
Phishing Analysis
Detailed analysis of captured phishing page
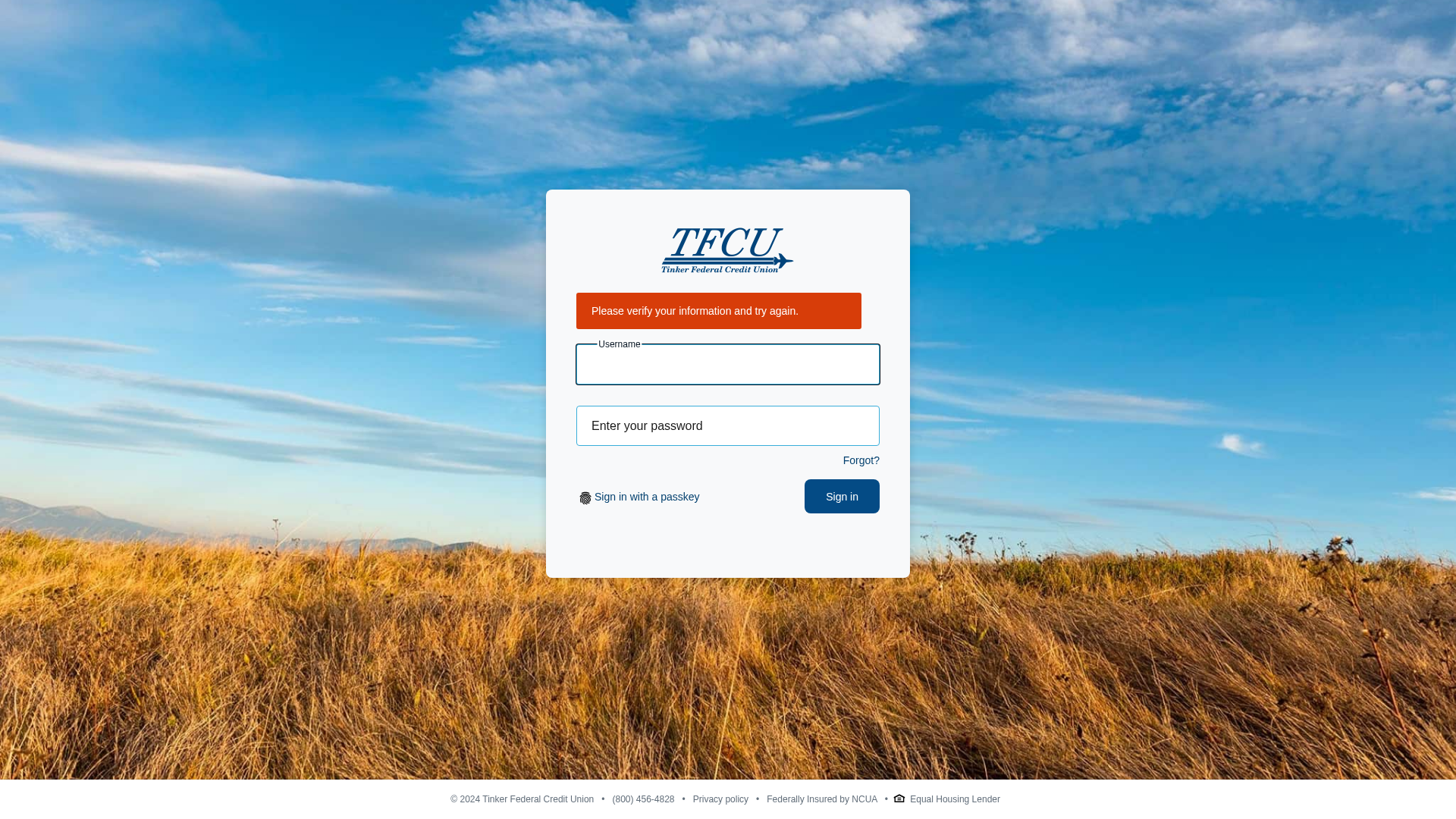
Visual Capture
Detection Info
https://ricardornunes.com/---Tinkerfcu_ldentityverification/session_relogin.php
Detected Brand
Tinker Federal Credit Union
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
aa8564a9-8e4…
Analyzed
2026-04-08 22:33
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T10D5165618000AC2BA19386C437E75BDB7A9147D0C7074724C7FD231DAECBED5DD226A8 |
|
CONTENT
ssdeep
|
48:T8KoN1bywMFi+BIijJ2BUlRhZM9mNPfdOdfHssdCBJpgqu:T8Kk1uwMFi9itlGcNPfdOdfHssdKpgqu |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
dc9f2624951b9959 |
|
VISUAL
aHash
|
0190f8f8fff80040 |
|
VISUAL
dHash
|
77233030b0b11195 |
|
VISUAL
wHash
|
09c0f8f8fff800f8 |
|
VISUAL
colorHash
|
02202010040 |
|
VISUAL
cropResistant
|
3327302330b0b121,92ccc8bf9ece9c38,9793939300960600,030307070f0e0707,eacb1b3ec1416061,00004a20b4dc4210,3122218111519593 |
Code Analysis
Risk Score
50/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🔐 Credential Harvesting Forms
📤 Form Action Targets
- ./assets/grabber/session_relogin.php
📊 Risk Score Breakdown
Total Risk Score
70/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
🔬 Comprehensive Threat Analysis
Threat Type
Credential Harvesting Kit
Target
Tinker Federal Credit Union users
Attack Method
credential harvesting forms
Exfiltration Channel
HTTP POST to backend
Risk Assessment
MEDIUM - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
🏢 Brand Impersonation Analysis
Impersonated Brand
Tinker Federal Credit Union
Official Website
N/A
Fake Service
Account login portal
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
ricardornunes.com
Registered
2015-08-14 20:36:55+00:00
Registrar
ENOM, INC.
Status
Active (older domain)
Hosting Information
Provider
ENOM, INC.
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for ricardornunes.com
Found 6 other scans for this domain
-
https://ricardornunes.com/---Tinkerfcu_ldentityver...
https://ricardornunes.com/---Tinkerfcu_ldentityver...
https://ricardornunes.com/---Tinkerfcu_ldentityver...
https://ricardornunes.com/---Tinkerfcu_ldentityver...
https://ricardornunes.com/---Tinkerfcu_ldentityver...
https://ricardornunes.com/action/chamx

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.