+5kHjmsjW9V0dpZdTR5H3+X9gkQEJGFO5kEY5HPTAr+gZbn56f3Rx3cMsSzRYKsAQQcjB6HjIpjP1IHWvwu/ZR/4KJ6T4VTQvhZ8QZHmspIlRbqXcZIABj5icbk3fiPev280nWNO16xi1PR50uLedQ0ckZ3KwYZBBpJ9xrzPgT9tdL/T9b8Ma1ZJ5kcbTrIhyFJIyM49MGvkbxH4s00WVpbabMslzIvmXHB/ebj/q1wOCo96/Vv4t/Ch/icunQGYQx2cxeTIzuU9uPWvhz4w/BLwz4H1uGyQMIbwGdHHHlsD0XP8AI5r+XeP/AAjxWZZg61BWTP1ThPi2hhcN7Or0Pl+/sku4DqdoBBZyLlBIMNG/b61Hpdk0lgPNlxcwsCUXBE2BgHJIPHcYr6u8K6F4Ra28iTTvM8rgpKxYP/tYGP0rr0Twdbal/Z2n6VbQMCpa4VMyHPQAvvAA+lfP4f6NuNTTqzSPdxPiXhkv3Suz4wttH1pb2NNFWQ2jMVkklTChM5IXG4swPQ9frXsth4F8R32km/8AD+nvqckI/c+YhZdwP8WcEfSvuLxNLpjfD631eytkt/s8m0KoABJXbnj8/rS/s638ly+r2M77yHSTnrkjmvtsv8AMPSs51dfQ+exfiPVqwcIwsmeyfC19ek8B6XJ4mgW2vjbr50S9Fb0A7fSvQgxHSo449vC9PSpCCOtf0FgcEqVKME9lY/MqsrybKV9aRahCbe5XchGCK8d1/wAD3GjI97o2WhPJT0r3IbQuTUJAKkEZz610mZ8J+NpoHgIkA3MCMEdu/HavyR/4KhfCnTv2jP2V9Z8Aa6im4it5HtZNu5ThSdvPKngciv2M/aMtYPCZg19I/wBxdNsfb1Q+3tX5vfGbX7a90GSwmaOWCZSox6E4XI+uM0Af5RnxR+GWreC/Ed7YW0T+VZ3T208fdJeeCP7pA4Oa8ei1nWtPtv7JtLy4igYndEsjKhOeu0HFfsF/wVq+Bet/s7/tW6oscckWi+LlF/bEf6syEndGT6g8/Q1+Q+qwot+AkZi2DDBuucdaLLqNOxvaHYWOpQO2pF2KjPLE1hLFBBe/uU4HY8g1q+G2draXJ68VmyKUut3bIpwslZFe0f8ATPTfDrDy1DKmQeMKBX0V4X1SSO1ObjygMK27DfgOK+aNBmO0HGSK9V0fUVkm+yf3h+tazmmOVS+x9t/Bu9WXWP7H193bS3G791gSs38IJ64z1qTxfp4PhHXo7iFh9nLsPLPygDpnsTXnXwt1i4s9Qtr68fBibDuACTnA4H0r6w1rwc9/pGq22qxOlq9vJLFAnyvMccHGDweuKiUtCGz8oowVAAGRinsuTkVLdRfZ7qS3lOx43ZWX0wcYp5PAPrUCKv7zoOvamed5Z3OMgfzqyzpnbnGeAfesS5vFB+dScHHHc+tAFhrzHBHX+VPScd8getY6Ss+4KdrDsf6VU+2SgbQSRQB2ETDPPTFPdsPtXpjqOlcoLuQJjFXbO8KxeUTwaAN0nIpKiiwV3ZqWgAopwcgYpp55oAcBgfN1qG85tGPoKspyPeql7xbvnrUVVeD9CoStJH9i3/BGJP8AjFiw/wB6T/0M+9fSvwWH/G13wQP+nWb9Eevmz/gjKdv7K9gR/ek/9DNfTHwZAX/gqz4LI/htZv1jev8AKbjt2znEPzkf37lyvk3/AG4vyP6D/Hcv/FGeI++LK6/RGr+Zcru/Zj+DIPX/AITC5/8AQxX9K3j2Vh4L8RD1srv9Y2r+agkr+zN8Gx6eMLn/ANDFflVKr7y/ruejk1Nxcm/60P6UZZA0emD/AKZr/MCvl/WP+Qtdf9dn/wDQjX0hJIyw6Ww/55qf1r5p1eRv7Vuv+ur/APoRr+lvBC7pYh+cfyZ+R8cq1SC9f0P/0P3c04lZ7sD/AJ5SfyNfiH4nJH7JfxM/7GqH+lftxp//AB93WP8AnlL/AOgmvxH8TD/jEz4mf9jXD/Sv8VYf778mf6d5B/u7P0u8Wf8AJiGpn/qUm/8ASavxX/YM/wCSJaR9Zf8A0M1+03io/wDGCGp/9im//pNX4q/sIHHwO0n6zf8AoRr3+Hv9wqr/AKeR/Jm8v4kvT/M/Ij/grZ8vxNsMd3b+Vfk5D95vrX6y/wDBWnn4lad67j/KvydQfOw96/0y8FH/AMIcT+FvF/8A5Gsv66EvbFFFIelfrJ+TC5xRkHpQcbDmmJ0oAfStwuaShQS3tQA0AEZp2M0p6mkoAXacHNRJyCp6VLkmm8DpQBG+1BnFVDVyRd4yKiEftmgCEZJ5qQoMcU5VfBHGe1TIm1cv1oAqhSOozTimRkDFW+2e1FHQqJzd4UhuIZ2yGimjkyeAcN/9av8ASF/Z88QXXiz9m/4d+MrRLOze/wBEhkW5Iy8g8gAqTxnIBr/N+8RLt0uWX+5hvyxX+i5/wSxsLb4of8E4Pht4r8UXcUNtZaTbW0KuBhSsjRli3UHbX88fSDp8+CjNrbQ/TvDWo1Wcb7n0lb6lqE+gNokkrmyMoZLV9rrHLjBkB7cchc1FHonxF0/xdpfiexuIv7LhhE0mlTnKXLxqVSaOLHzuww34V6leax/YtncWlq8V5oiNsuJI41ck4+Vi3UNn2rMTxpD4gFpaxDd4gAW30yXYBBHAn8RfP3ivHtX+fuMr8lVo/oaoixZx+JrGxuoNStZTdxWH2rCLxICeA4GdjjPfFcjL431vXry21XXoRdR20Bh35Al2IeA/HU+vauv0a/s5fK0n+0Gt/tc7rqN87bEabjZCnX5AO561oaDb3smsXR8LReXqFllZQY96mIE4YKxxzySK2yrFXrpWOatG0eY/ms/4OYtNTx5+y/4A8daZpwsLXT9SdVTO4sDHtOTjqNpOelfyXxSLLCkidGRGH0wK/ub/AOC/PhbWPiJ/wTn8SeMrxxqI0NrZ45ooRDHCxnCNtAOMlSVav4T9Gv8A7ZpVrLjhoEH3f7vFf6UeC9fnyaCXRn828eSUsdKXka9FIwB+lN+9yOK/XVLSx8IPqI8SAjtUi5PajAbrxipA8Z+KHh1bSWPXrVTsmyJAOzf/AF68jBbPSvr6+s4NYsJNNuhlZP0r5OubSWxu5bK5GHjZlOfagCsDjmpoHPnqfQ549uagpykqcgcj/A00r/iVB2kmf6hv/BJ65vfiV/wTU+GOpeHorK4EdiYJ3nxmPyHZWwO5B/KvuK28L3EdpdaBr9y67SZYxklIyvRgVzwc8LX4g/8ABBHUrzxh/wAEx9O0W0lL32lahffZ4i7JuJYEqu3uQx471+x9/eeIINds9O069jtbmxRVljnG+KVgFBR2PPXj1zX+ZHjNg3DM6sbaczP6t4WrL6vF+R2/hjwXFf6iiXUv2O1sCXlt5GJ+1KgyNjHqW9+gqaG01280Cc6PNbxyXAbyYHmQMkXLOFB/iOOh61zsWqR3mlTjVZk07UbdQ7WUgJEzcriJ+yZINYdnNo8TTz3ltM1xM8TSchRaycAFCOXBX8q/GqjSWiPo9L7kUfiqy0ewRfBSgm6t0tRczJmV3cfP357jmvhz/gr1oXhTW/8Agk78QLPQg91PpsUsk8zIQ3mboyQc8YHAGPSvuKz0LSvGt/DNeXrWL+f+7FuPlt4VbDksP4m4/OuK/b/8MeFNX/4J1/F/4daNcR6mraVOYnjGGDsAfnHPJKHB71+teE2KcMfRl/eR8jxXBSw815H+TxsMjM3ufyqJACa072E2t1Lbd0kK/kaqpGM1/qGp9V5H8wSjqTKATg8A9cf0r97v+CT/APwWh+KH7Cqx/B34nJL4m+Fmpzj7Zpztl4AeC9ux+64ODjgHH41+DESKTk4rRVgzAHmvGzzJ6GYUHh8VG8Wetl+OlQmqkHZo/wBZD4G/F74J/tSfCCz+Jv7O/iGHX9IJDraJIpvbdm/gnjyGUgHjPXHGRW0GmZ5X0J7h7yNxDdy7WYBF4KYIBBA4HFf5fn7MX7X/AO0D+yD43h8ffArxHcaXPbkM0G7dFJg/ddCdrD2INf2W/sQ/8HPP7OnxP0+08IftoaE/hnXEKD+19MBME75wWmQEFQec4LfhX8fcefR9r0XLEYBc0H06n7FkHiHTlaNVn9C2leJLy+0a81S1uzbWkC/ZYHZDE0jD70ZB5Jx3A61ydg+p6drVtZ+H7dbrVo496faP3lvGg5+Yn+LPIJ6VseAfit8BPj/ov/CU/CvxnpfiPTLnY9qkDKGtnYt87ru5I6HPNa2q+BfiZp2pQPo9oLpXU7byFt6TZ5VGU8dODu7d81/OeacE4vDStWg18j76jxBSq6xkUbfTtOaCXVNaZBHMw8y4Zd0jzFj80IxuUckbumD6Uuv6T4gh1yx1Sw1CO3mtozJCrKSS5OfnPIJK8f0qzJqGrj7Wk1l9lv4MpI86/wCjbADkKSdu8dqoWepaJ4i0Gx1PSpo4PDtnulvbqVv3plB6Ln+HPHpXzdTI8RF2selHNacjk/FC3V3Eni27uRaXuqShVx96NzlXcrgZBOBwASCCOlc6LXU9E1qa3glinW+ZGad2OA0Yww2MPvZzya6q68WahrmoS6j4UsxcTSSLIftIIiigA6gDuRyDmsrWfD1zfWkmpWVjeTR3wYugRl2Ad4gTyctnI6itcPw9iHLY6KeOpvRMdqWq/aLO+trxzeSyEItqy7RGhX5nU9Mkcj3xWZo9zNf3EttNcyNcpAFjnkzJ58Qz8sYHQrnBrvtL8MXsvhGDVb6e2itdpRFmdVuGKnGCDkjGM8818d/GT9sD9lD9nq/N78YPiJp9hDpm7ybC1ZUnXIy/KZZiT24r6jLuA8XiJqMINv0ZyYrPqFFO8z6KDXtndR3evBrO2sk8mGEqZDPu+XlFBOSTjmtjxZ4z8FfAnQk+IHxu1mw8K6K2+5muLkhTFGeQiKT94g42gHP4V/NL+1h/wdA/D7wpbSeFP2SfC/8AbN4kbRprmq/IyOc4KIOWA7Enmv5Sv2oP26f2mv2u/Ek/iX44+KLrVmlfcLbzGW3Q8/diB2jGcd6/ojgr6PeJqzjWxa5Yo/NuIvEalGm40Hdn9Kn/AAUY/wCDkO6hvtR+EX/BPWGTS9NjZ4JPEdwP9JuN3DtCh/1Yz0PfqMV/JH428ceMPiN4pvfGfjzUp9U1bUJWlubq4cySSSMclmY5JP41w7ueDnmlWYgYPNf1nkHC+By2kqeEhbz6n4tm+c4jFSvVZPIB1pI18xvem+ahHNIZIu3+f0r6G7PMVRdD+i//AIJZ+J7jxT8ANX8LZM9zpk7JAp4GyQbxzng8V/Un+wd+0/8AAb4S/s4Xvgv4yPdw6n9vN5stEff5eBtAI7Y61/HB/wAEb/Eyjx/4h8GKGkNxFFPGinkkHaePTB5r+jnR/Cd7peqzrd6eJ5v9S6yfKpjOARH2OAa8LiPIKOZ4dYevsd2AzKWHlzw3P1Lvf2+f2X7+5i1C003UZNOt5C1n/C2xThgQ7Asr9eOmKzLz/go58PoL+e58NeD5FEnzp5koDbUGCMYYY9eTX5naJjR2nNtZxvbacDawPjKxOygfMOecAmvVtOt9CTUoru52m5itnkSOJQyy5QNnnkAnAwOO/evgKHgvk0Xdxue5U4zxb2Z9NX//AAUg+IdzZxTeEtJSztpW8qPcsjNHgHdlm2rjI4Nefah+1j8cPFt+Io76C1kjysc5iHlyy9VVV7nBO5ulfP7eGl1qW6urWXIjjkQhVVo2ZmBVE6dckE+maml8NxwX1lBpcIZ7uAw2qnG23fJ3bmzjOM9elfTYPw8yijtRT9ThlxLjZ7zNDxh44+PV1qFtrGp65MtssrZiVFEIYY3K/A3deBnHpW9F8aX8QaLLoWru092DHE8au6siAkdF6HHBxkDIrnNVudbOjpYwalvhVo47gBekowrAZz174rlNZ+HGu6vqza3aQE39shxDECuIjz8xB5wBkg19HgsnwuHg40Ict+x5uMx9Wq/3jud4ms6Vc2Q+3wFoYiqoFVnmONzKNxOeW+VunT0rmtE12O01GO6vnVJLg7ZVk4a2aTPY88LyK9u+C/7Onxi+M+trpHw/0h54lg2yzFcxh2AYHc2PL2A8DJNfs78Lf+CM3w7sUTUvijqct7O0cbTRRYwZQADl+49v1r0rHCz8YYNWSRrPUjMZrlBst0Bwzqo+Vyei5bJxwc8mvtv9nP8AbJ+IvwYuo9F0+4N5Zu5aWzZt8cWASxU8hcgdRjmvuXxv/wAEtPDOkaqL3wBOVsdpDRyfM8bY/gPpj64r5i1v/gm58R9Fjez0G7+0Rv8APKuNrFI88Z75oQj9pvgL+1D8OfjrpoOhXCwX6qN9rI4D5749a82/bRutN07w9p2pXbkSI7/KecjA9fQ4r8qfhf8ACH4o/DLxvZeLZoJrAW5SaXcuI0hiPzZbgj5Rn36d67T4/wD7SNt8YPEsupAtHpFirRWKPjMrAjLsM87j+lXZPS4pRTR7x4L8VTaurM0nmPEQUKccenbPQ1ueOrvUtHmtvEgYC0vOFTcQyt3yK+GfBfxCaK/86QHagEileBvc4CsfRcZBwM5r72dovHfwsOoKAZbcb5SDnyxnHHuV5q7yUbXuU30PpP4fXcfjj4P3yoSBaHepbpwKo/spS38/iTxC10QUCxBcetcp+y3qP2vwXrnhov5h8jdGO5GMGvYf2dNJisbrW7yCIRoXjQMP4vvMc/Tdiso2RpDY+pt23mjdu5qibu3Ri0rjA4x1Oa4rWvGul6VCZZJ1XIIUFsHOeOKtSREtz0Esv3SeaaWXGN1fnD8Wf24fAXgRJt900ghnjtZnj+bbI/GFx1x1PpXRfCj9odfiPNea7bOyaLokT3FzeZIXESg7eepfNQyTk/8AgoZ8TU8JeHdJ0G0kX7XO/mlM87Qcc/UV+H3jT4ms+sNexTxWSID5tvO+crgjK9T7/hXH/tkftT+Ivib8TNU8bsxe0hJW1hZj5bIgOFX8v1r80/iB8Rtf8VW8ggg+y6lf8lJPvW6cnjpkEDr6UgOJ/bq+G/gz9r74can4H8WXNrDqttK0miXSHDx4AwW4ywJwDzxX8c3xO8CeLPhf4uv/AAT40iaG/sZTC+7+LbwGB7g9QfSv6nPF3iu1lkWaGIPOkQidQSCXGPnJ6Dn86/Hz/go5ZWniG40/xPqrRtr1vGqXLRDCsmeB7sPWgD8yfDbShJYcYKjOPWnyh2nAcbeaZ4ZklNzI56gVbuxItz5jUAdRoTLFzmu30m6EV0kgPOea80098L6Z7102lTzC5x2oA+svBmrGyu4pY3AG4NzyMjHX2r9NvDD634i8UzapcgSiW2QI7DG4snAQdMDBFfkd4PnKSwhz8xPH/wBev1L+H/iueex8PyZIb7NJE56bSvRvf0oA/K/4h6HceHvHmsaJfjbNBcShlPXhj/WuOySMV7r+0fazQfGfUZWXi5UTbuucjOa8MKY6mgCvMpAORxjmqLWMRYNJncBgkVrq204kGQfaoyHfPIAPQjqPSgDKGmRgdD7fSmvpiBTx9Oa3QzjBbqOD7+9QzIGlOKAOVe02sQ/y4qOJGR91dO9uGU8Avj5DniqD2UioNpBPcelAEdq7plienJ+la6nKAk8mqSKiRbT1HFW4wSg3fhQBZOxevQ96YetG4jikoAlXhsCql6MwuT6VaQjHNVb3/UP9KippB+gl8SP7G/8AgjUAv7K1ifQyH/x819LfBv8A5SseDD62kv8A6Levmj/gjIc/sr2OT/z1/wDQzX0l8FyP+Hqngv8A69pf/Rclf5Scdy/4WsQvOR/oFlj/AOEf/txH7+ePv+RM8Q/9eV1/6Lav5rDz+zL8HD/1OFz/AOhiv6S/H5/4o3xD/wBed3/6A1fzZOcfsy/Bz/sbrr/0YK/J8K+eSt3/AMz2cqhe/wDXQ/o8kYmLSx/0zX+dfOmqgf2pc/8AXV//AEI19Es+YtK90/qK+d9V/wCQpc/9dX/9CNf094HR/c4j/tz8mfjfHqtVp/P8z//R/dfTWAnuj6xy/wAjX4l+JBn9kn4nEdvFUP8ASv2u084muR/0zkP6GvxT8Rcfsi/E7PfxTD/Sv8VYf76/Rn+m+QTf1dn6R+KSB+whqbHp/wAIk3/pPX4p/sKEf8KR0sHs0p/8eNftR4pO79grVMf9Cm//AKT5r8VP2Fzj4J6d/wBtP/QjXu8Pu2Bqf9fF+TO2Ws2/I/JD/grNhfidp2f77H8CBX5SgESsT61+rP8AwVp/5KZpv+0T/IV+U7HLH61/pr4Jf8iOP9dWfwn4uyvm0kB60h+XrRQ/zn5a/WD8nAYb6UHaOB3pqjJ3dxT+Mc0AIeOTSbm7dKQgkYpVGBigBc849aDwcGmgc81IR3JzQAgIGc1H94Nj2qQY707jacUAQp/d70Kp3kUq9T/OntnsM0AR9eWGMU/qMjmkPQ0K2F24NADugwKMHGaSmMGJ4PFFrlw31KGqww3GmTiXONrD9Aa/ue/4IU+LV8d/8E/NF8Ma1qJ0/T7CeW0M+5sIYyXAIBI53V/DbMvmQyL38tx+Yr+xb/g3DGqav+xL4gsdElQTw63cDy7k/uSojBycDjpX4x464P2mUOa6M++8PcTbF8p+6zX/ANjszpM8giSKYvFIB8ssTHmXAzkjtmom8C77e/1nwrbi+tPs0c329nKPKrgKUhU4AYEc9M1esfs+s7dV8VM0VxbLsb7MmIrgbcLHGTnbk9emaLnVtLEVrrWpIN2lbI4tP+dUSJ8DGVxvZMkkjvX+a2Z03GvJH9J0q0eTmFOm6dZSDw5dwPdrCibLMY8vzG+baXPzGRMg8cn8K763uPBp1S38RSzXsd5DIqPHCC0coCgbNuck9j/Ku40nRfD3g/xKRc3cktk9vusXCnbLNL0cP2dckc4xnt1PP3nh/VtI1iG50++mvtQgcyAxxKYo+oGGb7z4/Wnl0ZwrRdjmxNXng1E+Jv8AgsHoMPi3/glt8SPCOlWo0ky6eZ49PQfMPKmWUu55I3AE46V/mz+Fvm0G0dT0DR8H+45xX+pZ+1Va6BD+x18SNJ8ZS/2hqeraRchIGXdMFEL4Mu3IXkZBBx2r/LM8HoyaXLA2QEuJQAew3V/o74CV75W4vdM/m3j+Evrex2J6U7IwBjFEY42ipiFJzX7kfDEKf6wCm+WzH6VPtXO6nfSgCJS8bgjrXz58TvJTxZMYU2jCk+5IxmvopdqNuHNeBfFa1Nvry3TjKzRrjHqKAPMwMjdSr1/A1Am4tntUwGT+FXBLdlR3R/en/wAGx+r23jT9j3xb4WmJWbQtZWSGZWw0LTR7lb0Iypr+inw74UsvGWlXetXF4k0dvIW1AMCrzygnGDkY5AIx1r+QH/g2M+OXwh+H/gv4teFfiv4pstBiu/sM0MN5OkJm2eaG2s7KOMjOOa/oI+If/BR79gf4VY13xJ8U9MZrTAbTLVxLDKoAX5jEWYkfTrX8TeK3AmLxmaTlRg2m7n71w1xDSVJRcrH6EavAtlLpcN8ofzGEUF5KN3koM/JIoOMkd+e1eY3+meVbSzzS7BPehLMxZPlMOW8w/wB1scA9Ogr8kPGX/BeL/gmv4Kv57jRPFN5rJu/mdLW2lZEHeNBLsAJ/vZr5g8Vf8HRn7HXhOS90b4bfDbW7uymQBXllt48zJ0fDeYccc81+f4HwSzSr8NF/M+gxHGeFp7yP6TruTQtC8PW3jCwkg0qzv2Fs0JXLfaVJBDqf4WPIP0rz34n/AA10m8+AfjzT7rw/qEGpavpc0rBEdo7lVVghDg7cLk4B9a/kn8Z/8HTHjK6+1S+B/hzYK18u2cX8vmqSAQrKqqoUjrxXyb4r/wCDmn9vPxD4cv8AwraWWh2drextDlbd2kRGUqdrs57dsV+k8IeCGaUK8as4WSaZ8nnvGWGnTcYSvc/nn8XW66d4o1OykUrJDdTIR6bXIwfcdK50XLbcGtTWtTuNc1e61u/bM95K88pAwN8jFmx+JrFZCWODX9mqHKuV7o/Ep66l+OcDrVkXODWP5g/z/wDqp4ckZFBBoy3jBcj/AD+tVllaUAD1yex/OolcAEMetAcAfL19RT07B1uj2L4e/Ff4o/Dm/i1f4f8AiW90ieJgyG3uJYjkdPukDj3r9UPhf/wXj/4KYfCGyt9KtvHs+qW9pgxfa1WZkwMAeYRuPHqa/GjS7nTIyftcbOfrxVW+uLVpma1Qqrds8V5WNyHB4lWxFJP5HoYbH4inrCR/Un4V/wCDqD9p+3mtD428G6PqCREGfYZB52BjcUYlA3fgV6bqf/B1F4w1i4M178PrNIzEIjCpXY65yQ4CgH8q/kTeaNOCKryhWG4da+ZqeGuSyd3QR6MOKMbH7Z/YBq//AAdp/GJbO4s/C3w10eDzYliVpCRhVGMfKBxjtmvi74x/8HLX7ePxNurebwuNO8MLbAqn2RGfjGMHeT7dq/nNjVueKsICBzxWlLw6yWDuqCFU4nxk1ZzZ98/FP/gpr+3F8ZFmj8X/ABB1MW8xLNb28pgjy33sKmMZ9q+JtW8Ra/4huJL/AF68mvJHYkyTyNIxP1Ymudb71N6/Lmvq8Jl9DDq1GCXyPPq4+rU+KbJGBAw3HpUeO9Ewc4U1EdwXrXX5nFK3Qk9qUjHWq+T1qVWz1oIHUAZ46UUfSgD9OP8Agkp48Hgv9sPR7UsFGrwyWhLcYJ+YDnjnFf1xXVteaprk0fnFo3/eQ+Ru8xQT82RjHA5JzgCv4UP2d/GLeAfjh4a8Wwu0YtL6JmKnBxuwcHntX9kOlftC+F7XVob22mWWG5hQLKWIeJ8ZI28buPwoA+nrG5u9SvY7jTLZZGleX7VNIFCFEQgSKoOSTnj5e9S6Fc287XdvDKsBXEdqu0hwoU/P8xwADggcAkmvGdC/aO8A6rpmteJbuIG4kjW0iEP/ACzIP39pwPm6H+VP8P8Axet4Egm8SXtvDeMoWKK3wS8bYwv3RlsdTxjp70AfQFt4b1q4lF14QursTW2Y55IB5h+Z9xjlUAYBAO7Prk1vaBpVnYWB1O4tbhmuYneMYUeRPG3yEZb+L07j2r+gv/gmT/wzj4h+D/2PwZ9jl1+5PmatBIQ0wkHH3CSQBnjFfamv/sifAPxFB5F94ct41DlwY/lwxOSRj/JoKUrH8m+saPc3OqQXVxl9w3MbYJIklw67iHQHjBxz2NfcX7JH7BXxV+ObweIfihHJpGhQOSJ5QVmuVbGUA4yAB1OOv0z+7nhv9jf9nnwzqw12w8OQS3CsHUyjcAw6EL0/nX01DZWsVuLOKFUiUDaoAUDHQAAYAoE3c88+Gfw58G/C7w5B4U8C2MdjZQKowigFiAOpxk565Jr0yM5PHenxKqHGAOOgqcxj+HigRTIDfL1Bqh9igB80gLJn73t6VubF/wA//rrG1u9g0rTbjUJvuW8bSN9FGaAPyq/4KD/HOPRLGL4VaFJtdk869dRhwueFyB0x1Hp1r8cb7xVHqU/9oaNEMxHaYxgLuXnGcjG4denFfUH7S7Dxp4tvfFepsxTU5nhjZeWRMgsT7cDB78ivjazZ0vZrKU4jtSyrtA+dd3B45JxjOaAOvl8Sy3k41O2YmcnBRf8AV7k4HHAAIHJ+nqa/Rj9lHx7b6xpk/hu6bL6hEY3hJyNpJX88EYPtX5qrBGZxDEq2gfJmQn5XwOCh65PQjAr1X9nbxC2m/EZLmSV4p45FUhOoQHrtyKAP2A/Zrik0jxLd6YmY0VGUhupAIUjPsea+3/CGkW3hvwrcXABjM0kkh29cE/L+Qr5S8LWq2XxiAtUzaagiyxN/DmRctg/WvsHxC8UGiLp7htu0g7aAPnnxt8TP7KuRZSSYkum2xRLwD/tMTyP84r8/fjf498Waf51r4WeWWe83Qi/m3FQSOVRe3pk4r9D7/wCF9r4t1CPVIYSozlnJ5OO2D+tPvfgLpV4Nt0qKMkIm3j3I/wAaAP5z4vht4+1bxRYeFbGM3pExnup5TuTe/UfRQeD1zX6R/G2R/gF+x9afDrSY9moeIrgRSKmBJJFGC8jAr2OAPTnFfox4B+Avg/wjK8EFupSVtzuw3NkkkjOK+Mf+ClfgrUVsPC+u6XmK0tRLaSOBkJvwwGe2cc0Afzr/ABCtdP0ywU2yfa5Lof62QZitg3Vceueua/PTxfptzNqxkmLzM5K+YGOc4Izx0Sv1D+Iuj2FlNcXcU8VtpbnLxjdmR8gbl4PrXyL4w8M2MUMt35btFGpxIDhdvP3uhHWgD4J8Rxanp2n3WmOU2OP3u4AfKMHKHqc4xX4YftbeJ5PEfj640neHjt49pK9CxJP6Aiv2c/aF8daf4O8J3F5M+8WykiQMBkAcD35r+c/W/EcniPWbrVJtwaZ3fDHJ5JNAHCeHYjbXbQvwc8VoXiM8zKeueKxLe4MOrH61q6m7JOHHQ0ALbMRIAzYA612liNm1wc151HK3nAjp3ruLS4GxTmgD2Dw3eM13FH075r9A/D14ZvAGi6olz+4tLtraZEyGJkIZef0r81vDuo/Z79ZHOVHWvv74WeI4o/h1fP5LzGK8gljiiGXJw3zUAeUftQaNqOj+OLXWNQt/sz3UW0IWDEBemee4r50c5BccgGvqb9q7VbnXodBvL2Uz3bKTKT1yx4U/TvXyiwk3bE4HcDuaAJ8mTa0h2pUZ5VTnDAY/AdPxp5yIgCMbetIOO2aAG4ZuGB3fXtSKGI3Dnt+FL82MmplGBigCLaBlD1Xp+NI8fPFPUq3yE8d/WmsSzbV6igCrsyCjVKg6J3FTFQBlutNGAwagAJycUYOM0BS3FKCAu2gBtV7v/j3f6VYqvd/8ez/Q1nW+BiXxI/sV/wCCMv8AyavYn/rr/wChGvpP4LnH/BVbwYp6/ZJv/Rb182/8EZP+TVbL6y/+hV9JfBzj/gqz4NP/AE6Tf+i2r/KHjx/8LeI/7eP9Acn1yj/txH75+P3/AOKM8RAf8+V3/wCi2r+bWVv+MYvg1nqfF11/6MFf0f8Aj0k+DfEIz/y5Xf8A6A1fzbXe9P2Yvg2Cc48W3J/8iCvyXJnzS17/AOZ9Bl0LRbXl+R/SBJNHHBpe84wgz+Yr581ORW1K4YHgyv8A+hGvbbyX9xpg/wCmYP8AKvC75Cb2Y+rt/Ov6j8DpfusRf+5+TPxbj/StBep//9L9zdOOZJz/ANMX/ka/FfxJ/wAmi/E3/saof5iv2n0/iacf9MZP5GvxV8SMf+GQvia3/U0w/wBK/wAVoP8A21+jP9Ncg/3dn6P+Kvl/YL1VfTwpIM/S3Ar8W/2FF3/A/Tfcy/8AoRr9ovFvP7BmrZ/6FST/ANECvxg/YQJHwN03/tr/AOhNXt8P/wC41P8Ar4vyZ6Nvel6H5Cf8FaWx8TNMYc4J/kBX5Thsuw9zX6p/8FZzn4lad/vEfoK/KiIksxPrX+m/gn/yI4/11Z/CHi4v+FaRPQOOaKK/Vz8oEHGfegnBApxIPakx3oAG+UZqEzAHGKlc5Wq+BQBJ5opvmn61WLDOMUoODmgCyJRjnigz44A6+9VsktuPNKAGOMYoAmM2OgpxmYKDVXaFyBUnUD0FAE/mj/J/+tTfNP1qsvI54pV5YUAXlORmlpFAC04EDqM0AKqqWw38Qx+fFf1yf8Gtuu+GdY+EPxI+Hvi9h9gtdQN0qliC77D8nUdQMjtX8jkcyxShiOf6V+y//BEf9vj4Gf8ABP3xt4+1L9pGG5m0bxDbqlklvCZ8SbzklcjBwcV8N4hZZPGZZUpQV2e5w5jVhq6mj+/G4tfCkV5c/aod6z2yJLBblXjt4gMLIAuSZB+Jqt5Xwus7jT5XtJNRTSlBjnWFmUCTgNOVXHynrnkelfzX+M/+DmL9hP4cWSaV8DPCuoXiwnerS2ixGRwc/MzSMevtXyX4o/4Oq/ElvBe2/wAMfh3DaQ6kxMwafy/mbhvur/EK/j2PghmdarKo6Vj9m/14oRha5/ZS9hoHh/QJbq+vEubGSRv7Q2RsVtQ4JSSD+7kjHHt6VS1vw9d3WhQaF4ejvNVtWHnQzF0UzKcEYbKnjNfwafEH/g5f/bI8S6cdF0G3tNHtVTYkZBl+TsNzdcD+dfGHij/guv8A8FBNbtls4/GQs7dBtRYo1UhfQEAnGPevqcB9H7GSam0kzzaniFQgtJNn+jTrPwYuvFfwt8W6Vq9+kKy6bcqI5XV5CzQuoRyDyATxzxX+U1q3hy58HeNvEXhG7GZNO1O4hJHThzXovjD/AIKVftc+LxMuqfETV1W5OZUhuZo0Y/RSB3r5Wf4t3E88t9eo01xO5eSRySzserMTySfWv6I8PeB8Rk9F06jTufnPEmdwxlVTiexgFTuPGKlGD8wIrwi6+K+qyE/ZIkX3rDl+IHieZ93nrGD/AHa/Sj5U+lArE4waeYZgM7CfpXz5pnjB2yb++bPsMVpSeMoFG2LUHAFAHuCRyOcBea5nXvh34t+JN5p/hHwVp02qa3eSbLWzt0Mk8xHOI0XJJx2FeUjxeeovmr9Hv+CPfjHxRZf8FNvhPrXg63Gr6rDq0S29vKflk3nawOeBkE0AflTr+g6z4U1W58P+JLSWw1C0kMU9tcKY5Y3U4KujfMpB7EVhmQ9q/um/4Ovv+CTdh4OFn/wUP+Deli0ttRMdt4otbdAqJcMP3dzhcA787T7iv4WGBB5GP/rcUeQ0yeK4ng+aF2QdMAkfypJNTupBtZ2I92NQ/wAH41VoSW9ilUktEy61yz/e+tN85R909evSqlFPmB1JPRstmUHrz+NNZ1aq1FNTfclu+5MSOxpC+DioqKOZ2sIKcGwMU2ipAKcrY4ptFAE4cEDNOZ1aq1FDdxco93304Se1RUUDJfMB7frTlmCjAH61BRQBKZcnOKTzP8/5FR0UBYmMpPWmM2RimUUAFSKgKls4qOtCwhe5uIraIbmkYKB65IFAEIRtu7Bx6008DNf20f8ABQL/AIIR+Gn/AOCPXwt/at/Z+0FY/GOg6HBqPiNYBh7u3nj3O+B1aPr9K/ideIoWikBVlODngjHUY+tBclY2/CZjXxHYSSttXz48nOMfMO9funY+JtWuZYrFiZWRFMMobCthRnDdsLX4KQyeUweLtzX78fDuxtNQ+FnhnWb4CRLi2V2KnmRiqqFP40EHUaFrN1FN9jtZWkUk42SYMjj69cGui0HxlrUtutvqDSvPbScMT/qD/LnrXIeFJLW3tW1K7jDG2mEfYbJSeSPUHpXocctu813dAgSXB+dePm47AUAe7fBb9o74tfCnXZ9Y8E65cWc0fE00UrIWXIJXK4zX7VfCn/gun+094QisodXaDVNNs5EikWWMb5FxlyXPoO9fzy2+lPBqMdvb/wCqvI8kqOFYjkEdjXayQyrFHJbyST/YV2XCAEhvO6EDvjFAH9l3w1/4L/fCbXbgH4g+GptFgdSyOsoctg4+UEDg8kc1+hHwp/4Klfsf/FO7t9Ps/EaabPcqGUXw8lcH/bJ28/Wv8/f+1blX8yX/AE94AkccZ/1Zjx02nuOldlp9j5eqwyWQkfKtIWQlfLbGdpAB6euRg/WgD/S88N+PvBvi+3jvvC+p2uoxS/da2lWUf+Ok12Zm+UlBnH61/np/Cf4+fHPwXYSjwl4guZEs3TbiTaQGzwuZOWGMHtX6G/Bv/gsV+0d8LL/7P49c6xpsQyfN+YljgAFhyPTAJ5oA/sc88kfdr5K/a01rXbHwR9i0CdoJ7jeGA4DrtO5C3QcZ479K+L/g3/wWR/Z78fafHF4vSTSL+ONXuEYgoA3dCcE+4pP2u/27/gDqGiaV4Z8NatbakNTO8zQyBhGAMjIHIY9OaAPmX4galeXuqKupW0NtdPCqQ8L5flqp3b16ZI6Gvj3xVoPlsJ13yCQt5BIAQDjCjGMjqATX0JYftIfDjWvNublIHhu18qeVjuKNGo+VcA/eqPVvGXgvxKba6SKGLTpgqIiJyCASGAwMOD6kKM5NAHyvY3U0qGfUojeSQNsEi9I5c4VuOCMds113hizuLLxcl7ZYFwjeZNKpGXBP3QR7V2s1lougWnlzXETuzY3Enc0ZPzHb3A3AADrjrXNKmm6Xrsi6bueGDdsw2Gy3DNsAyAvYHmgD95fhbrmk63r3gcRENJNpksjDqN0ZUdP7w5wa+3Lu0t7lAHQHHrX8837LX7Q1j/w2ToHgCecvY2enmGPByPNulaTn/gRAFf0ScbQDQBRtLC3gXYg4qw1nE7B8ZK9O9TIh5xVhAQOaAKK20SPux+FfK/7Z3hVvFH7P+tR2yB5rLbdKCM8xnn9DzX1uVB5rz34leGj4r8B6z4aDFTfWk0QI65ZcCgD+TfWdBbXIw0zwIIT5aRIoIRuu49a+MvipqVnY350/7al3Mi7rudwAFXnKqg446/hX2V4k8MXmharqWh3Z+y28U0izsSQ5eMkDA96+Afjkn9jaZciPy4IJIzl+ryLnAGffNAH85H/BRD4lw/ab3SNNIR7iQxgqch1ABJwOB1GK/Huwv5NoaVtxxivqb9sXxLf6v8T5oLtstFNIEPYIDwDXyQuxV3rwDQA9ZgdV+prsdUt3e3SQfX8q87Enl3gkevVbnBshu6AUAcdGPn57V0tlIMj0Fc08gRcjua0rSfaRk0Aei6E+b3zVIBTkZ6flX3V8D/EU8nh7XdHtjtuPs8c0bpwysrHkHnGM1+f+kTot0pIzkGvtP9mm7hl8VXGkSnBvbKVOnUkZFAF79oC2u7zQtF1jqclWcDgsDyfxNfNQy8hOfyr6Y+JF0L74Vpp8DmT7DcNn1A618yxsmxQG5cfrQA7YApbJzjnNOZA/TBIFIwLHrkHg5pVOWGOO3FADVKr8ydDTg+BikZSxO31pDgH26fjQA4BR82DRgKxcGm7mC4NKByM87v0oAVmyMUirup7JxxTQHHSgBG4+X0pDyc0rK3B9aQjBxQAlV7v/AI9n+hqxVe7/AOPZ/oazrfAxL4kf2Lf8EZP+TVbL6y/+hV9K/B3A/wCCqfg9j2tJv/RbV81f8EZP+TVbL6y/+hV9J/B/aP8Agqj4RJ/59JR/5Dev8n+Pf+R1iP8At79T/QHJf+RT/wBuI/d/x25bwh4hx3s7v/0W1fzfX3P7L/wcb/qbLr/0YK/o58bSD/hD/EH/AF5XZ/ONq/nHvyo/Zb+Djf8AU2XJ/wDIgr8jyTf5/wCZ9Zl1NWa9PyP6H75ysWm+0Q/TFeL3TbrmRvVif1r2LUnHkabjvAD/ACrxuf8A17/7x/nX9ReCH8LEf9ufkz8N8Q1bERt5n//T/cjTiTLdk9RC36g1+LfiMD/hkP4mD/qaIa/abTyPtF5/1yb+tfi54kI/4ZC+Jp/6miL+lf4owf8AtvyZ/pzlKtRZ+i/is5/YO1QHv4Vk/wDRAr8Yf2EePglpY7F5P/QzX7O+KX3fsJ6mD/0K0n/okV+Mf7BwI+C+mE/3pP0dq97Iv9wq/wCOP5M66rsn6H4//wDBWb/kpunD/br8rY1HzV+qP/BWIEfFLT/9+vyyCAuSfWv9NPBl/wDCLC39an8K+LX/ACNZEY6ClqyVIOKTBHWv1w/JStgUtSFct7UjJjpQBCwJ6UmGHGAasKmRk0u0ehP+frQBDgY5FNaJXG0AVbUFuFGfal6deKAKH2VsYoFqw6VswrGlu97dOqwxgkknHArxrV/ieglZNJh3FSV3E4yOx96APTTattyGAqPZDGPncZ7jNfPt5478Tzqyrc+Uo4woA/lXH3F3fXEvmXLyOW5OTzQB9Sz6jpdvGXupQCOfyrD/AOEz8Oox23AJH1/wr5sLAf3vxNNMuBng0AfQlz8RdDhPyBnP+zWLJ8UIOTDasw/2jivEjMx9qb5h70AexSfFKUfdgAA455rLvfiTqF8MPDFIAcgMM4rzMTEDGKaspViw70NdBp2OkvvEeo3nDxxxf7qAdaxDdXHXzSPYGqruznLUymm1ogcmTtO55LFu3NJ5zYxjiogSOlLvai7LjOysh7H5cipAcVDvaguTx/n+VIzYrPngVHRRQAuT0oyaSigAr9gf+CDySXP/AAVn+CccLFc6/GePZTmvx+r9c/8AghZPJa/8FXfgpPEeR4hgz75BzQB/po/8HBK2b/8ABKD4oJd2aXafY0AD4+UiRcN/wHrX+OXc/wCuYDGM9Rzn3r/YY/4OK777N/wSV+JMvmeVvggUn2Mq8fjX+PAxJY59eBQAlQt96pqhf71ADaKKKACiiigAooooAKKKKACiiigAooooAKKKKACiiigAooooAKKKKACvQfhZpUmu/EXQdGhXc91qFvCo/wBp5AoH5mvPq+nf2MNAufFP7Vvw60G1G57jxHpq49vtCE/yoA/2jv2bfhdYR/sYeEvhX4ut1uLb/hHYLK6gcAh0MCqynPqOK/xof2/fhXpPwT/bL+I/w38PRmCw0vXr6G3iYcpEs7BVwewAxiv9vzwrYLpvg6x09BtEdsi49MIBX+Nz/wAF3NCPh/8A4KnfFnT5cKTqzylQOgfDfrQB+YN94csJPC6eIfD8jyLH8t5GwGYn/hIx1Rh39a/Zr9nfX5r/AOB/hqIjzBBAqIrDgSFipbPYL1r8OI7u6gt5YImKpMAHA6NjpX7Qfs13KP8ABbw7c2iGSSBQAoIwCZCMkHjA96APoqXTo7B7nSYJFuIbZwpkAATOc78nqeCK6Gzv9Od5bi2iIa1UIHOMPgDP456Vg6kWHiCezt2GyZOHAPluy5JO31BOBkda2/DFjbSldNt0mmlgUkxlQdzDg7hjkhs9qAOj06Z9UsUa12QJIwO1zySvGc+tdpbXGuCW1vIVjaaQsssecbkjPylSvUisTTtNFnp00dzFMLnzPOkl2nYAf4VXHGe9ep6VpmjFY44oWKWoy4XcSPO6Fc84FAGJFogls4f7LnF7J5jltpKmA5+bIP3jmvVvCmjTXLQx6D5jlnkE13Ip2yk7QUOeBxxketJb+E2k1C9huAPs8KxgAfIct0LEcMRnJHWvo6z8JWMHg6ytJZDcyIgJSMbXBOOQQQ2PlyetAHrHwk8G6bJfmdraNmgRknQPwEkBXn/d67u2RXF/FS18GeEb9tJtzFJbWJ8mKZfndpi22QsueRjJU9gua4Z/HkuiX8miaNbNcXiRDc6cSRxmMZOMAsVHzZyD6V5nruoz+KNWtbTUoltRPHI8KIAyshII8zqMn+83O0YoA53xb4/0bTr5bLT4PPdBk3Q+RWYDGRj7w4xx169q+dNc+MmoS38NzZzvaQKyIRliynoSpOcZr1qH4eO2niPWTJCsrlYVDAqfdewBzwMHnuK5lfgpLMs9wj7SxRismRJLnnjHYYoAg8PfHrxboM5gsL9hDF+8ENwflLn7zZI64HSvePBX7VfjfT9Qaz1M/a2ugs05jf5UUcqEHYgda8Gm+C2tT7oiHWOd1kiJH7rP8SFvUgYxWvpnwR8S3MiySYjnuJT5kjExCB1/5Znoent6UAfoB4U/ad17Vg+n6kgllkGIm34McKNuwQecjsa+i9J+KGpeKIbYQXRgdSscMgX5ZApwxJHXJ4r8+fDfww8RaNbXelateLG8SgEknEmCpDKcZYnPtX0lY6lD4K8G3s6yNFb28LkQsmUXaN4CE5KjuCOc0AerfsffFhfEP7dWo+IQCkujyorQDrIYSAxX5RxgV/b9o2pxatplvqUf3biJHUHrhgDyK/zef2CPFus2P7S17cQSvIbx2dJmO8oA24oxPT3r/Qo/Z28Wjxz8HtG8QM6ySeQIXZectF8pNAHvEDBlqeoofuVLQAVGzLyCKkpjIOSOtAH8/wB/wUV+C958O/HbfEXSLcSaTrPzSKEOxJD1U9snrX4F/tI+FfsXhie/Km6upEPksgJSPJ6EDpgGv7mfjN8LdA+MXgC/8C+IF3R3UTBJD96N8cMpHcGv42P2mvhd4n+FnjTWfgz42jMUtmSbd87RNEfukEcHIOfzoA/gy/azivbb4v6jb3jAsHZiBnhicHr9K+aQflAr9EP+CiXw6l8K/FEaowIS5d0y33jtPQnvjt+Nfne7EAA9aAGSoSwNeppKl5p/7rnivLC5ySK7nw5KFt2XsKAM+ZMMVZfu0xCyMBmtS/UlN59axnAOOelAHZaNcqtypJ5PAr7A/ZqnD/FbSZ2mEUJcwyHuAQR/M18MWlyYZlzwM96+kvhLriad4psL55FVIp0chhw2GUgH16cUAfVfizT10bUfFXhqQBo7Z5JEGOD8x7V8bxX37tFkHIzX3Z8V0WD4o6jDcx/Z49Ts5JVUdG+XK/nivhF7ZxOEljwRlQB35oAvR3UQOxjkEVOHXaCv59hWfsXbtUgIOqP2P+zUiNNtBkJY+5+XH9MUAXQWX1we9J8nQknPQ+n1qJZom4Gc/wCeBVhfLcZXj2oAkAGPWkwq5bFNIwMrzmmbT3oAez5HFMy1KhGdx47VLuU96AIdzetJTn+9TaACq12cWzn2qzVe6INu4HpWGJ/hy9GXSX7yPqf2L/8ABGcY/ZXssesv/oVfRfwhfH/BUnwke/2OT/0VJXzp/wAEaFJ/ZXsv96T/ANCr6F+ETZ/4KkeE8/8APlL/AOi2r/KLxI/5HGKt/eP9BMg/5Fcf8KP3R8dzMvgrXCD1sLrP/fDV/OzfgH9lf4Pn08V3OP8Av4K/oh8ekf8ACHa8P+nG7/8AQXr+eLU12fsp/CA/9TVcn/yJX45kT0Xr/mfV0FZadj+gC8kc6dYuSciAYP8AwEV53JHG0jMQMkn/AD0ru7mTOmWQ/wCmA/8AQRXDv98/Wv6r8EP4Nf8A7c/Jn4L4lv8Ae03/AIv0P//U/cbTiPOvT/0yb+tfi34kYf8ADH/xN9vFMX9K/ZzTWDyXhB6wsf0NfjB4k/5M9+J7f9TTF+mK/wAUoL/bvkf6cZU17Fo/RLxOzH9hTU8f9CtJ/wCiRX48fsKAr8GdKHqZv/QjX7D+Jxt/YU1M+nhaT/0QDX48/sLnHwa0r2aT9WNe7w/pgqj/AL6/JnZVVvuPx5/4Kyc/FTT/AHevy1jUFzn1r9Sv+CsY/wCLoaa3+1n8q/LWJsuT6V/pr4MRbyWD/rc/hTxaf/CrImMYHU89qdJFnkVMhWQjeOlQM5RMj7pr9bPyZMEt8/N2pI4SzEYrOute0y24uJdu3qMZqKHxPY3w8qzidwejcgUAa0ieWMGo0O1OaRIy6/OyxqBklmwP1rjdW8b6DoTNG84mf0T5h+lAHXyOI13dSfwqGbWJbVfs8Xkb2G7D9cDvivDdY+KupSv5emIsUeMfMNx/XpXmc+p3t1ObmSZzIwIJz69vpQB7N481C1u7WOX7V50m7lQflA57CvGbu5M7eYnynpxVJ3bZtycVGHxxQBveHNDvvEms2mh6eN9xeTJDGMZ+ZyAOnJ5NfU37XP7E/wAfv2KvGWl+D/jzpT2FxrVjHqNlMRlJreX7pU5xn1HUV83eAPElx4S8ZaV4otMCXT7uG4UkZGY3VhkHjqBX+n5/wUs/Yp8D/wDBVf8A4IweGPjlpFhG/jfw74ch1nSrq3QbyVgU3EB9UYKxx2IoA/y1ZY2TvVatO7tJ7S9lsLoFZInZGBHdSQf5VRkAU7aAIqKKKACiiigAooooAKKKKACiiigAooooAKKKKACv2D/4IMaY+of8FZPgvEASE12N+P8AZVia/Hyv6Df+DZvwPD4t/wCCq/gHUZgW/syaS4A7ArGwz+ZoA/v3/wCDlDP/AA6P+I0adltR/wCR1r/IGXClt1f6+H/Bypc+R/wSP+Iztx8toPzmWv8AIQVg2S1AEeQeVqF/vU7eAeKYTk5oASiiigAooooAKKKKACiiigAooooAKKKKACiiigAooooAKKKKACiiigAr9Rf+CM/hKbxp/wAFI/hVokCCRm1qGQKRu/1R3E49q/Lqv3y/4NovCUfiv/grx8No5gWS1+2znA/5527kfrigD/XttmUWESg5xEv48V/j1/8ABxhZy2v/AAV2+KULgDfPbPxx96FDX+wesXkxCIcbVA/IV/kAf8HHty13/wAFfPig7jG2S1Xj1ECUAfhrtKrtB4Nfuh+xzpkP/ClNJ1K6gxbhMSbdwZl3kjBHTJxX4YkhTtboK/og/Zc0uKL4KeFomJjj8oNJGx2ltnzjH44oA9Dh8OrOmn3d6gMoLbEAB3HKkYPBztPcDkV7R4W8BQWt21xe3DLgrLJOD8wc9EOec9qqrZWd1pdh4hBI2bxDD0Zvm3EyL/HtHTI4r2DwYujebNLKxljuE37AgYb+cEkDIx7igDmfCvhptXtZ79s7ricrFuJKlc/xA9DXoen+FrW33LHLmNcgyjjdIvOP+AmptM1UaPZxa1Ii3hJ8swREc9twHHI796dqDWk2ji0gm2Qq7XEwUbmgkH8MnpuoA6zQ9YtxffatejV2jG+5ZVBLkArGVB4OMiuj1S613U7tbLXbyOM3TK0MUfDMoIH8PJ4Hb15rxe3XVNYMGqWO1ZXdY/LaTZsJ+ViR2wPun1r3+48I3uqaxHF5IEunIGQlMBWOSGDg9OOADg80AVLv4bw32uRfaJnNiYDtVGCSpJtKoMkZI3DBJPT6VWtPC7apeW2l2sfm38GwzAKAv7sERxlvRup55r0TQtd0y71mOfVXm86WIwSsynYrsvDlegAPPHHfvXRX6wWVpceHtPCRpcBdt5vwJJEG4qccHPUHtigDi5/A+lTJNbnC3N9gSptysP8AukcqTnAPtWtaeCbjRnVxDHJb2SKy3MmWZnyOF/3jwK6UQ3LXgNkqvA9vH9ryf3jnnG31/Cuyk02AwxWMQaeaTYFifPlwjcGGT6jHFAHBw6FoF1bx3l4TBg/6VAo5SfPyMenHOeK7O10fwbFdQX15G08tkSszr/qmbHyu3XJOelOt7KTTdet9VuYY7+GSRkKjrNjhQ3P8J/St++srS1luId6WtuAVaJF3lLhiBgnpt56k0AZE1tYiOPUZ4lh1T5la3KZXyyfmfcemOK+Uf2lvG8mm+ALhNNz5CkRRqSF3yncSpwOADzxzmvpPxB/bFvI9pII0vL1SjyHDfLyRs54U7MZ9cV+bX7Z/ioxWlppk7mG3iVvLTGCMc5Knp0OD689aANr/AIJz6xLd/Eq5kuyy+ZOzPMMD7vOFPbFf3j/8E7/Ei6p8HZ9DHBsLjdzycTKH5P1J7V/Ax/wTsWHSvFEV+2JYbiQkRA5O0ZPQ4PfAHXjnFf3L/wDBLRnk+H2vSS5LGaA5PXBiGMjsaAP1Vt+VJqeq9t/q/wAakeQJ1oAkquZTuwMmk80ycqOP618m/Hz9rv4W/ANktfE1ws90fvQxkF0z03AdKAPq6RS3AOCeB9a/Cn/gt78B0174JxfHbQNlrqXhqTdcTAYd4G+XbnuAT0PrX6O/CP8AbP8AhB8V9WXQNMulivXAZYiRnHXkHBrg/wDgpd4aTxl+xR420/AYi08xc/7LAg0Af5Wn/BU6Dz9K0LWFALXMrOWHH3kBPH1Nfi633jX6/wD/AAUh8T2uraXoGkwIFWJJ12g/xJJgmvyAPoPQfyoATvjt3rtNCZRE6j+KuLrpdEk/dkA4zQB0V0u5CG6CuemGxQW61uyS5TFYzrvTDdqAMtpSzgg8ivR/Amql9URJG2lXUge4xivN3i6sOtWtJuhZatHdO23Hf3FAH64fF26kuLbwp41ddwuLVYZPc4x/Ovi7UIcandBh8plbZn88CvsjVNniL9mXSteYsbvTZQGX0Ugba+UfFqJFrRKjhlVxjkDeOaAOVaIOAMAE/wAQ7UkqncGKqVPBz7dxVsLuB44PT2qNTtb7uR05/nQBSRJRIVYjaOgqdZFVjlffrUksCdcYYd/WqLxPuMg7nbigDQWXeQF6EZpwkJO01XijC7c/w1OHXdnFADHkUjHvTQVBG4ZqTarAgVEsZY5z0oAn3r24o3rTfL/z/k0eXyBmgCQEZ4qCcKbaQ9wKcGywJptzxbvj0rKv8D9CqX8SJ/Y5/wAEZRn9ley/3n/9Cr3z4QlT/wAFSPCp7/Ypv/RbV4H/AMEYyD+yvZ/V/wD0Kve/hAAP+Conhb2s5/8A0W1f5Q+Irtm2IT/vfqf6D8Or/hKh6I/cjx0+7wdrp/6crv8A9Bev55NWcj9lX4Pg/wDQ1XP6PX9CvjRg3grXjn/lyux/441fzzasc/sq/B//ALGm7/8AQxX4xw4vdXr/AJn1lL4fkfv3OCdPsv8Ar3B/8dFca/3z9a62Ztmn2Z64t1/VRXMeVu+bPXmv6u8EH+5r/wDbn5M/AvEz+JT/AO3v0P/V/a/R5GLXRP8Azwf9Aa/HDxDh/wBjj4nOf+hpj/mtfsXpPEl0B/zwf+Rr8b9fk/4w4+Jy/wDU0x/zFf4qQf8At33n+mmU/wAI/RXxS4P7C+qJ6+GHH5wCvx0/YXkP/CmNLPu//oRr9gPFbeX+wrqcnf8A4Rhv/ScV+PX7Crg/BXSW/vb/AOde3kX+4Vf8cfyZ6lfVteR+Qv8AwVeJf4n6aD2P86/LSFRk+9fqH/wVwuYtO+KenF+F8zH4V+W8d1DKhkt/bFf6e+C8LZFCT/rVn8F+Lbvm84+RZkmNqjNtLkDK47nsK4lPFuvEbn0tYW6MJJMk+mAAK7FiSxJ9f5VUknjU5mRWIAGTyePev1M/KY7HEt4i8WX0pSz0NWI7t/OrEmjePL2EXOp3ltYRH+Ffvj6Ada7JL+7jQiHAHuap3WpWtrbPc3u1ePvH9Tmgo8f1bRniV7jVdTeW2j6qco7+yr/WvMr5LIymSyJWM9A/3sV6jrfijTUQyae0V1uO0Syrlk9wDx+lec38cO0XTTLIz8naAB+HpQBjbXUfOeKicjaeKczqzYUUx/u0AQ0UUUAWYZTGuV65z+XP9K/1s/8Ag27+JEP7QH/BInw14U1eQXLaXFeaNPu5wrkhVP8AwFq/ySE6V/o+f8GYvxbfWP2cPiH8J7mUFtL1SG8ijJ52SJsOB6ZFAH8MP/BRn4Ay/suftwfEv4GSdNC126ijx0MbuXQj6qRXxDL97Nf0q/8AB1Z8KIPhr/wVU8Qa3bxiNfE9haamDjG4vGEJ9M5Wv5pixbrQAlFFFABRRRQAUUUUAFFFFABRRRQAUUUUAFFFFABX9Sn/AAaY6eL3/gpbBMIi/wBl0u4lJH8PG0H9a/lrr+xP/gzS8OQap+3r4w1a5TIsfDUhU+jGaMD9DQB/XN/wcrxxSf8ABI34iCbgEWn6Triv8gpgSTtr/XW/4ObZHT/gkV8QwpwDLaKfp561/kWJIEUqaAIKKU8nNJQAUUUUAFFFFABRRRQAUUUUAFFFFABRRRQAUUUUAFFFFABRRRQAUUUUAFf1M/8ABpF4QXW/+CnNv4jdMrpOkXj7v7rOmwfnmv5Zq/sc/wCDNzR5L79svxtqoQFLLRo8n0LygCgD/S9uGO+U9gM/piv8a/8A4LweKf8AhLf+CqPxY1U9tT8nn1iVV/pX+yXqLi1srm59EJ545Ff4kf8AwU68Xy+OP2+viv4gkZWaXxJqAypyMLOyj9OKAPhgMpcbuRkZr+jr4Q6hKngDw7YKsayLAGhLnb8hjXt6V/OJaKXuo0H8TAfrX9FfwzSX/hD9K0iNY/tMVugDzYOIjGpYAnnJ7UAfSFlrFjbXNxNcKZZ4ZNkXltiNicZA69PpXQ6DqkFvqC2tvM5jO8l8bGjZhkhv74HavlyfUZbgS6dZq7WguPlyQrpnqT269K9O8J62rWBW8czSZ8p3dv8AVAcB89xjFAHt2geI4ra/tS15akb3kdnGGkUcAc/dY9j1B4ruNWl8rS/tGi3a2F1qCzNcQyKGSTaP3IL5Gc1832fiiPSNVj0VoLe9sJJSst7gkn/ZTtjPp9a7TWvEB1IW1ve2MfkQl2JBO+ZcjYM5/h7YxQB798NY47vTbia8Kym0iQRt/G9zwWDoRkqDnpXsdjHBphgsfE0klnHch5JG3E+dhvlRR/D1/CvkLw58SNYsVtrjX1L2kjbIbdAqXAB7l/vE++a9K8M+NLy7llstSja8tC7i2aXO6Bm7O3fJPc9qAPqSBLhdRtEu7hbexmj3rEy+Y5aP5VR3HABNLBPa6f8AarfWpPsSH91HaFdwLyHBkGcDGOgzXk2iXUccE628xu5JFkEzZDCDIBxjPTGOe1dPoXiQ2dhdx/Zre6S7jSDzJczm3kH3SCT1b9KAPUbDQLTdGWt7y1nMcaWkq7nUrnligPTPvXogtNAiE1rqdxc30TL8ksCEP5oIILDPbv7V41bXPipIbe+sLiS2urf5LmIOWAiXkkZbCgj0xVnS/FJ8TatPcQxvHbKpjWRH2GIsCodlB+fGfegD6SN9JY6nFcRvCklvYGJ2CA5hJxvKclXPr9K84l1XRbSFp7OA7M75PO+RZYwCd7MeCV9MZNeeJPpfhTUru1tr6QzRlXuJpMsJoVA2gEk4JwBjv9a6Dz/tUMllcLloB9snEpB2qeQqD0CnoOvegDjje6VqN01zdalOYFl35a334CgYTcG+6SwxjPSvyW/az1hdd8YXkcc32mNZVjjkbOXRcKAY25Axn0r9W9L12O+0TU5NQmuUgJYRIyDhiuBjIyOOh7fWvx4+NULTeNbmzu4WhnaR5DMQcSKpB4HTB5A4oA+xf2AdKNz46MUkQSDCySNIOCiKchT2IzuA9q/uE/4JZ6Fcab8JtW1MrIILu5jERlyXIjjxyT17H26V/GV/wT/8PX97rE19IQVe2uJnDY2sgBU7B/eyRjvX9xP/AATq0nUNK/Zk0ua/lLmaWZlDAjYoIXbzz1BoA+7Y7hI1KE461lz6lCuN7jLdAapfb4p7preP+6xJHp2615Vca5K/imHQZGXaznymXBZsYJLemM0Adv8AEbUNW0fwDq2raC22+is5nhY8hXCkg4/Wv4gfjj8V9fuPilf3/jvVxfyJMbi+S4ziRlbciRrnk5PI9K/utv7ODUNMuNOuBuimR4m91ZSD/Sv4vf2u/AGiaB8aNb0qzsopjZXEywsIwzLLuwC+R0x3oAs/szahN4Y8UWvxZ0iWSC/nkV7tpWJjYHkLEg5QBeOvWv6OP2x/HNl4q/4J7+JvGFu5SO40nduPUcDOR2r+cz4M6haeFbB7YReexKvcTKxJjbriMdMZ9q/br4lappvxI/4Ji+NR4fnaVE0u45lB3jbGWO4fQcUAf5TP7XPi1vEGt6ZGh82KCK4COOnzTNx+FfCcgw5HWvZfF+pT3smLuQyLFPcID9ZDXkN0gWVvY0AVa1tMm2NsxWTVm3JW4THGaAOtyCmR1qKePBBXuKInTp61ZZNwJPrgUAYroM4NVJo0JX0U5NbMsO18tyMVlTxk4BoA/Uz9l/Uf+E/+CniXwpOPMWKISEE4YbVBBU9/oK+d/FsbjUrd5BgNbjn3Xius/YX8QpF4wvPDd/LsguLeVV44Lben4U/4t6SdC1G30w/6yJ3WT1GTkD8qAPLAwReTnPtR8p56H2pVbaeckGnhcMcj8ulADXCleCcdBVcITyelWXACgCglQNuOlAEagA4p7Iu2jK9h/n86QsTxQAwKB0pUQZx/n+dFOUgdaAEPBxSdsVIAGJNR0ABqC5wLZ8+lT1WvBmBqyr/A/Qql/Eif2Nf8EZHA/ZXs/wDef/0I19A/CNlH/BT7wu3cWc36xtXz9/wRjjQ/srWJI6tJ/wChGvePhF/yk68MN/05S/8AoDV/k94kO+b4j/t4/wBDuGI3yqHoj9ufGc//ABRXiD2tLv8A9Aav589XO39lP4PEf9DTdf8AoQr+gDxj/wAiT4h/687r/wBBav5/dUOf2UvhDnt4pusf99ivx3hraPqvyZ9ZFJI/fOdidPtD/wBME/8AQRWMn3B9K1b4mPTLQrx+4T/0EVhxu3lrz2Ff1V4H/wALEf8Abn5M/nzxO/i0/wDt79D/1v2f02XD3WTj9w/8jX46a2C37G/xOY/9DRD/AEr9c7C5WSS6JPHkP/I1+Rutyf8AGFfxOA7+JocfpX+K1OP+3/ef6a5Uv3R+hPizn9hLVQf+hYb/ANJxX49/sMEr8FdI/wCB/wAzX69+K5M/sI6v6f8ACMn/ANJxX5FfsLLu+Cmk/R/5mvdyCH+w1F3qR/KR6E53n8j8W/8AgshJv+JOnp6y/wCFflZo1wyQiInjiv1S/wCCx0X/ABczS/8AfH9K/J6GOVFXZ6V/p94Ou2QU1/W7P4M8V3/wtT9DvfMDjCfnURsBONyjI9KxbW6dISh61rpIXh2hsdq/Tj8sWx514v1NPDl/HFal7wsmSFJwp9/WvL72fxH4gn8pi7RHlVJwB+FfQz6XHb58pVy/J6ZNcNrPhbRUc3s+oNaTf3NwJ/IdKBnjkmmS28QF/LsKnAUdayJhbH7hrr9Rj8NQ5a2lkuJR1dulcbJ80jEL+XSgBn+7QeEIPNJ5fOcEU50O2gCvRRRQBKnSv7m/+DK241Fvjb8T7fJ+yf2VCSM8b/NGOPzr+GADPFf34/8ABlV4XmEvxW8X+X8u20tg2OOC7Yz60AfB3/B5XpJtP+ChHhG/X/lr4WiXj/ZmkH8uK/j+r+6b/g9K+Ed1B8X/AIcfGeNG8m4059OZu25JGfGcf7Rr+FsqRzQA2iiigAooooAKKKKACiiigApcE9BSV/Vt/wAEcf8Agi/8K/8Agpr/AME8Piv4vhle3+IuhXsa6HMrbUDCEuI5B3SQgg+9AH8pNFegfFH4b+K/hB4+1f4Z+OLR7LV9Eu5rO7hkBUrLC5RuDzg4yPavP6ACjHeivbf2fvgN8Sv2lvilpXwZ+EOntqniHWGdbS1U4MjIpYjPQfKD1oA8Sr+43/gyy8JXB/aC+JfjZ0/cpoyWufRnnRh/6DX8VfxI+HPjL4T+OdU+HPj6xl03WNHuXtbq2mBV45Izggg8/Q96/wBAL/gy38LMvwx+JvjVk+/e29tn2AL/AM6AP2G/4OiL8WX/AASJ8cHp51xZr/5HWv8AJBYFjx6D+Vf6w3/B1rcSWn/BJzxFCh/1uo2Cn6CUn+tf5PL9voP5UANII60lFFABRRRQAUUUUAFFFFABRRRQAUUUUAFFFFABRRRQAUUUUAFFFFABRRRQAV/a/wD8GXNukn7S/wAT5m6rpFoMf9t6/igr+17/AIMuZ/L/AGmPichHB0i0yf8AtvQB/oj/ABV1dPD/AMNte1yaTy0s7KaYt6bEZq/ww/2hNabxH8efGniBj5n23W7+fdn+/cOa/wBq3/gon47j+G37FHxO8XyHaLPw/fODnBz5D9PzFf4hniDUP7V16+1TOftM8kvP+2xNAFHTUeXUYIk6tIo/Miv37trmTTra3t7aIvPFZRoQP4V8tefavwg8Eadcat4w0zTbRd0s9zEijrklhgV/SPD4IuINSs49ViS1eG2VppgMb1CYABPDfMME/hQB5cLC51TUxJqA/cGHzJAufwz712fgm31abUE063Z7bzFIywwjR9fmz6frXZReE9QuhY3cEQikA2XQGT+6HIb35znOO1bg0DVJNRAhuFktrhj5EZBBZT9zLbhggc4FAHH2IvzDLZWuXW3uNyKMnYO5B9MVvSRyWtzHf2l15su4kGUYDx4G/wDFTUmoaRdOyzSXZt7eGQeYsQJO0D73DdumO9Zd9p0moXsbairR28imS2wGDbUYbpCPyOB170AbemvYaLKsrWzSTr8sDMfkfe33h9M16B4T1eXT5J4prjKqyyvGxzvcEgKp5zXDCwTVtBafUklDIqxQEKVWQE/e3fwk+nauz8O6IyRWlvHgaezceaMzCXGAdw6rnvQB6t4EvW1G8k1G1hMVzZyFmgc5WVGPKOfTpivTtN1GKTSr6301FgtLif8A0k4LLayg8bCOeRxkcV5BYaFJbeIb/SPEF35KNAHke3BZXKDIRSDwTwDzXoS7PsqXSE6Za3Fvn7Ix3CVycByccH2OaAOitvEOp6rHHo+iQyLBZsRcXZ6zoPm5757VWPiq0n1z+0NYs54IbbciqDhiPugsD/CM5rhLnW9QWxgt3vliiscqvkr8xI5y/t2rxrxJ4l1+FUttQvXnjllDSSxjdtizwhx6nFAH0CvjKaPVVtLc582djLI2NsoRQFTJ57/pXqmj+InbTYYdUb95AjPs5DLk4AY9wcV+dWp+IFs5rOKyu3mMjsY+32bac7jnhg1e5fDT4oSXkjQQxmS7fd593cnMZjBx8n+16DrQB92aPBq+qXd7FrlwgLW7Su4IK7cDavTGa/Kz4v2d1J43dtS3O5eQQBudoOQBn07gV+s3wu1TTNeki0hIleB494t15eeQHjc/8K+3evjr48eE7mx8ZTx6vbxx3F06SQoCpdGBbamBjC9qAPp7/gnToEY8Pal4hu7Mq+g2XltlcFZrl12j3AI6V/aT8EZ9S+H37NGiNcILjUWtXuIoAQpcuS4HJ9DzX8xn/BOzwjql14MvPD95axrdanfWsdzKRnLBDhCPcnGe1f0xfFvT7/wjbeHdS0qKa4ntLEWsdrCDje2BuOOOBQAvwM+InjH4m+ItX1vU1VdJ09MKqZUmdeSoB6j8cVyXws1ufxf8XdQ1WFGt4YZSfs8h+eNnGwr9DsJ/Gt5F8TeFPhufC2k2c8N1efvLi5gUg5c9AQOD657Vx/wVsvE+nfEGSXXYPJW5XftcgzIQcB2ZerSHJbP3e1AH3/AC6qyZAwMZ64xX8m//AAUqju9I/ax1fStL228d0UO8rhV8wZdz1B/Kv60VfyoAzYyM89Oegr+L/wDbw8VS6/8AtOeK/F1zdM62tzLaLbqBlk3BS2ckgKBk4oA4vwdqGmWurm+0ZHeytFHlKCf3zg/ebPBUkE1+0/7M/ia48f8A7OXxA+H+qMnm6jo9yQiAAAtE0e3H1INfz4eHvGTWs0cyy7of9Va+QrYK9BvJyPxwK/Q39kb4ran4N8bQafqVwkdtMrpOm7dhJBjk9DzjAoA/zSfiZZXHhT4ga94RvRtks9SnQr6FXIP8q8yuwHleRTkE19/f8FTfAtn8PP8AgoD8TvDdkgWzOtTXFuQMAxT4kUj2+avz6kxt49aAIasQ/wCtiNV6liyF460AdICy4NaKsrJhjjPf3rnoLgAbJOtaSSyHg9KALkuzoDkis6WMkDNPeXnvTN4oA9u/Zw8Xr4W+KtlPdyNHalyhx/edcfzr6a+O6bPFX7/5ppnaV88dR8tfntYamdK1i21CIZMMyyD6rz/OvvP426vaeIdQ0XxBat89zYRSyrn+NhjmgDyU4AwO/FNBIHljpTMsFx60oPBFAEg5HPao3+9RGQoOfWpdwxmgCD7vXvRT3YGmDkZFABTlXdQhAPNNoAeBtJFRjpTtppKACq13/wAe7VZqre/8ekn0rOqrwfoVS/iRP7HP+CMh/wCMVrD6yf8AoRr3j4Trj/gpt4YYdrGb/wBAevAf+CMXH7K1gT/ek/8AQq95+FvH/BTTw8P+nKb/ANAav8mvEx8ua4l9uf8AE/0T4S/5FdNeSP2k8XTE+C/EIJ/5c7v/ANBavwL1bj9k74QMeM+KLr/0IV+7fjCUDwVrwX/nzuv/AEBq/CjW0z+yP8ID3/4Si4/9Dr8e4edrLs1+TZ9dXhyo/ePUJN2m2gH/AD7L/wCgiqMKN5K8HoKdcMTpVt7Wo/8AQRWtaOPssX+4v8q/q3wRX7rEf9ufkz+dfE6NqtL/ALe/Q//X/WPRLotJdKT0gf8A9BNflbrQJ/Ym+JZHbxPF/MV+luiXOJ52zndC/wD6DX5qaywb9iH4m8dPE0f/ALKa/wAWaH+//f8Amf6d5TFey+4++vFGT+wjqoz18MH/ANECvyW/YU+X4KaSx/uv/M1+sPiiTb+wrqfv4ZI/8gf/AFq/J39hQFvglpR7AP8AzNe9kH+5z/6+R/KR1VY2qfI/GD/gsSUb4l6Xn/noP0r8rIruCIBGGcV+pH/BY3/kpemez/0r8k7gkx/Lwa/058H/APkR0/66s/gvxXf/AAtTOpW8tc7jxnmpZdT8kAQruDccVwUSyLjzCWz0rSt9Plfa8U2xR1yeRX6gz8tWxleINCugj6lJfzRxsc7Bx+A5FcLqOhXDWxuo7a5lH/PSQ/1r2C81BIguj2Mb3lwByxXCj8c1zOpG41KVrLVL4QRj/lnHxgj1PekM8W+z3nlGN0wAe9aGm2WmXAJvJ/LA6iu3/sjw4jjJkuJCepPFTPDpu8RLagLQBz0+m6VHbbrMS3WR1HQfXmuQkR4l2OO+a9elFysAt9JQRow+fvXmup6bcQymWY4BOAKAOdIwcUlTTRPGcvxmoaAHouTmv9OT/gzx+FqeEf2CvEfj+WLEviDXXYMR1WCNVGD9Sa/zI7ZPNdYh1Y4/Piv9hb/g3j+C7fB7/glZ8ONJmiEUmqWz6jJxyxuHLfntxQB+a3/B4N8JD43/AGAfD/j63TfL4Y1jezAZIikTbyfQkfnX+Yc4IWv9lL/gvR8HLL4y/wDBKn4teH2jDXNhpRvrc45D27CTj8ARX+NlcRtA7xEY2kqfrmgCnRRRQAUUUUAFFFFABRRRQAV/oIf8GVPjpJNI+Lfw+EmGhNjdhc/3jImcfSv8++v7o/8AgykngX4xfFu2J+Z9LszjvxKef1oA+PP+Dvj9mLwf8HP28dL+L3he3W2l8f6f9rvFjXarTwkRs5wBlmGCa/kfr+83/g9n01f+E0+DmreXhmsr1C//AANSB+tfwZUAFfvJ/wAG1d/bWH/BYH4WyXUJuFaS9XYOxNs+G/Cvwbr9uv8Ag3Z1gaJ/wVv+FV63H+k3CZP+3Ay/1oA/of8A+DuX/gmH4W8PjTv+ChPwtsPss99Ilh4kjiT5Gb/ljcMR0Y52kn0r73/4MzfC7af+w7418Rsv/H5r+1Se4SIf41+m3/ByDotzrH/BIr4jJaorlIrWVgRn5VkGT9Rmvmb/AINNfC1voP8AwSv0/U7ZMSajq97Ix6Z2sFH1oA0f+DruR/8Ah0/rnGc6nYlvUfvOK/yhZByPoP5Cv9V7/g7T1uPSP+CWd9YP11DV7RAf90k/0r/KilyG2t1H/wCqgCKiiigAooooAKKKKACiiigAooooAKKKKACiiigAooooAKKKKACiiigAooooAK/sr/4M1df/ALO/bA8daTkYu9HiyPZJQa/jUr+0v/gzO+Feu+If2ofiD8SoCVstF0qGJsj5WeaTgdeuFJoA/rn/AODhz4kR/Df/AIJXfEm9WTy5b+1WyHOCfPO0j8RX+Oqx6mv9QD/g76+MUHgf9gDSfhuJCk3ijVkCpnlltvnY/QbhX+X+eBmgD6g/Yt8JHx3+1L4J8KLA1wbvVIE2LkkktxjHpX9s/jr9jTXfCGtTaP4y0i5VYoUkjW8Q/vxgsqRkgKBnsDX8pH/BFDTbLVf+CnnwjsdRUPC2uQlgeAQATiv9h/XNB+Hnjhl8PeLNLt7+G3jjIaVQxzyCBnpj60Afwq6n+zXpz2Njd3Dm3urkyG78okNGF2/K6YyB6VxfiP4Ay3uqWcOpweQkKFLXoqMoOFbI6MfU1/Yf8ZP+CZ3wn8atd6v4BkbSdQu8llBJiY8fiOg71+XvxZ/YN+OPglL3+3NPOo2CxKiyW67lwnOeMkZ+nHrQB/PnrvwkuLnSVt3tFktbGUmaE4+4Cc/dOXOOvIBNZF98Jr2J11fRZWt2BEFsbpcxeS2crlsjLt0HYLg1+qeqfDKDTEGoXlodJVD5MMaDdIrZyPM3AArnPNeS+I/Bei6nHc6dbyTiaJ2lkaZMxiJRg7ecHJyeg570Afnf4c8B3tjczzWVtJuLhBDJ/wAe54GZQehXryDgEV1Om+E4LHRpZzBdQ3ZYDcq74u4ymflKeuDxkV9lL4I1HTfMl00tJEY3mVHGHeJzxEVyQFAPG01k3FnJpyWdjp1yqTzqxaznUfuo1Pzc9fYZNAHxhpGhgaguiWF21nazI5mSRcmRh0ZWPOAc5PAFJdao0F/bMtn5pQfZ3WQl1kAJPmD0xxivX9dt7e815Z9LeO8trSKRpdmN8SsSGCgZ3bRjA4968faytJVuNb04HzkxEzzHbGI2PyHgnB9aAOL8V3a+H9E81IP7JkkDMCnztcLnq+c4z0rwzW73Tv7Plmsbr7Osg+ZCp3M3fbxjNfQ1z4cj0+JNKnlnvLWUGRp8bnT2Xr8uenSiDwLc+IpJL7TxBNECsfnPtxGDgLkdNx6dKAPirVllvpCZAYobS3yEKkySFv4j7j0zj3rqPA+s6tpd2YLC5N1DKSx+0ALBHlexOAHHpnrX0XqnwpSTUYrvVnMam8dZnX/XBRjZtHQqapav8BNX0wXMOqPcKu8Tm0iRQzRMcq+SeGx6flQB9H/s4axbnUYTeRSTQb1Tz4GZPMPX5vUDPUce9ej/ABq8M2954v8AtcEC26xfPbySHzfMKkEKO/Byeea+X/h4uoaL4ht7uNne5QBPsjKVBjOTzk/e6emTX6F+J9KtZvDuk+LtQkexaAyP9ojUO4+QYRV6Zzgc9PegD9S/+CSvh8/Eaxt9Ysllljg1M3KXEowZwnLsRxjngZr+lTXrO4urCS1sJFt7gj93IQG2n8jX4Tf8ETtGu7fwD9uvVhErpO7rFn5Q7rt3DJCkkdj0r967eBEXynO7ByvPrQBHBaziwSGd97NHskYDbuOOW46GuO0D4caD4dvJb7TlbzJzl3kYuxGemTXoSyxs/lrjgdM07z7YMyFgGTkjIz/OgDM1PfHpczZ+6jYP05H8q/h0/aO8V3EnxM8XbJgHhvp51kCjzIHLnLHIy6kdu9f2/wDia9SPwvf3sJyEt5W+Xn7qseMfSv4Ovjh4h0/Uvidrc2oWkZa7u5IreYZ3q2STvHTH1oA8T8P+KLS7t4HtZZ7a4cHbJChiS6wSMqD69WB/MV7L4D8USaLq0LfM7q27O1kjk55XnnOfrXz7e6pJplg1lZ+TKwRhxjZG+SSqkcAH8Me9VB44fQWbSNfneZbbmJ1XlD2ZjgEkDuBgigD8N/8Agubp1rJ+2Db+M9Mt3httW0i2JJHBlizG344C5r8ZZBgY9DX7wf8ABX2WfxnoPhnxiqiaOxlkgknxjeJACv6ivwelOD5Z5xgUAVcsW2irEeecVCiHfmrCrtoA0YIlkUFutXiWX6VSgkCKD3q+wyOOaAKZcliKnVG27iRUJjKsWP1oM3GOlAFS5iA3N3Ubh+NfSuiaw+ueFNPdjueFfLJPUBTxj2r5wlkUx7D1PevUPhpftIlxp2eEAZf60Aepkgge1IqlhkUjcYxzTwwByKAHAMOOKVgSMU3zP8/5FHXnOKAG7fm2mhlIOBS5xSFsnNACYI60q8tSFietAwG3UAPZsHiozSkknJpcfLmgBtVb3m1ce1WxycVXuuIHB9Kzqu0H6FUv4kT+xT/gjJ/yapYp6NJ/6HXvXwvGP+Cm+gL6WUx/8cavC/8AgjFs/wCGWLIe7/8Aode5/DU5/wCCoGhoO2nzn/xxq/ya8T/+Rri1/iP9E+Ef+RZT9EfsF4v/AORN172tLsf+OvX4Za22P2SfhCvf/hJ5/wD0Ov3J8WNjwXr3vaXf/oL1+F+tg/8ADJvwibP/ADM836vX4/w8tfmvyZ9li+3kfulLJt0+EN/z7D/0Gti1kX7LH/uj+VYN3xp8HvbL/wCg1sWn/HrF/uL/ACr+rPBD+FiH/g/Jn85+KH8Wl/29+h//0P0g0mfa8rD/AJ5OP/HTX53ar/yZB8Tc/wDQyxfyWvvnRpsrIf8Apm/8jXwBqDE/sNfE5m5/4qaP/wBBSv8AFjDv/b/vP9Psv0oqx95eLHz+wtqSr/0LJ/8ARA/xr8p/2FJvL+CWlIRxh/5mv1N8Tybv2G9RGf8AmWW/9ECvyy/YXRT8E9KI64f+Zr3cif8AsU/+vkfykbSd5Sfk/wA0fih/wWUuEj+JencdJD/KvyQ8+OTkdMV+tn/BZiMn4labxn5/6V+RCKqId6np1Ff6ceED/wCEGi/63Z/CPi0l/bNS3mWre9txNgkMRwBT4vFlrBcmyVTcSn+HHBPpXO3McADSxqScZpbUvE6yMwVc8f3q/Uj8pO4tbrVC5uhCtkW/EkVTvVguZTLIqO/fAx+NY91r+n2cJ+1SMfdefzrjpPGZjctZRE/7RP8ASgDsbiBy3mx4QD6Csx3eIAb+T3JzXGy6vf6ipkmmCj+6OCaypLqBfmiLu3+10oA9Hkv5UhZIcAkda8u1G4ujOfPbdzkUpv78DJPyntVF5WmP73rQBCzs33jmmVIyMo3YwKjoA9A+F3hyfxj8QdE8K2ilpdQvYYFUc7i7gAV/t5/syeGbf4B/sa+EtBkgEUXhrw5bs8Y4/wBRbKz/AInmv8eD/gk98Lbn4w/8FCvhP4Kig86KfxHZNKMZAjSQM2f+Ag/lX+vX/wAFFfiyn7O37BHxL+Ju3C6P4futoXH8UPlqOfQmgD4c/Y9/bz8G/wDBZf8AY7+LtnpGiHSYbB9R0Axu/mB2ML7X6cV/kT/Fbw1d+DPiR4g8I6gmyfTdQuLd1xjBjkZTxX+gT/wZz+Ol1v4I/FzwOz/vJtYN4V7lZYiNx/4FxX8Wf/BUrwSfh5/wUD+LfhIjb9k8SXoUYwNryFhQB+f1FFFABRRRQAUUUUAFFFFABX9rP/Bl3Ncj9rH4hxpLtjbQlBj/AL22VcH9a/imr+x7/gzY1eOx/bi8V6W337vQZMf8BcGgD9Ff+D1nQ/N8B/C3xAVBMM1zDu9NxUj+Vf55lf6Mv/B6RH/xYX4duzAkai+K/wA5qgAr9SP+CMfjmw+Hf/BSL4XeItSYRx/2vDFuJwB5h2frmvy3r6i/Yntru8/a3+HFrYsUlbxDYFWXqCJlNAH+tT/wXpME3/BKH4nCXBEmnxBc9DlkwP1ryP8A4Nn/AA1/wjX/AASb8EREf8fVxeTZ9jL1/Sv0C/bs/ZBf9uH9jPVf2bZNT/sd9ZtYB9rZS+1oyrYKjqCBXV/sKfsoaT+xB+yz4W/Zw0W9OpJ4dgZHuSNgkeRmdiFOTjJwKAPw4/4O5NO+2f8ABLuS7AB+z63an6A7hX+VfN97nqQD+YzX+rd/wdgwPc/8EpNanxgxapYn83Ir/KSm+9n2H8hQBDRRRQAUUUUAFFFFABRRRQAUUUUAFFFFABRRRQAUUUUAFFFFABRRRQAUUUUAPTngdTxX+lh/wZt/B+Tw5+xz4x+MM0Oxte1f7MrFcFkt0wCD6Ak1/mqW6b3C4JJIAwMnn096/wBi/wD4N/PgfN8Cv+CVvwy0K+tTZ3Or2P8Aac0Z4bddZcZ/4DjigD+en/g9kGqR+EvgxIkj/ZHn1Lcufl3/ALrB6ehr/PlPSv8ASX/4POfBi61+yj8OPGoTcNM1aeIn0EyJ/Va/zaT0oA+pv2MviHdfCf8AaC0P4j2UrW8ukO06yoSGRtpUMCOcjNf6FH7Av/BazTfFt1o/h74uSCW0JW3SdHPmyNjAdwxyeh7V/nU/BGxDXOpasoUtawj5W64Y4JH06190/BDxzNoWt6fq1rI32m3cPbruLchtwJH17cUAf7Evwx+K/gj4t6K2veAdQjvxGdsmw4KHAOGHY4PpXozFZeHUMh4bI+6T255/Kv8AN3/Zr/4KDfH74E+INN8T+DdedL2aZnurM5aHYecOCcHJ7DoO9f1PfBH/AILifDbxT8PU1D4kaPJa68gCLBbtuFyxGNyZwF+bse3egD9N/wBqL9nL4L/Ejwdcax4xji0u4t42ZLyMBSCBnBH8WT1zzX8+nir4eWOo26+H41R518xGHGwwq+5WO4dWA6EYruPiR+3t8S/jZ45nj1WY2Oh2pJawViCUx8oIHPuzfkKzdK8deHZ7+K4unVpZY5fOYjDRZ5iXJPIA5P1oA8b1fw7bWNq19oFnJbSI6wFpssImHUgZ+VBkDgbfpXzD8Q/DN27XkU+nKA0Q3XgfBbp93nI3DJO4Aehr9DFvofEEaWNuY5reVBGFvCFPyDdvbIz6e3HWvGvGvw206/0U3s90nkRM6HywxV2CjajeqewyT270AfldcaG6rY32nubXT1jnEgjwsjAZG88HIJHIrkNZ8Ai8s4Y552kvbpEkE8SnyViXGBIFG0c9zX39f/CzU7j/AIm2t6atst8wsUiTB2Q5w0ijPBx2OOMVyqeDdT0mTU57Gye4i3i0QICEe2Ug4QHqwxk0AfPVp4P8R2ukz3N6/wBseCNV8y2VWUwvwqBRgk561p6V8OoFP2y2sDYeREZEglwiO7YAZwe+ScV9aeG/C2mNZyw2KyadZQossVxtG6NyfuOGwTzXRXXhNvEatpVlG1vqHnR+ddXnEDhGyCAPzoA+WvDfw/1TSPE8GvXqQancwQPHcI4LIHYZySOAFH3e/vW6/hu51nw3BqYMml3kanG8hpLkEkARk5OAOg619aWvhC/0aT7ZbwwwpesVbksl233RgLkqvU5xVNPD3hvR5bE7Df6rATGtqWOIZAxweB9wDjJoA+D9a+FmrXd3aa3aLNDawBppkKjzCp4Z2yMknpz07V9NeDY1tvh7PrHh+1E1ykI+zRXJyjFflKhD/FnnPWvq2HQNP8RXI0TxYUW/uR5szQcxJF3jP8K/UmtXxX8JtJ8M6Gtro0kZlSNp7MsNqhSv3z+PNAH3v/wRn0q303w9r9umRcR+SJGzwzAfNgY28dOO1ftbr+qrZQZY5cjhcd/rX5v/APBOfwMvw/8AAWmaWqKW1GGW9lmxyxYgIB7EHNfpHrOnNqkZs2A+bgH0oA+PPjP8Q/il4Uur220sxtNFbia0hVsSSr3wO5Hevz61n9oT9oXxv4httf0SVrbSonS2kmgH76SbP+rKc8Z4r9Rfjn8Jh47msb23mNreWhXy7pQThR1BwRwe9fD37Udlefsz/ALV/iDp8cK69dDyoCBthMrHAbb/AHsfNn2oA6LxH+3L8PPB/wALfFei3Wopc61pWnskltHyyzSqVK47ncTmv5RvG1tLbXX/AAlN+2+51aVhIjdYWb7px2zzz2xXuGl6tpa2v9u69JKb7UJJJLlpchnmYkjdnrivnfx9rhvtZ3aaoM0cZSYkfK5b7mO2etAHh11HY39w8Qgeyhi/cy5wBM2Cdyl+vBGCPWuJvPEE+lalFomo2+eP9FvYl3R46bZOMAj1bg9q9Ovfs0unWsd2ySiAguJORG4JUL+XbkV414j8RpbZuUk8zTpzi5ihyTtBOMbsdx0oA+U/297VfFP7OWsx3KxtcWrRzRBRjhDgsB756jiv5vJSDISOnH8q/ox/aKvLfxd8MNditN6g2ciRB+oRRkA81/OY+NxAGMH/APV+lAD42wcU+ok61LQBKoyM1tRjgH14rGQ4UE1sI44FAD5kUrmst1Aya15CCmRWVJ0NAFcqD1rtfAk0dt4iAJIEi4x7muLbhN1XtLuPsuqW0zHAEi5PtnmgD6aIeKRo2XuaYxIPHenfaFmPmeoBHuDyD+VLkHpQADOOaKRnwOaasgKnNAD6VRk4puflzSIx60APYYOKSgnPNTbFoAh5zz0pd3GB0pX/ALvam0ASRgE59KgvPmgkU+lWE4BNQXJBt3x/dNZ1vgZVL+JE/sR/4IyDH7Lliv8AtP8A+hV7p8MR/wAbQdEP/UPn/wDQT/jXhn/BGX/k12x/3n/9Cr3P4Yn/AI2h6IP+ofP/AOgmv8mPErXM8W/KR/opwf8A8i2n6I/Xjxbz4L14/wDTpd/+gMf61+HmtqP+GS/hGPTxRN/6Mr9xvFYB8FeIPa0u/wD0Wa/DrW/+TTPhH/2NE3/oyvyDh34v+3l+TPsK2qVz9y7tB/Z0R/u24A/75Falp/x6xf7i/wAqzLn/AJBkf/XuP/QRWnaf8esX+4v8q/qvwOf7rEf9ufkz+dvFJfvaX/b36H//0fvbw+flf/rm/wDI18JX3/JjHxP/AOxoj/8AQY6+5tAkXa/+zC4P5V8MX7qn7C/xPZun/CUR/wDoMdf4uYWP+3tep/qFgV+4Pt7xMN37D2qqeP8Aimm/9ECvzB/YTxH8FNKHs/8AM1+nPiwn/hh7VSnUeGm/9EivzB/YTcH4J6V67X/ma9jI/wDcqn/XyP5SLn8T9D8af+CwVuJviRprt03n+lfktJbQyFxjAzX65f8ABXw4+I+mr1IY8fgK/JmHULcOyyAdT1r/AEz8H/8AkR0v66s/hDxa/wCRvP8ArocVrEUGlxpLdEiOQnAUZP1+leW6vd3pvyY5fMHQMOh+mK+jbm60e3VHeIDz8IzEbuO+0dc/SucuvBMF1vbUAltZp9ydyqZHsrEMfyr9ZZ+UniFgl9OpW0QzzOdpXGcgVsXWl2tlGsmrl0kcZK7du0/3a7ew03wbYu9vpl7c3L8gyxJwh9jWDf6bOsrXsgllgHG+VtuffHU0gODAjd9uMY6cY4qYzfZpMBAWPc10Vjpv9sOYLNxGAeXKknHscV0cfhXw/F+4uJJbiQ8fLGev1oA80mRpHEsvQ9qiVLNmyFcgdcGvYbfwPdFyumWbOF5/fPgVd/4V5qkh8yf7LZoeuWBI/KgDxO4lgnIW3Vgg9fWs4xlep4r1fxDoHh3QF8kahDcOeoiDEj9MV5lMINxWM5HagD+mX/g1E+EEHxK/4KhaTrV7D51v4e067v8AJ6B1TYh/N81/af8A8HQfxsHwf/4JTeK9GVts/i2eDSFx6SEyPx/wCv55f+DLv4atffFD4kfE1oQfsFnFZpLjlfPbJGfcLX1//wAHpPxpi034FfDT4HQSEPqWpzapIoJ+7DH5a5/Fz+VAH58f8GYnxBl079pz4h/DyZ90N9oq3IjPd45QP61+On/Bxz8Nk+HX/BWL4lrAuyLVbiO/QdOJkB/U5r69/wCDTHx6nhL/AIKd2PhxmwPEGmXNpj1YKXA/MV1P/B3l4BTwz/wUisPEypsGs+H7V2wMZZCy5/QigD+UOipdi5xmjy1/z/8AroAiopWGDikoAKKKKACiiigAr+un/gz2ujD/AMFENRhxw+h3PPv8vFfyLV/Wj/waESyJ/wAFFrlB/Ho9yfyVaAP2d/4PSbVH+AHw9vO66i6j8cV/nI1/o0/8HpbTr8BPh1Gn3P7Qcmv85agAr9Bf+CWXg2fx5+3z8L/D9upZm120fA5PySqTj8M1+fVft1/wbv8Ag+Txt/wVh+GGkrH5iR3Mtw/GceTGzCgD/Ydtw8GnQRIeFjUA/QVF8w5NXNv+hxxgcqoH5CoHZI8GYhQePmOAfbnv7UAfzcf8HVlpJJ/wSR8SyjkRalYk/TzFr/Jyc5I+gr/XT/4OcdLXUf8AgkR4+ikj8wxS2co9sTKK/wAio+9ACUUUUAFFFFABRRRQAUUUUAFFFFABRRRQAUUUUAFFFFABRRRQAUUUUAFFFKBmgD6e/Yx+DesftAftReBfhBocBuJ9c1qzttmCRteVQxOPQc/Sv9wfwL4R0bwB8P8ARPBugxrBZaZaQ20KLwFSNAqj8hX+V9/warfs6H4z/wDBTfRvGd7Gr2ng21l1I7xkeZjYh/BmBr/SR/4KIfty+C/+CfP7N99+0T4206TVbW1uILRLWOQRF5J22rhiCAACaAPw3/4O7/C95rP/AATUttbtk3Lp2sWzMw5wrkrX+Wxla/1q/wDgtbf2P7ZX/BDfW/i1plmbZNU0e116OBjvaNRtfG445A71/kobSr49D/KgD6U+FGnW1v4Mv9YYN58sqoGwcBFGcfnXqHhjXG0Od7lVz5nGfTNeZ/DbStRHgOXUCHMU1wR7fL1rr4YpJINxBUDgUAfa3gX4ktGpeKXa2ckn+6PSvvv4M/GjTEVNU1e7AhjX5ACPNDZIBx1xn2r8WtD1VrYqs+75emO/tXsfhTxxf6Oz31qQsw4z/eX0544oA/o38A/Eue7aHUJrwRNOQZI5P9ZOoPBb+6cdq990z4g6heXUN5azpLHIGZ7eRggAAKhsnsvrX86fgz44SvMJbm5kaVcbTJ82W79DxX2b4Y/aYSW4nnnjWBZo4rd03ZDRAfNt9CxoA/cmD4peIdUmhj1KNnaS1+zpGhbZsI3By2MYOOucV3KeL5bRrU+IJ4wtqqtDaWoDoXYYDOwJy4AzX5meC/j5o8+u29pFqOy2jt1DyqciPIwI/LPLYUAEgEV9N+G/HekW1pc3WnSQ2tvNGQ0RQvLOcZ3bedo/KgD7J0PVPDcMoeSeWfULwrIy3AKJGFJLMFxjkcZ96nTxN/ZNk3iDV7QfZknka2VOEiZ/lAYjr6/SvnjTvFEWl/Z01JBJdhY3ecsXPlPjEKoB1I4GAa37C9kC31zGJ74yTlFsZlIhRSD8xPQbe/PFAHsF94r0O91G3stetllEDeaJh8sM7HDAE9OKmufGmj6c8tgyrqEt9csz6a/ACA8bH7djXj2sXZeC38ONs1KLbh7cP+5gJ53Aj5Rt98E1w+oSakkUmm2Ei3NrGMT6hn5gvOI42PJOegHTHWgD1W0+I1npesiz0yGSO7nEkcbOwMVhGeuT6+hrldN+Jvh+4aFDEYlsVaL7ep+a9lYnBUnqMk5rxGxt9Umx4d0+4mhcpJIkVwCpcE5EUzEfMT1GDV/w7pGoQah59/NbQzWIZGgnX91asTkMqDhuDxQB9R+FPFfiBvFFp4biSCdLtBJfouC0cQO4bjnrjrXreteMpfiPfJp8pNtYysbO24/ePgbQoHZS1eD+AfB+qeHfC9zqUIWW71WQmOYMqO8fdg+flU5PFff37Ef7PCeNvijD408WR/adOsJFYEgiNUjGQFHr74oA/Xb9l+3udHvbfwVfKiNoenW9uEH3lOwFt3r9a+4dg65r4g+FcM+n/HK9aRtwvxI+R6Zyo/IAV9wD7lAGXcRZ+U4wTjkZr8Zf+Cu+q3N74c8OeCLJDsR3u3YfdyfkUEHjpnn6V+0j43At61+TP/BQXwhJ4g8V2LEsYxaIGx22yHoMj1/SgD+efxf4e/tSIxXREspVSNvqmNxPpkg1+e3x41jS9HklksDJDcNKA8aZO6QdQv4c1+oPxo042N6t9prtNLGAsWPk34A+8Ce/vX49fHy71rV9avLq6ZYHikLCLbgh8jnPT9aAOBvvFxn0QA3JaAsCI8jc7jux9jxXPeKNYebTw90EilUDKJymPQ/zryZNZ1a1muJRHtAwAsgwcnqVH9aW617TjpgTUl82Zznkc57EH296APLviNdQ3mj6pp0CkJeWcpILFvm2HOPQcdq/n3uo2iuGhPVePyFfv7rzWFxLLErMzAMrMxyGLA8AfSvwe8WIIvFN/GBgLcSAD0wxFAGFHHk5NTCPn/P+NNTrUtAAVVPm61ZilVMKSOaqsMjFKuBjNAGq7ZUVWnjkk2iBd57inI25c5ziu08FfELVvAV3cXOjw20stynl7riJZPL/ANpdw4NAFPTvhz8QNVg82y0m5eI87vLO386w/E/hrVfC16tjq4Al2q3DBsZ7HHQ10HiD4nfELXD5WrapNJH2RW2qB6YXHSvPp5LiU+fKSfUn/wDWaAPpvQpPP0uCcc7o1H5VePAA71y/ge4eXw9AH/hzXUyMGckUAPf7tMGMccGnMwIxUVAEmcdKPM/z/kVGeKDwcGgCUSYpfM3EA1CCucMad8vDKeKALePkwKaMLzUWVPO6lDA8CgCbcfSq13LttnPtT9zd/wDP61VvTus5MehqZfA/Qql/Eif2Nf8ABGMlv2XNPYdzJ/6HXu3wyI/4eiaJ/wBg6f8A9BNeGf8ABF4g/sr6aPQyf+hV7h8L/m/4Ki6Njtp84/8AHTX+S3iX/wAjXF+k/wAz/Rbg+P8Awm0/RH68+KiP+EN8Qc/8ud3/AOgGvw917P8AwyL8I/8AsaJv/Rlft54p/wCRP8Qe1ndZ/BW/xr8RfEHH7IvwjJ/6GmX/ANDr8h4d+L/t5fkz62s9EfuJcPu02L/rh/7KK2bT/j1i/wBxf5Vz0jn+zYVP/PAf+gVv2jr9li/3F/lX9VeB/wDCxH/bn5M/nfxS/i0v+3v0P//S+5PDrbo5j/0zevh3U/m/YS+KAH/Q0R/+gx19s+G2JhlPrG/8q+KL5c/sKfE8Hv4njP8A47HX+MdB/wDCj8j/AFFwEX9XXyPtrxQwP7EGsD/qWj/6IFfl7+wl/wAkX0v/AHW/9Cav1B8Ujb+xHrCjn/imj/6IFfl/+wphfgtpR74b/wBCau/Jv9wq/wCOP5MqqtX/AIf1R+OX/BX1pP8AhaOm7BwTn9K/Hu5AjkfcuTk1+xf/AAV2Td8TNMcf3gPzFfkTqNk/ls5POTX+m/g7G+R0/wCurP4Q8XnfOJ+rPOPEmrSp5NtYORMrArt/hJ+ma2/I1CPzP7fk+3XLr8pZs7APY9f0+tWjaQNAzKiiU4w+ORiqSvcoCjliPUmv1Y/Jzn/sF95jTJN9mVuGWIEAj6ZxXa6LaaPcwiC8LTkcYkPH5Vz20rkr196dF5qneh2kelAHs9nHp8EYitY0TbwFUD9anudR02zgzehUGeSBivIYPEF3ZvuLbfVj0rO8ReNoLiAwq25j1HUUAd7rfi7Rbq2ZLWd1XpuQ46V4JrOoO8jJBcSSqTnLNVWTWbiaLycAL6CsIsS27vQA92Yj0/z60sQ3ZJPTmozuPWrdjB9onWA8byF/M0Af6bn/AAZ5fBr/AIQj9ijxH8S3h2t4k1MKJMfeFuvT8zX4Tf8AB4z8ZrTxx+3X4Z+FtlKSnhPQ0WRVPSS5cyH8cYr+yb/g37+D978DP+CWHw70G8h2XF3ayam/HX7QSw/8dxX+cF/wcGfGT/hcn/BVT4n65G3mQWV6unxnrxbp5f8AMUAan/Buh40bwd/wVt+Eyg4F9qL25P8AvwuMfnX7i/8AB6Z4GSx+M/ws+IQTLajp9zaF/wDrg6sP/Qq/mr/4I7+M7b4f/wDBSv4Q+LrptkVt4htSxPo7hSP1r+v3/g9O8ES33wf+DnjyJcraXt/bsfeSOJh+i0Af55R4O406mkA8E06gCF/vU2nP96m0AFFFFABRRRQA4ISM1/WR/wAGhbQj/go/OJT850e5AH/AVr+TgPgYr+uP/gz50cah/wAFDdTvwufsuiXDZ9MhR/OgD9jf+D0VQf2dvh846jU3H8q/zjK/0hP+D0GxZ/2ZPAl8B8q6sR+YFf5vdABX9O//AAac/D6fxV/wVS0PxLGm5NE069nY4zjdEVGfxNfzEV/an/wZf+C01n9qb4keLmUFtJ0WFVPfM8wHH/fP60Af6S3ylQAK/lq/4OYv2sPHn7PHgn4PaB8NtauNJutb8WRLcG3lMZeFQSVYjkgnAr+o/wA0Ebh0NfxJ/wDB4J8N/FY8MfB740WmW0zT9aW0kVcny53KyKzenCsKAP2Q/wCC4ujXfjn/AIIw+NWkZp5jo9ndO55J27GJ/TrX+P8A3CGOVo26qSDn1HFf7MHx8Gn/AB2/4Ix63dTr56ar4BFwo65K2m5f1U1/jTajn7ZKTwS7Z+ueaAKNFFFABRRRQAUUUUAFFFFABRRRQAUUUUAFFFFABRRRQAUUUUAFFFFABTlGTim1oaVZSahqENnFy0jqo/Egf1oA/wBFH/gzN/ZuTSPg18QP2jdYsDHdX13HpVlcMMb4UHmOVOOgYqPwruP+DyP9pK38D/s1+BP2ddPkP2vxTqX2yUI+GENphgSvcFz3r92f+CGPwNi/Z8/4Jg/C3wbLAkV5d6d/aFy0Yxua6cyBm99hWv8AP6/4Opf2ov8Ahe//AAU41rwLp139o07wLbRaXEgO5FnAzNt9OW5+lAH9pfwN1OD9of8A4N34LONRdOvw9uLdgOf3tvC6Y+oxX+TBrVk+naxc2cow0UrKR9Div9Uv/g3H8SSfHH/giPH4Qk+fbJq2jnPPUdD+Egr/ADCfjv4YuPCnx68UeEdRQrJp+sXNrIvceVMU6fhQB9l+BPB66b8LvD1nINv21Gmk9PnPFR6j4UUq9rag71Yqv0r6i8beDW0PTPD1jp4AUabbMo6AnaCR9ea5DX/CGNSjWNvmuCCQAQRj36UAfKUWl3lszRTDlDg1qRxeWA7HPsK9jk8LJGkq5BDZyepB9TWFN4Hlt3jDEM0pG3HQigDhrW9ureZjDhQPbpXb6T4lmYjznYOD8v8AwHvTtR8KSW1yY1+XAyV71jNpE0MZkkBzGTzntQB9G6B8YNWW8hluAmFCxoygDGP4j619r6D8fLqDXdKdrzzZT+6l4wNjYHB9a/J2zlWGLMWQJDhfavQ7TWriFIIcZMZzvoA/fzwP8ZtNg8Qv4daQxBWFwl0x3NnACKue4PavvT4Y+JtPvLaXTtEvHl1CJj57zjCbZOX3eue1fzA+DviVcrfQLeXBS3iKlpQTwwPUZPXpX6g/s2ftSfZtWWx1ht8F5N5TkYBfHCEnr9aAP1xudCaLRr3UnT7LZX5MawwJukfA6+uGPSuXj8FR3S2iN5kcUQcpbIMJEwX/AFkuce55r3j4ba++s6ZDd297axG3TBaXBJB+6qeuBxxWgdP8N3lhqF+Ha2tIlxdnBElw4PRQezHjjtQB4Ciaho8LLrlwmomd2824SMZWOL7rxnrycDOK1tFsP7YuLU3tgl7I+2aXcPlm5wqsw+92z6V6/onw71O41mO+vm3RahaeTDGR8lvEMnDcHBOR9a998M/DnW9SvZNPsLSO0CRpDbQfd8sFQTIxI4DDpmgDzzwX8OdW8V6qNE0KyjjtHdUbapLwDP3YvUZr9ub3SdF/Zt+FWieHLONUu9XkSOVs4PIBf8s4rhv2TfgdbLqi67e2wjjsOd+CA8gqz+3RE48S+FZZifISZtqjOMhuQPcgUAeyW5h0L4rafc2X3J1RM/73B/WvtCNiEXNfENxLHcL4Z1yLo0ibj65wcfgeTX2whLRqR3FACy7SQa+Tf2n/AADL4i0NfEdsNzWy+W4x0BJOc+54NfWgj39TWP4g0mPVdHudMlXes8TJ+JFAH8kH7UXhWXR7m6it0MO9Bh+uwrwcfTB/Kvxl+KugyRNJqWs5YTbWxjDYByNw/wBoYzX9Nf7UXwm1Ga8n8/bnTZC5Vv4gozj3zk5+tfh78UfA2oX19d6jfxALeMWkY4PloOy0AfkV410W2kuBrMbM8/Qoq4AHYCvBNZu5opzNfAKznCx55+tfpJ4s8CXWoTS2vh+0813XKhBkhV/iPYV8Q+OvAGoadqpW3h+1yRjMsiDciZ9D0zmgDwu91Cyjvbe2gG9RiQnn73IxX4sfE2BLX4g6vDH91buX/wBCNfuG/gvVZJcNE0TGTccj6V+JHxbcSfEvW1GPlvJl49nIoA4NOtS1Cpwc08Pk4/z/ACoAfRRRQAAkNuqWSQPjjpUVFAAeaRl3oyZPOKWgnafxoA9j8CThdGWH+7n+eK7Hztgrz3wRuFkwH8P9Tmu5y3cZoAtCYse9KJTv2HioI2C9Rj8aUsrvnoRQBfGVBxUSkHhj/P8AwqHzHZlVT9af5kik/NyOnFAE3AGM8Un8GAaiMrsvzt+lRCRx270AW0OFy1PEirz1qk7vu3dqRXznb19KANAyqSVqC6/485PpVdHLZZuKbeS7bR8c8VFT4WXR/iR9T+yb/gi5/wAms6f9X/8AQ690+FIz/wAFRNI/68J//RbV4j/wRaiB/ZVsH9PMP5NXuXwqQD/gqHpJ/wCofP8A+izX+S/ibpmmLf8Aj/M/0b4T0yunfsj9bfFUgTwd4jY/8+l5/wCgEV+I/iLn9kH4R/8AYzzf+jDX7Y+Lzjwb4jHrZ3n/AKC1fibr3zfsi/CNP+pom/8ARhr8g4c+L5r8mfST6H7cz/8AHjCP+mA/9BFblp/x6xf7i/yrEuRixhP/AEwH8hW3af8AHrF/uL/Kv6s8D/4WI/7c/Jn89eKX8Wl/29+h/9P7U8Psy2zEd4n/AJV8a35x+wp8Tf8AsZov/QY6+xNBfEMq/wDTOT+VfHV7j/hhf4k+h8Sx5/75jr/F+lL/AIUWvX8z/UnBythkj7V8Vnb+xPrPt4aP/ogV+X/7CabvgrpTH0b/ANCav028aOT+xLqyrxu8OYP/AH4Ffmt+woqx/BPR4yOof+Zr1MkV8DUXecfyZNaV2/8AD+p+M3/BXqfy/iZpeP7wP5CvysGoW3k/vYw3J61+pP8AwWFlFt8RNKz1LV+RVxNhMfjX+nfgz/yI6f8AXVn8G+Lcv+FmbLtzqVmZGCxgKtVxf2DxldgrEklDLz3FVPL+UjPFfqT3Pyocx3SOdoA7c01UkJ8wDOPw4qxHFtTeq7sVRa9u5C0cUJQe/Q0gK19eeGVhfzt88nQrjgGvKr1oDM3kDA7CvRr6W7tLR8iNc/3VANeXSMWcs3U0AOjJqTJqupOanoAK7D4f6LceI/G2laHajL3V1FGPqzACuOPavuL/AIJvfDGT4w/twfDf4eqm+PUNds43H+z5y5/TNAH+xt+z1pll8B/2FvCdlI21fDnhK28zPABgtAzHn6V/i6/teeO7r4l/tPeO/Hd1IZX1PWrybcTnh5mI/Sv9j7/gpT40j+An/BNz4pa7pR2vpPhK9itucYIhMaYx04Nf4oOt6jPq2sXWpXBy88rOT7k5oA+kP2ONeTw1+0/4G1qR9vk6zavn/tstf6Df/B3ppc/iX/gnj4G8VwrvitNWgl3+guIMdfcgV/nD/CW7aw+J/h69j4aLULZh+Dqa/wBNv/g5M01PGP8AwQwsvFSp5z240G4DAfc3hQfzDUAf5cDk/lxTk+6T70jn5QB2pY/uH60ARE5OaSiigAooooAKKKKACv7K/wDgzO0e5vP22PGWqptMdpoDb+u755FAr+NSv7s/+DKjwrFL8UPi14qkHzw6fZQox9HkYkfpQB96/wDB5lZyP+xh4Mvm/g12NfzU1/mr1/pkf8HmVpdH9hjwjdgfuV8Rwhj6MyPgfkK/zO3AA4oARApPzdMiv9DD/gyv+FsGn+Afip8WJ12veTWlijZHITMh/pX+ejGua/1Cf+DQjwDL4e/4J3ar4xZOdX1y42n/AGURF/Q0Af1miZJUwBjFfnB/wVW/YmP7e37Fniv4EaVHA2vTJHdaTLKwVYruBwyEsRxlcqfrX6HxuttH50n3a/ky/wCCQf8AwVL8S/Gn/grb8ev2afiJ4jnvtPudRu5NAguJt8afYpzGY4VYkL8nJC4z160Aftz+yz+zX8R/hR/wTSsv2bPjQ8Vzrdj4du9NuDCxkQgxyKiq3fCkV/jTfHrwifAfxk8T+Dtu1dN1O5twO/7uQr/Sv94C7tY5opIXHDqQ3uCMfyr/ABUf+Cwnwll+C/8AwUh+LngopshTxHfSwj/YllZx/OgD8z6KKKACiiigAooooAKKKKACiiigAooooAKKKKACiiigBQCelBBHWnopILDtX6H+D/8Agmr+0Z4+/Yo1j9unwlZRXng/Q7v7JeAN/pCYUFpFXui7l3UAfncqlulKUOanlGzOBtOT/OvXvB/wD+MHj74ceIfi74Q8P3eo+G/CnknVr+FC0Vr9oOI/MI6biDQB4zsavpP9kD4La3+0J+0t4N+Dfh5xFd69qcFtG7DIBZxknHtXzlX9Q/8Awam/skyfHr/govY/FTWrDz9F8CWsl+8jfdS4PywZz3LGgD/TN8P6fof7MP7MFraXbrHZ+DdBXzXbhQLO3wzZ9DsyK/xPP2svivqv7Qn7Svj343XivM2v6zd3zvyQgnlZl3HoOOBX+r7/AMHEv7TH/DNP/BMD4galpl19l1LXbP8Asiz2tgl7r5Gx6/uy2a/mH/4Nwv8Agmx8Mf2wv+CePxuPjrTbe+v/ABhv0yynnjR3tpoIy8bxyMpZT5rLkjBNAH6l/wDBnt4pt9U/4J7eIfBMUuZrHxBdTOmfurNHHtOPcg1/C1/wVq+Ht/8ADD/gpf8AE7wjewC3lXxDPMiAY+WeXzU/MGv7Lv8Ag1G+H/xU/Zm+Lvxy/ZW+KenT2N1ok8YHm5VGMUskbMueOQV5HYD0r+fH/g4S+F7x/wDBc3WtGkhJi1240eYKoGWDRx7vxyO9AGV430251SPR7piX8vTY1SONcsCUAzj2rzG/tZ4XsLsRFlhDb5858xuoCr1z2Oa+2rPwrHfzl4/NENurRPNGMN8hx5ZB67cDp2zXEax8NWt7LT7vydsjShAV4ynI3EHnPIye1AHzHp/htbbdLFaCRriNmcN6dgvvmss+EpFsLWObb5ruSUIJ8tM8AH19a+q7fwFNbLEkUgclySjqS5J4wo9B1B+tZl14fOnN9nhtpmR5QJJgp2MxflV4PJ9PSgD5Y1vwbc3NwYvKaD7P/GRkO3fB9K5XVfBQlYTzMFRhkoM9R/jX3ZrHgv7RJHpvliPZAJI1TnBIzg4x0qkvgIQ30U2p2gvbi4CtEsYxHxyQVHGRigD89ZfBUk9y32xfs0Uahl/Hsax5dKuipguYzDHz5bn+LHpX6DeLfh3PqVpNqFtaLZI8gWRgpO5s9EHQY/KvENW+E+ozyJfXMwdI2IjgfhevUkcdug6UAfNGnDylaGQ5KgAivWfCHji68OX1u9ttbedrA9Rnv7Vj+IvAs2gzOkOWkdwp2jO5u+D6YrE+xi2vltzlmDfNjgjA4H50Afsf+zX+07daNHb6W++6uomHlec37tAD156iv268N+O5fiJZaaYbuz3k+ZNcoN0SED7hX1/rX8e+h6nqVncQzW7MfIJwASGByMcnmvuD4HftJal4PvzpWrXsped2EuzOFU8BwRy2O4NAH9Pekz6hZajPY61dvdXl60bm2UYUxp91lYcL681+hvwT0PWfiVrVrpMMBt3kKm5mzkkKMAEdRgDGa/Ab4C/tG+F9Q09tPmvZJ/tB+zpPI53qF5JyDwD/AHa/o/8A+Ceuv6Jr9/Jd2QxL9k+YHndjv75oA/UTw14e03w1o0Oj6dEI44wAQO5HevA/2pvhu3jv4cy3mmx+Zf6Y4uIOMnK/eA+or6b3BvmHemsqupVwCDwQaAPgfQLw6p8KNMmKkyW20gAYIYdSfSvt7w1f/wBpaHa3oP8ArIlJ+vQj868A8YeFrTwxdXUNmmy2vcSKOwkHUD0r1f4X3YufBltJ1xuH/j1AHoyttPNOk+7uzjFVWk83hBgjnI9K/MH9qj/goLZ/BzxfceAPBttFqEtrDm6mdjiFiegA5OBjn1oA8x/aM1bSpvFmr6fq0LPb+a3zg8Eg8D+lfkD8dfAv/CWObnSYPKFw+0rtOEiHJcgeteh/En9onXfE+jtrt5dF5NQZpmdydiJ1yB0BPr1r4O1f9qFbm8cT3ZS2jYxKuTmdu5Pqox0oA8S8ZaFJo2rPp32w2lkmVfZ/rJMHkLjoPrXnGp6PpMSyPBAotpF3JHkb2x/e/HmvYvGHi463ZvqGmwW8lwiGURMp2jjlgvTOOc1+T/xf/a3k8PSzWAmPmqWWVogQR1GM0Aex+Pdb8N+F9OubzxLGseVaRAmOSoJwT2GBX8qHjfVLbXPGWp6xaArHdXU0qg+jOSK/Qj4tfH/Vtd03UzNeMyXUZjRCTkBs5/OvzSkbfOWAxmgBaKKBQBZXlc0lMV88U+gApCwHFB6GoKAJ98fXJx3oVkdizHAHNQ5OMVJGqFtmR74FAHoPgO4Y6jNbA/IRmvV/Lz90n/P5V4n4NvBB4lhAHEw2mvezHg7T2x/KgDMkhPXP51FHEclm7VqvFk+tRNEqjGcUAU0UGQoOh6mnY2k7ecd6lVQOFGM0jRH7q8Z9KAIg3PuaQZEh/venb86mMBVR3yajMfzbe1ACQgspA5poyZAGpyrIPunFIn3t57UALIAOnpUF5/x6MfValZW8vOabd4Fiw77amovcbLo/xI+p/Zr/AMEWv+TUrD6S/wDoVe5fCjB/4KiaQD/0D5v/AEA14P8A8EWXx+ynYA+kv/oVe6/CRt3/AAVB0o+mnTf+g1/kv4nr/hRxf/b/AOB/o5wt/wAiykvJH6xeLz/xR3iL/rzvP/QTX4n67/yaP8I/+xom/wDRhr9sfGXHgzxFj/nzvf8A0Fq/EvX/APk0z4SDt/wk8v8A6Mr8f4edn/28vyZ9JVVmkfuDfACxgA/54D+QrXtP+PWL/cX+VYt+T9ht/wDrgP5Ctq0/49Yv9xf5V/VvggrUsR/25+TP558Uv41L/t79D//U+xdAIKzY/uSfyr4/uuf2F/iVjt4lj/8AQUr7D8OoDHKf+mb/AMq+PLj5f2F/iZnv4li/9Bjr/F6n/wAjJ/P8z/UfCf7uj7K8VjP7FWqg/wDQu/8AtAV+dP7DcSt8FNE9lk/nX6NeJk3fsW6p7+HD/wCk4r8/v2GLMf8ACltFB/uv/M125PP/AGSa/wCni/Jky+J+h+GP/BZED/hYulezV+Pt028AHpX7Ff8ABZSBv+Fi6WV6bq/HG4LDiv8AUHwWf/CFT/rqz+DPFn/kbyKcikjC80CK4kHyHAqMbsU+JgnGa/VHuflpXeFkfLtkioy5BEgOD3qa4kxnFZpYvz2pAZusxpPCZOlect9416LqpxanFecnnmgApyfeptOT71AE2M1/RX/wa/fBnS/i7/wVM8Lza1D5sOhwzX44+7JEpKn86/nVGe1f3Df8GYnwXtNZ+NnxB+MdzHmbSrCO2gcjo07kHB+i0Af0gf8ABzx8XV+Ev/BKXxhJHJ5cuu3FrpcfOC3nuSw+hUGv8jJyC5Ir/R4/4PO/jOumfs4eAfghHLt/trUm1FkzgkWowvHphvzr/OHbJPPWgDqPBcxt/F2mzqcFLmNgfowr/Uf/AOCu8zeNv+DcBdTuhvaTw/oMxPf5WjzX+WjoDGHWrSQ9pU/9CFf6oH7WdlL8R/8Ag2ki85N8reDLCXH/AFwKHP6UAf5VhGGOKd/B+NSXEYjuJFHZu9R/wfjQBVooooAKKKKACinBS3SkII4NACV/ojf8GVfgq9h+F/xY8bzpiG4ubG2jfHdPMYjPtmv87vaTj3r/AFRv+DST4bReCP8AgmW/il49kviDXrmRmIxuWKOJEwe46/jQB51/weO6Y0//AATR0K+RSfs/imy3E9fnR81/l/FGHOK/1aP+DtfQbLXf+CV809yQv2XxBYyrnudslf5UHATZ3B/n/wDqoAjgXMigjqRX+wv/AMG7Hw3h+Gn/AASm+G9l5IibU7Z79uxbzmODX+QN4Z0yTWfEFlpcQJa4mSMY/wBtgv8AM1/t3/8ABPf4fQfCb9iD4YeAYU2Np/h6yRhjGGMSsf1NAGj+3f8AtBaP+y1+yP49+OGrEAaBo9zPCCQMzCM+UMn+85A+lf43v7NP7WHxM+EP7bGhftP+DLpotcXxAl+X3EFzPNl1bHBBDnNf6RH/AAdcfHSz+F3/AATDv/Axn8q98V6jb2sC5wWjRt8vTtjAr/N5/wCCdHwHuf2kf20/h18HYo2b+1tZtY2CjJ2iRS5/BQT+FAH+158J/F83j34Y6D4xul8mfVNOt7t1P8LzRhsD2BJr/LM/4OuPgvc/DD/gqHq/iOGEpaeJrC3v1bBwZGXEmD9RX+qh4R0CDw34c0/w9Z8RWMMcCgAcLGqgD8q/h4/4PPf2cDqfw/8Ah3+0lpNvl7K4k0y9lA6rL88QJ9juFAH+fx4U8B+LvGwvf+EV0641A2Fu91OLeNpDHChAaRtoOFBIyTxzXLPGUYo6nK9a/vA/4M9f2HNK8b2vxO/aS+IenpfaNd2aeHIoLhA0c63Hzzj5gRgKqg455r8S/wDg4J/4JR3X/BOL9rK71TwNbMPh/wCMHe/0h1B2wbjmS3J6fI2do/u4oA/nyeP060wxuOoPFes/BLwfJ49+LnhrwdDGZ/7R1C2gKgZ4kkCn+Yr+zD/gv7/wb+6D8HP2evDv7Y37Juipa2mh6Ra2/ibTLZWyWCgm9UemWw4/GgD+HPBrotE8JeJvEkNzcaDp9xepZx+bO0EbSCNB1ZtoOBz1NYaoxfB6nHFf3Bf8GfP7KXhr4ta/8VfHXxD0VNS0R9MGjSG4jDQv9qILKCw67RkEdKAP4fzAy8MCP/rV6B8Lvhd42+Mnj3Svhh8ObB9S1vWZ1trO2T70kj9BX7U/8F6/+CTeqf8ABMn9qKceEEln+HviySS80O5ZTiHcctas3QtHnA9V5rz/AP4N9PBOoeO/+CrHwx0vTbfzzbXhu2XbnAhAYnn0AoGlc/Kf4xfBv4m/AP4g6j8Kfi/pFxoevaSwiubS5XZIhIyOCAcEc15YsYzX+lx/wdYf8Eq/CHxm/Z9m/bo+G9glt4v8IQqurGJcfbLIdXkI6tF2P92v81C0t5ry5jtLdSZJWCKvcknGKAasf1hf8G7X/BIf4Qf8FHvg78YdU+LUEck1rYpp+jzkNm2vZA7xzAjn5SOfav50P2vP2Uvit+xj8ftf/Z6+Mdg1jrGhXMkJODsmjDHy5UJADK4wQR2r/UA/4Nkv2Jbz9kb/AIJ56d4s8TI0WtfECYatPFIu0xxFQsKke65b8a/F7/g8A/Z78EeIfi58FfFnhuyUeJ/Et6+kSyxr+8lizGse7H3iC2ATQI/lX/aX/wCCSn7Rf7Nv7HHw+/ba1dY9R8IeO4FlDQBi9kzD5Fm4xh/4SK/K3ystjvX+1f4d/YM+G/xA/wCCaegfsWfFawS90v8A4Ra30+VXXLRyiFR5i9w6udwI7qK/yYfjv+wV8SPhp/wUD1X9hzQ7Y6jrMfiAaXZrGM+bHLIPKbA5+ZCD+dAH67/s1/8ABBC9/ag/4I86z+2n4Le6fx/p9zPd2FkgzHd2EWPMUjGdw524r+YTVdOvNJvptMv0aKe3YxyxuCGVlOGUj2Nf7fP7A37LujfsjfsfeCv2dbOJT/Y+mRxXQwNryuuZuMc7nJHPav8ALn/4OOf2b/hr+zh/wU/8X6H8K7dbTT9eSPVpLWNQI4ZpwTIqDsCQW9qAPxL+Fvw88U/Fbx5pfw88F2r3uq6xcxWltDGMs8kjBQAOT37dq/2M/wDgnj/wTl+H3wD/AOCamg/sZ/EPTIp4NV0pl1qGRQ2+5vEzPn6EgD6V/KB/waf/APBI+Pxhr3/Dw34zWPmafpbtD4dt51+WacDBn5GMJng+tf6EUcq+cFxwO/40Af4tn/BW/wDYZn/YA/bp8Y/s76c/2nSre4+0aXL/AHrW4HmRKR6qCFI9RX98X/Bu/wD8E2vCMH/BH/VvBXxr0VQfi+bi4vBMoLG1aPyoDgjPHzMPrX5Gf8FLP2F/FP8AwUP/AODimD4Q6RBJLoennT5tXuMfJDawwpLKd3vwB7mv79/BXhHQ/h34O0zwJ4ZgW203R7aG0t4kAULFCm0AAfSgD/Fq/wCCmv7CPj//AIJ5/tceI/2efGsZaK2uGn0yc9J7KRiYJM8clOD6Gv79f+DSL9jzxj8Af2MNb+Nvji0+xzfEO5jlsw6lZDa24KoxB6BmYkD6GuY/4LB/8Edfjf8A8FIf+Crnw78XW+mGD4b6TptmNW1X5djrDKXliHcuR8o+tf1ifD34d+Fvhd4G0r4Z+C7aOw0jRLWK0treMYCRRKFUD6AfnmgD+JL/AIPPvjLr9l8OPhp8ELJWFjqF5LqUjDOC0SlVX06kmv2F/wCDZL9kXXv2ZP8AgmJ4av8Axchi1LxrI+tlGGDHDcL+7Uj/AHefxr86/wDgu5+zh4x/b7/4Kqfs/wD7Jul6VMdEhh/tLU7oRlo1gE+ZAx6Y2pjr3r+w/wAFeGtH8B+D9N8FeH4FtbLS7aK1ghUABI4lCqvHHQUAWLHwh4Y0rU7jXNLsLe3vbvHnzxxKJZcf32ABJHqTX+et/wAF/fhpf2X/AAXT+GviG0VZP7Sjs5WB6BYFbJ+oC1/onIdwGK/je/4Lw/s+6vqn/BQ/4R/G420n9nLbS28l3hhGsmGVVLHgHkUAfltrPhawt72TU9RuwkMrO+2IHiYnA7chQATiuQ1jwxbadpFhpVkWufm8x74sFKqvzYwe5ycfWvrg+CLtZ5JorVPNijcvG+7YU4GU/wBo1w3g74c+F9Turpp76WXT47p3K5yGBABjVvY5BHbFAHzLcaJqGn6tp2rvGIE2Oys44MZHyoMcEn+dQJYLayQWd5EcfahNLI+7aiEkAevfNfTus/DS9kibR5o1W106cfYwxw+wt8rkdePTvW8fh/p+thra9he5NoSTGF2pcY/iP0PagD5o8RfDuW/ie88N3Y864HlxTqvDBxhgO4HBwans/Bezw7DY2qY84HyxIPmWTO0tu67SRnmvqV/Ct1pejLefZf8AiXyyrBapCPn2YJ+X/wCvXpeqfCvxDqFk+r6bEiRXkccc8jD/AFMcQ+QCMfdkbnJFAHxBpnw3F+sSOSJIQ6eUeUyvDtjuS3T61wM3g2C7tp/CvhnTvtNztZ5GuPlMDqec/X19q+0tM8H6xd38WqXcUtrEsQMEhBzHI+V3OD97J5xioNa8HW1xCC0mLwyf6U8alftKgDJ55UfX1oA/OS5+Ec+rWnkbYgbmRYwVGFxGNzkemeg9SDXgmpfBpLvxPcR2dsYERRNKhHIiBwSpPRq/X63+HNhcwR6LZaZPEt5N5ixs33UQHDq3XG7k/SshvhBqUF1p0uugS6q4lZlXDiaIDCbx2Hf8KAPyBuPhLfW2szaRpEBklu08y3lY7cIBzu965eHQH0u1a8uH8uazIEbkHDyZyynHBBAr9YpvgzZardy+H9LnZoJG33N5twY3/wCecZHBH16Vn2nwAt9a1JPDK6aAunIQZp/uMVBYuRxufjPHY4oA+LPBWs+KLW4kvZro2gitRNPEvOGB+UoBxwetfor+yt/wUY+IvwL1W31ctPNLbLh5F3c4IzxjBB6EZr59g+FU9lFPdtZ+ZezMzKEbcv2ROMsM4yTkk+lcIfBWu3E6Wtu0cQdWRxgrEICSeo6E9C3UHpQB/Zv+yl/wWb+FHxc8vw/8VLc6PqG0f6RHgxHJ6sM5H4cV+yvhnxj4V8Y6ZDq/hm7ivbedA6PEwbIYZHQ8V/msaBHrujCLWbFCljDKPOuud7hf4Bj7p4446Cv17/ZB/b58YfBvxRp2k6fJJcXV+6iG0lLMBbdCSx4z+HFAH9fHxruY7TwWb1xkpIhH41gfAHWVvvDN3ZuhUQS7ix6EuueK8Z1/9pj4f/ET9nW5+IGnXMfzyJbtGWz5dxu+6PU+ldD+yb4zudZ8C3h1CJYYbeRWUjjG/t/wHvQB7B4v8T3eg297qzSFLTT7OWebH9/GEB/Gv5Ofi0db8ZePtY+IFzKxmkllLW6gYKbu+ef881/Wp4m8O6Z478A6rp+kyic6rC2HzlS5Hy9PyxX8zPxp+EvjH4ca3qGmXliYL13IJZcN5RbnB6Ee4oA/GH9oT4oeKrZJ9F0XdFZTZQNtwd3Qr6dR2r4jtPigulW81lq6b7hY9pXvGc5yv1PWv1g+O/w0vHtZLiWJJxguwQfcJHB+rHn8a/I/xp4OvNI1QRta/v2UzCYrkMM42mgD0nRfis2neHhbODNe3h3tIeir2X61+Rf7Z+l6xpvigeLtPz9huzibHUOc9fY4r7ptL6aK8NteM0hb5kUfdTnoa8w+KVnp3i7wzf8Ah2+jwbhSN5wQnPBH40Afih4v1l5dHMSvkZ715Arl2DGvQPiFpt34e1Kbw7dAq1q5Q574PX9a89Rh1oAsUUL83SigAooooAKKKKACpUPBHZen49aip6kY2nvQBqaTMLXWLeQ9mBNfSAYuNx78/nXy/Ifl3Lww6GvpbRJ4rzSLe4B3FlFAF9UyOafwoAp5VhTXGQM9RQBCYuc04LlCpqUA9KXHuKAKjwnA21NHHj7xqQjHelG3vQBVxgkUbQWBzU7KpOcU4BQMUAV3i2nCVQvlAtHI9K1j0rOvYx9lkwc5FRVl7jRdH+JH1P7HP+CLzbf2VbH6Sf8AoVe8/B0lv+CnumE/9A+b/wBFtXhf/BGCLP7K1l/20/8AQq95+EKbP+Cnulj/AKh83/otq/yZ8UJf8KeMj/i/E/0a4V/5FlL0R+s3i7/kTPEfvZ3o/wDHWr8Sdf8A+TSvhKw6f8JPL/6MNftx4s/5EzxC3YWt5/6C1fiPrrAfsjfCUf8AUzy/+hmvx3IN/wDt5fkfUYj4kftvesTaWw9YB/IV0NmCbSIj+4v8q5275tLX/rgP5Cup02Rf7Ot/+uafyHtX9X+CX8LEf9ufkz+f/Eqjz14J+f6H/9X7I8OMPKmB7Ruf0r48uxn9hb4lf9jLEf0Svrjw658uc/8ATJ6+SLjn9hb4k+/iSL+S1/jFTj/woN+R/qRRVqOh9n+JH/4wu1MD/oXT/wCk4r4h/YZtQnwW0UH+4x/U19s+IHz+xjqAPQ+HP/aAFfHn7EEefg3omP8Anm38zWeVT/2ea/vr8mFWOq9D8Cv+CzX+j/EbTF/2jX4vzSiR2HTFfs7/AMFrm8r4l6WB6n+VfiiZMO1f6l+CX/JP0X5fqfwV4sf8jiZIeBnNR5I5JqCWQCPdVM3XHAr9Xe5+WFmSVW4zTI9uNvWoMbsnvUkQ2t81ICjrCH7PhR715uylTtPavWr7yjalWrzOcgzNgUAUKcvDCkPU0Dg5oAsgfMF9elf6cn/Bnj8GZvBv7C/iD4v6jAIX8RazJDGSMO0dsMZ+mWNf5lWl2k2p6pb6fZRmaWZlRUHJYscACv8AZ2/4It/Ab/hn3/gmz8MfA97aixvZtLjvrqHHzCa5JkOffBGaAP4m/wDg8e+KF/4r/bD8HfDl4pY7fwzpTgu6kRs9wwb5DjDAKBkiv43PI3SFV/DPXriv9fP/AILxf8EmfDf/AAUm/ZUv4fClnHF8RvDMTXmiXSqqyz+WNzWjMQSRKBhcng/lX+UD8VvgP8Vv2cviZ/wr/wCNfh+88P6tZyjzLW8iaNiqsOcHGQfUZoA4TW/APjfwLeafJ4t0u6037YsdxbfaYni82JiCrx7wNyn1Ff6p2j6fdeKv+Db63tLsF5G+Hzycc/LHGzDn8q8j+IH/AAS0+BH/AAWT/wCCRvww8R6Dp0fhnxpZ6Bavo2osnlGKSJRG8UowS0chUnPYHNfoL4K/ZV8b/suf8EYtZ/Zr+Jd1Hqmr6F4N1G2meIlk4gkIVWOMhRgdPSgD/Heurd5L2RYhuZmOAO/JFU3UoMH1r+h7/g3G/Yx079q//gpTptt4v0yK/wDD/hZZ9RvYLmMSROEzsRlIwcsRwa+/f+Dlb/ghNZfsj63P+2l+zLYCHwJrFyE1bTYEO3T7mXJEiAcLC5H0BIHegD+NipjC4ALDAIyM1IItk4jPXOPzr/QB/ZM/4IKfBr/goH/wRD8JeILSwj0b4pJbz3ekawsYV5wrnZBPgfMj4wCeRQB/n6UuM17H8c/gd48/Z4+KWt/B74nWMuna3oN1Ja3MMq4IaM4J+noe+a8lgVVlDeh9KAPo74CfsgftFftPaX4i1j4EeGLvxHD4VtPt2pi0Xc0MH97b1boTgc4FfOd7Y3dhcvZ3sbxSxkq6uCGUg4IIPoeK/wBMv/g0L/Y0vvhb+xp4l+PfjezVZviBeqLTeg3NZW6shB3Dozt+OPrn8cv+Dqv/AIJEeFv2bPHtp+218B9OSw8OeLLgw6xZwKESC+IyZY1AwqSL1H9/JGM4oA/jDs4WmuY4R3cD8zX+y/8A8ELfhXZ/C3/gll8JdDji8trzS1v3H957hi+T+BA/Cv8AHv8Agn4On8d/Fnw74StozM9/qFvAFHXLyKp4+hr/AHEf2aPh3ZfB79n3wZ8MrCPyotF0ezswvoY4hn0HX2oA/DD/AIOoPD0mvf8ABKDWZEUubPVLObj2DLn8jX+VH4Z+Gnj7xnpOo654U0i71Kz0qPzrya2heRIIgcb5GUYUZPU1/rof8HFPhmXxV/wSe+IsMZGdPhhvDk4GInAP6NX4kf8ABpH+wr4W139j74j/ABa+Kunxalp3j24/sdLa5QMjWsMf73hgRhi45HTFAH8KP7E/w7uPiv8AtXeAPh3ao0j6vrljb7QOSJJ0H9a/3EvDmiW+heG9P0W0ASK1gjiVR0ARAAPyFf50vhz/AII9eJP2C/8Ag4N+HGh+HdPlvvhzrGuLq+i3OxmWKEEyeQ5xgNE+B24xX+jBrGtWeg6Jc65qTrHbWUDzSMfuqsa7mOemAP5UAf50v/B5P+1Ta+Lv2ivBX7LGkXJI8JWDX16g+7516dy5HTIjUevet3/gz7/YRh8b/FnxD+2l4009ZbPwzD9g0h5F4F5L96VM/wByMNz6tX86v/BTj40+LP29v+Cm3jjxdppN4+r68+l6WI8vm2hkMEAXruyoGMd6/wBUH/gkN+xFp37AP7DfhD4Ft8+qtB9t1Nyu3/SrhQ7jjn5cBcHNAH6bq7IxIOOeCeK/I/8A4Lh/sR+Kv2/f+Cenir4IfDaBLjxGHgv9PUlcvJbuCyK2Tgsm4Cvt/wDbJ8S3/g/9lD4i+JtKma2ubDw/qE0UqEqyOlu7KwI5BB71+Bn/AAa2/t4+MP2uf2W/Evgf4narc6p4i8M6m0nm3MjSv5FxnaA7EnjHAzxmgD9TP+CP37Fcv7B37Bfg34FatbJb61FCbzU8Y3G6nO5gxHUqMKPTFfhT/wAHk9tpUv7EHgq+uole7TxB5cchHzBTCxIB9Div7GW56gjPr1r+N/8A4PLDj9iLwPAq5MniRQp9zC1AH8nn/BuR+x1qX7Wn/BSHwoLqy+2aF4YY6rqjN9yOODDoSemS6gD1Nf6y/wAYfhn4e+LXwk8QfCvxLClxp2t6bcWMsbqCNksZXj6V/MF/waafsMj9nz9iy5/aJ8VWPka78QpfNt5XUhxp8ZARcnsz5b8K/rCeJShB5yKAP8ML9o74Lah8K/2n/FXwVhhcXGla3c6ckYXk+VO0YAHPYcda/wBa3/ghP+xTY/sS/wDBPHwj4TvbZU13XYV1bU3IwzyXCqyK3sikADtX8t3g3/glJr37U3/Bxx451bxHpE9t4G8Ka4fEF3O6DypTlZ44icYPmMwBAA4zzX+gxZWcFnZR6fYII4YVEaKOAAo4AHoAMUAfxlf8Hok9rD+x58N4fLUyP4ldQ2MkKLdiQPT/AOtXx3/wZzfsHPea54p/bx8Z2wMNsraLojyAhvNIDXMgz2C7VBHUk+lfTn/B3Rbap8ZLv4MfsweFIJLrVdX1g3CpGGY4mX7OhwAf4m/Sv6gf+Cbn7Hnhj9hb9jbwX+zt4ZG9tKs0a6kIAMlzMA8znA7sTj2oKjfoeXf8Fjri1h/4JnfGaS9wEbwvqIG718ltv61/l+/8EOf+Ce2t/wDBQr9urw94FurYyeGdGlGp61MQdiW0R3Fd3Ay5wo9Sa/0vf+C6lp4r1T/gmT8SPDfg7S7nWb/V7I6fHDbozMBO3lsxCgkgDJ47V8n/APBtv/wTaP7Df7E9r4x8f6WbLxx42P2y/M64mhgBHkw88gbRkj1oHK/U/oK8LeGtF8G+HrHwr4et1gsNMt0toIUGFRI1AVQO2AK/GP8Abr/4JceMv2zf2+/hN8fNdvbOXwN4DKXNzYyu3mGeF/MUooBBBIXn2r9uQuxiQfYdPfP5+9SR5BwTnH07dOlBArbFhEEfChdoxxxx/hX4BfCr/gibo3hz/grZ4t/4KT+PtTtNSgvlSXR7FVYywXHlLGZJAV2gptJQgnOc1+/8g4qnsYElePpx+PHegCWIs8rDcVBGMiv88z/gsN/wT0+IX/BQP/gvj4e+DXhDT7i30u8sLGXVb7YfLhgQkzPu4H3Rgc9TX+haTlSvrWNa+EfC0fiE+LBp1uNUeLyGuxEvnmIc7N+M7c846ZoA4H4EfBXwF+zh8IdC+CPwwsksdE8P2kdpbxIoX5Y1Ay2P4m6n616iqsnTnkEVoNAzMc546cdvek8rA6Y+tAHm2lfC74caB46v/ijo+hWNr4i1VVjvNRihVbiZEG1VeQfMQBxya75duAA2D/n3q2YsjFJ5J9KADLA7gTn1pVYrnuT1pwic8Dr/AJ96VoGZQBQBgv4d0CTWI/EU1lA+oxRNCly0amVY2OSivjcFz2zWv0fA6VOsGKXyOc0ASxqcbs9a/m4/4OSPiNN8KP2Y/DviqeSKOxfXLeGbeu5txJYMp6jGOSK/pGDFRt9K/lX/AODu7S3l/wCCZ9nrUSHdZeIrRjjsGR/60AfiP4N/bJ8C+N9OutIm1YWv2RUMMURyJ2wDw55/AV8969+2nYeAvtGgXKI9vLdNcR2yqV2MTyxI5JPUe9fze/D342614algu45ysYVSV/2l6fT8K77xj8crvxjOL2/m3zsu0MvBUDoD70AfuB8WP+Cg+l6p4gjvPBu5ypiIuZFIlBHVcdCB0ya9u8G/t6PcNHqviotIsYK29pAoyTIPmkJ7t6dh6V/MAfG12LhI2uiNx2lie3+Ne++CviTqdhbjT5mMlpuG5s5c59DngUAf022P7VPhDxf5dxdGTTLoHfDNFxtX+4V+6WxxkVu6N+194g0DTb/UfEVn9s0+OQCO6smBl4/ilRuQPU1+DXh/x7qEGmKuklxApDJvzkOeoHNQ6p8WfGtrcN5oMaMpWUOxyfr0BzQB/Uf4H/aj8B+O/EKa1qOp29zI0MZWUAZSXgBFGNoYLgcjtXr3ii10jxv4VXwrb6nbx3VxJDPc3UQBlWNycq59cDIx71/G2P2iPE/hzUo7rR0NgykElG+V8H7zJ0Ne9eC/26fiRYXYe3maKSDDfaGYkSFegK5A9voaAP6rr6PSdLhadJEkj063aC3lJPzRsvVxjq/TPGK5u80fRRqY0/R1j05oLJGnuTuJkMmN0SserAcDHSvwG0//AIKk60GNxrcAme6iEFyMDARcbdoOQMcnvXfaL/wVB0fUtlv4kTfEjOYVXGVLH5SaAP1/u7LwjJe/ZbS+MIWQ7bOAHhsffk4NYOoeH9O1XUfsC6lM11b/ADNPHkHaRtESgZ6jAPHrXyl8Pv2v/hh410RRqk8Gi3chLvchv3jIFyADk5J+ldHa/tXfD7SyC+qW9tcgiKCYOob1Mj8ZJPQZPegD6j0T4XveWc1re6PPb3EiLujDDBi6s/X7uM5HrXqfh79nPS/GNpcs9klzayMoRbVgJSF4CkHAAGASBmviq/8A29/hLpNlcTrq2+JI41maOXEjuMlzwCQD6D868Suv+C03gO2EWj6VpoVLNt1qUHl5cDAdjnknv60AfsjbfsHa1r1+2oCyabTvKULbQxZj8zt5q8Z44OPevkH9qX9k3xH8BbyDV9ds/sX2xBHFJAMLGgPzKhyCvHOK8z8Kf8HD/i3w5arZafp8bXExx5uQdoA5xkMK474o/wDBR7x7+1zozeJfiEptNBsDlFx817KBhY0yOB2JAoA+jdM+MXiD+w9D8B+Fybee9eCCK0Mh+ySeV83myDOd5ITnngkd6/oIv/jzP8B/ghD4U8POL3UYLLZLAEz5tzMAzP2+Vc8c1/KP+yck/j34rN8RvG2Vi0lg0dsp2oJtwKIuegXA3Y7V+v8Aq/xDvfFunumt3j/Y/NDt5YIkeU8BUb+4O4oA/fb9gubxNe/AiC98UXDSy3MpkSIn/UqQMKMdM9cdule6fGj4F+DvjR4cbS9ft1W6RMQXIGHRj056keor83P2XP2xPhb8Lfh/ofgG5OURyLq5Jydz8k4J/hPWv1m8L+NvDnjHSo9Z8MXsN3bSkYeNgRz2IzwaAP5nv2ifgBq3wt1y78PeIrQbwGaKQfdkBJKlfU88+nSvyI+KnwakgtpRbJ5khB3FhnIz0/Cv7UP2uPhFp3xR+GN7epGn9qaTC9xBIQAcKuSvPY4Nfy6a3L4d8QW0t3bzAKVKHf2b29QKAPwr8dfDW/8ADNy95pIbzXBE64wMH0zmvkTxYqG5kEVoYVX75H8WOOfp1r9sviL4QtYnknlxcQR5JZuN3tX54fFrwRZ/ZprzToY4vtB5Td9wcjmgD8Ev2rvCEkmpw+NLJQYZ/wBy5HZl6FvQnmvjMqqqNpyDX7p/FD4beGta8P3mgapNFHBcJjdxhHGMMPxr8VvGfhuXwp4gm0OZg7RORuHQjPBFAHMKhBzmpKeFBUmmUAFFFFABRRRQAUo6ikpR1FAEzDKlfUV718MpUm8NtFncYpP0YV4KRxnpivXvhHeIBfac3DHDr744oA9c8oMTnjFRPBnp+dXTjJxScd/woAqCJd1IYlBxirgz+NIRn7/FAFTylo8tcYq15a7ST1HNDxhVyKAKBhNM8v8Az/k1pBVFQyBg3FAFIx8f5/xqjdKot2+lbDMQcVkX3+rP41nW+Bjg7Tif2Rf8EYR/xixYr03F/wBWr3T4Sc/8FQNNX+7p0/6Ia8M/4Iw/8mtaf/vN/wChV7z8IF3f8FO7Rj0XTZz/AOOmv8mPFPTNMZ8z/Rzg/XLaV+yP1g8VkHwX4jX/AKdbw/krV+ImvjH7I3wkP/UzS/8Aoyv248U5/wCEL8Qe9pef+gNX4k+If+TRfhJ/2M0v/oyvyLh6ztbuvyZ9PX3R+2l03+h23tAP/QQa6TSjnTLY+sSf+giuUunP2SD2t1/9BFdLpMjf2Vbf9ck/9BHtX9U+B7fssRf+5+TPwHxNk41qbXn+h//W+uvDXMc4/wCmb/yr5HlY/wDDC3xK9vEcf8lr6t8Ky5SQesTfyr5Pugf+GF/iXt/6GSP+S1/jEv8Af2f6kUf4R9ma8Qf2LdRZv+hcH/ola+TP2GU3fBjQz/sMP519Y6+pP7Geor/1Lw/9ECvln9hhdvwZ0P8A3G/ma5cqf7ua/v8A/trKqPY/nt/4LcsU+Jmkk9dxr8SWb5iR3r9s/wDgt+cfE7Sh7sf1r8Q0bLEmv9WPBlJcO0PT9T+C/Fv/AJG8yZvmG1uRVV0UNgcc1IXOf8/4VE91AoPm8Gv08/KSVS2cL+dOJZeprJm1G3QfIayH1u4ZisYzigDfuZnaMqxzXD3C7JmWrUuo3hrPaQudz9T1oAgPU0qjJxSHqaVRk4FAH3B/wTd+CGqftD/tt/Dn4V6Su6TUNatS/Gf3ccis5x7KCa/2gfi74tsf2ev2Y9e8b222GHwnoNxdIWwAotbcsOD2BXpX+Yh/wamfAG8+K3/BUHSPiC0JksfB1lcX0xxwrSIYkz2+84r+8f8A4OCPjmPgH/wSv+JfiNGZZNVsv7IQpwf9NAhP6E0Ach/wQe/bZ+On7dn7O3iX4r/Gq9j1GSPWTDp8ixxxgQ7QdoEaqMDrk817l/wU7/4JC/s3/wDBTfRNB/4WXANM13w7dpcQapbxr5zRBgZIJGGCysBwDnHavg3/AINU/Cb6P/wSs0fXZVKvqmr3coz3RGVFJ/AV/SmAAPloA4L4deBPDnwq8C6P8OfBtollpeh2kVlbQxqAFjiUIOB7Dknk9TmvLf2tbTULz9mD4gWekwtc3UugX6RRgFmZ2gcAAckk5xxya+ifKIOcYP8An3o8ot8pGQaAP5K/+DWD/gntr/7Ovwb8X/tGfEzT5rHXPGF61vbR3CPG62sLEs21wCN7dOOgHrX7xf8ABUHwNoHxK/4J5fF3wl4iRXtp/DV83zDcA8Ue9Dj1BUYPavvCG0htoRDCgjRRhVUYA+gFfHn/AAUQgV/2Dvi3EH8rPhbUfm/u4hY5oA/xZfgr8JtU+LHx90D4R+H4Tc3Wq6tDYxqoJLb5Qnb25r/bp/ZX+BXhj9m39nnwj8C/CCrFZeG9MtrNcdSyRqXOT1LNlifU1/mu/wDBrH+xle/tAf8ABRyb4y65ZefoHw9WXUGldcobliVhXPqTlh/u1/qL+WFcAHoPxoA/zGP+DwD9na2+Gn7duj/F7SLQQ23i/SUkkdVADzwHY5J7kjBr+bf9jX9m7xl+1j+0l4R+A/gi3ee98RahBbDYu7YrsCzt/sqoJJ6cV/oH/wDB4/8AAO08afsieDPjvCALnwrqj2rtjlor1QV9+Gjr4D/4M9f2Cv7d8a+IP24PHFh/oujRnT9EkkHBnk/1jjj+FeP+BYoA/uw/Z1+C/hj9nH4H+GPgf4OhWHTvDmnwWKKoxuMSAM592bLfjX5Pf8HFXwV1n40/8EsPiBaeHrNr260aBdQjjRNzYjb52AHPCknj0r9yW8oSsuDkf/q/pWJ4o8O6N4v8Mah4W123jurPUIHt5oZRlXjkUqwPXjBoA/x3f+CEvwKX47/8FQvhr4AvYy0UWpi5l4JAW0Vpm3fXy8V/sX6jqml+HtMbUdauI7O2t490kszKkaKmBks2FUe5Nfw4f8Eaf+CaOv8A7M//AAXV+KEl1otxa+H/AAit/c6PcyRny3hufkiIY4B+VyM1+tf/AAdF/GXVvhL/AMEutaj0C+ewvtb1Wxs0eMlWkQyAyKMHPbpQB+pP/BRX9lrV/wBuP9jLxX+z14Q1GCzl8S2cccN07boCu9GyWTPyso6jNWv+CdP7G2k/sHfsleFv2bNKnW7fRoWa6nUHbJcSHdIVyPu5OBnqBWp/wTm8Vf8ACZfsI/CbXmZnlk8K6WHZ+pcW0YY5785zX2ihGR60AZeoeH/Dmo39vrOoWUE95ZsWt53jVpIiwwSjEZXI9K/Oz/gr5+0bo/7LP/BOj4n/ABW1mXy8aRLYQAHBM99i2jx9GfP0Ffpa0WUyK/An/g4D/ZL/AGof23f2ePCX7Nv7P+ni80nW9cifxBLuUGC3hGY3IP8ADuYljzjA4oA/lW/4NTP+CZFl+0b8d9U/bM+MukvdeH/B86nSjcofJuL8ncCNwwwi6nqN1f6S8wiQ7YVChRwB7Cvlf9ij9ljwN+xf+zN4W/Z48Awx29vodmkc7xqB59wVHmzNgclm5r6Vi1bRbjVptHt72GS9gQPJbK6mREP3WKg5AJ7mgD87v+CvOu+L9D/4J1fE0+ArSW91S+0x7KOKFGkf/SCImO1QScBj0Br8+f8Ag2y/4J36/wDsMfsVf8JL8SbE2XizxzL9vuI3BV47bnyVYHGCQdxHBGea/oilSKZDDOgdT1VhkfkRVTUdUstI0yfUr6RYLa2jeWSRvuIsalmZvQBQc0AbRfcgb0Ffzuf8F0P+Cdfx7/4KVaz8LPhJ4Ahii8I6bqn27Wb6WSMC3ZSFUlGIYrtz0B57V+vf7K37ZPwG/bL8P634j+AupPqdjoGoPp13IybAZUXJ2HJ3L05r6kRecZ6+nvQB538H/hh4Y+DPwv0H4UeC4Rb6X4fsoLO3ToAkKqo4z1OMn3r0r90/ysAQfWvjf9v39ozxL+yf+yd4v+OngzSm1vWNHt1NnaqpfdLIdillGSVXOTXKf8E1fjZ8bP2j/wBj7wr8afj7p8emeI9bWeaWCKJoh5QlZY22NkjK44oA+4YfDuiW17canZWsUFxdkNPLEgR5CBgF2XBbA4GTxWoI9gyvOOfp/nNU73UbPTLKXUNRnS3t4ELySSEKiqOpJOAAKz9C8UaF4n0hNa8NXsOoWcpISa3dZI2wecMpINAHifxD/ZS+Afxa+Knhz4zfETw1a6p4k8KNv0q7myWtyDuBAztODyMg19EHbs+TofSoVnBXJOKkJZjzQFyK5treaMpMiyKRghhkMB656/jTIzghQoAxjj0HSrAySAa/Lr/gpZ/wVE+En/BN3w34am8X2Umt6/4rvFs9O0q2lCyydnkOQfkUnHuaBtn6ivFtOCKRYyvJrA8Fa+3izwjpviiaE276jaxXBiY5KGRQ20n1HSujLgHFAiORlx0r5/8A2kf2lvg5+yh8KL74z/GzVU0nQ9O2pLKQWZnc4VUUDLMfQV7+4QqWfgCv89D/AIOqf+ChU3xr/aQ8Kf8ABPP4T3rTaf4du4ZtbET5V7+Qr5UZI/55huR6n2oA/vg+D3xP8IfG/wCGuj/FnwLM0+j67bJd2rsCpMcnTIr0ecKkJPRV5J9h1714F+yx4Hsvhj+zp4H+H9jF5EWmaNZQbF6BkhXd/wCPGvyP/wCDhX/gp5F/wTs/YtvIPBdwB468cK+maOqnDQCRSJZ+OcIp+X3oA8M+GP8AwV0+J/7T/wDwXGk/Yr+Bc6XHwz8GWV4mt3MaKyzXcCYZhKQSFSRlAwwBwa/pmR23cHr15B5r+Dj/AIM0fhhH4m1H4wftC+Kp1v8AWbtrW1SaQ5lxIxkmdj1+cgdeuK/uL+JnxM8H/CDwBrXxQ8fXcdlpGg2sl3dTOcKscS5P6Yx70Abt94y8Ladrlv4Xv9StodTvOYLV5Y1mkHqiMwZsd8Cuk3t61/DR/wAEf/2mvEv/AAVn/wCC1njX9qvxReyx+FvBFlN/wjumGX5Igp+zxZXnOULOT3JFf2S/tF/HHw1+zv8AA7xZ8cfFs0cNh4a02a9LOcIzRoWVM/7TYA4oA90V23Ur8civxQ/4Ib/t/wDxm/4KRfst6v8AHz4wafBpzLr11Z2K26lVNvGFYZyecFsZ9q/aMsCTGrZI5wDyPrQB8Hf8FLP24fDX/BPf9kTxT+0frixz3OmQhLC1kbb9oupCFjQevJycdhVf/gl9+21a/wDBQL9jfw1+0ksMVvd6mHiuooc+Wk8Rw23POD1FfxM/8HgX/BQG/wDHfxm0D9hTwdcg6V4YRdS1ja3LXsgPlow/2I8H8a9Z/wCDXr/gsf8As1/s0fs3+Kf2Yv2nPElv4Yg0N31fTLi8cqs6ycywocEbuMgDrnFAH+gcetfzn/8AB0n4XfxZ/wAEo/E0ccRlay1CzuCR2CsQW49Aa/VT9h7/AIKAfs7f8FBvh5qHxM/Z1vpb3T9NuzZTmdPLbeBlSBk/Ky8g4r5N/wCC9fh4eJP+CV/xVi2+Z9k0iS66d48N/WgD/HAiuprQkx8knj6VfOu3IT516+5rH3bZDu9TUgcHp/KgDaGrmZB5i4xUlj4r1qwuY57CVh5Zzg9D+dYWc0wttOKAPf7D9ofxrbxLEAjFDxu4Gf5V7PaftgrqGnG08W6Ws7YVWaMjDbeh5Ga+Gww65qEsT1NAH2Vr3x48G+KxHaw2zWrKflLDAHtxxWy/iDw/caQJ4rlHkXlgrAfpXw3kr92pI55Yz8px9KAPs228Uac21bqZQByQD1z61h+K9X021Ky21wM8HcvUgdBXymLu7DcSH15NSPqN8V8tpNwoA98i+IOvW8kdzFdSKqHKc9Pr6V0U/wAZvEt5P5l3eGaWXC5Ujv646V85WeqzKPKk5B619D/Bj4aeIfjZ4lh8GfDqwe/1S4yTDGCSyqCWPHoATQB7N8OvAvjP4subW1vjDdjHkQSPw4OdzHtj0r2WH9mDxJKEttTtHVkO2WSHnbt6NgV55oHg+88Ha9JoejeLbO18Q2sxt5rWdmgeJk6qS4x8vTrX2h4Q1P8AaB0uCP8A4R+TTtckH31juo5HkPoeQfyoA5b4LfBPw/qUs+l/Ee4GneH9OY3DXki7JJCg+4vQkt0r6T8KaprXxd8YWeneFVNn4c0hsWwf5YokU4D49T1J7145F8Gf2nfip46hm8eaXNp+kwP5ht0T93j1IB5+tfb9l8L/ABL4bSKTwnEht4VEc9tIpTcv8WdvO3PTvQB9aeAfHXhXw1Np2iaRLHDp9lIq3E/Tz5cZb0zxX0Npvxlt9YkbSNAmjM4EnlKWx5achyTnG5R/OvFP2Pf2TNa/a/8AiN/wqrw1dfZo2ie7kM3yxQMnEjDPzHA7d+lewfHr/gnx4r/Zy8Oxa54P1SHXfDVzdG2l1i1J8lrnJWSFieVIx1waAPF/jH8ZLrQtUlTTp5ppgiqJIf8AVM4UeYFUd84Ge9cX4D/4KJftMfCm3ls9A1aS1tA3nyxsdpVVwMeu76U23+HM9nePb21xFqM1mu6W4I/cx57IW5Yjucdayrz4PWH2VZrlGlS4JfzOm85469BmgD1LXf8Agtx+2Frfg+68FTX9wbPVHa3VmcCRIzlT8wG7BHPXjNec/DD9qaUS3dl4gtw7RQ+VEGORvHJcn396811D4JW9zq5+y2ysUjaWaUnEcXy549/618w/EHUNJ+HWkyJFMzyMhkdz0CDpQB6D+0x+2/D4A0N9EmZWnum8xV4yBnscZr8fvHH7YHifXLsyrISpB+UHj/8AXXzx8ZfidqfxV8bT31w25ImMcPptFcjF4PuvLEpXJxuIoA1fFfxm8U+JRLBcyNFFIc/ePNfPniO6lvbtJ3Ys2MEscn8zXa+JoksE8nILA5x6V5lcuzyljQA0ScYpnmj/ACf/AK1MpMCgCwpyM0tMVwB/n/CneYv+f/1UAB6VFvapCwINQ0AO3tSh2yKZTlBzQBcHzLg967L4d3Bt/GVsmQFmyjZ77hx+uK44Y21e0S5Wz1u1u2GRHKpP0zzzQB9e3kXlTbMg8Z496r7C2DW34n0G70DVIoDl4b+JJrZ/7yt/gRislVZRtbqKAIgBnOaa5LNntU+FpmOtAEfX+VB+YYNP5BGRSNgNtHegCLJ34p5GeT2pfKIPSggjrQBAYs9az763UQOwOcKTWsEK+9Ur6M/Z5G/2TWOI+Bl299ep/Yp/wRfi/wCMXrFew3/o5r6B+EEQT/gpsh7DSpf/AEE14J/wRg/5NesMf9NP/QzX0P8ACpf+NmYwP+YVJ/Kv8kfFWVs0xn/b35n+jfBv/IupeiP1E8TEHwbr47fY7r/0Bq/EbXST+yF8JCf+hml/9GV+3Xinjwf4hH/TtdfltavxD17j9kT4Q5/6Geb/ANDr8k4Wlf71+TPqK+yP2qvmYW1sB3gX/wBBFdTpP/IKtv8Arkn/AKCK5DUD/o8GP+fdf/Qa6rSA50q1Iz/qk/8AQRX9Y+B/8LEf9ufkz+fPE93q0v8At79D/9f6n8IfeI/6ZH/0GvluU4/YW+Jo/wCpliH47Y6+pfB/+sP/AFzI/Q18sXJC/sMfE328Tx/+gx1/jD/zHM/1Jo/wT7J11if2M9TX/qXD/wCiVr5X/YaBHwT0Mn/nk38zX1TrmF/Y31Pd28OsP/IIr5X/AGHgR8FtET/pi38z/hUZQ70p/wCP/wBtZFTZn883/Bbz5fibpIPq/wDM1+ISkEke9ft7/wAFwGB+J+kf8CP/AI8a/D9OCWr/AFT8H/8AknqHofwf4tf8jif9dCTeKrSRWZU70ZuakPJzUckvlfeGa/T9z8pM64+wImI4ju7VgzXDFjujCVtTlVBkz8x6YrHnmll4mB3CkBnSOw4NQU5iSeabQAU+MZcAc5plT2sMlxcxwRAlnYAAcnJ9KAP9GP8A4MzP2df+Eb+BXj/9pC9gBk8Q3iabBIw5EdqN7Y9ixA/Cun/4PIv2lbvwb+zb4G/Zw0GQH/hMtSkubtSeQljtI/Bmk/Sv3N/4IO/s5D9mH/gmF8MvB13bGy1DU9Nj1e8jcYbzrwead34EV/DX/wAHYP7RcHxo/wCClWnfB/w9Ms9j4LsLe3JU5H2qc75R9RwKAP7af+DebwjJ4I/4JO/DHTLiMJJcW0tyQP8AprMzD8hgV+1wkX7oWvz8/wCCX3gS9+Gn7APwo8L6jF5EyeHbGR4zwVaSJXYHOOctX3Jq/iPQPDlqt/4ivYbCF3ESvcSLGrSN91QWIBJ7CgDoyC33v8/rSKpByaj80tH5i8qehHIIOOeO3NMSQnkAHHbrQBYV0kYqDkj2r4a/4KZ+HfHfi/8AYG+LPg/4Y2Mup67qfhy9trS1t1LyyySoU2oo5J56CsX4zf8ABRn9m34D/tT+Ev2P/GNxdyeMvGvk/Y0t4g0SCdiqGVywKgkE8K3FfdzxyKQytgY9+Afr1oA/B3/g3l/4J96x+wZ+wzbxfErTDpvjXxhctqOrRSptljXGyGJu4wo3EerV+g/7U/8AwUI/Z2/Y58beEvAHxg1GZNV8ZXCwWNvAnmONzqgdhn5V3MBxn6en2sXLgzTnAUFj+H4Cv83X/goN+2LZftif8HFfhLwjodwLjw74G1yx0GDY++KV7a5VpnXtzISPwoA/sR/4LefsN/Ef/goX+xDe/Av4TeS2pXV/Y3SrcSCNSkT5Y7jxnaelfWX/AAT4/ZE8K/sMfsjeDP2cfC0MUL6NZIb54+RLeSfPcyDPq5OPYD0r7XskIs4WGOUXP4DArxz4+/GPwb+zt8HvEnxv8f3AtdJ8M6fc6jcSNgHZbxliFBIBJxgDIyeKAPy8+OX/AAWI+F3wi/4Ka+Bv+CcWmaXHqeq+JlX7beCYg2ckoZo02gHJIHOema/aKWMIudvFf49Xwu/br8Q/Hf8A4LZ+Hv2zPFtyY21HxdFcxMTgRWpfZGmc9EjIHvX+wFo1/Hqnh201OJg6XEayKR3DjP49aAJILKwhvXuYoUE0ihWkCjcR6E4BI9iTX8Mf/B558ePsXhH4T/s8abMVN9fXWrXkYP8AyziEUcWfqzN0/u/Sv7pIvmmaQdAOa/y4P+DuT41R/EP/AIKaWvguxmWS28JaDaWy7TkLJKzSyAgdG+7QB/fj/wAEftQm1H/gm98Jrmc9PD9qvPHCjAr9MESQNwp/L1z/AIV+Qv8AwQR8TzeNf+CV3wv1S7/1q2LwHHpFIyrjPtXk37a//BVzxJ+zp/wUy+DX7EHhe2t57Tx1h9SeQbpF8yUxqEORjgZHFAH7uiXHB6jtVeWQluKbLmNymcngk+5FRglnH15Pp/n+lAHgH7VP7R/gb9kb9nzxR+0L8SJ1h0zwzYzXjqSAZGRPkjUn+JmAA96/lq/4Nrv2lfir+3X+078dP2xviZezSjWZ0tLS03uYoIWkaSOIKeAqIoAwAcgZ6mvh7/g7z/4KY2GqanpP/BPj4Xan5kdmV1DxL5D5UueYIGweSvLFTjtX0t/wZfaZAP2bviXqOQZH1y3U4xkbYWPr0zmgD+2B/lbLcCvwk/4OIf2+oP2Ff+Cd/iSfw9cQp4p8bRtoelwyH5yt0pSeVRwf3cbE596/d2SVI1adztRASxJwAByc+1f5Qv8Awctf8FArr9uH9vq7+HHgW7kuPCPgGRtJsYznbJdq5juJQAD95hgew7UAf2qf8Gunwz/4Qb/glh4e8TzoRfeJ9QvL+aRjkuN+xM55+6vev6MWcRw+YFxt4/pX5If8EL/BFt8Pv+CXXwq0a2ZnEmmee+4YIeVixB57Zr9SPHA8S/8ACGaongwI+rm1mFmJDhPP2N5e49huI5oApjXfBPi+7vfCiXNpqNzaAC8sw0czRgnpJH82Oem4VtWlrbWKpa2MSW0MShUjiUKoHsFA/LGK/jm/4Jqf8Enf+Cuvwv8A+Ci1/wDtafH3xjDo+hXmoSzanALs3DahFIxJiEaHbt6bS2MV/ZU0RMu8fdoA/OX/AIKu/CL9pX49fsQeK/hN+ylLHD4q1vyoW3yiFmti/wC/SOQ8KWXg5IyuRkZq/wD8Ep/2bviZ+yd+wx4P+CvxlKt4j09JpLzbIJQHmcvjeODjOOPSv0QSOX7yAn6YB/Wmqku8mXnd3zn/ADigDg/iP8Q/Cfwk8A6z8TvG10ljpGh2kl5dzuQAscQyTz3xwPcivmn9g/8Abe+H37fnwRf48fC+zns9Ka/uLKPz/vSeQwG8Y4wRX4hf8HY/7SvxK+BP/BPGHwP8P0ZLXx1qS6VqdwpIaO3VfNKg9t5XB9q+/wD/AIIG6Z4B0r/glP8ACmT4dsrxXumm4umGATcu/wC/Y++7A5oA/XnWtf0zw7o914h12dLaxsonmnmcgIkaAlmY9gACc1/mafGP9sfVP+Cxn/BfX4f6HpUTTeDNB8QQ6ZpkLA7fskEu+eYjpmRl3euABX9I/wDwdM/8FEZv2Tv2MV/Z/wDA2pC18WfEQNassRxImngFZicHIDZ2jjkCv4ff+Dff4u+Hfhd/wVP+G2s+LlDwanf/AGIyOcBHuVZA/PfcRQB/sK2drb6ZYwWFshCxIsaqAeAowOKwdN8Z+DtX8QX/AIU0nVLW61TSwjXdpFKrTQB/u+ZGCWXPuK5L40fFjwt8D/hH4h+MXi6QJpPh7T5b6ZmI5SFNxAPTk4HPev8ANJ/4JV/8FuNU8K/8FlvEHx6+MGpSWfgv4r6pcW14szlktYpn/wBFOBgBYvlB9PegD+/P/gqf+3Fo3/BP39i7xb+0LeiN7+0gNtpkT9JLycFYhj0VsE+1f482mftKeLdY/aztP2n/AB0RrGry6+msXYucusreeJWVsn7o6AV/ZN/weE/t1+C/HekfDv8AZe+FXiC11WPM2r6tHaSLKoDBVttxQkcgk4+lfwbDcG3ZwwORQB/ua/sq/Hjwt8ev2XvCf7QOi4t9N1bSYrxl6iP5AZFHshB/IZ6V/lVf8HCP/BRTV/2/P299dvNMuM+EvBbvo+jIhOySOJsvMV6bnfPPpX2h+w1/wcx+OP2R/wDgnpq37Hmq+EzrWrQWs9loepicIkEdwpVhNGwy23JKkHqea/li1rVJ9b1S51a5OZbuV5nPqzsWP060Af1Vf8Gm37dS/s6/tu3H7Pviq6S38PfEi3+zZkb7t7B88BGeBuOVP1Ga/e3/AIO3f+Cg+qfBX9nrQf2Qfh1qATUPHYefU3R/3qWcLABCByPMf16gV/m6+FPE2v8Ag3XLXxJ4YvJbDULGVZ7e4gco8ciHKspByCO1d/8AGH46/Fz9oLxafHHxn8Q33iTVdixfab+VpZNqDAUFicDgUAftJ/wblft46X+xF/wUE0W/8WzCHw94uT+xb92bAjW4IVJPTKPg5+tf1pf8Hcv7WmreBv2KvB/wL+F+rxY+Jeqql2LdvnmsoY/MUoVOdjMwyRweK/zOre6ltJI7i1do5oWDI6nkEYwQe2MV9hfBnxL8e/2rv2jPh18OfEWsal4svP7Ts7HT7e9nknEMbSrlEDltq4HIA6UAf64H/BG/9n/QP2cv+Ccfw08C6Jbi2e40aDUL4DgyXVynmysx+pC/QV/EJ+2x/wAF3v2rP2Kv+CufxM174Yau2u+HrOafS20e6ldrPIAXcqA4VkZcgjrzmv8AQ6upYvgb+yzcXt4Ft18M+H3kODhU+zW+R+GRX+JF+038SLv4t/tBeMfiVdP5kmtavd3Zb18yVm/rQBc/am/aO+In7W3x88S/tD/Fa4W517xRdm6uWUYUfKqqoHoqgD8K8AXcG44z70h5INLgudqHBAoA/q7/AODW7/gplr37K/7UkX7LfiKMXvhn4jXUMAUthre7HyxypnjHYiv7+f8Agr9po1P/AIJjfGmB1D7vCt+6jHcRlv51/jw/sm/FLVvgT+0D4N+Mem58zQtVt7hTnHMbq+P0Nf7CP7cnjqz+J/8AwSd+IXxDhiM0Gu+ALu9VVGeJ7MuCAOvUdD1oA/xWrhFLMynoTx+JpsLfLtqxqAYXsy/dwxGPxqvGQi4NAE1Qv96n+Yv+f/1VGxyc0AJRRRQAUUUUAFFFFACjrX7h/wDBC7RtVH7SeoeMtJiWaXTLPJ3LuCiQ4PHrivw8HUV/Qv8A8EZ7yH4a/CP4ofF5lKz2+nTCNxxjyoyw/XFAH5q/8FG9V8K6n+2H4y1LwVIJLeW6zNwOLjH70LkdjXxhpur6/pkq3Gj3M1s6HKvFIyMD9VxWn4k1m58X+KdR8S6g5klvrmWd2PdpGLHP51BHE20CLjFAHvXhT9rr9qfwknleH/GOqBQMYkmMgAHYbq/QX4Ef8Ftf2tfhHrOnT+M9N0fxhp9lhWg1GxjZ5ExghpFAJ/Gvy50FY2YCTr9K9AiFqpEdxGsiHngYNAH9sv7FX/B0R/wTn8FSSSeP/g7/AMK9vpwBLd6LEs+8nhuwZVPUjNfslon/AAUP/wCCK37ePhSPwVb/ABItfD9pN++/s26nGmoZ5CTvKvhfMJ6nOK/zDh4B8F6380L/AGeQ8Enoap3P7P2tvcRDw7c+dIQOgKlfcn+VAH+n1N/wSc+DvxHtzqX7OHxGtNV05B8kKyR3KgsMq4ljJzjtnNfk3+3B+zF8UP2D/GOi6B8TtXfxDYeJl26bqQjVIYbmMgm32j7hwQ2Twf0r+Lv4eN+3p4AuRB8H9X8SwGPhv7JurgINv97y2wMfSuy+NP7a3/BRfxTpmn+E/jv4j16+g0JxPbxaosjtEwGA+5wcnGOvtQB/Rvrfi7VIdOnstQ+eGMlpIIwCjkdDlec9zz+FfiP+2h8c4LzU5vA2gETXV24Nw0XPlJj7nHTJ6jtWH+ytdf8ABSP9q3Q/FWufAKE+LE8KWy3Wo2SiP7S0LEjMUQ+aTGMnHSvlLXvj9qfh7xFd2nxE8Ki21pZSt2kymOQMOoKyKCpz2wKAI/h18LrpmOpah0clgSOM1ueP9Vt/CFo0TsGlkGwDA4yM/wBKxZv2r9Jewe0tdIMJIwuCOP1r5U8TeL9U8T6nJe3krMrHKqe1AGVqmoXV3fvPM2dxNZbZzyc0M5Y803AHSgAooooAKKKKACiiigAqVOlRVKnSgCwmCNtJODGgYHHPT6VEcgfKcUqygn5iTgHAHqaAP0vhubXxx+zroviuL/j80c/ZnPUkda8cKsM5PT1rov2TNZbxL4Q8SfC64HySRNcwZ67wDnH5CsFkdi3mnDKSOfr0PvQBH0YGnsMjj2ph5YA8GpPpyB3oAaQcsR3NGcHIHNBYA7epoG0nJ4NAErRMcNnrRsVGHr3zVgE7dr/pURBTGCDmgCJgnk/Ic1n6if8AR5P92tV1VQFH1rM1ArJaybRjCmsa+sHYun8SP7E/+CLv/JsFh/21/wDRrV9G/Cv5f+CmA3d9Mk/lXzn/AMEXgR+y9p59fM/WVq+jPhe27/gpeox00t//AEE1/kb4ryX9p4z/ALe/9KP9G+C3fL6S8kfp94pOPCXiA/8ATpd/+gtX4geIiP8AhkD4Q/8AY0Tf+jK/b/xWh/4Q/wAQN/06Xf8A6C1fh/4jGP2QPhD/ANjTMPzkr8p4S6eq/Jn0eO6H7T37DybXn/l0T+VdvoUkf9iWfP8Aywj/APQRXA3xBitV7/ZY/wCVdpoKE6HZH1gj/wDQRX9ZeBP8Cv8A9ufkz8A8Tv4lL5/of//Q+ovCBPmEeqf0NfLV02f2F/iaf+pnj/8AQI6+ofCRb7QwHQRMfyFfLN0xX9hf4ne3iiL/ANBjr/GeEH9f+R/qTR/gs+3deTH7G2qH/qXT+sAr5G/Yec/8KW0Zwf8Ali4/U/419na1b7v2L9VkYdPDn/tAV8W/sPAf8KP0Zv8Apm/8648olahL/H+jIqRbg35H893/AAW2y/xI0dv98f8Ajxr8RwmSwNftz/wWvKr8Q9JJ/wBs/r/9evxKYgMcV/qr4Nvm4eoNdj+DvFu/9sS0/qxGOgqvNEX5FWwhxThuXtX6hzc77H5UYVxG8aExrzXMzT3TjE/+Fd+ecjHWuf1O0XO4CkByvlkjcTTfL/z/AJNTBxyGHGaYzpnjpQAzZ/n/ACa+8v8Agmd+zXe/tW/tzfDb4JWeHj1bWrYXGRkeRHIGkzg9CqmvhMbMZNf1+f8ABoB+zPdfET9t7VPjnqNpvsvB+nu8NwVyqXE58tRk99uTQB/pP3UujfDL4cvdQxrDYaHp5bYowqxwR/wj0AXj0r/FL/b++PF58af27PiB8aWlN2l94guLmAsTgxpJ8g4wcYA71/rLf8Fqv2kk/ZR/4JqfEr4mrceVdSaa2nWwBwzSXgEI2+4DE1/jGX99NqN/Pf3DFnmkZ2J9WOTQB/qTf8G9/wDwW51f/gohLP8As8/EPR9O0K/8KaJB9jW1aTzbhbZFjdvmJ7c4FeL/APB3X+0V4k+D3wB+FXhnwtqMunXM/ipL+UQOyO8dtHnkgglc9ulfxR/8EUP26LT/AIJ+/t6+EvjZri50Z5jYal823Ftdfu3b32Z3YPpX7F/8HbP7X/wo/aW/aD+Gej/BbxLb+IdO03QDczLZyrLFHLdSFkyykjftOCOooA/0Of2LvjloX7SX7JvgD43eGpxcWevaJaXAZGyd/lqJEb/aVgVI9Qa958X+NPDfw68G6p4+8V3C2mmaPbyXV1M/CpFEpZzn2Ar+bz/g1Y+H/wC1D4K/4J22l78dbmb/AIR3U5vP8N2k334rRgSzKCMqrnnHqTXrH/BzT+1jd/sy/wDBMnxJpXh+9W11zxnNHo9qA21mjcg3BHt5eQfrQB/M78Ef2+dF/wCCkX/Byn4a+LOjwmHw3p1wunaLGxzujso3EUpHQGR/mHXg96/0esMV+fv06entiv8AFT/4JH/HTRv2f/8Agoh8Lvip4lulsdPsNdtvtUzEhVjeTDE47Yr/AGmtN1fTdY0eDXtLmWeyuIllimU/K0bAMpB9CvegD8xf+Cxf7bWj/sE/sF+M/jBLdCLV7i0k0/R03AO95cKUUrnrtB3Ee3vX+Vt/wS28S6t4s/4KU/D/AMT61M013e+Ibe5lkkOSztOpyT65OT61+x3/AAdUf8FOp/2qP2qz+yd8Prrd4P8AhvJ5czRvujutRcDzJMjr5YJT8DX4F/8ABObxnpPgL9tf4ceJNalEFrDrln5j5wFUzLk59KAP9vSKQpbQAfxKMfkP8a/kK/4O7/23/wDhS/7IWl/sueGrh49Y+IV0XuGjYArZ2uN4YDnDvge4Br+urS7u2vNBtdTtZA8ZgV0cEEFSoIIPTkd6/wAkv/g5e/a6t/2qP+Cm3ieDw5em50PwbGmiWiBt0ay2423JXHHM28e+M0Afg14P1c6J4r03W0kMb2tzHLvU4xtYEmv9tb/gnj8aNC/aA/Yk+HPxT0G9W9t9S0W1xIpyxeKMRyBh6q6sCK/w/g4Q7wBgfzr+zr/g24/4LzeEv2StOH7HH7Vt69v4PvrnzNJ1JsuLGWTAdWA58pySTjoSTQB/pHTOlnbS3Ux4jXt69/rX+MF/wWe+Klz8Wf8Agp78X/F9yTLHD4huLWPB/gt22KB/3zX+vh+0H8bvCvg/9lnxP8eNCv4L3S7fQ7q/trmKQNFIvkM6FWHUH1Br/EO+Lvj7Vfih8TvEPxD1wlrrWb+4u5CTnLSyM56/WgD/AFwP+DdH4u+GPip/wSl+Hl14fWOOTSIJbC6hTH7ueGRslgP73DZPY1/Fb/wWu/bguNE/4L223xV8PTM9v8Pb2wtYMnAHkkM+PTkmsT/g20/4LG+Av+CefxK134P/ALRuqPpvgDxPGZPtTiSRbS6UfI2xc/K2ApI9c9q/HL/gqZ+0P4D/AGnP29PiH8b/AIVSeZoOramz2Um0rvRAAHAPI3EZFAH+zz8G/iLofxg+E3hv4o+G51uLLX9Ntr6GRCCGSeMMvTjp1968W/bp/af8J/sZfso+Mv2jPF86W8Ph6wlkg8wgB7llIhQcHJZ8D6Zr+PT/AINxf+C/PwW8D/BGx/Yz/a/1+PQDoX7rQ9Sut3lNEzcQSPghcZ+UngCtX/g8H/bh0PWPgN8M/gH8JfEFvqWmeJ55dVv/ALFMsiSwRqBbk7TyMljzQB/B9+0L8bPGH7Qvxq8TfGbx5cPc6p4j1Ca9ndmz80rlgBnoBkADsBX99H/BmT4u+FkPwY+IHgy21ot4qlvEuJNOYgf6Ko4kQdTy2Sewr/OoMhz0r72/4Jyftv8AxD/YG/ao8NfHnwLdTIlhdRi+t1YqtxbFgJI3APzAqTx60Af7R/xh+LPwp+CHgO88d/GjW7PQtBhG2e5vJBHHhv4ST6jsK/l01+y/4NVtK+Jd34w1++8K3+ua3dG5ldrm6nXzpGyWVVbC5Y5r8af+Dk7/AILW/AH9tj9nf4c/CD9l3xHLqD3LtquuJCHjWDMYVYJScZYOTxz0r+KdL27abz2kffnJbPNAH+718E7T4W6f8JdBtfgitunhIWcZ0oWpJhNuQCmwnJxj1r8o/wDgpJ/wXe/Y5/4Jp+P7D4WfEw3Wt+IrpVkntNPKFrWN/u+aWYbSeuOuK/CP/g2B/wCCy/gRv2ftZ/ZR/ag8W22k3PhKFrrRbvUp1iRrRfvwb5O6Z3KPTPpX8Z//AAVc/aItf2oP28fiJ8XdLv21Sx1HVp1tbhiGDwI5jjI6jGxRjHbFAH+od8Dv+Dgr/gmj8ffGPhr4eeD/ABxEmteJDFHDbToymKeXhYpGPCtnjrX2V/wUJ/bv+HH/AATx/Zq1T9pH4lwSX9jp7xRR28BAeWSZtqgE9PU1/ieeAfHfiL4deMdN8deGbhoL7S7iO5hdTgq8bBwfzFf0v/8ABT//AIOI73/gof8A8E/PDH7KOoeGX0/xFDNBNreoswaGc2wARoh1DOeWz0xQB+yvjr/g9B8Hxaex+H3wzY3JYY+2Tkoq9z8iAk1/WL/wTp/bz8Af8FBv2VNB/aX8Hotql9GyXltu3Nb3MP8ArEPfGPmHHSv8RcYHJOPQ4r9n/wDgmX/wWy/aj/4Jm+C/FXw3+F4h1TQ/E8RzbXZbbb3BVl86Ig8HB5HfAoA/cf8A4OYP+C3fwN/a28Jaj+xF8HdGnuH0HWQ17qtztEZe2JVlhxz1yCc9K9l/4NJ/+CovhXwFofiT9i34+eI4rC2dl1Dw219KscS7ARcQqWxjPDcmv4WvGXivVfHPivUfGWuSeZeancSXMrf7crFmP5msW01G+0+cXVjM8Mo6OjFW/Mc0Afuj/wAHFX7Xegftc/8ABTTxl4p8D6k+peHNFSDS7LD7og1sgSYpyRhnycjrX4neAPG2ufDzxppfjfw3O9rfaXcJcQSxttZWQ5GD2+tcxcTy3DPNcEu7nczMSST6k1TBwc0Af3Rfty/8HK/wV/aZ/wCCSR/Z3021vV+JviPTYNN1PjbHC0WBJLvGA3mBenvX8NCXLW8iywEqwIIOeQR+FRgk4HYmmuu6QgUAaGp65q2tXIvNZuJbqUAKHlcuwUdFyxJwOw7Vm+Z7f5/KozxxRQBJv4xz+dKHzUVKDigCZWzzUytk4xVaP0qZPvUATV/Qv/wbJ/BGf4wf8FU/Bl/LafaLLw4lxqU7EZCGNCEY/RiMV/PRX99n/Blr8Copj8VP2gdThH7hLXSrVmXnLl5JMN64VKAP6g/+C3PxsT9nn/gmR8UfGryiBpdJk06MqcYa7HkqB1yQGr/GPmlMk7TNyWOT+Nf6bX/B4h8dG8DfsO+HvhBDcbG8W6su+MHkpagPnjjHIr/MiQbyd3GRmgBrMW6VGytt3jqKnVQCRUsUYeVU/vEUAdBLdS2eiWkUZxIZTIG7jHTFf1tfDn/g6A1Hw3/wSyvf2L/E/hqbUPGp0Kbw7baoWT7MbWSEwI7qfmLxpgcdSM+1fyPeJCI7qK3j6RRj86wtufvc/WgB91P9puJbluWkYsT9Tk/rVanMMHAptABS4NA5OKmAwMUAQ4akqxUbIAM0AR0UUUAFFKFJ6UuxqAG89utfux+yp4ibwB/wTK+IetWXD332iBm7jcoWvwoHWv2R+G2u2nh7/glX4sSfl769WNB7yOo/oaAPx9tJ/L+Q85JNdBaynIx0rmIgm7ceSRmtOC52HaaAO6t7gIB5fB9a6TTb6QuDMelefW10DiuhtJ0ByDQB6xp11ZNJn7v0r7K/Z98P2fjLxJb+H77VFs7e72jz2OdmfX6V8B6fcxo43Nxnmvbvh3rN1omrLq2mSHajA4U847nFAH9rn/BN/wDZM+AHgTTbmPX9bTWbjUMvFtI+zs49SRnI9BX9Fvw4/ZU/ZL+IngWX4e/ETwhpGtjVYnia5aGN2KsCOGILKcDg57V/n+/s5ftkaj4a0i20S2mMpsn85JCxD7s9ODX7MfDj/gqtqvgbw2utXV7KL4HZHG2Qq4GN2fXmgD8v/Bng2X/gjz/wX8g+F3wm1WUeErzUYW8rd8p0+9+9DIvO7YrEAnkdRXsH/B0XpH7FHxT/ALE/aP8A2fbS2sfFyag2l6ybYBI7sGLzN5UcFk4y3Xmvyt8SftIWv7T3/BW3SvivM/2tfOVC7En54VbOM9t1fHP/AAUI+JN/4s+KGq6GLhjbW2qXEqxZO0blCdOnRR2oA/OgHcdxFLtAbIpqdKfQAUUUUAFFFFABRRRQAUUUUAFSp0qKpU6UADgkYXqa3mXS9P0zY6+bcS9M/wAGOv55rFBKkMOoqSNlBZn5J9aAPff2YvG0PgD4tafq16R9mfMcyjjKNgH17V9XfHLwA3gvxTJq+lgSaLqh+0Wkq/dw/O36j0r85dAuI7HWrS+k4SCZHb/dDZP6Cv2GtLiz1eK5+G3iHEunXIE1lMf+WPmjcjKfTsaAPjMptYPnNSKiuC4P9K0PEGm3Xh3X5/D+ooySwNgE4wy9iPXNVM8YAxQAwJGByOfWkKA/Lj8e1SA4+negFQNr9PTtQA0B8ZxxQhUkhhTwxYnngdKYke45H1oAjCHYwU5qpfqPsTt0+U1oHn2qpeoGs5F/2TUzUXCVuwU5rnR/Yh/wReC/8Mu6dk9n/wDRjV9GfCxQf+CmQxz/AMSp/wCVfMX/AARquBF+y7p7L0zIB+Epr6U+C8zXH/BTV0HRdJk/kK/yH8VIOWZ4u3978Wf6OcGvly6k32R+pXixM+DfEB/6c7z/ANANfhx4m4/ZC+EA/wCprl/9Dr90vF0WPB3iEj/nzvP/AEBq/DHxGgb9kD4Qk9f+Erk/WQ1+V8JLVLzX5M+kxmrSR+yV6x2QN/07qPyXNd34dkz4fsT/ANO8X/oA9q8+u2PlxBu0PH4LXdeGiW8Oaex720X/AKAK/rHwLS9hX/7c/Jn4H4oRtUpf9vfof//R+nfCL7JiT/zxb+VfMNxFn9hj4oE7cDxTFk54+7GMV9R+GYw9nLbfdkdCAw9xX5eeKv2bv2xW8Q6p8KfC+oufAOv6jHqV0hUFvMDDvywGPQ49a/xzwSoSxs3XqqFl16+h/qPSU3S91XP2f1RfP/Yg1iWPoPDjDP0gFfDP7DkiH4IaJF3MbD/x5hX6I+ONGm8Kfsb+KvD1wd0lrocqlh3Cw4r83/2Io51+CugMhADRMQT0Pzt3r5zBzvgalSm72mvyZtC3N7Nvofip/wAFcPgd8V/id8VtPsvBGg3eoi2R3doo2K89BkcV+REv7G/7TNpay3994XuYIYEaSRpFCgKoyTyRnj0r/Q30PQtC1WSOfVIEkkJ28gEH86+ZP+ChPhrw9onwYuJtIto7YtZ3O8ouC3yHHSv6t8JfHzEYejRyeNOLUbK782fg/iF4a4atVli5ato/z0E8xoy7DawLKV9CpxTMmpLneZZ2B4+1SVEqnYQ3pX+gMI88VI/jXHYf2VVwQZIHFZt3BcOjMvNainaNpqnd2/mKWU9qZyHCvC4clxxmoyIs9av7WV2jPNZ8iEcAUAN3joK/0/v+DQT4FL4B/YS8RfFG4gCyeJ9WIWRgQTFbptxz2yTX+YvoGkXeua3aaRZxs8tzKkaqoOWLMAAPrX+0v/wR9+AF7+zL/wAE6vhf8LNXtfsmoRaXHc3aD75kuf353d8gPgjtQB/Nx/wea/tOnw18EPAP7MmhXIWbXL2XUr6HPPkwAJFkdxuYn6iv85mRjjA6en4Cv6c/+Dr3482/xZ/4Kfap4S0u48618I2FvppUEELMq7pAMd8tzX8xJUjpQAqE7q93/Z08Jw/Ez48+D/A+sz7YNT1a0t3Z+RteZVPX24rwhQd1dZ4P8Uan4M8T6d4s0aTy7vTLlLmFvR4yGX9RQB/u4fCXwb4f+Hnw18P+CvC9vHbafpWn29vBHGAqqscSrwo4xwTX+dX/AMHjP7W8vxD/AGl/CP7L+i3ANh4Qs3vrpFOQbm7xwfQqir+df1ff8Elv+Cwnwm/bP/YFb42+ONUtdJ17wJYeX4jjlcRqr20W4zAMR8sirknpkkV/lqf8FEf2n9V/bC/bE8e/tBahIzx67qsz24Yk7YAxESj2CqOKAPjG1uJ7S4S7tmKyREMpHYjpX+iX/wAEs/8Ag47+BHh7/gmhqngX9p3XvsXjrwFpclpZxPuMuoxBCkIjJB+dTgEHtX+dR5n+f8il8w/5/wD1UAd18UvGd18QPiTrvjm6d3k1e+nu2aQ5b99Iz8+/NcvpWoXWk38GpWLFJYHWRGXgqykEEH1BFZJOTmkoA/0//wDgmJ/wXI+BHxg/4JTa1YfGrxpaeH/HngjQbiwnW6njjuLnZCywTQKSCzcBSBznmv8ANE+J3im58bfELW/Ft1K00mpXs9wZHOWfzHLbmPcnOT9a89DuoIUkZ602gCwOOlSRu6MCjFfQjqD61VVttO8z/P8AkUAftZpP/BdD9tPS/wBgi+/YBN9bXPhq8i+zJeSBmu4LU8vCj55VhwCfujNfimzSbiW696PM/wA/5FR0AODuO59KC7HqabRQBbWWWP54nKsDwQcV0Wv+M/FnitbVfEuo3F8LKPyYBPI0nlxj+FdxOB7CuSooAVjliaNxznNJRQA9pJGO5mJPXmhXYE+9MooAvQ3U8B3W7shIwdpIzUbEhOKq0UALk04yOepplFAC5NAYgYFJRQBKhyKfVeigCc8jFMCEHmmDg5p/mf5/yKAJKVPv1F5n+f8AIprHJzQAjdTSUUUAFFFFAEkfepk+9UMfepwRsIoAsLGSNw56YA9ScYr/AFlf+DXX9n8fBz/glhoOu3Vt9nvvGF9Pqk3HLRnEcefwUkV/lbfBH4a+JPi58VvD/wAO/Ctq95e6vfQW8UKAksXlVcDHJPPav9vf9kX4VQ/AH9mLwV8JvJW1Hh/R7S3lVeArpEC/47hzQB/n6/8AB5b8dJvEn7Wfgz4CwTh7fw9pCXrRg52y3TNkn32oPzr+MFTnkdOlfsj/AMF7f2ibv9pD/gp58TPFryia20zU5dJtWUgjybI+SpBGQc7a/GzzP8/5FAElWbH/AI/Yl9WqiZCrBgOlWLLBZ5j/AAigCTWLg3F+7g9OKhjYsvPpUYbc5b1pJO1ADX+9TaKKACpA4A5qPviigCXzF/z/APqqPJowakQEDmgCKirG0NwaNoXpQAxOlPoooAjbAINfp9ZTzL/wTNv9L2Zlm1mAIncjze2K/ME7lkDgZwR16V99/Db9tuy8IaDZ+GvEXhKy1WwtACI2YqNwH3to/i75oA+MLjwD41tCol0u6UOoK/u2OR+Rqm3hXxXHA92+m3SxxjLOYmCge5K1+0Xhn/got+yRqVulr4x+Hlzp0pxuuLCf5uPUHrX0d8Ov+Cgf7D3h67n1fTbjUYkjhJaw1S2W4t7nH/LNgOeemaAP5tYL+SE4atqHVouDnGa/p58Mfttf8EQPjRYvP8b/AIVjw3qDuVZbC32xHP8AErIwZfX2qXU/hf8A8G8Hj+LzfD+s6hoU8nID3U0aD6hiV/WgD+ZaDXowRsPNb2leLLqzmEkMgXB/Cv378d/8Ekf2CfHllD4i/Z5+OFolrMctHclJxEvqxUhuPeugvv8Ag1+/a68S6JB4p+APjfwn4zsLmMSxvHfeQxB6DDjGfxoA/EDSPibeaW6apYy+XKpBYZwCB1r6S8b/ALSaeIPhx9gsXMNwISdxPKnHTPua9y8a/wDBv1/wVo8ETTRxfDSfWBb5JOl3Vvdbsf3UWTcfptr8vPiv8Ifjr8BtcuPBPxq8L6r4Y1AZV4NRtZLduPQOoB/CgDrv2S/EUuiftD6J4jZ8OkkkjE+pU5/WuS/aB8Qya58TdY1RjuE9zIcj61znwn1ODQ/FsWo3D7BbpI2Twc4xXH+J9R/tXVJb+Pkyu5P4mgDmk6U+iigAooooAKKKKACiiigAooooAKdET+lNozjmgCxRTVfIwabJ2oAlAVvkJxnvX6xfBS5PxC+Hvh/XDh57BHsbrb/CIh+7J/SvyUr9KP8Agnxr5uNR1vwI5y13EJoV/wBpOufwoA9k+NXhlvFHge28T28H+maUzJNKo4MQIAB9818mwy7lBPOa+/dZ0ww2l34GmSaKCZZGlRgQfMI4ZQeq8da/P1FkillgOGEbFQP90kUAW+2096DtP3zSKp2F1Oe2T1+lGEKjd070ALjshqVH2IVHX1qLzDHxnIoyJPl7UAV3fDQq+R50qwjnGGc4Bb2ya+79M/4JpftP+I9Ig1nw5FBqVvcIHDQt1ByK+DrrcrW0pHW7h/8AQ6/vB/4Jw28T/s9QyOgk/codpx/dHPNfg3jf4g43I8NTqYa2p+y+FPCGHzFzniI3sfPH/BNT4S+Mfgl8ALbwb45tXtL6zklSRXUqCSxbKnoRz1r0X9ny6Wf/AIKe3cQIYppEnTtwv+NfT/xe8e+GNF8mHWtftdKPGEupVjV29txAOB6V8J/sb+K/DXij/gqdqY8P6pbagp0mTa1tKs6nAjyNyEgkDr6V/nFjMTWzWWLzCqnez9P8j+0IYahhcOqMHokj9w/FoX/hD/EAx1trv/0Bq/B/xAzH9kP4QA/9DW//AKMNfux8R31Gw8EeIZtMj+0TGC7RYl6lmDDHtX8s2hftK+NfiB4a8G/sqWvhCaDV/CfiBry4vMsylTIchlK/KV7npXg8E5TUxEZ1aTVoWbvppqEqzclKx/SLqc3leWD/AM8f/Za9C8MSL/wjWnf9e0P/AKAPavGpbiU2VtLcna7xZYds7eleu+F3X/hGdO5H/HrD/wCgCv6Y8Cl+5xFv7v8A7cfh/ij/ABKX/b36H//S+nvD09lpkM2qanKLe2t03zSvwqIOpPsK+kPhVrHhHx94fHiX4d6nbeILFDtaS0YMVZTyrL94H8K+XrTS7HxVoeoeD9V3G21OF4HVOG2uOSD3PtX5keEPB3xa/ZR+L2oaz+y9fzHUtGO+70C7lJTUIQegQfxEdhg1/jRUyDCZhUlCpU5anS+3nd9D/UOliKkYctNXP6M/HeieD9W+DHirQfiZqsfh/QNXsWs5tSmKqIRMpQldx5Iz+dfnz8IP+COXwfm8F2Oq/D34r65qmgTtm2mtJEWJxuI4A4655+tfBPi5f2lv23PjJ4Z0z9ou+m8M6dqdyosvDNoxjVYwfnklHHGMkdTX9Tnwt+HPhf4S+ANM+GHg21NppukJHHEnPJ7sc9STkk85Jq8TGeT0HhqOJ53JptJKy3Wj6+p4GYe1jNVNj8Qrn4ZXH7I37VGlfBPwprt9rGm6nZiW5OoPvcM3I2HtjFdD/wAFD5zN8DJXk+99juQfqE/+vXVftiM0X/BRnQIW4JsUA/79mvNf+Cgd0ZPghKv/AE6XR/8AHBXdwZSlLOqTnu3Fv7zzs5rOeXOT6xP8+m5kVUuMDn7W9VfMZvl9aknT5Jyf+ft/60kQXHNf7CUJvkj6H+fmavmxMvVitzjHagKW4FPyvpTlIPSqPPOX1GzaJt8YzkVjGGb72016IFRzhxkVHc2aGHcowPagD0P9lLWdC8G/tK+B/EXjJF/sy01e1kn8wfJsWQE5+lf7e/gTxp4cl+CuleOdNuYptO/smK9jlQgxmIQhgVI4xgfpX+EZc3N2bkBG2eS2V+o71/cz/wAEz/8Ag5A+B/wM/wCCWOufs9/tAXlxN448O2FzZaHAyNMb6G4QiNA/QGN2YYJGFx6UAfyPf8FC/jHdftAfto/En4s3bb/7Y168nU5J+QyttAz2wK+NW29q2PEOqya7rl3rU42yXczysvoWJJH4E1i0AFFFFAHeeHPil4+8HaPf+H/CWtXen2Wprsu4YJWjSZehEiqcEYrgpJFZTjvz3/lUFFABRRRQAUUUUAFFFFABRRRQAUUUUAFFFFABRRRQAUUUUAFFFFABRRRQAUUUUAFFFFABRRRQAUUUAZ4oAeEY9BThHj7wqaNSOtWBayyHgUAUti0bBWkdPeP941V2UZPFAFXYtIyccVawtGFoAqoCOtSBSelSMmelKoIGDQB/S5/watQ/BOb/AIKa6VbfF3Tk1G7lsphofmKGWLUAMxuQc44yA3VTg1/pw/tofGHS/gF+yt49+LWszCGHRNGu5g2cYk8orHz6liMV/j1f8EkP2k9L/ZQ/b/8Ahx8Y/ELrFpun6vB9rdjjbC7BHPPoDX+gx/wc1/t7fB7wl/wS81Hwh4H8Q2eoat8RHtoLKG1mWWQ25/evIVQkhduOTQB/l7/FHxdfeO/iJrfi/VHaW41G+nnd2OSWeQsST+NcDSk5JJ6k5/OkoAUdMVatwyxSDHJ6VVHUVdjOAaAKyqVPNJJ2qV/lOTUDMG6UANqSKKSY7Yxk1HSh3Q5Q4NAFk6dfZ3Kh4pPL2DEgwfStGLU7yKMfNkVZF1BeMfOG1jQBi7SG2Y5pSpHWtCZIIW+Vt3bNZxJJzQAlFFFABRRRQAwFwcdRTAuM7ulTUUAUynPFSYAHFT4WkO0daAIa0tM0rUtZuhZaVA00pGdqLk1UAU81raPreq6Bdm+0edoJSpXcvXHtQBbuP+Eq8LzGykkntG6ELIwX9DivUPAf7Sv7QHw2ZLjwH4z1fTPKwVWC6lVRjpwHxVrwx4m0/wAR2iWmqoss6jlXGQfcDtXWSeCPB91KGe0G49dme/tQB9a+AP8Agt9/wU4+HFxa3Gh/FLUmFqQUE22TOOx3Dn86+vfiX/wcNfG/9ov4D618Fv2qfA3h/wAcXGp2slvDrE8Xl3luzrgSKyqQSCAcAr9a/H3xL8J9KudOeXwlEyXcSljG5+8B1xmvneaBUJj2kMM5GORjjn0OaAIDO3zrEdqljtxxx6VBRjHFFAFfpxRUzrnpUPfFABRRRQAUUUUAFFFFABRRRQAUUUUAGSOlOLbgKbRQAhYDrX0V+y747fwH8WrPVGfbHJHJGwH8WV4FfPAVWXnrkD861vD17JpeuW13FgmKVcE/X/CgD+k3w94h8OfFjwr52sWqwapKhSxZeCV77vX8a/I/xfpL+F/Hmo+FboFZ7Z+V+vv0r2Dwl4/1HQtRtLy3nkupJQPIWI/LET1Fdf8AGey8JeObKPx7o7MviaJdt1EQMXCAY3LtP319COlAHy2SUO1RkUx/mGcYqFpmL4kUq5B6+2Mj6jvUqElDx+NAEizRAYcgGoZJtwOwcDvULEjqAaHBZNoGDQAXUo/0fd0+0w/+h/8A1q/u9/4JzTY/Z6tsdGtkAz/u1/B1eHalqfW6h/8AQ/8A69f3Vf8ABPi4Nv8As7WWP4oVH/jtfyD9LSP+x0Uj+j/AaTU6iIPgN8E/hj+1j+2z4v8AA/xt0uPWtO07TGltoZncLG6smdoUgfnX2Zof7On/AATu/YJ+JmmfFW1WDwRrGrK9nazSu5ikDYDAg7gDwM5PTFfOX/BOiYzf8FBvHqp90aVMPf7yV9h/8FD/ANnPwb8fP2dby78T2Jub/wAOob6zlVzHsKD5wWyBtK9RnnFfxL7WpaGFlUlGlLSSj1+R++5jUlPFThfTQ+iL4RXUB8QabImoadesZYbm2IaKUSc9RkYOea+N/iZ4g/Zb+Fvjm08OeO9Q07QfF+rsv2a2UAyuzthPN2AkFie+K/Ff4JfEj9u34E/Di50H9me5g8WeE9ejMcR1HzHbSWLFWkj+YZAyeueletfsI/s0+GfH3xe8SfEb4sXI8a63oPk3E15eOxYX7ncTEhORGnYnIz2FbS4RwODpSxcsRzJrSMd+yuunmfS4JVuRK2h+sGtuY7nEzYZQVb04r1bwxIv/AAjWnc/8u0P/AKAPavn/AFq/nmmee5Pzuzf/AF6+gfCNuZPCelyA/etID09Y196/dvA1OOGrf9u/+3H4p4pK1Wl/29+h/9PF+Mfx0+MnhK/T4c/s8eEb7WvEF2iiXVFgka1sY3437guCw9jSfsY28/wG+JF14l+L+m61fajrc6i71jUrYpC85IwsYcZUe5NfbPw58a+LPDkDWWhXskMUo3MgPBPFWv2srnx746/Z+u1gnlvJ9P2XghHBYRnBPHJI6/hX+OWd8VUXD+y6dNLm3l3P9QcHQm4ucdj5b/bu1HRPi14qtofhXb6quo6KwnTWNDge4+xyryu/YOMnkgHpmvrb/gnb+3X8bPEnia1/Z9/at8L363wdLfT/ABJDaTC3uDxj7TlBsZuu716163/wTs8BX/w2/Z7tL/WIwNQ8QzPfSFlO/Yx+QHPt0z61+nXhqQXDxB1BJIJ4HrXiYLimlGhLLZQ5uz8/I+e4h55Um9rJn4d/twO9v/wU10K1HRLJO/8A0z9MD/69eZ/t85f4Kzf9et0P/HM/0r0z9uCNpP8AgqDoo7CxjwPT92a85/b4BT4KSr/06XRP12Gvr+FFy5xQt5fmeRif+RPd/wAp/n4T8rcIf+ft/wCtQJuSrbKGNwT/AM/b0eWTxX+u2FV4L0P4Fzj/AHh+rFUKw61NHGOf8/1qFIypzmrMferOAcEAOae6lo8dqSpEcfdPagDh9X0maJjPGM55rnGExBBQ/gK9e8tZV8txkUqWMKnbIgP4UAeSx21yV4jY00wXEYzLGRXtiwRhAsagHtxXH65aXJ+SQ4HPagDzp87uRiq2MsRWzPp0ka5J/GqKqFQlhz2oAg8r61GylTVje1QuxJwaAI6KKKACiiigAooooAKKKKACiiigAooooAKKKKACiiigAooooAKKKKACiilUZOKAEoqXym/yP/r0eU3+R/8AXoASP0qVhg4poXb1pxOeaAE+lPSNyM00dalQkE+1AF+CBD941rwnYwGOKyIlGc1oMdse/PSgCfUpUEeFPJrnDnPNSTSSTPvzUXPegAooooAKRjgZpaa/3aABJ5EYMnBByD6GtLU/EGtaz5Y1a6muRCuyMSyM+xfRdxOB9KyG4XNNHSgBaKKKAFUEnirqAgc1Wi61c7UAVpSKr1M0ZY5PekER/wAj/wCvQBFQRmpzFx0pvlN/kf8A16AIce9O3MTknn1qTym/yP8A69HlN/kf/XoAFlIGG5+tKpJGTR5XvS8KgNAC0U3etG9aAHUU3etG9aAHUU3etIXGOKAL8EAfn2q2dLEhGGAFZZlZEGD3qRbl/WgDWXw/vGRIAajm8OXcY3KwIqut0ejGraX5j4Un/P50AUNJvp9O1JJgSrKQPwr6hstejFrDcKcMRz9a+Vb+XzZvPXjNd1YatKtmi7yQB0oA+jLTxEruJS4D54NR3XgPwd48uP8ATpTpt03JljXcrn/aX+ua8Qt9dUYjduK7TT/EZhlSQPuXI6+9AGpffsqfEOe2k1Lwi8Gr26Zz5bhZBj/YPX8K+edc8P6z4bvW03XLaS1nTqkqlSfpnrX0FpnxZ8R+DdadNMunEDHdtDceuK6X4o/HTQfij4FbSvE1sg1W2w1vcqo357oxxyMetAHx/TWXPSgcHk5p+4fw0AQFGFNwR1qyST1qF+tADKKKKACiiigAooooAKKKKACiiigApwYg7u+c02igD9KvhHomreI/Aen+JbcW7QvkSea+Cuz5M+ucqenbFesRQXptXjMy2cQz5srjIIHQR4GT+dcV+wHBpPjjwtrvgvVT5k9lItxDH3KMMPj0AIGf/r17p408M3ml3B0qWUFCyvlj8iKOcDjg4GPrQB83+NPDkU1o3iTTI/LiZ9sq+gI4k+jEc+5Ga8pJaP8AdZ6d+x9x7V9ZaTbS6pqclnrASC2v/wDiXBB0XzAfKkwf9oAkk18w+JfCuueDPEF34a1mIxXFm5jZW6/L0I9iOR9aAMfGDmgDHGab+8PtQxIWgCvdLvW2HpdQ/wDof/1q/uR/YMcxfs9WCr/zyU/+OCv4cZult/19Q/8AoZr+4j9hQkfs+aew/wCeS/8AoAr+Q/pWy/2Whc/pDwEjeVQ9N/4Jxzw23/BQL4h395kx2+k3DttBLFVKEgAA54FfN37Xfx+/a5/bD1W8+H+k+C/E3hD4XQStE8VnaStqGphWIU79uERuoHHHWvo//gmrMR/wUN+ICE8/2TM3/j0dftpqeo3kc3zSHAHrxX8WT4ljlrdTkvJLR9j94q0pTzGo09rH4d/sr/Fn4f8AwT+Gd38MvGWkX3hyXRoDc/ZdWiH2g2zZ2yHJG/JBGFBxXwN428JfG+T4tx/tD/s02XiPw5qMm6a1aSykl07VYCdyRSLHkr5inIZhivvD/gon8B/G/wASPj/4W1zwjZz36a/FBo9xIgLLaok253OAeSkhOSQPl+ufv7UdZvvCOnx+G/Ct49vZaaiW9uiN8ojiXYB78DivnsJxTTwVWOYx1c91p13PvrP2ajHc+Bfgx8YfiB8XvCM+ofFfwjf+CvEliNt1aXkTRw3B25863Y4yp7r1Ffol4LUjwdpI3f8ALnB3/wCma18n+NfEmta5diTVrqS4wrBN7E4AHOB719MeCZyfBmkE/wDPlb/+i1r+n/BuvCvHE1aUeVNxdu25+E+KkPfo33979D//1PobwjKHkRR1JxjufpX1p4KnvrCWK4QKzKxUxv8AddG4IPtXwnNYaprXhbUdH0K7On3lxbyLBdAZaNzwCPpXxv8ABb9rT47fsrau/hj4+Tt418IG42z6nAC91pr7urqOdg6kHnHSv8WMbwbUzKrJ0KiVRbRejenR7L9T/UnC4pUqd2f0r+Fr2XWJkjgjRGhUJsQYREHAC+3GK+ivDSNbzxh+u4V/MF8ZP+Cg/wAUfj3qVj8Iv2NIZdK8O6jdw2j+JLlTFJPLIwXy4f4goJ5IzxX9EH7OPgvxp8OPhZongD4g6yfEGsafEPtN8VIMjOxbBLEk7eBnvivExXBmJy1wq4ipao94aNr7j5vOcSqtN8q7/kflr+2fEs//AAU/0ogdLBP/AESa8y/4KBWxg+DcnfNpdf8AoAr1z9rOFbv/AIKaafcf3bSPH4QkmvMP+CibNF8Htnf7Ld/+ixX3HB2Lbzek2ux5mJh/wkxX91fkf57wU/6Vntdv/WlwelW9pLXYHJ+1vQI2POOK/wBhsGm6a9D+Ac2pr6zK/dlVY2zSojgnNW/LH+f/ANdTm1+UMB1renFWueW9XoV/LbtQIj+P0q/Hb/Nuap0iCk1mBUQBEDAZNW15bmjy9vShTg5pgWgFCjiuU8XPdW9mCq7t2Ru9K6XzQvIouPKvbV7WUbgw/X1oA8QknucBJGLY96gJLctWjqNpdWd21uVDY71UWHUH+5H+lAFU5x0FVm+/XR22j31wRvXFdHb+EopQDN+dAHnghdvu80GCVeWH6V7bp/hfS7fDMCx963L/AEC11O0+yIiRj1oA+dPLPejy/wDP+TXo+o/D69sVMpfeg5461wEytBIYyCMHAzQBXKcf5/xpgxn5qnDPnABq7Fp11P8AMI2x64oAzDt7U2uvtvCGq3IzDGefU4/nVHWdA1LQii38W3zBkHIPFAGAFJ5p3lnGf8/zq1b2t1cOEgRjn0FdNa+ENauztCFR64oA4unoMn1r0qL4damw+citW2+H8q/LKR+FAHkLgcYpmGr3mP4f2gxuINaEPgSz6AKaAPnfa3oabX0Vqek+GtB0yX+1IAfM2hXyd6+69se1eBTqpuGMY+XJIoApgZOKf5f+f8mpKKAI/L/z/k0eX/n/ACakooAj8v8Az/k0qpg5p9FAC5ajLUlFABknrRRRQAVKnSox1qwhBORQBaBYAFfWle4ZsKajqFyCeKAJvk7mkxD61BRQBG5IPFOX7tOooAKa/wB2nU1/u0AQ+1FFFABTlGTim1IgPWgCaJQM1NTEBHWn0AFFFFABRuC8mimP0oAcWyCRUOWpKKACmt93FOpCQvWgCCirIBIyKSgCvRT3GWxSFGAyaAG0UUUATyY8v8aqoTT6KAHrJg4NPMrZ/wDr/wD1qhpj9KAHmQONp71pw3TRoI+orEq4HIwp6UAaUtywYEd6tQ6vcwr5dY9NckJgUAW5rqa5YvNziq0rB+STmovMb/P/AOqpByM0ANVGUfPSkenFOooAZhvWmMCDzU1RP1oAZRRRQAUUUUAFFFFABRRRQAUUUUAFFFFAH1h+x18W9Q+Dvxeh13TxG32mB7d/N+6AxHJ9hX7d6PqnhX4pWdxpzvHGI2M1zKoB3nn5IyegOa/m+8HX0dnr8Esn3chT24PB5r9R/g7411TwVNts7drqzd98e8n5G45JHUCgD63134P2d3bS23h63axkuXLRFuRtQna+fVSB2rwT9q3w3f8AirwTovx5toWh89P7P1BFA+S6tv3bO3+8Rn8q+zvDfxB1rxDpNokNolzfyB0SQHIA+9uB/ug8GvSJvhhB8QLLxV8F76SGZvFGn/2pp7x48uO8iX98ir2YsM8UAfgmCTEJEGAQDimtkqMVX/s3UtBvr7wzrilbzTZnhkDdQVJBqx5oHBP61qqegBKoL2w/6eof/QjX9wf7Cq4/Z9sC3/PJf/QRX8PU0ij7O4PAuof/AEKv7eP2Fbkj4AWLHp5K/wDoNfx79K+FsLR8j+mPAWSvVPT/APgmx/ykR+IMo7aPNx/wKOv2yv7ea4zIcc8DJxn2HvX4k/8ABNOTH/BQ7x+3YaRPn/vqOvp3/gqL8NPit44+B+n+MvhR4wTwlP4Wne7mZ2kQTbwqoN8Z4KkHGQRya/hTM8sjisRCjOfKpaX+4/cpzccbVa8j6u8TXsmnTSPGoXIw2SVbA/iB9jXzX4kttQKTumESIAc/JnPpnr+Ffl58Lv8Agrl4g+Hnw+fwT+114XvNX8Q2UZ/sfU9IVXh1Zl+VFkbBAJbq4/EZrx/4eX/7TP7Y/wAd4fib8W/EP/CH2eitFc23hzT1dgkaHcqzNuwC3AYNk/SscV4U4ihGdXFV4wpx2e/N5JI+0wWOlONnE/R7xVMscgCnkKf1FfWngYg+CdHOOtjb/wDota+MPFN7JNqMsqqArFsDsMDtX2V4EeQ+B9GIHBsbf/0Utf0n4FU+TD142S+HRf8Abx+K+K1NqpR/7e/Q/9XnPiF+0/8ACz9n3RTqXjCRr7VpgVtNItsvcTueB8ozsTP8Rx7Vzv7Efh29+Onxa1nxN8avsSXGtItyulwOHjtoegSaMcO/1ya9c+Hnh79ny01248YeOfB6a5rlz8ouppCdijgBFKkJ7kda2/jbH8PPD/gy18W/Cbw2vhy9tLpZJL2CY79oH3WAxkMeOT+Ff5A5/n2Cw9J4bDQarS053+nY/wBRcuw85Lma0Rzv7WXgw/s0eOvDfjX9ni1sxf6K32qLS5wDbyqnzMAnCBgM9OffNfqz+w9+358HP2vdLTTrG4XQvGNtj7dol0fLlMgADtBux5i8dASRnkV8N/speBPA/wAbvANx8Tf2gdMl1zUb27kSydp3Xy7aMgArgjBJ745r7e+HP7IX7JehfETT/iv4f8KvZ+ILGWOWC6+0SZV06EjOD75696+Vnm+Cnh5YbMdakNVJb37eh5OeUJSi3TifM37Tt1HN/wAFJ7JVOdtoBntn7O1eb/8ABRWaEfCGVpCAEtbvJ7f6omtr9py+K/8ABS2KZmBItUyT0OYCM/Xn9K9z8aeB/BHxo8Ov4U8bQfaLZyxC5x1AHpyK8zKM1+q5hSxNW9lZ+tmZRy/2uAjTj1R/mvgC3ku2dWJNw7YCnpU0mpRRkReU/wD3ya/0GLX/AIJtfsyEhItBtkX08lD/AErUX/gmL+zDcks+jWpHr5CbfzxX9+4L6WeXcqUaD+8/mvMfAytOs5+138j/AD00uYpX27Hyf9k1pQkTQg4K5OAG4P5V/oYWX/BL39liOI3K6LasUB4EEfWv5Cv+CxXw/wDCPwm/aatPCHgayisLSKLyysShQxVsZIUDmv0rw/8AG3C8Q4lYejTte/4HwvFnhfVyvDuqql0fmSdiLk80xioOKyUldSQ/YkfrUqynHJr926H5JfRXLE8hTGO9Qo+5sZqCR93BqOE4fgZqRFuY8bQeetVg7YypqxMBksnJqCOPKZJxigCsLGKaXzpBuNakdrGgyoA/Cqp8yPBHQ1dRgeCaAEWBRxmpduwUHb/CKRCx5PagDQhYACtq2ePaSx6VgrG23INS24I3bjQB2lnsc/vSMEd+a5a6+HOlajetf3MkmGJO0YHU1Payu2N3bp7VrpNIoyGO71zQBz6+CPD1hJ+5VmH+0a24bOzhQJEqgD2FPkZ25NVy+z5iKANAeWAAAD9KoX2jabq5V79A+zIGfepEkj27l6nrVmAvKdo4oAZZ6XY2QAtYlQDgcZrRZmAIXp+FLGjY2nrTv3nTt9P/AK9AFeGNec0yVAPu1bMXPB4oKIo6c0AZuG9DVmLI2npUglBcBqe5DEADGe9AHj3xZ1BWnt9NjP3fnb8elePnoa6bxfeSaj4hnnP8LFB3+VeBXMnoaAIKKKKACiiigAooooAKKKKACiiigAqaM4Gahp6tgYoAn3tVfcxNO8z/AD/kUwcHNAEwzjmlpoYEUb1oAdRTd60FgOlADqa/3ab5n+f8ikL5GKAGUUUUAFSoRjFNVcjNPVcHNAFqio/M/wA/5FPU5GaAFooooAKY/SlL4OKRjuGBQBFS4NKUIFW1iI+XGfegCKKME/NVtbLeOWzmp4rc+lacUK5xjpQBWTQVddyt2rMn027hbBTj1FdNHcSQttHStJNQLLsZQQetAHmssbq3oah2MT87V6s+kaNep+8PluRwetc9qXg29hTzrX94nt1oA4mippYJYH2SqV+tRbWxkdKAEopm8Zwadlj0FAC0x+lSBWIzimsueKAIBzxVhjnHtTAmDn/P86fjPFAEynIpW4XNNjznaadL8vy0AQVOOgqCpx92gBaKaGDdKdQAVE/Wns22o2OTmgBtFOUZOKf5R/yP/r0ARUVJ5f8An/Jo8v8Az/k0AR0U1m2nFPPFACUUUUAFFFFABSgE8CkqROBuoAntMw3CyKRkEGvvL4afFO2bSLeCV1jZflLPwcNxg89O3tXwLGAJQRxz9a9e0RnRvtCKFUL0I46UAfrd8PPE0VsF1XSLh1ht8O1s2WikB4YKRyPpX154f8WS6VLomueH45J7vQr1b7zIAS3kT/62EjuBj3r8bfAXxIv/AAm0d3aXBW4tnV40dN0bKRzkZ7V/SN/wRs0fwl8bdX8S2PjiOK+S3McpIHG6Qliv06V8R4g8UvJ8uljV0PreEeHY5liFQk7H5M/8FF/g62lfH3T/AIu/CjTpb/w94zthcBLZDIyT4/eK6KCVbdzg4r4l/wCEH+IKjH/CP6p/4DN/8TX+hw/7LnwKR8QaTGF6kYGORgnoDkjvXN3v7MvwPhXd/ZMOB1J61/LM/pYSg+SVPX1P3Gn4E0pw9opO3oz/AD4brwX47aGCI6DqSf6RE5Z7dgoVSMknFf2jfsNxzx/s82W5esQX8Qoz/OvqXUvgD8ErdNh0eNwPXbj8uc1iSWOjeB9KfRPBVnHa2nJ8tWA5bGT+lfjHiv41y4moxocnK117n6rwJ4dwyfndN81zi/8AgmkrSf8ABQf4gn7o/sm43E9VAaPn6etL+3h/wU98BmO6/Zx/Zj+y+JtcuA0WqaxcR7tO0+JDhiokGJXBzgjIB6ZNc3/wTSkuLn9v/wCIaXqkpLpNyrqOCwJjHB7HHSv0oj/ZT/ZU8JWrw6J4DtI4pMNJlVZ5OSQzsTlhk9Cfzr80r5lgsHXdbFUnOXKrdv6R7/sW8zm3tofnH+x38EfhP4x+Cv23xRf2niGe0Mim5b54llK7mKo65iAz/D9a+CvE37ROt/se/FzWtR8IGx8Q+Dby6C6rosR3XlsEO3z4XwSeeSCcV9L/ALZunah8I/jVHbfBqF9C0rxTYwWC2Vp8sMl1JIYiwVRhWIIJ9a+trrwd8Ifhrpun+Dj4D0zWptNt47a6vrpEaWd1X94zEqxOW5bJ9q8zC8Q0KFVYrGe/TlpZ/wBbn275raKx8/eE/jR8M/jt4e/4Tz4SakNRsXXbMpBSaBgM7JUIGGHTPQ9q/Sj4etu8A6G3rp9sf/IS1+bl5pXgDSdVu7/4f+GrHwul4p8+GxUIsrLnDsBjnFfoh8Op2/4V9oXH/MPtf/RS1/T3g17FwxE8MrQbi0nulroz8T8T23Kjzf3v0P/WwtF1dbSVY2438jgYNe7+Hb7w/rijQvHFtLe6HdZhu7eLl3TqChOcEH0qX9j3xZ8ONG1K70nx74VtPEbXjYhe4coYtvXAXr+NfoZH8Tvgfp832e1+HGloi9/Mk/wr/EfjSjT+tXlO1r7H+mtPM8dBOFKldeqX5s8c8Jaj4W8Pw2+geBrI2GjWiJFa27MSVUf3txPPPNfUfhfxNHayxSSsoUEdxzz0rkYvjV8J7XP2HwBpIPXhpM/yrrtD+PvhUuBZeDNJj+hkz+eK+F+q0FUc/aNt+TOPF4vMJRs6K/8AAo/5n5zftYfs2/tj+OP2xm+PP7PGmJqehzW0SRzYjkG8RhXG1iDwfSrvh/4A/wDBUeacSnQYo89/KhH6b6/V7Sf2iLiyKxadoFnAg5AillUDv0Fdgv7Vvi63YLa2Eaj/AGZpMD68V+h4PiHBNRp4qKaSttqfM1q2eQXLRgkvNo/MG3/Zw/4Kky4f+ybYfVIh/wCz1H4n+Ef/AAUq+HHg3U/iF4sstPXTNFt3u7lJSF3JGCzYKMecDiv1o8PftY/EbUtUhsJ7CGOJzhm3uxAx9BXwF8Cv2/vin+25+y5+0hbfEjTrWxXwOJtOtPsy4LfLIG35Y9AM5FfofD+R5bmNCpOhH4Fc+WzDiXPcJKEsVFcraWnqS/Ab4kJ8Ufhvp3j5VMf22E70OOHXhx9M9M1/Ef8A8FzLoH9saNwvAL4/CQj+lf1w/sK6o7/s86VFIRy0pOO+XIP8hX8i3/BbyYS/tdWzNyef1kNfqv0YKTp557PpaRj4wyvlcl6H5BNN5sjHGDuP86kDMowahbH2uXHQOwH5mpDvJyK/0Z6H8XS2QEk8mlVioIHepUjymTSiEk7u1SQWIW2oEPTpnvQvl5ZVz7ZpFDr0x70/5SpbGBQAzdt+VASPf1qxA4bKkYYcn0x/jSh0YDgccVMgDYzQAmeNw6U+El8jGOaUADA7Cnlwo4FAGgmD8lTxRKDmoo8FNw6+laccSOgI4PegB8EQySMcVcEWSB61YitFBwe3U1dEK7cgdOlAGayjO0d6je33Lirzxq/KiofKJ6UAZogCHFXod6OCajdCOfSo1uWDZU/MOg7GgDpoYhxjLA/nmmyRhDwC30rPhvbpmGSPWtSKV3UFsZINAEOz61C6t0rRXGOuaruuTwM0AZ21YzkjJqhqc5tbSS75AjRjW60QA9TXGfEa+Gl+FZU6PcYjX+Z/SgD5wed3mad+rEn86qHoalZgoVSORyaiPQ0AQUUUUAFFFFABRRRQAUUUUAFFFFABRRRQAUUUUAFNx7mnUUANx7mnUUUAFFFFABRRRQBKnSn1EhOcVLQAVKnSoqlTpQA+iijGeKAGfKWzVmONSMioUj+atKBBkAUARJCCc1pw24IzQkfz81rRQgcUALDZAjjuKux6ZIMkVfgi+UfSteBDkUAcjPZSQ/vGGazdzDcMV6NPbxyptasO50obcp3oA5eK4Kt8/T0ro7HXRB8jN8tc9dWc8SksKz1Rwo8w4oA9IMejamN1yq7/AENYOpeCbO7QvYvtbstYEe+Nd8Zya3LLVpQhSXg0AcxP4O1u2zsgMgHcGsKXT7u3OJ42Q+mK9eg1RmP+sNbMc0VwNrgOO4wKAPns4BwCfpTdjV7lqGhaXeKQImibsccGvPNY8MXNhA15EwaNTzjqKAOfXSNRcbkiYj1xxTTp93G2HjIr0jwdqIvLI2bdUNdw1rFkEqPyoA+f/IYDdggj1qF/nGCMV7RqWnwPbyKseWI4xXjt7azWdx5bqQDzzQBUEagYp+OMVKYmBxR5cuOgxQBEoVBjFL70rIwI2nFNLL94dPegBknakVQ3WhmDdKaCR0oAcnWrOSV6jmqydafsFAEm07sGlZQBkVIhOzFBAPWgDNk5fFPHOc9qe0YJzRtwOOvegBoHALd6UgLwetOTvSdiTwaAGf5/GiipEVSCWOMdKAIjntTwSBgnANLHy2GJC98Vo/breBQtvFk92f8AoKAKaw8jdkA19E/Cu0sNWtLiym2IzISkr5O3HPPbkV85TXcspwxzXrPhrXJNCVXt0LKxXcvQdMfyoA+sNG8HRPptrqVmRJfXd6ltFCwzmEjbv+hb9K/od/4IE6XceHvFXjfTbrDeTNHE2Om5NwJH5Cv5rPDnxH1CCa3kkY7LWdFVcDKRk7iF4r+j3/ggT4nj8QeIPGd/aA7XuY8buuCW61+HfSEp/wDGOVZH6b4Sf8jeJ+6/7UvxJ8YeDJtD8HeAp4rfU/EV9HZpNOW2RLIdu87ecA4zXX33/BM//gpLrEa3EPj/AEXy5F3/ACmQcHnutfMH7YuqKfiv4D35z9rB/HetfuT+3b448Q+Dvg/oWo+ENSm0u6FzpoMkBIYq52kHHUH3r/OjIsFgYYeeKxdPn10uf1FxVm+YUa+Gw2BqcnPf8D8pLz/glN/wUrmyf+FgaJz7t/8AE1wOpf8ABI7/AIKWyh3Pj/Qcn3I/9p19JXXxx+M73jJ/wkd7t3EDGMChfin8ZrwjyfEOoMGXIKjOT39q4o8b4CMm6eFTO54fiKKcZ4pWf905v9gj/gmv+05+yf8AHLxB8bPjdr1n4hOsafLarDpxYv5zspUgMFGPl96++PEHhfx7c2/+i+HL/PdR5f8AQ5r5K03xT8c77Hm67qbjoM8Y/EGvS9PvPjSoEh13Usd8Ef1r5fiTNaOY15YjkcVaySS/yReEwuPhNzdSMpPq7nKeLvgpqviG9s9d8ZeANS1XUdImNxpz4UCGXghiAwB2kAjNeEeKPg58bL15J08JavK8xLSHyl+Ysc4PPA/OvsYeJfi3DH5EniXUkPUcp2+oq5p/iP4oXGo2fneKL91Ew3xsEAYc5BISvlcPPD1pRpe9Zdz6DDzzRaNxf3/5H5N+P/BPxC+HMcbeOdDuNIEySGI3GzMm0ZOADu4/Kvvb4c2zN8PdBYdDp1qf/IS+1fid46+IXxS8Vft8/ErRPiTrtxrdrpNjcLZxTOxSBDjARchRt6Egc1+3fw0lz8OPD5B/5htp/wCiVr+8/CPK1h6VWMHo1B/gz8y8Q686ioue/vbfI//Xu/spLNqPi4xpzt3NxX6BweFL2+vUtEOGnk2byDwD7CviH/gnzYprXj+8t35KwuQPxFfr7YaJDY3MVxLGMxsDj1wc4r/DbxFjD66otaXP9TcA1GnY/PrwLqn7WHx013Xbb9k3wBYat4f8O3j6fLeanOqSS3EXDkDd0wCRjjvXvug/Cz/gqTp6f6V8LfD3HrOp/wDZ68tf4f8A/BTz9nX4m+Ibf9gabR73wv4uvJdUc6sUDW88hLScOQRzwCoO4EdK/Qn/AIJX/tKftX/tL+HPG0P7W8FhDqngzVVsI5dNLRrLKqEyhtrbWAIHJx7V+sYDg3KKmBp1acYN2XXr95/OXE/Eec4XFzipWjfsfO0ng/8A4KdJEJB8KtC45OL1V4Aznqe3tXV/s5/Ei0+Ovg7VdUvLCDT9Z8Pag+malb28wuIkmQZbZIoAb+lfDPhX9vD/AILFftW698Rf+GZNI8ON4b0C9m0Uw3myKZCxaMMpLAvgfMSTj0ya+tv+Ccn7J3jz9j/9nnUPCHxXvYb3xX4k1SXVtQFu/mRQyShRsV/4scnjiuPjfw/wOCy2Va8VUT+FO+h7nBmdZhXqf7VZx9D7J8N+H4f7XgkQbvwr8ef+CfaJoX7N/wC2dCx/1OrXY/WZf5V+4fhaBY9Xi3jBPavwb/YzvYbH9nv9tkFjzq131+s2Kjwmk4YfE69Ejt4/bmoRS2a/MX9hPxAv/ChtHCnr53P/AG1av5Yf+C0h879ra1kJ3cHj/tpX9JX7B1/IfgHo7joRMP8AyK1fza/8FkiZP2r7Ijvn/wBDNfvn0d4ez4ilHspHleL0P+EuTfl+R+TaW++SU9MyOf1qYRYGCKvmArvYd3b+dP8AITn3r/QZ7H8Vqd0ilAg2HnrTzEccCrkEKDOaseWo5/pUgZyxDb81KVRuCDxWj5BLZprwEUAZxjH8IqykRKjFWVtwRk1citlo1AoGP2qUQh1y3atL7IfT9f8A61TR2meopagVIoHABBy/bHSt61t2++3XvU1tZLitNLZs4FMCSJQThfxq2kQGQv60sEYDbXGcelaKKoG7GBQBlGDco4xUJtsvx2xn2z0rZZULk9R+VOaKNcISCfUenYfhQBz9xpjuf3XXvVAaJOG3oMjsK68Nt5HU9aeGUcA0AcmNNuF+YYXHarMFvIqjzTjmujKggnHWmEBlG7JH4UAUol3ZVhz2pxhDcEYq4m3d06dKYVYNk9KAKCIgfJHSvFPjHchri10/PCKZfz4r3xF3PgDJOB9MnrXy78U75LvxZPBG25YAIgfocmgDzhjuO9u9QyHIGKlk+ZQB2qvQAUUUUCuFFFFAXQUUUUDCiiigAooooAKKKKACiiigAooooAKKKKACiiigAooooAUHBzUqtk4qGnp1oAlqVOlR4xzUidKAH0UUUAOT74+taScMfrWan3x9a1UAOQfWgDWtEEitW3FGNorL09Mbh7VtIpEYJoAuw/IMjmtGOX5cisdZfK6c5q5HIQu4/lQBqqgcZJ5q0EGAKx0kZFAz97kfSrccx7npQBZlsoZkO8c1zF1oDOS6dPSutilVl6805xuGRQB5nLY3NvxH0piQyAYkHNd7PaqUyOfas24tWCAhaAOY27farlrK8TZDFTV5rMEZIwaiEPPTpQBqx3lw4Akc4+lTwFJGkiuMPGRyDVCNGXlvyq9ByxDrhWHH4daAPONC36R4jazY8AlfrXtKK0yDivGfFSGw1uK7TgnDGvWtIu/tFnGwPDqDmgCzJDsGQ2K5TU9FhvmDOcn1/pXU3JAbaDkVjTlgpYH7vOKAPItQtZrScxEbQp61W3r6ium8VA+chxwwrj2QbAaAEcuW4IpgGWO//wCtRRQBH5f+f8mjy/8AP+TUlFABHHzUmwZ2Zp0X9afz6j8qAExxs6ZoIQjI60U0sB1oAi2IgO7vUWY+1SyMGxj1qt3P1NAEn7umDqKSgcc0ANZWyOKsKMLTPMb/AD/+qms7Hp/n+VAD33fw/wD16Yevf8abuf8Az/8Arpck9aAIyuPmr1XwRCNS3QyjjGOePx/CvLq7nwxqZ05SxOApAP40Ae5ad4YdZ4Qj/u/OXDHqx5r+jn/g3gT7LqHjOIjaRMnX/gdfzxeHtWW98hCfuSo1f0P/APBv3Ju1fxrNHyDOhz7EPX439ICH/GMVWfp3hDG+cRP1f/bJu9nxV8DMTytyx/8AIiCv3e/b6sW1L4LaNFb/AHo5NIf/AMi1+AP7ZcpPxX8EbuouG/ISpX9CP7WVympfDfTLJucDSD/5GFf5kZpWUMqkk9Wz+quIcK5ZjgmunMfAFr4Jkn1yKCTcEaYL2xtB5zXhXwe+Aug/tkftL/EXwj8XvGl54P0zwVFa22l2ljdC08wEvvmcE/N2Gfev0Lbw7El2rw/eDf418p/H3/gnL8LP2r/GVv4513VdQ8MauqiC5m0xlX7WijCGUEYLKOAx5xwfWvi/DjH4OjjnLGO0Jdd7M+j42oVa2BlTwsrSufQOj/8ABIz4QtD9r0n4teI7u3XjEGoCTnp/DmtKf/glt8INNuF07U/jDr9tK+T5L6okcpAGeFbnofSvmz/gj9+zjpPwH/aq+L3hzSfEGo6xa6F5Fnai+wWKyhXdjztDBhgEcYr4euv2T7P9uj/gpx8e/DnxO8Y6tpNt4YEE1gLJuFZ2C4IJOFA6AAV/Rv8AYmDqyqT9pF04JO6WrP58hVzJVnQjUd0fWv7DvxLt/FPxg+LvwX8J6zea/wCF/AE6xWV5qMgnuJZSxVyswH3NykKADmv0dsNElTVLQnJUTLnPXO2vnr9lf9jn4RfsZeELvwn8K5J9SuNVmW4vtRu8Cadx0Bx91R1wBg9etfWtiNt5bf8AXVf61+DcUzwM82ksAvcS/wAj99yJ14YS9Z3dj+WH4pQDS/8AgpB8VrQ9TYzH/vpUNfuV8K5EPww8Nk/9Auz/APRCe1fhV8fLkp/wU5+KQ/6hz/8AoKV+33wplb/hV3hv/sFWff8A6YJ7V/bHhdD93P8Aww/Jn5lxvO8KLf8Ae/Q//9D0n/glJE2rfFPWEbkw2Tvz6blH9a/dSPw+jjcUxnn1r8Iv+CMN+uq/FvxImc7dMc5/4Gn+Ff0OQrhAD2Br/E/xCwH+1s/0moZg3FxvsVfCemSWeqxyQnYq7uDnkMK+ff8AglHtjs/jFkZ2+KLpj7khjnrX1TpBIv1HbH9K+W/+CVJYw/GTaOB4luf1Vq9Hw/SjNQUuqPynxFd4c/U/Pn/gkXM9vD8bZUZ0Y+KjwrEDl3Gf8a/Wlr4zkuRjjt/jX5I/8Emz5a/GvPQ+KT/6Mev1XM65ODxivM8Xsycc0nFS8vwR9xwXhY/VoysdPoN6Bq0O3PJxX8+f7LeoOn7O37aB6M+sXP8AOY1++WgSZ1i3A/vV/O7+zlqP2P8AZ9/bLTOCdYn/AFaYV7nhbiZywtd+cfzRXFWBUqsEYv7B94f+Ge9DHfM2fxkav55f+CvjJL+1PYMw/hJ/8fNfup+wpr4g+AuiIScZm/8ARrV+B/8AwVf1aK9/aetpXO1YkIye/wAxNf094Ex5eJqse3MfMeMdB/2M7d1+R+cgiBLZ/vN/OoTCQcYz/n6VaW4h5ZHUhjnr605XEmWBH51/fkpwsrtfefwrCEo9GRR24PNTi3Ofu/pUkEy55KjHvWrFMkh2kr+dL3H9pfedEU30ZniEsNu39KUWvqv6VthYlPVfzqzGkJO7K/iaLU/5195XI+zMAWn8IFOTTpGc4FdKn2ZfvMv51aWWHGVK/nVKpD+ZfeP2b7P7jnRp8gI4q2lpjGRW158Xcr+dOEtqRnK/nQ6sP5l94lTfZ/cV47Zdo5FWEiRWzmnC4i/hK/mKa11CHwxX86j2lP8AmRXs32ZbjAXjjFTERKvHOarC4gYbgR+Y/wAalNxbEAEj86fPT/mX3h7J9Ew8w55wKMj7qng88io3uLUcbl/OpkuLIR5MiZ+tDnT/AJl94vZPqmNXI6EUu45xxSG5sGOPNX86RprFRhpU/wC+sUc1PpJfeJ0pPZMCzk4fpSeYAuCDTRc2ePkdSPrml+12/quP96jmp/zL7x8nkx6yRE4BGae3zDAqH7banhSufrSG6jPQqPxqXOH8y+8jkn/KyQt9nVrlzxEpkP8AwEZr4h1G6a+v5r2T70rsxyfU19beL9TWx8L3tyCCxjKLgjq3FfHsgwc4B98URXZpjjCT3TEqEqQcVMBxxQ8Yzwavl/q5XJ5MgxzijA9f8/lTvKG/IyaeIvXNDS8vvJ9g3rZkePekwPX/AD+VTeUvv+X/ANejyl9/y/8Ar0tPL7w+rPsyHHvSgZOKl8oe/wCX/wBekEZHO0n60aeX3lexl2Y3y2/yKQoQcGpMD/nmKcpCf8s1H1zTsv6Yexl2ZX2mkq35i/3F/I1IHXr5f5HFLb/hwVNrdMoUVoBlzzH+tP8AMi/55GhfL7ylH+6zNAzS49xWgzwnrF+Ypu63/wCeQ/I/4UW8vxD2f91lAjFJV/zYl4EKn8DR58f/ADwX8j/jU6dw5H/Kyjg0u04zmtEzRj7sA/I/41CWBOfJH5GjTuT7OX8rKm33FGPcVayv/PEflRlf+eI/KrUF3Q1Tf8rKu33FJgev+fyq3lf+eI/Km5H/ADxX/P40cnmg9m/5WVwB6/5/Kl2Mfu/1qfjvEo+mf8aT5R0T+f8AjRyea/r5j5P7rGj/AGjipkKgdajyvdB+op4dQMBcfjT5PQzcZX0TJKKPOH9w0olUnBQ1fsl3X3i5J/ysVcBhuOOa27ZBITgjrmsyNBIQpZVHua34Wt4EA3ofxP8AhTVHzX3hyz/lZqW4VDnPbFaOSUABrFS7g67k/M/4VbW5iZch1/OlKjbqvvBQn/Ky+q/3qczBThTn6VS+1w9PMT8zU0c9vjmRM1Hs35feP2c/5WXo5Du39B2zVg3Hzc85qgJozwsqGmNLGpG+VR+NHIurX3lKnLrFm9BKOma10uolAQnnoa5i3nthgiRCfXNaQvYkbeWXGMdaOVd0P2b/AJWbJ2c5xioz5TccGs5b6F/uyIfxFWhNB1Dpn6ijlXdfeL2b/lZNJbqFzgVSe1B5AFXpby2VQGkT8xUf2m3I+V0/OjlXdfeEqcv5WZpjC/Kf0pyqXDJuI6bfb1q15kTc70/76oQRN/y0QfU1M12t95PLLrFnE+NIdmnx3CjJztzXQeEL1JtNVCclVx+Rq7qEMVxYvbTSRiNgcAkE9K4vwNPHbXc1pMwA6gk8VKXdoOV9mepyLG0ee9c9dW5baVP8WD9K3x5Lc+Yn50GOB0KiSMHsM0nbuh8r7M828V24Onm5IxtOK80V8qQa+ibzTbXUbd7eR42Gw8Z/irxC6042MrxSAZXP0qouPdfeS4T/AJWYtGCelW/3OPu0gMa84rV0P7yFyz/lf3FbBHWkq3lG9qTaPUVlODS6fePkn/KyKM4p+5c4z/n8qeMDnIqXzYzx/Q1F7bhyT/lZB9CP8/hRyehX/P4VYyvoD9TTSVH8K/gf/rVPtF3Dkn/KypKpOMkcelVtjde1aRCN1AH41AY4R1yxqlIOSf8AKyjRV4bAMBT/AJ/CmFuMBOarTuUoPsypRU43nqpH407a3p/n86V49x+xl2ZWoqztb0/z+dG1vT/P50Xj3D2MuzK1atqx+yXG088H9cVQ+c8FT+f/ANar0W1baTKkEgD9atSgt2HsZdmeieE9auUmhVCWZipwP9nk1/Th/wAG712Zj4zd8k+bFz+D1/LLoF8thqEDA45xubgDPGTX9RX/AAb3TQ2X/CZiM7wrw8joQQ/T2r8a+kBWp/6s1bH6l4OYeo85XuvY/Wb9tN/K+J/gyU/89pP/AEYlf0BfGWMa5omm2OcsU0lsH0Emf6V/PH+2vqUc3jnwjLF2mf8A9GIa/fzW9Vjv/EWlWbHP+haa+P8AgT/4V/lFxHXf1OMY9Wf2Lj8LP6xRlb4U/wATsrfR4zMzOOQc/wA/8a6rSNMWKdNg25NVN4EjE9z0rc0+6G5Gb1r47A0Iwdm92Xja8+RtLc+Tf2A4lg/bL+N5ByPtVqP0HNfGH7HLKf8Agqh+0xIOhhtx+Uor7P8A2Aw037ZPxs2qWDXMBJAzjAHHFfDv7HrPD/wVH/aUjlVkcxw8MMHHnDFf0pOc45RipPZQR+OZTFSzWor6n6mtOQflI6DFWLK9Y39rGeomX9M1gTygDGcFe9P06UHVLQZ6zf0r+ZcJi28e0u5++rDL2OvY/lh/aFvdn/BTT4pv/wBQ5v8A0FK/dX4SzqfhV4ZPPOk2X/ohPevwM/aTlCf8FKvimQc/8S5v/QY6/eL4Qyf8Wn8L/wDYIsv/AEQntX+jXhnpSk/7tP8AJn4Zxw7Qo/8Ab3/tp//R6T/giBOn/C4vFUWemly4/CVB/Wv6LvtYjUgds1/Lx/wRw+MPwa+E/wAWPEmp/GXxNY+GoJ9OkSJ72URLI/mphVY98ckd6/eF/wBtT9isg4+K3h7H/X2tf5CcfcM4qviW4J212Vz/AEFy3H0/eUvI+r9O1mOPUYgx2hztLfWvxj+FX/BQHUP+CdXxL+Jfwt+JXww8R64Ne1e41G11DS4vMiaJwyqOVAJzzkHHNfb1z+2l+xQ6bR8VvDwyMf8AH0p/rTm/bd/Y4EHk3PxZ8OSjtvkRiPxry+CMPi8rrOpOg5+qseZn+V4fHRUZSsfFf/BKTRvHFn8LPiH8UPGmhXXh2Dxj4g+26bbXq7ZnhJLZwe3PXAr9OVeTPzcE9uteCz/tp/sWXbL9o+Kvh59n3f3wUDtxzUA/bK/Yoj+VPil4fB/2bkN/jXy/HGUY3NcbPFujJXeyR9RkNbDYSn7Ln0PqXwv/AMhiH2NfzT/CLVV0/wCCf7YkBO3frEp/8fk/xr9x9C/bW/Yth1iL/i6WhD3+0qP5ivwE+Akmm/FXRP2mfBHgLUob6HxZrTxadeI37mUu0jBwQPuntX13AWVVcDhas8RFwjzQ3/xK4Y7E06+KjGnroeS/sZ63cWXwL0NVGUZZGLE4HMrnnrWn8ZP2M/2c/wBo/wAVweNfidJfQ6hFGE22LK0RAJOckDmuL+GP7BH7efgLw9D4W0fxPpSWdvuEKMobALFjyUzwTXvWk/sX/wDBQhogE8U6SP8AdQf/ABNfoNfOaeBzCeNwGNhHmb1TfX5Ho5jhqeJw8aVelzeR892//BKT9iqVcm61zB/2o61of+CUX7Esa5+1a3g/7UdfTMP7Ef8AwUQmXB8V6WB/u/8A1qsR/sHf8FDZnx/wlmmHP+z/APY16C8Uswe+Yr73/kfLR4Eyx6vD2+SPl8/8Eq/2J4zlLvWB/wACWpU/4JZfsX52pe6ufbctfV0f/BPr/goXKMnxXpv/AHz/APWpB/wT1/4KGE4/4S/Tx/wAf/E0n4n4z7WYL73/AJDfA2VLeivuPldv+CWP7Gw5W51Yn/fX+imj/h1r+xyvW41f8JB/8SK+qz/wTy/4KGAZ/wCEwsD9F/8AsapS/wDBPz/goVHwfFtgf+Af/Wqo+KOKt/yMF97/AMg/1Hyn/nwvuPl1v+CW37GZOXudWz7yLn+VA/4JZfsYkZ+1ar/38X/CvpZ/2B/2/wBFxL4ssc+wx/7LVc/sHft9ryfFtj/n8KteKeK/6GC+9lrgLKWr+xX3Hzh/w6z/AGMgc/atW/7+D/4mnj/glz+xkB8txqx/7aL/APE19F/8MK/t8ngeLbP8v/saaf2E/wBv4DK+LLL/AD/wGn/xFPF9MxX3sf8AqFlX/PlfcfOrf8Euv2NO82qn/tov/wATTR/wS7/Y13YE2qj/ALaL/wDE19EN+wr+3/0bxZZfkP8A4mhP2Dv2/Sct4us/y/8ArUf8RTxn/QwX3/8A2of6i5Z/z4X3HgA/4JbfsaPyJ9Vz/wBdF/8AiaX/AIdcfsbLx5+q/wDfxf8A4mvocfsJft+qcL4stD74/wDrU8fsI/8ABQAjI8XWf5f/AGNJ+KeM65gvv/4ALgTK+tBfcfOLf8Euf2L26z6x/wB9LUZ/4Jb/ALFpHNxrGP8AeWvpFf2EP+CgZb5vFlnj/d/+xqb/AIYO/b9HTxZZH6j/AOxqH4p4v/oYr73/AJA+Acpf/LlfcfMv/DrX9iztcax/30tOX/glp+xeRgXWsf8Afa19Ln9g/wDb/wC3iyxH1XP/ALLQP2Dv+CgnVPFlgf8AgH/1qX/ET8Y9f7R/F/5Fx4Ayq2lFfcfNQ/4JX/sYd7nWP+/i/wCFP/4dZ/sX4x9p1j/v4v8A8TX0kf2EP+ChB/5myx/74/8ArUn/AAwf/wAFA+v/AAl1j/3z/wDWo/4idjP+hl+L/wAiP9QMpX/LhfcfNi/8Er/2MAc/adX/AO/o/qlSf8Osf2Mf+fnWD9JE/wDia+kf+GDf+Cgn/Q32P/fH/wBalH7Bn/BQQnA8XWB/4Dj/ANlprxSxf/QwX3v/ACIXBOVJ3eH/AAPl7Uv+CT/7FeqW/wBmmutaCZz/AK1P/iawB/wSB/YY2hXu9dOPSRP8K+wG/YK/4KD5yvi3T/0/+Jpv/DBv/BQpeP8AhLdO/T/4mumn4s5hHbMfxf8AkW+Dsn/6B/wPj/8A4c9/sId7jXT/ANtE/wDiDT2/4I9/sHHn7Rruf+usf/xNfXn/AAwb/wAFCP8AoatPP4f/AFqef2D/APgoaAf+Kp04+23/AOtV/wDEYMx/6GK+9/5Ef6mZN/0Dfgj44P8AwR8/YS3cXWu/9/E/+IpR/wAEfv2EB96613/v6n/xuvsE/sH/APBQ/r/wk2m5/wB3/wCxpjfsH/8ABQ7+LxNpv/fI/wDiaf8AxGDMf+hj+L/yLXBmS9cP+B8hj/gj9+weel1rv/f1B/OOnj/gj1+wgeftWu/9/o//AI3X14n7CH/BQwDnxNpp/DH/ALLVlP2EP+Che3/kZdN/z/wGj/iMGY/9DH8X/kNcGZJ/z4/A+OD/AMEff2Dgcfatd/7+x/8AxFNP/BHz9hIcm517/v7F/wDE19kL+wV/wURYn/iptNx/n2qX/hgL/gonJ/zNWmY/z7VP/EYMx/6GK+9/5B/qdlH/AD4X3Hxh/wAOfv2ET0uddH/baP8A+IpR/wAEfv2EV63WvfhLGf8A2UV9nD/gnz/wUQY4/wCEq0wf5+lW0/4J7f8ABRHHyeK9O/4CM/8AspprxfzH/oY/i/8AIUuDcnt/AX3HxUv/AAR+/YQJ/wCPrX/+/if/ABJqX/hz3+wfj/j617/v4n/xFfaf/DvT/gor28Wad+PB/wDQRUg/4J3f8FGmG4eLNN59/wD61P8A4i7mX/Qx/F/5ELg7KP8AnwvuPik/8Eev2Esf8fOvf9/I/wD4mmr/AMEef2E883OvH/tqv/xFfbf/AA7l/wCCjnX/AIS7Tf8AP/AKUf8ABOX/AIKPnj/hLtLGf8+lNeLuY/8AQx/F/wCRceDso/58L7j4lb/gjz+whj/j413/AL+r/wDEVH/w55/YR7XGu/8AfxP/AIkV90R/8E3v+Cjj9fF2ln/P0qQf8E3v+CjS8f8ACW6Z+H/6qP8AiL2Y/wDQx/P/ACG+D8n/AOfC+4+FR/wR5/YQPJuNe/7+J/hTf+HPP7CP/Pxr3/fxP/ia+7v+Hbn/AAUgblfF2mY+v/2NRn/gmz/wUjc4Xxfpg/z/ALtL/iMGY/8AQxX3v/IyfBuU9KK+5HwyP+CPf7Cg6Ta9/wB/E/8AiaT/AIc//sIry82vY/66L/8AEV93L/wTU/4KSg5/4THS/wDP/AKlH/BNX/gpIeD4v0z8/wD7Gk/F/Mtv7R/P/IFwjlP/AD5X3I+DR/wR/wD2D2+7Pr3/AH8T/wCIo/4c+/sI/wDPfXv+/qf/ABFfeB/4Jof8FIj/AMzhpf8A31/ilH/Ds3/gpGenjDS/++h/8RUPxbzL/oY/i/8AIr/VLJutJfcfB/8Aw5//AGEB/wAt9e/7+R/4Cm/8OgP2D/8An617/vuP/wCJr7y/4dm/8FJM/wDI4aZ/31/9hSf8Ozv+Ckuc/wDCX6X/AN9D/wCJqv8AiLeZL/mY/i/8iXwlkvWkvuPg7/h0B+wd3ute/wC+0/8AiaU/8Egv2DBytzrp+sif/Eivu/8A4do/8FJF5Hi/S/8Avpf/AIil/wCHav8AwUm/6G3Sz/wIf/EUf8RfzH/oY/i/8g/1RyX/AJ9L7j4NP/BIH9hN/uT63+Mif4Un/DoH9hYcfaNb/wC/if4V95H/AIJo/wDBSCTr4u00fRlP/slM/wCHZ/8AwUgHH/CX6b+LKP8A2Wn/AMRazF6/2j+L/wAg/wBUcl/58r7j4Q/4dBfsMdrrW/8Av6n/AMRTD/wSD/YYPBudb/7+L/8AEV96D/gmf/wUe7+L9M/77H/xNH/Ds7/go31Pi/Tf++h/hVf8RbzL/oY/i/8AIP8AVHJf+fK+4+DF/wCCQn7DAXatxrX/AH8T/wCJFPb/AIJEfsPjpd62P+2if/Emvu8f8Ez/APgox/0N2n/99f8A1qU/8Ez/APgoz/0N2n/99f8A2IpPxbzP/oY/i/8AIP8AVDJ/+fK+4+D1/wCCRH7EHe71v/v4n/xIpf8Ah0T+w0OGudaz7yL/APEGvu7/AIdn/wDBRjt4u0//AL6/+tUEn/BM/wD4KN7uPF+nY+v/ANan/wARazL/AKGC+9/5FR4Qyf8A58r7j4bH/BIr9hjH/Hzrn/fxP/iKQf8ABIn9hssCbrW/+/i//EV9xf8ADs7/AIKMdT4w03P1/wDrUv8Aw7U/4KQf9Djp35j/AAqf+Is5l/0MF97/AMi/9Usn/wCfK+4+JP8Ah0T+w0etzrZ/7aJ/VBR/w6H/AGF+82uH6SoP/Za+3R/wTV/4KQ/9Djp35j/CpF/4Jp/8FIZP+Zv00/j/AILTXivj/tZj+L/yIfCeUX/gr7kfDx/4JEfsLk58/XB/21Q/+y04f8Eiv2G1+7c65j/rqn/xNfcq/wDBND/go/jnxfpv5/8A1qX/AIdo/wDBRwf8zjpn5/8A1qP+Ir5j/wBDD8f/ALUn/VTKP+fK+5Hwg3/BJD9hqPOyfW/+/qf4U9P+CSf7EhHyza3/AN/U/wAK+5ZP+Caf/BRcfe8X6Yc/59Koyf8ABOH/AIKJWo2t4u00Y/H+lYvxcx3/AEMfxf8AkXHg/KW9KK+5HxM3/BIr9ieQg+frX082P/CrUf8AwSO/YkUYefWh9JE/wr6xuf2CP+ChlqxVvF2nHHt/9jWZJ+xR/wAFB7PiTxVYHPouf6Uf8Rdx3/Qx/F/5G74Iyl6exX3Hy83/AASP/YhBwLjW/wDv4n/xNN/4dI/sSf8APfWj9ZU/+Jr6Vk/Y9/4KAJz/AMJPYH/gH/2NUT+x/wDt/E5/4Say/wC+f/saH4u4/rmH4v8AyE+Asq/58r7j56/4dH/sSk4SfWgO/wC9XH/oFV1/4JB/sSrNuW51od/9Yn/xNfSH/DH/AO38qn/ip7If8B/+tUZ/ZH/b6+7/AMJNZH/gP/1qF4u4/wD6GH4v/IS4ByvpQX3Hgx/4JKfsTDpPrf8A39T/AApB/wAElf2Jw4cT61keskf+FfQafshft+quR4mssH/Z/wDrVYT9kT9v7H/IzWX/AHz/APWrCfi3jr65gvvf+Q/9Qst6UF9x84n/AIJMfsTqeLnWwfaRP8Khuv8Agkh+xFdx+W02tZPfzI8/+g19Gzfsift+Kdx8S2X/AHz/APWqEfsjft9yH/kZrL/vn/61aw8XMctswX4/5C/1Dyz/AJ8L7kfNSf8ABHj9hwjmfXf+/if/ABNWE/4I7fsNj5hca8P+2kf/AMTX0uP2Pv2+x/zM9n/3z/8AWqzH+x/+30Rg+KLMf8B/+tVvxgzHrmP4v/IT4Eyq2lFfcfMqf8Edf2G5Ot1rw/4HH/hWhb/8EZ/2G5X/AOPrXcf9dE/+JNfS0f7Hn7e2efFNmP8AgP8A9atS2/ZE/byhPzeKLQ59v/sa5KnjNmK2zC/zf+RmuBMu/wCfC+4+dLf/AIIr/sJScNda6f8Aton/AMTVof8ABE79g7OftOu/9/V/+Ir6eh/ZW/buiHzeJ7Tj/ZP/AMTVwfsxftz5x/wk1n/3z/8AWrgqeN+aJ/7/APi/8jSPAeWPeivuPllf+CJ37B2f+PjXf+/q/wDxunt/wRO/YO73Ou/9/U/+N19TD9mL9ubv4ntP++f/AK1O/wCGY/24x/zM1qf+A/8A1qj/AIjlmi/5j/xf+Rf+oWV/8+V9x8pn/gif+wf/AA3Guf8Af1D/ACSmN/wRO/YRbj7Tro+ki/8AxFfV5/Zj/bmP3fEtqPw/+xqFv2ZP26wfl8S2p/D/AOxp/wDEdM1/6D/xf+Rk+Acsv/BX3Hyp/wAOR/2DD1vNe/7+L/8AEVIv/BEb9gwHJvNe/CRM/wDouvqf/hmb9uscf8JNaf8AfP8A9jS/8M0/t2r8y+JrPI9Vz/StP+I55r/0Hfi/8iV4f5X/AM+V9x8un/giT+wWvIu/EH/faf8AxFSj/giV+wWRn7Xr/wD32n/xFfTh/Zv/AG8e/iayH1jpjfs4ft5YwvimxH/bMf1pLxzzP/oP/F/5HX/xDrKv+fK+5Hy9J/wRM/YPX7t5r/8A30n/AMRUcf8AwRP/AGEG63ev/wDfyMf+yV9Qn9m39vA9fFVj/wB+xSf8M0/t3Hn/AISqx/79ilLxyzR7Y/8AF/5Ez8PMr6UV9yPmBv8AgiT+wdgn7Xr/AP39j/8AiKni/wCCJ37BZgKG78QEH/ppH/8AEV9M/wDDNf7d45/4Syw4/wCmY/wq3F+zf+3iIyR4ssP+/Iqf+I35r/0MPxf+RC8P8tW9BfcfK4/4Il/sENybrxAMdxJH/wDEV9kfsv8A7JnwM/Y507VtN+C51CaPVghnkvnVnHlghdhCjAwx4rlR+zn+3moJXxdp3/AoRis6X9nv9vMZz4v0wEdM2y142eeJ+OzGg8PiMwTi+jbt+R6uU8KYHC1faUaXK/JGV+1pqIufE3hKUsuRKRz7utfvZp2qf2p8TtMtYhuKabYbypyMZkPH4V/PJ4j/AGSf2wfF+vaRqvjvxPplzY6bcLK6pDsOAwLD5fXHev0Q+Lv7X8H7O2oWPjiw8JXfjZp4oLQWttI8ZiaEZLnYrcfNX5lmmWwxHsMLhKqqSk+n/Bse7ioqXPJLZH7M3LuJSAOvvWZLqcljKrn7qnJGccfWvwwl/wCC3WpFsyfAjVEPq0sn/wAaqpN/wW7uB/r/AIIaiB3zNIR/6KrpXhXmzdlSV/8AFH/M+Tnm0LclSLPrv4q/Ab9tnwD+0Brfxr/Yf8Q6Pb2/iiJW1Cz1SdY9soUA4G1s8jINXf2J/wBlv4x/A/xn43+O37RmuWWtePPHRjS5WwfdDHFGwbrhcnPHToK+IJ/+C4ekqczfBKXd/wBNG5/9FZqAf8FydALZl+DMkee6ylT+kYr9JxeVcRTwDy90lytWbvHW3zPlsHgsFRxTxPK7n7hOJQSJAce2DmrWmI7alaseAJR19wa/DQf8Fx/D8Z2/8KdvQB6XEn9I6uWn/BdfwpbzBpPhBf5jO7/XycH1G6KvzzCeEWZ06rrShrv0/Q+2q8U0XFwhF7H58/tSObb/AIKSfFN4z/zDyPzWOv3z+D0m74R+Fm450ix/9J0r+aLxh8XL/wDaI/ak8eftFp4fuPDWna5bLFDa3LZbckaglTgdcZr+kX4NXA/4VB4U5/5g9j3/AOndPav7g8N8H7KM6dRaqME/uZ+RcZPmp0ZP+9+h/9L8GtX0nSfEGF1eMyojHAU471Tg8B/D/n/QXGf+mprTicgFux5H41bUZUkcV/BGPniYyapS0P7zy9U0rVUWdK+GPwwlkU3dhI30lOa9m0L4M/BQ2wkl0+XJHTzTXj1tPNEQN2B613mk+I44Nqu3418hj8TmTVo1GfU4VYNrWKZ6ha/BD4GyyBJNHfB/i84g/wAjXovg39nn9m/U/E1h4V1jSLixi1SQQQ325mthK3AV3AwDXl9p4ltJkKrIDxyMnPtV/wAc/Hr41+BfC0HgbwRaWeo+FHlS8kWQHz4515J3DkDPTFePglm1as6Uq1la+ump6M4YSKvGCP1O/wCHOvw4Uq09kzEjJw7FWH1zzX0R8Of2EJ/hXpQ0H4fyHSbMsHZIUG4uerMTyfYdq/HLT/8AgrN+2nZ6Zb6dY2NjJFDGI0Zt5O0DAye/Her8P/BWL9uSRgU0vTT+D/4142c8KZ5i6fsp1FKPnNEUMXhoT56cNT97dP8A2avHsSgf25dZH+yBXa2XwC8bwAbtbuuPpX8/EX/BU39vW6j2xaTp35P/AI1pwf8ABS//AIKFSjdDo9gc+z/418NPwsx9/sf+Bo9GWarpc/ojsfg74rtwPN1q6/Suhi+GHiJHyNZuPyFfzpxf8FF/+Ci8ybl0XT+vfd/jT0/4KC/8FH5jhdBsD7jd/jWU/C7G23h/4GjN4y+tmf0hwfD/AMUpgJq8xH4Vop4E8SAf8hmWv5tU/b4/4KROf+QHYj/vr/Gp1/bx/wCCkjdNDsv/AB7/ABrL/iGGM7w/8DRcMVfeJ/SKPA3iX/oMSn65qrJ8PvEbddXl59K/nJ/4br/4KUYz/YVl/wCPf40n/DdX/BSZvvaFZf8Aj/8AjUvwzxi0vD/wNF/WI9j+il/hhrUnL6xLmqR+FWskn/ibTV/POv7cP/BSSQbv7Fs19hu/qaf/AMNwf8FJQP8AkDWf5t/jUrw1xPWVP/wJf5mTxj7H9C5+E+uDk6zLx7Goj8KdbxhdXl/EV/POf23P+Ckp/wCYJafr/jTf+G2/+CkX8Wh2mPx/xrV+G+ItpKn/AOBIFi3/ACn9DI+FWuDrq8lSJ8LdaB51aSv55o/21f8Ago+3/MEtP1/xpx/bY/4KRLwuh2h/P/Gsn4c4pfbp/wDgSNvri/lZ/RGnwy1VTg6u9WR8NdVJ41WQ1/Oj/wANrf8ABSBjzoNqT9T/AI1cT9tH/gpdgeV4etcf5/2qX/EO8V/PT/8AAkZyxafRo/oj/wCFb6njA1SUUn/CttVX/mKzH8B/jX88a/tof8FNH4/4R215/wA+tOb9sr/gpmoyfD1p+Z/xo/4h1iv+flP/AMCQlXvsmf0Nj4baq/8AzFJvy/wp4+G2rrwNVmH4H/Gv54F/bO/4KYr/AMy/afn/APZUv/DaH/BTH/oX7T8//r1L8OMV/PT/APAkaRxE+iZ/RAPhzrA/5i0tKPh5qZODqs3PsK/ne/4bQ/4KY/8AQv2n5/8A16eP20P+CmP/AEL9n/n8aX/EOMV/PT/8CQOvP+U/off4Z6p1/taaqz/DLVSeNVm/If1r+ewftmf8FM84/wCEetPzP+NPH7Zf/BTIj/kXrT8Sf8av/iHmJ/np/wDgSJdaS1sf0GH4Z6oOuqzfkKsRfDXU9nGqTfhgV/PU37Y//BTRunh60/X/ABqI/tl/8FO4ztTw3Zkfj/jSfh3ietSn/wCBIl4lv7DP6Hv+FZaueRqs/wCa03/hWmrf9Baf8xX88f8Aw2h/wU//AOhbs/yP+NA/bO/4Ke558NWf5H/Gl/xDrEf8/Kf/AIEg+sS/kZ/Q23w01fHzaxPj6CmD4aap21ef/wAdFfz0D9s7/gp3njw1Zj8D/jS/8Nn/APBTzv4cs/yP+NT/AMQ6xH88PlNIl4h9Ys/oZT4aaqDk6vP/AOOmry/DnVQuP7Xn/IV/O2v7Z3/BTo8Hw3Z/kf8AGpP+GyP+CnRPPhm0J+h/xp/8Q8xH/Pyn/wCBL/Ml4vyZ/RPH8PtTXg6xN+VTN4CvMf8AIXm/z9TX86Q/bH/4KgH5V8NWePof8aev7Xf/AAVIbgeGbM/5+tT/AMQ7xP8Az8p/+BIX1vyZ/RMPAV3n/kLT8f7taFt4Juo841ac59MD+Vfzm/8ADWv/AAVJPB8MWg/D/wCypy/tYf8ABUx+I/DNofzH8mqZeHmKW1Sn/wCBJCeK8n9x/SGnhG4H3tWuPzq7H4Wccf2pNX82v/DU/wDwVVJ48MWf5t/jUsX7UX/BVM/8yzaZ9Mt/jULw9xj/AOXlP/wNMxlikt7n9KcfhZx97UpKsL4YQHJ1KSv5rR+0z/wVVdSU8L2n/fTf40n/AA0l/wAFYHHy+GLX82/xq14f4pb1Kb9JpESxaezZ/SwvhuMHI1OSr0Xh+MddSkNfzMD9ov8A4KyHn/hGLX82/wAauR/tFf8ABWQDH/CMWn5t/jT/ANQMR/ND/wADRH1nzZ/TQuiW4HOpvT00ezB/5Cb1/Mu/7Q3/AAVefhvC9mW9y3/xVMHx7/4Kyt93wvZY+rf41a4Gr/8APyn/AOBIrmk9pM/puOnWGOdSfFCabpmeNUkr+ZUfHf8A4K1ng+FLE5/2m/8AiqnT43f8FaJDgeEbI/Rm/wDiqP8AUjEfzw/8DQSjNa8zP6Z/7N07/oKP/n8acul6WRltUf8AMV/M3/wur/grWv3fCFp+bf8AxVJ/wur/AIK2Hr4QtPzb/wCKpf6l1/54f+BowdSX8zP6Z/7J0r/oKP8AmKT+y9K6/wBpyfmK/mSb42f8Faw2P+ERsx+Lf/FUg+NH/BW0/wDMpWn5t/8AFU1wRX/np/OaZEqkl9pn9Of9kaZ/0FJD9cUDSdMP/MSf8xX8xx+NH/BWo8f8Iha/m3/xVIPjL/wVnJ+bwjajHu3/AMVT/wBSK/8Az8pf+BIh1ZfzP+vkf05Po+nYGNSb9KaNI00cHUGP4iv5km+M/wDwViAAbwnbD8WH/s1M/wCF0f8ABWH/AKFS3/76b/4ql/qZVX2of+BpG0KsrfEz+m86Vpef+Qg35igaVpef+Qg35iv5kP8AhdX/AAVhH/MpWv4lv/iqUfGr/grDn/kUrX/vpv8A4qj/AFHr7+0p/wDgSK9rL+Zn9OR0rSsf8hA/mKb/AGTpf/QRP5iv5kT8a/8AgrER/wAipaj/AIGf/iqQfGr/AIKxj/mVLU/8DP8A8VS/1MxH88P/AANC/ffzM/pxGlaUP+YgfzFB0fSm5/tA/mK/mQ/4XX/wVi/6FS1/77P/AMVSf8Lq/wCCs38PhW1A/wB5v/iqf+peI/nh/wCBoOasvtM/pv8A7D008jUD+YpP7I0nr/aB/Ov5kP8Ahdv/AAVmHH/CKW3/AH03+NMPxt/4Kyng+E7b/vpv/iqf+pWI/nh/4Ggdaqt5n9OLaTpWPk1BgfY03+ytP/6Cbj6Yr+Y4/G3/AIKwR8nwrbf99N/jUjfGz/grMq7x4Stsf7zf/FUv9S663lD/AMDX+ZlKrNvWTP6bxpumAfNqkn6U19O0wjjVJP0r+YofHz/grCvzf8IjanH+03/xVO/4aC/4Kw9P+EQtf++m/wDiqtcEV31h/wCDF/mTzy7v7j+lC70G2kcmLVJT/wACrLk8LmT5RqEp/Gv5t5v2kP8AgqvD/rPCtqv4t/jVdv2n/wDgqjDEXbwxaqB3Jb/Go/4h/iP+flP/AMCR2xrtdWf0M6t8P7u4lPlahMPxrjNQ+EeuXJBh1WVR+B/nX4Fy/tb/APBUWBN7+GrQZ9Cf6mqz/tif8FP1BH/CO2g+uf8AGl/xD/Ef8/Kf/gSR20sZLm6n7sz/AAS8QMCf7Zl/Sss/A3xGTka3N+Qr8LZP2xv+CnCnMvh20/DP+NQn9sz/AIKWj/mXrb/P/AqS8PcR/ND/AMDR1/XJ9j92R8CvEx6a1N+Qpw+A/iPP/IZl/Ja/B4/tqf8ABTJPueHrX8c/40g/bX/4KcHkeHrP/wAe/wAav/iHWK/mh/4Gh/X5rofvE3wH8S/w61L+QpU+A/iUHLa1L+O2vwcP7av/AAU3PP8Awj1n/wCPf409f20/+CnGMDw9Z/8Aj3/xVL/iHeJ/mh/4Ghf2hU7H73x/BHX4vlbWpvwApz/BTXT01mX9K/BBv20P+CmDr8/h6zz35b/GkX9s7/gpavH/AAj1n+bf40f8Q7xX80P/AANDWMn2P3wj+CuuAZGtTcewp4+DGvZ51qY/UCvwQj/bV/4KXjgeH7Xn6j+tTr+2j/wUvb73h61Ppyf8a5/+IcYvq4f+Bot43T4T97B8FtcHJ1iYfQCpx8HdaTprU35CvwJf9s7/AIKZMMJ4dtfzP+NU2/bG/wCCnLnK+HbXHtn/ABprw3xX80P/AANGMsbbVo/oAPwf1xjkaxMfwFA+Dus/9BaX8lr8AP8Ahsj/AIKfKPl8O23H+f71Cftmf8FPT/zLtr+v+NXHwzxUvt0//A0yVmltkf0A/wDCnNXI51ab64H9KY3wY1TodYl/lX4Fj9sr/gp4Vx/wjtp/n8ab/wANjf8ABTo9fD1p+v8A8VTfhjiFpz0//AkH9rv+U/fQfBnVh93V5/wI/rSH4NatnnV5/wAga/A5f2yP+CmiD954dtD+JH8jS/8ADaH/AAUwz/yLtp/303+NT/xDLEf8/Kf/AIEiHmd38J+9p+DusDj+17gVXPwZ1r/oNT/mK/BGT9tb/gpj90eHLX82/wDiqhP7av8AwUxx/wAi5afiWx/6FWi8LsT/AD0//Al/marNNPhP3vPwZ1wjjWpj+ApB8FtbPXWZvyH/ANevwNb9tX/gpiv/ADL1iPxb/wCKph/bW/4KYn/mAWQ/Fv8A4qmvC/Ffz0//AAJFf2q/5T99T8EtbcbRrM35CoD8DfEIO1Namx9BX4JJ+23/AMFKUP7zQ7EH3Lf40r/tz/8ABShDgaFp2Pct/jSfhdiHvKn8pJC/tWS2iz96ZPgnr+3jWZ/yFV/+FH6+YyP7buQfoK/Bc/t5f8FKBx/YOn/mf8aRf29P+CkIU7tB0/8ANv8AGmvCrE/ZlD/wNC/taT+wfuyfgV4kwfL1y45PoKpz/s9+K5hldcuf++RX4UP+33/wUciGG0PT1/Fv/iqqN/wUK/4KNL10Ww/Nv8aP+IT4l7uH/gaKWZy/kZ+4l1+zn46ZSlvrtwAeuVB/SsC4/Zp+I6jNtr0w28j90v8AWvxPl/4KMf8ABROHPmaLYDv/ABf41Sb/AIKef8FA7HiTRtOP1Lf410UfCTFJ3Tj/AOBr/MTzKX8jP2g1D9l/4tagwWHxBI7A9PLCmvz9+M+tXPw58fSfDY38+tapbpvu5LdN0NqTztkY/dx/OvlUf8FXP297SQXC6Npu8HP8R6fjXlvwv/aL/aW8Q+M9cvdd0+z03T/EsrS6y7DdJNnshYEgegBr6bDeHWMowlUrNOy6T/4I8LmEXNKSPpW48YaulsVe4yMkAbR0/CuOufFM5QsJ+fbiuQnupJICkeVUcCuWllK5JY15f9lYp7qSt53PpPrFBR6HUX3i7UxIVWYtmuavdZv5h5hlbPf5q5e+1aJJM7uayJtQdiQM4PNetgMrrKaumeZiMZT5XynQvqDvIxZiSyEfe9q/oF+D0yn4R+Fjkf8AIIse/wD07pX85CzOZwc+1f0NfBudv+FQ+FeP+YPY/wDpOlf1T4TQ9nSrc3939T8J8Q6t507+f6H/0/PdY/4ITfthaH8t3qXh44A+7ekjp/uVxk//AARz/aisX2XGoaFgf9PZP/slf2HeP/8AV/8AARXyr4h++fpX5xU8OcqnJqUPxP1Cl4g5m9XP8D+ZRf8Agkf+0lGcJe6Hn/r6b/4irsf/AASV/aZUZ+26J/4FN/8AE1/RKn+urQT7tRHwqyXrT/Eip4oZrSlyxkvmv+Cfzswf8EpP2l7Rwy32ie/+lN/8TXW2P/BML9oiP/j6u9EYDqDdMc/hsr98pelVe7VzV/CnJf8An1+Jt/xFrN7bx+7/AIJ+I9r/AME1fjXDGvmf8I90HPmtz/46K0oP+Cdfxnh+8dAP0mb+iZr9qx/ql+gqvH/rR9RWD8Hsitf2b+89L/iK2cRSamvuPx8t/wBgH4x26jcNEI/66S//ABuuis/2Gvi/CP8AmDj6Syf/ABFfrq/3abH3rg/4g9kcnyum/vBeMec94/8AgP8AwT8q7f8AYx+L0Jwx0n/v6/8A8RW9a/sifFWHhm0rI/6aN/8AEiv02b74qo/+tasqngjw/b+E/vD/AIjJnXeP3f8ABPzmX9lH4po3/ML/AO/h/wDiaur+y38Toxnbp3H+2f8A4mv0N/j/ABq3J9w1j/xBHh//AJ9P7w/4jJnXeP3f8E/PKL9mj4ng4xpv/fZ/wqwP2afif3XTf++z/wDE199J96pquPgbw69XSf3mcvGXOr7x+7/gnwKn7N/xMQYI00f8DP8A8TT/APhnH4l+mm/99n/4mvvF/vU2uOp4GcO3f7p/eT/xGbOu8fuPhf8A4Zv+I/pp3/fR/wDiaev7OHxIU7iNO/Bj/wDE193DqKsp96pXgZw7/wA+n9//AAB/8RnzrvH7j4QH7PXxIXGFsOP9ph/7JVyP4B/ERRh0sM/7zH/2SvumoX+9XTS8BuHJO3s2vmH/ABGfO+8fu/4J8Qj4D/EJT92w/Bm/+Iq4nwM+IgGdlh/323/xFfaFTfwfhXT/AMS/8O/yS/8AAv8AgB/xGfO+8fu/4J8XR/Bbx6rD5LA/9tD/APEVaHwb8eDpDYf99P8A/G6+rYv9Yv1rUo/4l/4d/kl/4F/wBrxoztbSj93/AAT4/Pwd8eDrFY/99n+qCm/8Ke8d/wDPKx/77P8A8TX11P2qvR/xL/w7/JL/AMC/4APxozv+aP3f8E+Tf+FPeO/+eVj/AN9n/wCJpR8HvHeeYrH/AL7P/wATX1jRR/xL/wAO/wAkv/Av+AL/AIjRnfeP3f8ABPlEfB/x1/csv++z/wDEU9fhB47z9yyP/Az/APEV9V09OtH/ABL/AMO/yS/8C/4A/wDiNGd94/d/wT5Sb4PeOz/yysj/ANtD/wDEVIvwg8bKMNDZ/g7H+SV9XVYT/V0f8S+8OP7Ev/Av+AL/AIjPnfeP3f8ABPkr/hUXjT/njZ/99P8A/EUv/CovGn/PG0/76f8A+Ir62HUUv+f0oX0fOHP5Jf8AgbD/AIjPnfeP3f8ABPkgfCPxopz5Nn/32w/mlP8A+FT+NP8AnhZf9/D/APEV9XS/6o1Spf8AEvvDn8s//AmZy8aM7vvH7v8AgnzCnwl8ZHkwWX/fw/8AxFWk+FnjFf8AlhZf9/D/APEV9Mp0p9H/ABL7w5/LL/wNmT8Z87/mj93/AAT5uT4aeLU/5drPP/XRv/iKux/DvxWp5trIj/rqR/7JX0JVV/u0S+j5w5b4Jf8AgTD/AIjNnf8ANH7v+CeJDwJ4kAw1nY/9/wD/AOxrQh8F+II+tlY/9/j/APEV6on3v8+lWu9Zx+j1w238Mv8AwJi/4jNnf80fu/4J5nF4b11ODY2X/f7/ABWtSHSdchGPsFofpMP/AImuzf71A+7Wj+jxw3b4Z/8AgTFLxkzp7uP3f8EwYLbVY+W0+2/7+D/4mr8cupA4Nhbj/gf/ANjWv2/D+tB6mp/4l64b/ll/4Exw8YM5fWP3f8Eqx3eoJ96xtz9H/wDsavxapeoOLGEf8DH/AMTUY6Cj/P6U19Hnhv8Akl/4Eyv+IvZx3j93/BNaHxFfRLtNjH+DZrQj8UXij/jyX86wovuVbHQVn/xLtw038E//AAJmL8YM5/mj93/BNX/hLmzn7ClSr4xB4Nin5f4g1y1NHU0v+JdeGn9if/gTFLxgzm3xR+7/AIJ1v/CYR/8APin5D/Cnr4yiUfNZJ+Q/wrjT1P8AntUcn8P4U39HThq3wT/8CZzf8Rezn+aP3f8ABO6HjWH/AJ81/D/9VP8A+Ewtv+fFPyH+FcIvWpe9NfR04a6wn/4GwXi7nN/ij93/AATtv+Ewtv8Anxj/ACH+FH/CYW//AD4p+Q/wrhx9007vQvo58NfyT/8AAmH/ABF7Of5o/d/wTuU8ZQD7tin5D+mKf/wmcX/Pin5f/Xrh4uhqWo/4l14a/kn/AOBM6afinm0ldtfd/wAE7P8A4TOH/nxX8qP+Ezh/58V/KuMpR1FL/iXThr+Sf/gbLfijmvdfd/wTs/8AhNIf+gePyo/4TSH/AKB4/KuToo/4l04a/kn/AOBs5f8AiK+bd4/d/wAE6z/hNIf+gePyqJvGkG7mwT8VGf5GuYqnL/rDTj9HXhpfYn/4GzSn4qZs3a6+7/gnXHxjAefsEf8A3yP8Kb/wmVueP7PjH/AR/hXH1EPv1tH6O/DT+xL/AMCZNfxWzeNrOP3HaHxnF/yzsUH/AABf8KZP4tjuIGVdOjLepwv8hXJnp+NFY1fo8cNp25Jf+BM2oeLOdNXU0vRFR77UJiWWxiAJ4+fH9KzZ5NWYnbZQ/wDff/1q3Y/uj60h6GtY/R44b5fhn/4Ezth4s51b+IvuOKu7TW7nhbK3GeB+8/8ArVhy+G/EkoKi1tRkY+aTj+Vej/xj61Zf7tN/R54bt8M//AmZx8YM6v8AFH7v+CeCX3gTxZcrsW2sv+/h/otYFz8KvGVweIbL2+c//E19IRffq1/GPw/nTX0eeG7v3Jf+BM2qeMGeRV/aJ+qPlB/gz41I3NDZH/gbf/E1WPwV8YE5NvZf99n/AOIr6/fpUVH/ABL5w5/LP/wJmH/Eac77x+7/AIJ8it8EvGG0/wCj2f8A30//AMRTF+CnjMDBt7L/AL7YfzSvsw9DUU33T+FaR+j/AMOfyy/8DYf8RpzvvH7v+CfHQ+CfjE/8u9l/32x/9kqRfgp4xAx9nsv++3/+Ir6+g6mrNQ/o/cO/yz/8CYf8RpzvvH7v+CfHJ+C/jMcCGyH/AANv/iKcPgt4z6+XZf8AfZ/+Ir63k/1jf57Uyto/R94ct8Ev/A2H/Eac7/mj93/BPk8fBjxln/VWX/fZ/wDiKkHwa8ZR8+XZf99n/wCIr6sXqf8APaln6Cpl9H7hy3wS/wDAmH/Eas8/mj93/BPlFvg/4z/552X/AH2f/iKhb4N+NmOfLs/+/h/+Ir6rqcdBWS+j7w5/LL/wJmtLxlzub5XJL5f8E+S/+FM+Nv8AnnZ/9/D/APEUv/CnfGBwBDZj/tof/ia+tKgHUVX/ABL/AMO/yy/8CZdfxdzqNrzT9V/wT5RPwX8bZ4SyH1kP/wATQPgv44/hSy/CQn/2SvrN/u0sHU0n9H7h1/Zn/wCBM5/+Iw5z3j93/BPkl/gt43K/PFZH6yH/AOJquPgh43c/6mw/7+n/AOJr7Am6VFH3pf8AEvvDn8s//A2H/EYc57x+7/gnx63wO8cbj+4sP+/p/wDiaY3wN8cFSPIsP+/p/wDia+w3++frTa2XgFw9/LL/AMCZ6H/EXc75b+0X3f8ABPjBvgJ45PPk6eP+2p/+IqJ/gB46Ycxaf/39P/xFfaH8P+fSlfpUVPAXh5Ru4Sf/AG8znj4z51feP3f8E+IZP2d/iBJ9yPTv+/jf/EGqEv7NnxIbkLpvP/TRv/jdfeUH3D9asn7grkXgZw7/AM+n/wCBMqfjNnXeP3H59f8ADM3xHZSNumf9/T/8RVNv2XviURgrpn/f1v8A43X6Bp/rKnl/1ZoXgbw7/wA+n/4EzJ+M+d94/d/wT84br9lH4myr+6GlZz3mP/xFY0n7IPxWkPyHSB/22P8A8RX6Uv8AdpsfevVwvgNw9KF+SS/7eZtDxnzq28fuPzIn/Yx+Lk2cSaSPbzXI/RK5m7/YY+L1w2fM0T/gTSH/ANkr9bIfuU09TW//ABAvIVpaf/gTL/4jPnXeP3H463P7AfxguOk2gHjsz/8AxusSX/gnN8ap23LcaPgdALiQf+06/ZWHpWzD92tn4K5J2l/4F/wDP/iMWc94/d/wT8Pp/wDgnN+0BIxFtdaOB6faXH/slYz/APBNb9oSYkvdaPnt/pT/ANVr92061XfrUw8F8kv8Mvv/AOATPxjzq28fu/4J+Cc//BL/APaDlOVvNIH0um/+JrPf/glt+0O7cXej/X7Uf/ia/fxehpE+9XYvBrJErqMvv/4BwS8Y86fWP3f8E/A+D/glh+0aR+7vdGLdv9KPX/vmv18+H/7PnjDwr4D0TwvqUtsbnTbC2tZSrMVLwxKjYO3pkcV9G6d/r4/94fzr0Gb/AFrfU16GC4KwGAbhQT1tvr3PPxHHmYY60q7WnZW/U//Z
📡 API Calls Detected
- GET
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Code Obfuscation
JavaScript code obfuscated using 10753 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Donald Trump (Trump Meme Coin) users
Attack Method
obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 10753 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Donald Trump (Trump Meme Coin)
Official Website
N/A
Fake Service
Airdrop/claim portal
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 10753 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
gettrumpmemeairdrop.pages.dev
Registered
Unknown
Registrar
Unknown
Status
Hosting platform (subdomain)
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.