Phishing Analysis
Detailed analysis of captured phishing page
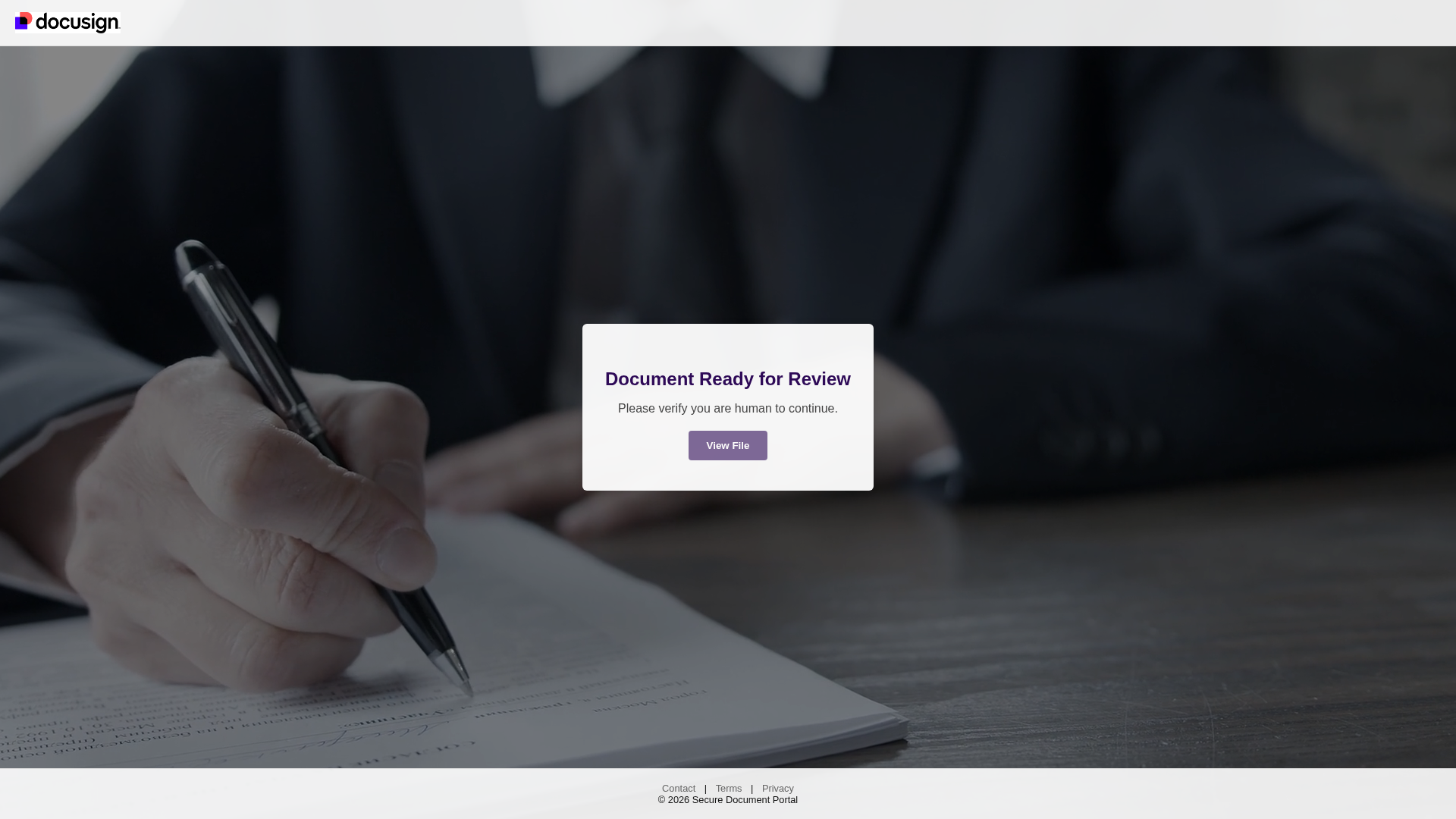
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T142211531B009D81B4662C2C4F7F0A50B3F81C3D9D7482E1576DBA6AA1EF7D59EC1A0D5 |
|
CONTENT
ssdeep
|
12:hRwMy7FU5GKNJdoRG7wv9Tv6qqET7ADAtJD1G7BzAewPrikkWCFwo7Qa59SCIUeD:hR/CCdo9v9zdnh7DmKvUuTCwvOPwyoTp |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
dc2fa7e2d89ca2c0 |
|
VISUAL
aHash
|
ff000018d8e0b8ff |
|
VISUAL
dHash
|
63636232b2ad2060 |
|
VISUAL
wHash
|
ff000018d8f0fcff |
|
VISUAL
colorHash
|
1e007000000 |
|
VISUAL
cropResistant
|
31b1232363636363,ae820baa8eccceb2,4c0c080c0c0c1818,63633232b2ab2060 |
Code Analysis
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: Two-Factor Authentication Bypass
Victim is prompted for 2FA code after entering credentials. The code is intercepted and used by attacker to access victim's account in real-time.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for ipfs.io
Found 10 other scans for this domain
-
https://bafybeifucnntp2tzvo2smmgd2nrz2anlih4bapzou...
https://bafybeidainj73npe2kepzldqmuwzes5stwbgtu2pb...
https://bafybeidzv5orafwm4qq7m5wdptagbyyaksssolxhe...
https://bafybeiby3jwvxj44lno5pu2qjn5ezh5mlm4fkoy4q...
https://bafybeiaz6xbudbilnb4a52kkl2ffapf7oim253s7i...
https://bafybeieqilhn5yjrdt2cs46bglcamzimrcgbfuvq3...
https://bafkreidpy5pr2m6yvnk6v7ry7tu5lydi2rkd5reft...
https://bafybeih4lunv4ykv3qnx3n4c2c3d3gl5vlonz34ui...
http://ipfs.io/ipfs/bafybeibo7ht7ythkoucqnhcd4lzr5...
https://bafybeicfvmv4fni2inofzgesr4hc754scsn2zsohf...